| download: | psiphon3.exe |
| Full analysis: | https://app.any.run/tasks/60118c15-e5ff-496f-9d74-1b8394826b1d |
| Verdict: | Malicious activity |
| Analysis date: | December 25, 2018, 17:35:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 475F5CF397EA373D9B413BF1E0D091CF |
| SHA1: | 3F8F7BAED23BFEE688D6769C9E6B72F2D2D2FE7B |
| SHA256: | 39ABE941FE1E92C46B77A9AF349439CB1404E1A609C8DAC92741DBA17AB37B4F |
| SSDEEP: | 98304:5Q6olATRJXpmzhMvTZCk/BwtqvwDPcz6sIM/daMgBZ43dvv785mGCUjbvfxA:5WuTRJc9M7wOBKqvw4Wsb/W6fUe |
MALICIOUS
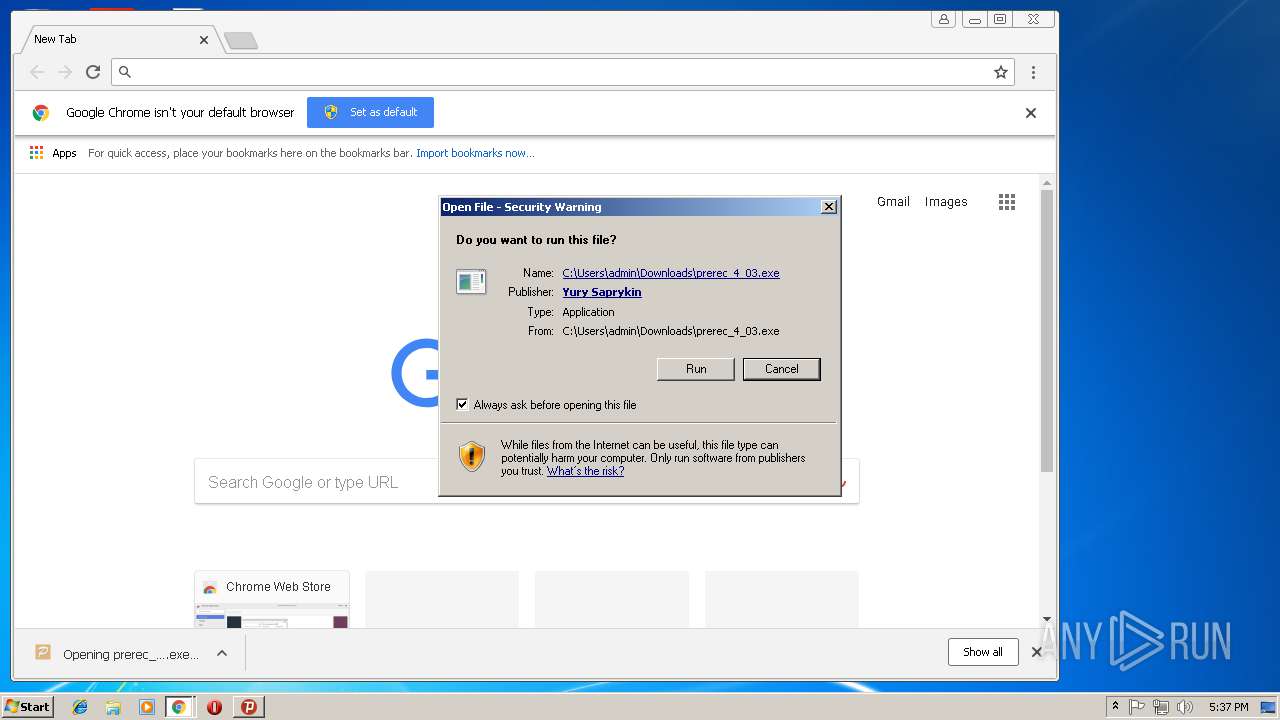
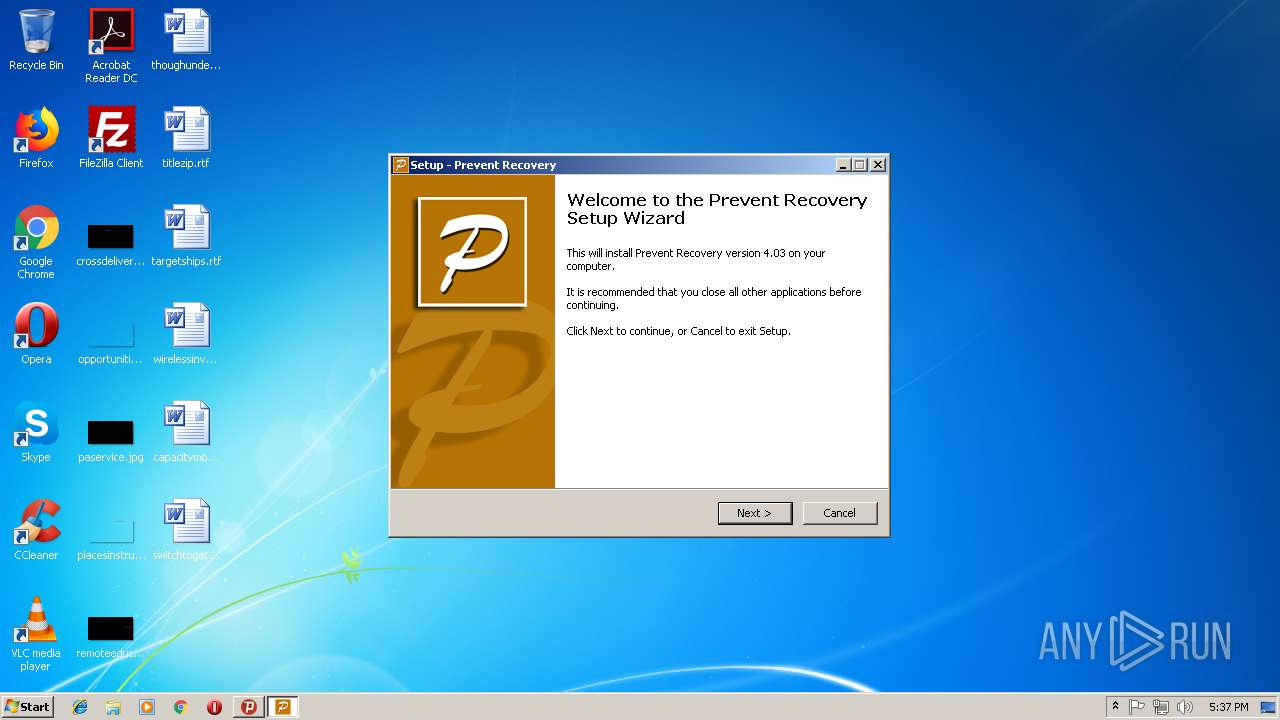
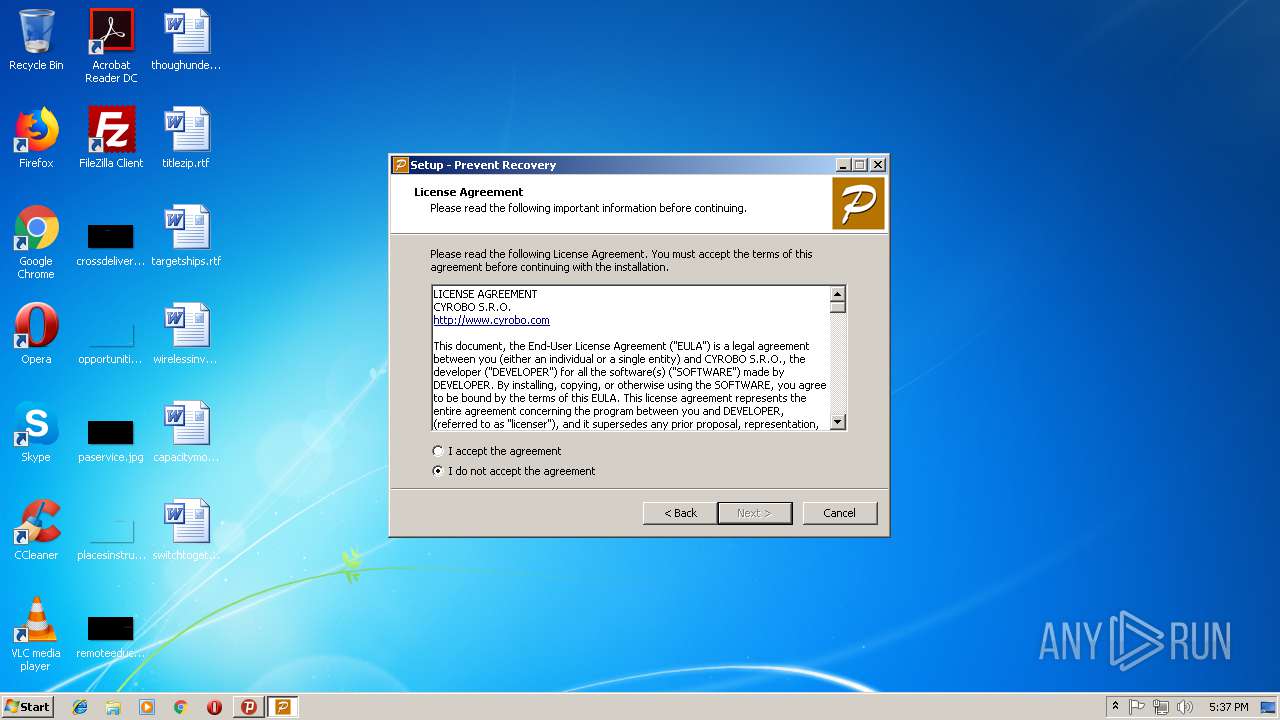
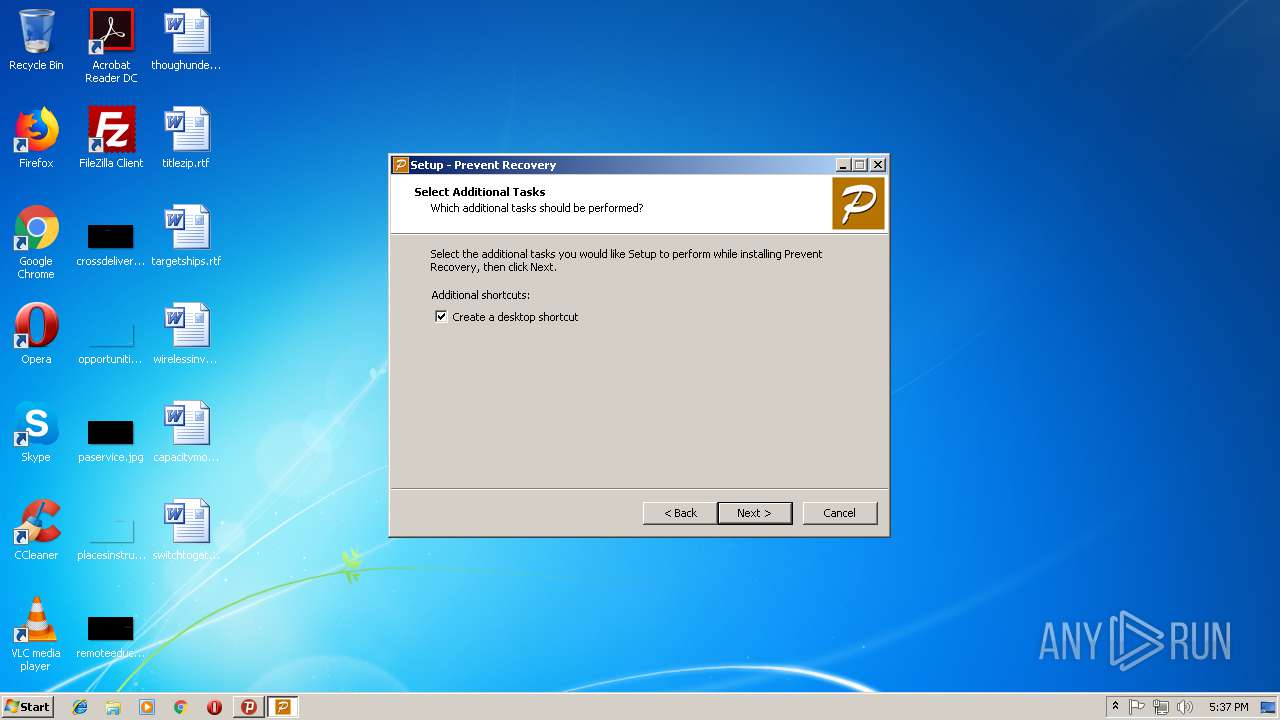
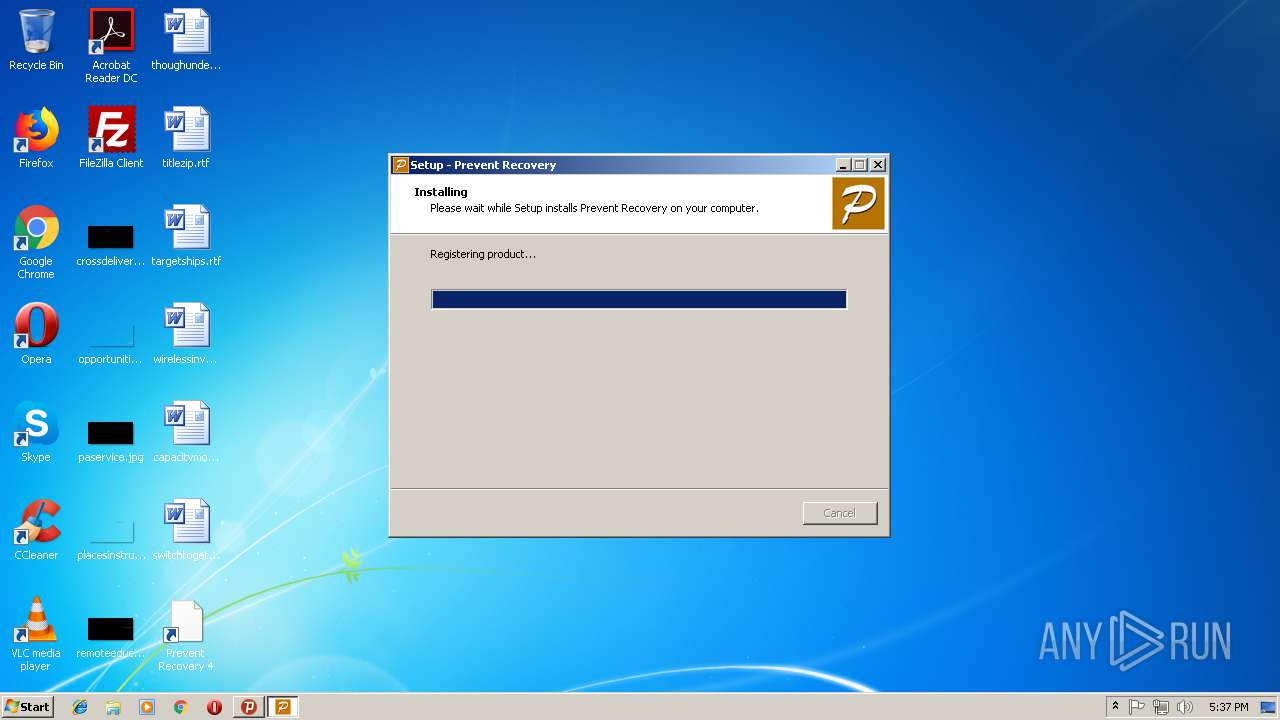
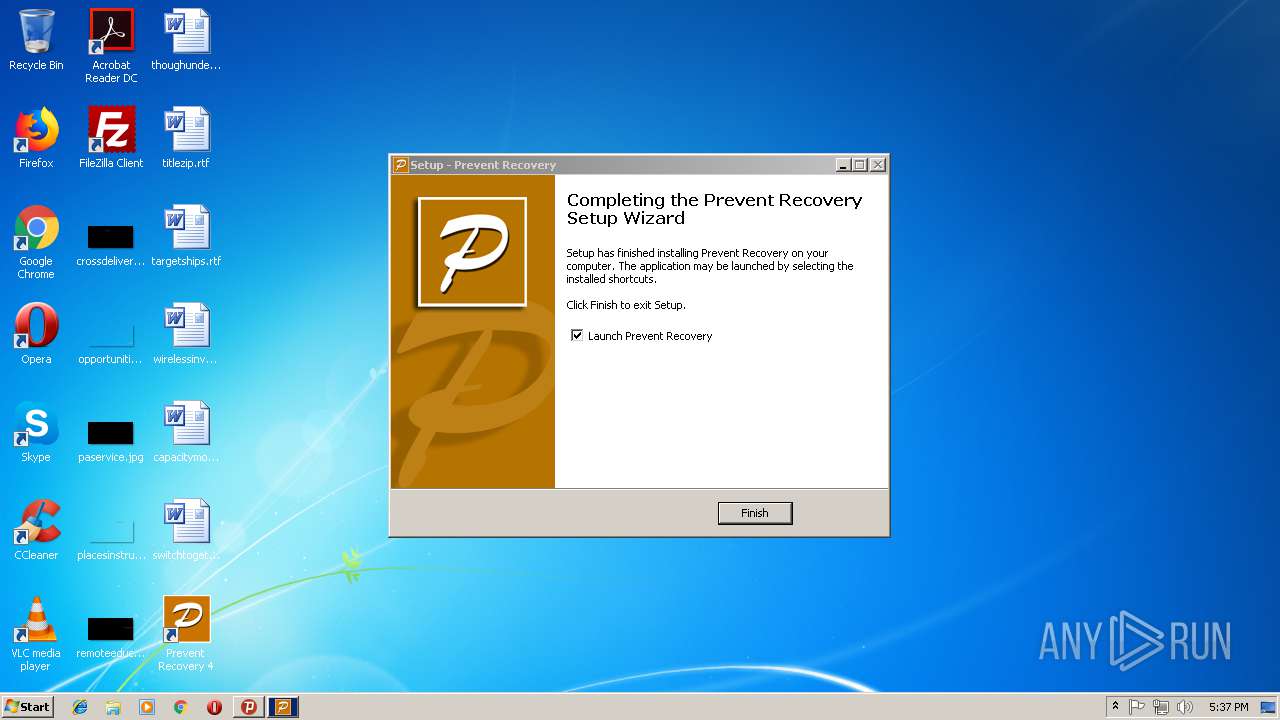
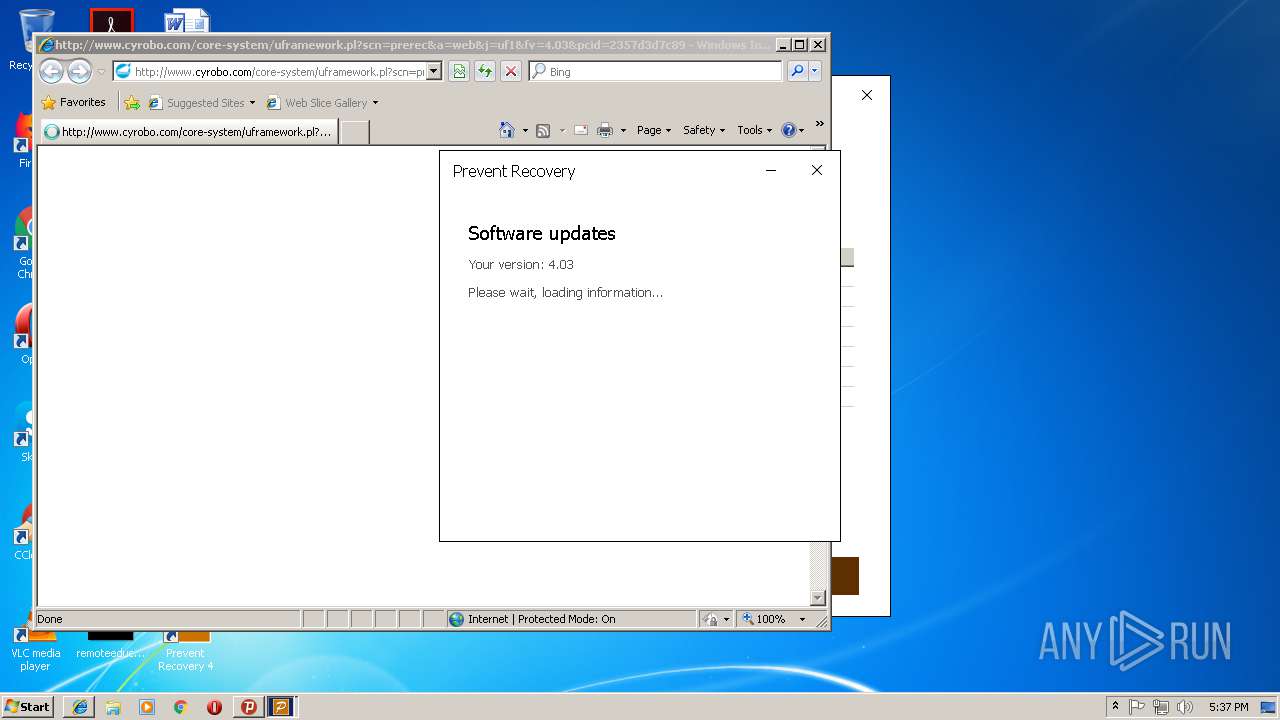
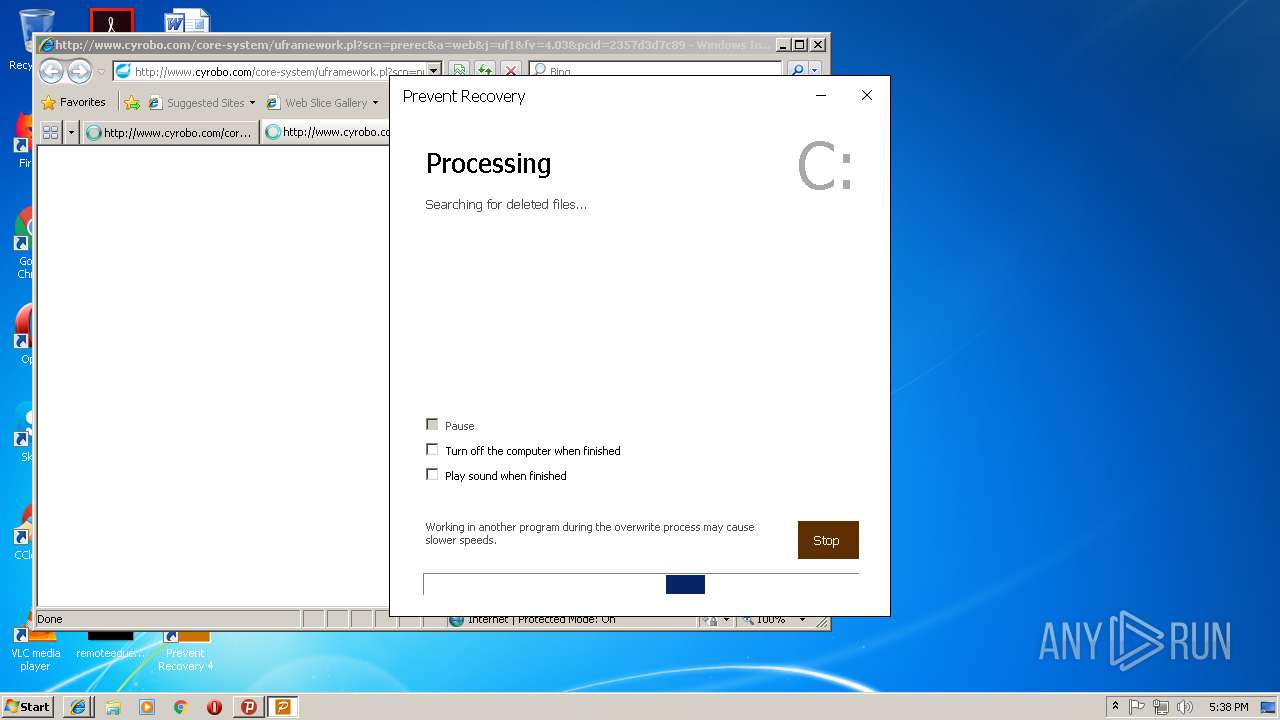
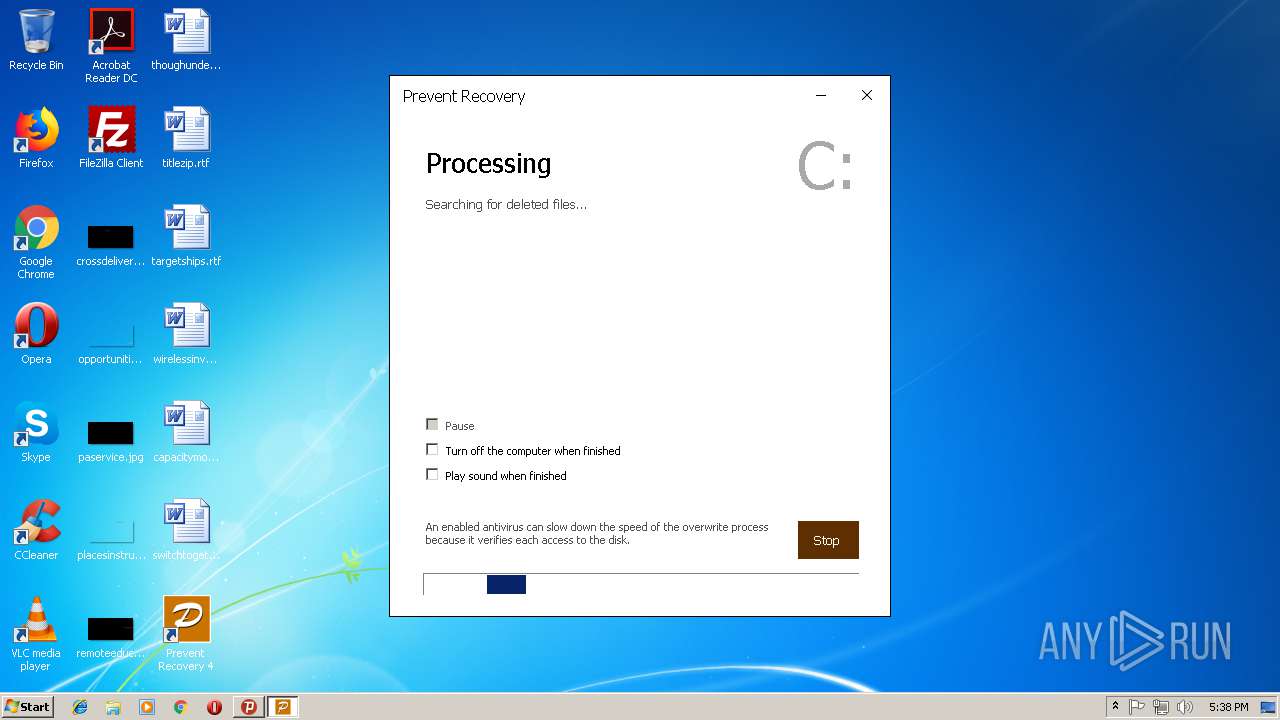
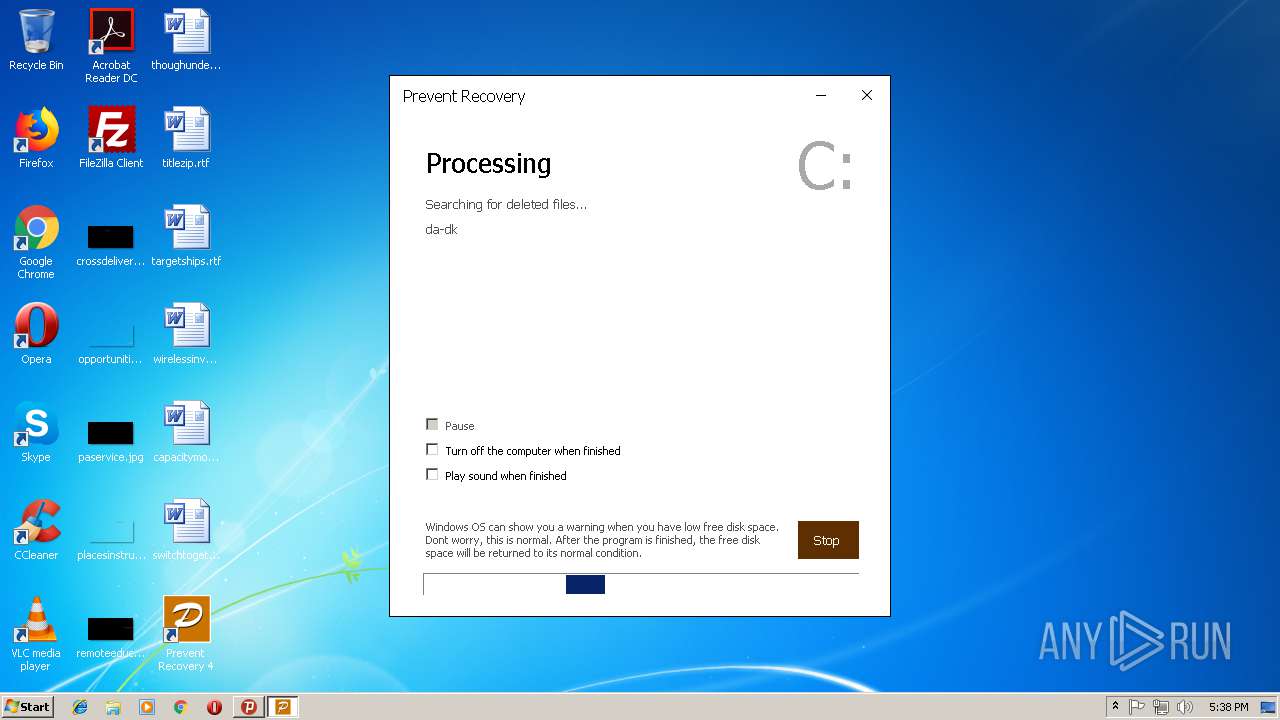
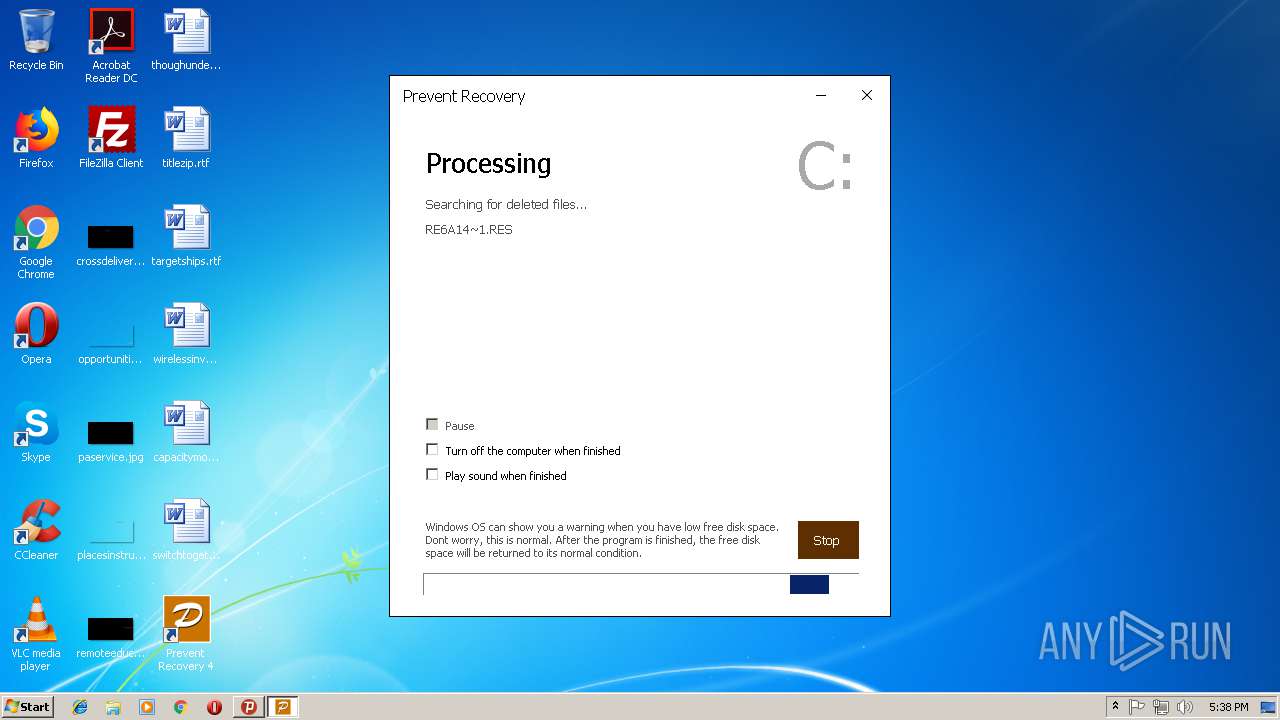
Application was dropped or rewritten from another process
- psiphon-tunnel-core.exe (PID: 4072)
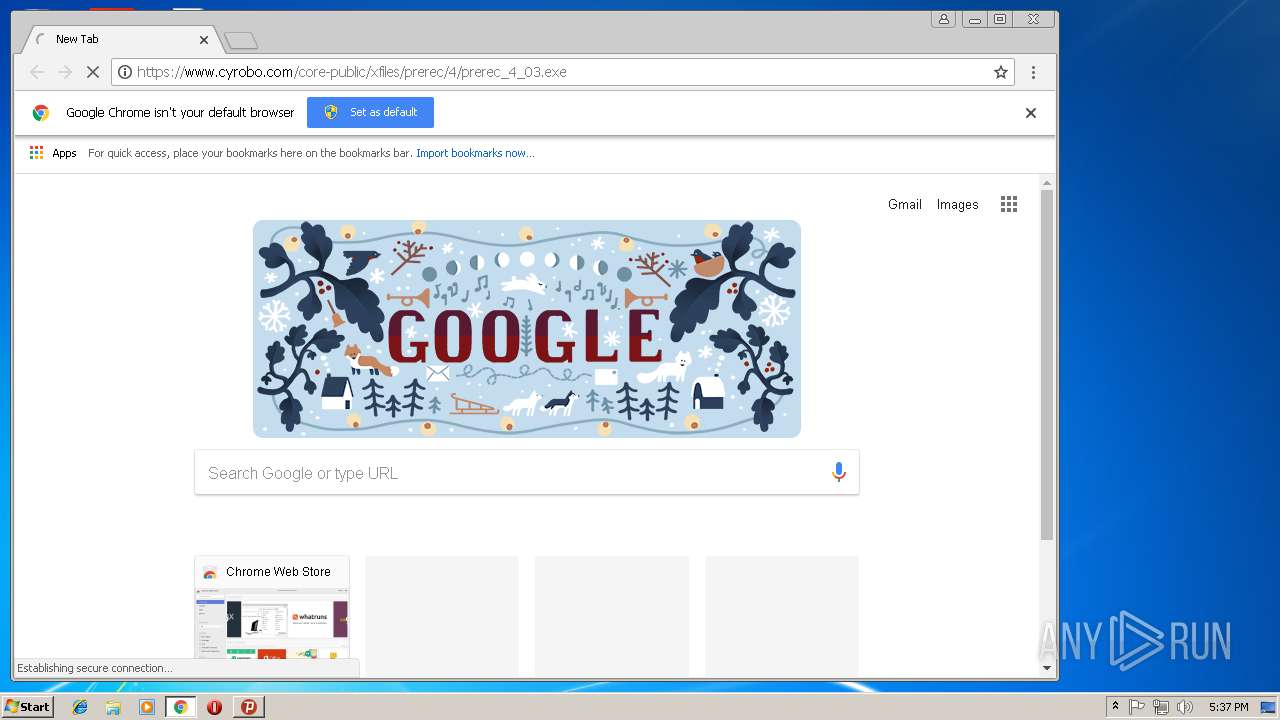
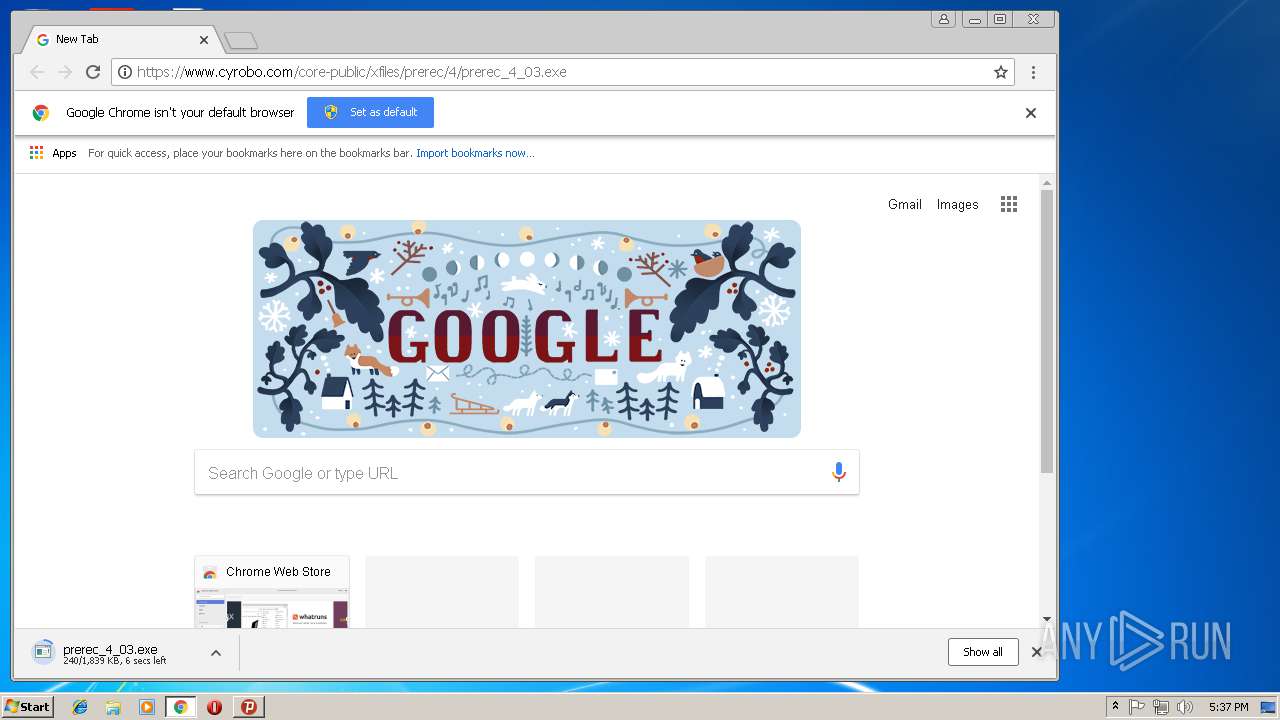
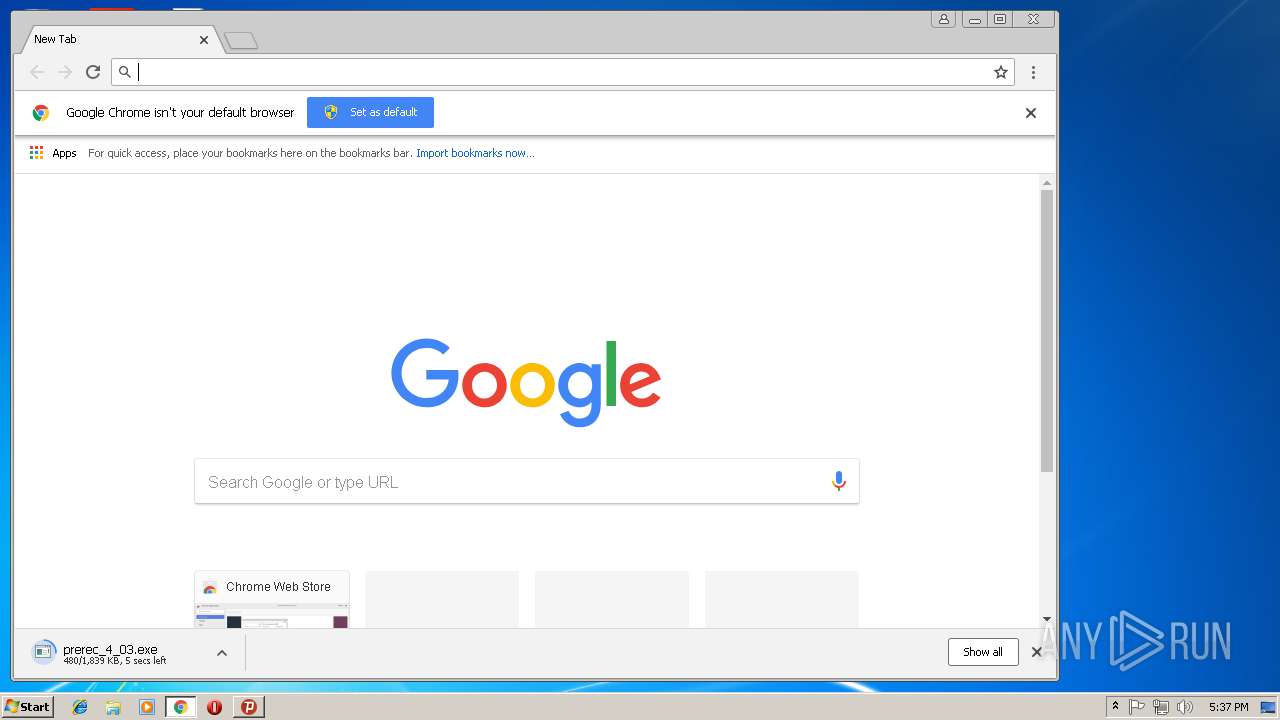
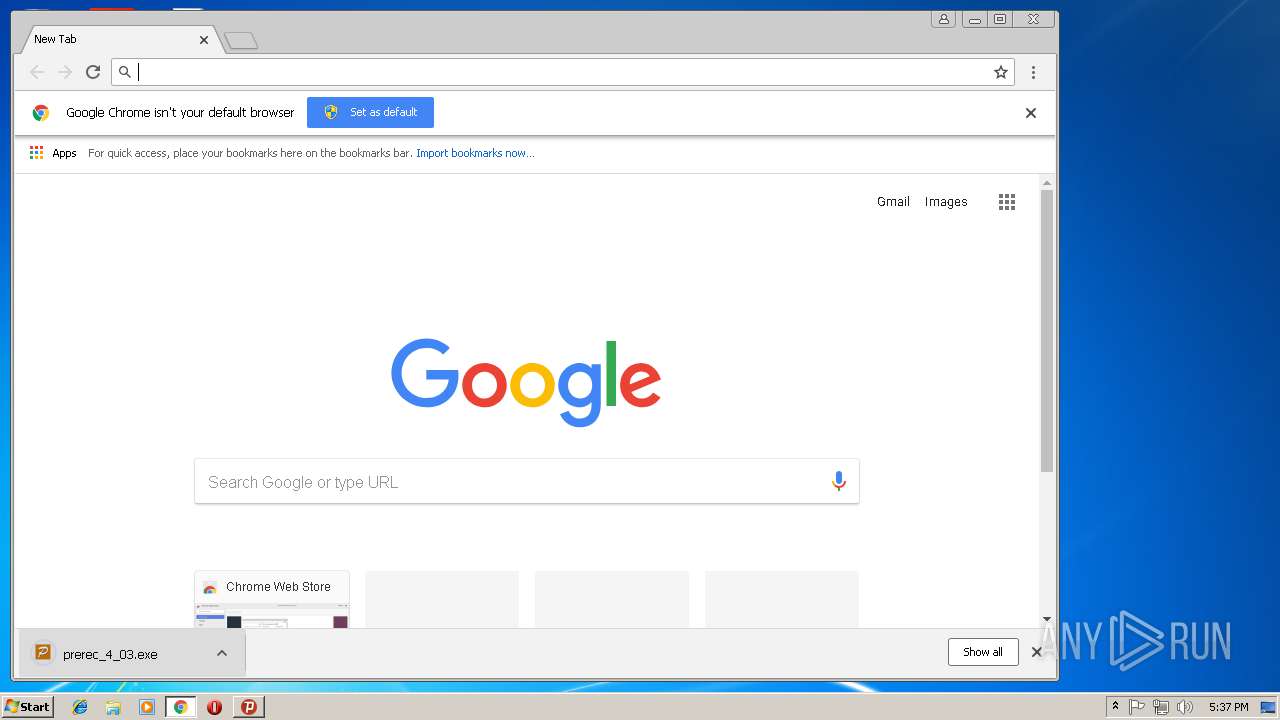
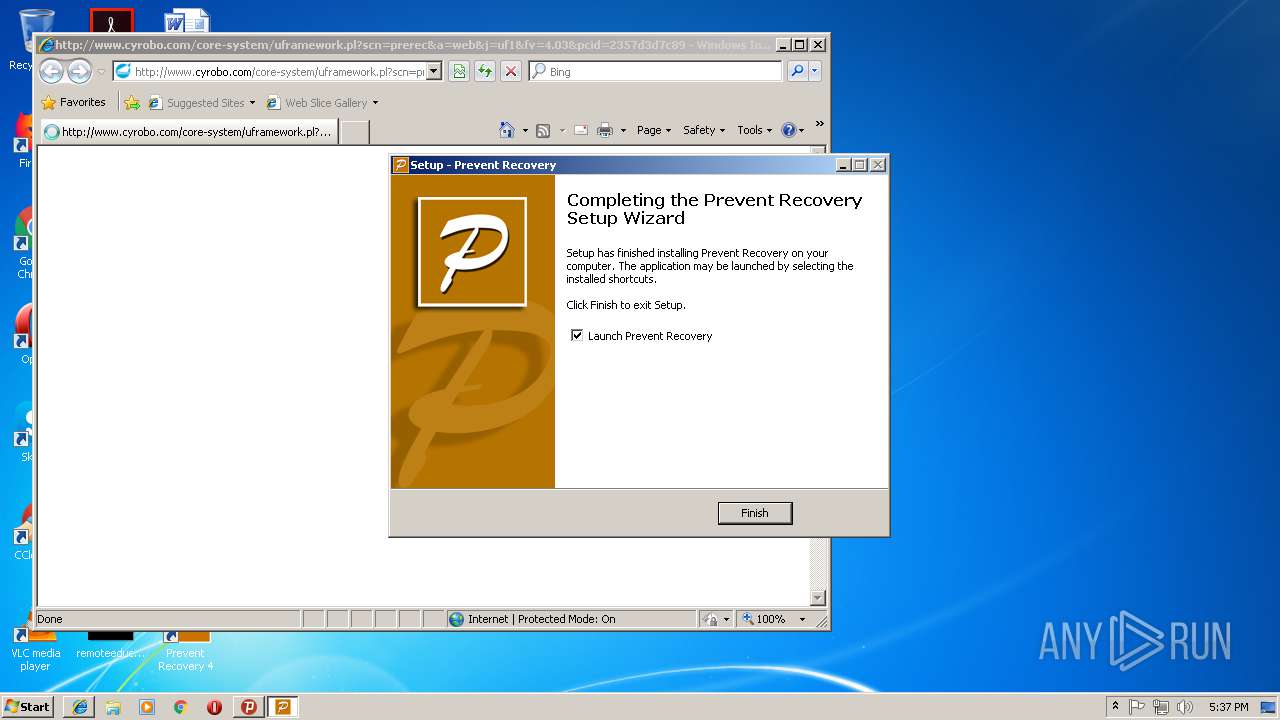
- prerec_4_03.exe (PID: 3100)
- PreRec.exe (PID: 3848)
- PreRec.exe (PID: 1820)
- PreRec.exe (PID: 3780)
- PreRec.exe (PID: 3508)
- PreRec.exe (PID: 556)
- PreRec.exe (PID: 3852)
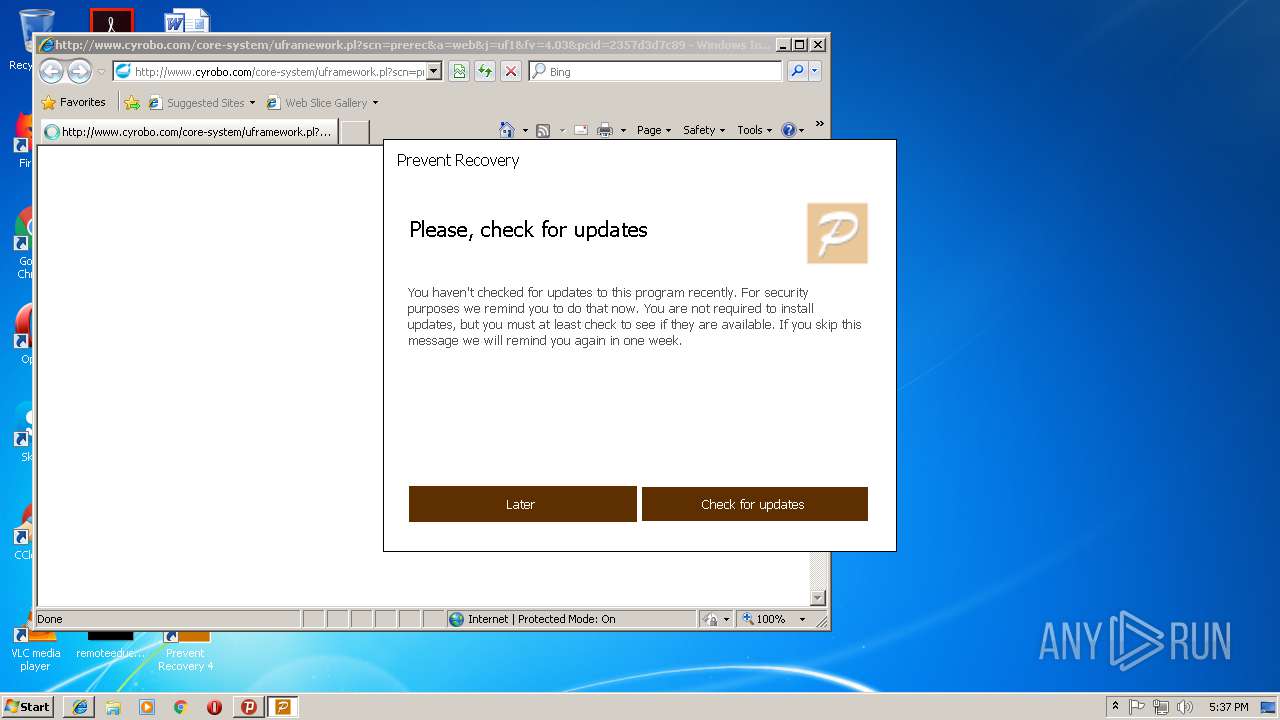
Changes the autorun value in the registry
- PreRec.exe (PID: 3780)
- PreRec.exe (PID: 3508)
SUSPICIOUS
Executable content was dropped or overwritten
- psiphon3.exe (PID: 3012)
- chrome.exe (PID: 3748)
- prerec_4_03.exe (PID: 3100)
- prerec_4_03.tmp (PID: 2504)
Uses RUNDLL32.EXE to load library
- psiphon3.exe (PID: 3012)
- iexplore.exe (PID: 3292)
Reads Internet Cache Settings
- rundll32.exe (PID: 3064)
- psiphon3.exe (PID: 3012)
- rundll32.exe (PID: 3168)
Reads internet explorer settings
- psiphon3.exe (PID: 3012)
Creates files in the user directory
- psiphon3.exe (PID: 3012)
- psiphon-tunnel-core.exe (PID: 4072)
- prerec_4_03.tmp (PID: 2504)
- PreRec.exe (PID: 3780)
- PreRec.exe (PID: 3508)
Connects to unusual port
- psiphon-tunnel-core.exe (PID: 4072)
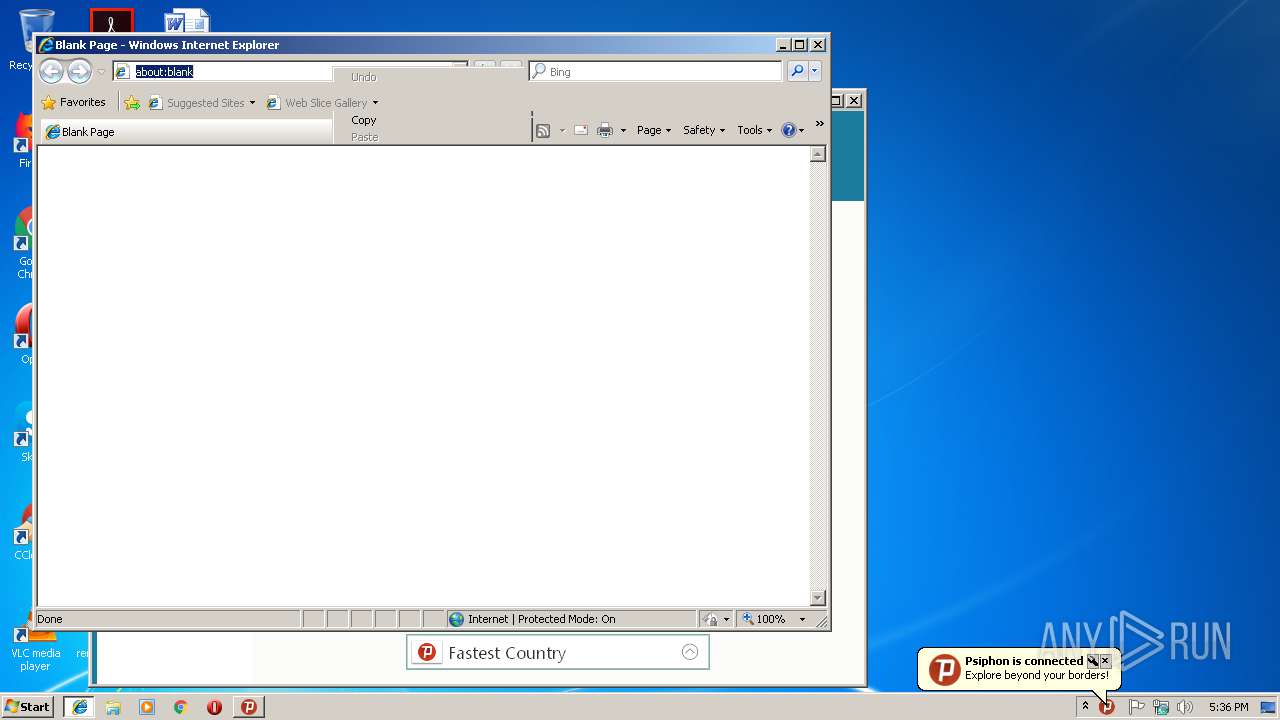
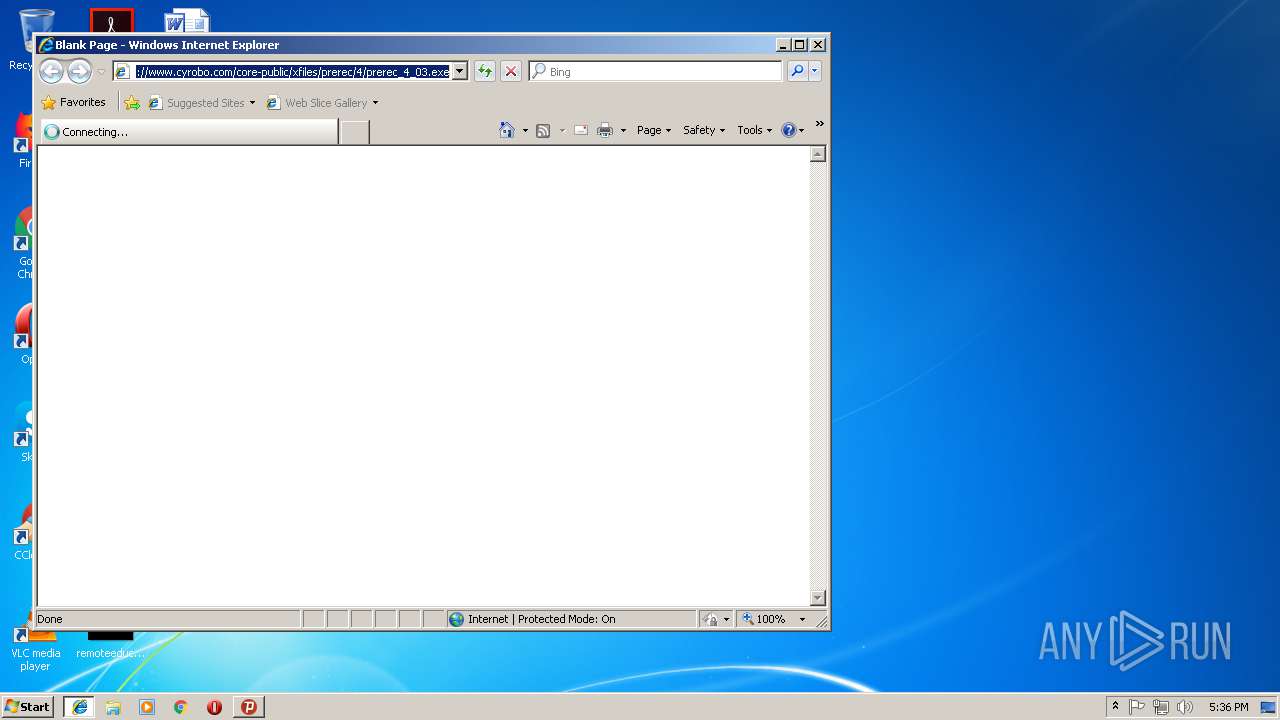
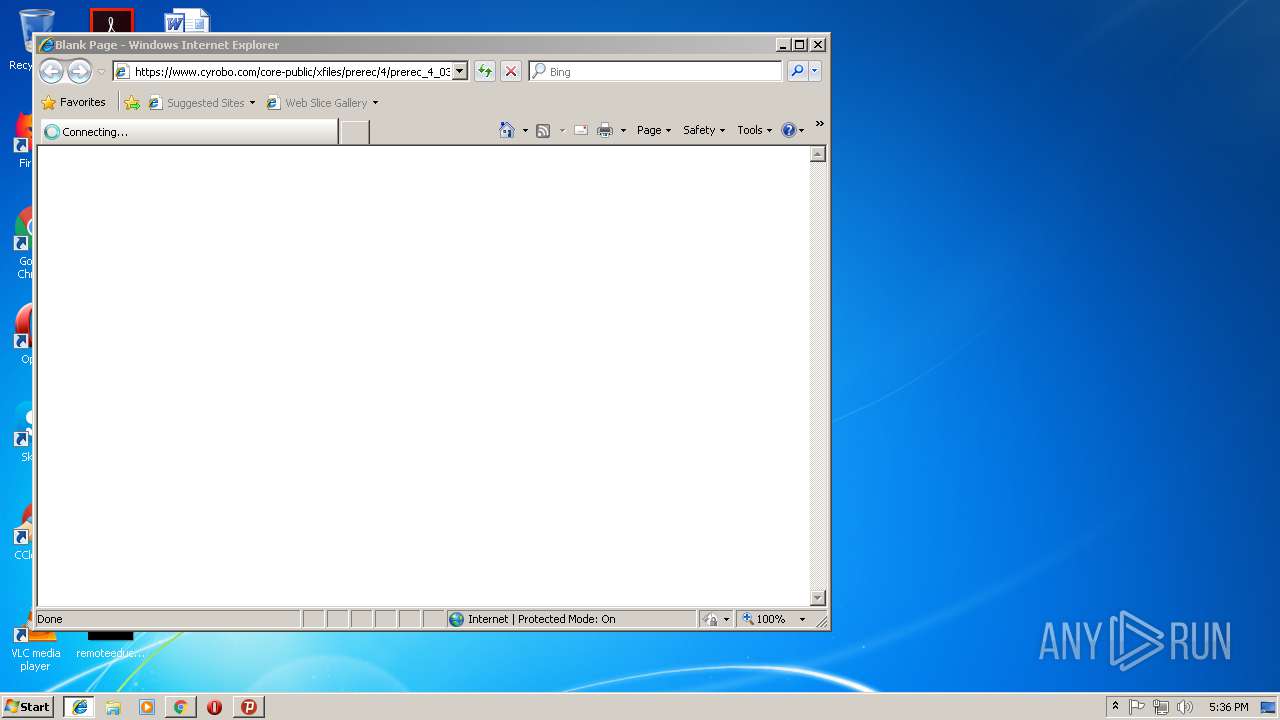
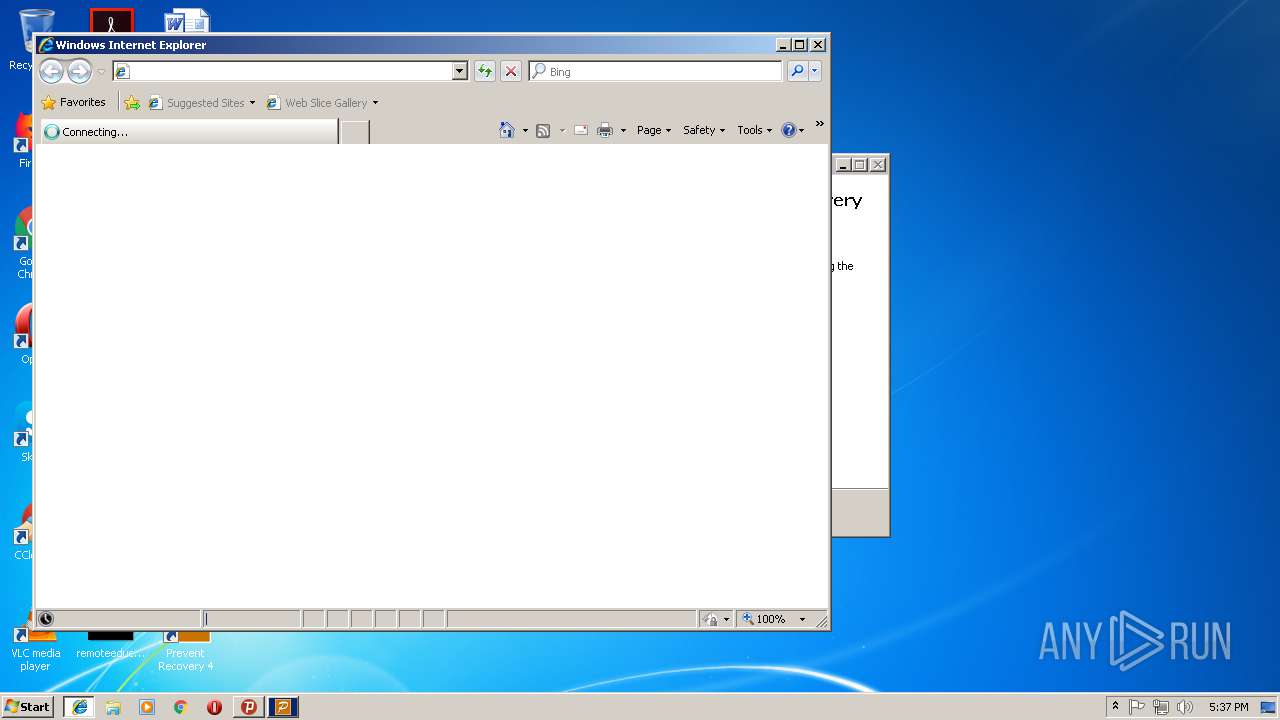
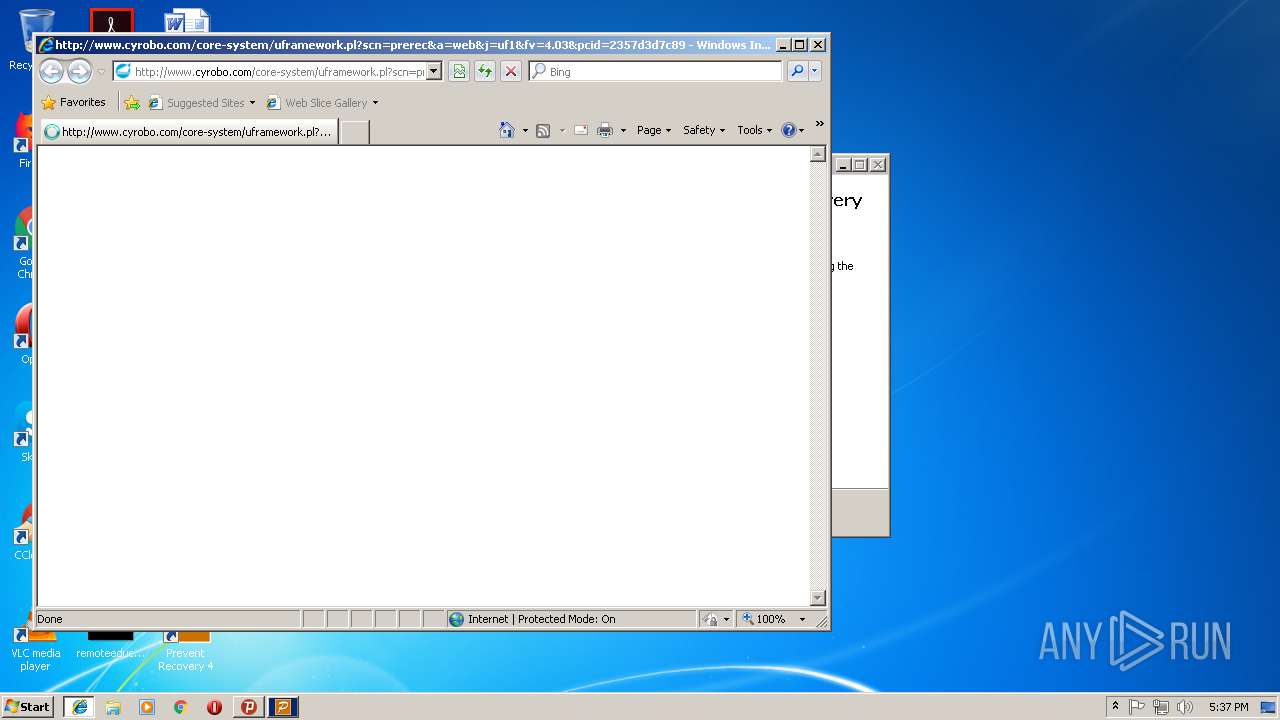
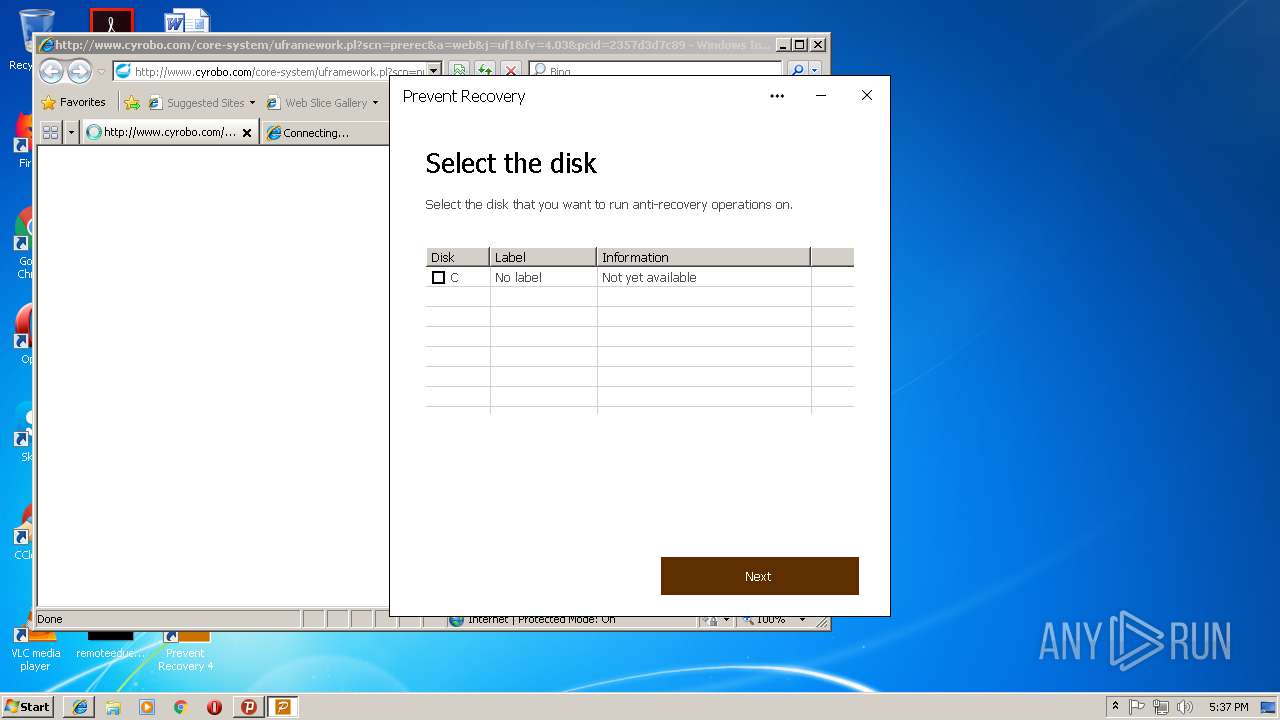
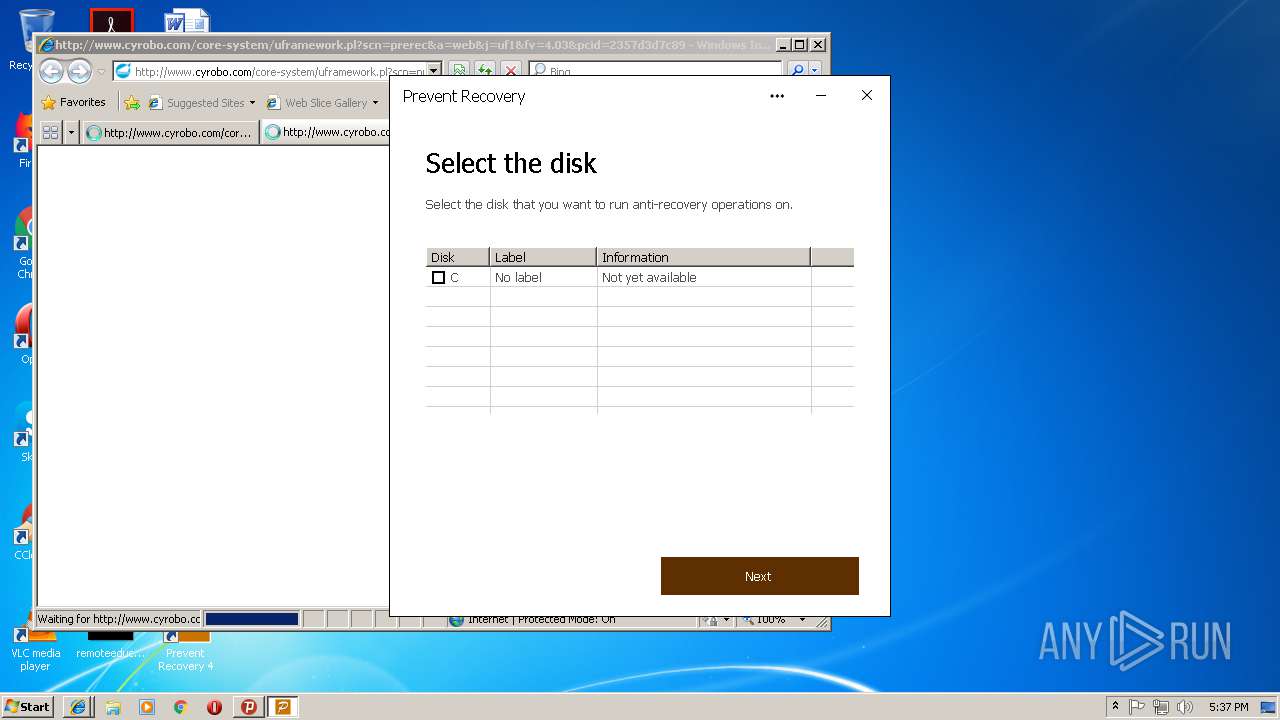
Starts Internet Explorer
- psiphon3.exe (PID: 3012)
- PreRec.exe (PID: 3848)
Reads Environment values
- PreRec.exe (PID: 1820)
- PreRec.exe (PID: 3852)
- PreRec.exe (PID: 3508)
Reads Windows owner or organization settings
- prerec_4_03.tmp (PID: 2504)
Reads the Windows organization settings
- prerec_4_03.tmp (PID: 2504)
Application launched itself
- PreRec.exe (PID: 3780)
- PreRec.exe (PID: 3508)
- PreRec.exe (PID: 3852)
INFO
Application launched itself
- iexplore.exe (PID: 3292)
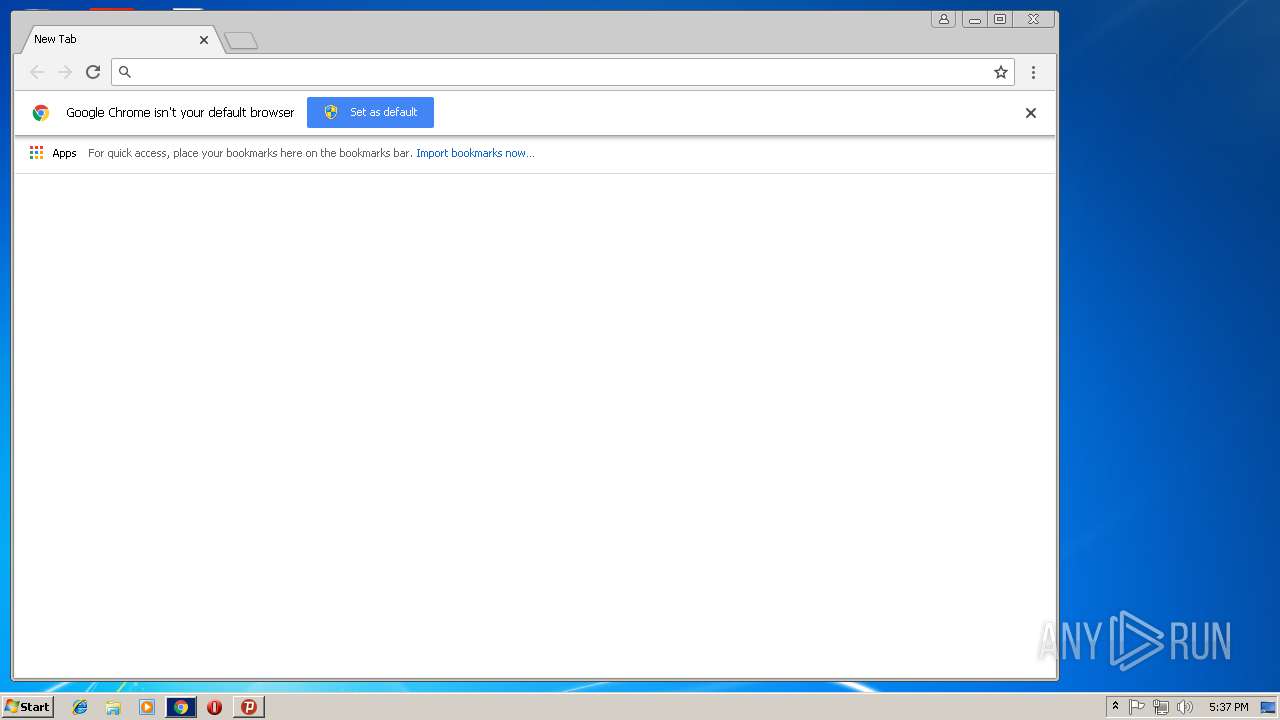
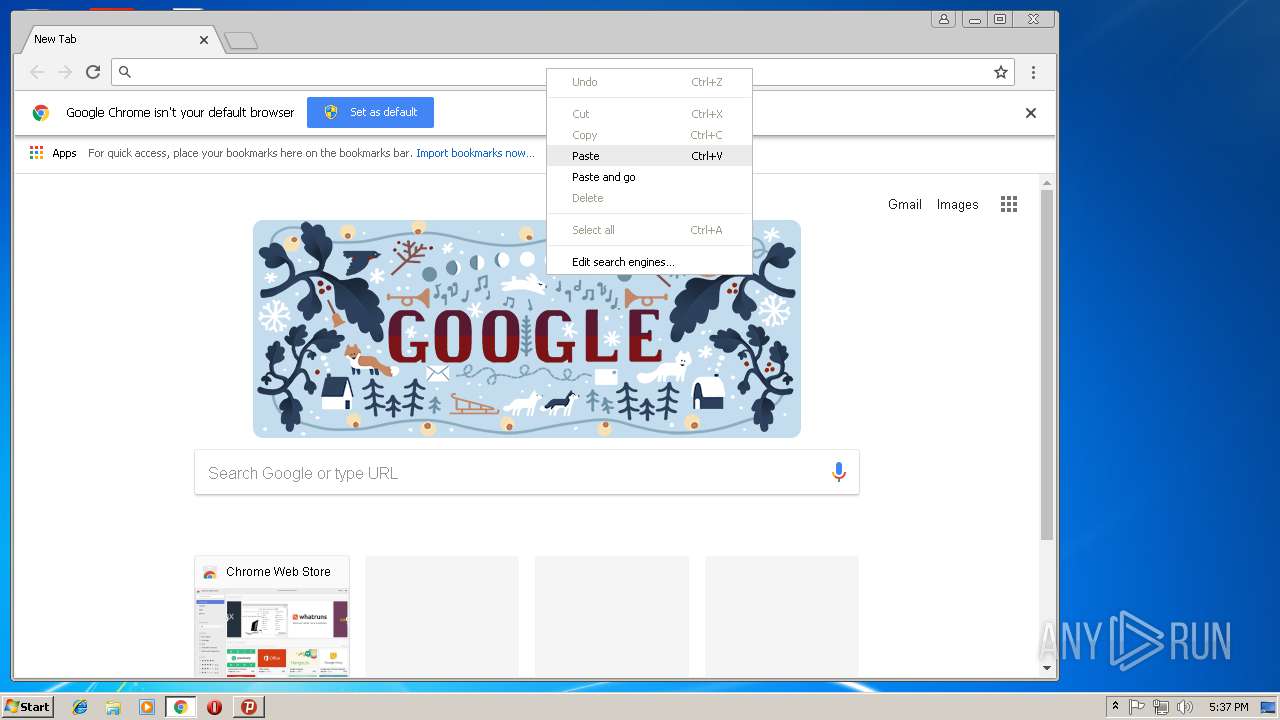
- chrome.exe (PID: 3748)
- iexplore.exe (PID: 2212)
Reads Internet Cache Settings
- iexplore.exe (PID: 4048)
- iexplore.exe (PID: 3144)
- chrome.exe (PID: 3748)
- iexplore.exe (PID: 3560)
- iexplore.exe (PID: 3816)
Reads internet explorer settings
- iexplore.exe (PID: 3144)
- iexplore.exe (PID: 4048)
- iexplore.exe (PID: 3560)
- iexplore.exe (PID: 3816)
Changes internet zones settings
- iexplore.exe (PID: 3292)
- iexplore.exe (PID: 2212)
Creates files in the user directory
- iexplore.exe (PID: 3292)
- iexplore.exe (PID: 3144)
- iexplore.exe (PID: 3560)
- iexplore.exe (PID: 2212)
- iexplore.exe (PID: 3816)
Reads settings of System Certificates
- iexplore.exe (PID: 3292)
- chrome.exe (PID: 3748)
Changes settings of System certificates
- chrome.exe (PID: 3748)
Application was dropped or rewritten from another process
- prerec_4_03.tmp (PID: 2504)
Creates a software uninstall entry
- prerec_4_03.tmp (PID: 2504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:23 15:36:09+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 6000640 |
| InitializedDataSize: | 90112 |
| UninitializedDataSize: | 11644928 |
| EntryPoint: | 0x10d49d0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Dec-2018 14:36:09 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 23-Dec-2018 14:36:09 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00B1B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00B1C000 | 0x005B9000 | 0x005B8E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.93001 |
.rsrc | 0x010D5000 | 0x00016000 | 0x00015C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.48744 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.0192 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 5.62289 | 1384 | UNKNOWN | English - United States | RT_ICON |
4 | 5.86281 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 5.32737 | 3752 | UNKNOWN | English - United States | RT_ICON |
6 | 5.87817 | 1128 | UNKNOWN | English - United States | RT_ICON |
7 | 5.69962 | 66 | UNKNOWN | English - United States | RT_STRING |
8 | 4.79539 | 9640 | UNKNOWN | English - United States | RT_ICON |
9 | 7.96592 | 19543 | UNKNOWN | English - United States | RT_ICON |
10 | 7.94804 | 41745 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.DLL |
OLEAUT32.dll |
RASAPI32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
67
Monitored processes
28
Malicious processes
5
Suspicious processes
3
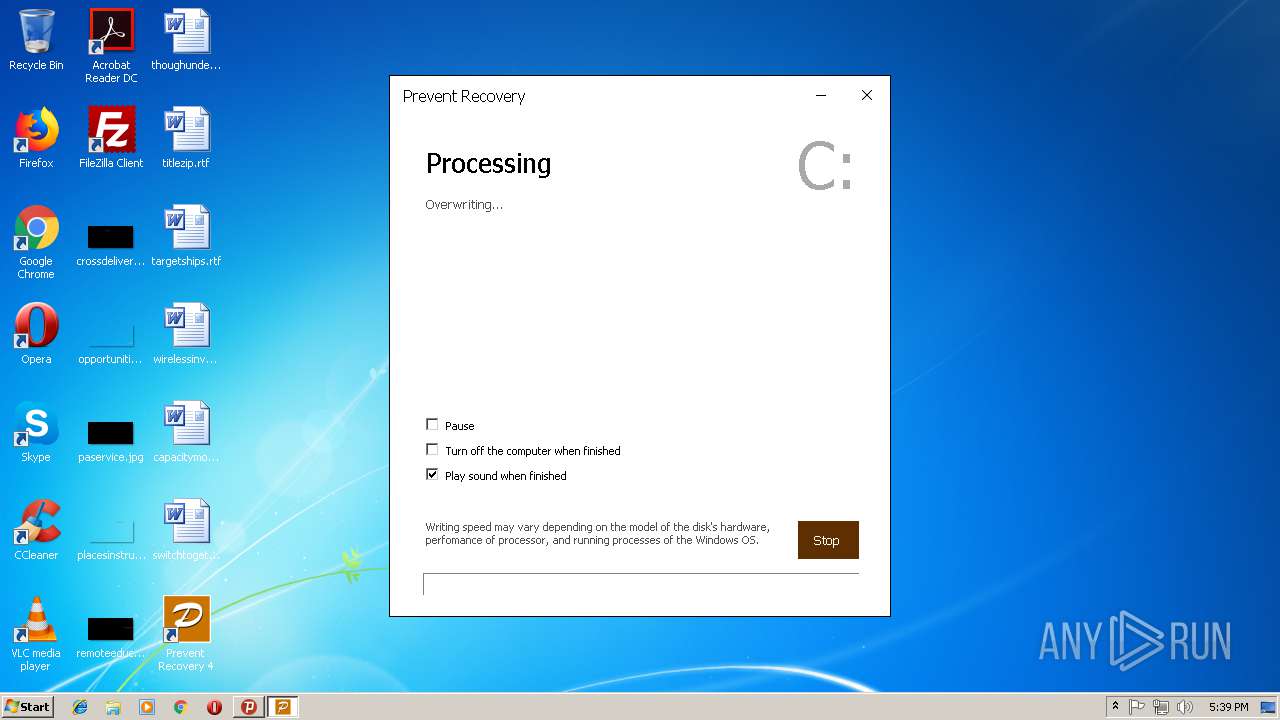
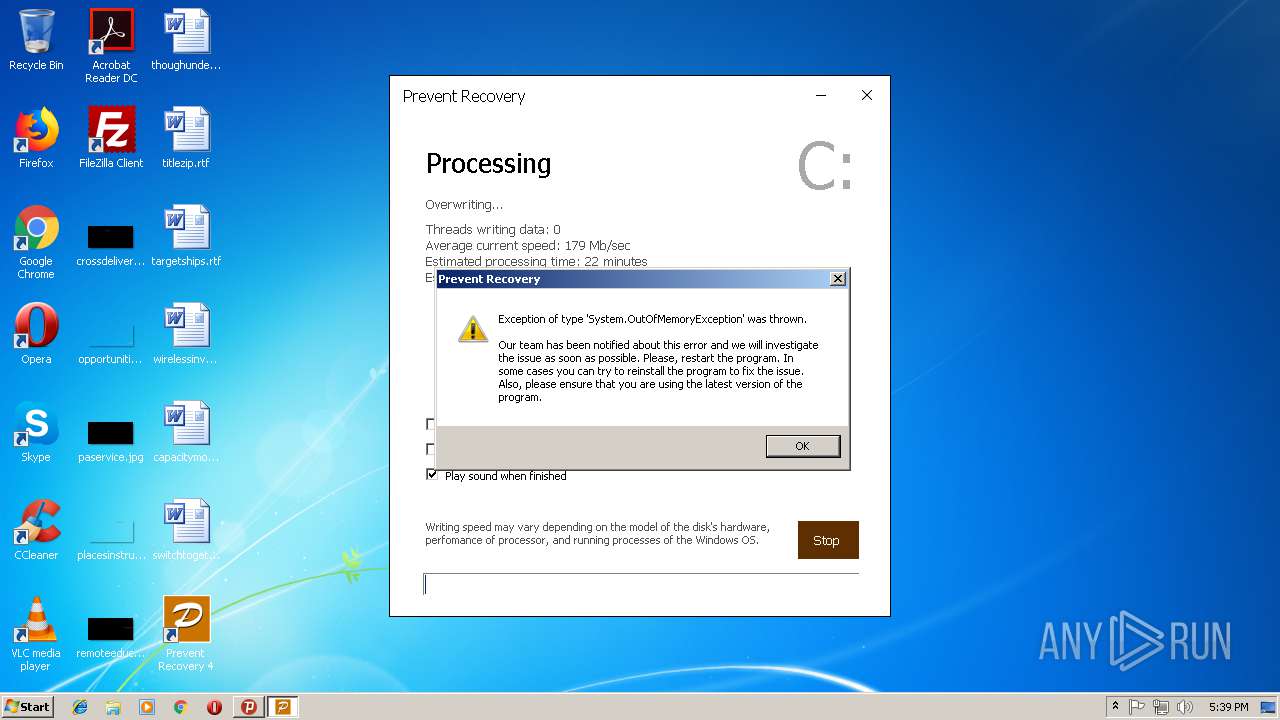
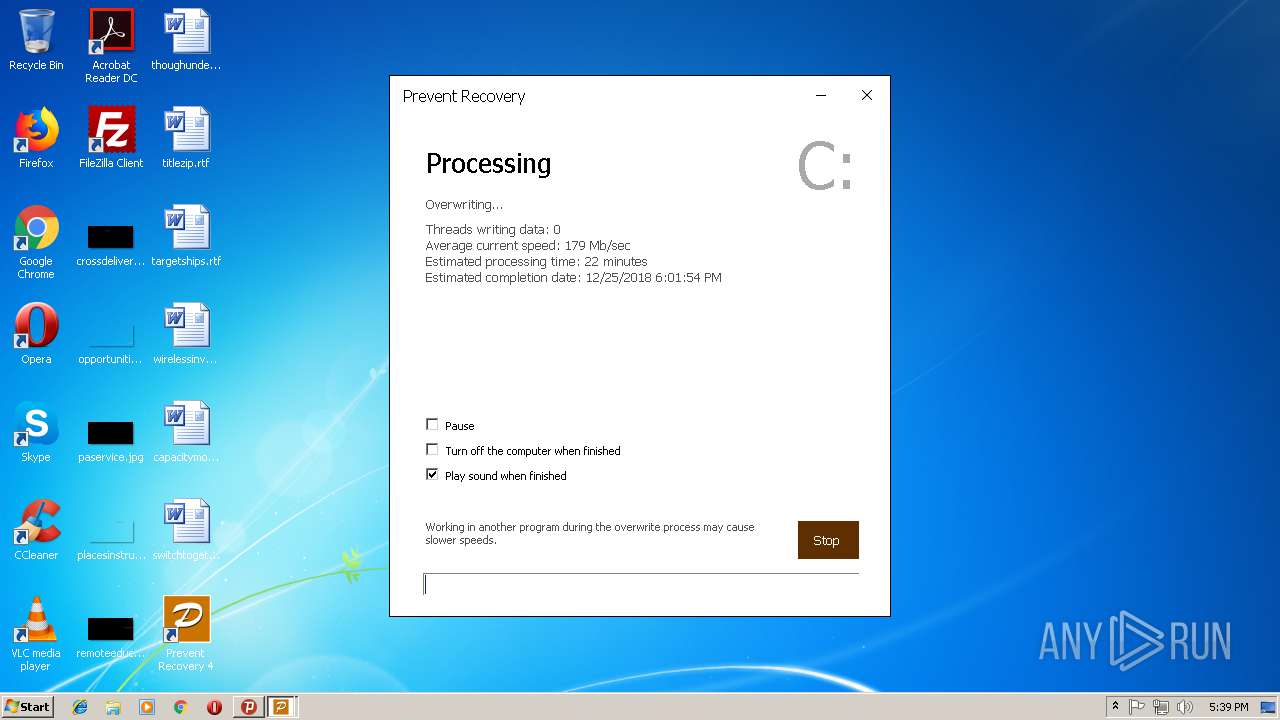
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
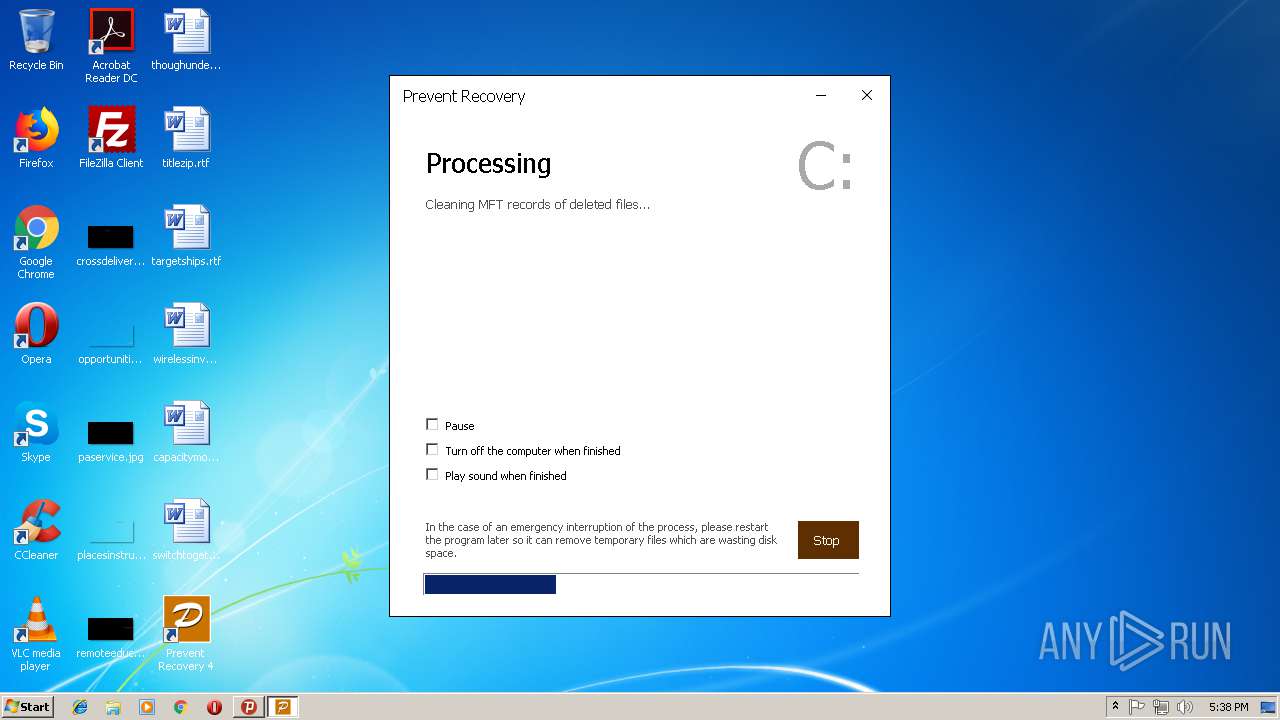
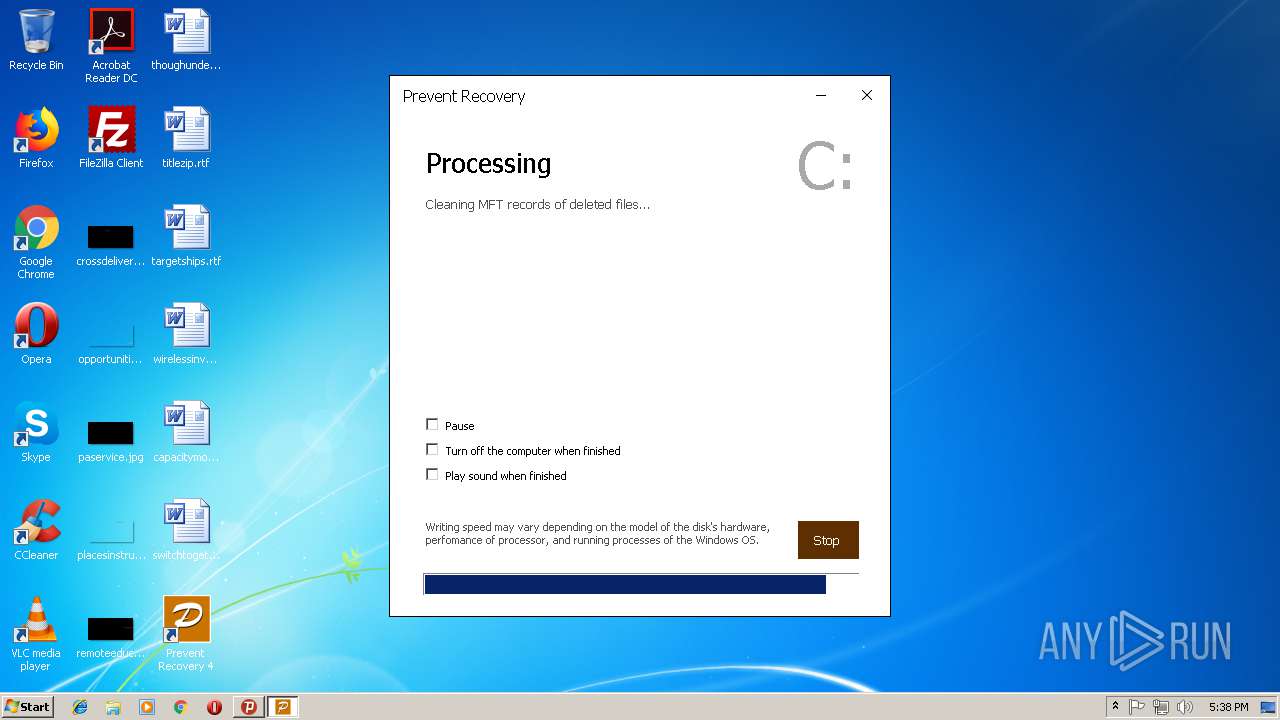
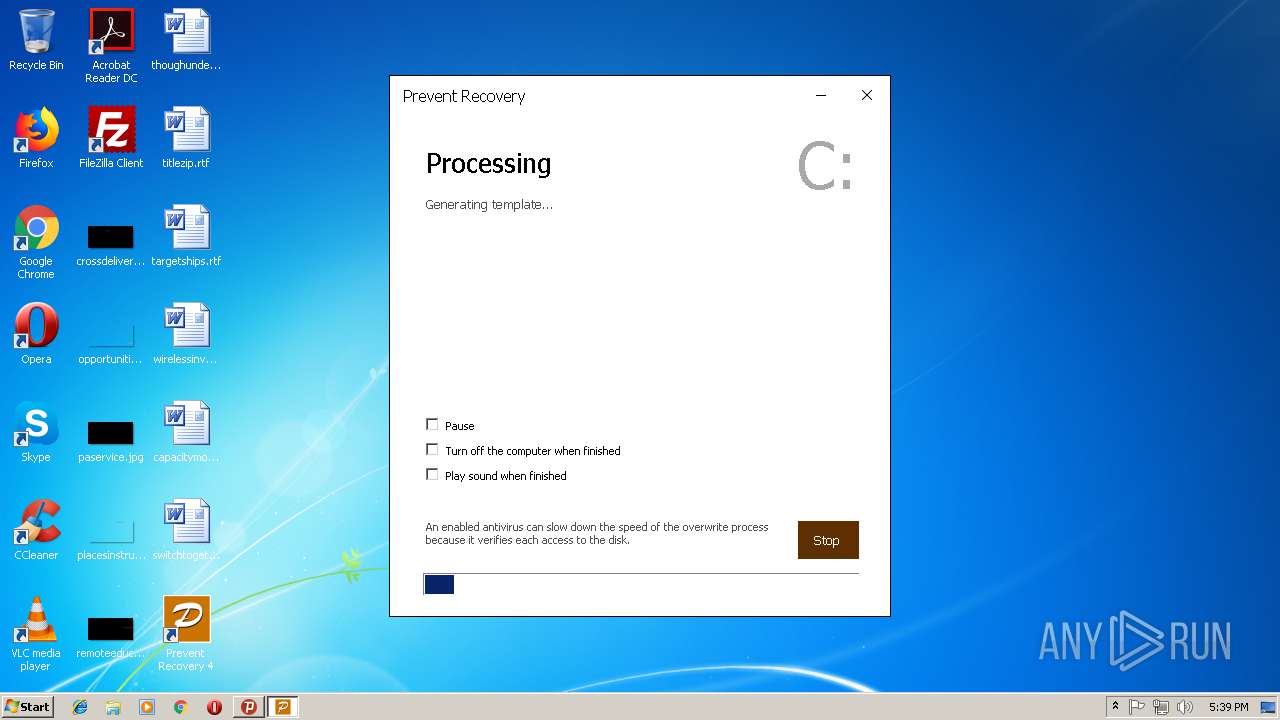
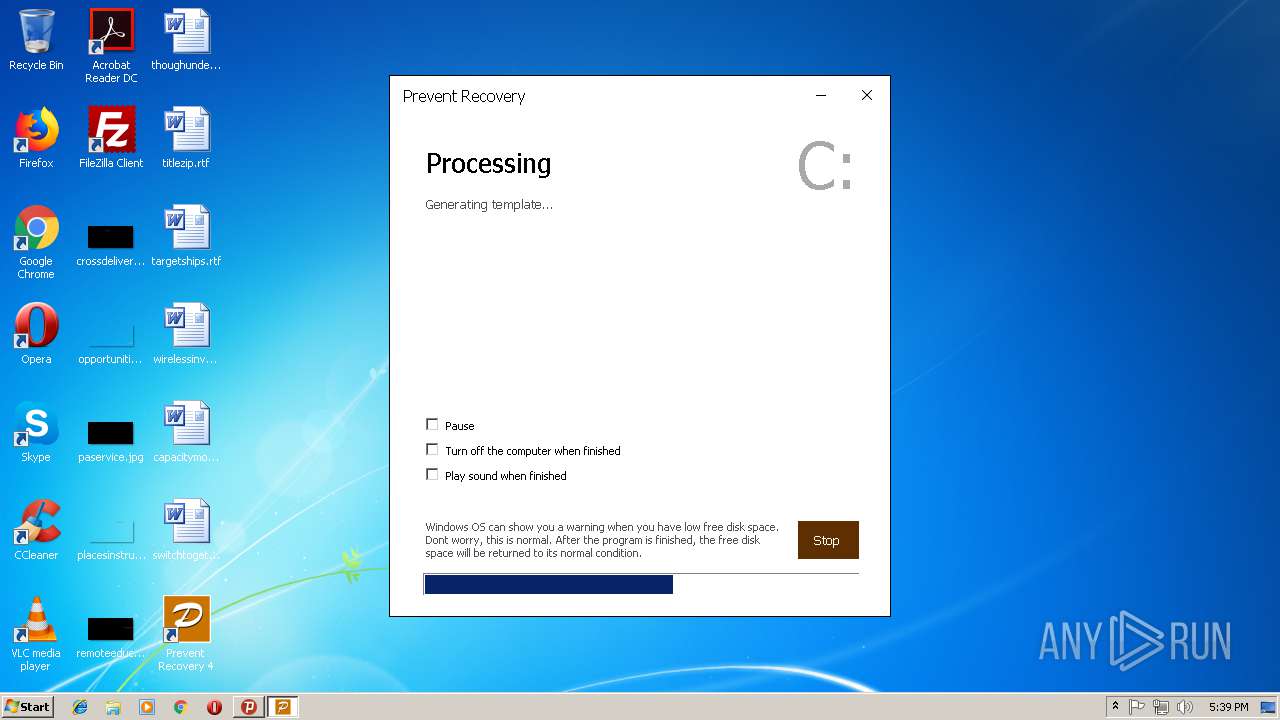
| 556 | "C:\Users\admin\AppData\Local\Prevent Recovery 4\PreRec.exe" protocol5 | C:\Users\admin\AppData\Local\Prevent Recovery 4\PreRec.exe | — | PreRec.exe | |||||||||||
User: admin Company: Cyrobo S.R.O. Integrity Level: HIGH Description: Prevent Recovery Exit code: 0 Version: 4.03.0.0 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,15580927468654885118,4438510032940390772,131072 --enable-features=PasswordImport --service-pipe-token=E577E2099EE5DA3FFB27F4A962180D70 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E577E2099EE5DA3FFB27F4A962180D70 --renderer-client-id=3 --mojo-platform-channel-handle=2100 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1820 | "C:\Users\admin\AppData\Local\Prevent Recovery 4\PreRec.exe" protocol2 | C:\Users\admin\AppData\Local\Prevent Recovery 4\PreRec.exe | prerec_4_03.tmp | ||||||||||||
User: admin Company: Cyrobo S.R.O. Integrity Level: MEDIUM Description: Prevent Recovery Exit code: 0 Version: 4.03.0.0 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | PreRec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3760 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2504 | "C:\Users\admin\AppData\Local\Temp\is-9J4RU.tmp\prerec_4_03.tmp" /SL5="$301A0,1421303,243200,C:\Users\admin\Downloads\prerec_4_03.exe" | C:\Users\admin\AppData\Local\Temp\is-9J4RU.tmp\prerec_4_03.tmp | prerec_4_03.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6e8900b0,0x6e8900c0,0x6e8900cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,15580927468654885118,4438510032940390772,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=60DCC0012DFA61CBA42F69ABDFDE12B2 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=60DCC0012DFA61CBA42F69ABDFDE12B2 --renderer-client-id=7 --mojo-platform-channel-handle=3508 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,15580927468654885118,4438510032940390772,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=AA3E6B36553300F5E73778CDEC4D8B88 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=AA3E6B36553300F5E73778CDEC4D8B88 --renderer-client-id=6 --mojo-platform-channel-handle=3472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3012 | "C:\Users\admin\AppData\Local\Temp\psiphon3.exe" | C:\Users\admin\AppData\Local\Temp\psiphon3.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 620
Read events
3 269
Write events
337
Delete events
14
Modification events
| (PID) Process: | (3012) psiphon3.exe | Key: | HKEY_CURRENT_USER\Software\Psiphon3 |
| Operation: | write | Name: | SkipBrowser |
Value: 0 | |||
| (PID) Process: | (3012) psiphon3.exe | Key: | HKEY_CURRENT_USER\Software\Psiphon3 |
| Operation: | write | Name: | SkipProxySettings |
Value: 0 | |||
| (PID) Process: | (3012) psiphon3.exe | Key: | HKEY_CURRENT_USER\Software\Psiphon3 |
| Operation: | write | Name: | SkipAutoConnect |
Value: 0 | |||
| (PID) Process: | (3012) psiphon3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3012) psiphon3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3012) psiphon3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\psiphon3_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3012) psiphon3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\psiphon3_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3012) psiphon3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\psiphon3_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3012) psiphon3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\psiphon3_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3012) psiphon3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\psiphon3_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
7
Suspicious files
74
Text files
185
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3292 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3144 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@ipfounder[1].txt | — | |
MD5:— | SHA256:— | |||
| 3144 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\index-alt[1].txt | — | |
MD5:— | SHA256:— | |||
| 3012 | psiphon3.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\main[1] | html | |
MD5:— | SHA256:— | |||
| 3012 | psiphon3.exe | C:\Users\admin\AppData\Roaming\Psiphon3\server_list.dat | text | |
MD5:— | SHA256:— | |||
| 3292 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF765CF1ED9CD9ECFD.TMP | — | |
MD5:— | SHA256:— | |||
| 3012 | psiphon3.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\flag_unknown_32[1] | image | |
MD5:— | SHA256:— | |||
| 3292 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF0F5A37FEB45FAE1A.TMP | — | |
MD5:— | SHA256:— | |||
| 3012 | psiphon3.exe | C:\Users\admin\AppData\Roaming\Psiphon3\psiphon.config | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
27
DNS requests
21
Threats
35
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
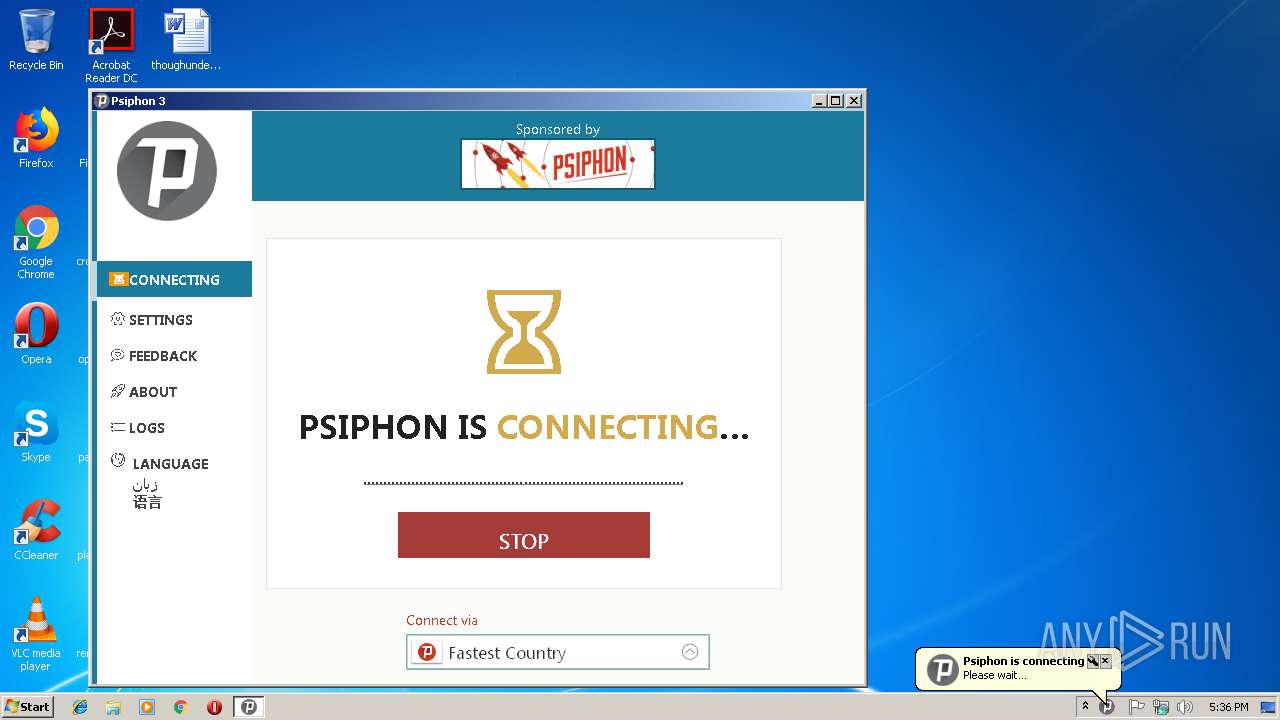
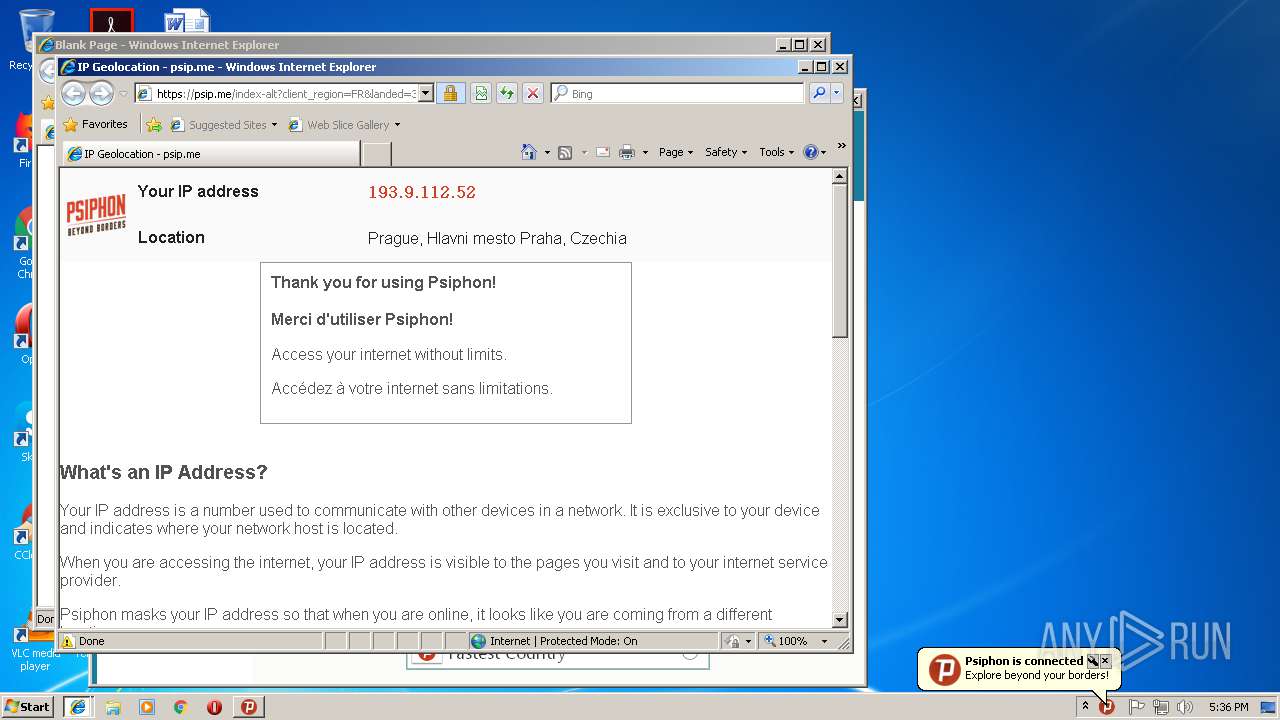
4072 | psiphon-tunnel-core.exe | POST | — | 213.108.110.83:80 | http://www.soupsoptbydesign.com/ | NL | — | — | suspicious |
3292 | iexplore.exe | GET | 404 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | xml | 345 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4072 | psiphon-tunnel-core.exe | 82.102.23.146:443 | — | — | GB | unknown |
4072 | psiphon-tunnel-core.exe | 37.46.114.23:443 | — | AltusHost B.V. | BG | unknown |
4072 | psiphon-tunnel-core.exe | 37.120.131.98:22 | — | Secure Data Systems SRL | RO | suspicious |
4072 | psiphon-tunnel-core.exe | 74.208.81.170:443 | — | 1&1 Internet SE | US | unknown |
4072 | psiphon-tunnel-core.exe | 128.127.104.95:53 | — | AltusHost B.V. | SE | suspicious |
4072 | psiphon-tunnel-core.exe | 213.108.110.83:80 | — | Greenhost BV | NL | suspicious |
4072 | psiphon-tunnel-core.exe | 104.237.139.112:53 | — | Linode, LLC | US | suspicious |
4072 | psiphon-tunnel-core.exe | 104.236.129.216:80 | — | Digital Ocean, Inc. | US | suspicious |
4072 | psiphon-tunnel-core.exe | 37.218.246.139:80 | — | Greenhost BV | NL | suspicious |
4072 | psiphon-tunnel-core.exe | 162.243.169.132:53 | — | Digital Ocean, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
prod.global.ssl.fastly.net |
| whitelisted |
a966.b.akamai.net |
| suspicious |
www.bing.com |
| whitelisted |
a317.w7.akamai.net |
| unknown |
a1827.g2.akamai.net |
| whitelisted |
a1020.na.akamai.net |
| unknown |
| whitelisted | |
a879.b.akamai.net |
| whitelisted |
ipfounder.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
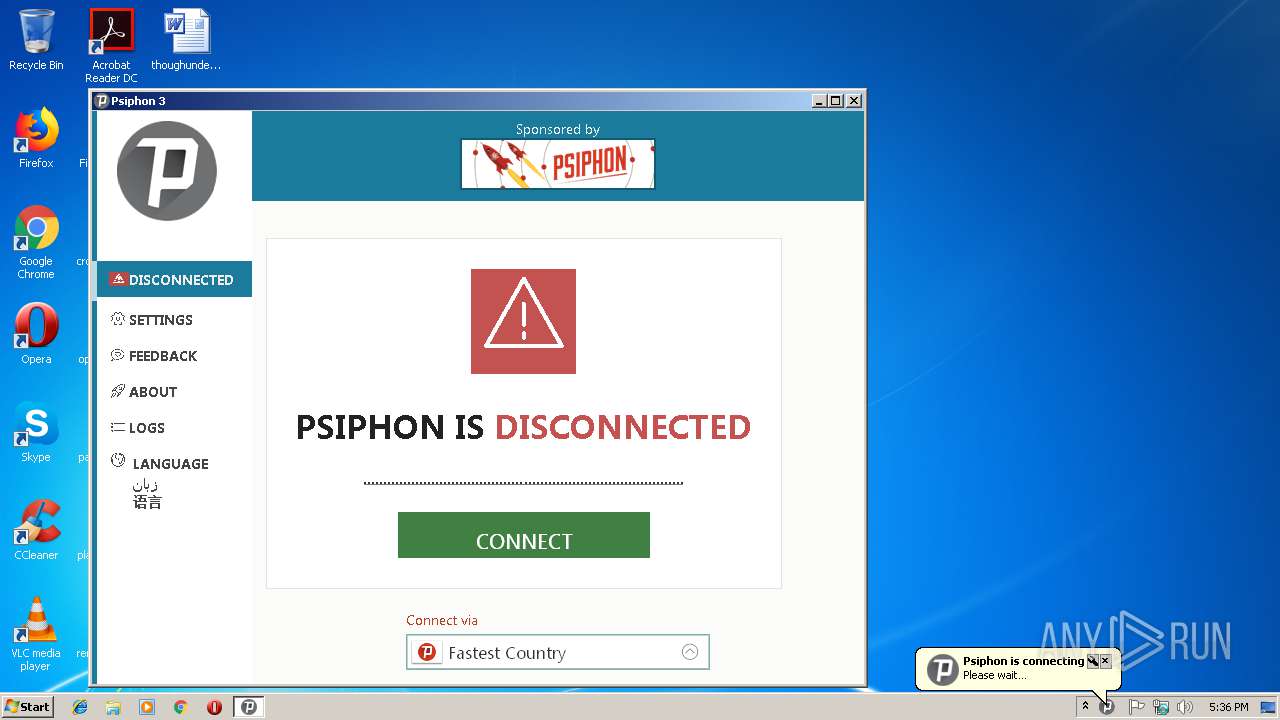
4072 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Psiphon3 VPN connection |
4072 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Psiphon3 VPN connection |
4072 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | ET DNS Non-DNS or Non-Compliant DNS traffic on DNS port Opcode 6 or 7 set |
4072 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | ET DNS Non-DNS or Non-Compliant DNS traffic on DNS port Opcode 8 through 15 set |
4072 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | ET DNS Non-DNS or Non-Compliant DNS traffic on DNS port Reserved Bit Set |
4072 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Psiphon3 VPN connection |
4072 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Psiphon3 VPN connection |
4072 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Psiphon3 VPN connection |
4072 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Psiphon3 VPN connection |
4072 | psiphon-tunnel-core.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Psiphon3 VPN connection |
Process | Message |
|---|---|
psiphon3.exe | |
psiphon3.exe | |
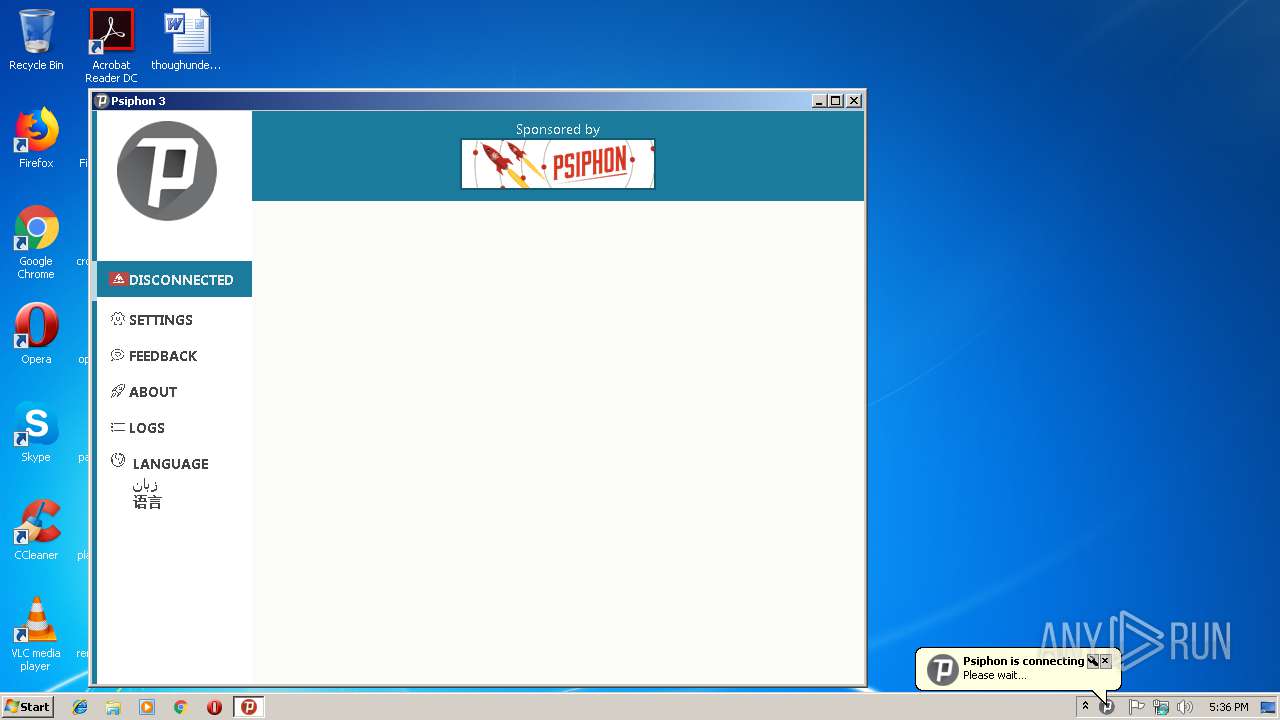
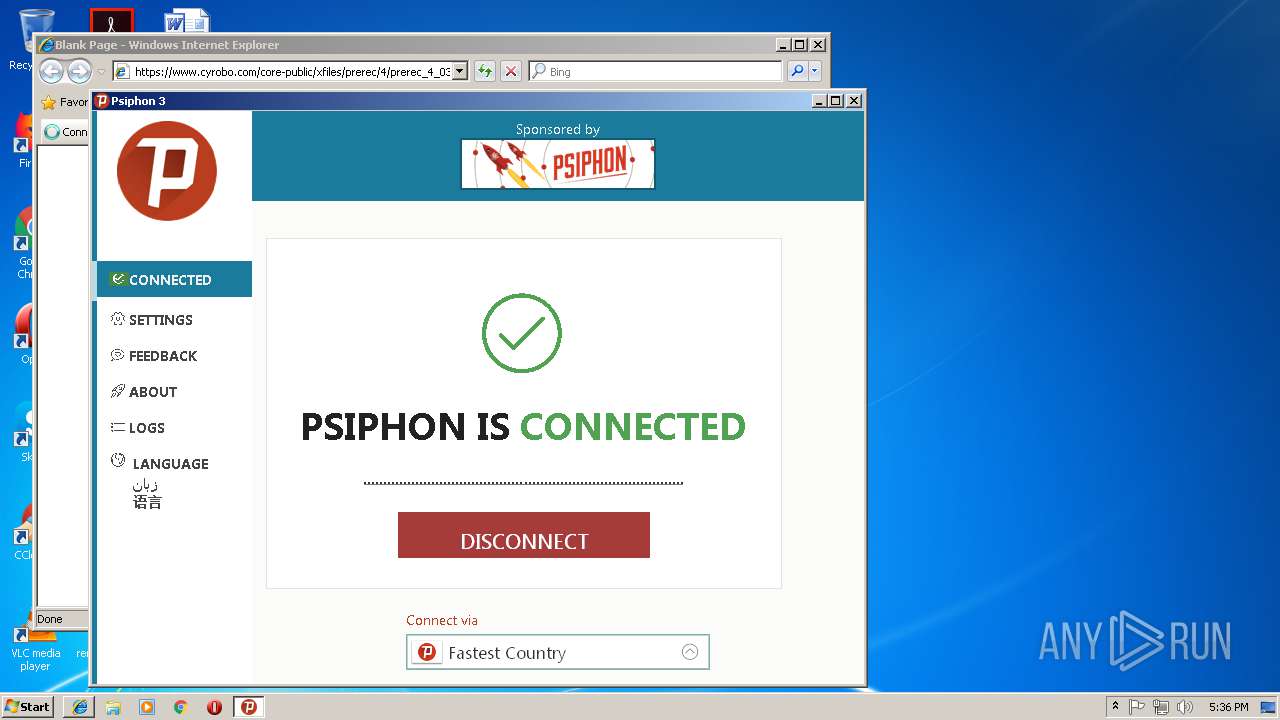
psiphon3.exe | Psiphon Tunnel connecting... |
psiphon3.exe | |
psiphon3.exe | |
psiphon3.exe | |
psiphon3.exe | b.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/bifurcation/mint":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/bifurcation/mint/syntax":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/cheekybits/genny/generic":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/golang/protobuf/proto":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/grafov/m3u8":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/hashicorp/golang-lru":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/hashicorp/golang-lru/simplelru":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/juju/ratelimit":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/aes12":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go-certificates":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go/internal/ackhandler":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go/internal/congestion":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go/internal/crypto":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go/internal/flowcontrol":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go/internal/handshake":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go/internal/protocol":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go/internal/utils":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go/internal/wire":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go/qerr":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/refraction-networking/utls":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/refraction-networking/utls/cpu":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/sergeyfrolov/bsbuffer":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/sergeyfrolov/gotapdance/protobuf":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/sergeyfrolov/gotapdance/tapdance":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/sirupsen/logrus":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/zach-klippenstein/goregen":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/crypto/chacha20poly1305":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/crypto/curve25519":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/crypto/hkdf":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/crypto/internal/chacha20":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/crypto/poly1305":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/crypto/ssh/terminal":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/net/http/httpguts":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/net/http2/hpack":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/net/idna":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/net/proxy":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/sys/windows":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/text/secure/bidirule":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/text/transform":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/text/unicode/bidi":"eed250f","github.com |
psiphon3.exe | b.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/bifurcation/mint":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/bifurcation/mint/syntax":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/cheekybits/genny/generic":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/golang/protobuf/proto":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/grafov/m3u8":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/hashicorp/golang-lru":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/hashicorp/golang-lru/simplelru":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/juju/ratelimit":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/aes12":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go-certificates":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go/internal/ackhandler":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go/internal/congestion":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go/internal/crypto":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go/internal/flowcontrol":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go/internal/handshake":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go/internal/protocol":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go/internal/utils":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go/internal/wire":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/lucas-clemente/quic-go/qerr":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/refraction-networking/utls":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/refraction-networking/utls/cpu":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/sergeyfrolov/bsbuffer":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/sergeyfrolov/gotapdance/protobuf":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/sergeyfrolov/gotapdance/tapdance":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/sirupsen/logrus":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/github.com/zach-klippenstein/goregen":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/crypto/chacha20poly1305":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/crypto/curve25519":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/crypto/hkdf":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/crypto/internal/chacha20":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/crypto/poly1305":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/crypto/ssh/terminal":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/net/http/httpguts":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/net/http2/hpack":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/net/idna":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/net/proxy":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/sys/windows":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/text/secure/bidirule":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/text/transform":"eed250f","github.com/Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/text/unicode/bidi":"eed250f","github.com |
psiphon3.exe | /Psiphon-Labs/psiphon-tunnel-core/vendor/golang.org/x/text/unicode/norm":"eed250f"},"goVersion":"go1.11.1"}},"noticeType":"BuildInfo","showUser":false,"timestamp":"2018-12-25T17:36:25.619Z"},"msg":"CoreNotice","timestamp!!timestamp":"2018-12-25T17:36:25.635Z"}
|
psiphon3.exe | |