| File name: | R000_24531.vbe |
| Full analysis: | https://app.any.run/tasks/b2eb0152-45d3-42c9-b6d8-2cb8445453f3 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 15:30:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 762B7643CC3E1B676D9DDBF7AADC10D3 |
| SHA1: | 6C1CC7AFBC6DCF01FC4A896D4E609F8481B96990 |
| SHA256: | 39EA694ED35A2A1CC6E9CDF37006827A9EAF60199ABF8FE8EE0CFAA19FA9E1F8 |
| SSDEEP: | 48:WyMUmw7jawbkAMTMTMTMTMTMTMTMTMTMTMTMTMTMTMTMTMTMTMTMTMTMTMToHoHW:WTY7ObZjvVa4AS7KKeHt8Xre |
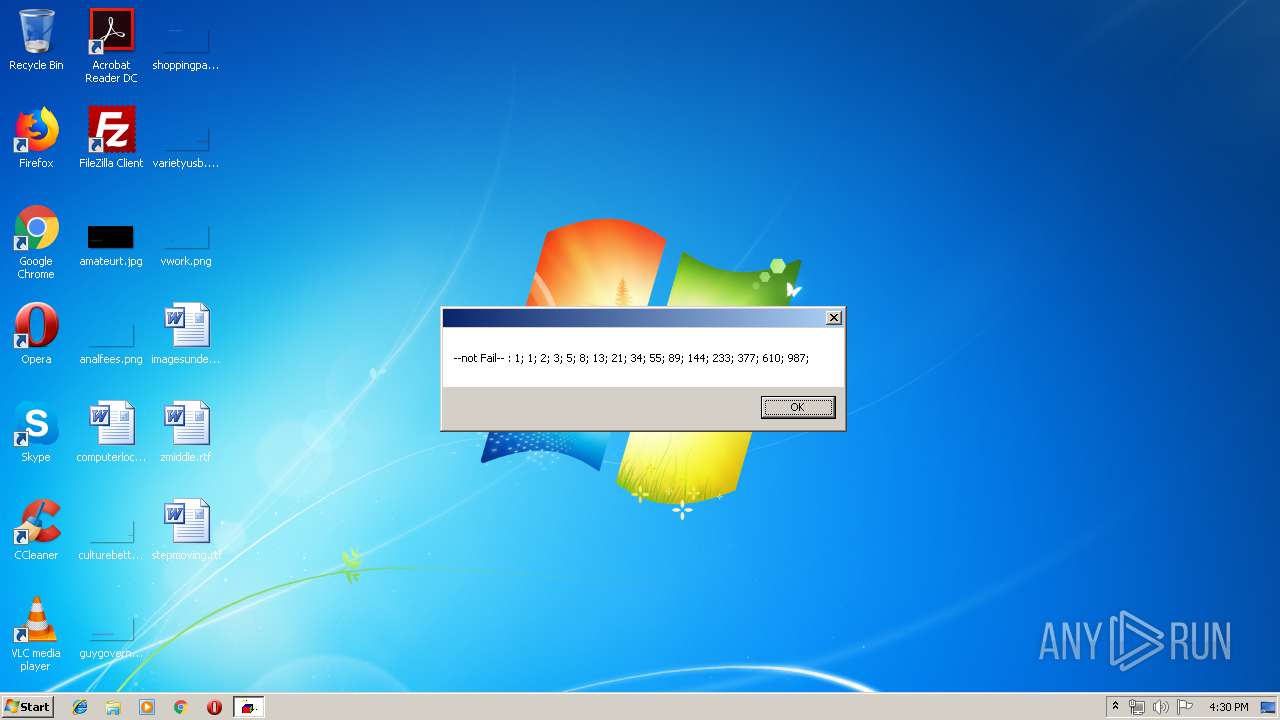
MALICIOUS
Changes settings of System certificates
- WScript.exe (PID: 3948)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 940)
Adds / modifies Windows certificates
- WScript.exe (PID: 3948)
INFO
Manual execution by user
- WINWORD.EXE (PID: 1520)
Creates files in the user directory
- WINWORD.EXE (PID: 1520)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 940 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\stepmoving.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3948 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\R000_24531.vbe" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
808
Read events
713
Write events
81
Delete events
14
Modification events
| (PID) Process: | (3948) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3948) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3948) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3948) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3948) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3948) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3948) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3948) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3948) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3948) WScript.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\WScript_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1520 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7BAB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1520 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{18D980B0-D195-4D45-BFDB-5A393359AFD9}.tmp | — | |
MD5:— | SHA256:— | |||
| 1520 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{EFEFE9E5-428B-4056-BE86-56BF44E89CA4}.tmp | — | |
MD5:— | SHA256:— | |||
| 1520 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 1520 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\stepmoving.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 1520 | WINWORD.EXE | C:\Users\admin\Desktop\~$epmoving.rtf | pgc | |
MD5:— | SHA256:— | |||
| 1520 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3948 | WScript.exe | 185.101.93.178:443 | lulipcxulci.info | Mike Kaldig | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
lulipcxulci.info |
| unknown |