| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/99e33d3f-629c-4a50-bbb6-454aa3fb4ed4 |
| Verdict: | Malicious activity |
| Analysis date: | August 03, 2024, 11:42:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3CA4CA5ED9B93988BCA6461DA327469A |
| SHA1: | 5C662A3EFA9E68AD8F0D25A21EB6E53A653B27F8 |
| SHA256: | 399A2A4B7536391205B5C657DD1148DF9CADF7CE7C00C73C34BA5DB0E501601F |
| SSDEEP: | 98304:9AIuVA2CdUowORN8cHt+n03D9z1lcI3Hf8HUhIiJQMnObxDYEef3D3kOqoujUFk6:cxt7U |
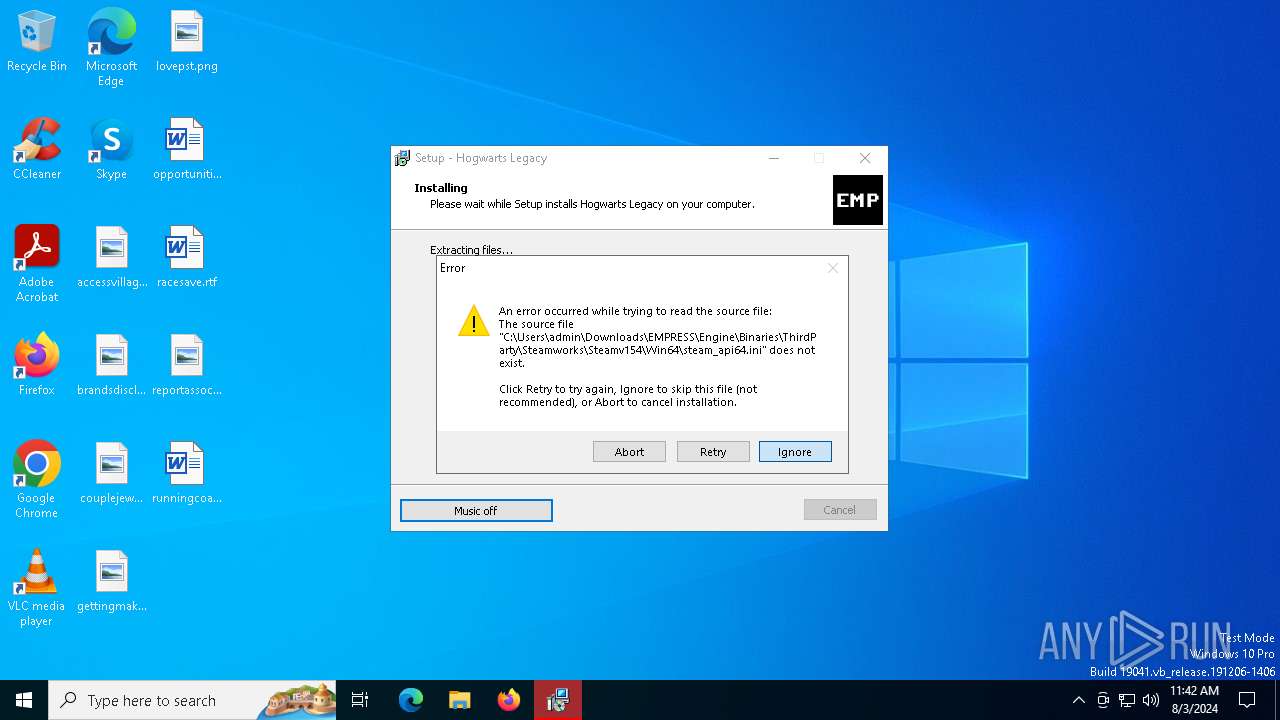
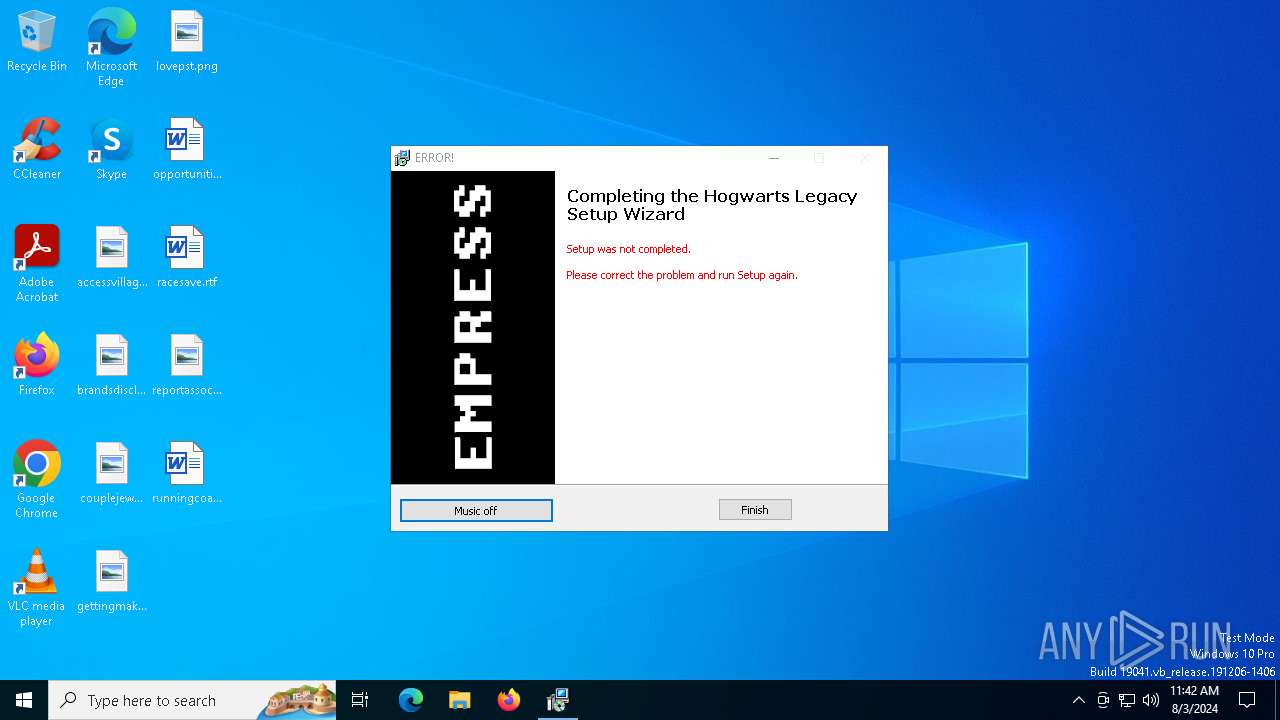
MALICIOUS
Drops the executable file immediately after the start
- setup.exe (PID: 6472)
- unins000.exe (PID: 5060)
- _iu14D2N.tmp (PID: 3268)
- setup.tmp (PID: 6496)
SUSPICIOUS
Reads the Windows owner or organization settings
- setup.tmp (PID: 6496)
- _iu14D2N.tmp (PID: 3268)
Executable content was dropped or overwritten
- setup.exe (PID: 6472)
- setup.tmp (PID: 6496)
- unins000.exe (PID: 5060)
- _iu14D2N.tmp (PID: 3268)
Starts application with an unusual extension
- unins000.exe (PID: 5060)
Starts itself from another location
- unins000.exe (PID: 5060)
Process drops legitimate windows executable
- _iu14D2N.tmp (PID: 3268)
- setup.tmp (PID: 6496)
INFO
Checks supported languages
- setup.exe (PID: 6472)
- setup.tmp (PID: 6496)
- unins000.exe (PID: 5060)
- _iu14D2N.tmp (PID: 3268)
Create files in a temporary directory
- setup.exe (PID: 6472)
- unins000.exe (PID: 5060)
- _iu14D2N.tmp (PID: 3268)
- setup.tmp (PID: 6496)
Reads the computer name
- setup.tmp (PID: 6496)
- _iu14D2N.tmp (PID: 3268)
Creates a software uninstall entry
- setup.tmp (PID: 6496)
Creates files in the program directory
- setup.tmp (PID: 6496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:10:02 05:04:04+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 86016 |
| InitializedDataSize: | 53760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16478 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
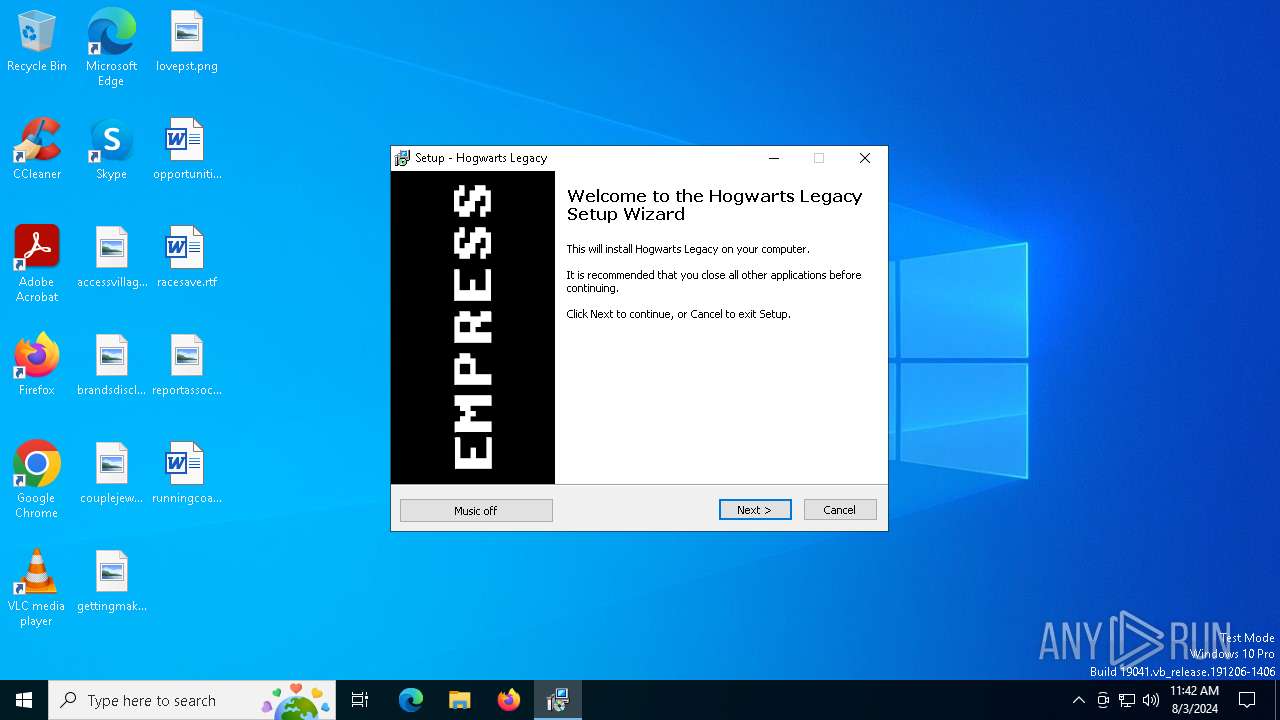
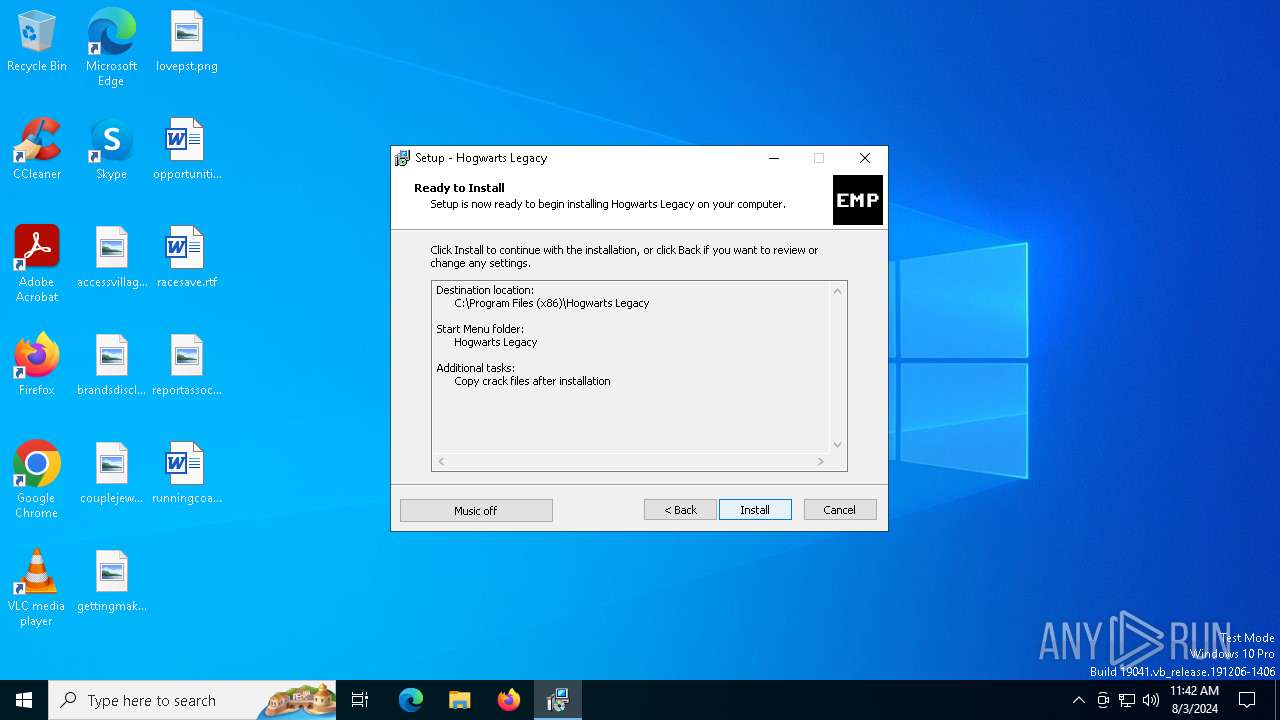
| FileDescription: | Hogwarts Legacy Setup |
| FileVersion: | |
| LegalCopyright: | EMPRESS |
| ProductName: | Hogwarts Legacy |
| ProductVersion: |
Total processes
140
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3268 | "C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp" /SECONDPHASE="C:\Program Files (x86)\Hogwarts Legacy\unins000.exe" /FIRSTPHASEWND=$A02C4 /VERYSILENT | C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | unins000.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 5060 | "C:\Program Files (x86)\Hogwarts Legacy\unins000.exe" /VERYSILENT | C:\Program Files (x86)\Hogwarts Legacy\unins000.exe | setup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 6412 | "C:\Users\admin\Downloads\setup.exe" | C:\Users\admin\Downloads\setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Hogwarts Legacy Setup Exit code: 3221226540 Version: Modules
| |||||||||||||||
| 6472 | "C:\Users\admin\Downloads\setup.exe" | C:\Users\admin\Downloads\setup.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Hogwarts Legacy Setup Exit code: 0 Version: Modules
| |||||||||||||||
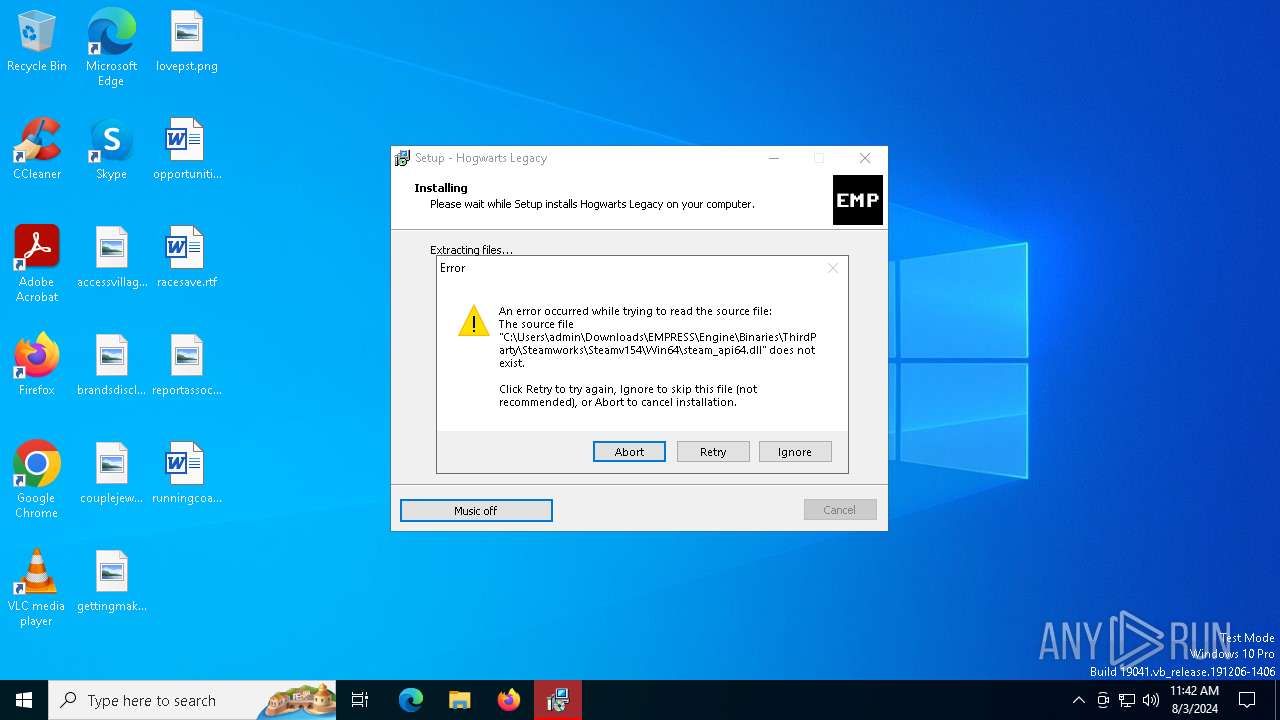
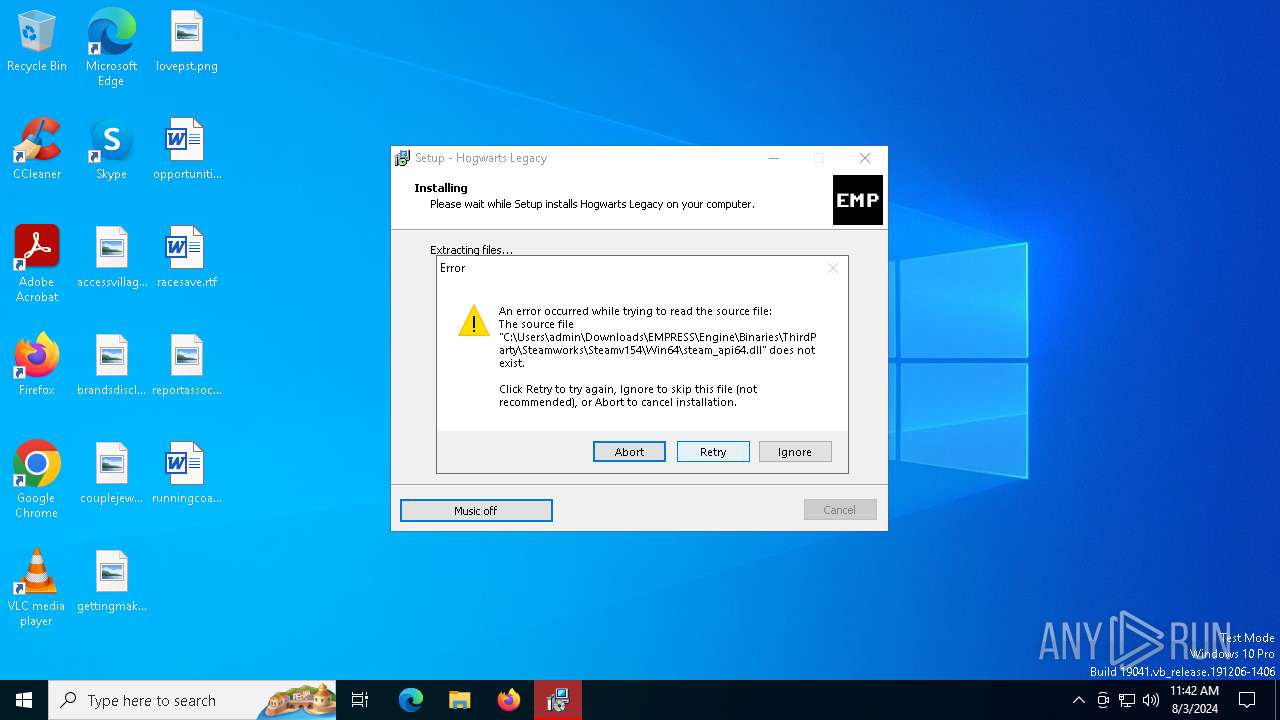
| 6496 | "C:\Users\admin\AppData\Local\Temp\is-IKUQV.tmp\setup.tmp" /SL5="$501E6,2539774,140800,C:\Users\admin\Downloads\setup.exe" | C:\Users\admin\AppData\Local\Temp\is-IKUQV.tmp\setup.tmp | setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
602
Read events
577
Write events
20
Delete events
5
Modification events
| (PID) Process: | (6496) setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 601900009443DD369AE5DA01 | |||
| (PID) Process: | (6496) setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: C0B48083F456693F723425C623A32C0E7D3D1A9CED24748A34B54DE3C96F62CA | |||
| (PID) Process: | (6496) setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
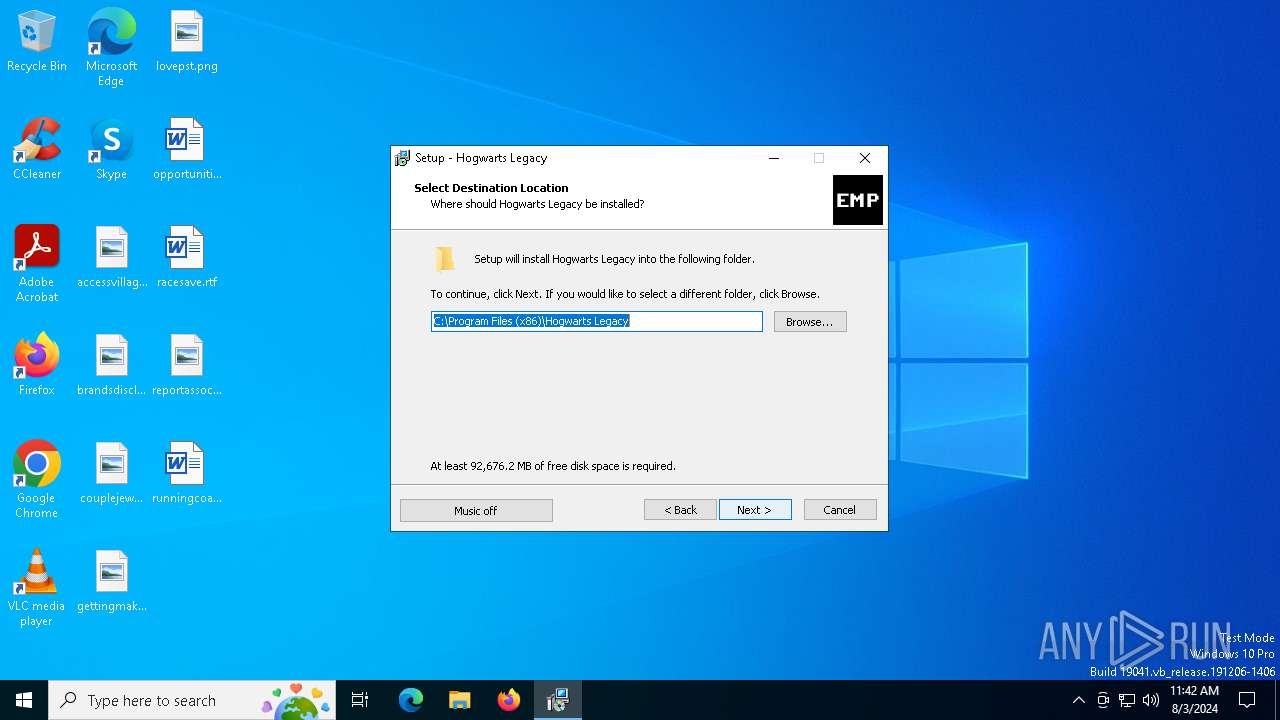
| (PID) Process: | (6496) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Hogwarts Legacy_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.1.ee2 (u) | |||
| (PID) Process: | (6496) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Hogwarts Legacy_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files (x86)\Hogwarts Legacy | |||
| (PID) Process: | (6496) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Hogwarts Legacy_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files (x86)\Hogwarts Legacy\ | |||
| (PID) Process: | (6496) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Hogwarts Legacy_is1 |
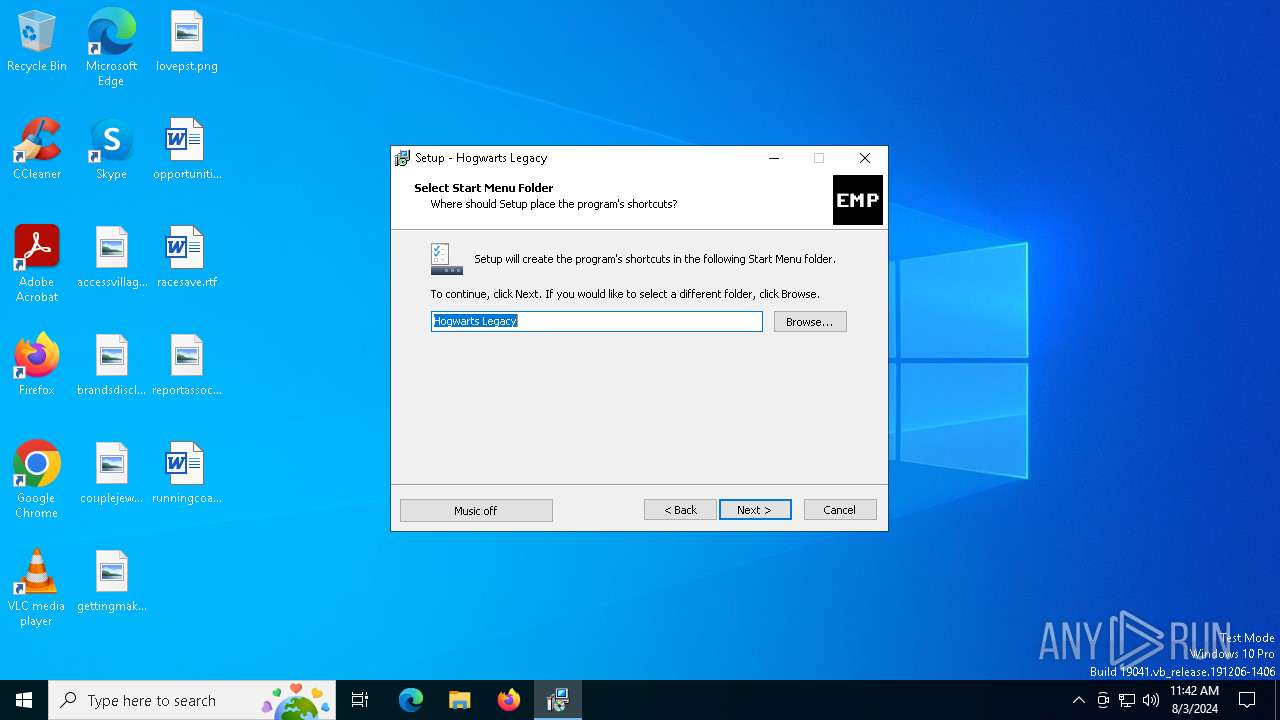
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Hogwarts Legacy | |||
| (PID) Process: | (6496) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Hogwarts Legacy_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (6496) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Hogwarts Legacy_is1 |
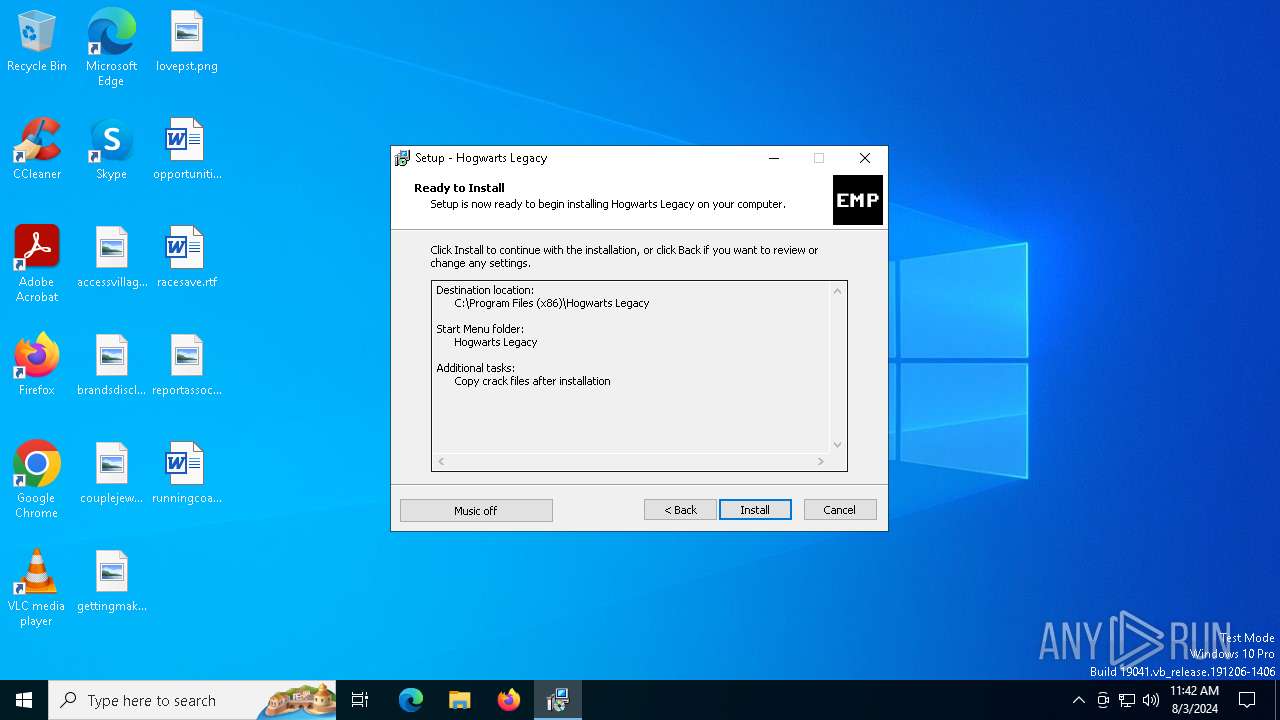
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: crackcheck | |||
| (PID) Process: | (6496) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Hogwarts Legacy_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: | |||
Executable files
11
Suspicious files
2
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6496 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2IF7S.tmp\empress.mp3 | binary | |
MD5:93C1572E2DAEDE3AE3A793C7932E9B73 | SHA256:CA01CE693AA9D28AD329F2F3E4C2103D2A05825C94191FFFF69885EAC23FCA91 | |||
| 6472 | setup.exe | C:\Users\admin\AppData\Local\Temp\is-IKUQV.tmp\setup.tmp | executable | |
MD5:AE9890548F2FCAB56A4E9AE446F55B3F | SHA256:09AF8004B85478E1ECA09FA4CB5E3081DDDCB2F68A353F3EF6849D92BE47B449 | |||
| 3268 | _iu14D2N.tmp | C:\Users\admin\AppData\Local\Temp\is-7M4BD.tmp\_isetup\_setup64.tmp | executable | |
MD5:4FF75F505FDDCC6A9AE62216446205D9 | SHA256:A4C86FC4836AC728D7BD96E7915090FD59521A9E74F1D06EF8E5A47C8695FD81 | |||
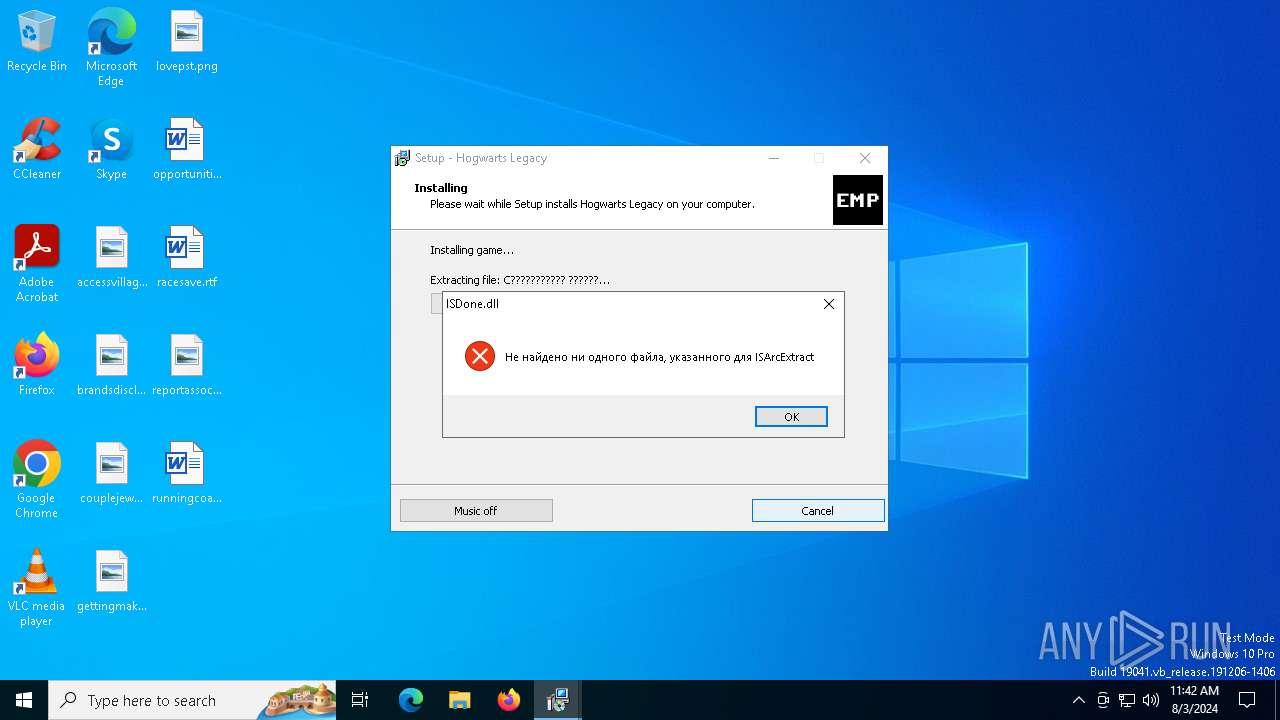
| 6496 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2IF7S.tmp\unarc.dll | executable | |
MD5:ECCE36A404BD861E727FA735035BED95 | SHA256:62DCA0D734D95E80340DEADE51BBC0DC8BFB39D83B7700633623C9FFB955B024 | |||
| 6496 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2IF7S.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 6496 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2IF7S.tmp\records.inf | text | |
MD5:0754C1398F3FDD27487DA1C9C099A01A | SHA256:6CFE824E687DBF482F2E91AEC11C4A36BF4CE3E9331F7B65EF083F7018F1107B | |||
| 5060 | unins000.exe | C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | executable | |
MD5:550D67BBF32BE69372E718D6C16837DD | SHA256:746F3C12C4897549372857F1B84F739C4FDBE996260518ED4E4F1795CC866B17 | |||
| 6496 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2IF7S.tmp\English.ini | text | |
MD5:B031BEE9106D82782B43BDF5D4AD79B0 | SHA256:E1B6F4DC9BA12E110B33D370E8F06F176228059C42754BE5DA7B92AB939FF38E | |||
| 6496 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2IF7S.tmp\_isetup\_setup64.tmp | executable | |
MD5:4FF75F505FDDCC6A9AE62216446205D9 | SHA256:A4C86FC4836AC728D7BD96E7915090FD59521A9E74F1D06EF8E5A47C8695FD81 | |||
| 6496 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-2IF7S.tmp\bass.dll | executable | |
MD5:C5B3059004E2C7631915EC044F4E6C63 | SHA256:3CD00F456F51829EDA119E0E133ACC1E45A5930D61FC335A2E9AA688A836A24D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
36
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5244 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5244 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7080 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7024 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
840 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1716 | RUXIMICS.exe | 52.183.220.149:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2120 | MoUsoCoreWorker.exe | 52.183.220.149:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
5336 | SearchApp.exe | 2.23.209.189:443 | www.bing.com | Akamai International B.V. | GB | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5244 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5244 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |