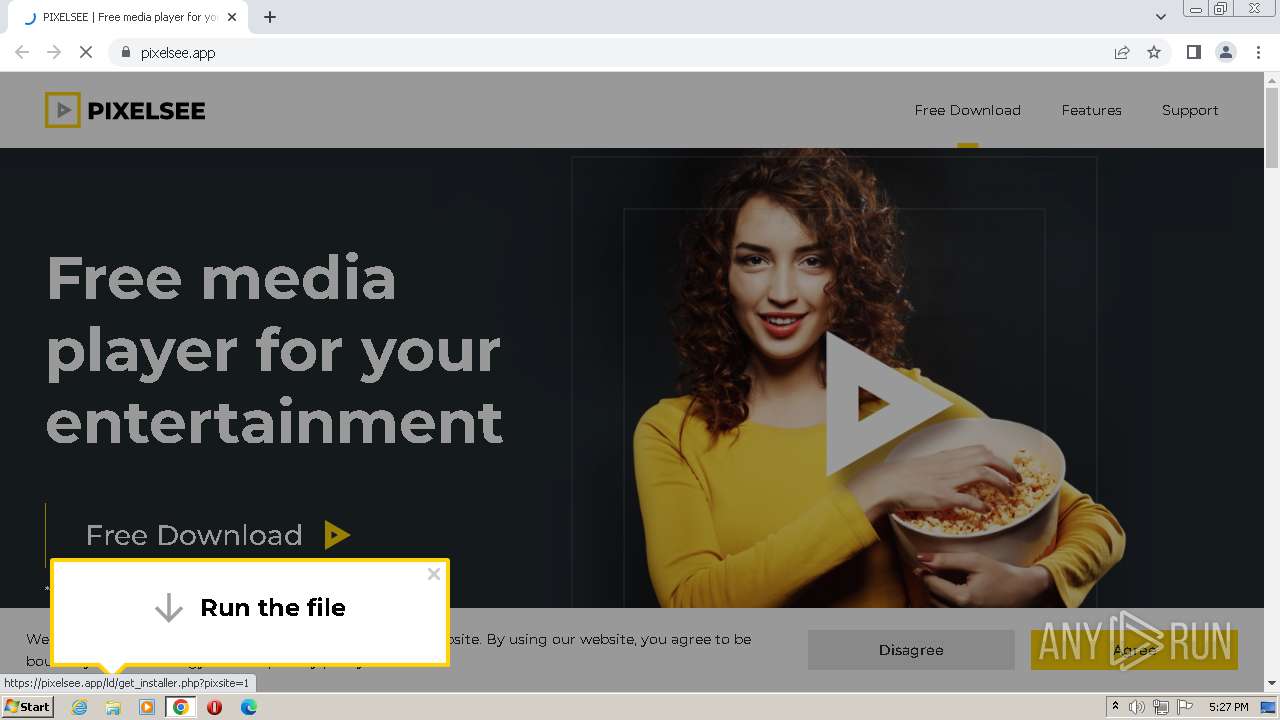
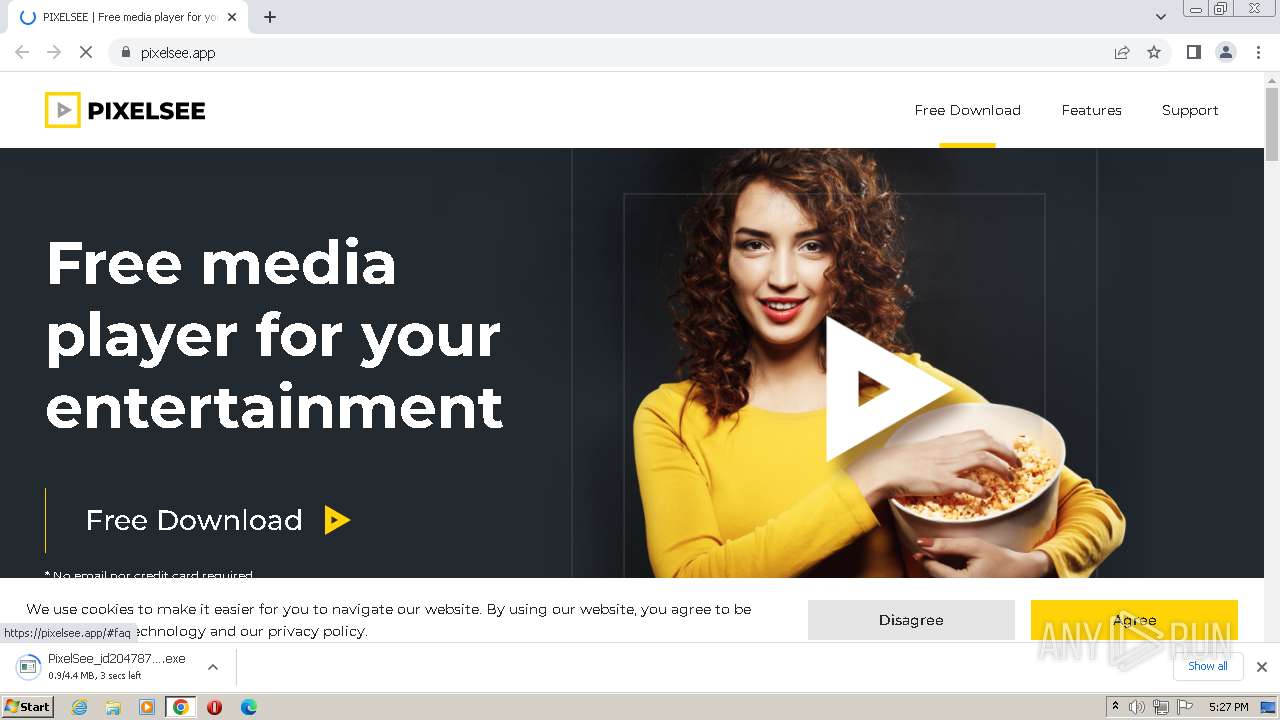
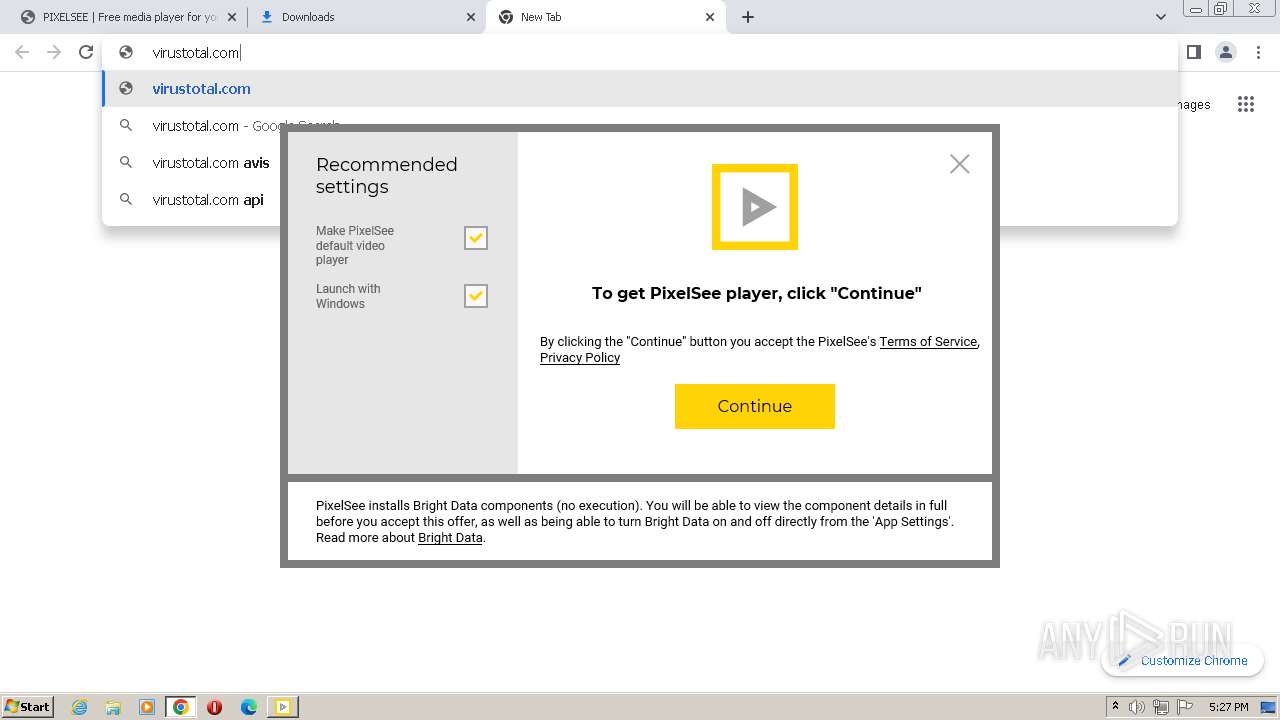
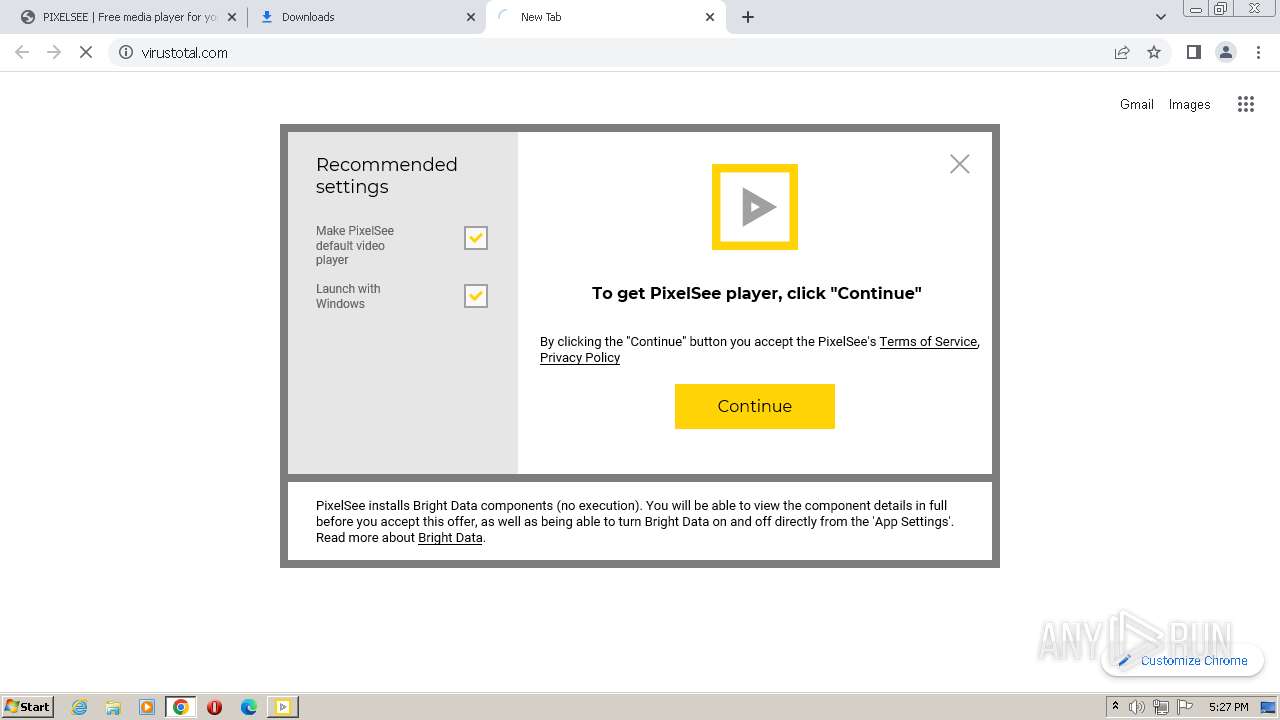
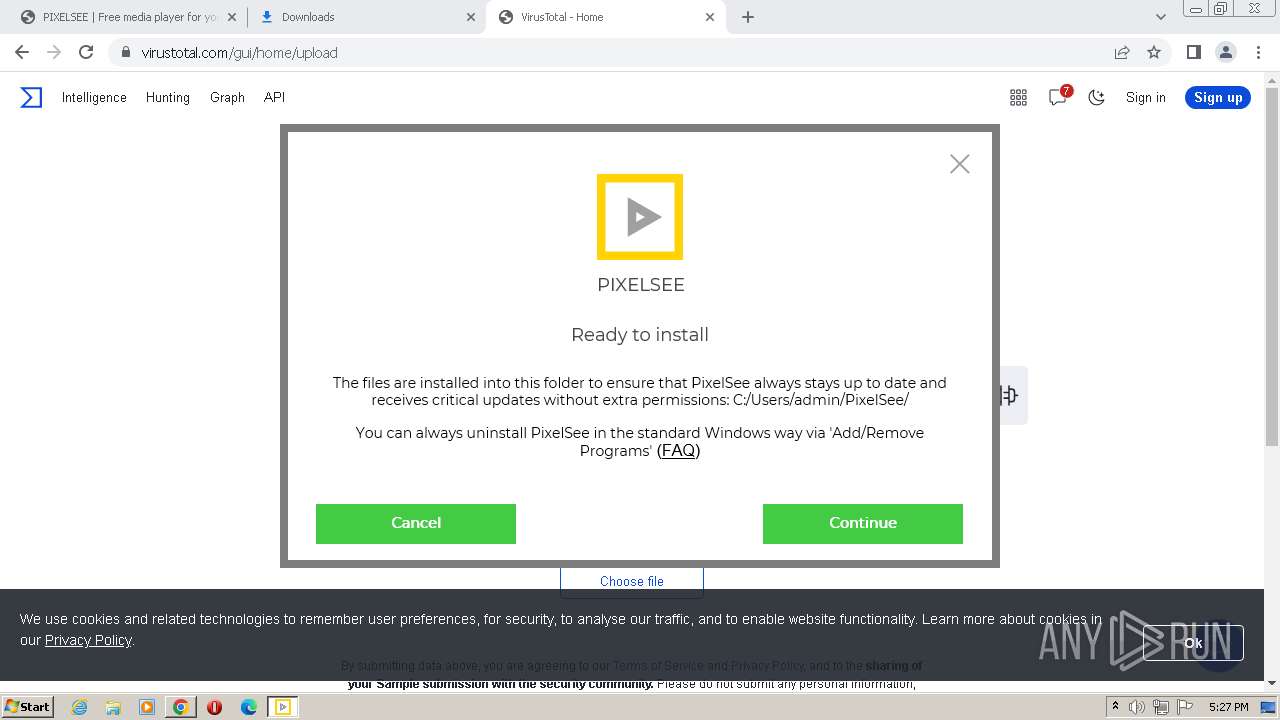
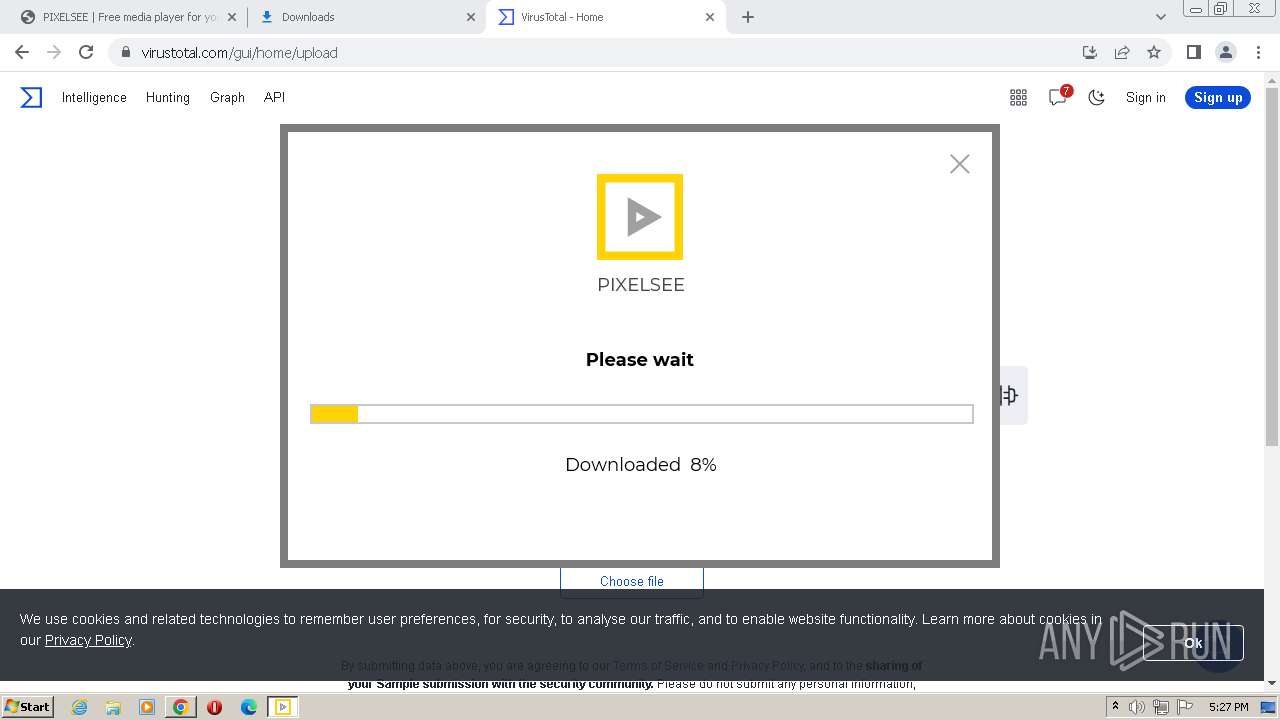
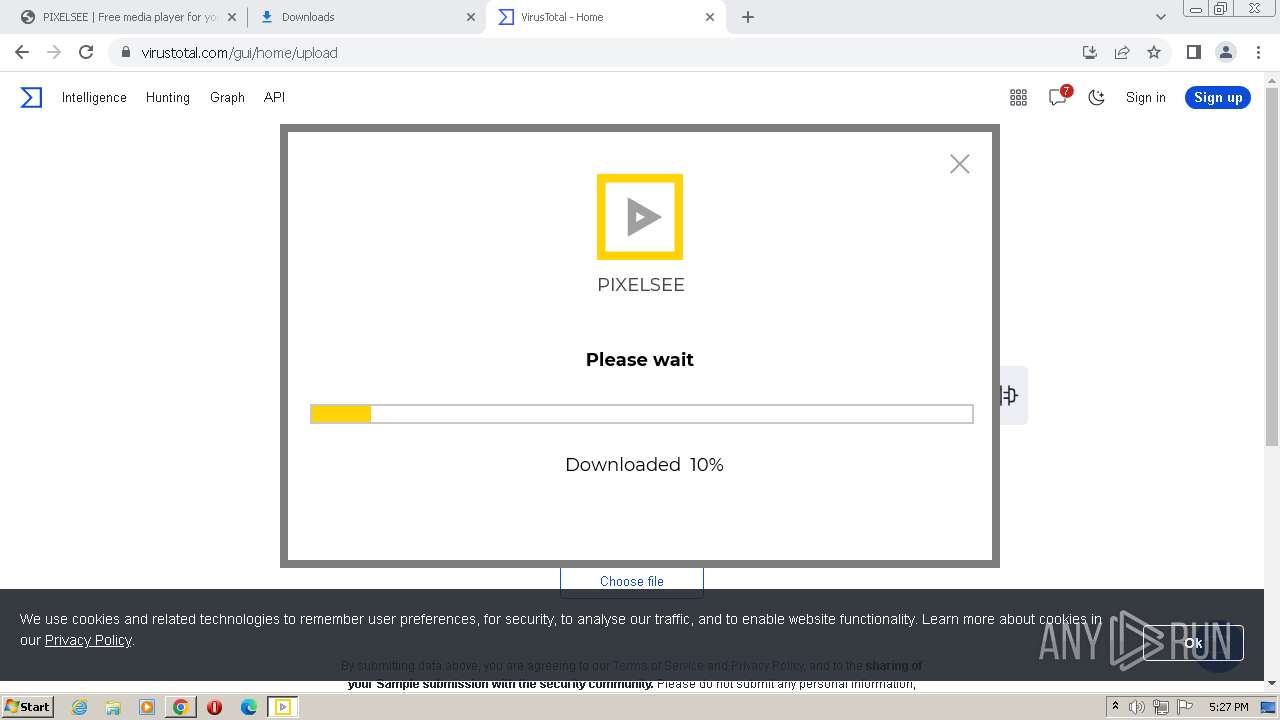
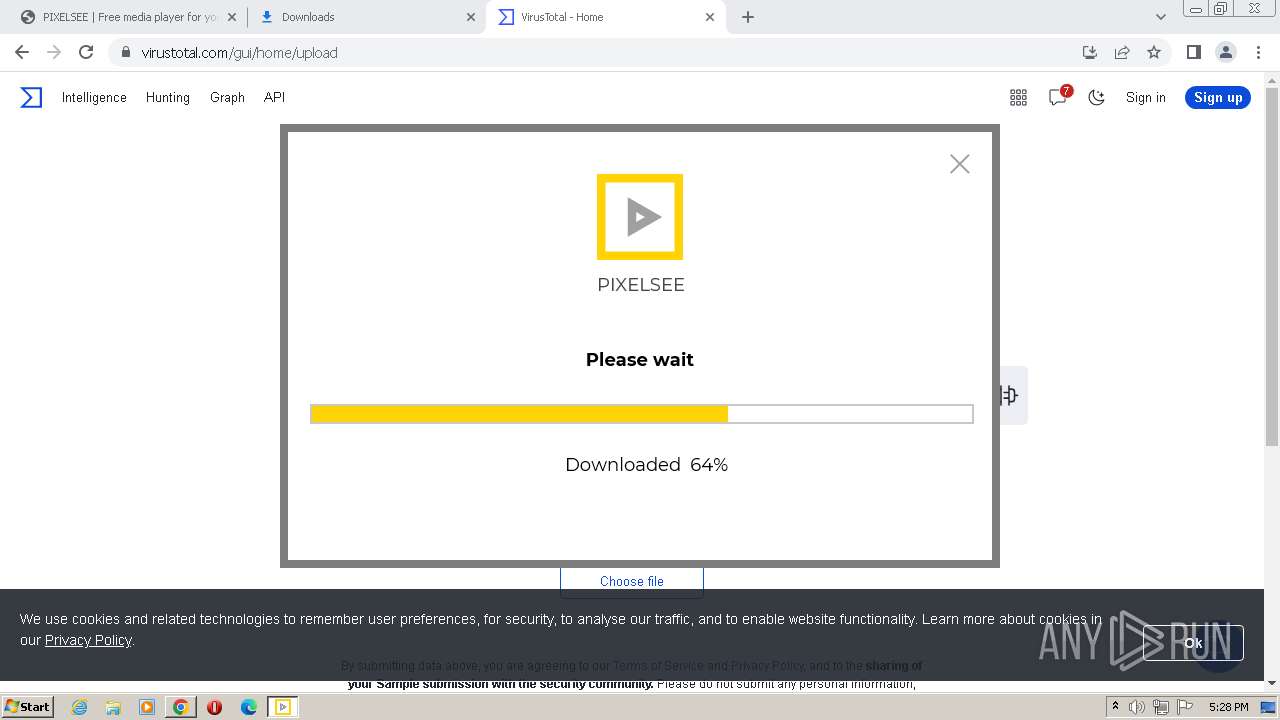
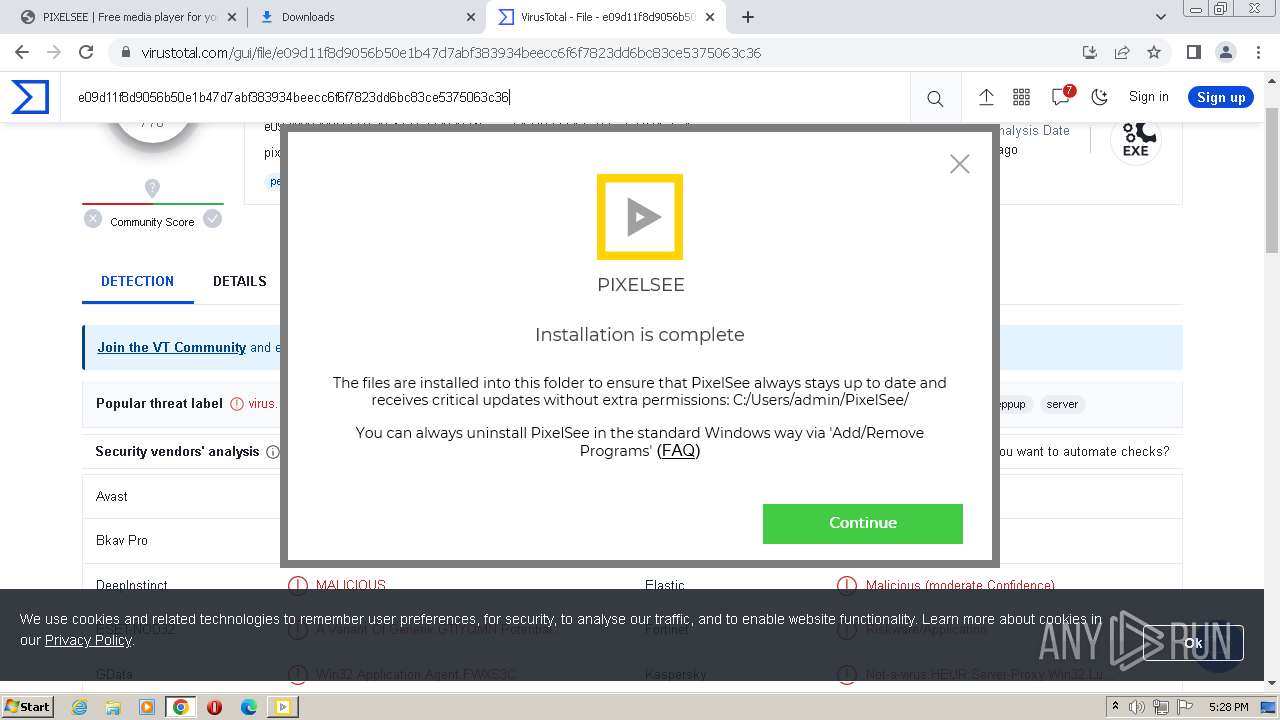
| URL: | https://pixelsee.app/ |
| Full analysis: | https://app.any.run/tasks/97eb313f-5ef7-4ee2-bdf8-81ad15688ae3 |
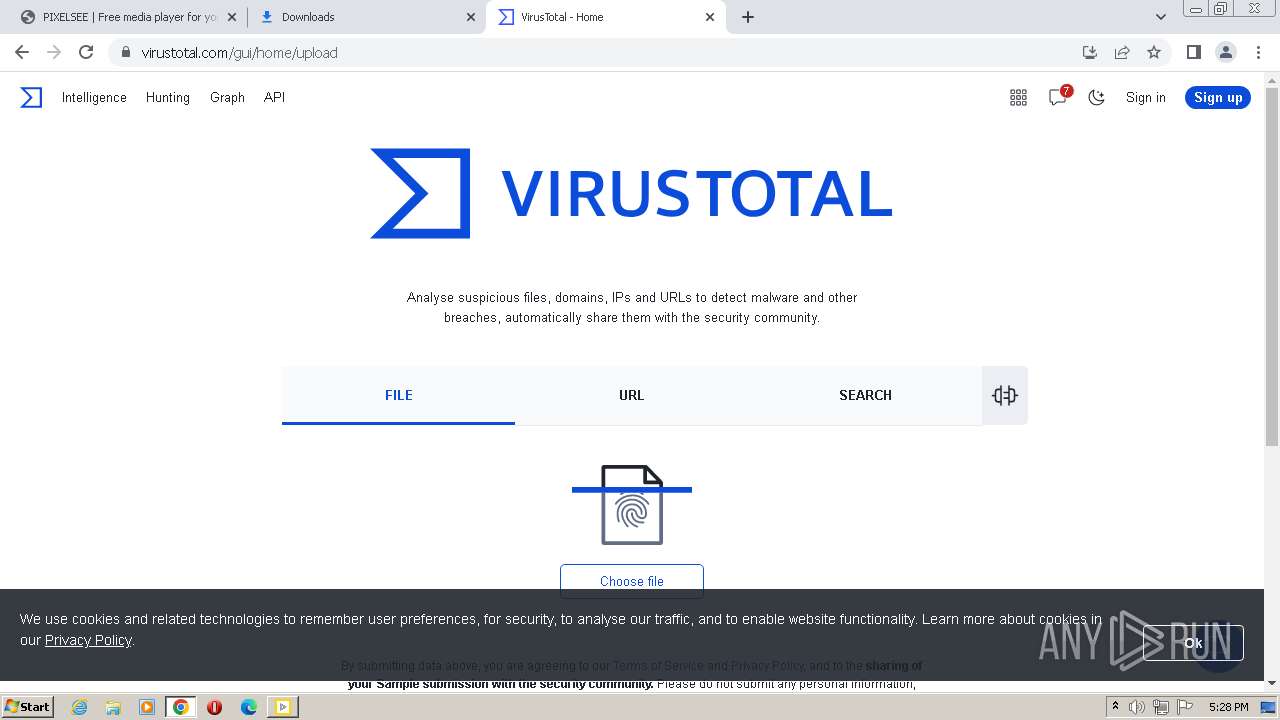
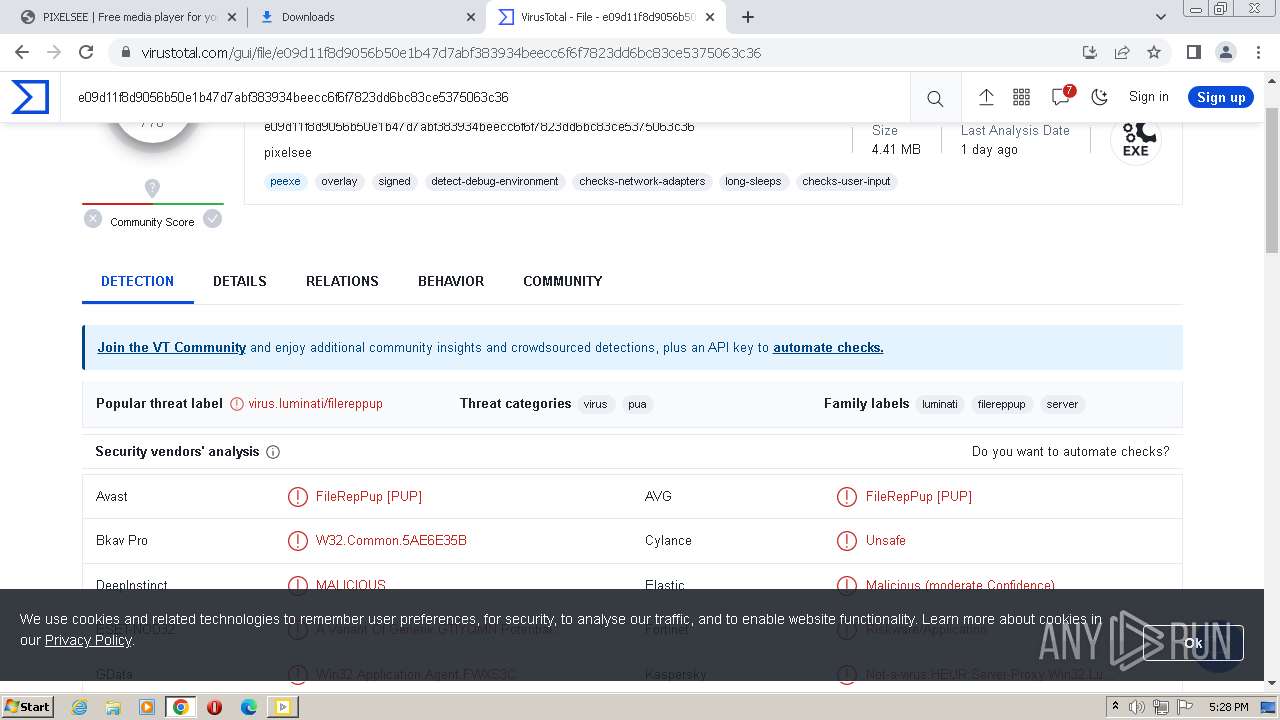
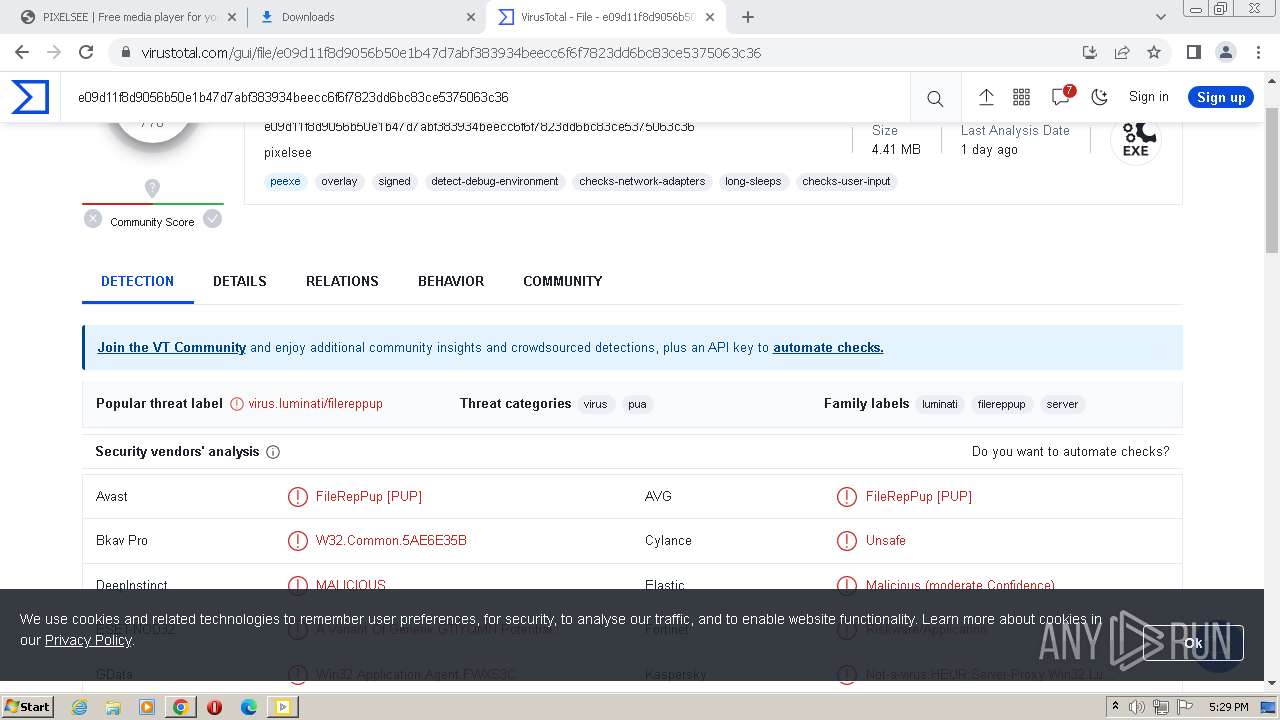
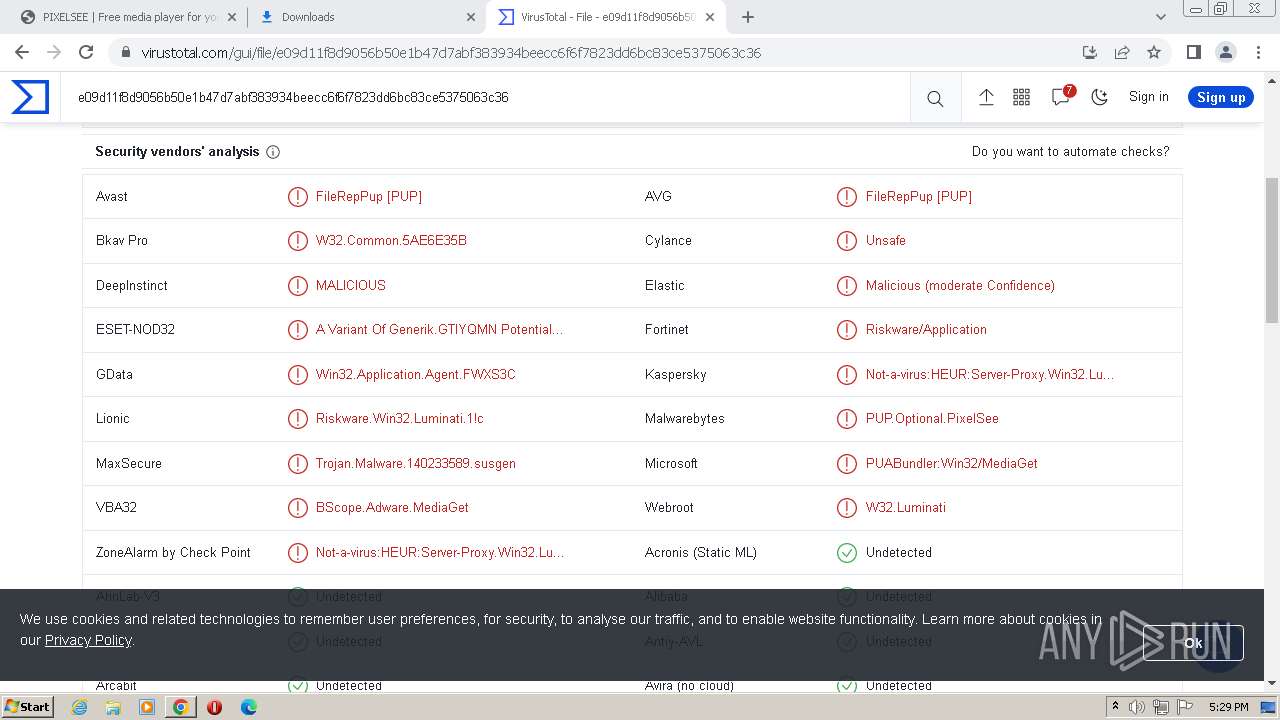
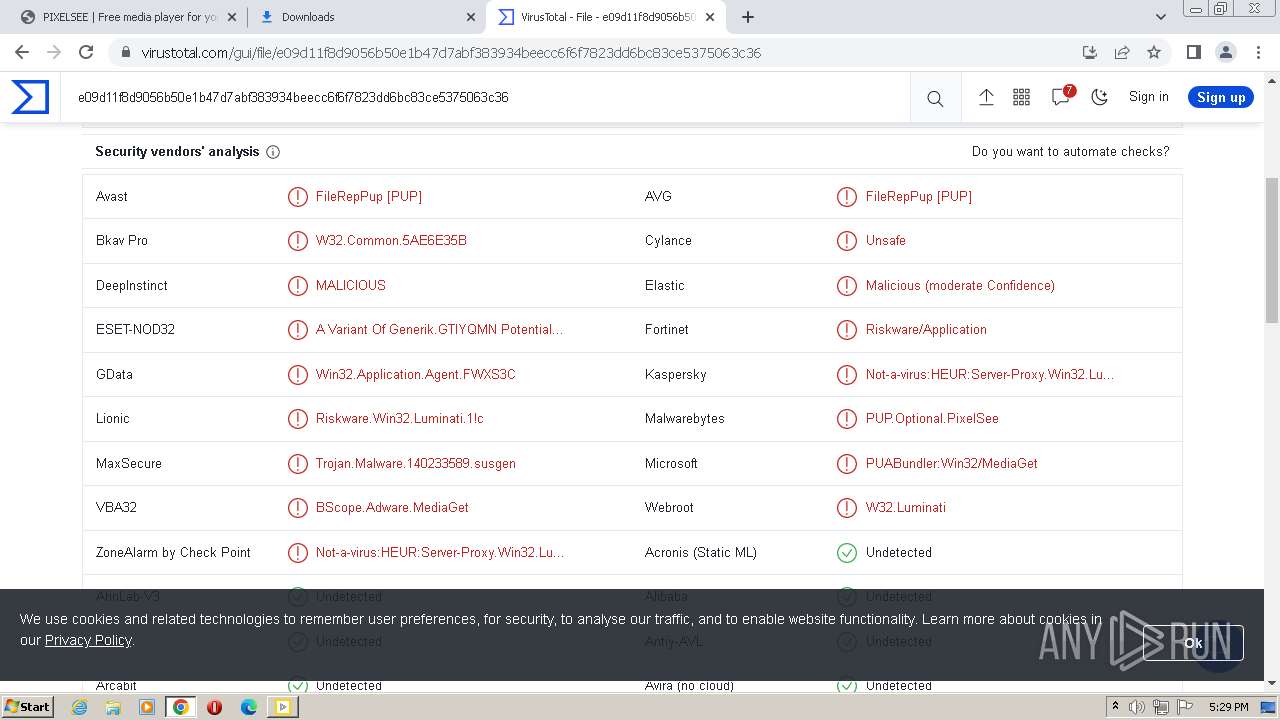
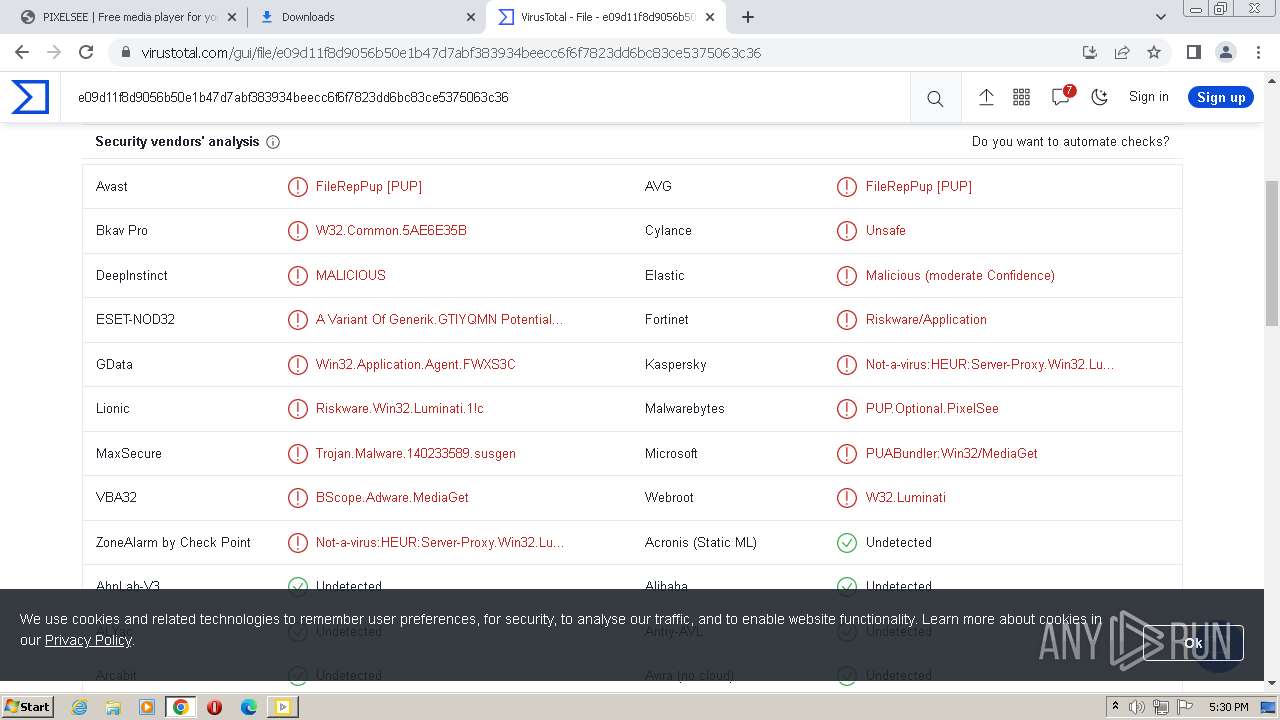
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | August 01, 2023, 16:26:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 13FCAC9610B48B0C2A40C0BFC33C8375 |
| SHA1: | 0C79753F5276387D29C79D0BBFBAF89146257B41 |
| SHA256: | 39B9A6F5D9975F0EE3898B0D13FC12BFC248D0C3912FBACD4E9C15827122B118 |
| SSDEEP: | 3:N8ISDKn:2IEKn |
MALICIOUS
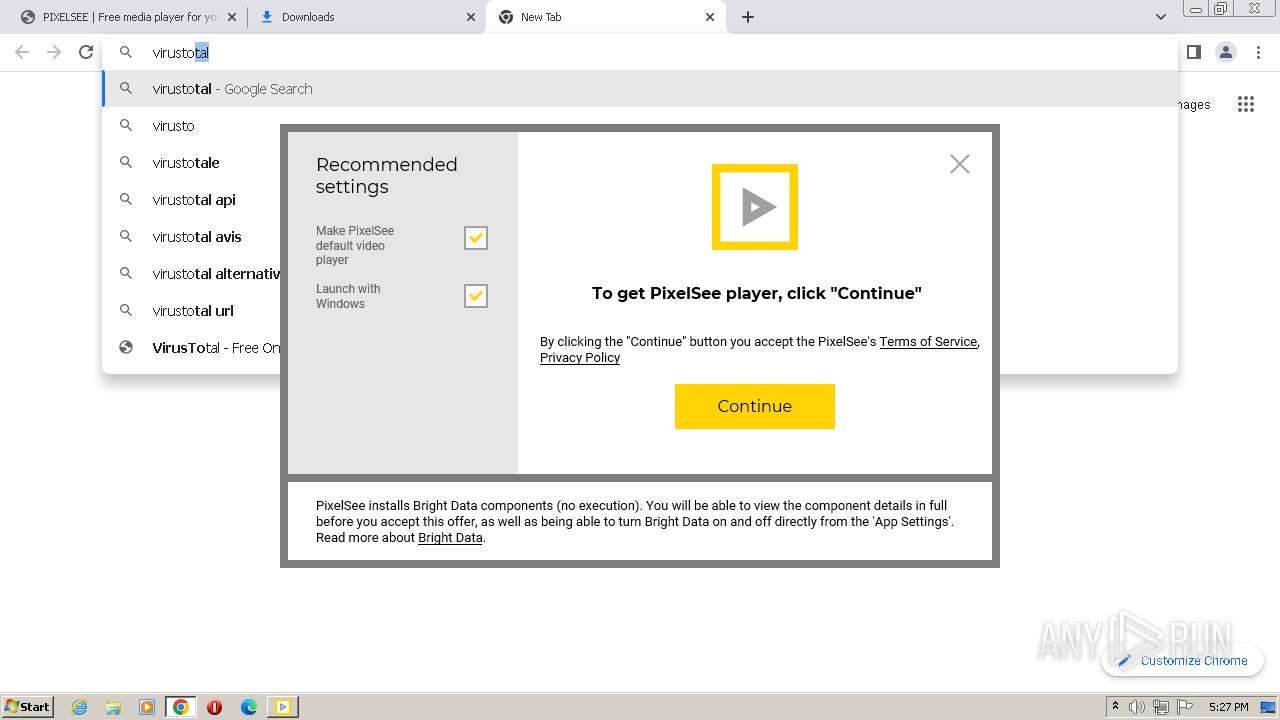
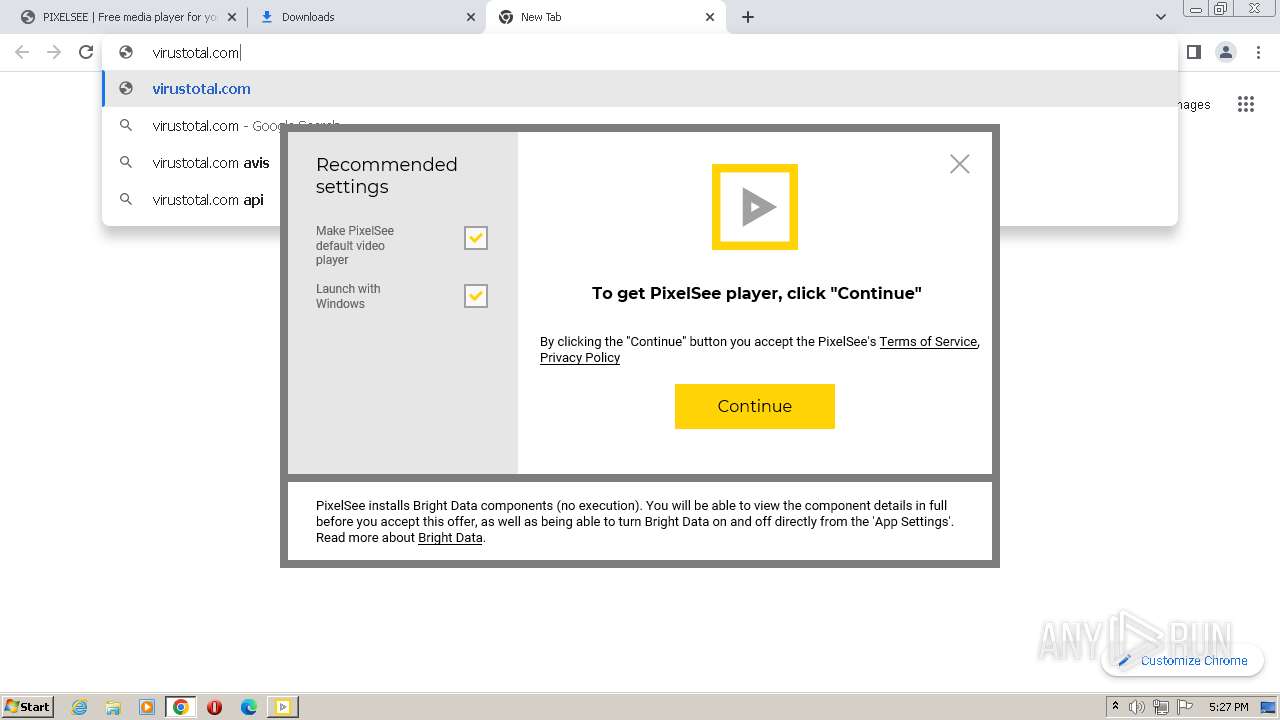
Application was dropped or rewritten from another process
- PixelSee_id2047878id.exe (PID: 980)
- PixelSee_id2047878id.exe (PID: 2580)
- lum_inst.exe (PID: 3120)
- net_updater32.exe (PID: 2240)
- net_updater32.exe (PID: 1412)
- pixelsee.exe (PID: 1572)
- pixelsee_crashpad_handler.exe (PID: 2084)
- QtWebEngineProcess.exe (PID: 3360)
- antivirus360.exe (PID: 3148)
Actions looks like stealing of personal data
- PixelSee_id2047878id.exe (PID: 2580)
- 360TS_Setup.exe (PID: 1660)
The DLL Hijacking
- SearchProtocolHost.exe (PID: 4036)
Loads dropped or rewritten executable
- net_updater32.exe (PID: 1412)
- pixelsee.exe (PID: 1572)
- pixelsee_crashpad_handler.exe (PID: 2084)
- QtWebEngineProcess.exe (PID: 3360)
- antivirus360.exe (PID: 3148)
- 360TS_Setup.exe (PID: 1392)
- 360TS_Setup.exe (PID: 1660)
SUSPICIOUS
Reads the Internet Settings
- PixelSee_id2047878id.exe (PID: 2580)
- lum_inst.tmp (PID: 3260)
- net_updater32.exe (PID: 1412)
- pixelsee.exe (PID: 1572)
- antivirus360.exe (PID: 3148)
- 360TS_Setup.exe (PID: 1660)
Reads Microsoft Outlook installation path
- PixelSee_id2047878id.exe (PID: 2580)
Reads Internet Explorer settings
- PixelSee_id2047878id.exe (PID: 2580)
Executable content was dropped or overwritten
- PixelSee_id2047878id.exe (PID: 2580)
- lum_inst.exe (PID: 3120)
- lum_inst.tmp (PID: 3260)
- net_updater32.exe (PID: 1412)
- antivirus360.exe (PID: 3148)
- 360TS_Setup.exe (PID: 1392)
- 360TS_Setup.exe (PID: 1660)
Application launched itself
- net_updater32.exe (PID: 2240)
Reads the Windows owner or organization settings
- lum_inst.tmp (PID: 3260)
Reads settings of System Certificates
- net_updater32.exe (PID: 1412)
- pixelsee.exe (PID: 1572)
- 360TS_Setup.exe (PID: 1660)
Checks Windows Trust Settings
- net_updater32.exe (PID: 1412)
- 360TS_Setup.exe (PID: 1660)
Reads security settings of Internet Explorer
- net_updater32.exe (PID: 1412)
- 360TS_Setup.exe (PID: 1660)
Detected use of alternative data streams (AltDS)
- net_updater32.exe (PID: 1412)
Adds/modifies Windows certificates
- net_updater32.exe (PID: 2240)
Process requests binary or script from the Internet
- PixelSee_id2047878id.exe (PID: 2580)
- antivirus360.exe (PID: 3148)
Starts itself from another location
- 360TS_Setup.exe (PID: 1392)
The process verifies whether the antivirus software is installed
- 360TS_Setup.exe (PID: 1660)
INFO
Checks supported languages
- PixelSee_id2047878id.exe (PID: 2580)
- lum_inst.exe (PID: 3120)
- net_updater32.exe (PID: 2240)
- lum_inst.tmp (PID: 3260)
- net_updater32.exe (PID: 1412)
- pixelsee.exe (PID: 1572)
- pixelsee_crashpad_handler.exe (PID: 2084)
- QtWebEngineProcess.exe (PID: 3360)
- antivirus360.exe (PID: 3148)
- 360TS_Setup.exe (PID: 1392)
- 360TS_Setup.exe (PID: 1660)
The process checks LSA protection
- PixelSee_id2047878id.exe (PID: 2580)
- lum_inst.tmp (PID: 3260)
- net_updater32.exe (PID: 1412)
- net_updater32.exe (PID: 2240)
- wisptis.exe (PID: 3608)
- pixelsee.exe (PID: 1572)
- QtWebEngineProcess.exe (PID: 3360)
- antivirus360.exe (PID: 3148)
- 360TS_Setup.exe (PID: 1392)
- 360TS_Setup.exe (PID: 1660)
Reads the computer name
- PixelSee_id2047878id.exe (PID: 2580)
- lum_inst.tmp (PID: 3260)
- net_updater32.exe (PID: 1412)
- pixelsee.exe (PID: 1572)
- QtWebEngineProcess.exe (PID: 3360)
- antivirus360.exe (PID: 3148)
- 360TS_Setup.exe (PID: 1392)
- 360TS_Setup.exe (PID: 1660)
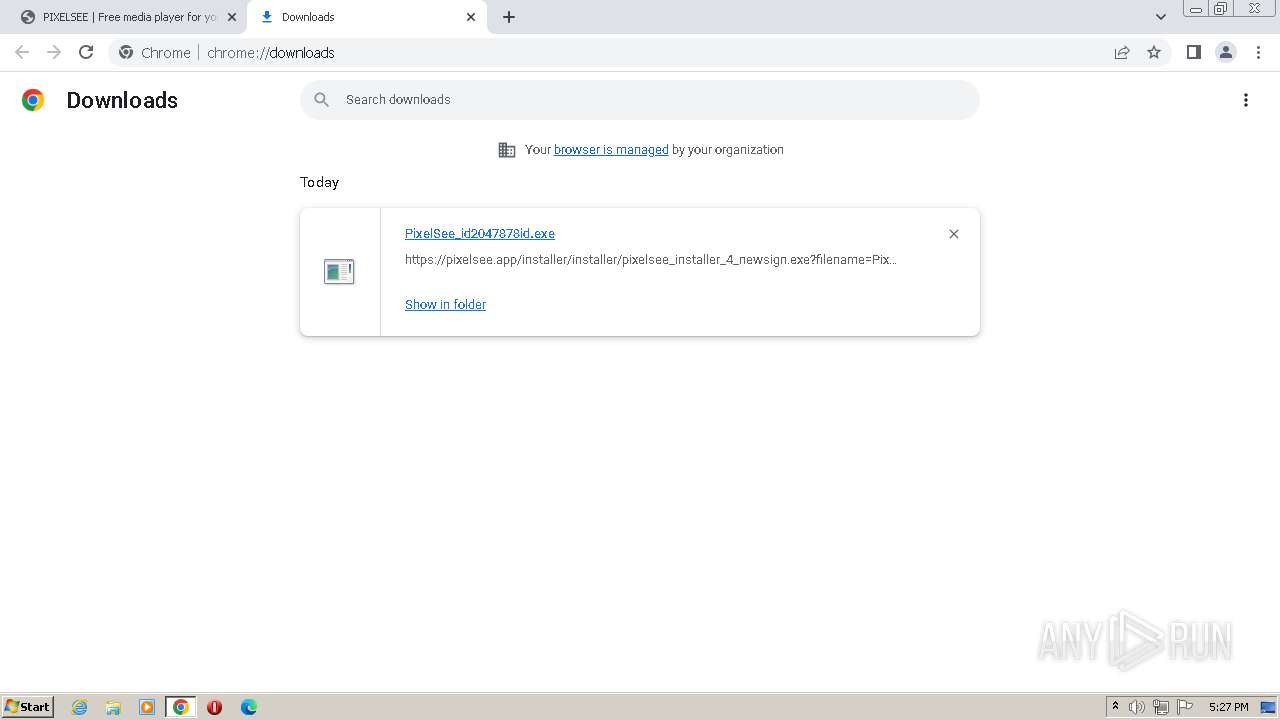
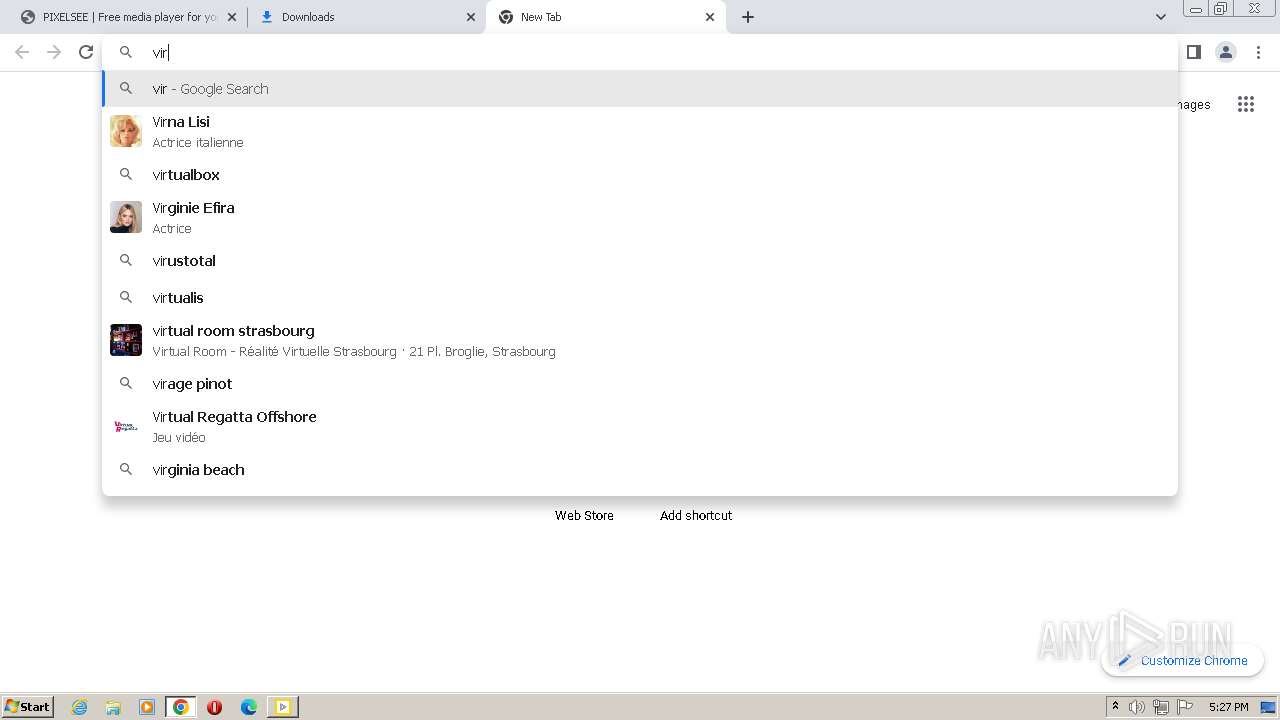
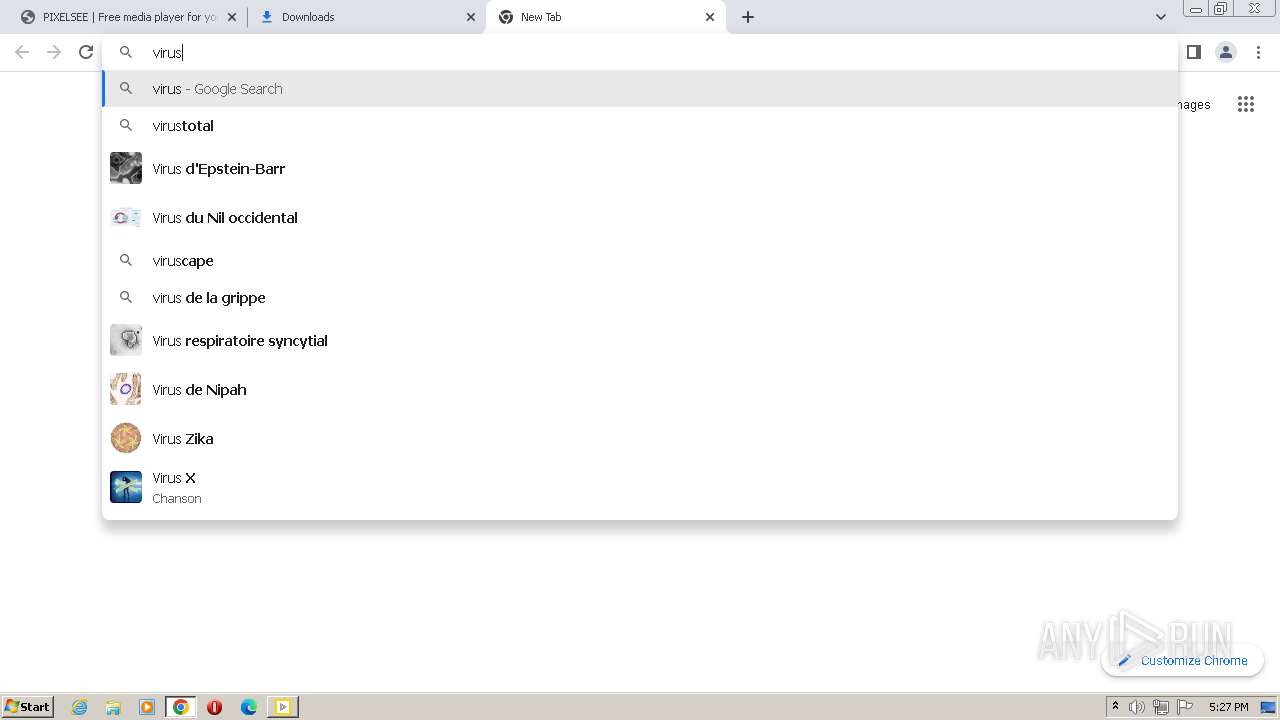
The process uses the downloaded file
- chrome.exe (PID: 1896)
- chrome.exe (PID: 1140)
- chrome.exe (PID: 3424)
- chrome.exe (PID: 1216)
Checks proxy server information
- PixelSee_id2047878id.exe (PID: 2580)
- net_updater32.exe (PID: 1412)
- antivirus360.exe (PID: 3148)
- 360TS_Setup.exe (PID: 1660)
Executable content was dropped or overwritten
- chrome.exe (PID: 1896)
Create files in a temporary directory
- PixelSee_id2047878id.exe (PID: 2580)
- lum_inst.exe (PID: 3120)
- antivirus360.exe (PID: 3148)
- 360TS_Setup.exe (PID: 1392)
- 360TS_Setup.exe (PID: 1660)
Reads the machine GUID from the registry
- PixelSee_id2047878id.exe (PID: 2580)
- net_updater32.exe (PID: 1412)
- pixelsee.exe (PID: 1572)
- antivirus360.exe (PID: 3148)
- 360TS_Setup.exe (PID: 1660)
Creates files or folders in the user directory
- PixelSee_id2047878id.exe (PID: 2580)
- net_updater32.exe (PID: 1412)
- pixelsee.exe (PID: 1572)
- QtWebEngineProcess.exe (PID: 3360)
- antivirus360.exe (PID: 3148)
- 360TS_Setup.exe (PID: 1660)
- pixelsee_crashpad_handler.exe (PID: 2084)
Application launched itself
- chrome.exe (PID: 1896)
Creates files in the program directory
- net_updater32.exe (PID: 1412)
- net_updater32.exe (PID: 2240)
- 360TS_Setup.exe (PID: 1392)
- 360TS_Setup.exe (PID: 1660)
Process checks computer location settings
- net_updater32.exe (PID: 1412)
- 360TS_Setup.exe (PID: 1660)
Application was dropped or rewritten from another process
- lum_inst.tmp (PID: 3260)
Reads Environment values
- net_updater32.exe (PID: 1412)
- pixelsee.exe (PID: 1572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
93
Monitored processes
47
Malicious processes
12
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3560 --field-trial-handle=1120,i,16696889174909232966,18016466755239570107,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
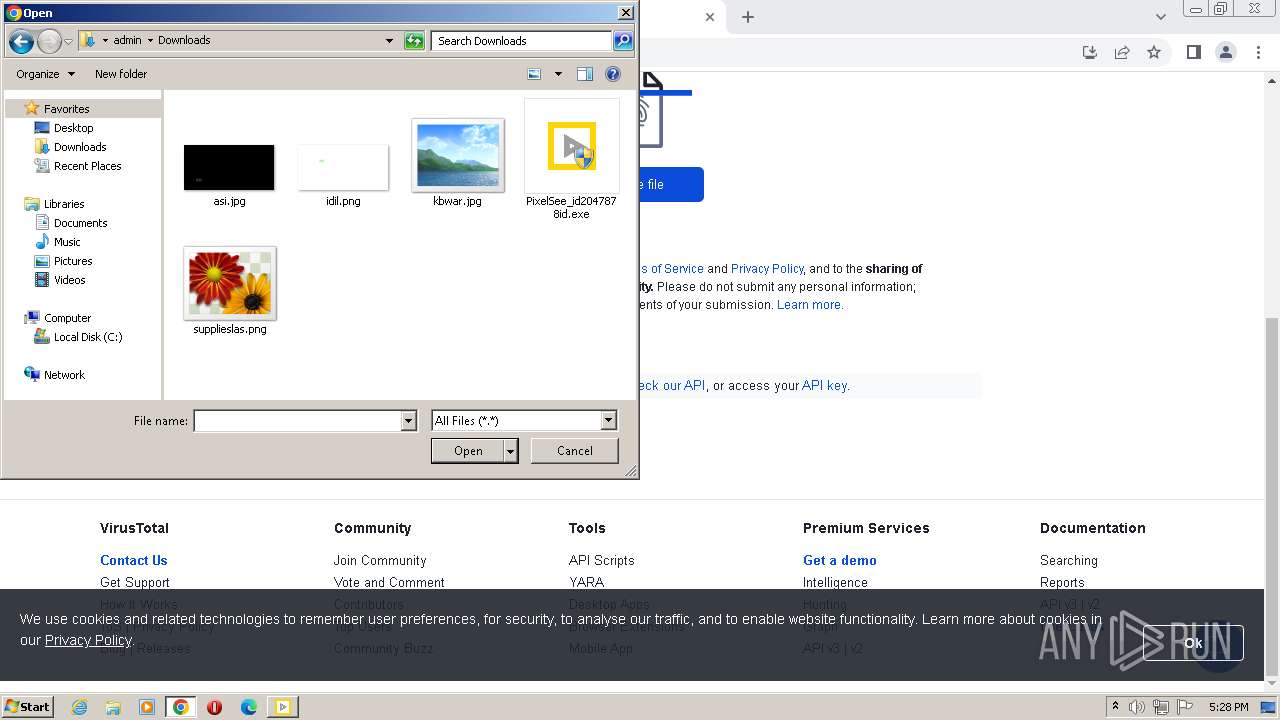
| 980 | "C:\Users\admin\Downloads\PixelSee_id2047878id.exe" | C:\Users\admin\Downloads\PixelSee_id2047878id.exe | — | chrome.exe | |||||||||||
User: admin Company: SIA Circle Solutions Integrity Level: MEDIUM Description: PixelSee Player Installer Exit code: 3221226540 Version: 12.0.0.0 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --mojo-platform-channel-handle=4288 --field-trial-handle=1120,i,16696889174909232966,18016466755239570107,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3188 --field-trial-handle=1120,i,16696889174909232966,18016466755239570107,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4068 --field-trial-handle=1120,i,16696889174909232966,18016466755239570107,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2040 --field-trial-handle=1120,i,16696889174909232966,18016466755239570107,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
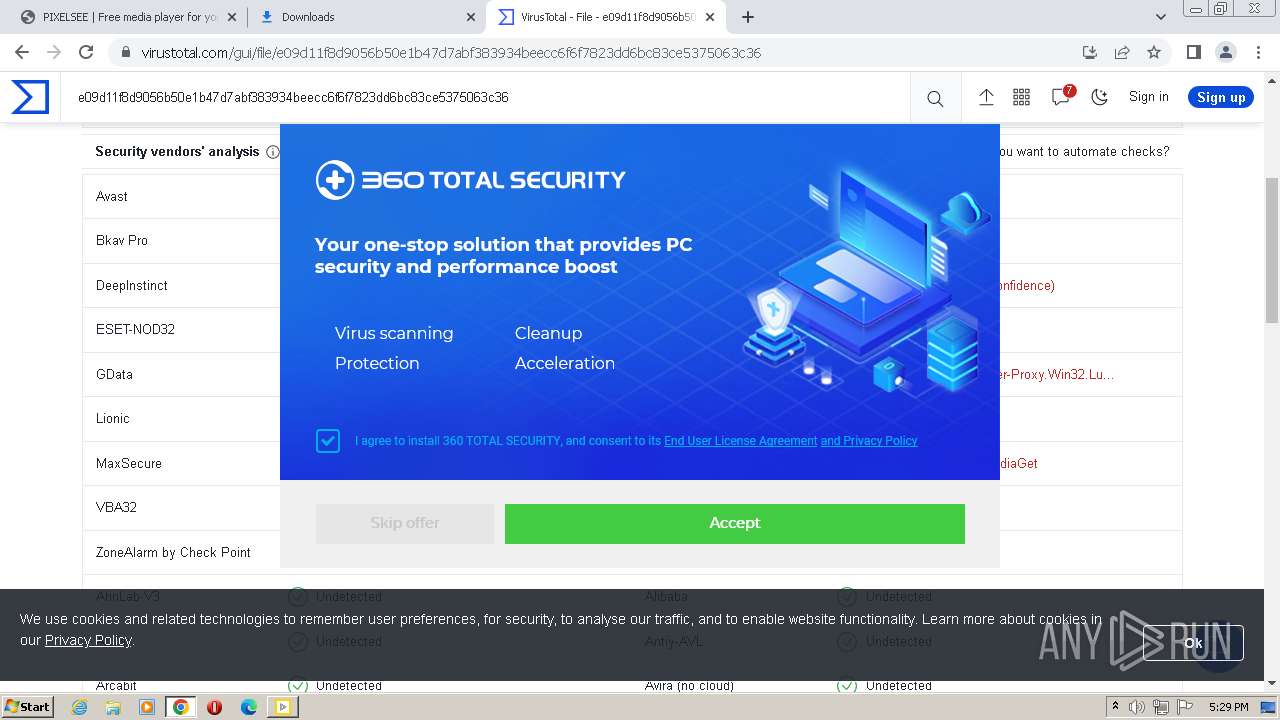
| 1392 | "C:\Users\admin\AppData\Local\Temp\antivirus360\360TS_Setup.exe" /c:WW.Mediaget.CPI202204 /pmode:2 /s /promo:eyJib290dGltZSI6IjciLCJtZWRhbCI6IjciLCJuZXdzIjoiMCIsIm9wZXJhIjoiNyIsIm9wZXJhX2lucyI6IjAiLCJwb3B1cCI6IjciLCJyZW1pbmRlciI6IjciLCJ1cGdyYWRlX25vdyI6IjAifQo= | C:\Users\admin\AppData\Local\Temp\antivirus360\360TS_Setup.exe | antivirus360.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Installer Module Exit code: 0 Version: 11,0,0,1028 Modules
| |||||||||||||||
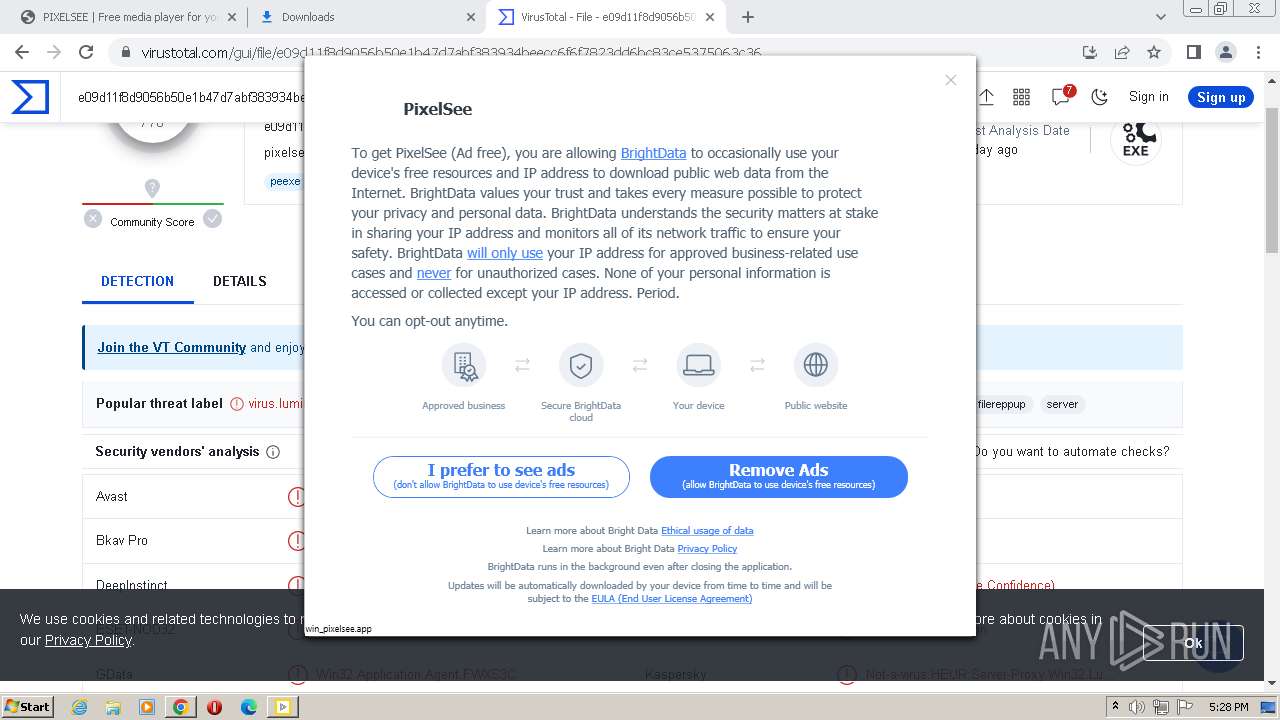
| 1412 | "C:\\Users\\admin\\PixelSee\\Luminati-m\\net_updater32.exe" --install-ui win_pixelsee.app --dlg-app-name PixelSee --dlg-tos-link https://pixelsee.app/license.html --dlg-benefit-txt "PixelSee (Ad free)" --dlg-logo-link https://pixelsee.app/installer/binaries/logo-icon.png --dlg-not-peer-txt ads --dlg-peer-txt remove_ads --fast | C:\Users\admin\PixelSee\Luminati-m\net_updater32.exe | net_updater32.exe | ||||||||||||
User: admin Company: BrightData Ltd. (certified) Integrity Level: HIGH Description: BrightData service allows free use of certain features in an app you installed Exit code: 2 Version: 1.379.314 Modules
| |||||||||||||||
| 1572 | "C:\Users\admin\PixelSee\pixelsee.exe" --installer | C:\Users\admin\PixelSee\pixelsee.exe | PixelSee_id2047878id.exe | ||||||||||||
User: admin Company: SIA Circle Solutions Integrity Level: HIGH Description: PixelSee Player Exit code: 0 Version: 12.0.0.0 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\1690907409_0\360TS_Setup.exe" /c:WW.Mediaget.CPI202204 /pmode:2 /s /promo:eyJib290dGltZSI6IjciLCJtZWRhbCI6IjciLCJuZXdzIjoiMCIsIm9wZXJhIjoiNyIsIm9wZXJhX2lucyI6IjAiLCJwb3B1cCI6IjciLCJyZW1pbmRlciI6IjciLCJ1cGdyYWRlX25vdyI6IjAifQo= /TSinstall | C:\Program Files\1690907409_0\360TS_Setup.exe | 360TS_Setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Installer Module Exit code: 0 Version: 11,0,0,1028 Modules
| |||||||||||||||
Total events
35 838
Read events
35 337
Write events
466
Delete events
35
Modification events
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (1896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
500
Suspicious files
606
Text files
359
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF466a5e.TMP | — | |
MD5:— | SHA256:— | |||
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF466a5e.TMP | text | |
MD5:CDCC923CEC2CD9228330551E6946A9C2 | SHA256:592F4750166BE662AA88728F9969537163FEC5C3E95E81537C8C6917F8D0929E | |||
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF46702a.TMP | — | |
MD5:— | SHA256:— | |||
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5727df01-499e-4263-8151-c5f9b61e67f0.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF466be4.TMP | text | |
MD5:BB9548F35E841C9C11626E490F597944 | SHA256:0BAF506A4A0BB37DC50395F36A451B3EF3F6D883615B864A7B50F8D064AAD12D | |||
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF46876b.TMP | — | |
MD5:— | SHA256:— | |||
| 1896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
162
DNS requests
97
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/bwz3vebv4a6glhoazexxdvgbfi_8149/hfnkpimlhhgieaddgfemjhofmfblmnib_8149_all_annfwlbl7g7xvzb23xslusnyhe.crx3 | US | — | — | whitelisted |
3148 | antivirus360.exe | GET | — | 104.192.108.19:80 | http://int.down.360safe.com/totalsecurity/360TS_Setup_11.0.0.1028.exe | US | — | — | malicious |
3148 | antivirus360.exe | GET | — | 104.192.108.17:80 | http://int.down.360safe.com/totalsecurity/360TS_Setup_11.0.0.1028.exe | US | — | — | malicious |
3148 | antivirus360.exe | GET | 200 | 52.29.179.141:80 | http://s.360safe.com/360ts/mini_inst.htm?ver=6.6.0.1054&pid=WW.Mediaget.CPI202204&os=6.1&mid=b8c075ec50c0ffb37ec9c97cc27794fb&state=153 | DE | — | — | suspicious |
3148 | antivirus360.exe | GET | — | 104.192.108.21:80 | http://int.down.360safe.com/totalsecurity/360TS_Setup_11.0.0.1028.exe | US | — | — | malicious |
3148 | antivirus360.exe | GET | 200 | 52.29.179.141:80 | http://s.360safe.com/safei18n/query_env.htm?v611=DgY0MAEI4uhtAgABAAA916gaFFx%2B%2BI8cUGG5v0L5N02EJgp6rem%2BVqV40sU1d2ZSpgltZHtQ9i%2BrIAaIXp1FtbbFMvAMtFYfvIcpwxEVXq0ecpc3AT4zcktITj7EA%2F32oyNplBszbY09wC1ka4%2BvBYzJMvVwwyZec8DTHUrqRP0mhOFwfSBPmy5nQZ0bYz4bu5Sx7GechQQ5d0zqeBzeuKxRyKkYOg608IVo6IIXj3Q6%2Bm1%2BYMWL%2Bs7kxrEGbfXXHoIiLsn9%2BLcu%2FTPycGcZLpGlGWpPQjmBCY7unhv6r5zkF%2Bm1R%2BoYCr7L9s8HGbih8ELGQ3He45Xw0mEW%2F9ukfm5vhvEs1FK176zC7pyweAmIwZpA2pMKJ43mCfJcIv1Rbd0NIWW292dg%2B1ff3aRtrC7Jmr3tn5FN2ETHKK%2FUwKVqxsj8myHxS%2BepuxadeQ%3D%3D | DE | — | — | suspicious |
3148 | antivirus360.exe | GET | — | 104.192.108.20:80 | http://int.down.360safe.com/totalsecurity/360TS_Setup_11.0.0.1028.exe | US | — | — | malicious |
3148 | antivirus360.exe | GET | — | 104.192.108.19:80 | http://int.down.360safe.com/totalsecurity/360TS_Setup_11.0.0.1028.exe | US | — | — | malicious |
3148 | antivirus360.exe | GET | 200 | 52.29.179.141:80 | http://s.360safe.com/safei18n/dimana.htm?lr=1&mid=b8c075ec50c0ffb37ec9c97cc27794fb&mod=360Installer.exe&ph=02a8342074eb25c8adb2d135e2bab7e5&p2p=1&t_id=360TS_Setup_For_Mini.cab&tads=652&tdl=652&tds=652&terr=0&tes=Status|1,ErrorCode|0,DnCount|6,HttpNum|1,DnFailCount|6,FStatus|1,P2SS|652,P2PS|0,PDMode|2&tfl=652&tp=t&tst=1&ttdl=652&ttm=1000&ttup=120&vh=1.3.0.1361&vp=1.3.0.1320&softname=360TS | DE | — | — | suspicious |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/khyuimaeoiymbe6yc4ayvc5mhq_660/efniojlnjndmcbiieegkicadnoecjjef_660_all_adznzx5neyehe6rpjntq7dumtxvq.crx3 | US | binary | 83.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2640 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3112 | chrome.exe | 142.250.184.205:443 | accounts.google.com | GOOGLE | US | whitelisted |
3112 | chrome.exe | 51.158.130.233:443 | pixelsee.app | Online S.a.s. | FR | suspicious |
1896 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3112 | chrome.exe | 142.250.184.227:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
3112 | chrome.exe | 157.240.0.6:443 | connect.facebook.net | FACEBOOK | US | whitelisted |
3112 | chrome.exe | 216.239.34.36:443 | region1.analytics.google.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
pixelsee.app |
| suspicious |
fonts.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
region1.analytics.google.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
www.google.fr |
| whitelisted |
connect.facebook.net |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1088 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
2580 | PixelSee_id2047878id.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3148 | antivirus360.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag false) |
3148 | antivirus360.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag true change port flag false) |
3148 | antivirus360.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag true) |
3148 | antivirus360.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
pixelsee.exe | QWindowsEGLStaticContext::create: Could not initialize EGL display: error 0x3001
|
pixelsee.exe | QWindowsEGLStaticContext::create: When using ANGLE, check if d3dcompiler_4x.dll is available
|
pixelsee.exe | > __thiscall Application::Application(int &,char *[])
|
pixelsee.exe | os version: "6.1.7601v" __ os name: "Windows 7 Version 6.1 (Build 7601: SP 1)"
|
pixelsee.exe | > int __thiscall Application::exec(void)
|
pixelsee.exe | > __thiscall PixelseeSettings::PixelseeSettings(void)
|
pixelsee.exe | INSTALL ID: "" _ OLD ID: ""
|
pixelsee.exe | > void __thiscall PixelseeSettings::flushSettings(void)
|
pixelsee.exe | reseller - "" installId ""
|
pixelsee.exe | main libvlc debug: searching plug-in modules
|