analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
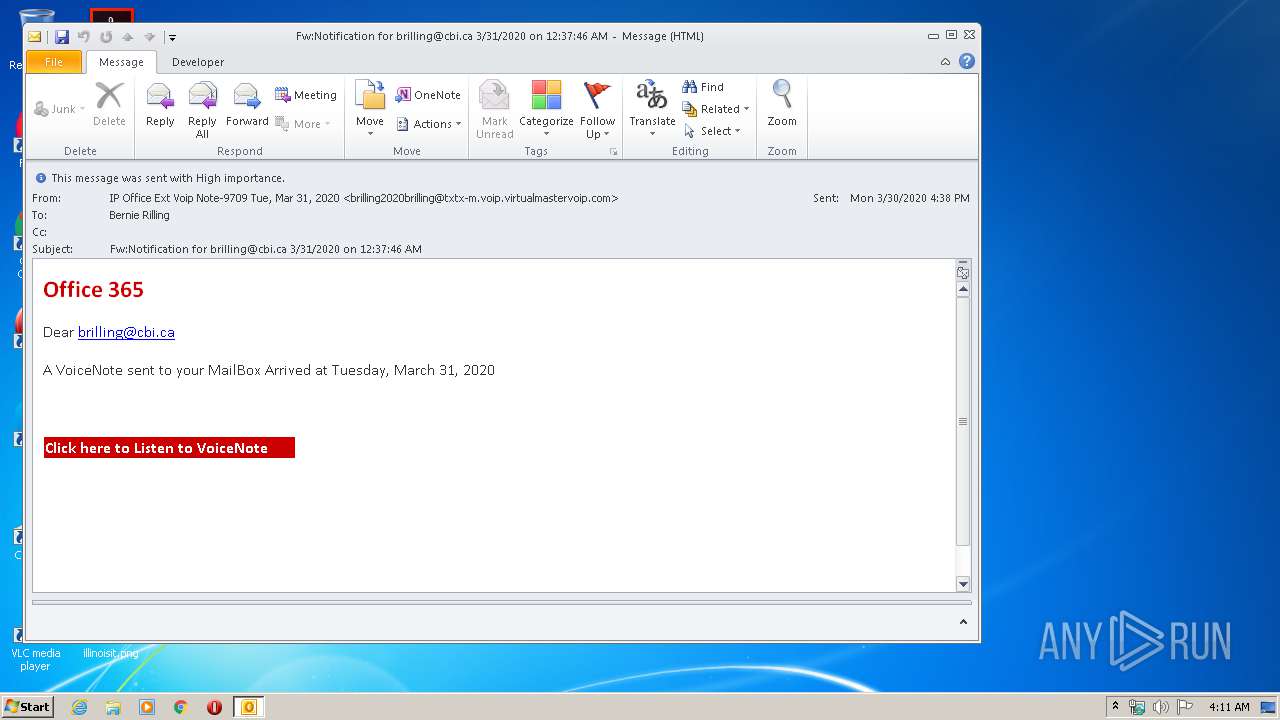
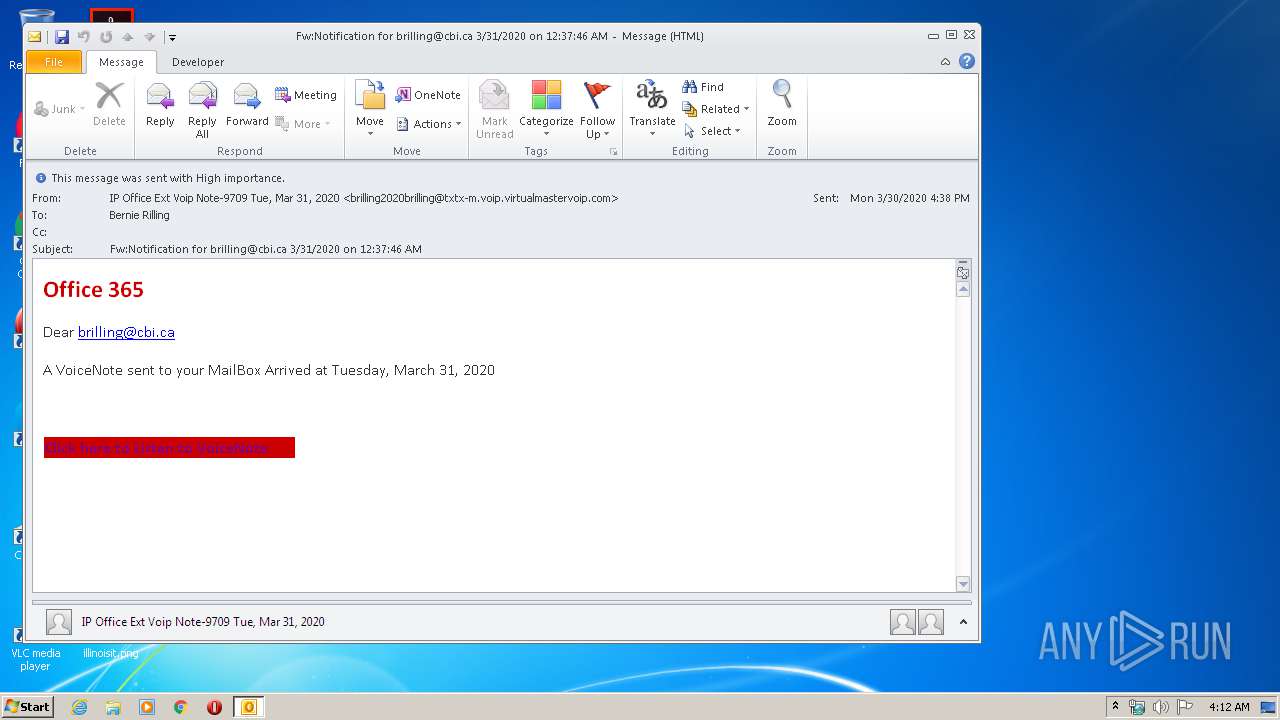
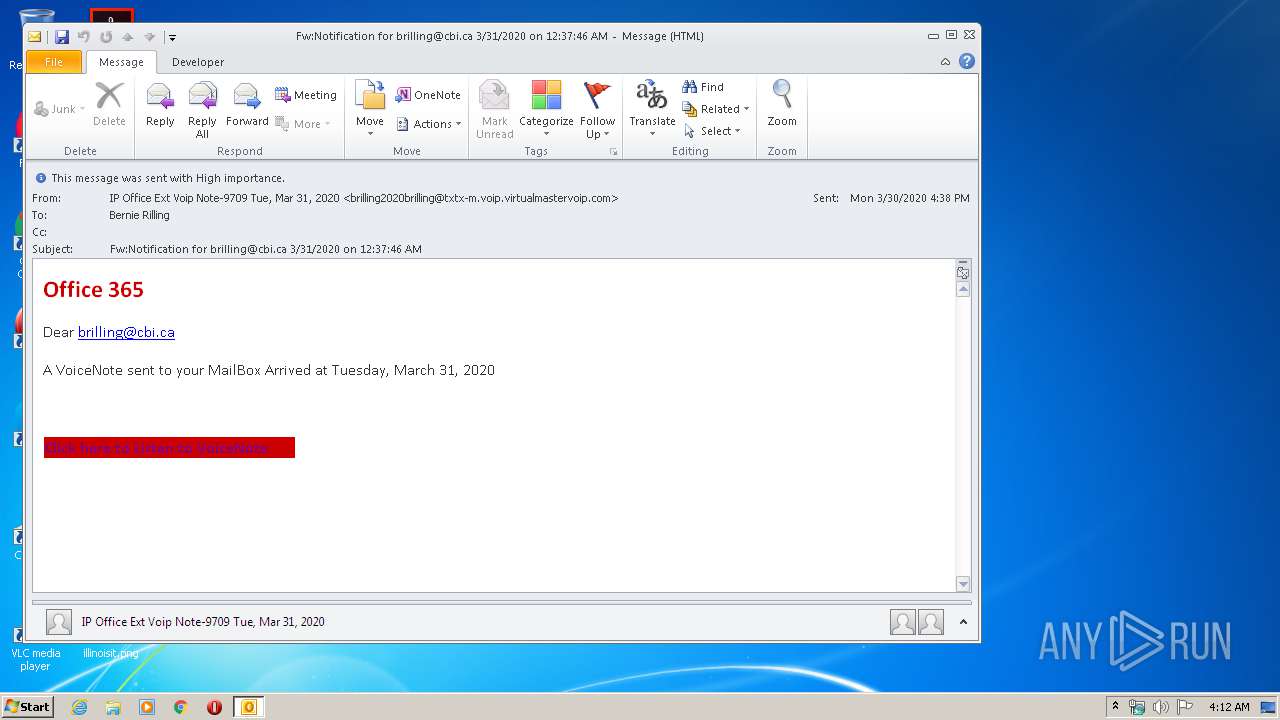
| File name: | FwNotification for [email protected] 3312020 on 123746 AM.msg |
| Full analysis: | https://app.any.run/tasks/75b36ed3-6138-4cf4-84db-daafbd5a6d2c |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 03:11:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | A2CF272A4306EB0510ED1A4FDDD2FAE4 |
| SHA1: | 9D28BD79A2C9C2C18F45D88FD4FD0C1567B70DC3 |
| SHA256: | 39DD236F289806A90B587818276E0154E62231567D94277812D39C04E5F01ED6 |
| SSDEEP: | 768:RtPvbcsKFbsKJ01sKFv0AfAHZa5u1vybsKF2d4eM:fbcdbGdv0AYHATd |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2872)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2872)
Executed via COM
- OUTLOOK.EXE (PID: 2588)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2872)
INFO
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2872)
- iexplore.exe (PID: 3672)
- iexplore.exe (PID: 2232)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2588)
- OUTLOOK.EXE (PID: 2872)
Application launched itself
- iexplore.exe (PID: 2232)
Changes internet zones settings
- iexplore.exe (PID: 2232)
Creates files in the user directory
- iexplore.exe (PID: 3672)
Reads internet explorer settings
- iexplore.exe (PID: 3672)
Reads settings of System Certificates
- iexplore.exe (PID: 3672)
- iexplore.exe (PID: 2232)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2232)
Changes settings of System certificates
- iexplore.exe (PID: 2232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
39
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
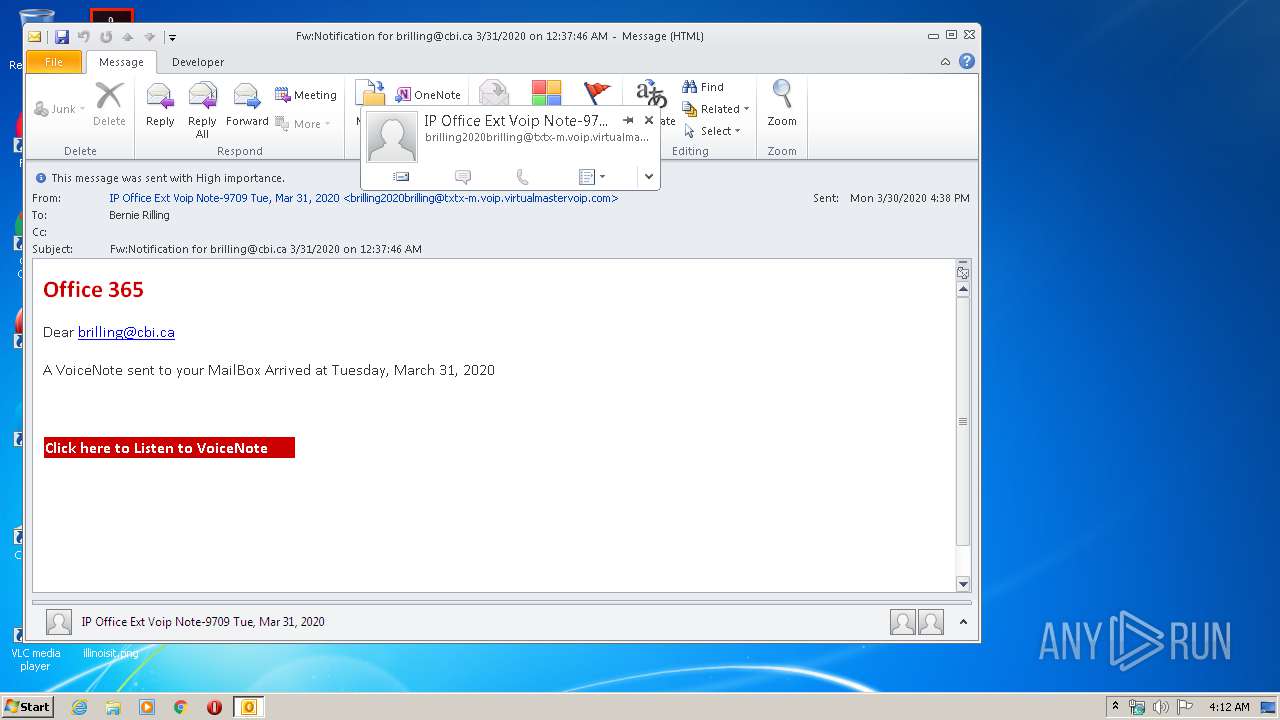
| 2872 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\FwNotification for [email protected] 3312020 on 123746 AM.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Version: 14.0.6025.1000 | ||||
| 2588 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | — | svchost.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 | ||||
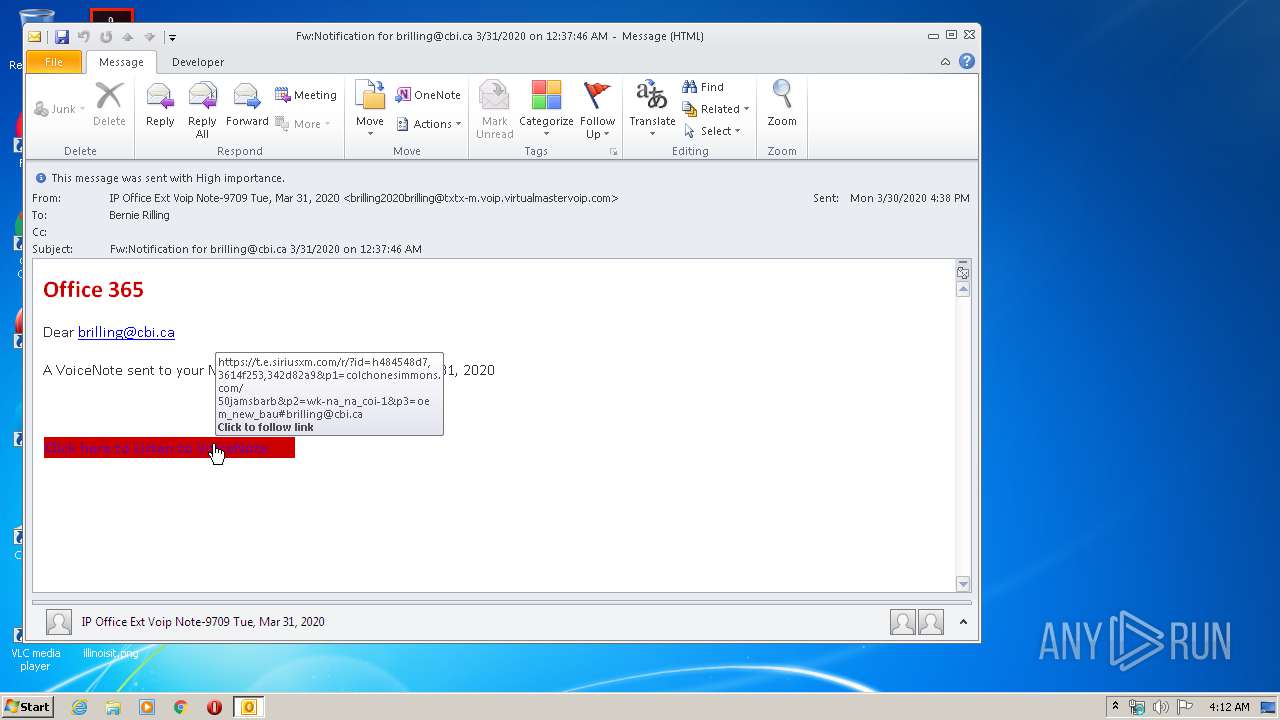
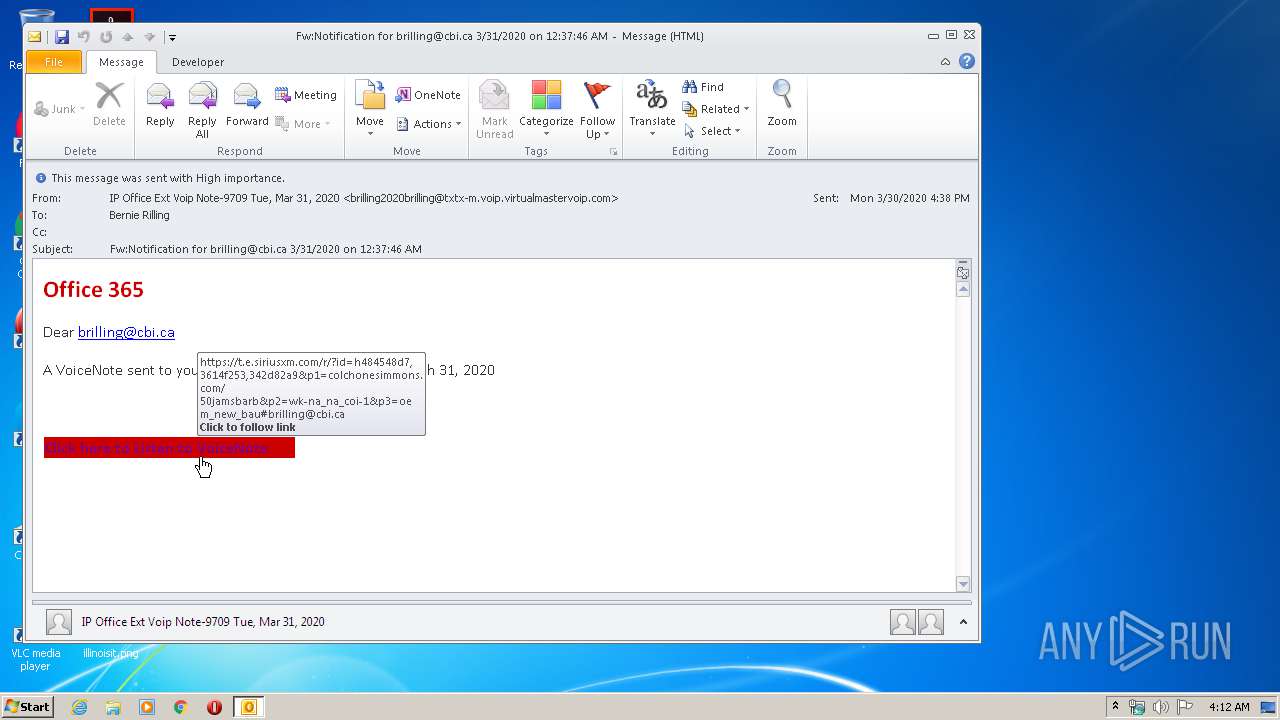
| 2232 | "C:\Program Files\Internet Explorer\iexplore.exe" https://t.e.siriusxm.com/r/?id=h484548d7,3614f253,342d82a9&p1=colchonesimmons.com/50jamsbarb&p2=WK-NA_NA_COI-1&p3=OEM_New_BAU#[email protected] | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
| 3672 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2232 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) | ||||
Total events
5 713
Read events
1 868
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
11
Text files
32
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2872 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR5C80.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2588 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR8DC1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3672 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabA0BD.tmp | — | |
MD5:— | SHA256:— | |||
| 3672 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarA0BE.tmp | — | |
MD5:— | SHA256:— | |||
| 2872 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:850D65FD6D9F370F8C2639AFFF5CC271 | SHA256:A51ACEDAE84A5041370E423C2D7DC259F56814862366F5A65F2C0DF371DA41CA | |||
| 2872 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:0CBEEDC4FAF9F994E55DAF021C377032 | SHA256:9CE0922BBC5D3CAE77AE8C1CE6CA6002955E89D1B5C5521F821C743E76EC345C | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF57408D47263D1B17.TMP | — | |
MD5:— | SHA256:— | |||
| 3672 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\D388BEBC625C181AB8B0CA40E7181396_34F77674E050D56F61C4EC7E8E06984D | der | |
MD5:0779D5883D410032F4597F4672686704 | SHA256:9D7C8F0EEFBB476DDC9C5663CDDB647F88EC53A753A023D3BDC54B9404260516 | |||
| 2872 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
16
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2872 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3672 | iexplore.exe | GET | 200 | 23.55.110.211:80 | http://ocsp.trustwave.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQ1mI4Ww4R5LZiQ295pj4OF%2F44yyAQUyk7dWyc1Kdn27sPlU%2B%2BkwBmWHa8CEQCSuHRPcc7Q4mxyo9jV2SWy | US | der | 1.62 Kb | whitelisted |
3672 | iexplore.exe | GET | 200 | 23.55.110.211:80 | http://ocsp.trustwave.com//MFQwUjBQME4wTDAJBgUrDgMCGgUABBRKUAJ27jxxuy1zYtpUHfLy0MHHugQUys4dGAN3HhzzfFiymnCoCIAW9K4CEwcLgzjsuWpkng9f8vuBGirSZfE%3D | US | der | 638 b | whitelisted |
3672 | iexplore.exe | GET | 200 | 23.55.110.185:80 | http://ocsp.trustwave.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQ1mI4Ww4R5LZiQ295pj4OF%2F44yyAQUyk7dWyc1Kdn27sPlU%2B%2BkwBmWHa8CEQCSuHRPcc7Q4mxyo9jV2SWy | US | der | 1.62 Kb | whitelisted |
3672 | iexplore.exe | GET | 200 | 23.55.110.185:80 | http://ocsp.trustwave.com//MFQwUjBQME4wTDAJBgUrDgMCGgUABBRKUAJ27jxxuy1zYtpUHfLy0MHHugQUys4dGAN3HhzzfFiymnCoCIAW9K4CEwcLgzjsuWpkng9f8vuBGirSZfE%3D | US | der | 638 b | whitelisted |
2232 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3672 | iexplore.exe | 192.185.21.150:443 | colchonesimmons.com | CyrusOne LLC | US | suspicious |
3672 | iexplore.exe | 52.10.227.163:443 | t.e.siriusxm.com | Amazon.com, Inc. | US | unknown |
2872 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3672 | iexplore.exe | 23.55.110.211:80 | ocsp.trustwave.com | NTT America, Inc. | US | suspicious |
3672 | iexplore.exe | 23.55.110.185:80 | ocsp.trustwave.com | NTT America, Inc. | US | suspicious |
2232 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2232 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
t.e.siriusxm.com |
| unknown |
ocsp.trustwave.com |
| whitelisted |
colchonesimmons.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3672 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3672 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |