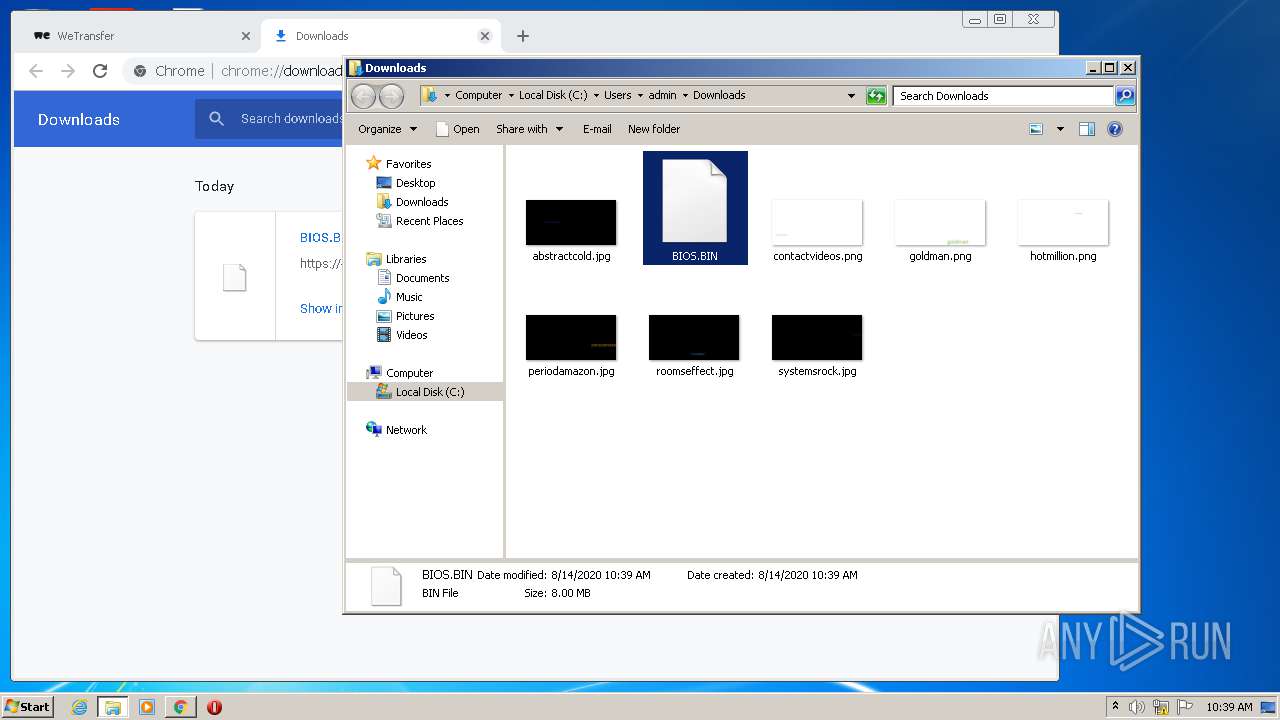
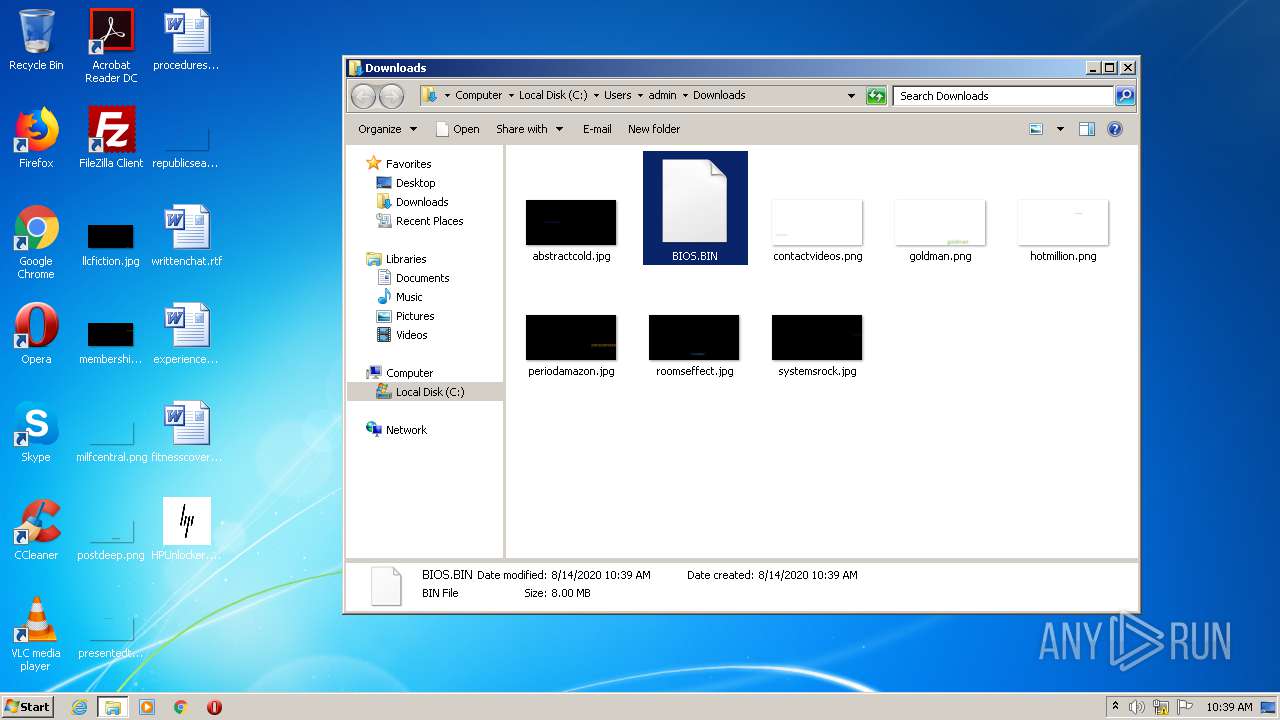
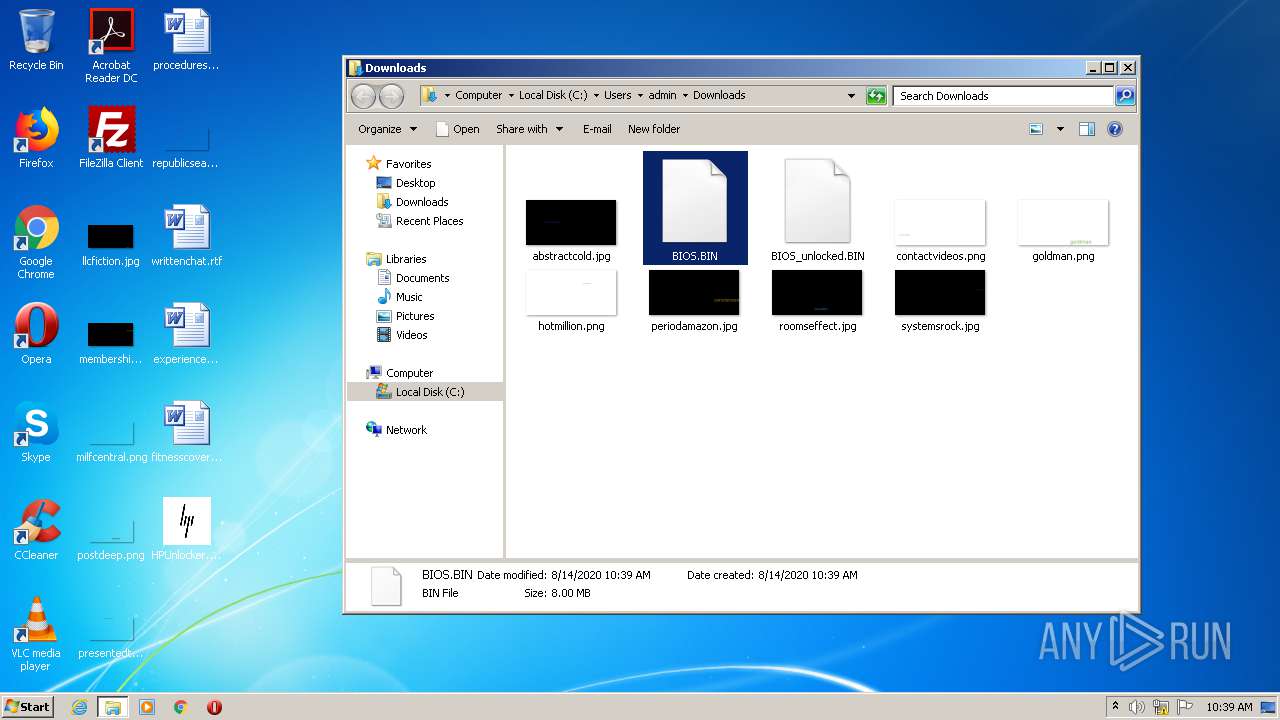
| File name: | HPUnlocker.exe |
| Full analysis: | https://app.any.run/tasks/d8f7f062-57ad-4e16-89d6-d4641af6438c |
| Verdict: | Malicious activity |
| Analysis date: | August 14, 2020, 09:37:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 18CE6A964452CD005B60FB6EF24726CE |
| SHA1: | 4C31A50473DCD88D7D552384E1C5E1C6623910BB |
| SHA256: | 39DA83CAEF2A930CBB64CEB00D2D040B25CC35DA620E233EE0357435C212EC24 |
| SSDEEP: | 98304:Zc7VlKTDbdRGQSxUTZeNEiIK176ykG5pcD7r2lQI4tQ:WVoTDp4QeUpg176K5aDn2/ |
MALICIOUS
Loads dropped or rewritten executable
- HPUnlocker.exe (PID: 2528)
- HPUnlocker.exe (PID: 1392)
- HPUnlocker.exe (PID: 2924)
- HPUnlocker.exe (PID: 2208)
- HPUnlocker.exe (PID: 3824)
- HPUnlocker.exe (PID: 2532)
- HPUnlocker.exe (PID: 884)
SUSPICIOUS
Application launched itself
- HPUnlocker.exe (PID: 4036)
- HPUnlocker.exe (PID: 3816)
- HPUnlocker.exe (PID: 3052)
- HPUnlocker.exe (PID: 3404)
- HPUnlocker.exe (PID: 324)
- HPUnlocker.exe (PID: 1064)
- HPUnlocker.exe (PID: 2628)
Executable content was dropped or overwritten
- HPUnlocker.exe (PID: 4036)
- HPUnlocker.exe (PID: 3816)
- HPUnlocker.exe (PID: 3052)
- HPUnlocker.exe (PID: 324)
- HPUnlocker.exe (PID: 1064)
- HPUnlocker.exe (PID: 2628)
Loads Python modules
- HPUnlocker.exe (PID: 2528)
- HPUnlocker.exe (PID: 1392)
- HPUnlocker.exe (PID: 2924)
- HPUnlocker.exe (PID: 2532)
- HPUnlocker.exe (PID: 2208)
- HPUnlocker.exe (PID: 3824)
- HPUnlocker.exe (PID: 884)
INFO
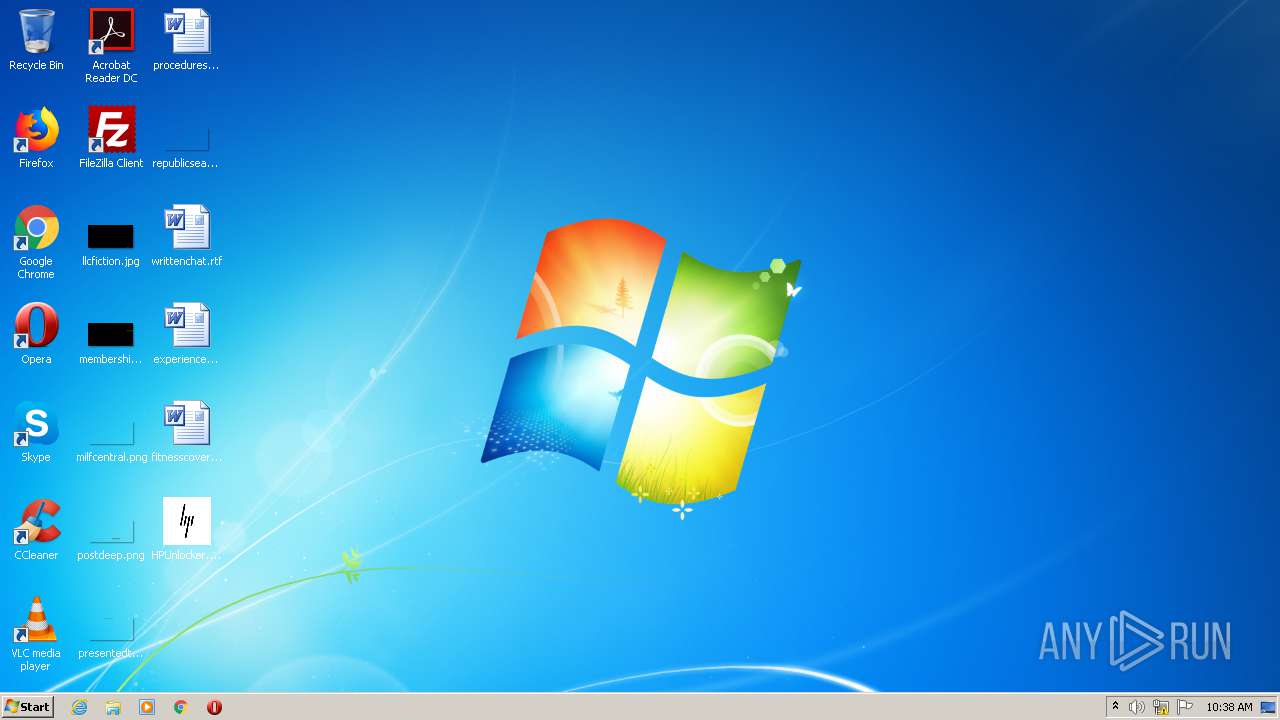
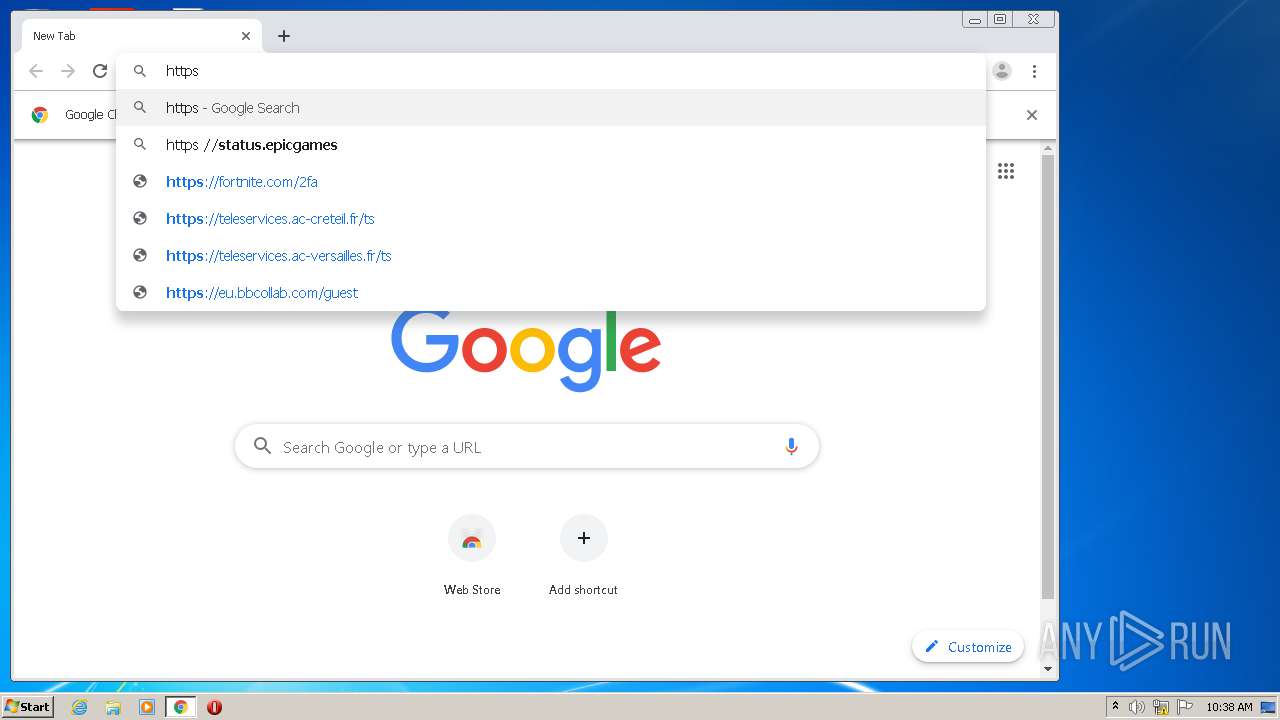
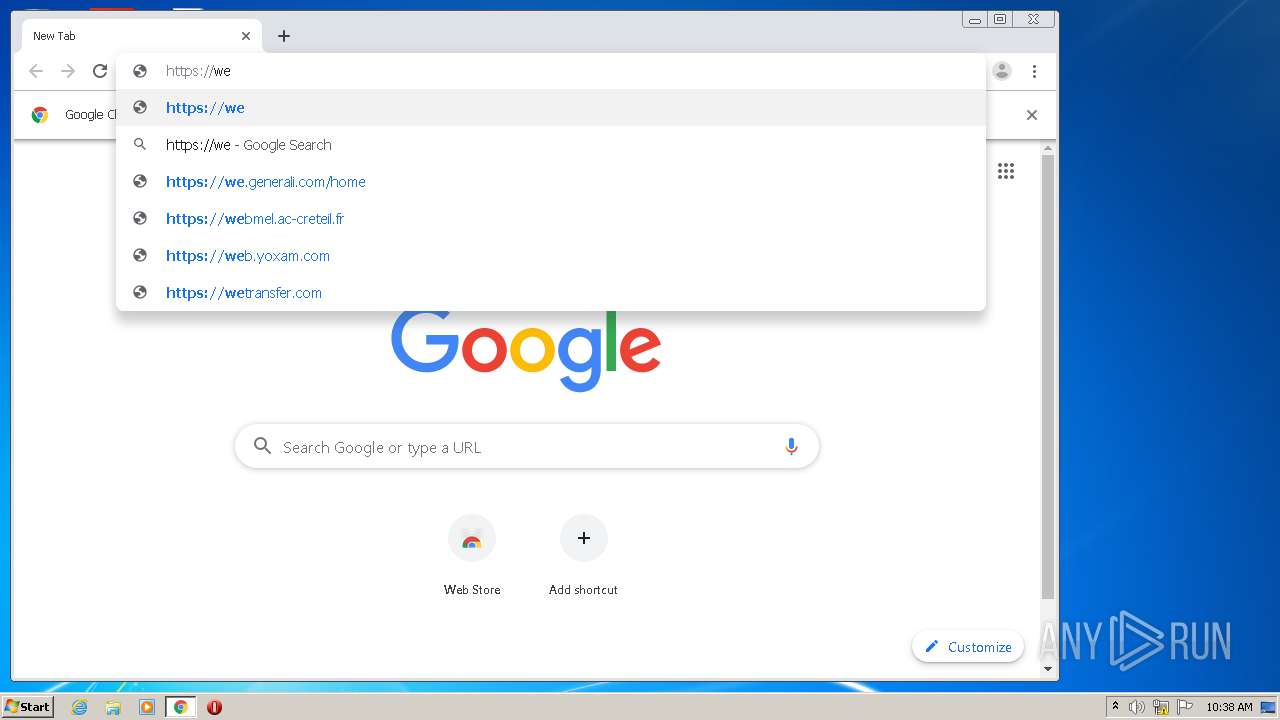
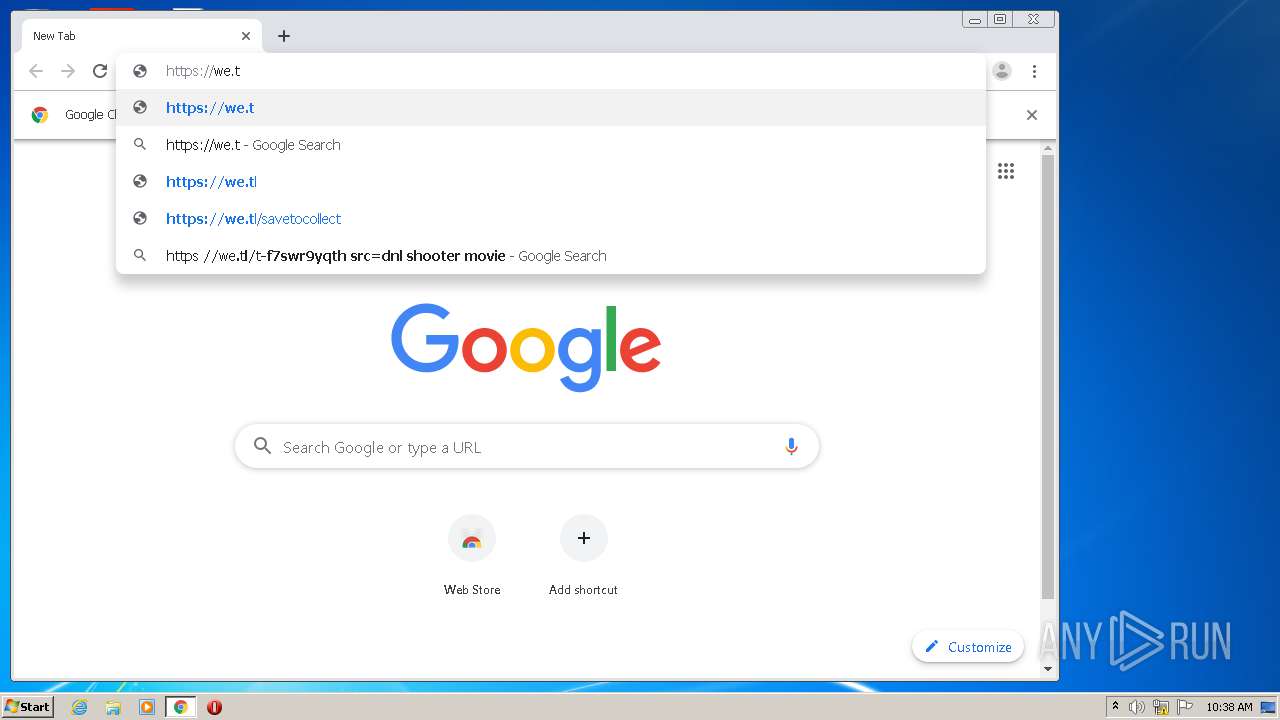
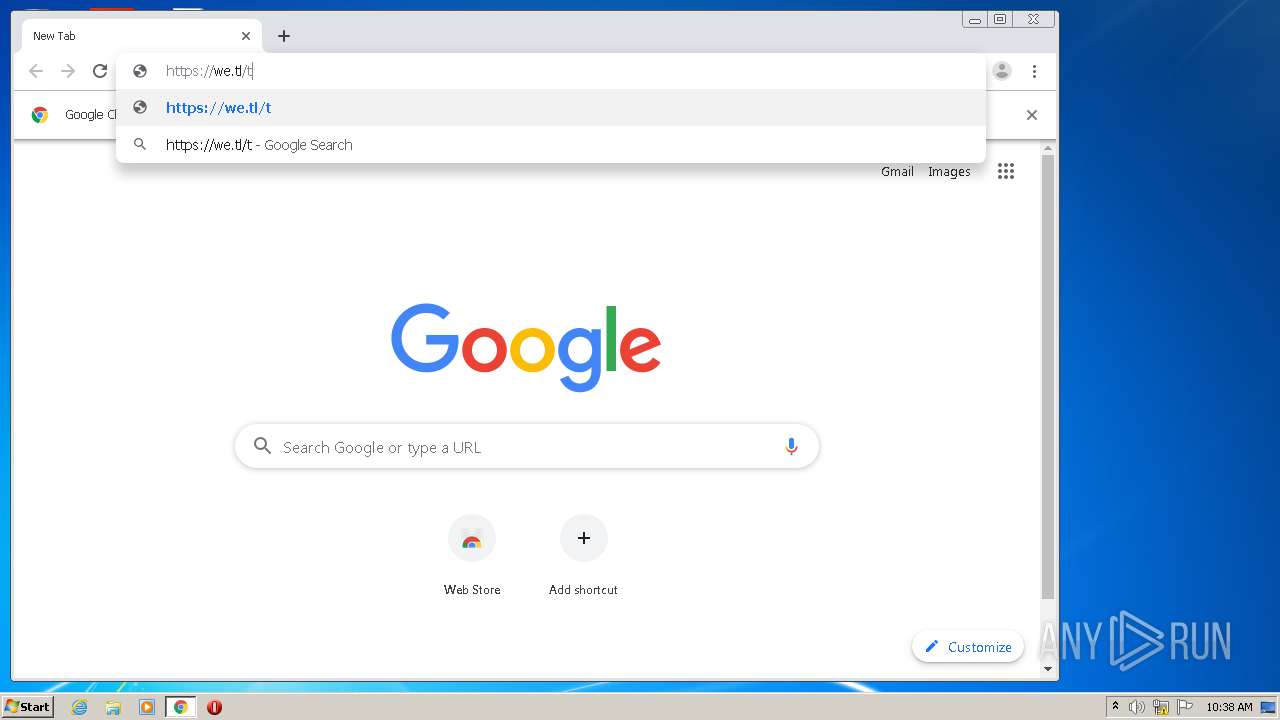
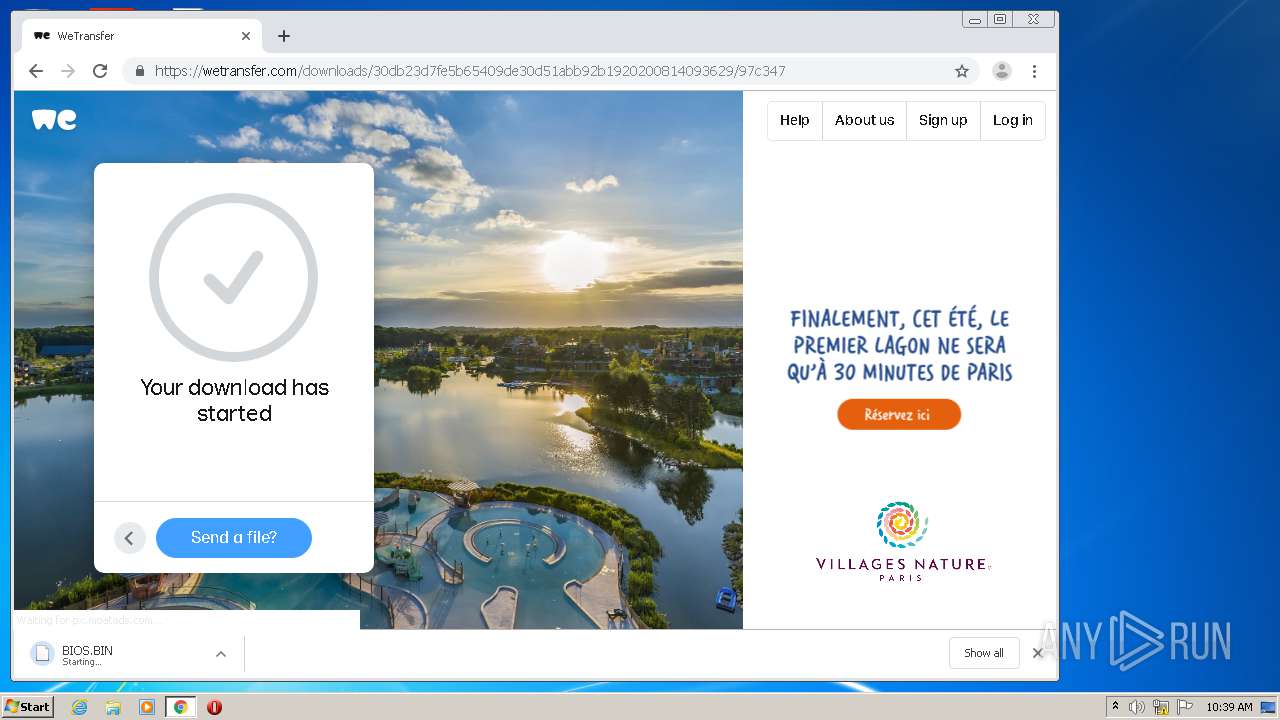
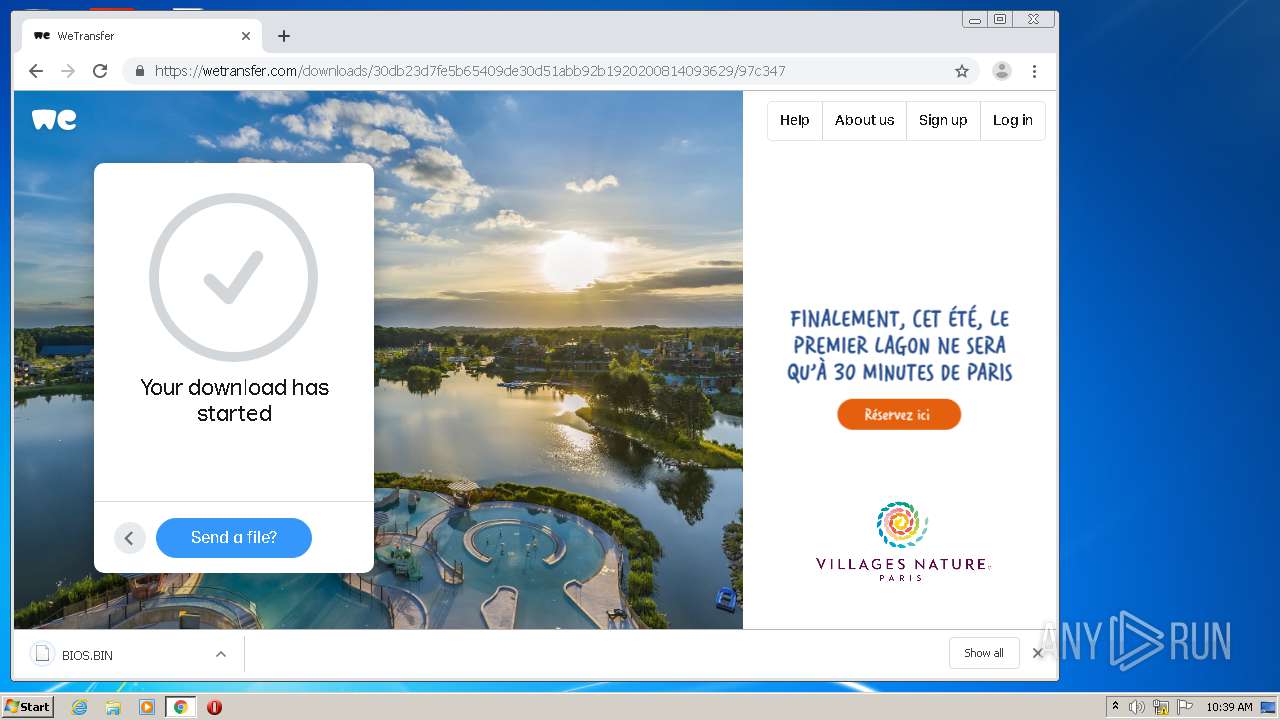
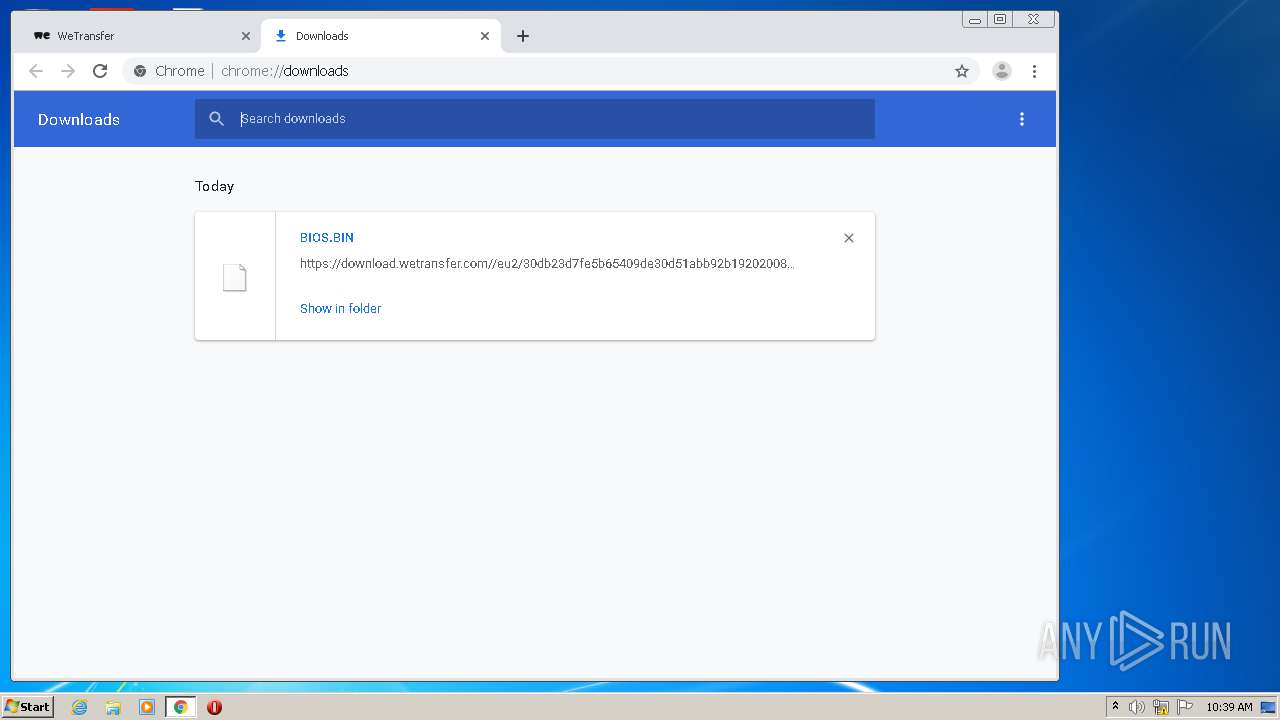
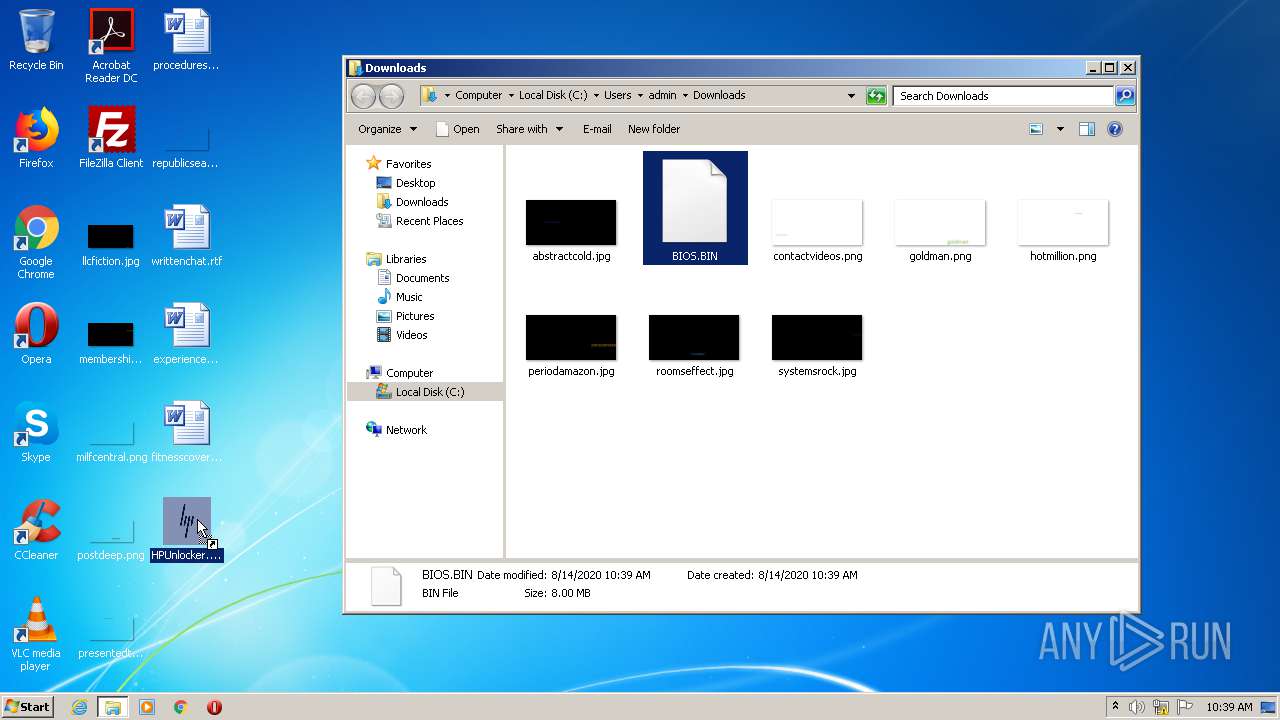
Manual execution by user
- chrome.exe (PID: 2980)
- HPUnlocker.exe (PID: 3816)
- HPUnlocker.exe (PID: 3052)
- HPUnlocker.exe (PID: 324)
- HPUnlocker.exe (PID: 2628)
- HPUnlocker.exe (PID: 1064)
- HPUnlocker.exe (PID: 3404)
Reads the hosts file
- chrome.exe (PID: 316)
- chrome.exe (PID: 2980)
Application launched itself
- chrome.exe (PID: 2980)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2980)
Reads Internet Cache Settings
- chrome.exe (PID: 2980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:09 16:23:33+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 126464 |
| InitializedDataSize: | 265728 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7b43 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Jul-2019 14:23:33 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 09-Jul-2019 14:23:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001ECA4 | 0x0001EE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64533 |
.rdata | 0x00020000 | 0x0000B164 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.10043 |
.data | 0x0002C000 | 0x0000E688 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.92387 |
.gfids | 0x0003B000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.85181 |
.rsrc | 0x0003C000 | 0x000336DC | 0x00033800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.18623 |
.reloc | 0x00070000 | 0x000017B8 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65903 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 2.01924 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
1 | 5.31683 | 1033 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 6.44895 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.77742 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 7.95095 | 38188 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 6.0521 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 6.15081 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 6.39466 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
USER32.dll |
WS2_32.dll |
Total processes
86
Monitored processes
40
Malicious processes
0
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,2821970658680616526,11244454890452964036,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=15898486021247744531 --mojo-platform-channel-handle=1636 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
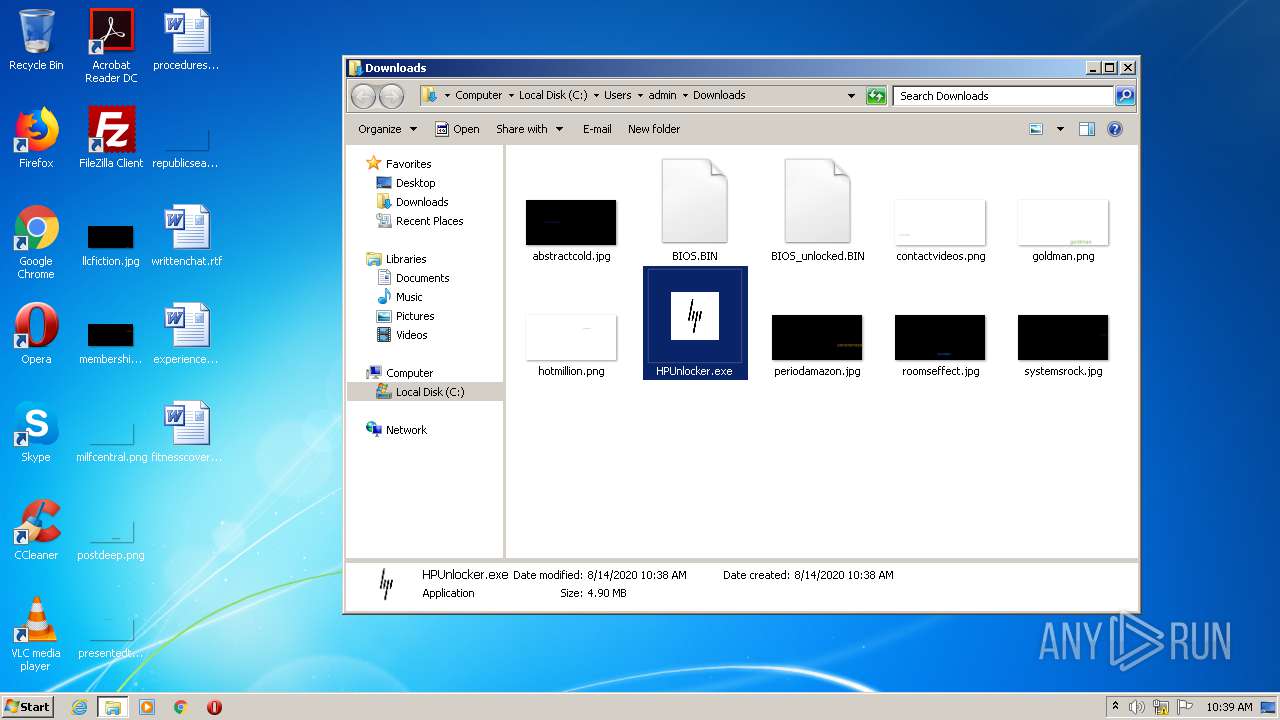
| 324 | "C:\Users\admin\Downloads\HPUnlocker.exe" | C:\Users\admin\Downloads\HPUnlocker.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
| 632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,2821970658680616526,11244454890452964036,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2831682871722702136 --mojo-platform-channel-handle=3316 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
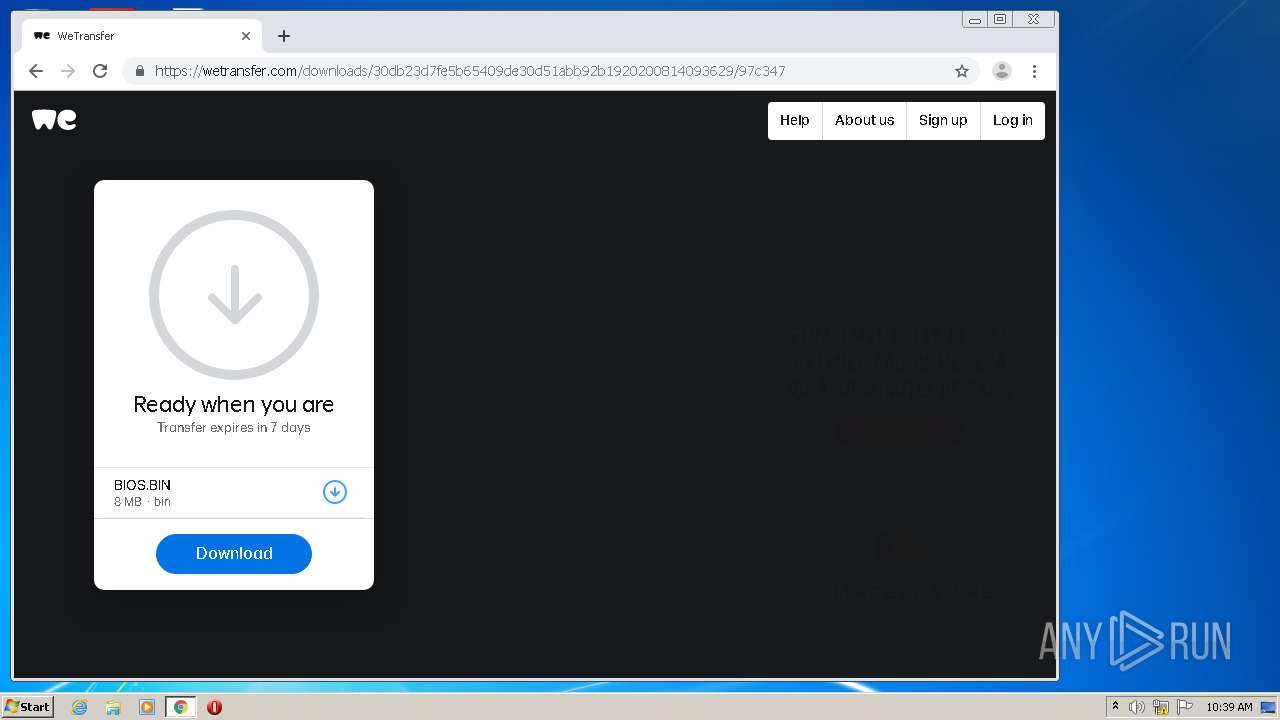
| 884 | "C:\Users\admin\Downloads\HPUnlocker.exe" C:\Users\admin\Downloads\BIOS.BIN | C:\Users\admin\Downloads\HPUnlocker.exe | — | HPUnlocker.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,2821970658680616526,11244454890452964036,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2763187502551400311 --mojo-platform-channel-handle=3288 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,2821970658680616526,11244454890452964036,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14128198645650741011 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2364 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1064 | "C:\Users\admin\Downloads\HPUnlocker.exe" | C:\Users\admin\Downloads\HPUnlocker.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
| 1384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,2821970658680616526,11244454890452964036,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=16985876358570873434 --mojo-platform-channel-handle=3252 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1392 | "C:\Users\admin\Desktop\HPUnlocker.exe" C:\Users\admin\Downloads\BIOS.BIN | C:\Users\admin\Desktop\HPUnlocker.exe | — | HPUnlocker.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2208 | "C:\Users\admin\Downloads\HPUnlocker.exe" | C:\Users\admin\Downloads\HPUnlocker.exe | — | HPUnlocker.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
Total events
1 008
Read events
866
Write events
137
Delete events
5
Modification events
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3084) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2980-13241871500880000 |
Value: 259 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
72
Suspicious files
61
Text files
104
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4036 | HPUnlocker.exe | C:\Users\admin\AppData\Local\Temp\_MEI40362\_hashlib.pyd | executable | |
MD5:E84E1BA269371E439C2D52024ACA6535 | SHA256:2FCB297733E6080480AC24CF073FF5E239FB02A1CE9694313C5047F9C58D781B | |||
| 4036 | HPUnlocker.exe | C:\Users\admin\AppData\Local\Temp\_MEI40362\VCRUNTIME140.dll | executable | |
MD5:AE96651CFBD18991D186A029CBECB30C | SHA256:1B372F064EACB455A0351863706E6326CA31B08E779A70DE5DE986B5BE8069A1 | |||
| 4036 | HPUnlocker.exe | C:\Users\admin\AppData\Local\Temp\_MEI40362\HPUnlocker.exe.manifest | xml | |
MD5:2FE927FFD24AE177B57C1BC3C26DD874 | SHA256:BD3B6F69FE74E06DC5EC7CAE2A8A189C889610FC656E3B489CC911FFA93BABBA | |||
| 4036 | HPUnlocker.exe | C:\Users\admin\AppData\Local\Temp\_MEI40362\_bz2.pyd | executable | |
MD5:FF5AC8FB724EDB1635E2AD985F98EE5B | SHA256:B94F64FCB49F40682ED794FA1940A1DC0C8A28F24A1768D3BFE774CF75F59B62 | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ef6a7b1c-b12b-443c-a90e-2bdb8715045e.tmp | — | |
MD5:— | SHA256:— | |||
| 4036 | HPUnlocker.exe | C:\Users\admin\AppData\Local\Temp\_MEI40362\_lzma.pyd | executable | |
MD5:65880A33015AF2030A08987924CA737B | SHA256:A71366B95D89D1539A6EE751D48A969C1BCA1AA75116424CC5F905F32A625EEA | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:1A89A1BEBE6C843C4FF582E7ED33CA1F | SHA256:65099CA087B66AA8CA420AB121DAAD713E1DB5A61C5A574D9B1C0DF24F012520 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
50
DNS requests
34
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
316 | chrome.exe | 216.58.207.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
316 | chrome.exe | 216.58.205.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
316 | chrome.exe | 216.58.210.14:443 | ogs.google.com | Google Inc. | US | whitelisted |
316 | chrome.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
316 | chrome.exe | 216.58.212.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
316 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
316 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
316 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
316 | chrome.exe | 13.226.155.59:443 | we.tl | — | US | unknown |
316 | chrome.exe | 13.226.155.54:443 | prod-cdn.wetransfer.net | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |