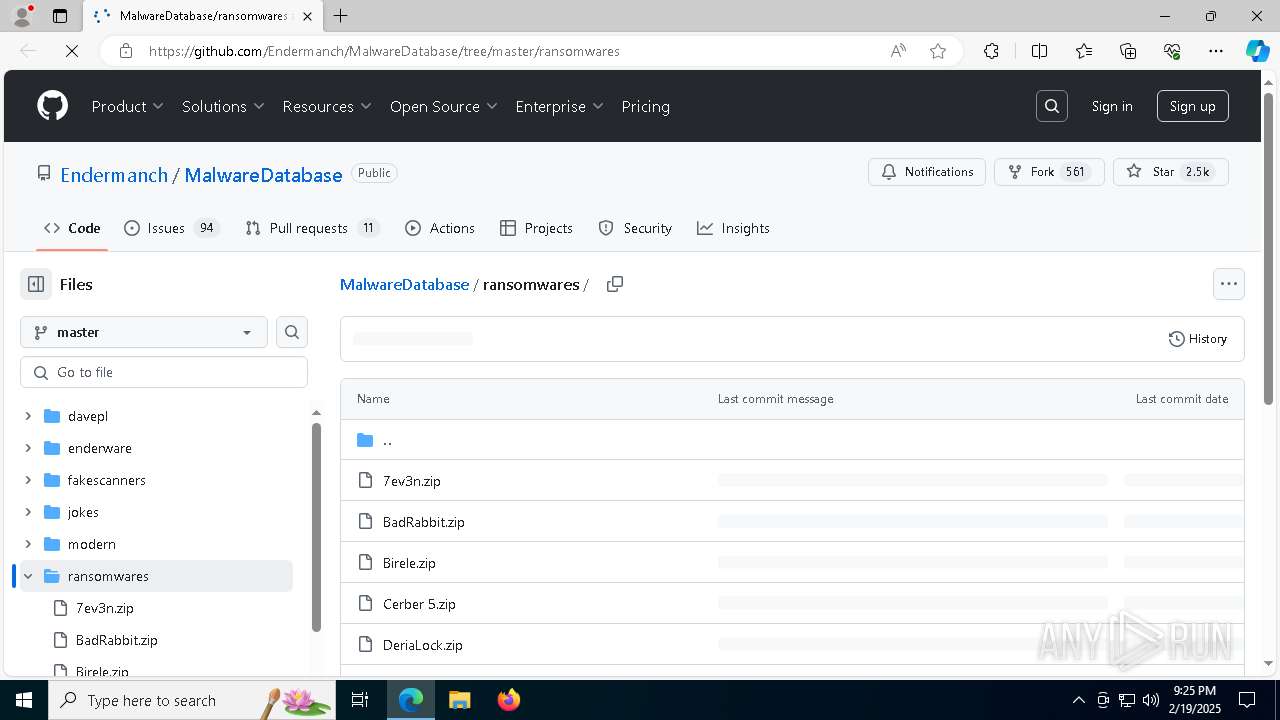
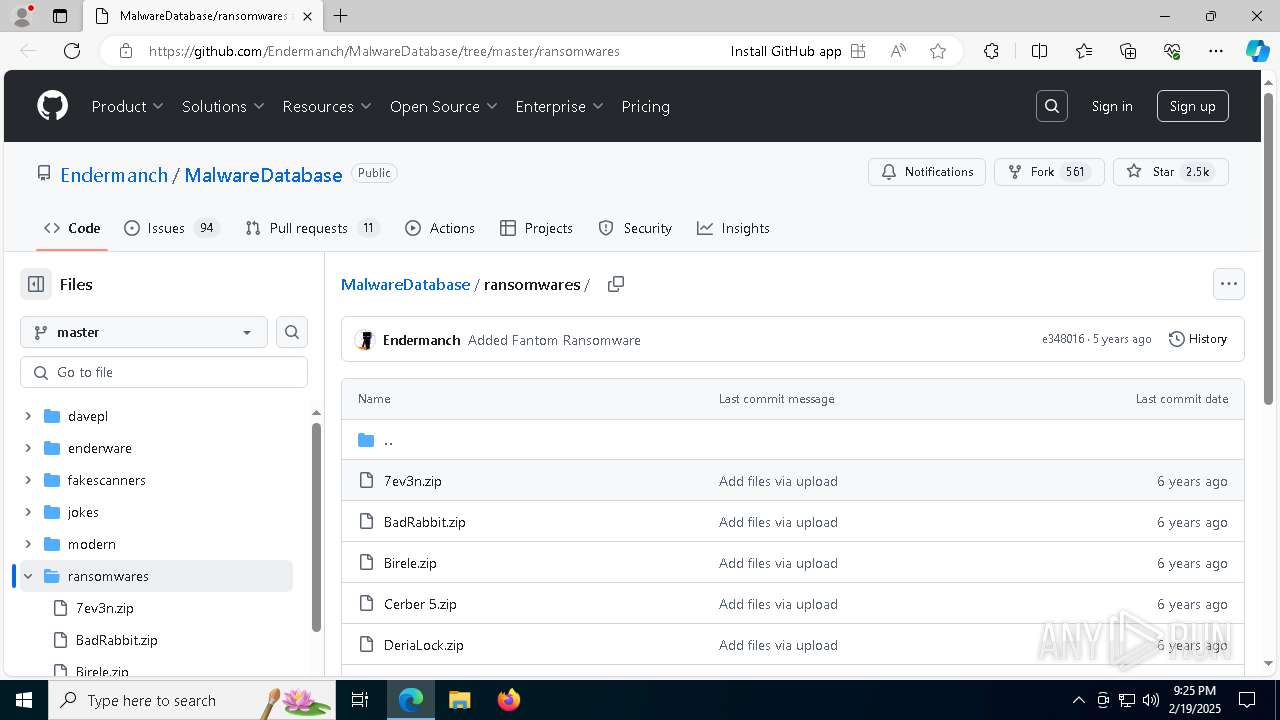
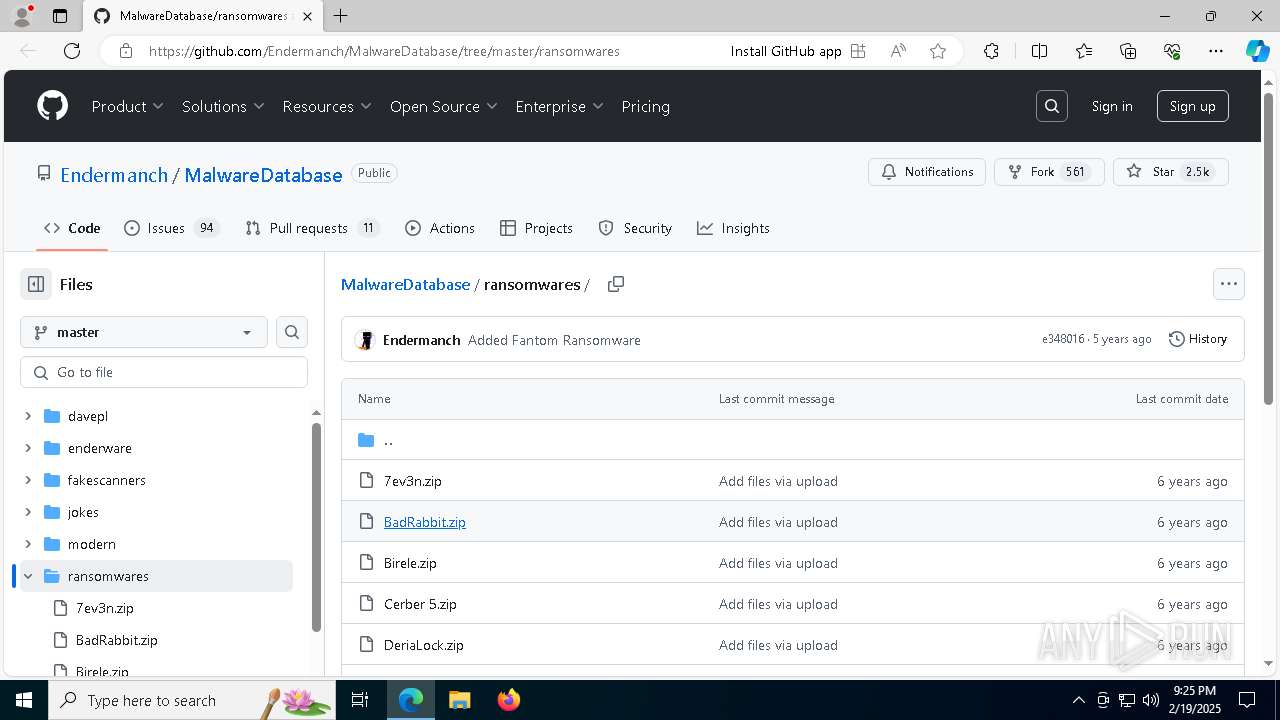
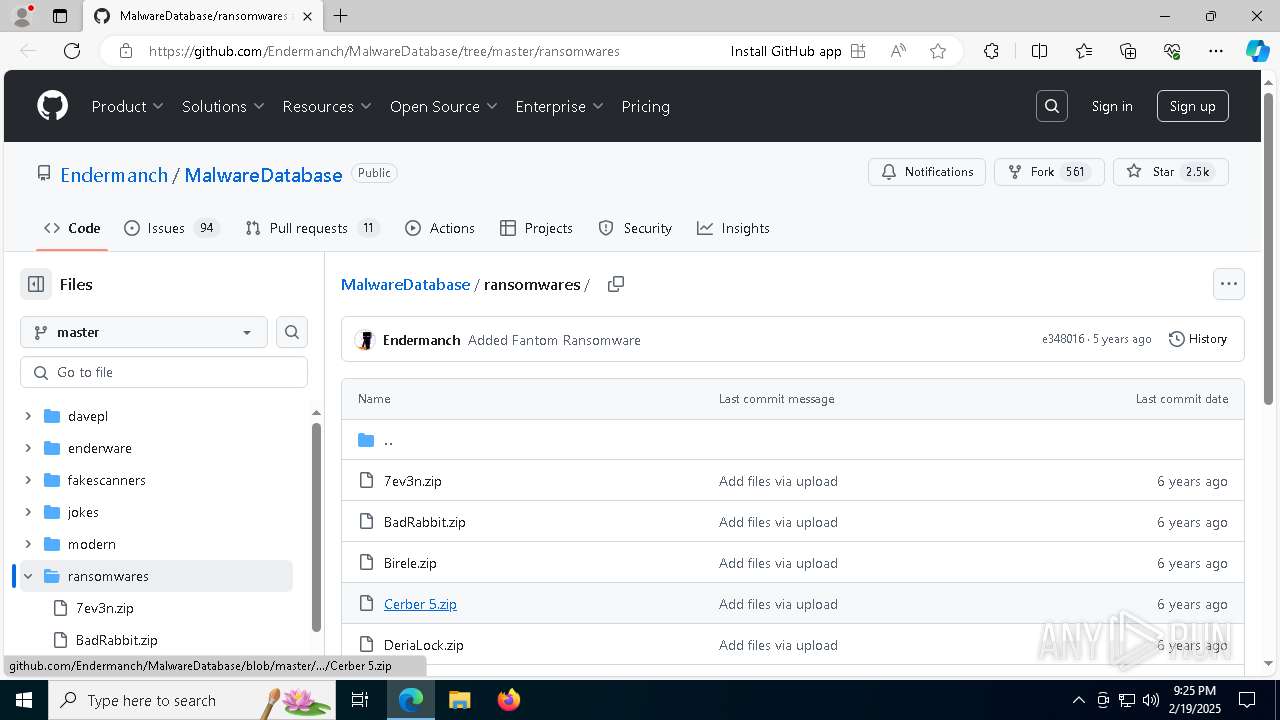
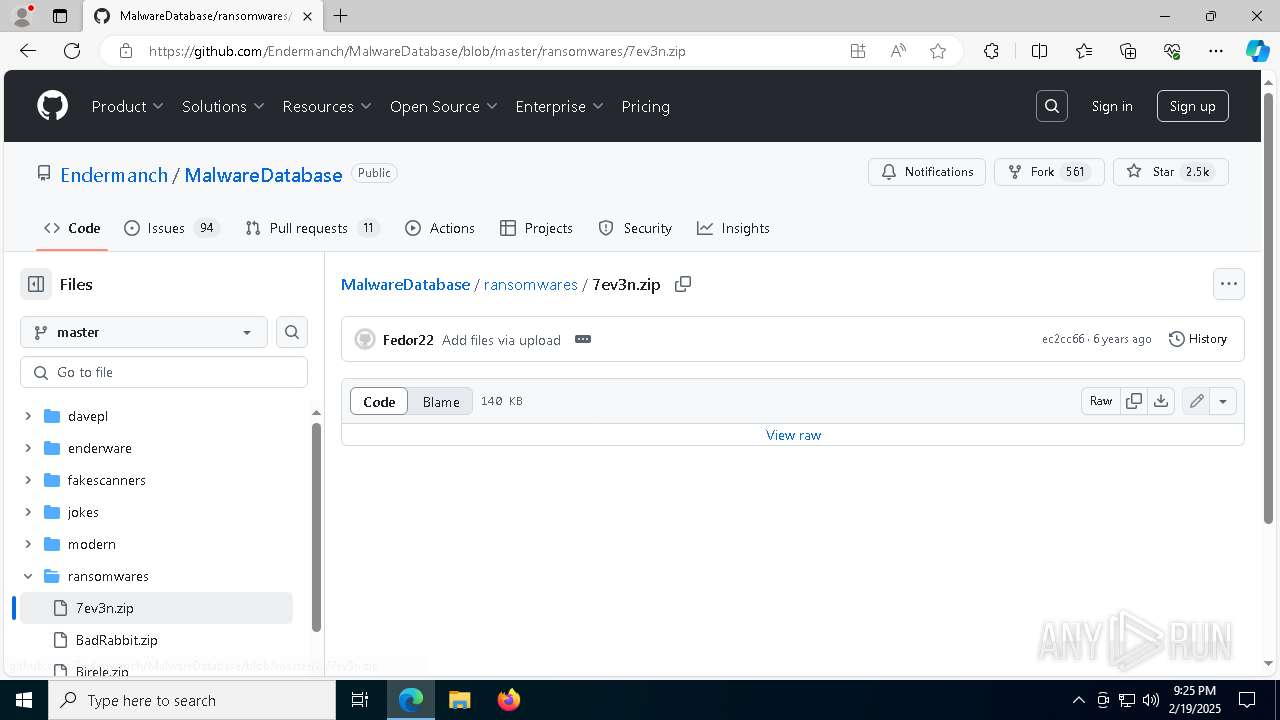
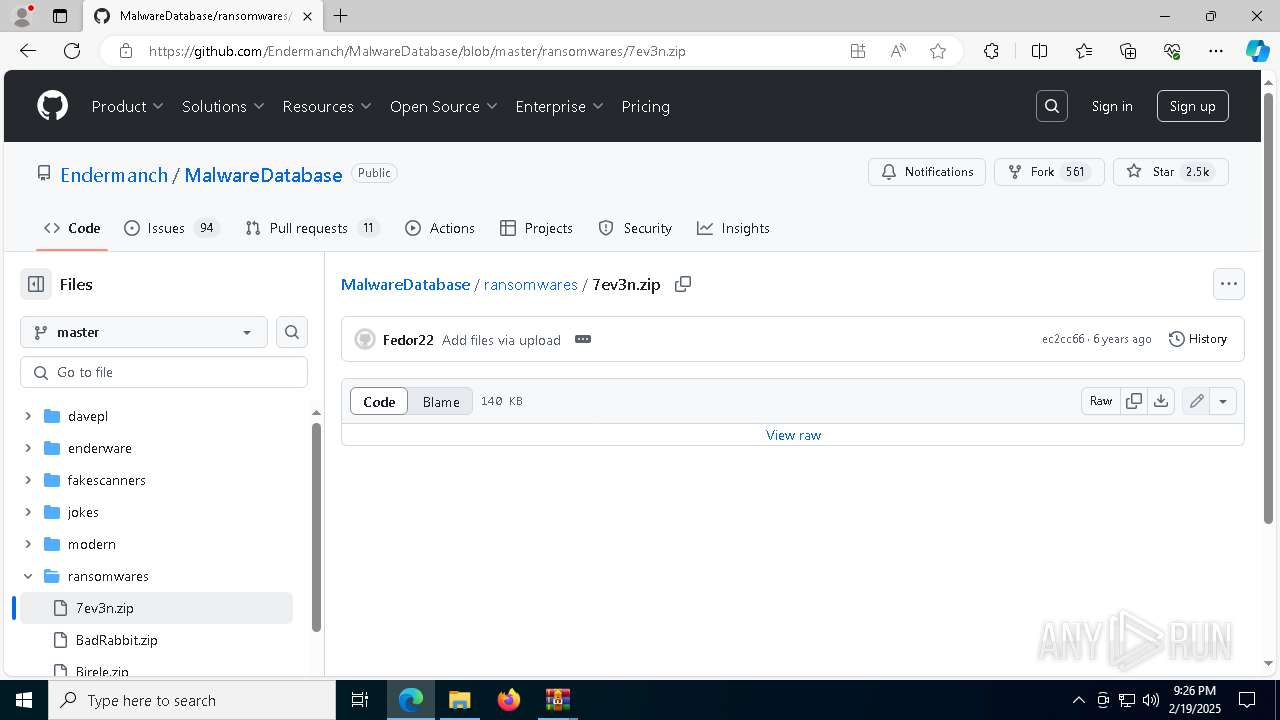
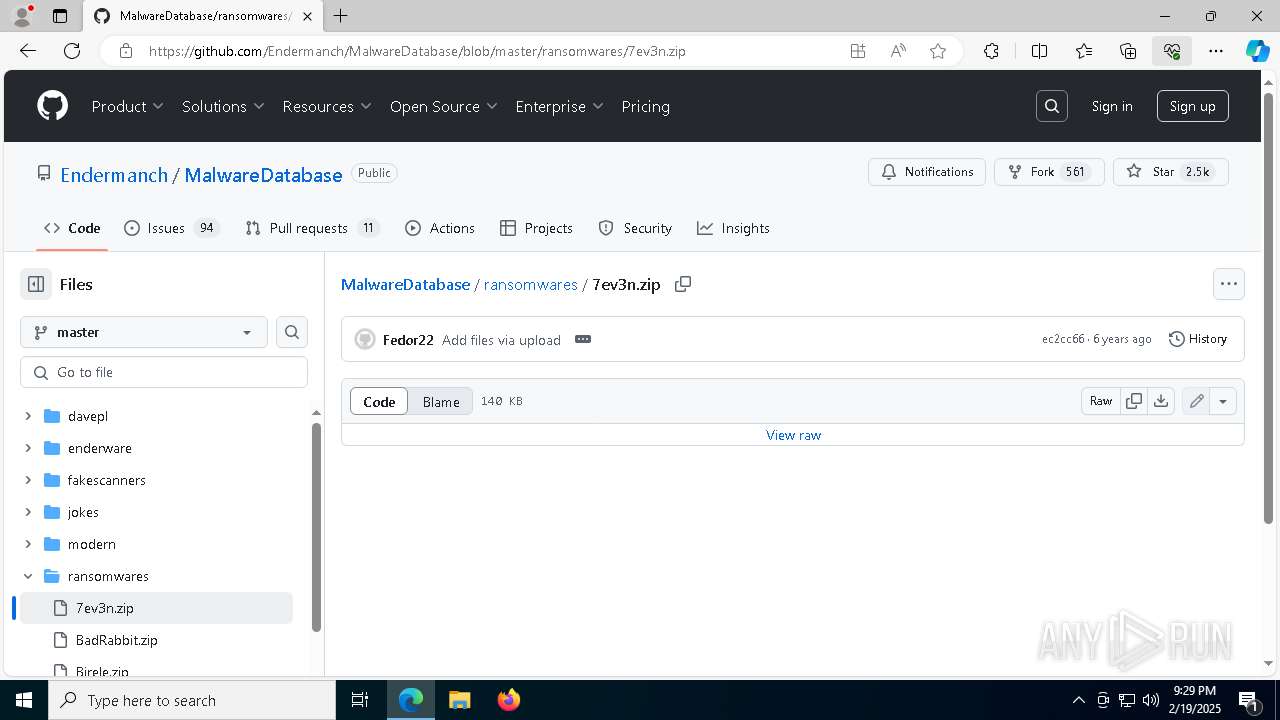
| URL: | https://github.com/Endermanch/MalwareDatabase/tree/master/ransomwares |
| Full analysis: | https://app.any.run/tasks/557d1b29-9046-4a5d-b8ff-33abeb31802a |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2025, 21:25:41 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 86ED1EAAB01CE864EE041A539F2A9DF6 |
| SHA1: | 3C2E03A9D46A7DBC6D0D8B21B8D99ED9C49D748D |
| SHA256: | 39E31F042FC70A5AA3B758FFA2720F7B1C8C190855FC25A4EEF88FF58DAB58B7 |
| SSDEEP: | 3:N8tEdegLaKoEJ3PqxQI+cEie+z:2ufLtfNI+cEizz |
MALICIOUS
Runs injected code in another process
- uac.exe (PID: 7500)
Application was injected by another process
- explorer.exe (PID: 4488)
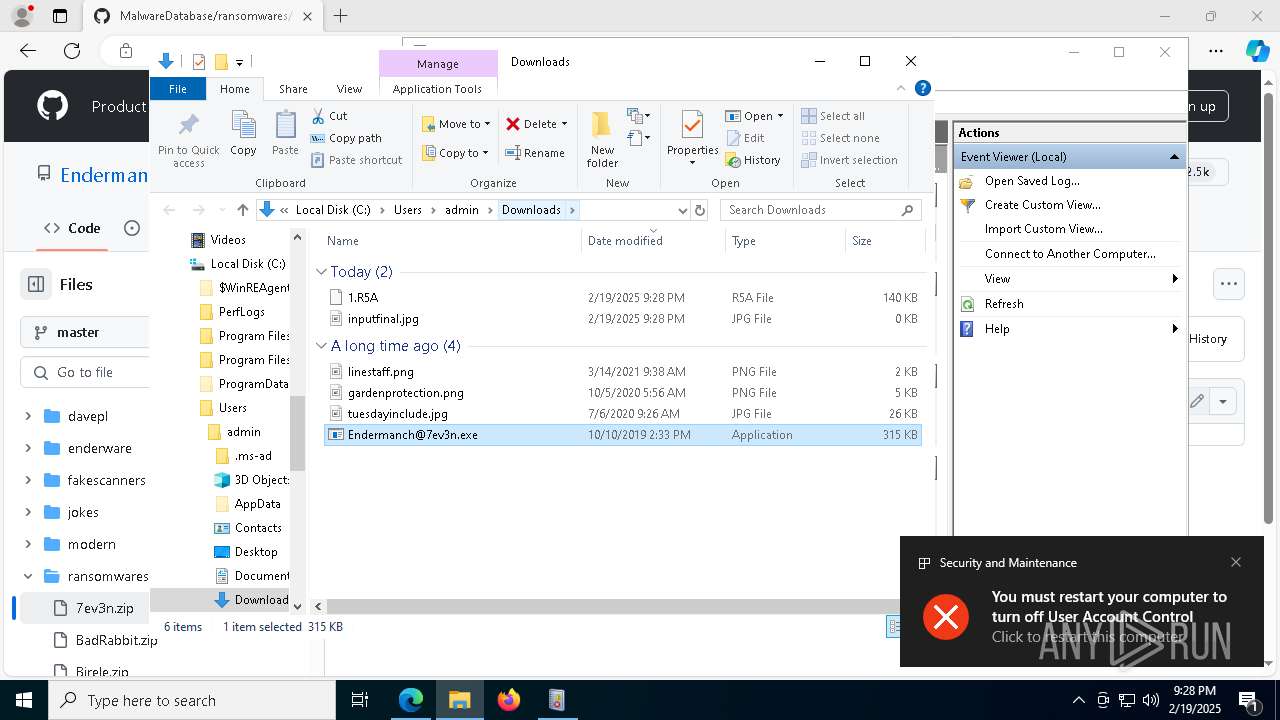
Uses Task Scheduler to autorun other applications
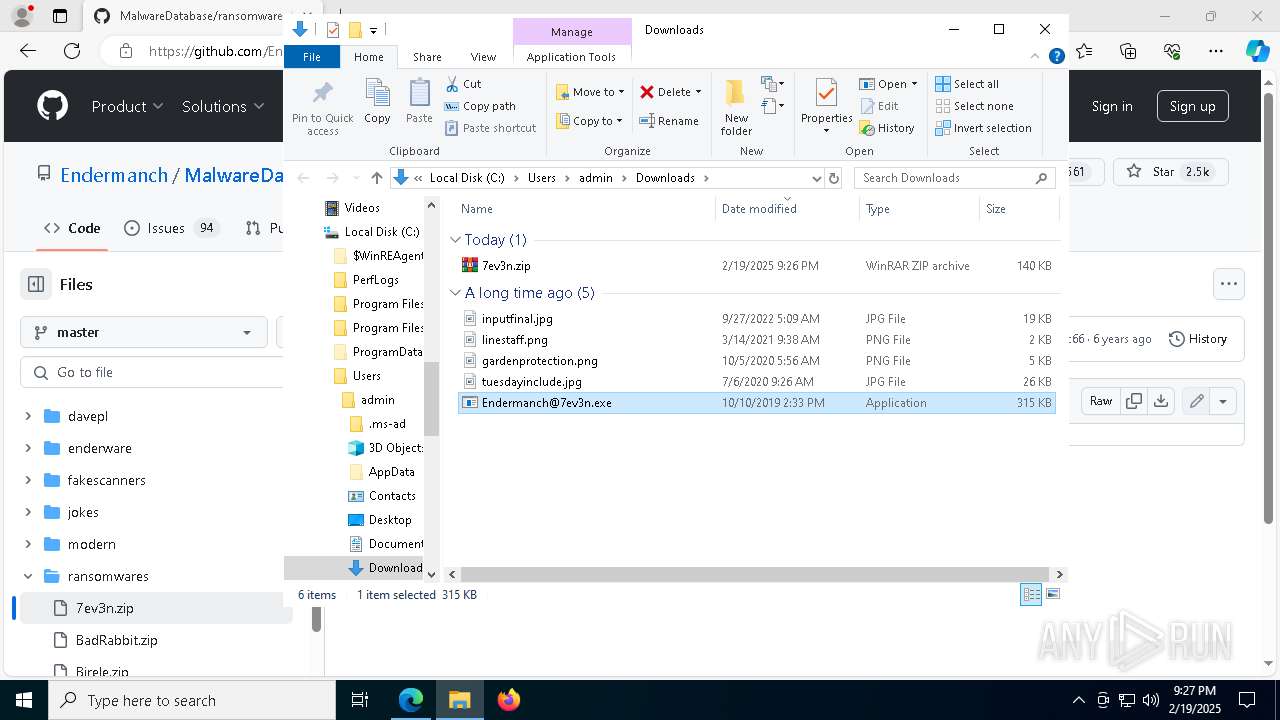
- Endermanch@7ev3n.exe (PID: 6768)
Using BCDEDIT.EXE to modify recovery options
- cmd.exe (PID: 2464)
SUSPICIOUS
The process creates files with name similar to system file names
- Endermanch@7ev3n.exe (PID: 5720)
Executable content was dropped or overwritten
- Endermanch@7ev3n.exe (PID: 5720)
- system.exe (PID: 4144)
- uac.exe (PID: 7500)
- dllhost.exe (PID: 732)
Creates file in the systems drive root
- explorer.exe (PID: 4488)
- mmc.exe (PID: 7880)
Reads security settings of Internet Explorer
- Endermanch@7ev3n.exe (PID: 5720)
- uac.exe (PID: 7500)
Checks Windows Trust Settings
- Endermanch@7ev3n.exe (PID: 5720)
Starts itself from another location
- Endermanch@7ev3n.exe (PID: 5720)
Starts CMD.EXE for commands execution
- system.exe (PID: 4144)
- Endermanch@7ev3n.exe (PID: 6768)
Reads the date of Windows installation
- uac.exe (PID: 7500)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 624)
- cmd.exe (PID: 3544)
- cmd.exe (PID: 4360)
- cmd.exe (PID: 3864)
- cmd.exe (PID: 1416)
- cmd.exe (PID: 3888)
- cmd.exe (PID: 7660)
Executing commands from a ".bat" file
- Endermanch@7ev3n.exe (PID: 6768)
- system.exe (PID: 4144)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 880)
- cmd.exe (PID: 2464)
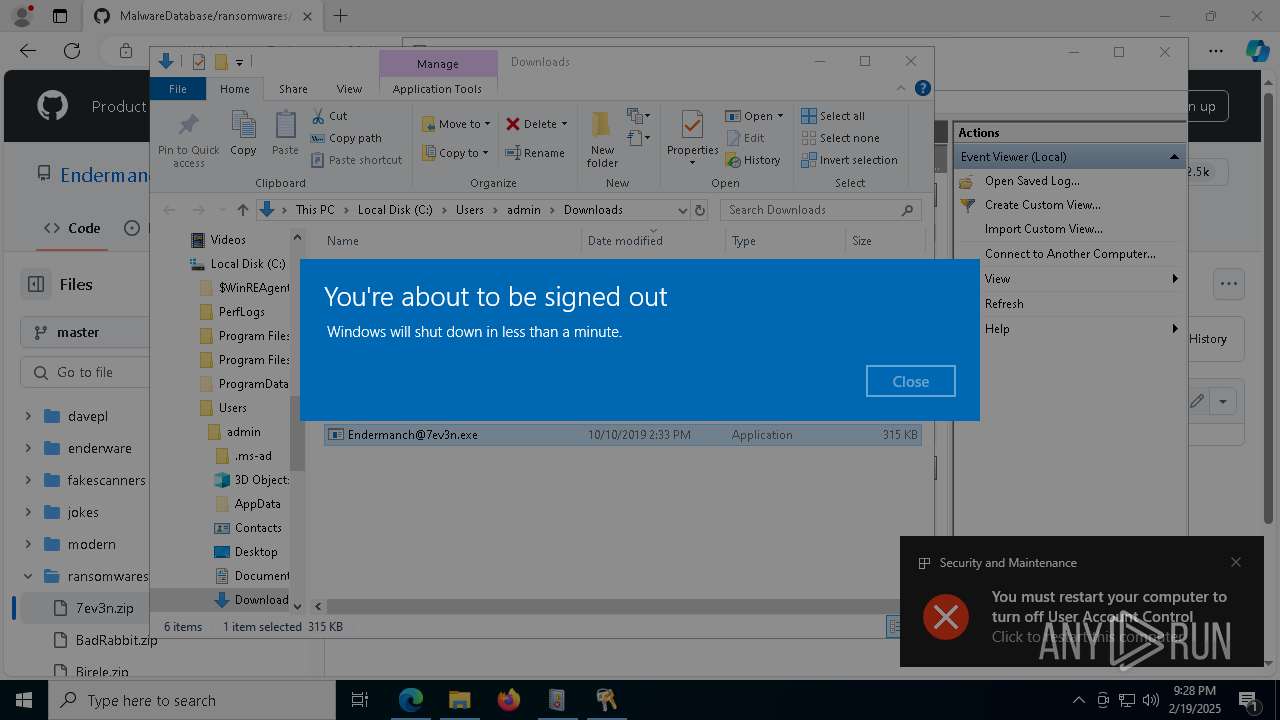
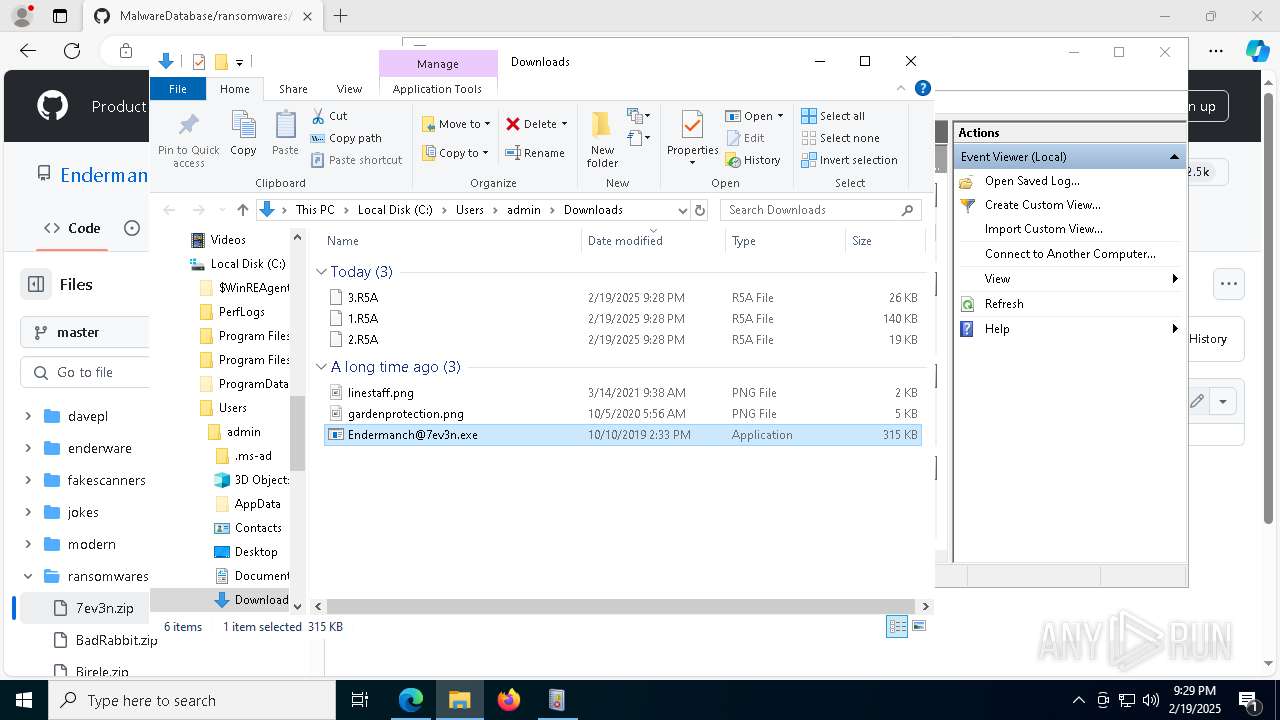
The system shut down or reboot
- cmd.exe (PID: 7812)
The executable file from the user directory is run by the CMD process
- uac.exe (PID: 7500)
INFO
Application launched itself
- msedge.exe (PID: 6316)
Checks supported languages
- identity_helper.exe (PID: 7172)
- Endermanch@7ev3n.exe (PID: 5720)
- system.exe (PID: 4144)
- uac.exe (PID: 7500)
Reads Environment values
- identity_helper.exe (PID: 7172)
Reads the computer name
- identity_helper.exe (PID: 7172)
- Endermanch@7ev3n.exe (PID: 5720)
- uac.exe (PID: 7500)
- system.exe (PID: 4144)
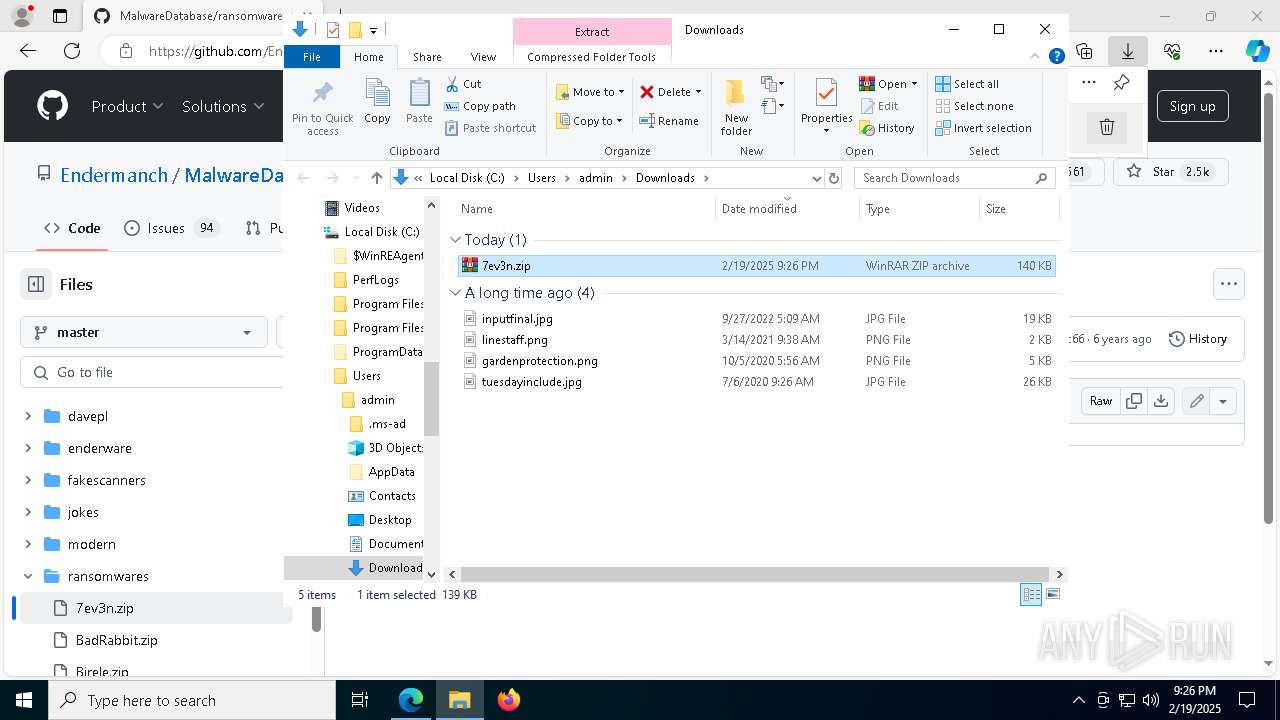
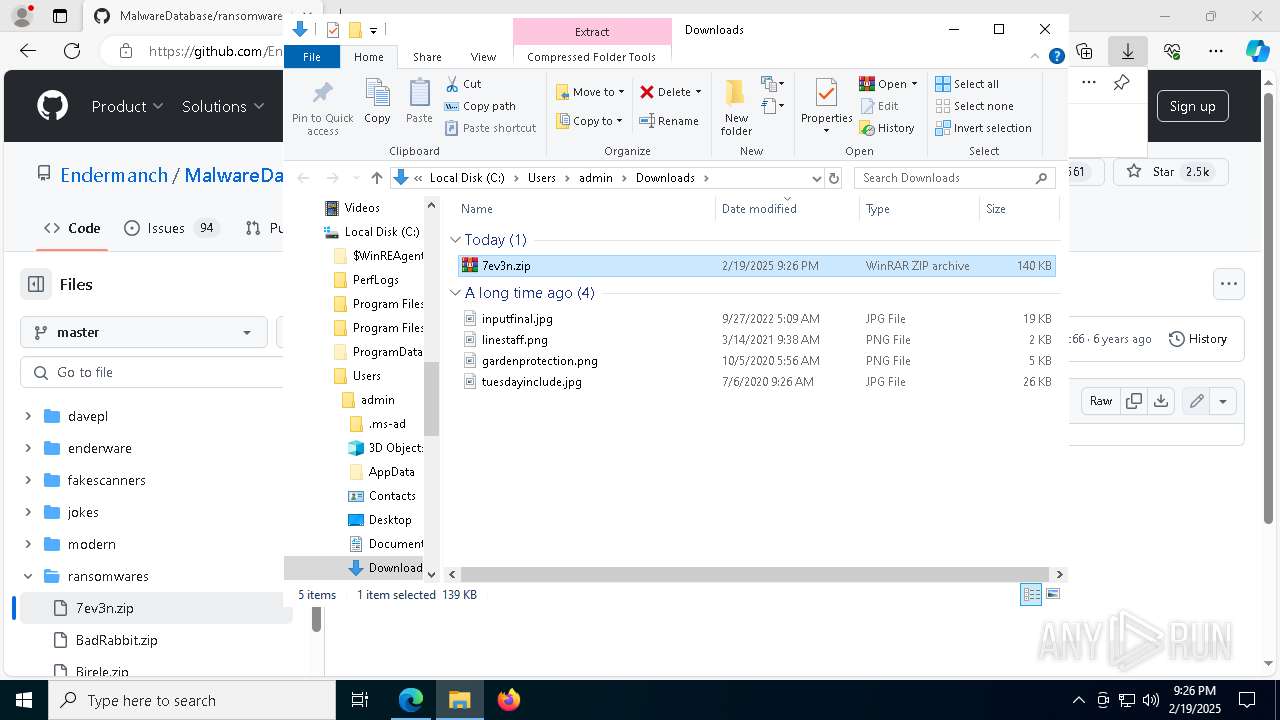
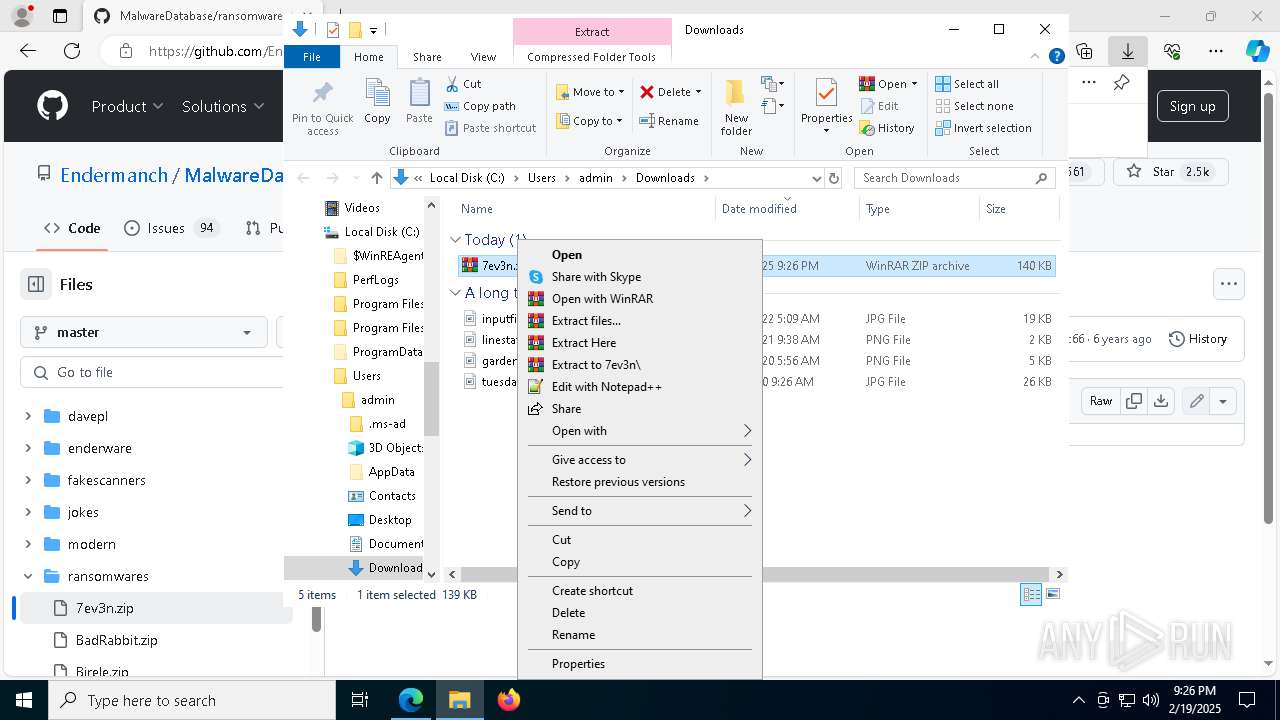
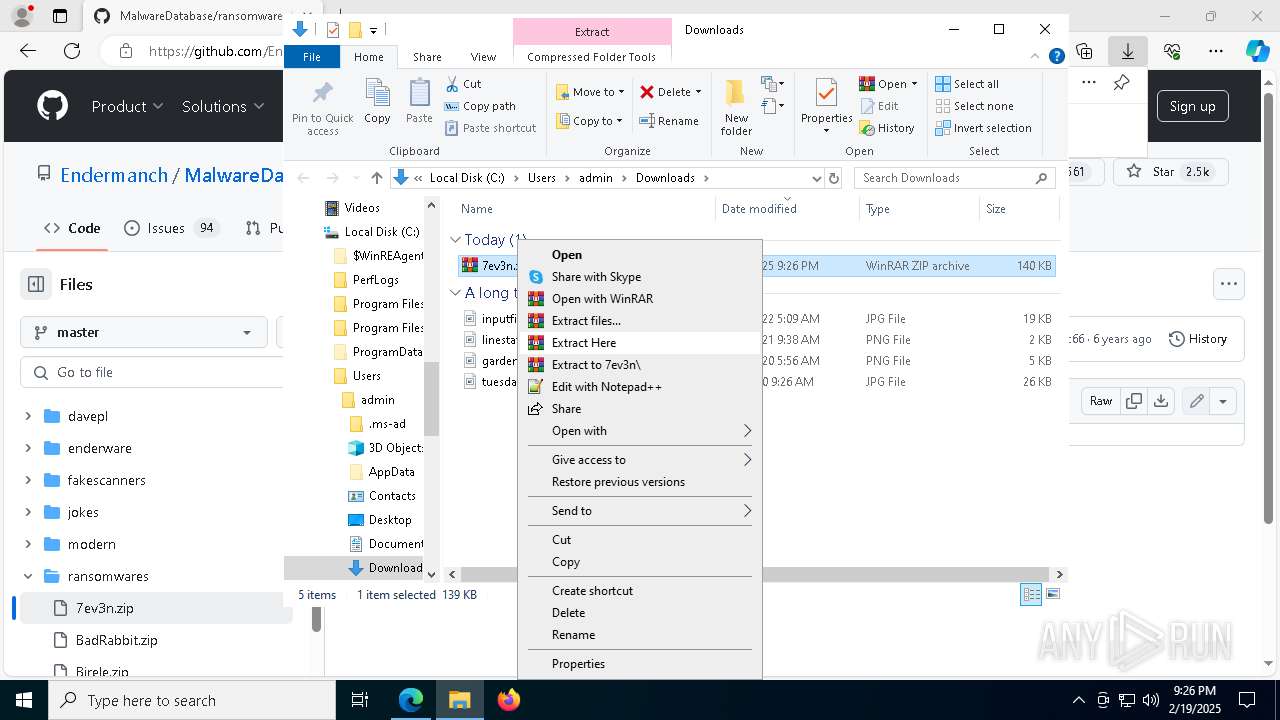
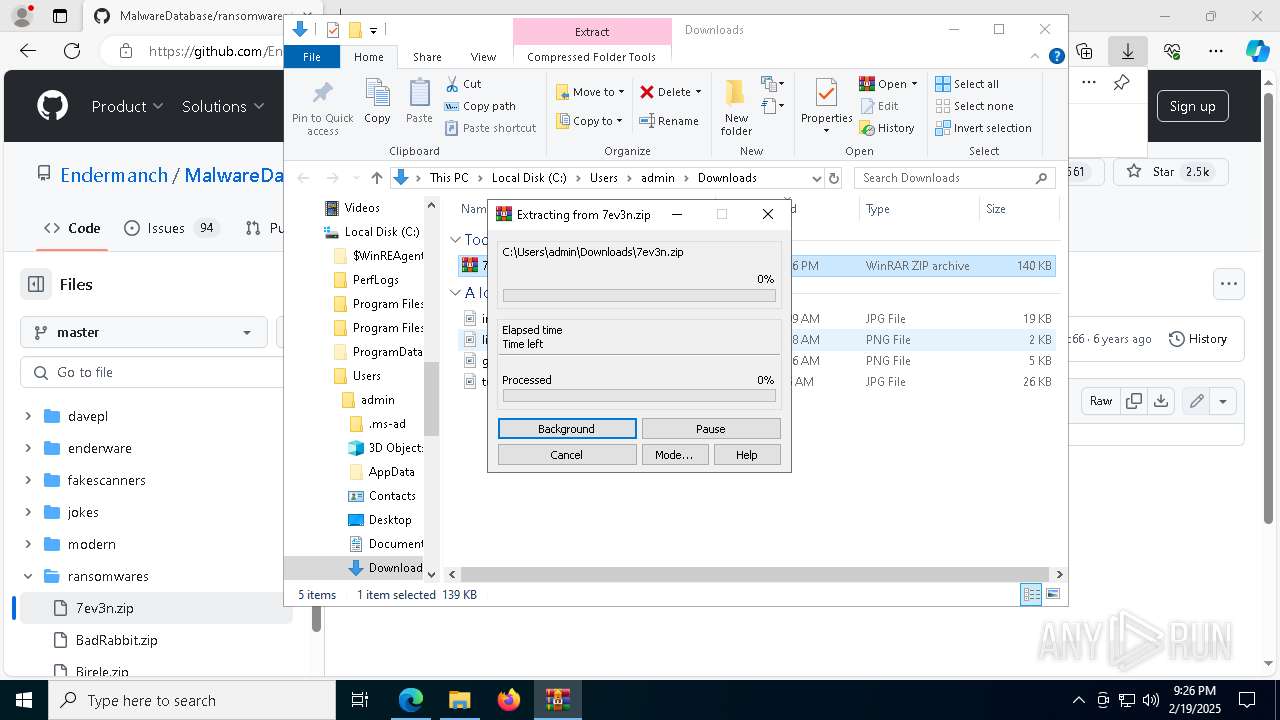
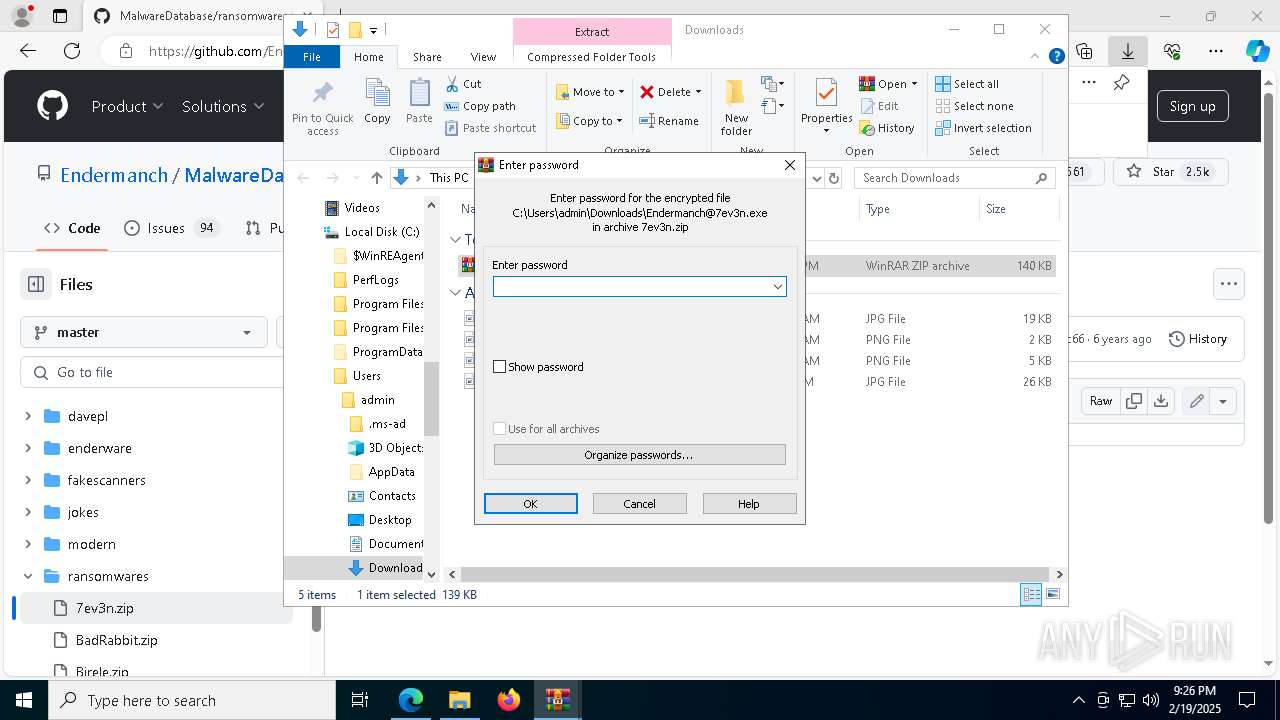
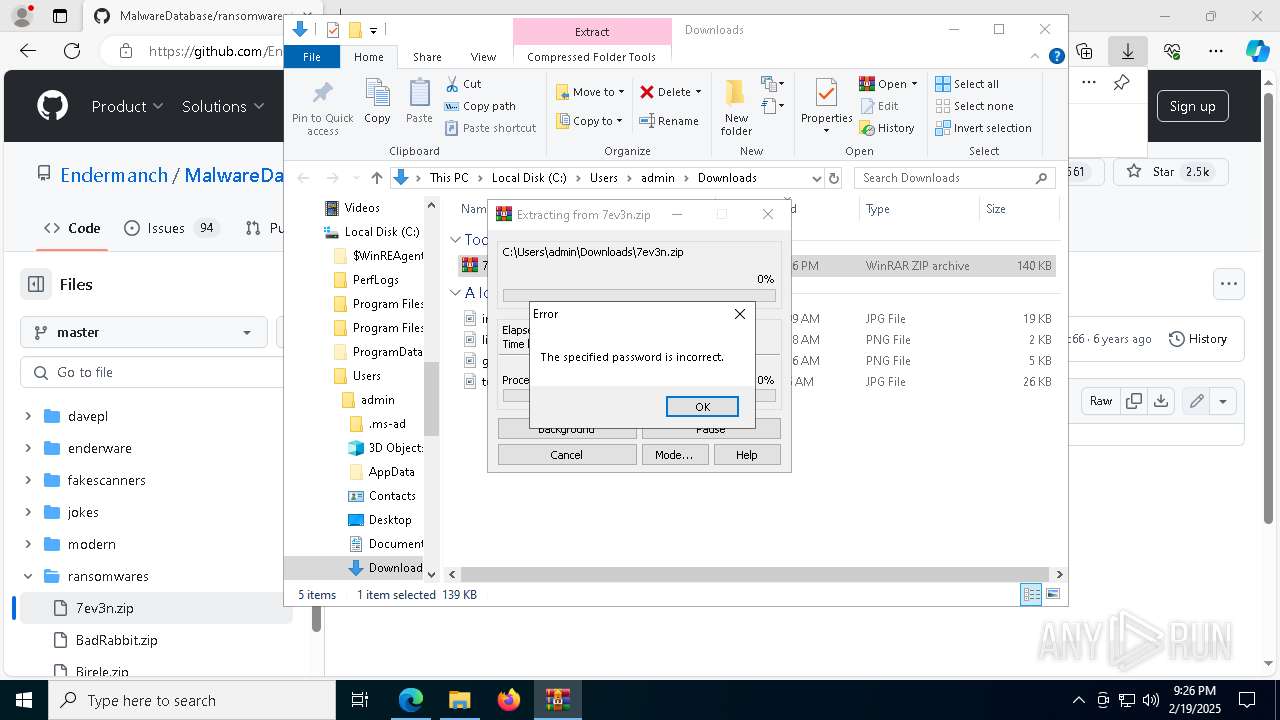
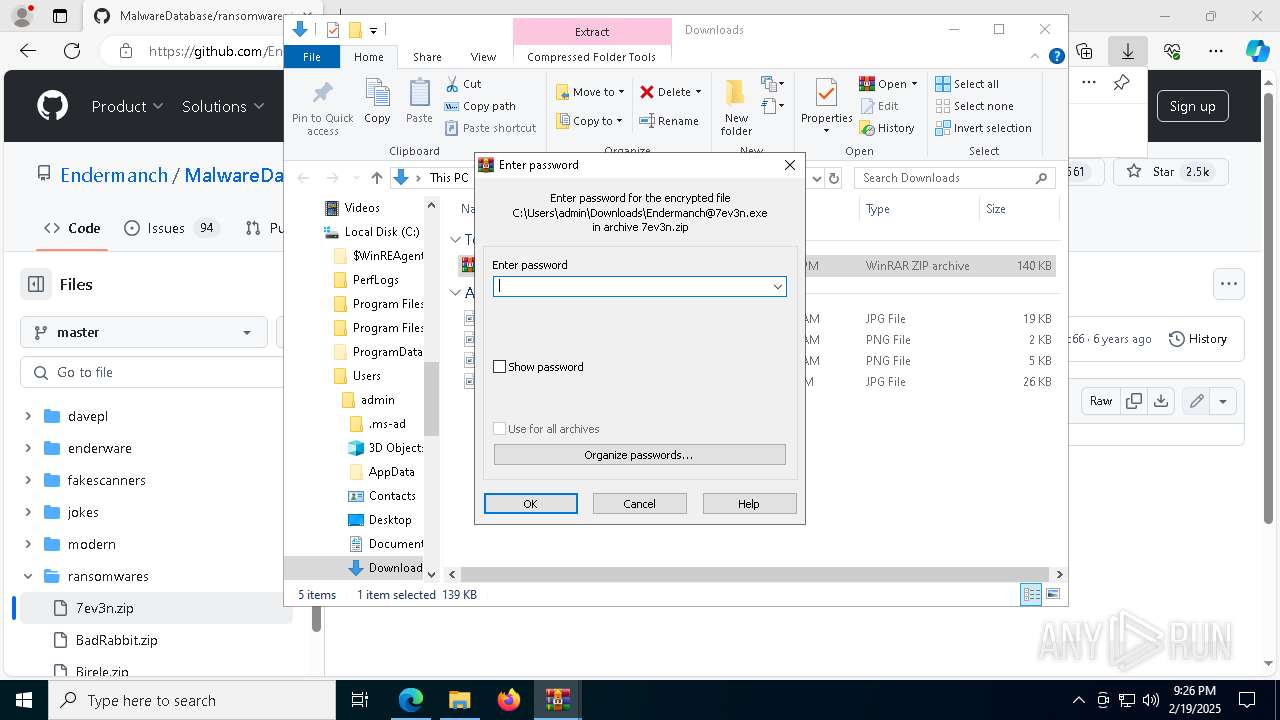
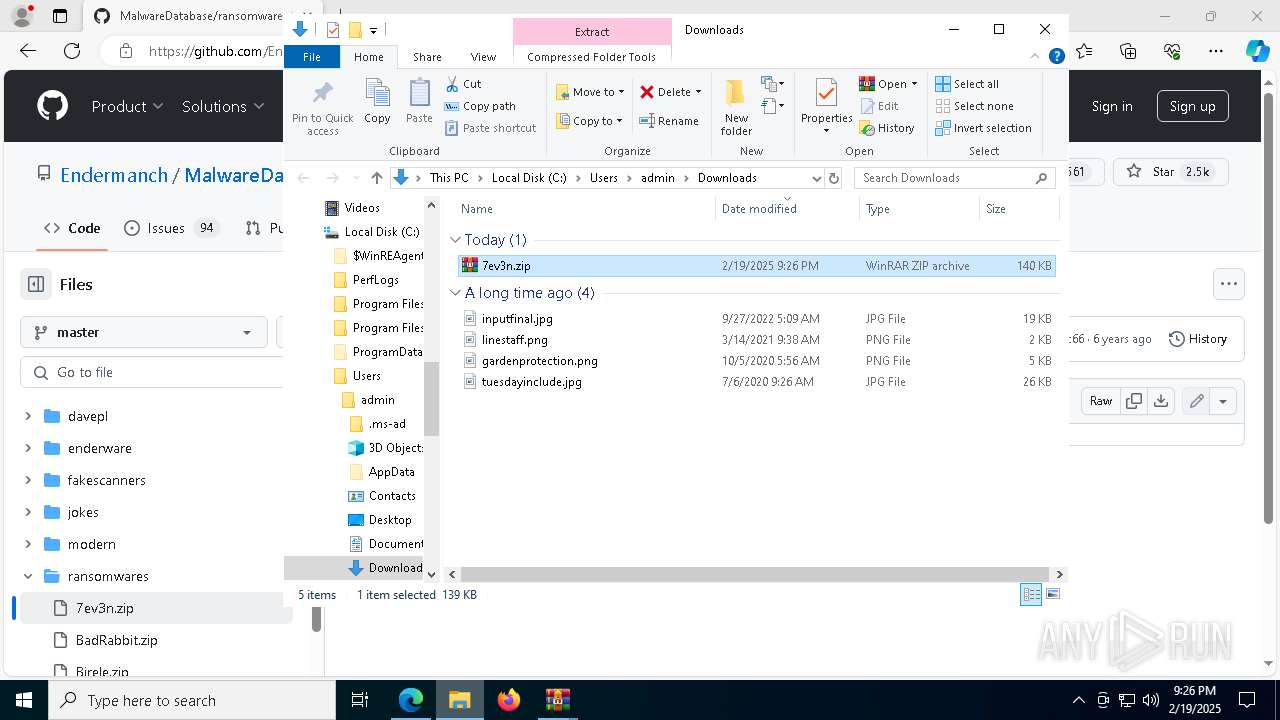
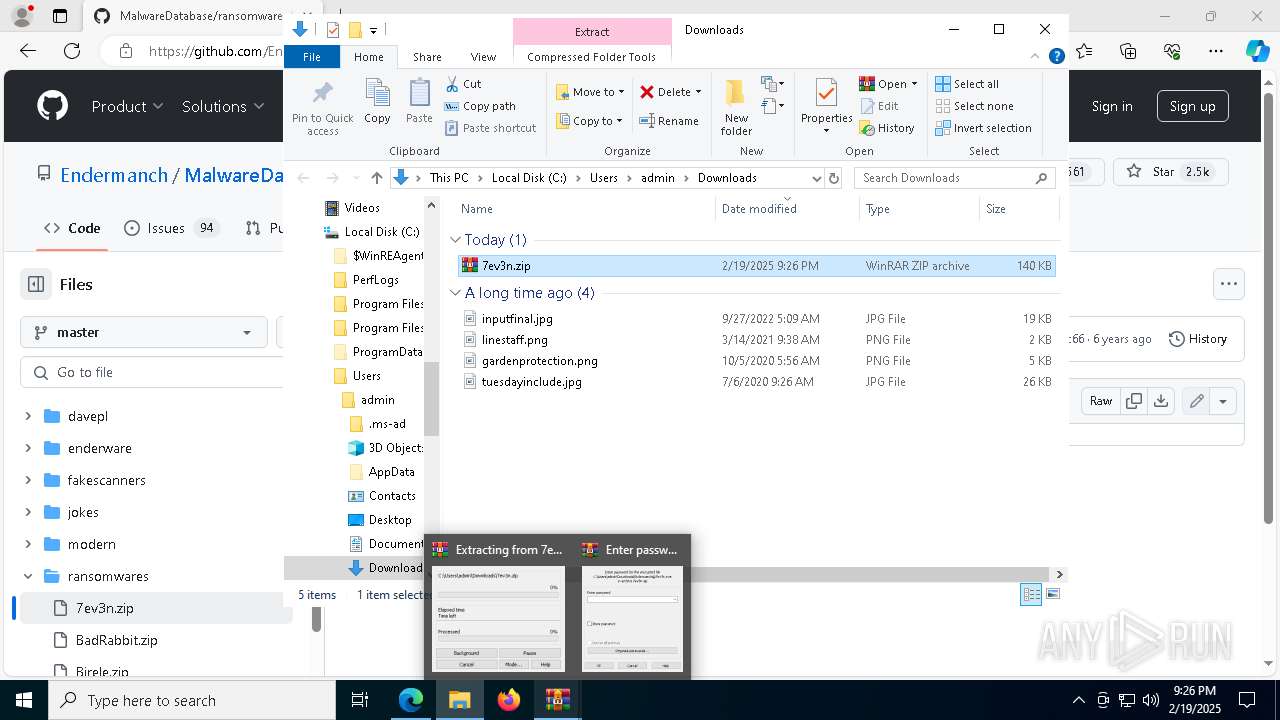
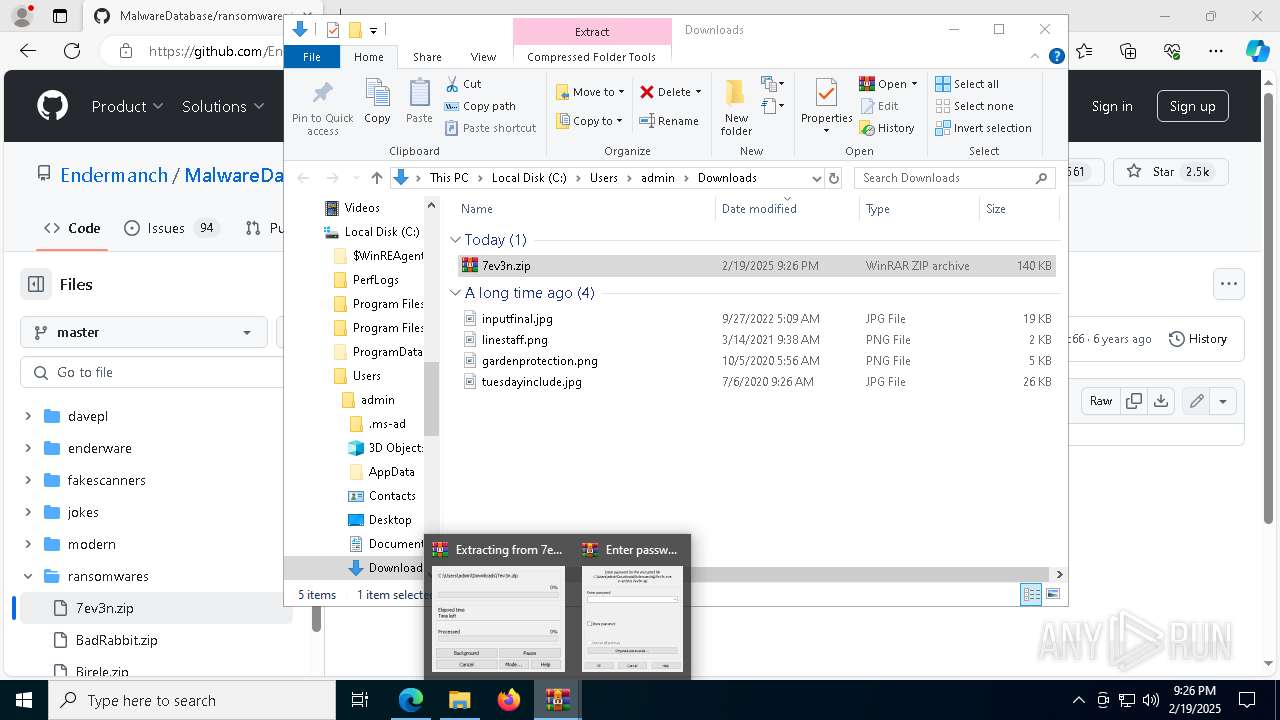
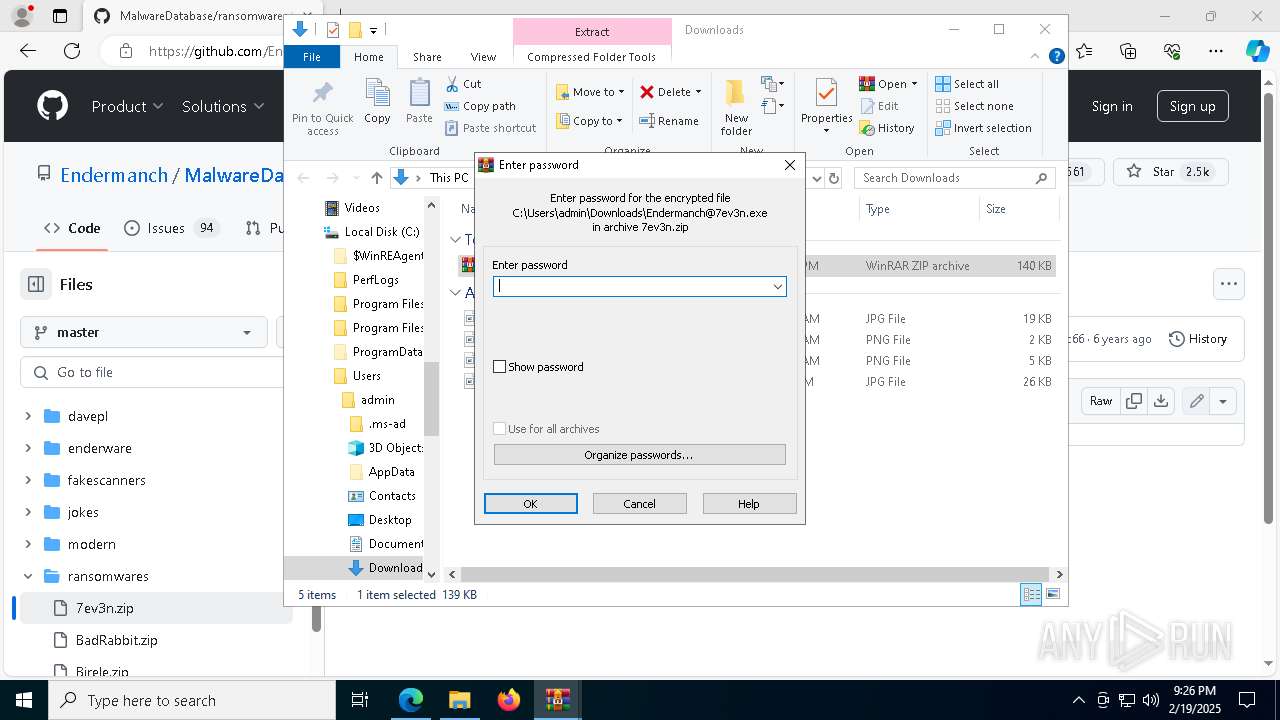
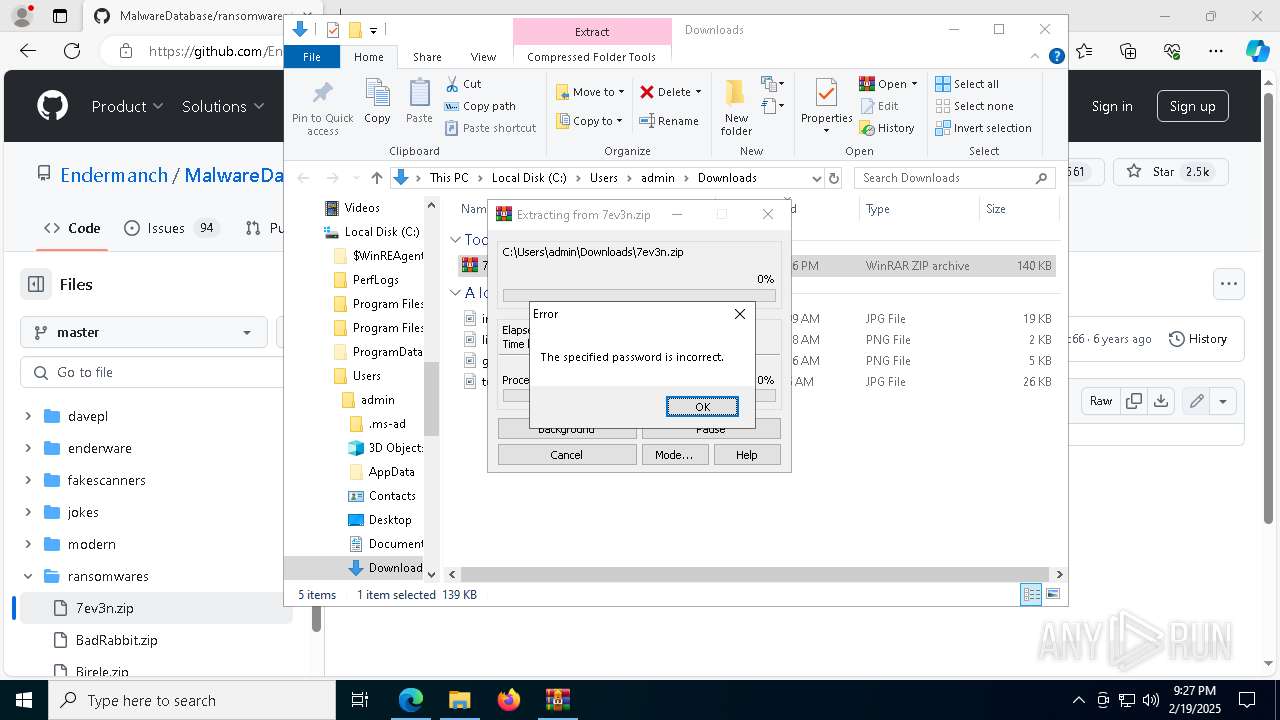
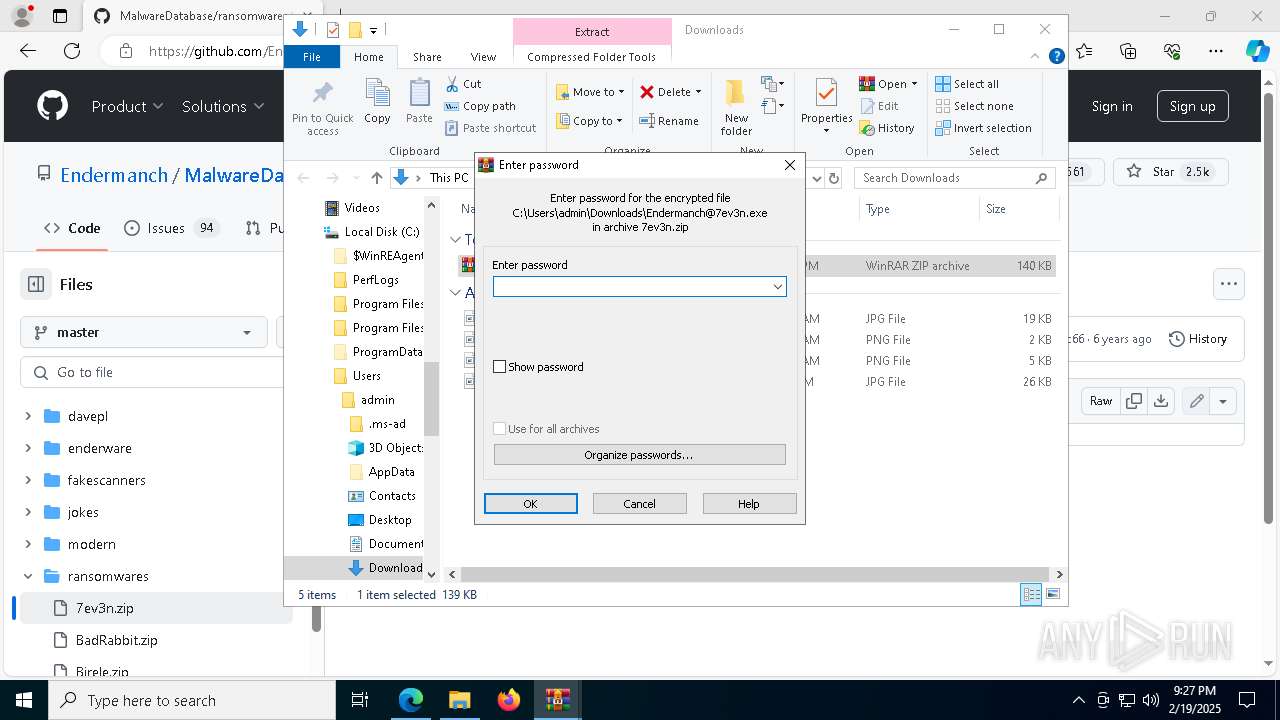
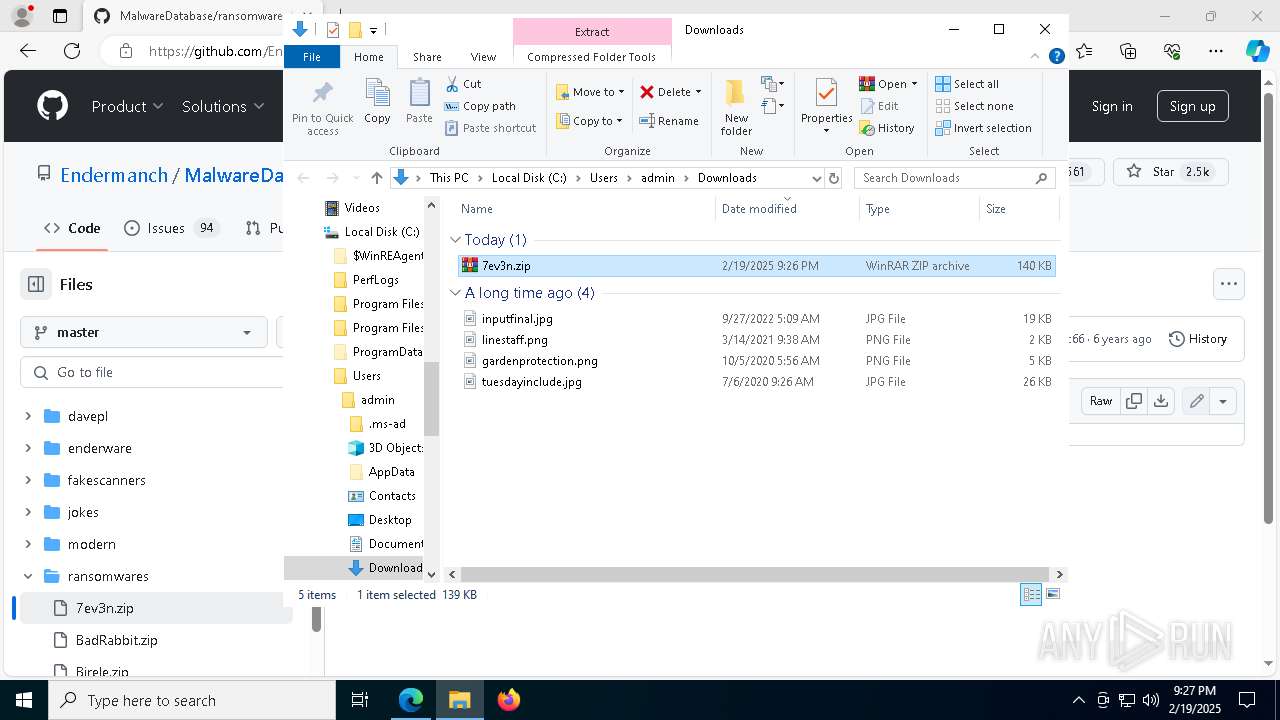
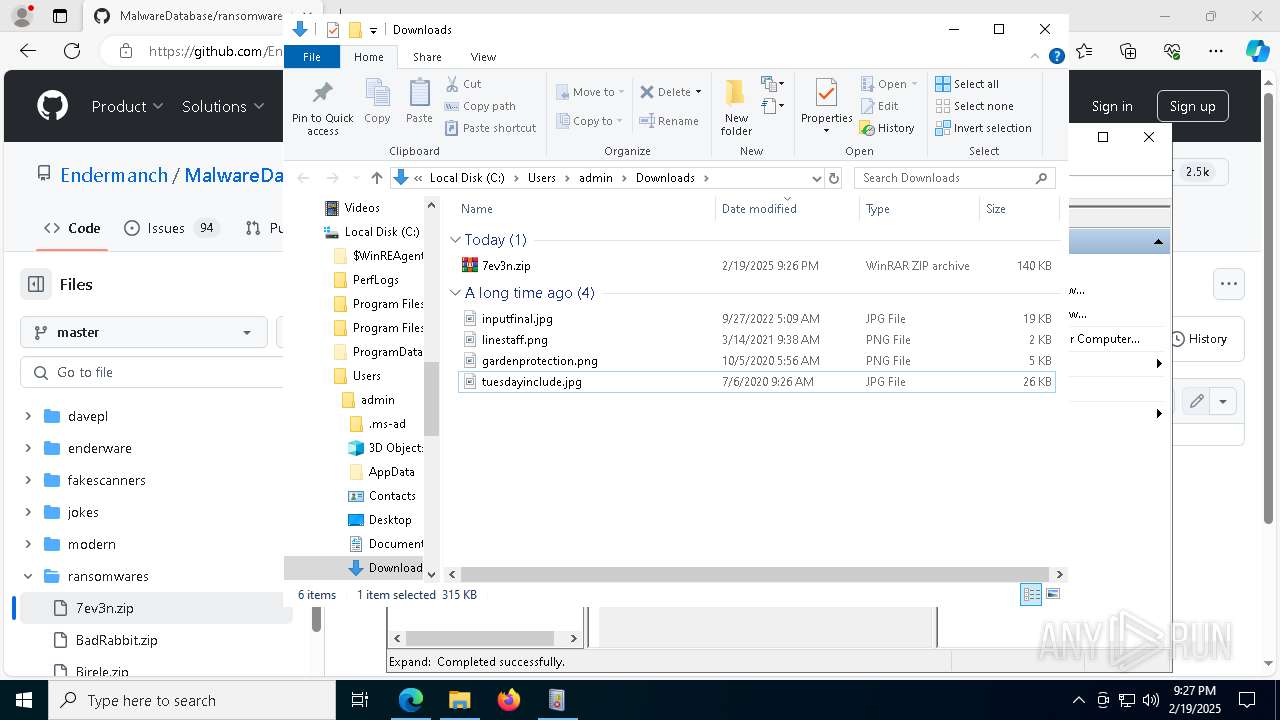
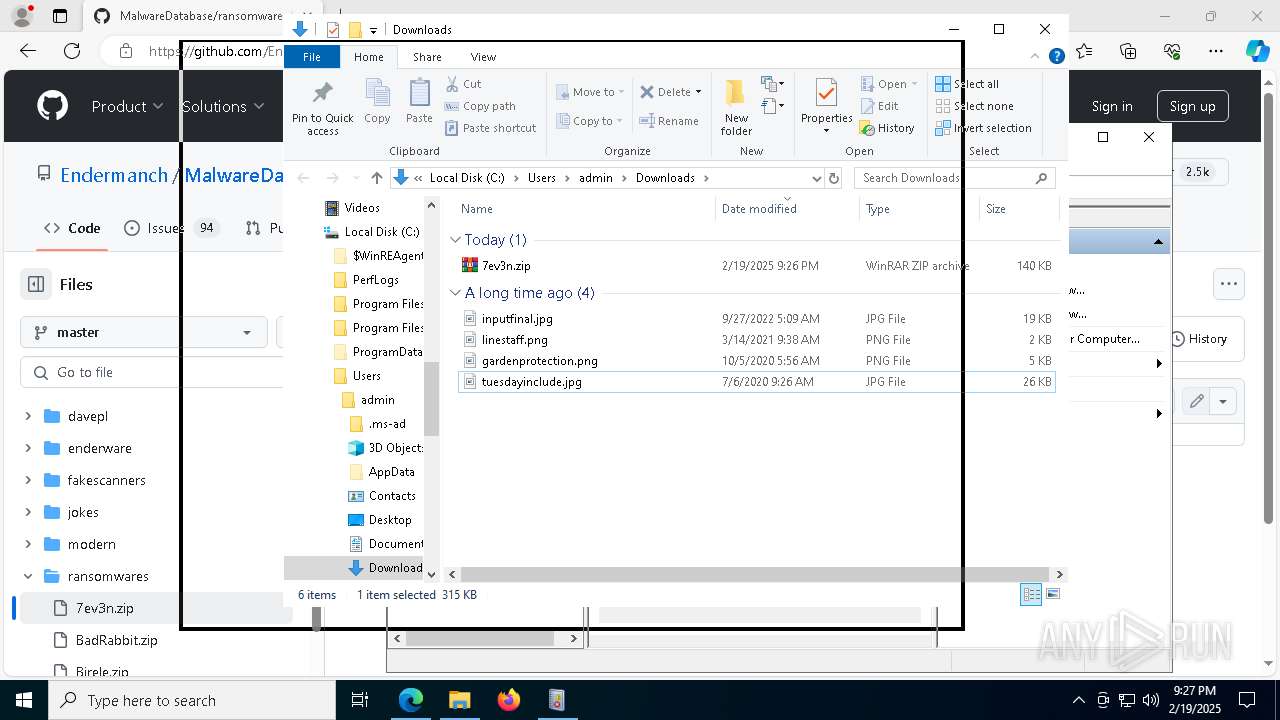
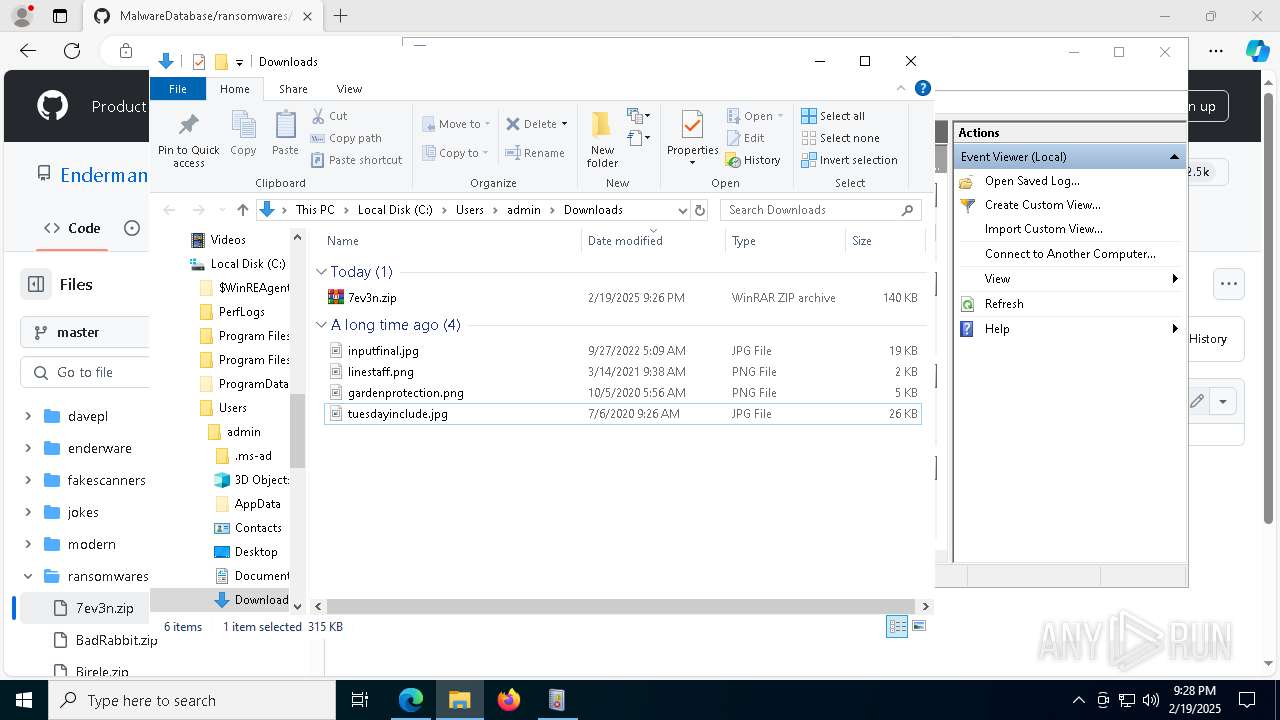
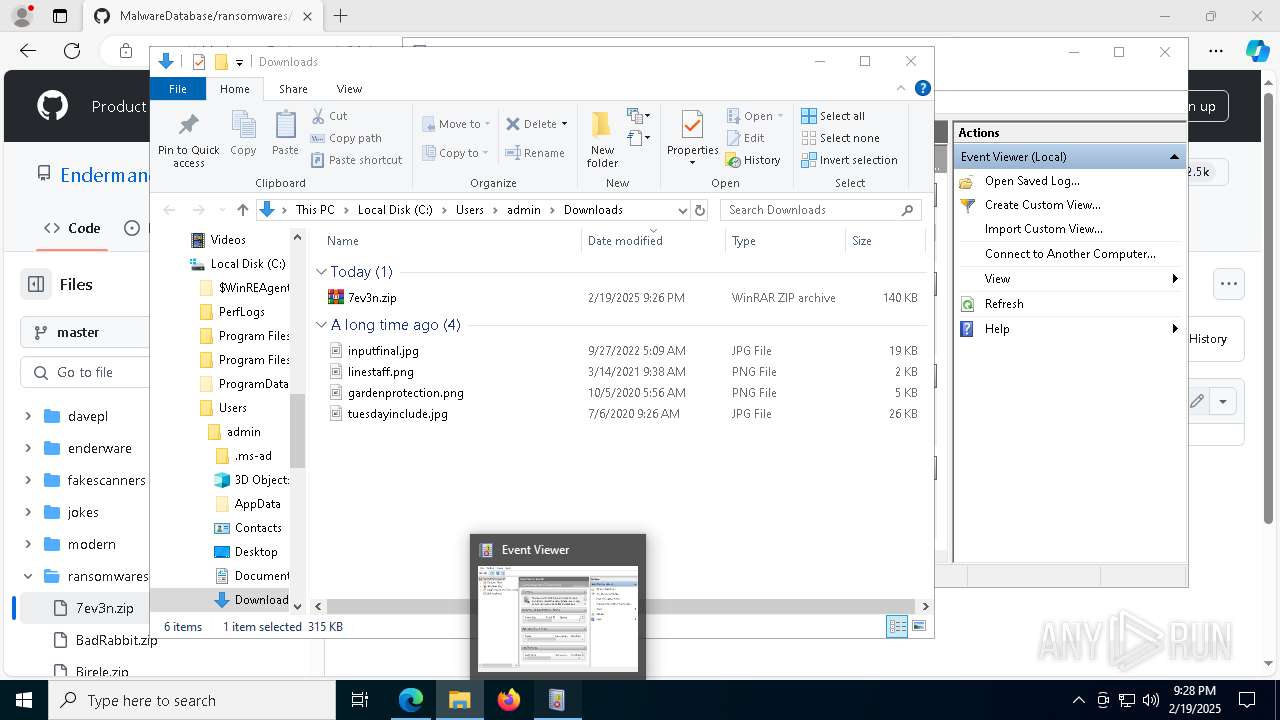
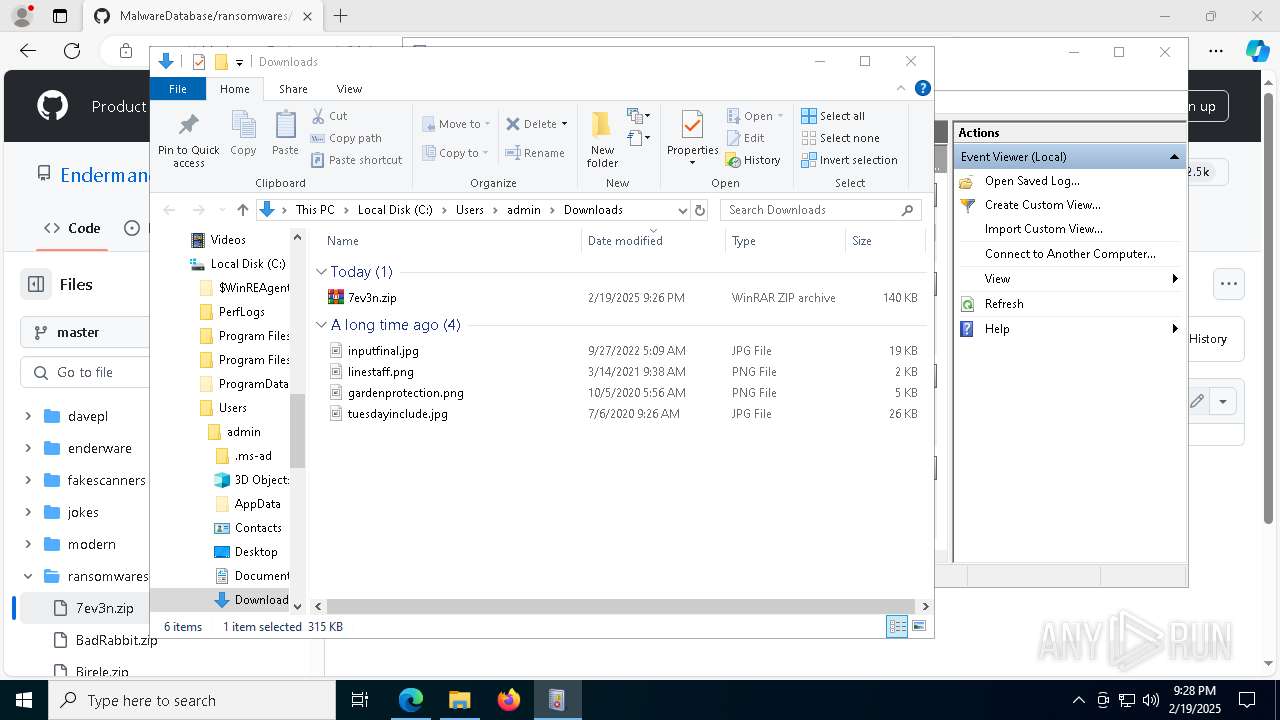
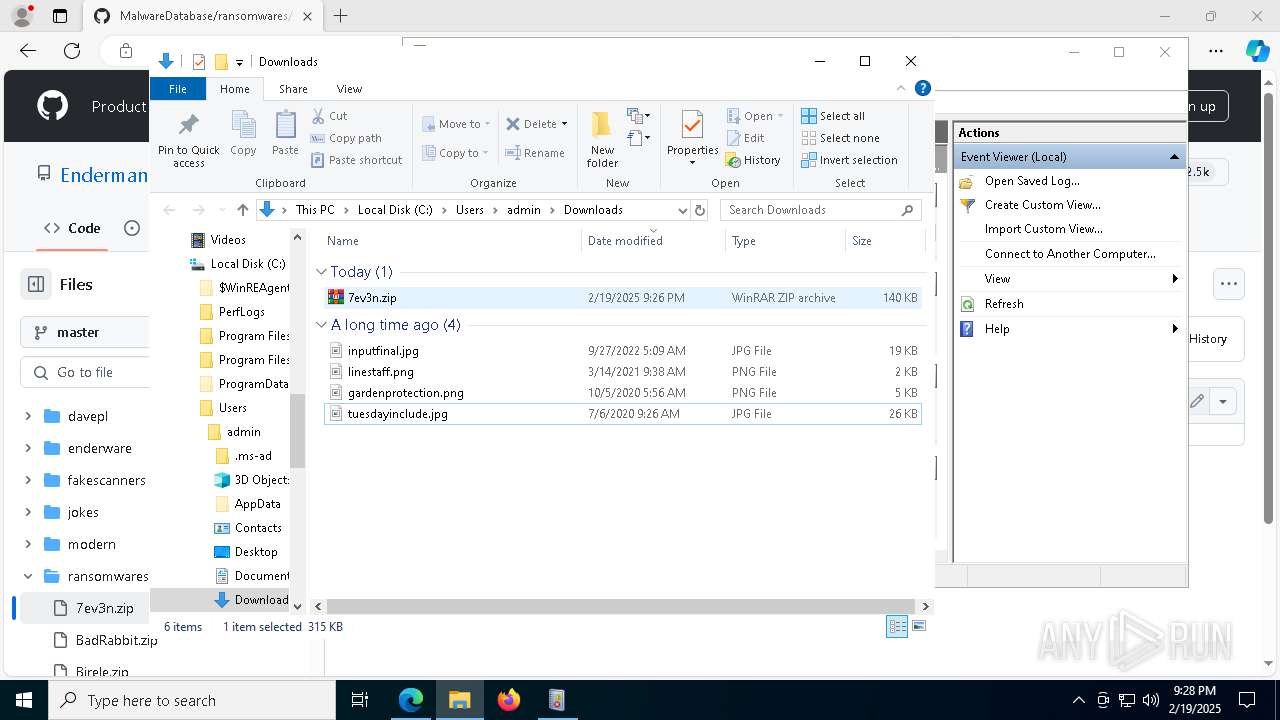
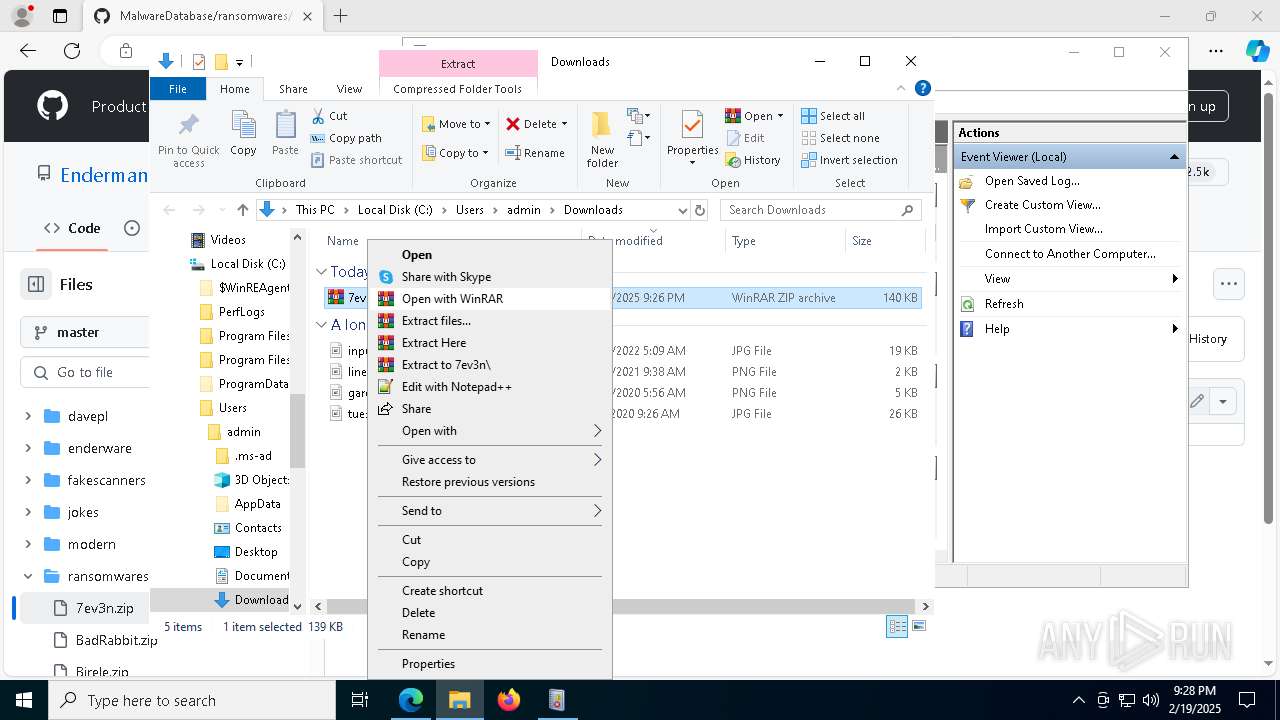
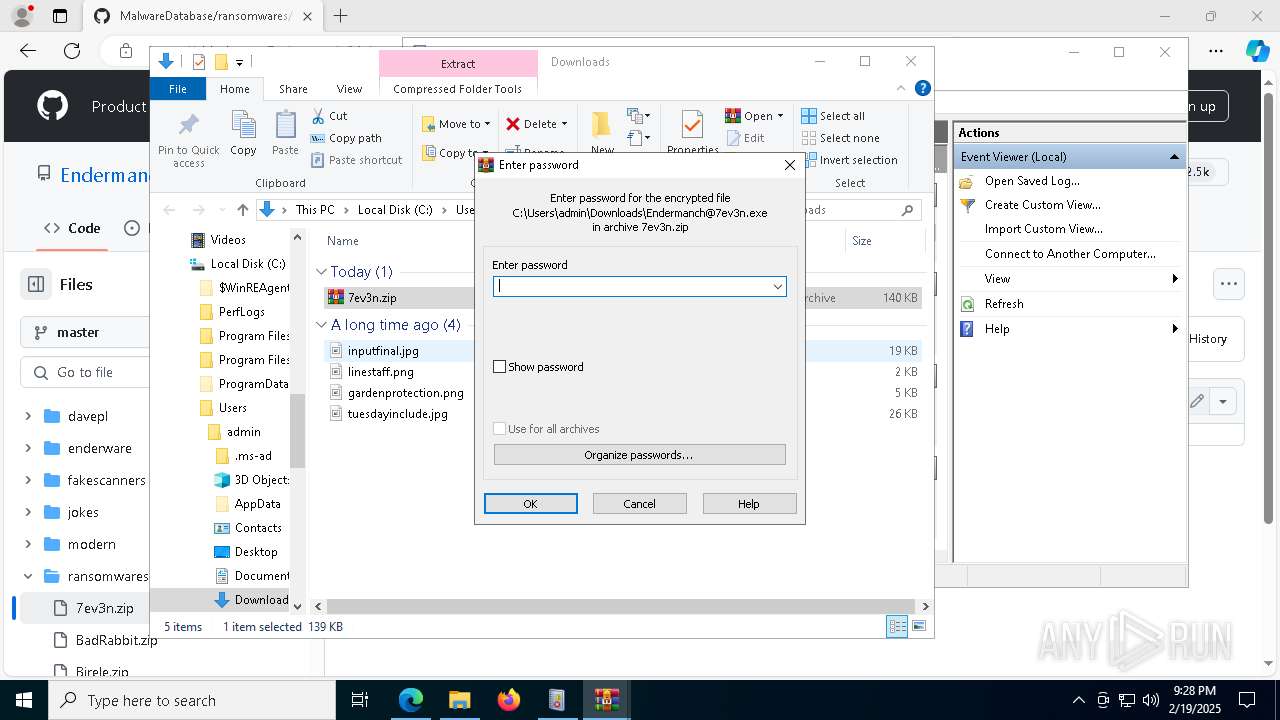
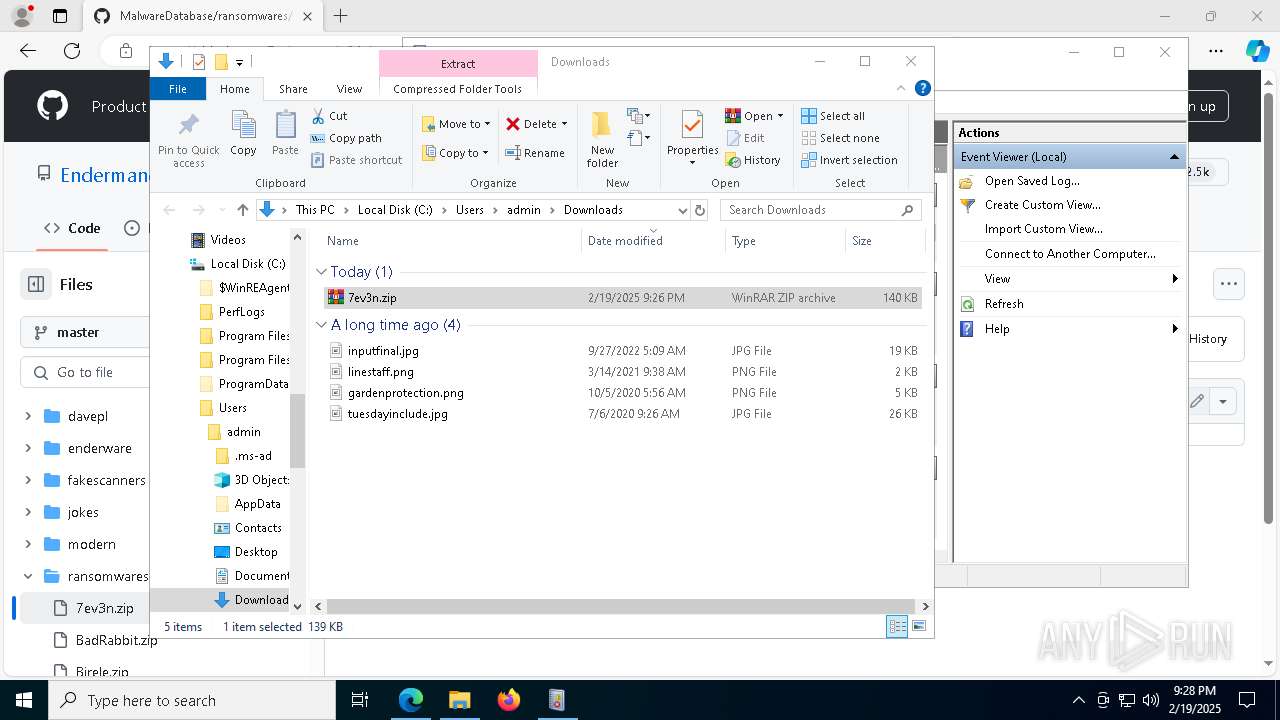
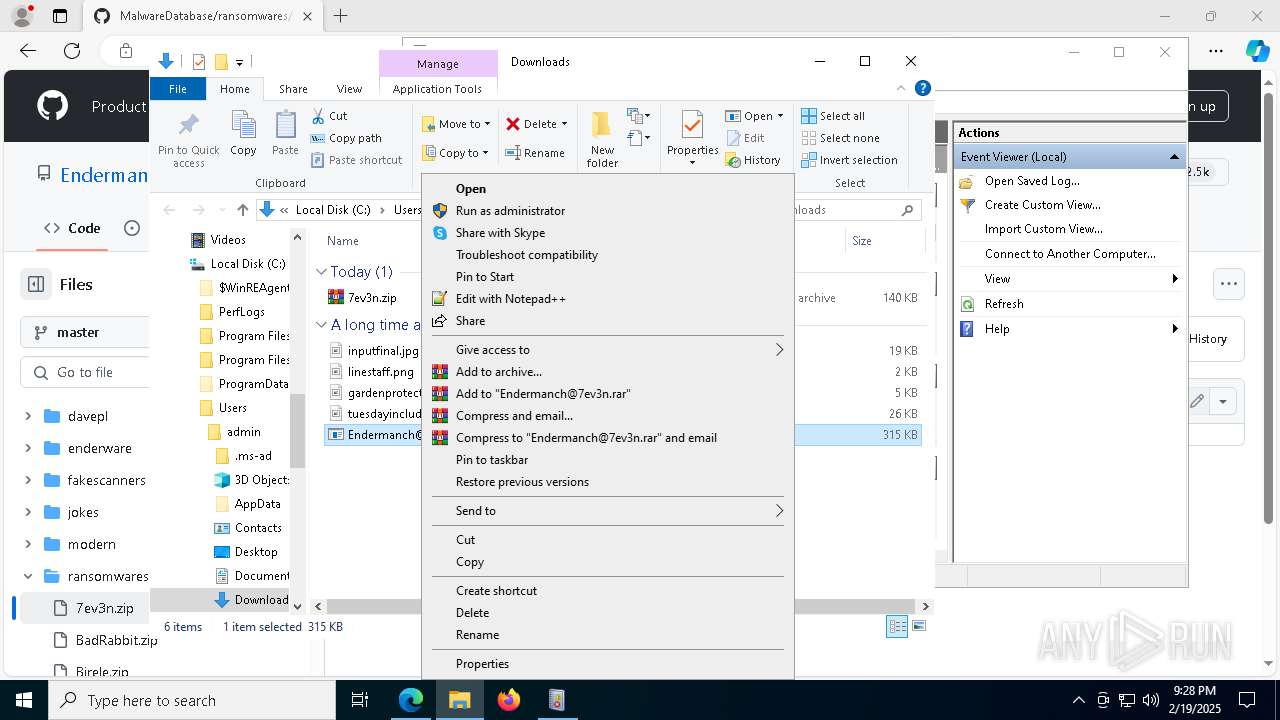
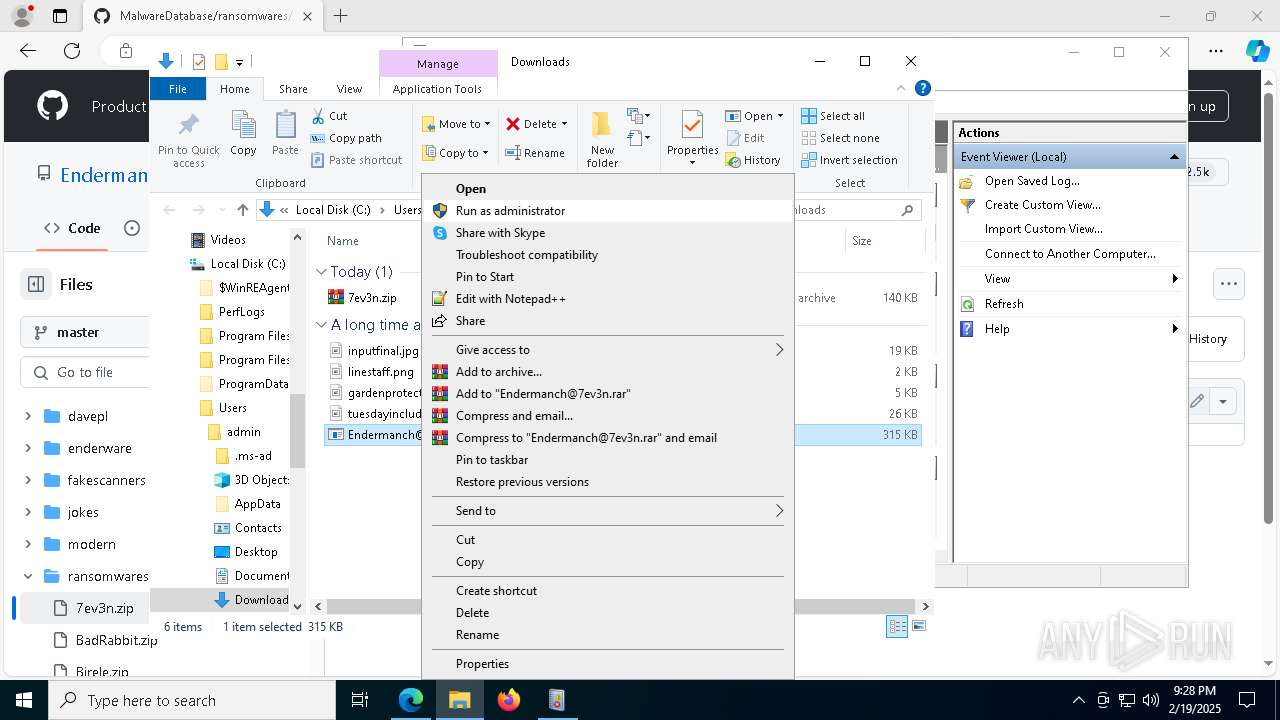
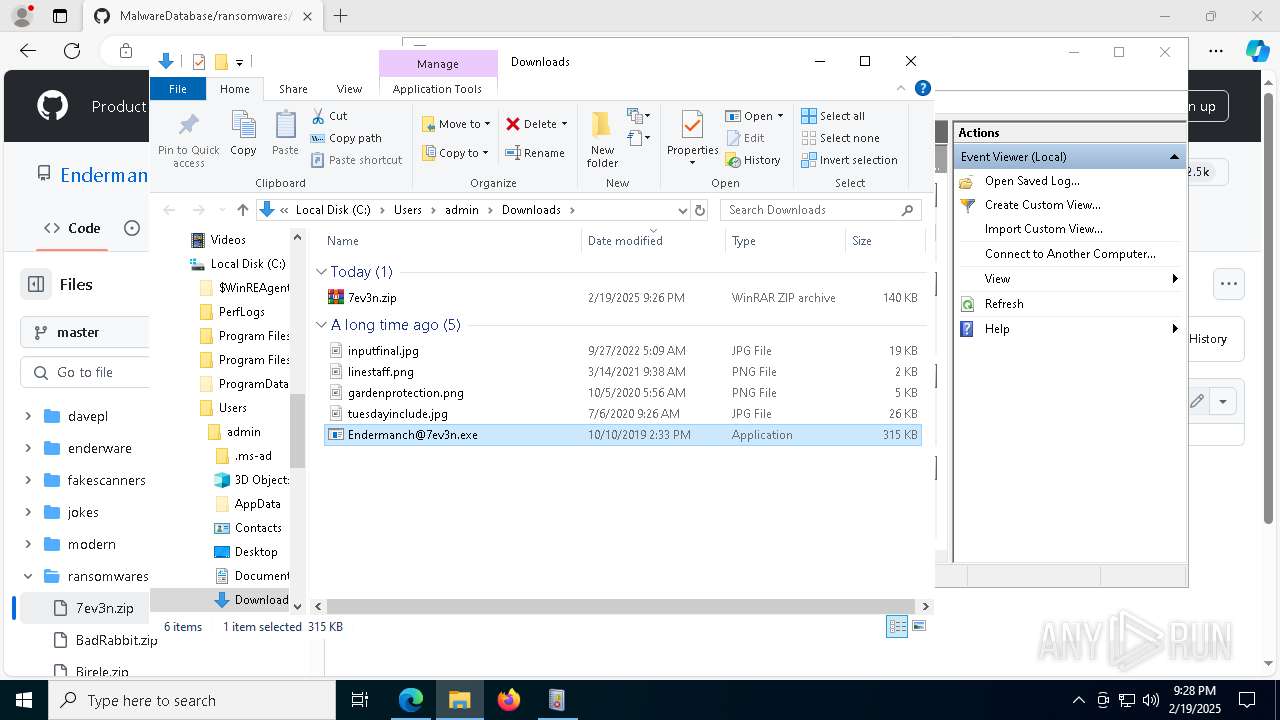
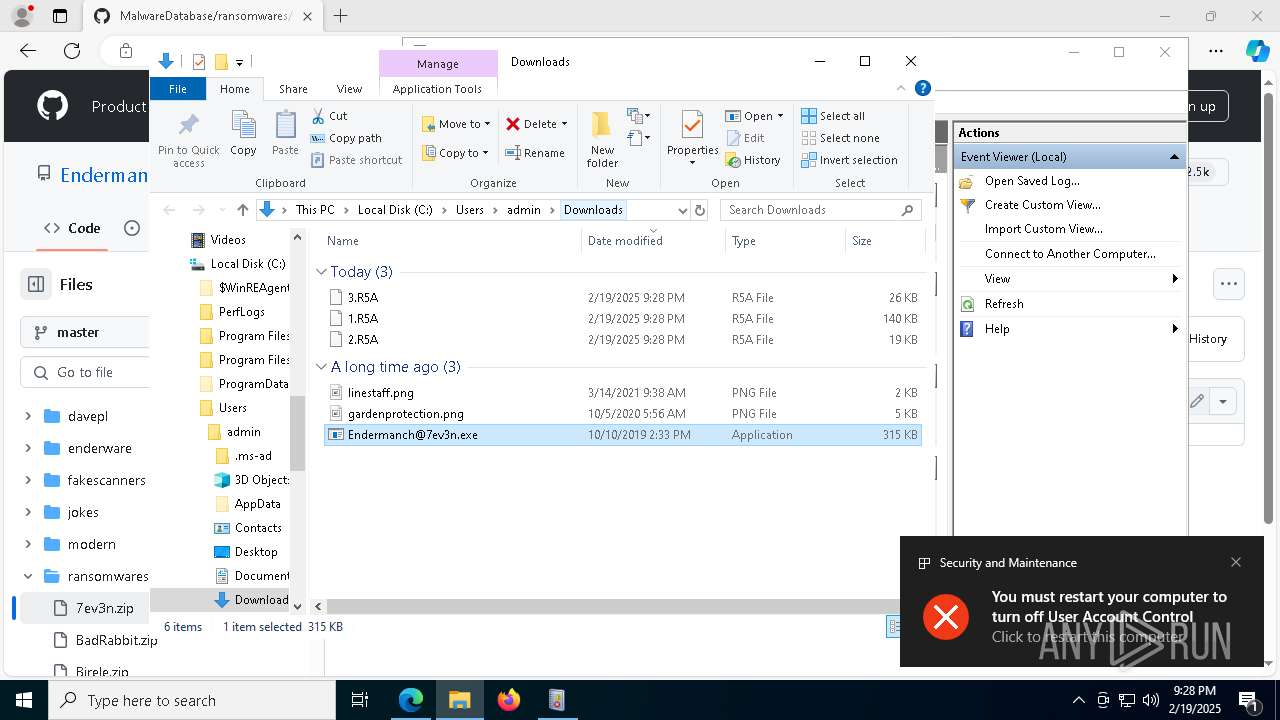
Manual execution by a user
- WinRAR.exe (PID: 7760)
- Endermanch@7ev3n.exe (PID: 5720)
- WinRAR.exe (PID: 1172)
- Endermanch@7ev3n.exe (PID: 6768)
Creates files or folders in the user directory
- Endermanch@7ev3n.exe (PID: 5720)
- system.exe (PID: 4144)
- mmc.exe (PID: 7880)
- explorer.exe (PID: 4488)
- Endermanch@7ev3n.exe (PID: 6768)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4488)
- dllhost.exe (PID: 732)
- mmc.exe (PID: 7880)
Reads the software policy settings
- Endermanch@7ev3n.exe (PID: 5720)
- mmc.exe (PID: 7880)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7760)
- msedge.exe (PID: 5980)
- WinRAR.exe (PID: 1172)
Reads Microsoft Office registry keys
- explorer.exe (PID: 4488)
Reads the machine GUID from the registry
- Endermanch@7ev3n.exe (PID: 5720)
- system.exe (PID: 4144)
Checks proxy server information
- Endermanch@7ev3n.exe (PID: 5720)
The sample compiled with english language support
- system.exe (PID: 4144)
- dllhost.exe (PID: 732)
- msedge.exe (PID: 5980)
- uac.exe (PID: 7500)
Create files in a temporary directory
- uac.exe (PID: 7500)
Checks transactions between databases Windows and Oracle
- explorer.exe (PID: 4488)
Creates files in the program directory
- mmc.exe (PID: 7880)
- PLUGScheduler.exe (PID: 880)
UPX packer has been detected
- uac.exe (PID: 7500)
Process checks computer location settings
- uac.exe (PID: 7500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
332
Monitored processes
102
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | C:\windows\system32\cmd.exe /c REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run" /v "System" /t REG_SZ /d "C:\Users\admin\AppData\Local\system.exe" /f /reg:64 | C:\Windows\SysWOW64\cmd.exe | — | Endermanch@7ev3n.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | C:\WINDOWS\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 880 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\7ev3n.zip" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6564 --field-trial-handle=2296,i,7439626143373308264,3643103636795944081,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1416 | C:\windows\system32\cmd.exe /c REG ADD "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /v "EnableLUA" /t REG_DWORD /d 0 /f /reg:64 | C:\Windows\SysWOW64\cmd.exe | — | Endermanch@7ev3n.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1480 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2084 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2144 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=6664 --field-trial-handle=2296,i,7439626143373308264,3643103636795944081,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
50 433
Read events
50 124
Write events
246
Delete events
63
Modification events
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:0000000000050310 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456A48A294F7A40804AB924005FF030B61F | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:0000000000050302 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456A48A294F7A40804AB924005FF030B61F | |||
| (PID) Process: | (6316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6316) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 75B714AF1B8D2F00 | |||
| (PID) Process: | (6316) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C5E534AF1B8D2F00 | |||
| (PID) Process: | (6316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328464 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D4959496-3A08-4C70-BF85-51AC90BAE1BB} | |||
| (PID) Process: | (6316) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328464 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {44E99BBA-8EC8-47F8-AFBB-3E97D62E9670} | |||
Executable files
16
Suspicious files
412
Text files
66
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF136610.TMP | — | |
MD5:— | SHA256:— | |||
| 6316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF136620.TMP | — | |
MD5:— | SHA256:— | |||
| 6316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF136620.TMP | — | |
MD5:— | SHA256:— | |||
| 6316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF136620.TMP | — | |
MD5:— | SHA256:— | |||
| 6316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF136620.TMP | — | |
MD5:— | SHA256:— | |||
| 6316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6316 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
102
DNS requests
99
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4516 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1740404151&P2=404&P3=2&P4=BZafwmrr8vJEY5a4UoziWQ1u1AfLec26wUevX%2bawREWLfU3lw%2fzSGZwDf5B0VIn662H88bY%2fCn15SXlcjOQ5lQ%3d%3d | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4516 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1740400550&P2=404&P3=2&P4=WutPBjreB2iBkatjedECpStGiiqXons7HJV8uoQVuiND6KFy1hmWrkwXiES%2bL7QMYUw4gf8g8ovn6vwnGmOvvQ%3d%3d | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2380 | svchost.exe | GET | 200 | 23.48.23.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4516 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1740400550&P2=404&P3=2&P4=WutPBjreB2iBkatjedECpStGiiqXons7HJV8uoQVuiND6KFy1hmWrkwXiES%2bL7QMYUw4gf8g8ovn6vwnGmOvvQ%3d%3d | unknown | — | — | whitelisted |
4516 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1740404151&P2=404&P3=2&P4=BZafwmrr8vJEY5a4UoziWQ1u1AfLec26wUevX%2bawREWLfU3lw%2fzSGZwDf5B0VIn662H88bY%2fCn15SXlcjOQ5lQ%3d%3d | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5488 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.139:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2380 | svchost.exe | 23.48.23.139:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2380 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6688 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6316 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6688 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6688 | msedge.exe | 13.107.253.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
github.com |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
Process | Message |
|---|---|
uac.exe | [UCM] Dll dropped successfully |
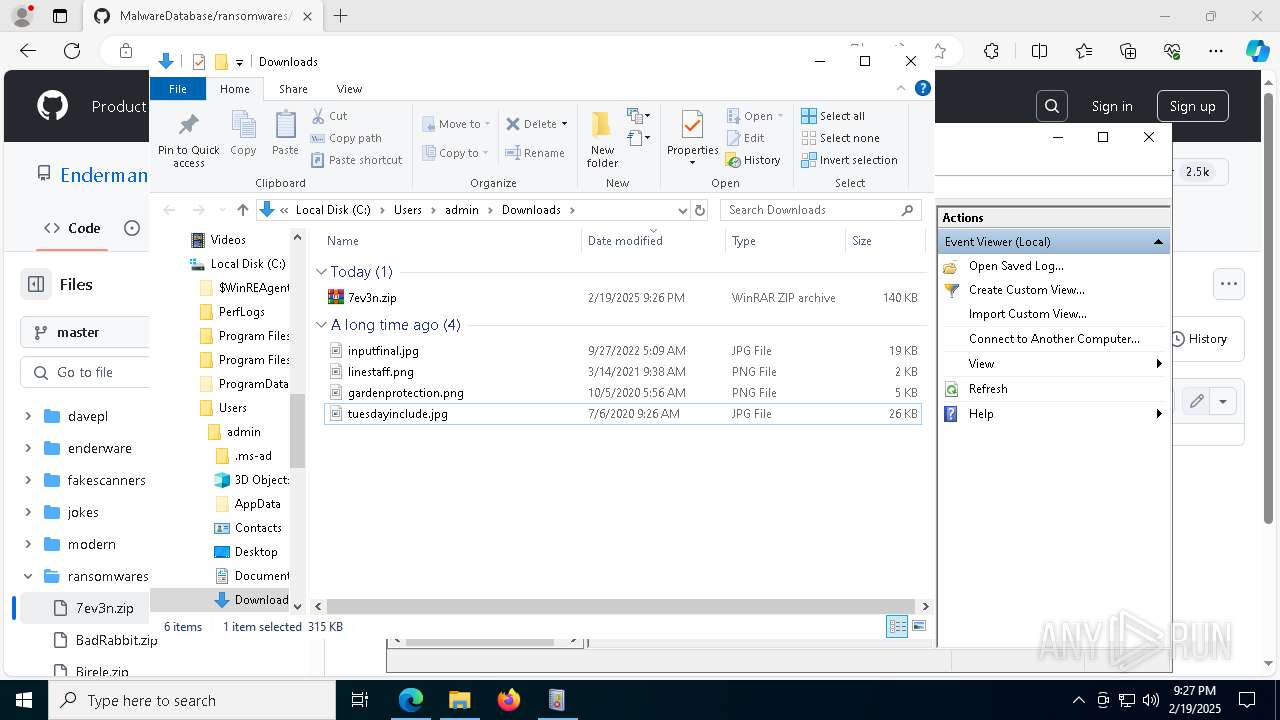
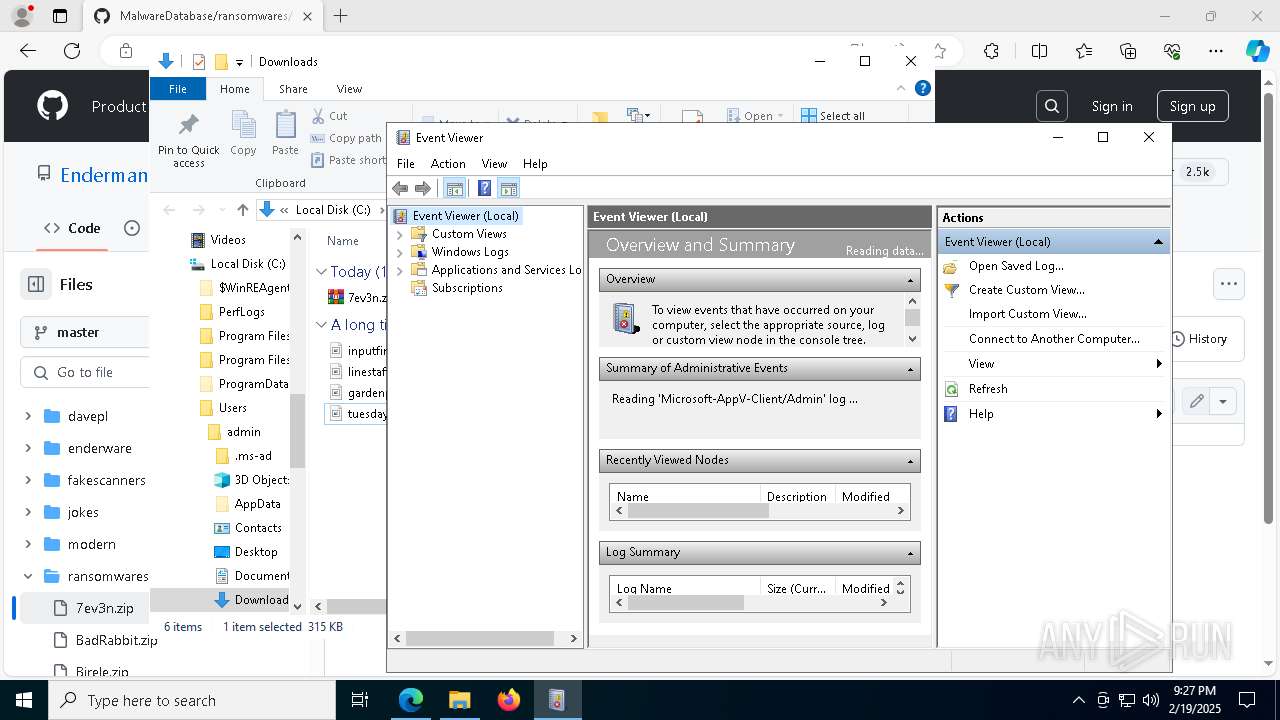
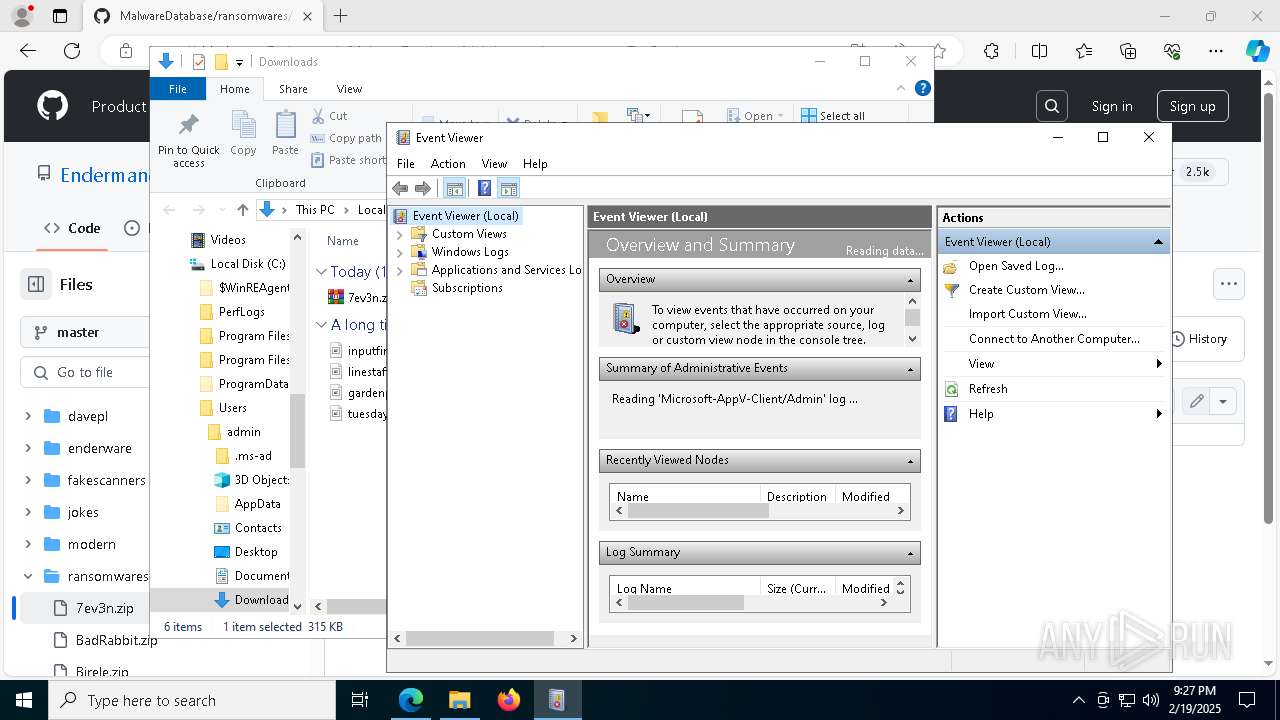
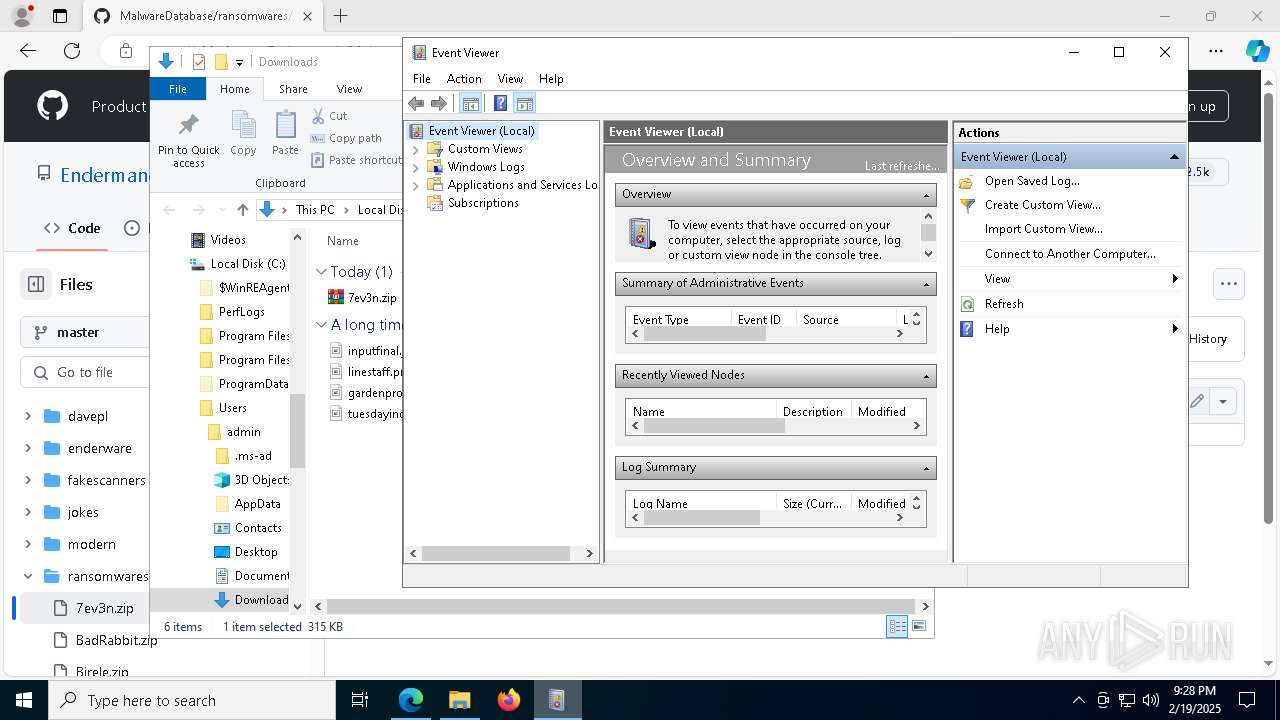
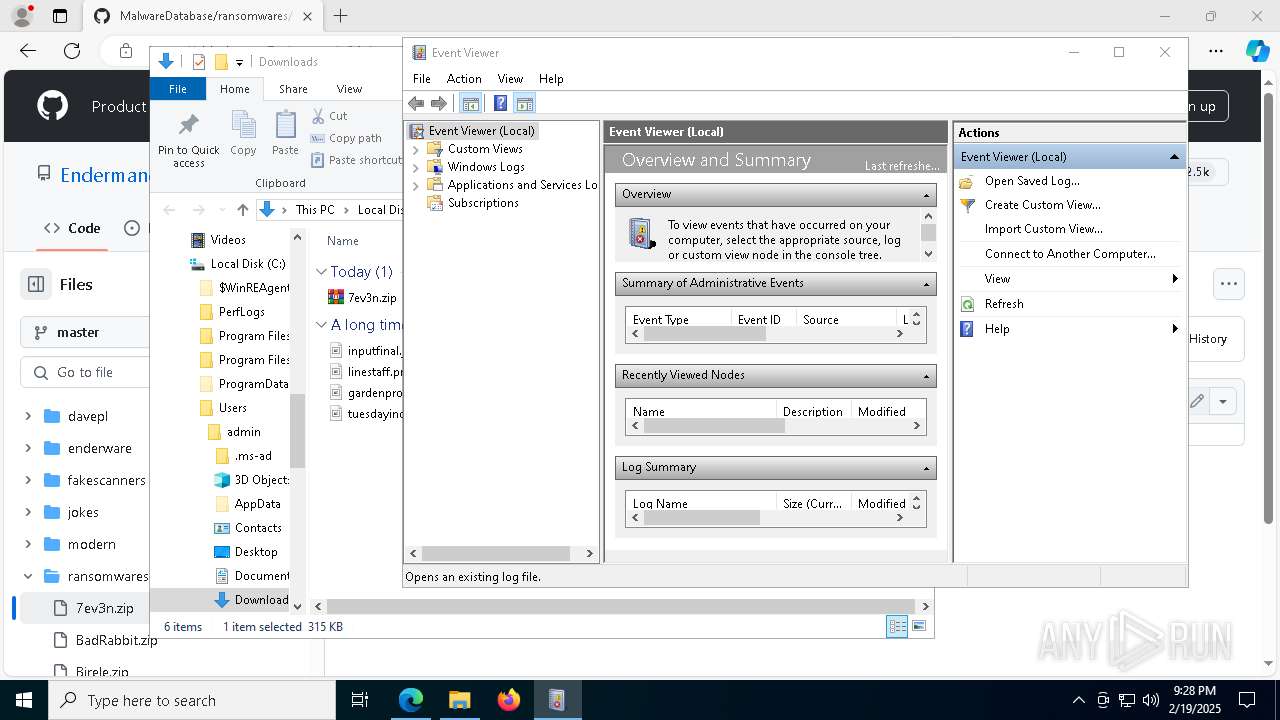
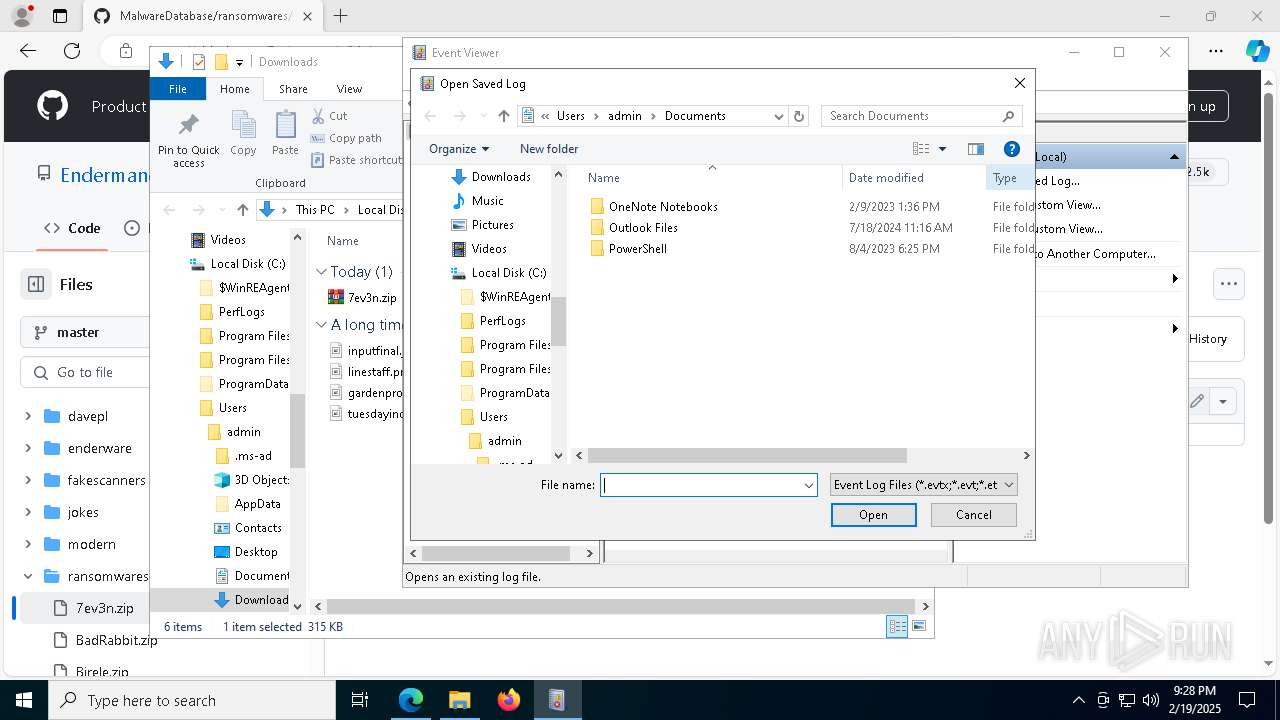
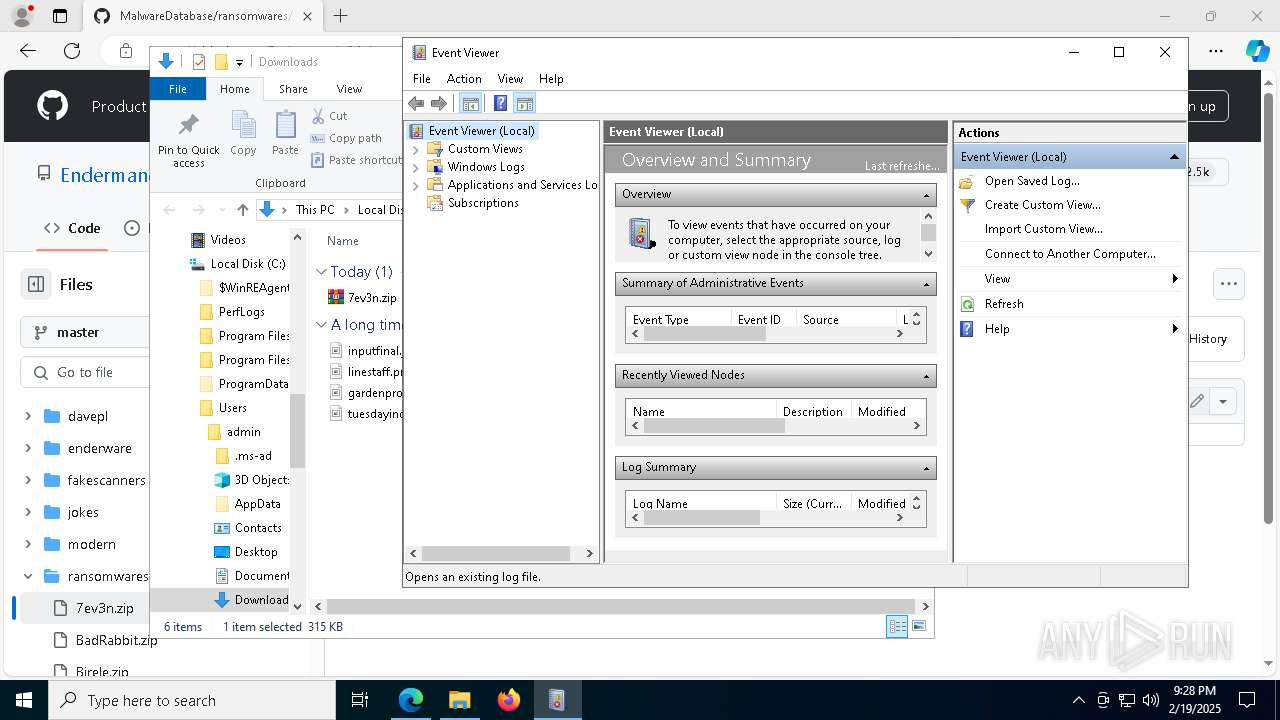
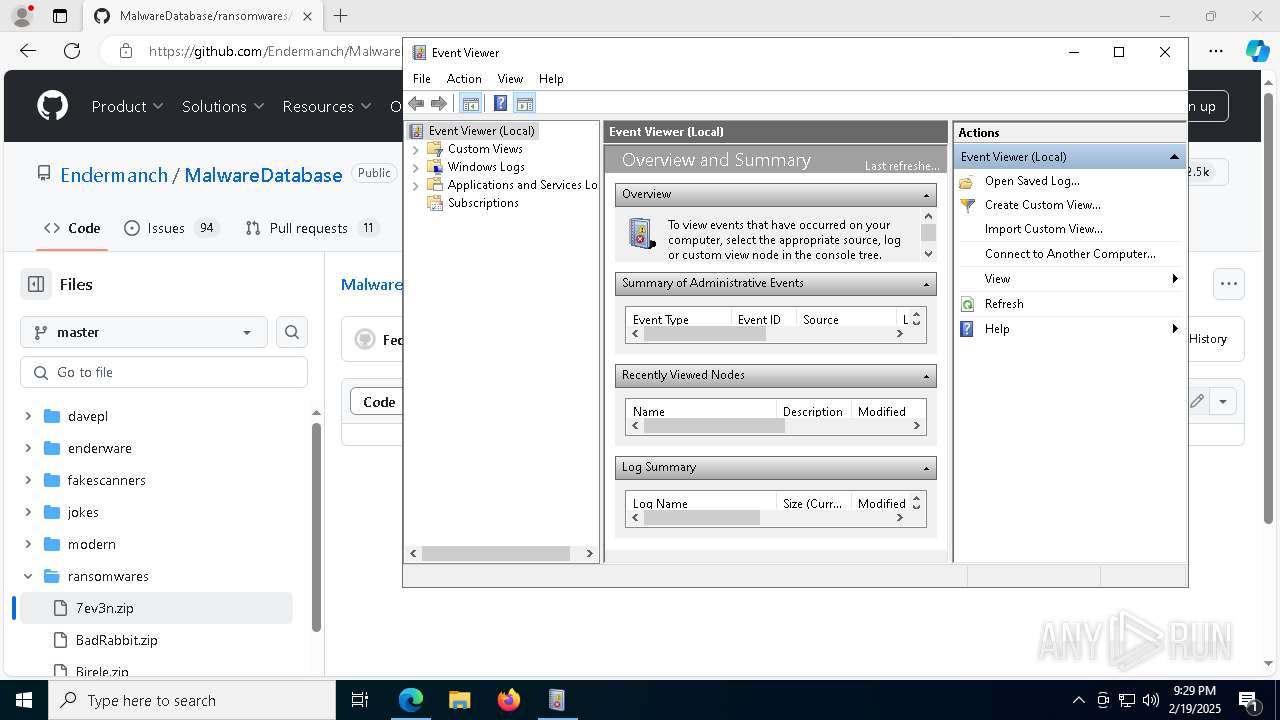
mmc.exe | ViewerViewsFolderPath = 'C:\ProgramData\Microsoft\Event Viewer\Views': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerAdminViewsPath = 'C:\ProgramData\Microsoft\Event Viewer\Views\ApplicationViewsRootNode': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerExternalLogsPath = 'C:\ProgramData\Microsoft\Event Viewer\ExternalLogs': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerConfigPath = 'C:\ProgramData\Microsoft\Event Viewer': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | Failed to get ChannelConfigOwningPublisher -122-The data area passed to a system call is too small
|
mmc.exe | Getting next publisher from enum failed-259-No more data is available
|
mmc.exe | Failed to get ChannelConfigOwningPublisher -122-The data area passed to a system call is too small
|
mmc.exe | ExpandNode:After EventsNode:InsertChildren CountOfChildren = 5
|
mmc.exe | PublisherMetadataKeywordName failed for not providing enough memory. Trying with the correct memory -122-The data area passed to a system call is too small
|