| URL: | https://www.purebasic.com/download.php |
| Full analysis: | https://app.any.run/tasks/c960b64f-824f-429b-9323-3dc01a0846eb |
| Verdict: | Malicious activity |
| Analysis date: | September 08, 2020, 08:48:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D3AE87B5EC82536A8966004485192092 |
| SHA1: | 12666927E24E26BAA532CAD0F1102303FBBB132D |
| SHA256: | 39ADDA5C91E7380184C411E5A3D7B479BA6E956AE943813E20D094C6A4C4693D |
| SSDEEP: | 3:N8DSLRkRKV:2OLSRKV |
MALICIOUS
Loads dropped or rewritten executable
- PureBasic.exe (PID: 3160)
- PureBasic.exe (PID: 604)
Application was dropped or rewritten from another process
- pbcompiler.exe (PID: 2900)
- PureBasic.exe (PID: 3160)
- PureBasic.exe (PID: 604)
- pbcompiler.exe (PID: 3884)
SUSPICIOUS
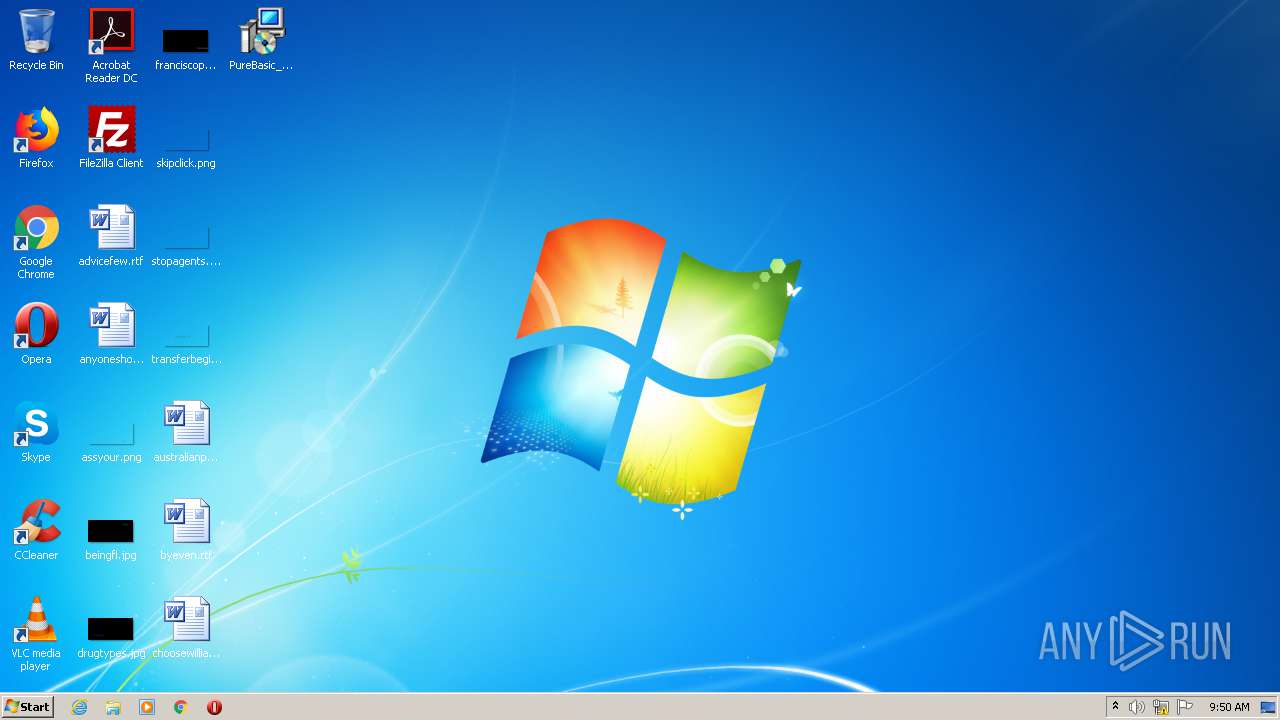
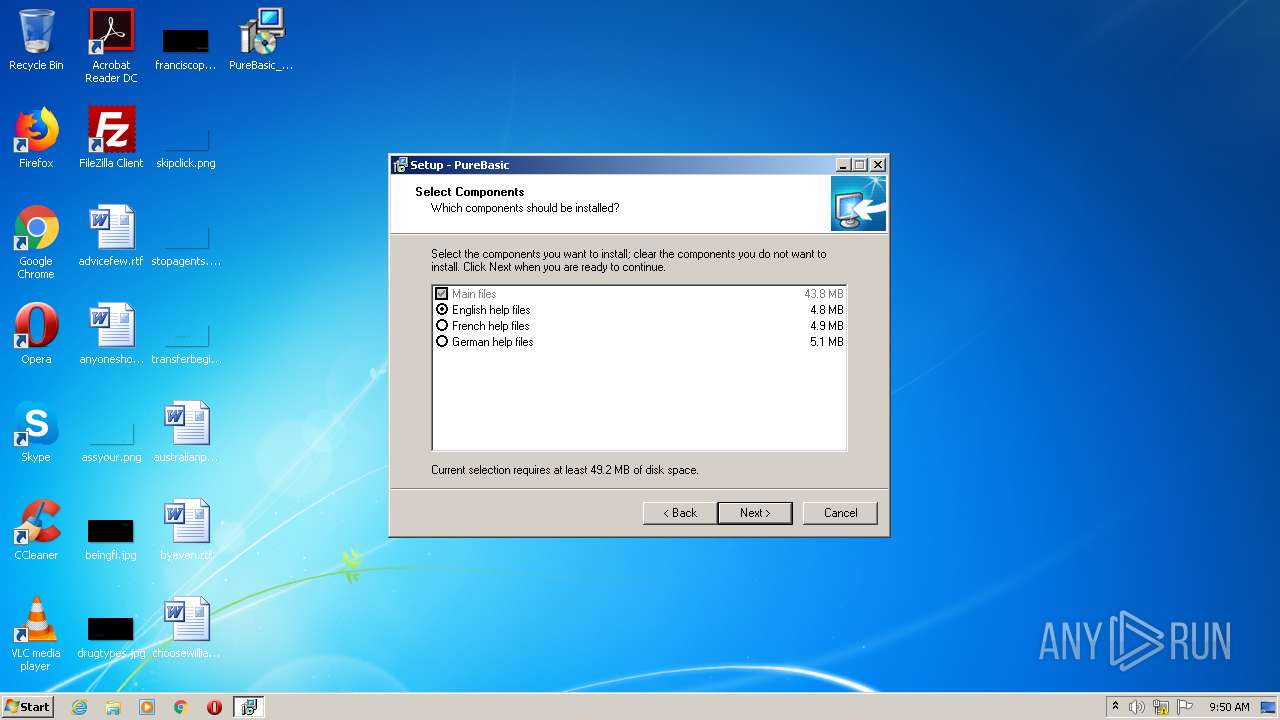
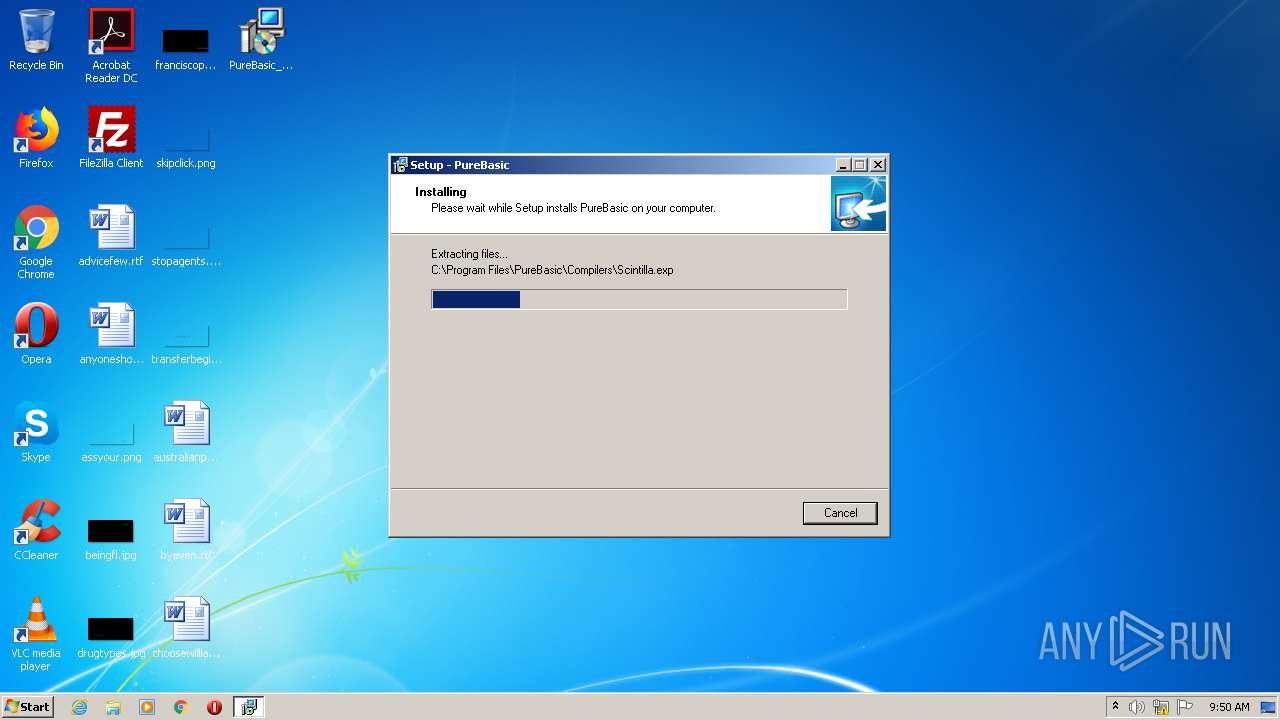
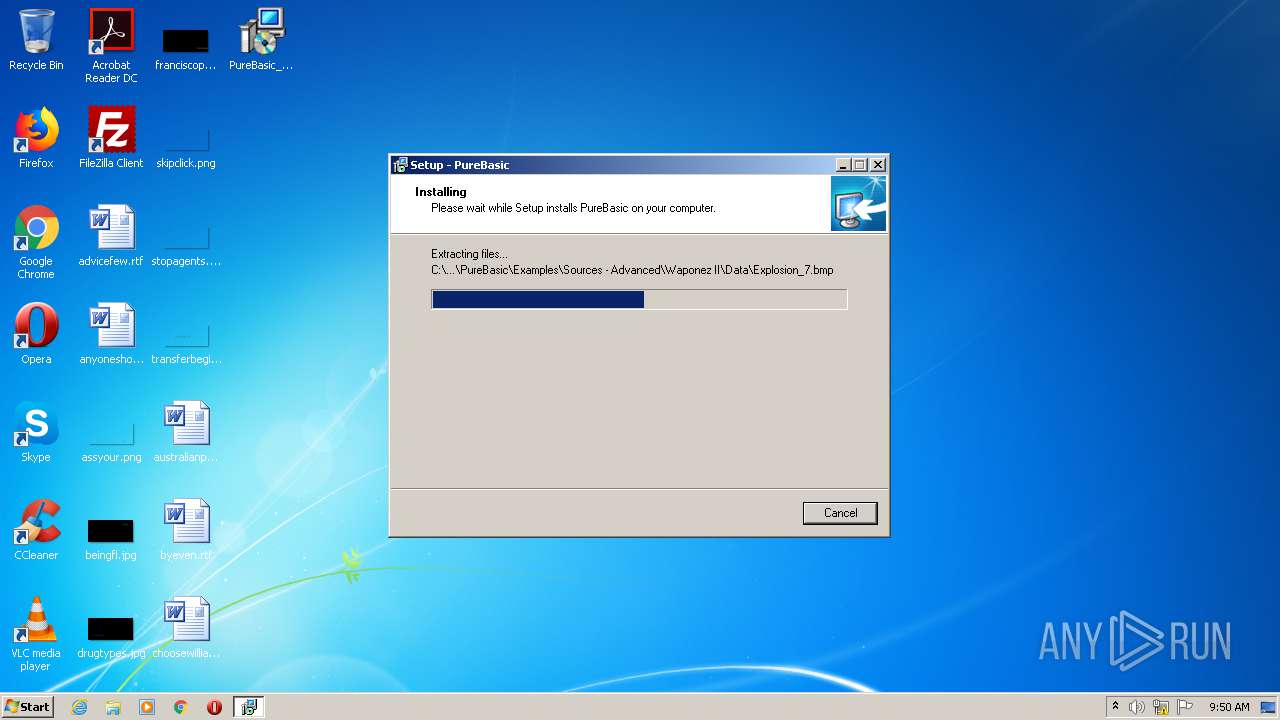
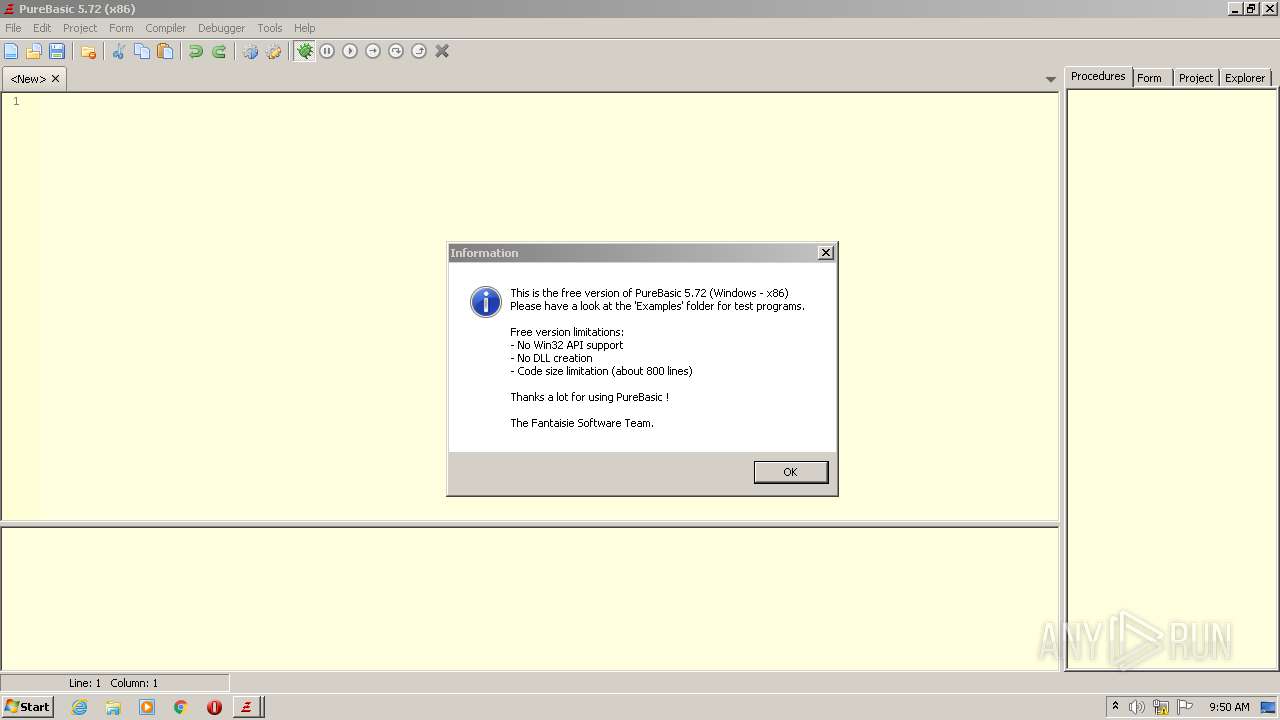
Executable content was dropped or overwritten
- PureBasic_Windows_5.72_X86_Demo.exe (PID: 1400)
- PureBasic_Windows_5.72_X86_Demo.exe (PID: 2744)
- PureBasic_Windows_5.72_X86_Demo.tmp (PID: 752)
Creates files in the Windows directory
- PureBasic_Windows_5.72_X86_Demo.tmp (PID: 752)
Modifies the open verb of a shell class
- PureBasic.exe (PID: 3160)
Creates files in the user directory
- PureBasic.exe (PID: 3160)
- PureBasic.exe (PID: 604)
INFO
Reads the hosts file
- chrome.exe (PID: 2420)
- chrome.exe (PID: 896)
Application launched itself
- chrome.exe (PID: 2420)
Reads Internet Cache Settings
- chrome.exe (PID: 2420)
Reads settings of System Certificates
- chrome.exe (PID: 896)
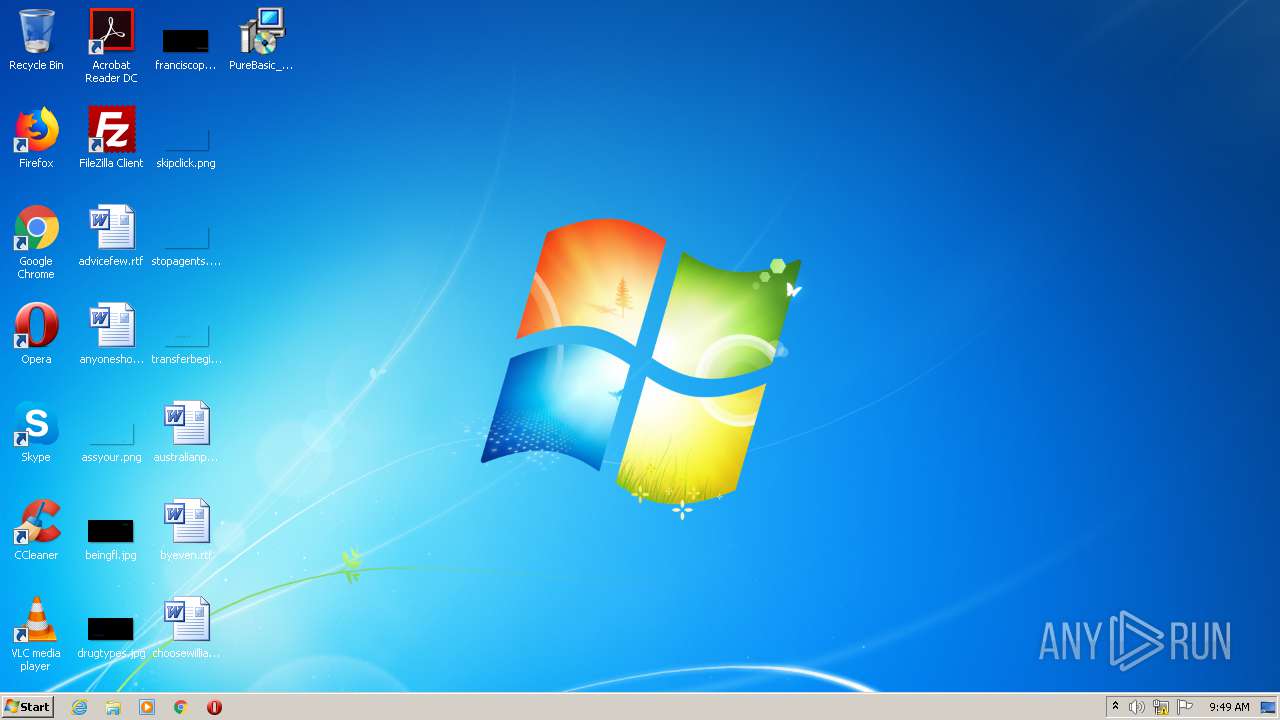
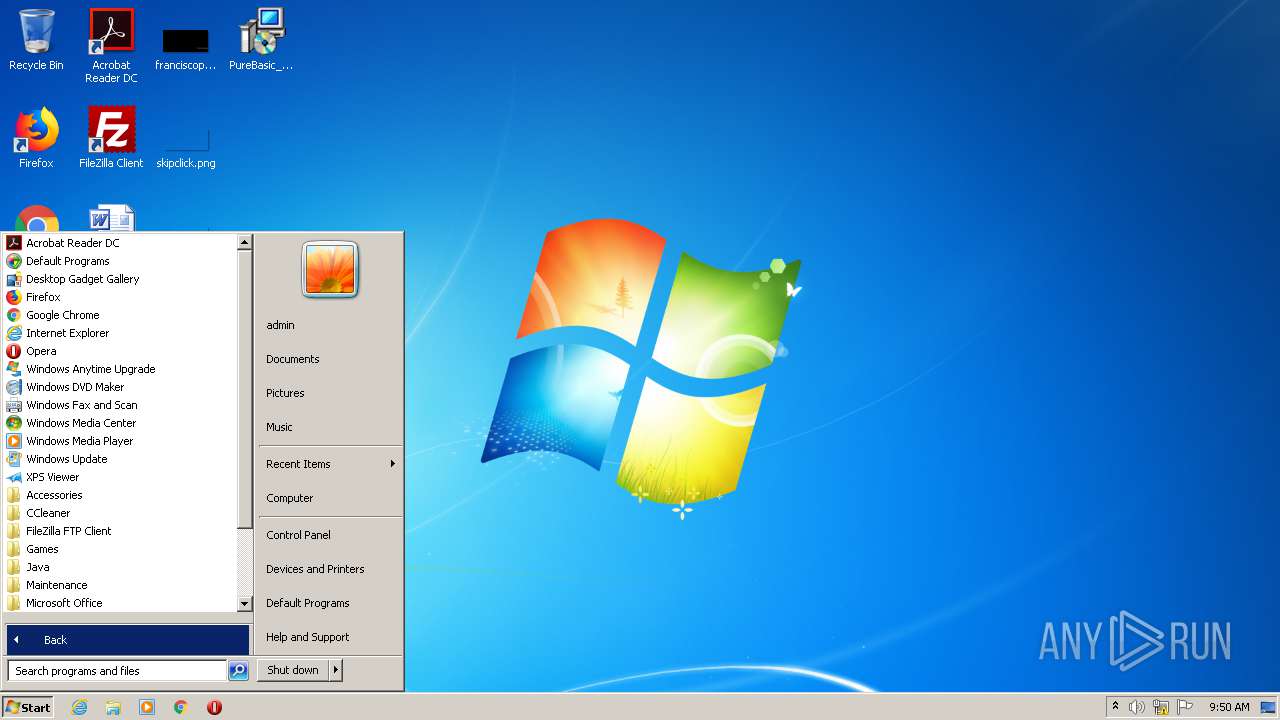
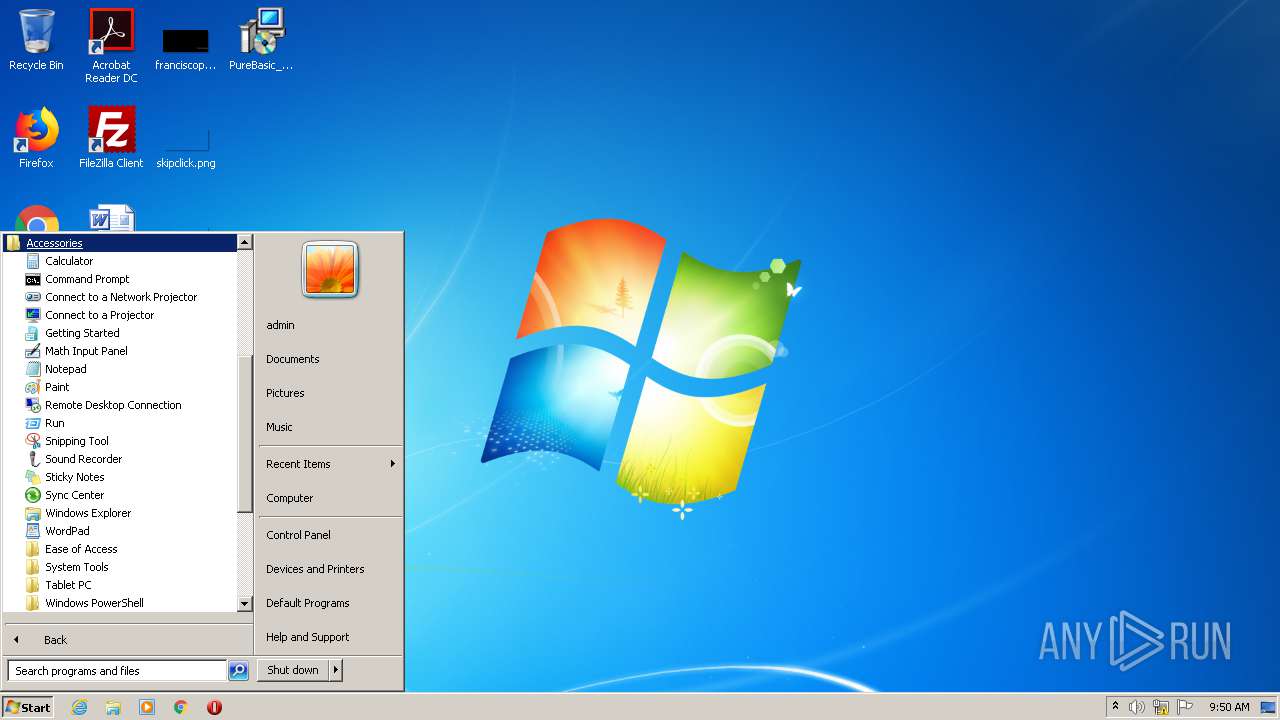
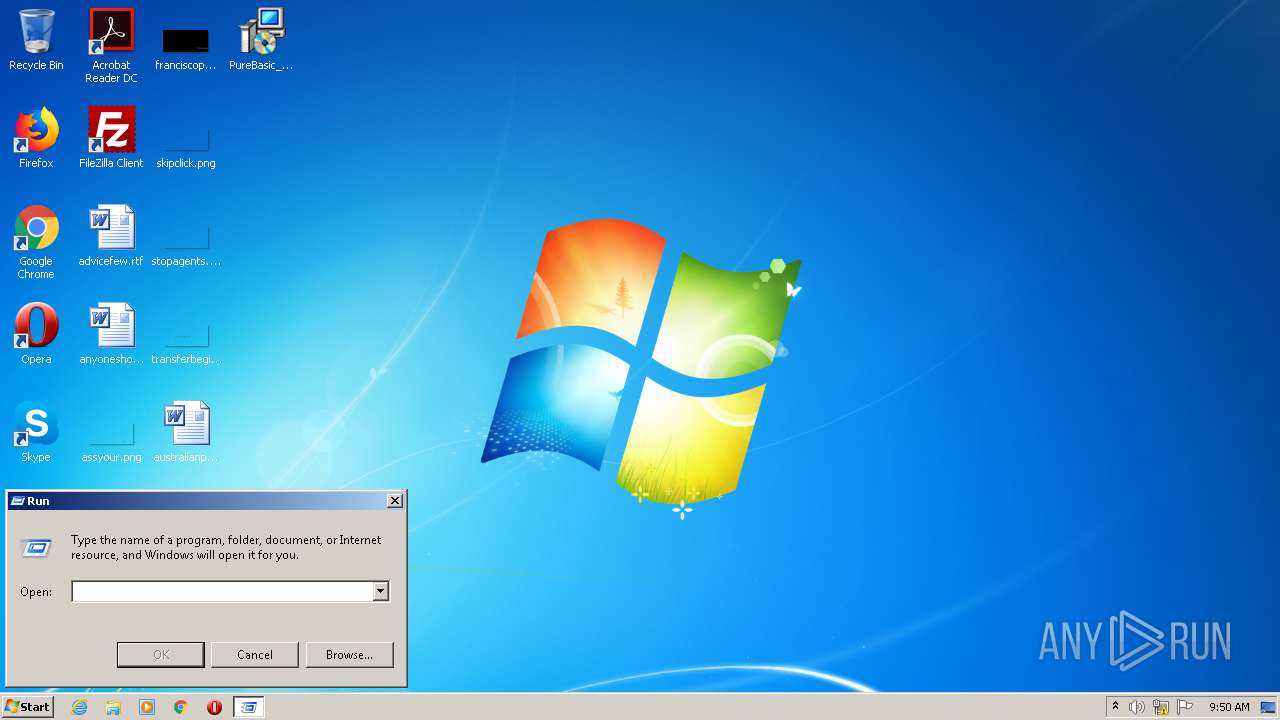
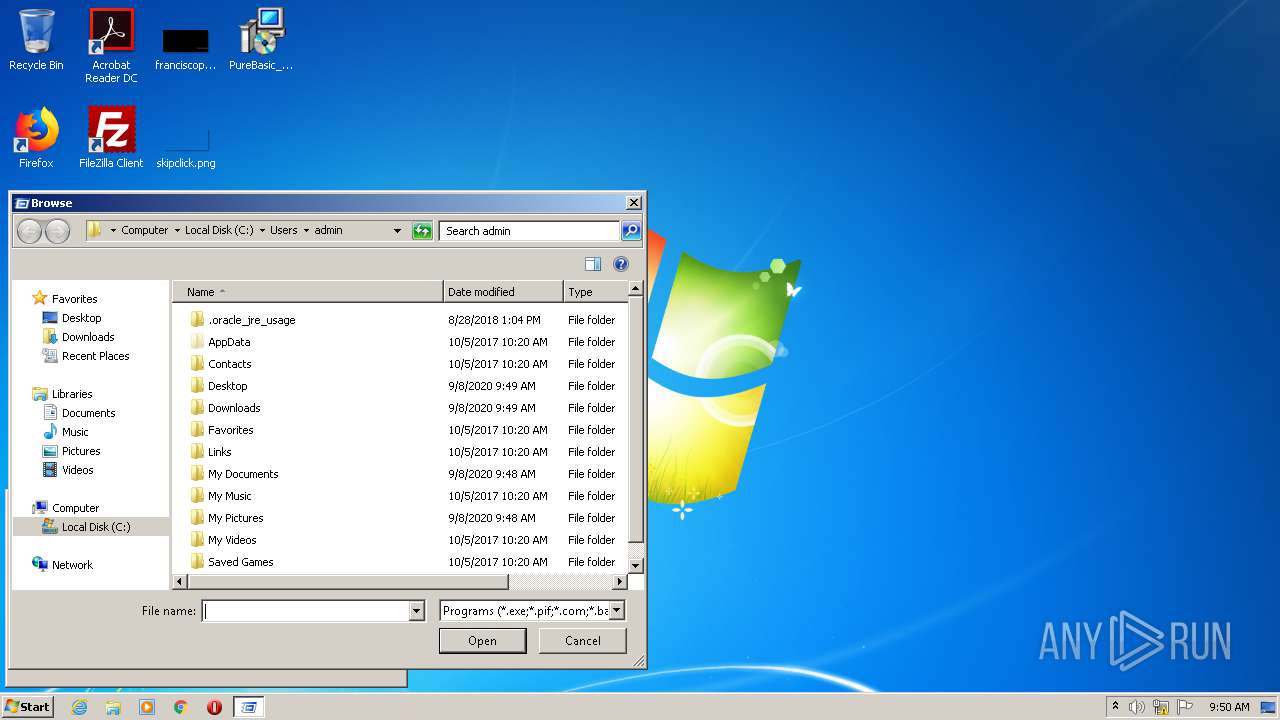
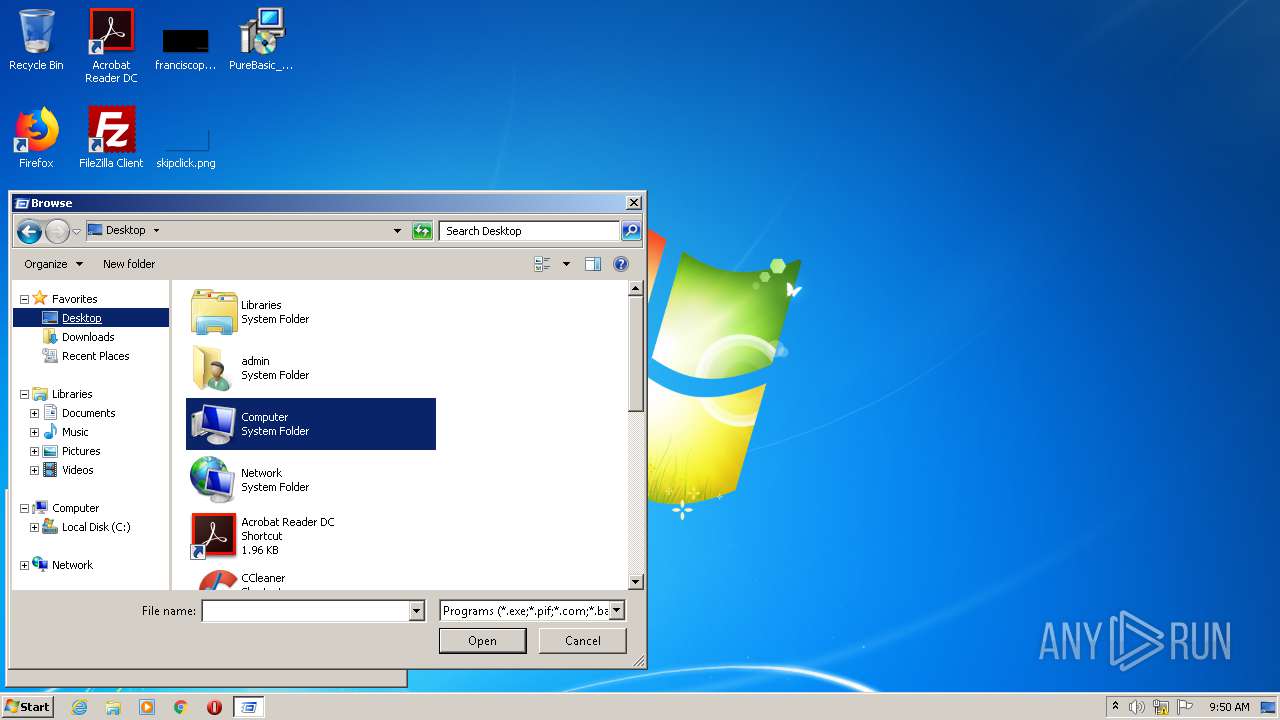
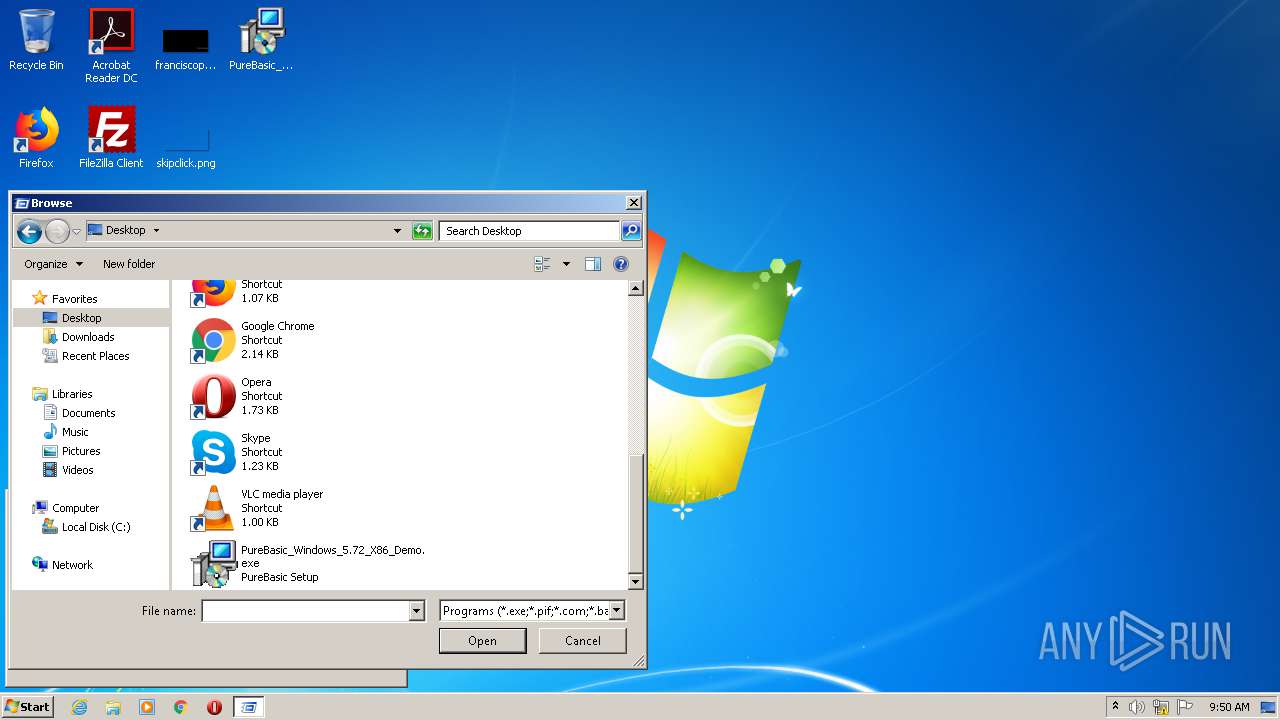
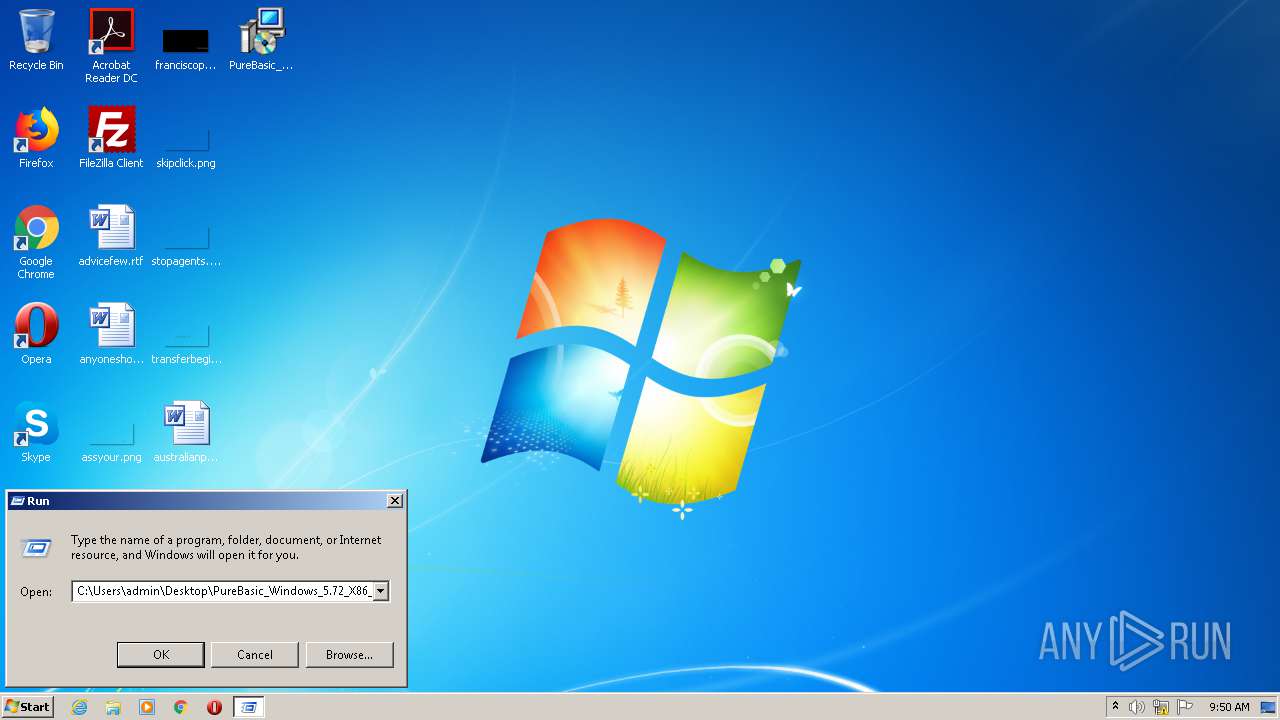
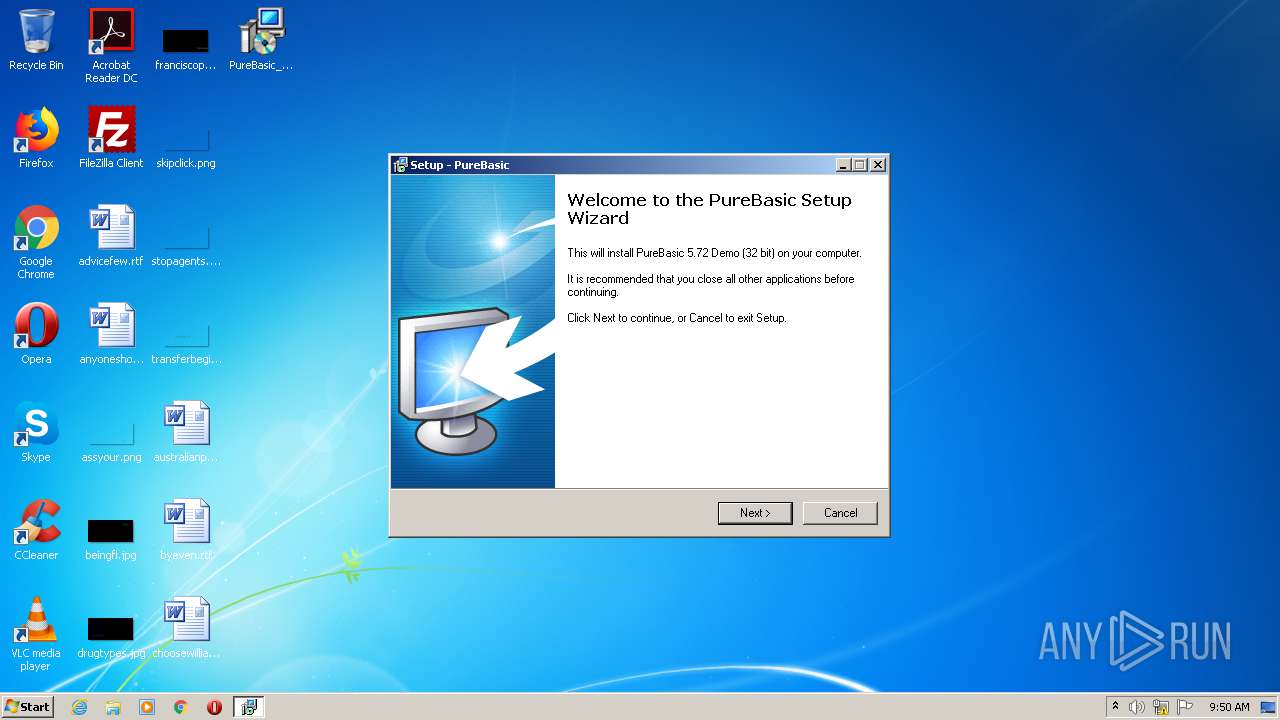
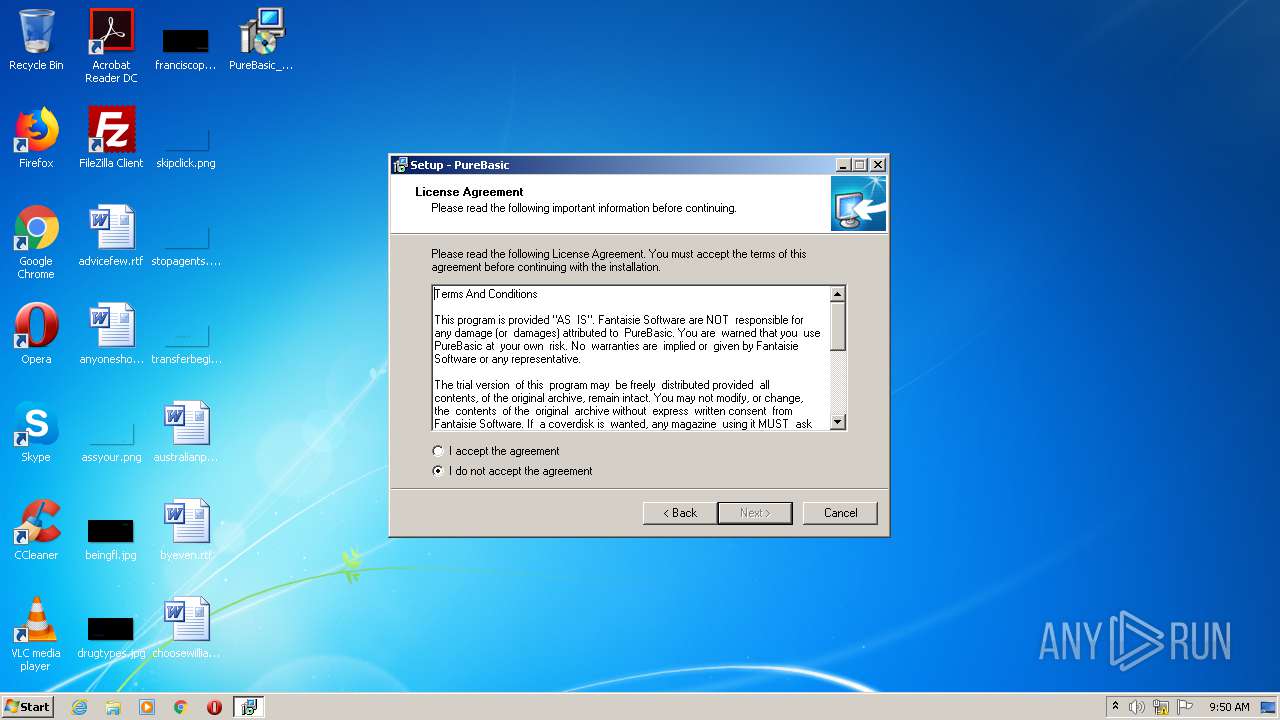
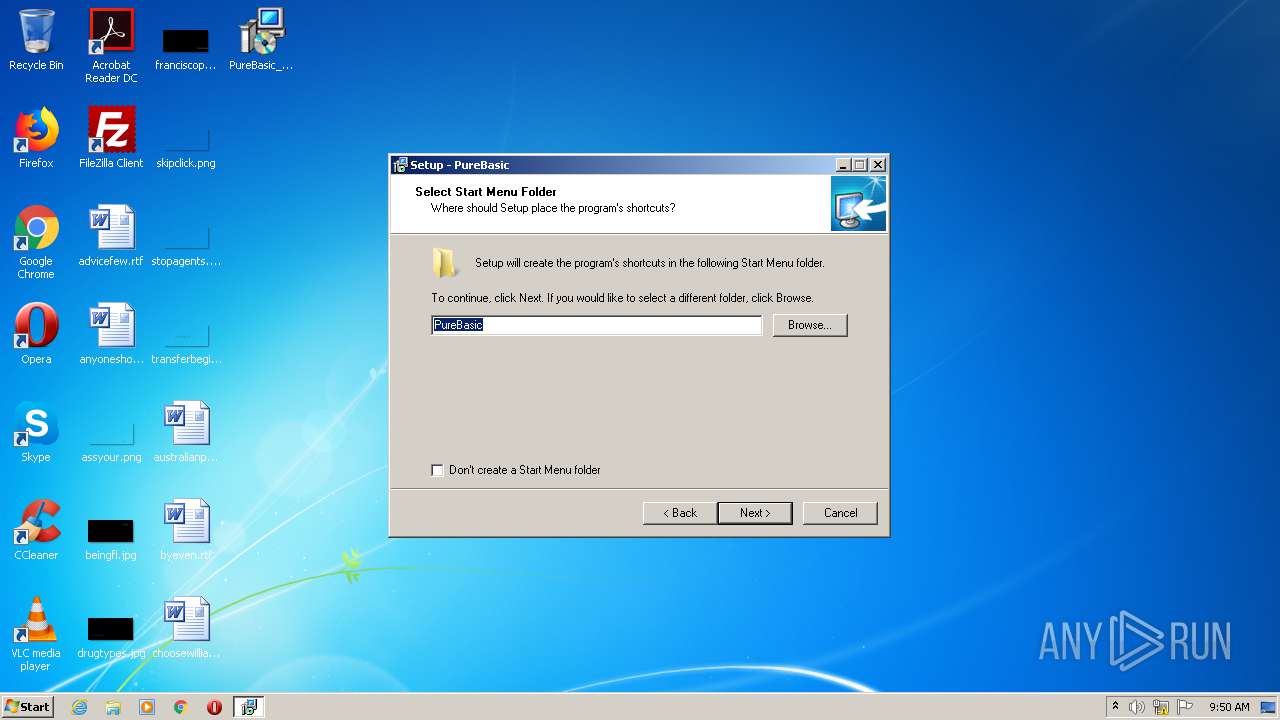
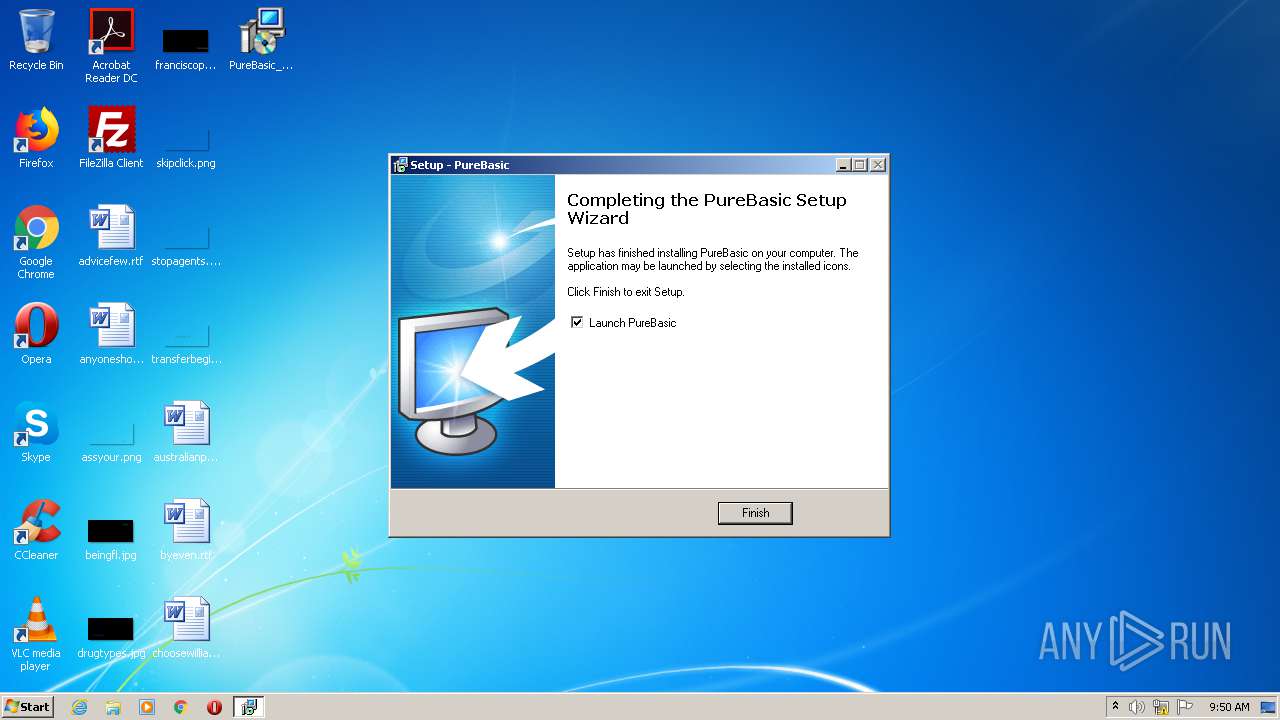
Manual execution by user
- PureBasic_Windows_5.72_X86_Demo.exe (PID: 2744)
- PureBasic.exe (PID: 604)
Loads dropped or rewritten executable
- PureBasic_Windows_5.72_X86_Demo.tmp (PID: 752)
Application was dropped or rewritten from another process
- PureBasic_Windows_5.72_X86_Demo.tmp (PID: 2748)
- PureBasic_Windows_5.72_X86_Demo.tmp (PID: 752)
Creates a software uninstall entry
- PureBasic_Windows_5.72_X86_Demo.tmp (PID: 752)
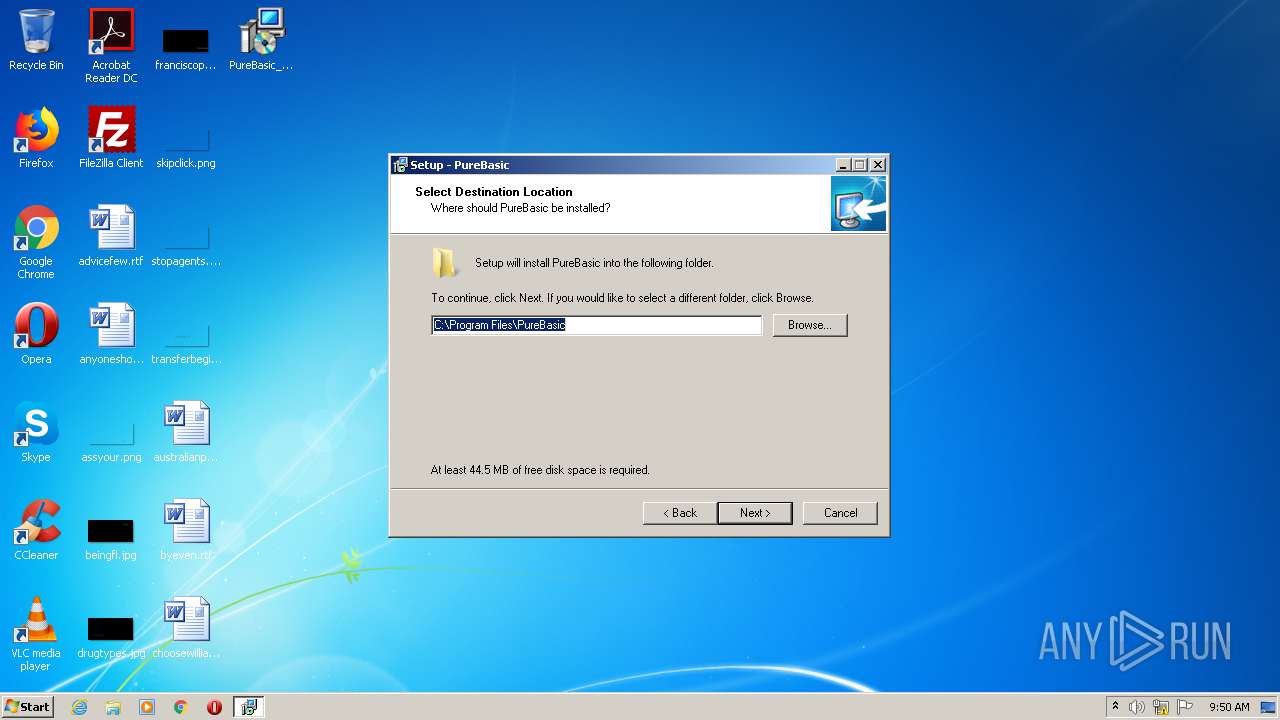
Creates files in the program directory
- PureBasic_Windows_5.72_X86_Demo.tmp (PID: 752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
21
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | "C:\Program Files\PureBasic\PureBasic.exe" | C:\Program Files\PureBasic\PureBasic.exe | — | explorer.exe | |||||||||||
User: admin Company: Fantaisie Software Integrity Level: MEDIUM Description: PureBasic Development Environment Exit code: 0 Modules
| |||||||||||||||
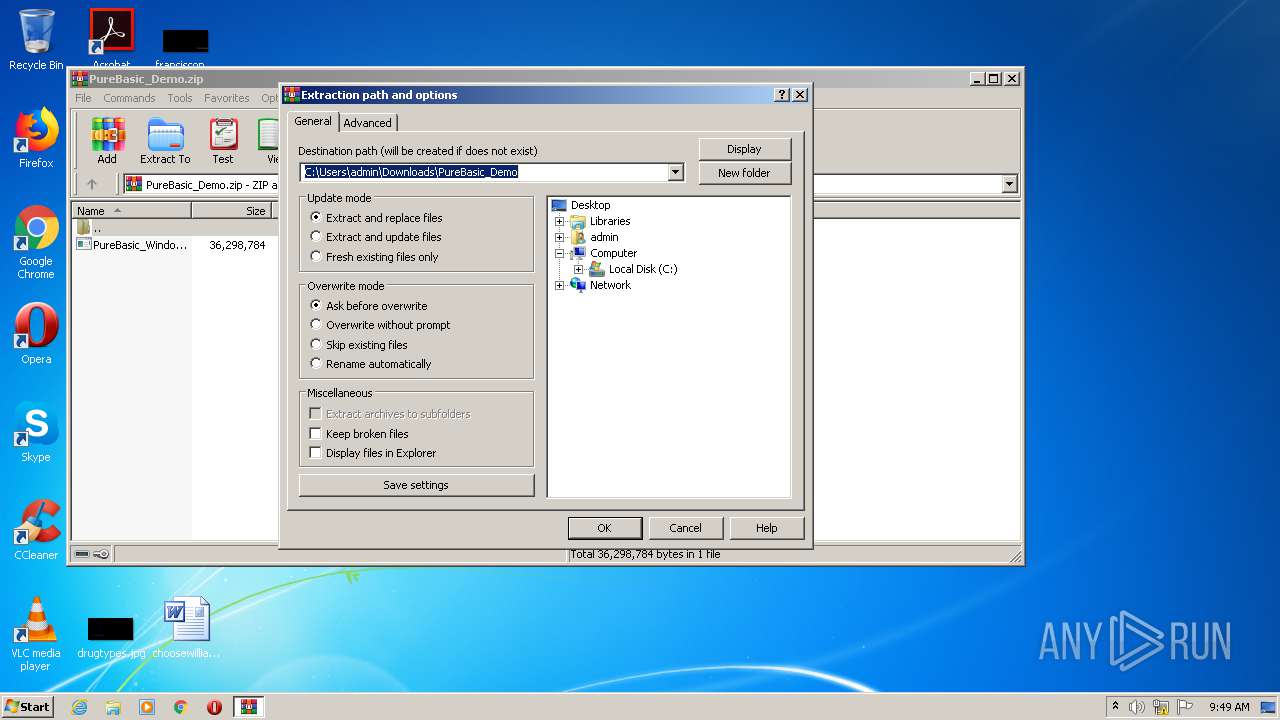
| 752 | "C:\Users\admin\AppData\Local\Temp\is-5R0FS.tmp\PureBasic_Windows_5.72_X86_Demo.tmp" /SL5="$7017E,36011372,53248,C:\Users\admin\Desktop\PureBasic_Windows_5.72_X86_Demo.exe" /SPAWNWND=$801CA /NOTIFYWND=$50140 | C:\Users\admin\AppData\Local\Temp\is-5R0FS.tmp\PureBasic_Windows_5.72_X86_Demo.tmp | PureBasic_Windows_5.72_X86_Demo.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.49.0.0 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,8055914640776217393,9842717125256522840,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6831402519990644025 --mojo-platform-channel-handle=1604 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
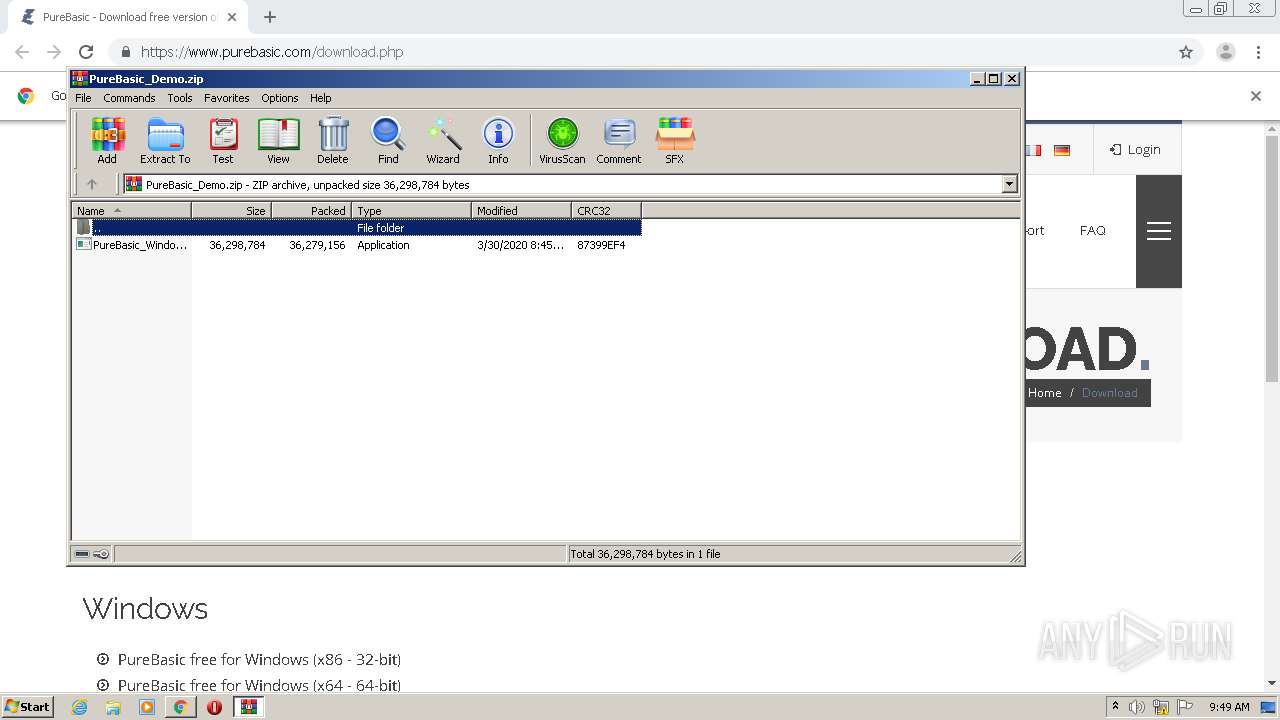
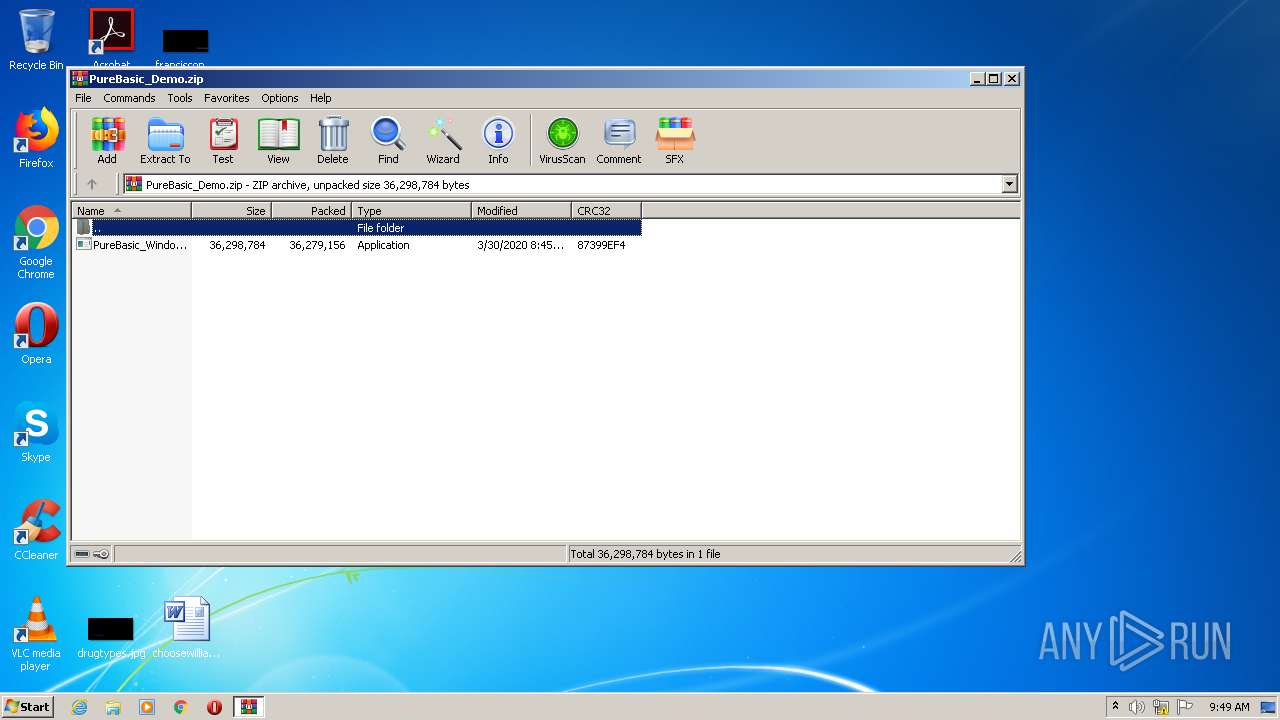
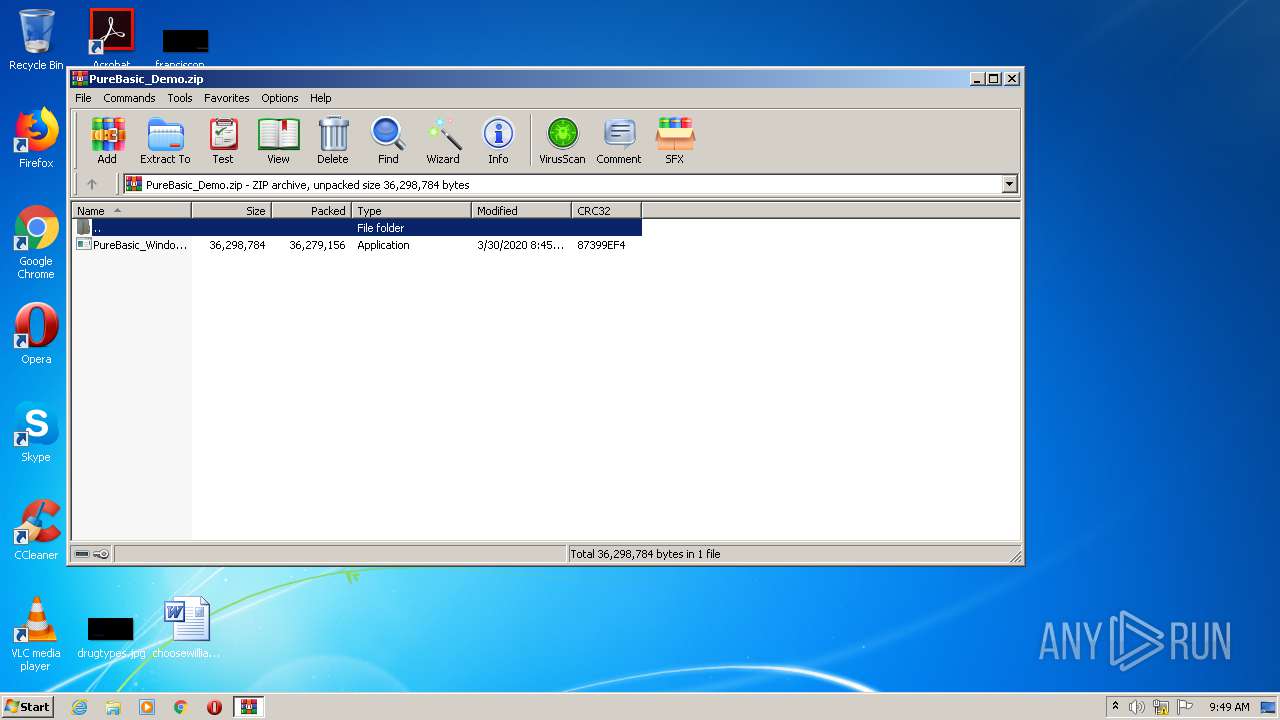
| 1012 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\PureBasic_Demo.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1400 | "C:\Users\admin\Desktop\PureBasic_Windows_5.72_X86_Demo.exe" /SPAWNWND=$801CA /NOTIFYWND=$50140 | C:\Users\admin\Desktop\PureBasic_Windows_5.72_X86_Demo.exe | PureBasic_Windows_5.72_X86_Demo.tmp | ||||||||||||
User: admin Company: Fantaisie Software Integrity Level: HIGH Description: PureBasic Setup Exit code: 0 Version: 5.72.0.0 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,8055914640776217393,9842717125256522840,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18007689402279581912 --mojo-platform-channel-handle=1056 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,8055914640776217393,9842717125256522840,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10934704946771479464 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2580 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,8055914640776217393,9842717125256522840,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1275068916589719397 --mojo-platform-channel-handle=3592 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,8055914640776217393,9842717125256522840,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10506848313697876576 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2188 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://www.purebasic.com/download.php" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 015
Read events
1 890
Write events
121
Delete events
4
Modification events
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2420-13244028528907750 |
Value: 259 | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2420) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
28
Suspicious files
183
Text files
588
Unknown types
164
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\18ab8ecb-756e-4693-a485-4931a87a7af1.tmp | — | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF160573.TMP | text | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF160535.TMP | text | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF160554.TMP | text | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF160719.TMP | — | |
MD5:— | SHA256:— | |||
| 2420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
26
DNS requests
14
Threats
8
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
896 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
896 | chrome.exe | 163.172.93.88:443 | www.purebasic.com | Online S.a.s. | FR | suspicious |
896 | chrome.exe | 172.217.23.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
896 | chrome.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
896 | chrome.exe | 172.217.23.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
896 | chrome.exe | 172.217.22.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
896 | chrome.exe | 216.58.212.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
896 | chrome.exe | 172.217.22.46:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
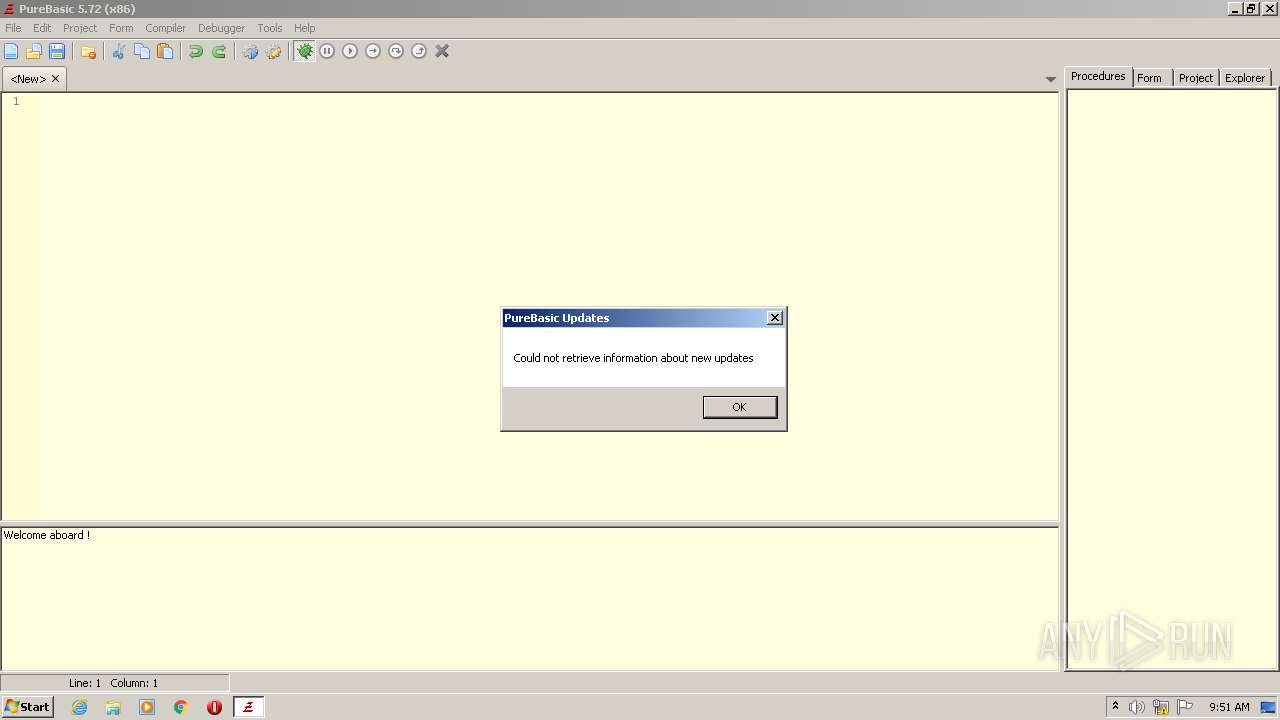
3160 | PureBasic.exe | 163.172.93.88:443 | www.purebasic.com | Online S.a.s. | FR | suspicious |
— | — | 163.172.93.88:443 | www.purebasic.com | Online S.a.s. | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.purebasic.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3160 | PureBasic.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3160 | PureBasic.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3160 | PureBasic.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3160 | PureBasic.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3160 | PureBasic.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3160 | PureBasic.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3160 | PureBasic.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
— | — | Potentially Bad Traffic | ET INFO TLS Handshake Failure |