| File name: | cod_bo3.scr |
| Full analysis: | https://app.any.run/tasks/3f5dad89-f1a7-4764-820e-be02d57cb07d |
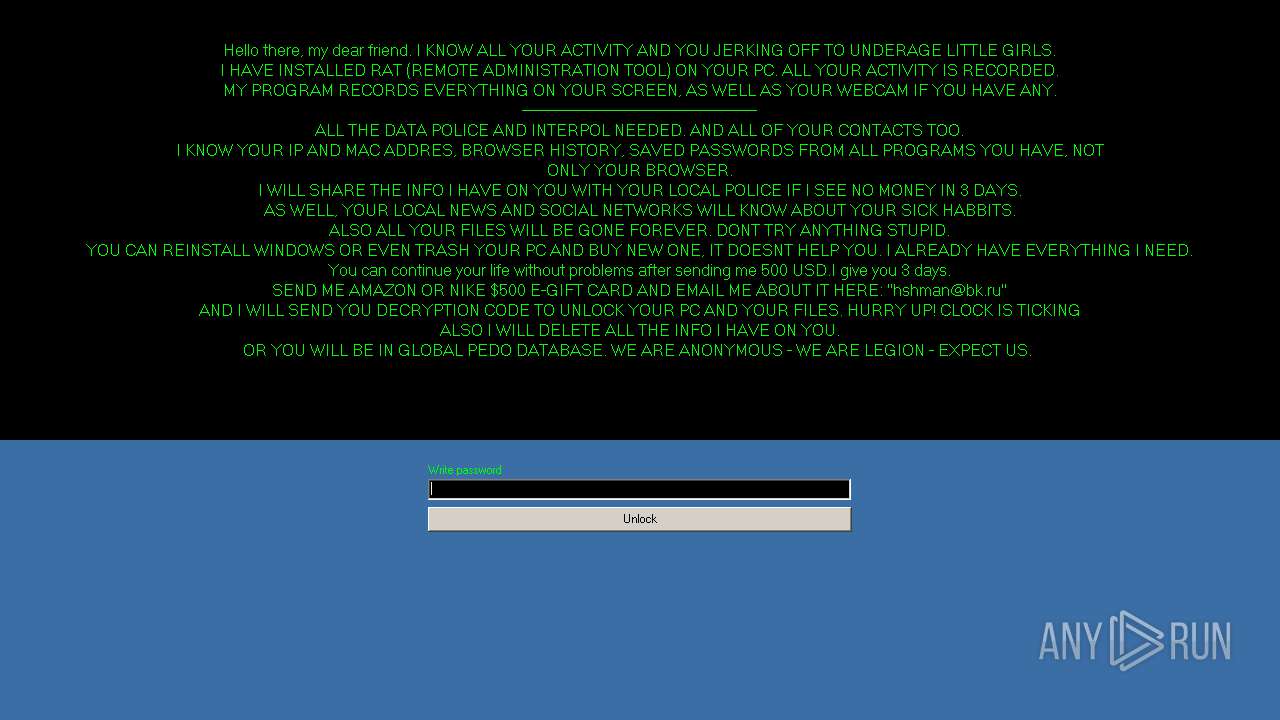
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 21:53:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 59BEB208586EE612E551E07CBA776306 |
| SHA1: | 5EA96859A6FA0853677F0C983BEB8B08BC71D87B |
| SHA256: | 39B91A48AF3F92AEED094C4368255D27C8F1185FE75D061C174524D3CCB676FE |
| SSDEEP: | 6144:UQl82ZBkPlFhoI/2xqE+Jk3i5GYNQPpgrJdJE3Ln9dXsuyMH7ZDR77/BZC5P/ZDl:z1ZBclFhtTE8DdN/TJE3sLSV7tZAR |
MALICIOUS
Changes the Startup folder
- Cobra.exe (PID: 2608)
Changes settings of System certificates
- Cobra.exe (PID: 2608)
SUSPICIOUS
Creates files in the program directory
- cod_bo3.scr (PID: 3352)
Executable content was dropped or overwritten
- cod_bo3.scr (PID: 3352)
Reads Internet Cache Settings
- Cobra.exe (PID: 2608)
Checks for external IP
- Cobra.exe (PID: 2608)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 308)
- cmd.exe (PID: 3508)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 3016)
- cmd.exe (PID: 3372)
- cmd.exe (PID: 2380)
- cmd.exe (PID: 1168)
- cmd.exe (PID: 440)
- cmd.exe (PID: 2940)
- cmd.exe (PID: 3728)
- cmd.exe (PID: 3932)
- cmd.exe (PID: 3972)
- cmd.exe (PID: 1412)
- cmd.exe (PID: 3248)
- cmd.exe (PID: 4036)
- cmd.exe (PID: 3420)
- cmd.exe (PID: 3872)
- cmd.exe (PID: 880)
- cmd.exe (PID: 1600)
- cmd.exe (PID: 3232)
- cmd.exe (PID: 2528)
- cmd.exe (PID: 2908)
- cmd.exe (PID: 2556)
- cmd.exe (PID: 2588)
- cmd.exe (PID: 2856)
- cmd.exe (PID: 2100)
- cmd.exe (PID: 2140)
- cmd.exe (PID: 1692)
- cmd.exe (PID: 3696)
- cmd.exe (PID: 3840)
- cmd.exe (PID: 3416)
- cmd.exe (PID: 1784)
- cmd.exe (PID: 2192)
- cmd.exe (PID: 2888)
- cmd.exe (PID: 2004)
- cmd.exe (PID: 1476)
- cmd.exe (PID: 2120)
- cmd.exe (PID: 1876)
- cmd.exe (PID: 1632)
- cmd.exe (PID: 1024)
- cmd.exe (PID: 1872)
- cmd.exe (PID: 660)
- cmd.exe (PID: 2776)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 1480)
- cmd.exe (PID: 1392)
- cmd.exe (PID: 3336)
- cmd.exe (PID: 3832)
- cmd.exe (PID: 2828)
- cmd.exe (PID: 1320)
- cmd.exe (PID: 2972)
- cmd.exe (PID: 3820)
- cmd.exe (PID: 3976)
- cmd.exe (PID: 2084)
- cmd.exe (PID: 2076)
- cmd.exe (PID: 2220)
- cmd.exe (PID: 3616)
- cmd.exe (PID: 1336)
- cmd.exe (PID: 4052)
- cmd.exe (PID: 3744)
- cmd.exe (PID: 5824)
- cmd.exe (PID: 3560)
- cmd.exe (PID: 3924)
- cmd.exe (PID: 3276)
- cmd.exe (PID: 3452)
- cmd.exe (PID: 5856)
- cmd.exe (PID: 5948)
Starts CMD.EXE for commands execution
- Cobra.exe (PID: 2608)
Adds / modifies Windows certificates
- Cobra.exe (PID: 2608)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (66.4) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 6 (26.2) |
| .exe | | | Win32 EXE PECompact compressed (generic) (4.1) |
| .exe | | | Win32 Executable Delphi generic (1.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 446464 |
| InitializedDataSize: | 87552 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6de70 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.8.8 |
| ProductVersionNumber: | 1.4.8.8 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Russian |
| CharacterSet: | Windows, Cyrillic |
| CompanyName: | Microsoft Corporation |
| FileDescription: | File Manager Startup |
| FileVersion: | 1.4.8.8 |
| InternalName: | - |
| LegalCopyright: | Microsoft Corporation |
| LegalTrademarks: | Microsoft Corporation |
| OriginalFileName: | Cobra |
| ProductName: | - |
| ProductVersion: | 1.4.8.8 |
| Comments: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | File Manager Startup |
| FileVersion: | 1.4.8.8 |
| InternalName: | - |
| LegalCopyright: | Microsoft Corporation |
| LegalTrademarks: | Microsoft Corporation |
| OriginalFilename: | Cobra |
| ProductName: | - |
| ProductVersion: | 1.4.8.8 |
| Comments: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0006CEB8 | 0x0006D000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51333 |
DATA | 0x0006E000 | 0x00001C9C | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.39634 |
BSS | 0x00070000 | 0x00000EF9 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00071000 | 0x00002232 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.89081 |
.tls | 0x00074000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00075000 | 0x00000021 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.36551 |
.reloc | 0x00076000 | 0x00008A88 | 0x00008C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.62139 |
.rsrc | 0x0007F000 | 0x00008600 | 0x00008600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.73325 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.28295 | 796 | UNKNOWN | Russian - Russia | RT_VERSION |
2 | 2.80231 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
3 | 3.00046 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4 | 2.56318 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4074 | 2.39137 | 120 | UNKNOWN | UNKNOWN | RT_STRING |
4075 | 3.23981 | 912 | UNKNOWN | UNKNOWN | RT_STRING |
4076 | 3.22996 | 996 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
wininet.dll |
Total processes
317
Monitored processes
181
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Windows\System32\cmd.exe" /k taskkill /f /im explorer.exe & exit | C:\Windows\System32\cmd.exe | — | Cobra.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 332 | taskkill /f /im explorer.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 440 | "C:\Windows\System32\cmd.exe" /k taskkill /f /im explorer.exe & exit | C:\Windows\System32\cmd.exe | — | Cobra.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 620 | taskkill /f /im explorer.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 660 | "C:\Windows\System32\cmd.exe" /k taskkill /f /im explorer.exe & exit | C:\Windows\System32\cmd.exe | — | Cobra.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 848 | taskkill /f /im explorer.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 880 | "C:\Windows\System32\cmd.exe" /k taskkill /f /im explorer.exe & exit | C:\Windows\System32\cmd.exe | — | Cobra.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1024 | "C:\Windows\System32\cmd.exe" /k taskkill /f /im explorer.exe & exit | C:\Windows\System32\cmd.exe | — | Cobra.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1168 | "C:\Windows\System32\cmd.exe" /k taskkill /f /im explorer.exe & exit | C:\Windows\System32\cmd.exe | — | Cobra.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1296 | taskkill /f /im explorer.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 182
Read events
621
Write events
2 374
Delete events
1 187
Modification events
| (PID) Process: | (3352) cod_bo3.scr | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3352) cod_bo3.scr | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2608) Cobra.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders |
| Operation: | write | Name: | Startup |
Value: C:\ProgramData\Cobra | |||
| (PID) Process: | (2608) Cobra.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2608) Cobra.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2608) Cobra.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2608) Cobra.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2608) Cobra.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2608) Cobra.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2608) Cobra.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
4
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2608 | Cobra.exe | C:\Users\admin\AppData\Local\Temp\CabD0B6.tmp | — | |
MD5:— | SHA256:— | |||
| 2608 | Cobra.exe | C:\Users\admin\AppData\Local\Temp\TarD0B7.tmp | — | |
MD5:— | SHA256:— | |||
| 2608 | Cobra.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2A086B549E10905E818876E77D6B349 | der | |
MD5:— | SHA256:— | |||
| 2608 | Cobra.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | der | |
MD5:— | SHA256:— | |||
| 2608 | Cobra.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2A086B549E10905E818876E77D6B349 | binary | |
MD5:— | SHA256:— | |||
| 2608 | Cobra.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | binary | |
MD5:— | SHA256:— | |||
| 3352 | cod_bo3.scr | C:\ProgramData\Cobra\Cobra.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
4
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2608 | Cobra.exe | GET | 200 | 195.138.255.24:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | DE | der | 1.37 Kb | whitelisted |
2608 | Cobra.exe | GET | 200 | 54.235.220.229:80 | http://api.ipify.org/ | US | text | 13 b | shared |
2608 | Cobra.exe | GET | 200 | 195.138.255.16:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgPAlKDFmOROcYdKkShFZ3AtUQ%3D%3D | DE | der | 527 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2608 | Cobra.exe | 88.99.66.31:443 | ezstat.ru | Hetzner Online GmbH | DE | malicious |
2608 | Cobra.exe | 195.138.255.24:80 | isrg.trustid.ocsp.identrust.com | AS33891 Netzbetrieb GmbH | DE | whitelisted |
2608 | Cobra.exe | 195.138.255.16:80 | isrg.trustid.ocsp.identrust.com | AS33891 Netzbetrieb GmbH | DE | suspicious |
2608 | Cobra.exe | 54.235.220.229:80 | api.ipify.org | Amazon.com, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ipify.org |
| shared |
ezstat.ru |
| shared |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2608 | Cobra.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup api.ipify.org |
1 ETPRO signatures available at the full report