| File name: | ConnectUtility_2.20.28_Logitech.exe |
| Full analysis: | https://app.any.run/tasks/05264503-22a7-4b4c-a331-335d0a5ba4b1 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2023, 10:52:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 4AB3B30E081A6F0B95C205F2D9A000FE |
| SHA1: | 9D8BE3F1029119490E59C389440703E987BE0E1B |
| SHA256: | 39D3BA982AF73366080F48D85020EF2E719AEBA8795ABA474F278CB4F720A66B |
| SSDEEP: | 24576:C0aHKsZpBj3uz0uIyBYPEtkcqOo1HsBdjQzMutbDP95zqV7h:CUsBnyq4krZ1ajQzMo9xch |
MALICIOUS
Loads dropped or rewritten executable
- ConnectUtility_2.20.28_Logitech.exe (PID: 1544)
- ConnectUtility.exe (PID: 2604)
Application was dropped or rewritten from another process
- ConnectUtility.exe (PID: 2604)
SUSPICIOUS
The process creates files with name similar to system file names
- ConnectUtility_2.20.28_Logitech.exe (PID: 1544)
Executable content was dropped or overwritten
- ConnectUtility_2.20.28_Logitech.exe (PID: 1544)
INFO
The process checks LSA protection
- ConnectUtility_2.20.28_Logitech.exe (PID: 1544)
- ConnectUtility.exe (PID: 2604)
Checks supported languages
- ConnectUtility_2.20.28_Logitech.exe (PID: 1544)
- ConnectUtility.exe (PID: 2604)
Reads the computer name
- ConnectUtility_2.20.28_Logitech.exe (PID: 1544)
- ConnectUtility.exe (PID: 2604)
Creates files or folders in the user directory
- ConnectUtility_2.20.28_Logitech.exe (PID: 1544)
Create files in a temporary directory
- ConnectUtility_2.20.28_Logitech.exe (PID: 1544)
Reads the machine GUID from the registry
- ConnectUtility.exe (PID: 2604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| ProductName: | ConnectUtility Setup |
|---|---|
| LegalCopyright: | Copyright � 2005-2016 Logitech. All Rights Reserved |
| FileVersion: | 2.20.28 |
| FileDescription: | Setup |
| CompanyName: | Logitech Inc. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 2.20.28.0 |
| FileVersionNumber: | 2.20.28.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | 6.1 |
| OSVersion: | 5 |
| EntryPoint: | 0x33e9 |
| UninitializedDataSize: | 16896 |
| InitializedDataSize: | 431104 |
| CodeSize: | 25600 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| TimeStamp: | 2009:09:09 13:23:14+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Sep-2009 13:23:14 |
| Detected languages: |
|
| CompanyName: | Logitech Inc. |
| FileDescription: | Setup |
| FileVersion: | 2.20.28 |
| LegalCopyright: | Copyright � 2005-2016 Logitech. All Rights Reserved |
| ProductName: | ConnectUtility Setup |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 09-Sep-2009 13:23:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006240 | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.42174 |
.rdata | 0x00008000 | 0x000018CA | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.87837 |
.data | 0x0000A000 | 0x0006667C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.35872 |
.ndata | 0x00071000 | 0x00155000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x001C6000 | 0x00000A10 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.04118 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19385 | 735 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
40
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1544 | "C:\Users\admin\AppData\Local\Temp\ConnectUtility_2.20.28_Logitech.exe" | C:\Users\admin\AppData\Local\Temp\ConnectUtility_2.20.28_Logitech.exe | explorer.exe | ||||||||||||
User: admin Company: Logitech Inc. Integrity Level: HIGH Description: Setup Exit code: 0 Version: 2.20.28 Modules
| |||||||||||||||
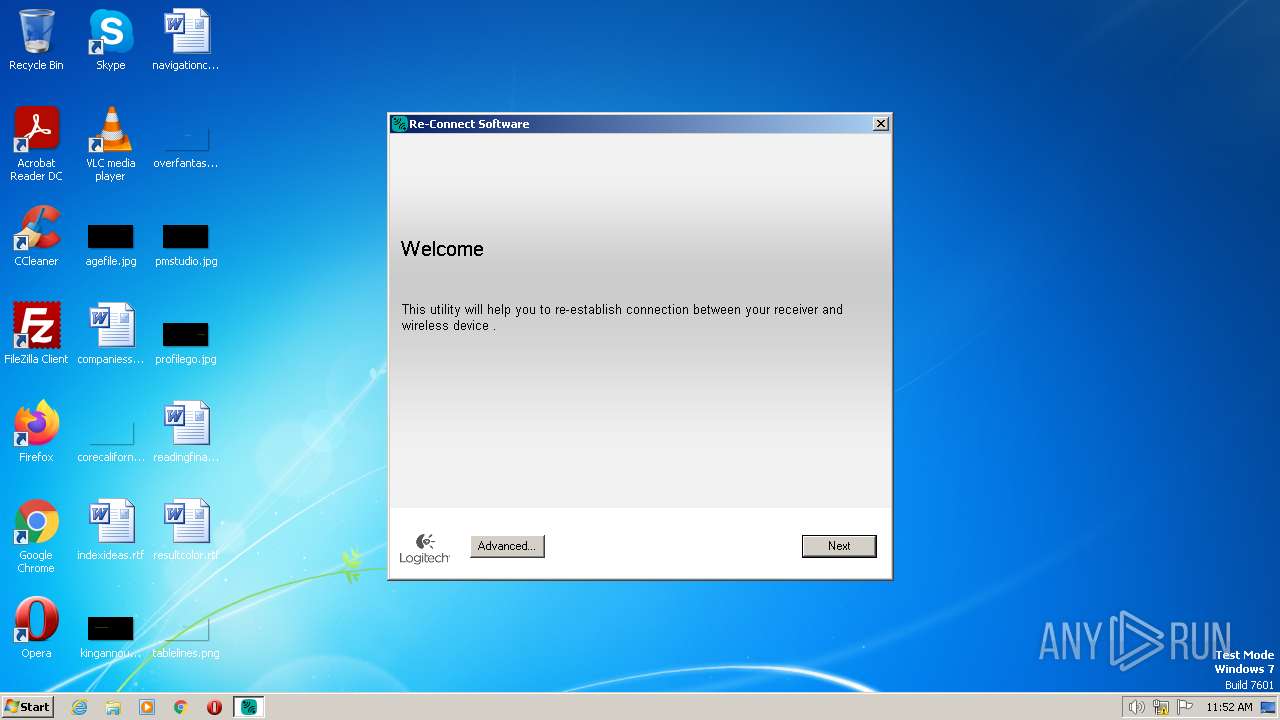
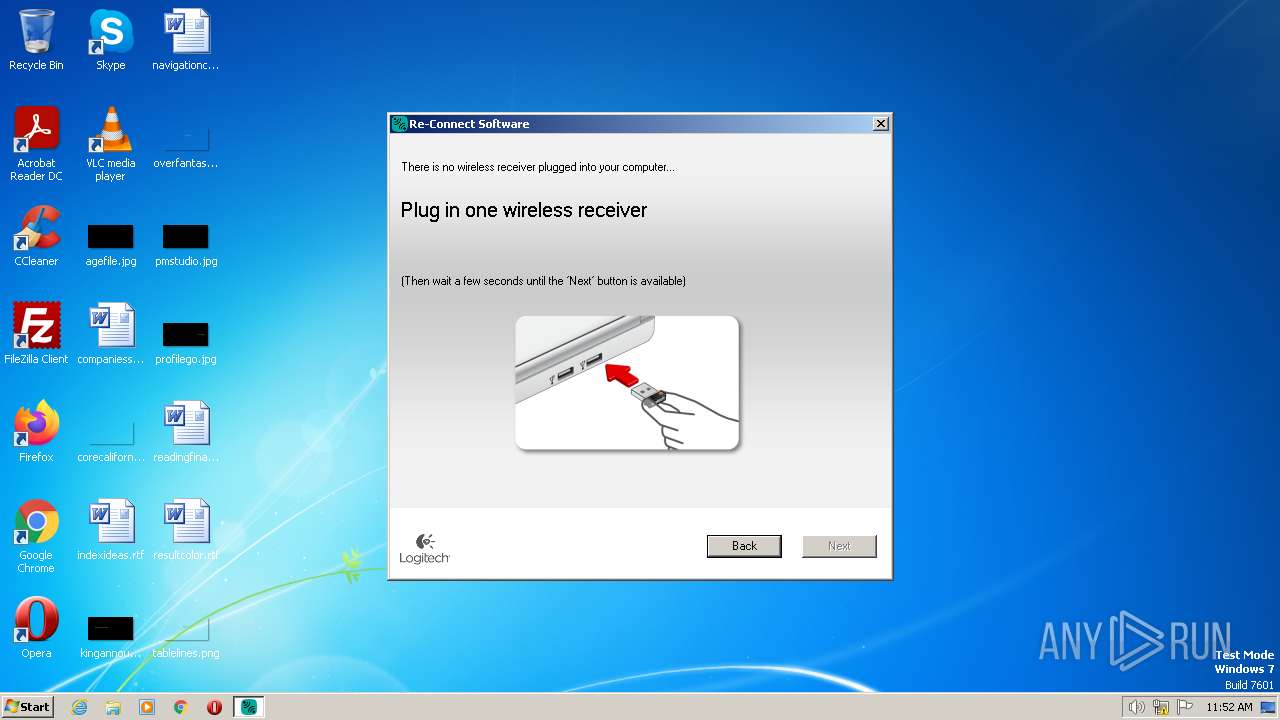
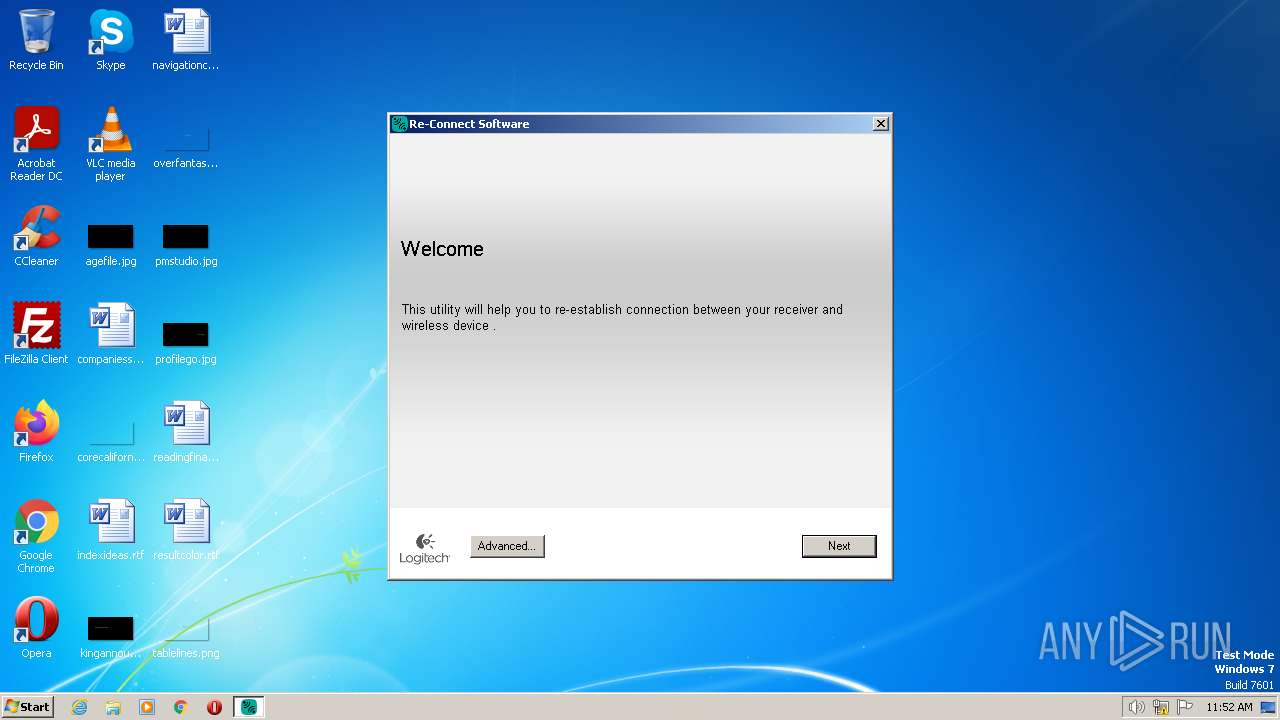
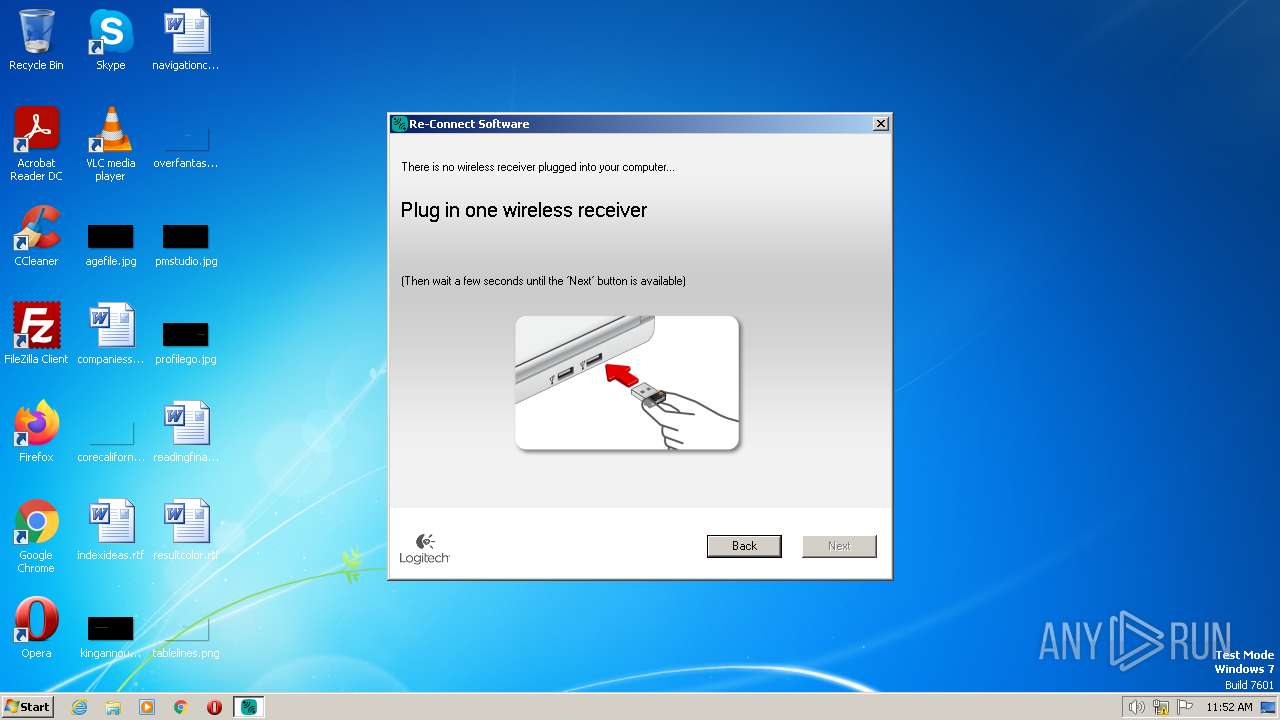
| 2604 | C:\Windows\ConnectUtility.exe | C:\Windows\ConnectUtility.exe | ConnectUtility_2.20.28_Logitech.exe | ||||||||||||
User: admin Company: Logitech, Inc. Integrity Level: HIGH Description: Re-Connect Software (UNICODE) Exit code: 0 Version: 2.20.28 Modules
| |||||||||||||||
| 3960 | "C:\Users\admin\AppData\Local\Temp\ConnectUtility_2.20.28_Logitech.exe" | C:\Users\admin\AppData\Local\Temp\ConnectUtility_2.20.28_Logitech.exe | — | explorer.exe | |||||||||||
User: admin Company: Logitech Inc. Integrity Level: MEDIUM Description: Setup Exit code: 3221226540 Version: 2.20.28 Modules
| |||||||||||||||
Total events
812
Read events
812
Write events
0
Delete events
0
Modification events
Executable files
5
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1544 | ConnectUtility_2.20.28_Logitech.exe | C:\Users\admin\AppData\Local\Temp\nscC7E7.tmp\UserInfo.dll | executable | |
MD5:351B802508EE5462CBF7F35454A9DCA6 | SHA256:39275EE1767AAC3AE0929A3E67A84A921610B45D5CFFF3DB1641893504D5C78D | |||
| 1544 | ConnectUtility_2.20.28_Logitech.exe | C:\Users\admin\AppData\Roaming\Logishrd\sp6_log\sp6_setup.log | binary | |
MD5:E36958BCEC33D3C12C6E505707ACFEDB | SHA256:B7F560303EE2CCA55615B53FCFF87C6AB2C55F9E71A6CEA93C61B572213E7075 | |||
| 1544 | ConnectUtility_2.20.28_Logitech.exe | C:\Windows\ConnectUtility.exe | executable | |
MD5:51C47F45691D8D10853E428605BA71F9 | SHA256:921AD757BF19E79EA8ABF528C012DB232B86373A4A2032857DD7D3A3FBD0661D | |||
| 1544 | ConnectUtility_2.20.28_Logitech.exe | C:\Users\admin\AppData\Local\Temp\nscC7E7.tmp\System.dll | executable | |
MD5:B9F430F71C7144D8FF4AB94BE2785AA6 | SHA256:B496E81A74CE871236ABCD096FB9A6B210B456BEBAA7464FA844B3241E51A655 | |||
| 1544 | ConnectUtility_2.20.28_Logitech.exe | C:\Windows\DJCU.dll | executable | |
MD5:795759630FA6F010A1C2F16D609D7883 | SHA256:50D3A8382929841B6DF4300B7BB57A175B00996116994B914200821CD6586CB1 | |||
| 1544 | ConnectUtility_2.20.28_Logitech.exe | C:\Windows\DJAPI.dll | executable | |
MD5:BF17F8E62235F0A4120D2B6175EDC806 | SHA256:1B8FFBF432A5FE0697F2504EE4E2F146432686527CB25E78AD69538893D8AD7C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Threats
Process | Message |
|---|---|
ConnectUtility.exe | Failure opening the EngineLog file
|
ConnectUtility.exe | The Logging system had trouble initializing |