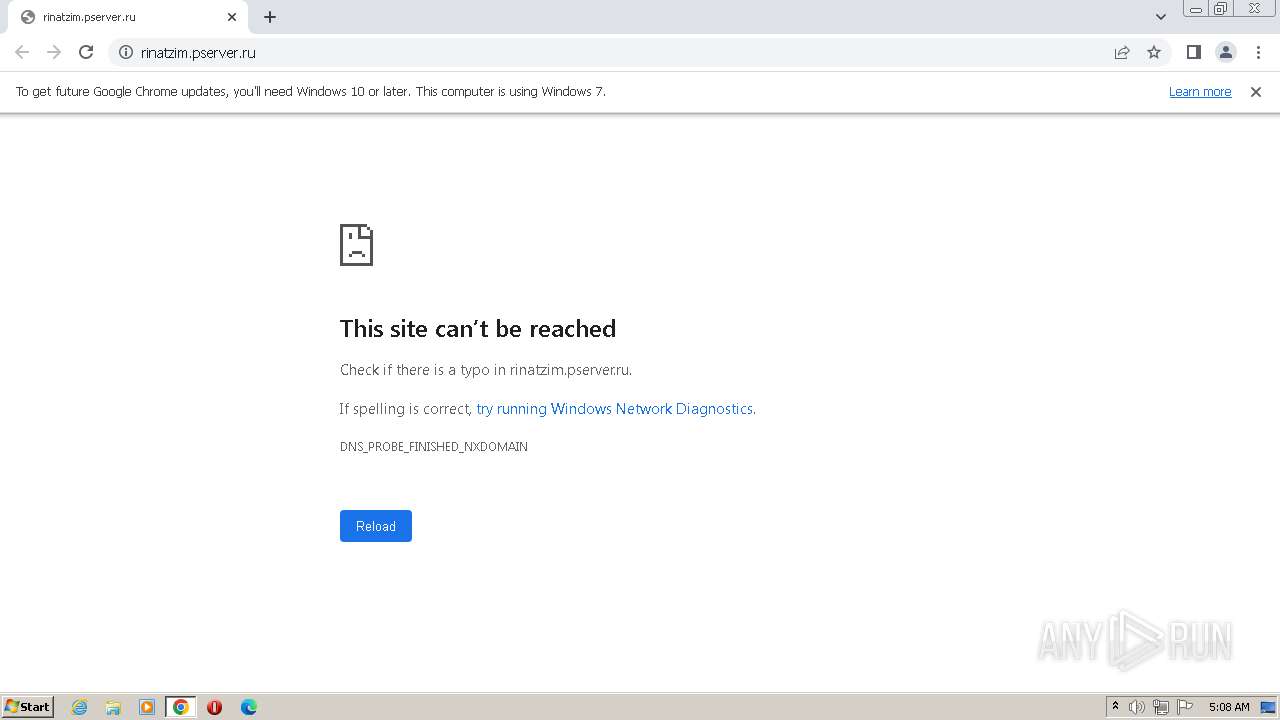
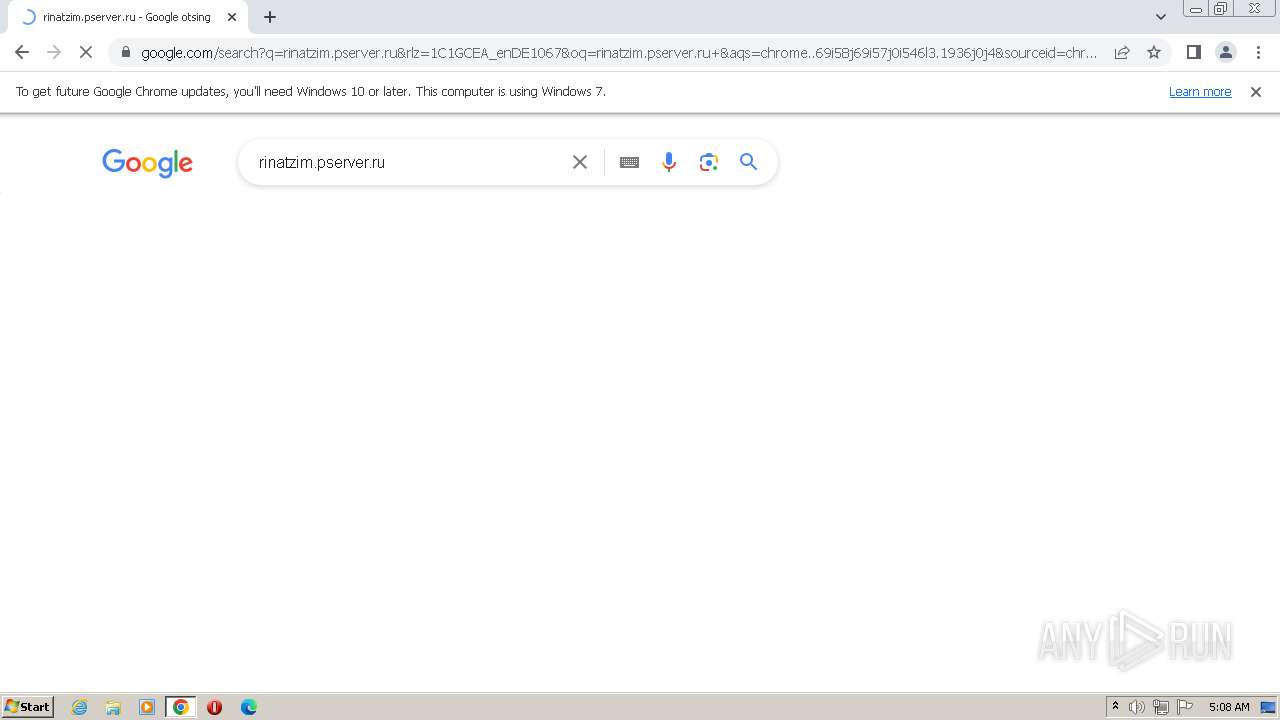
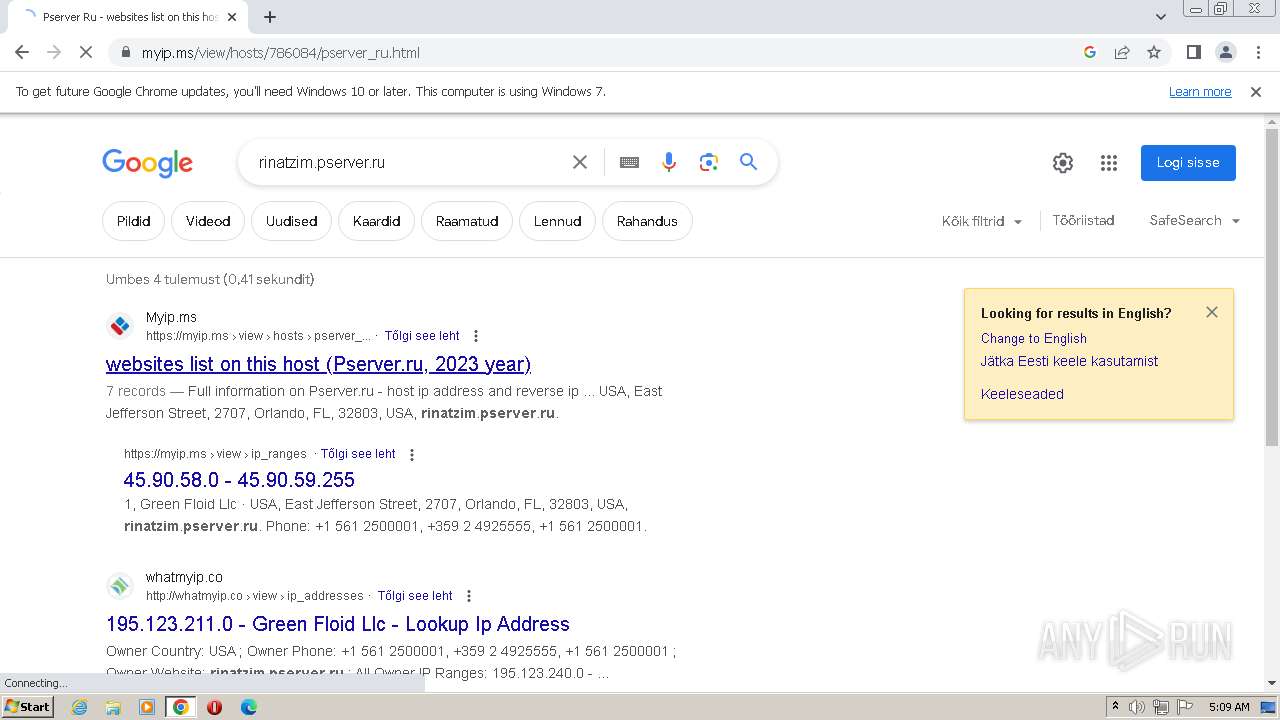
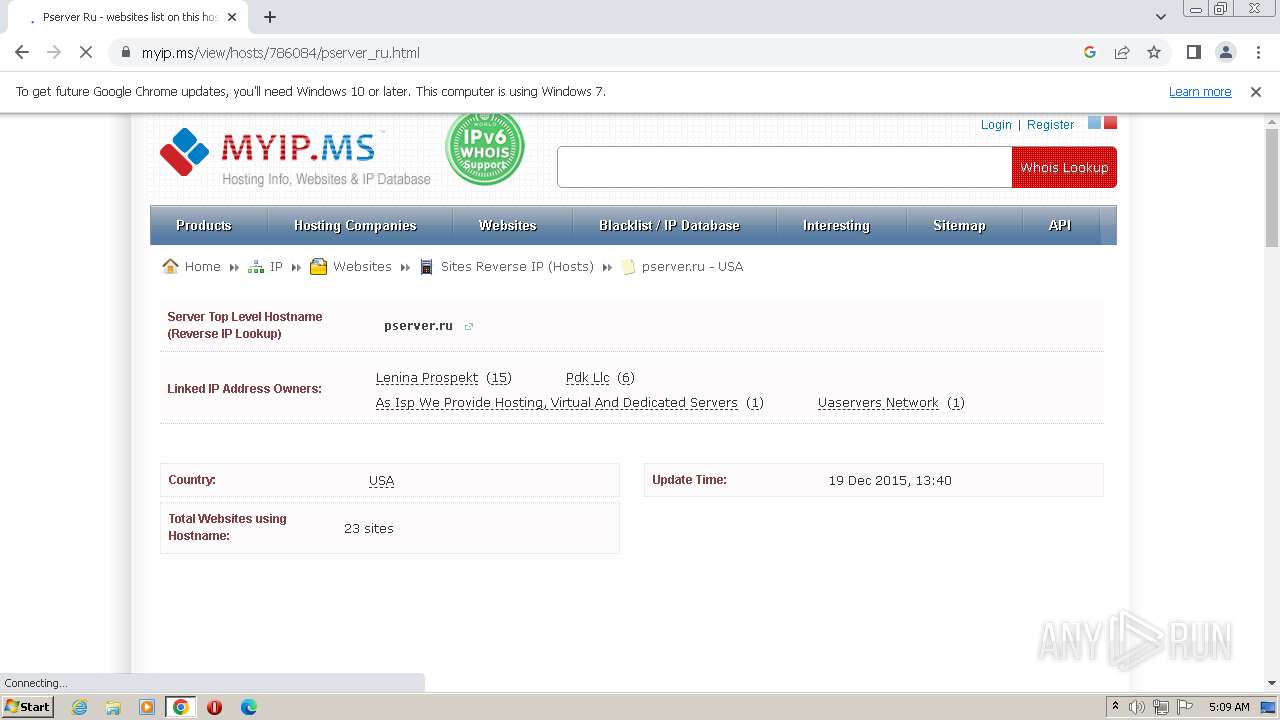
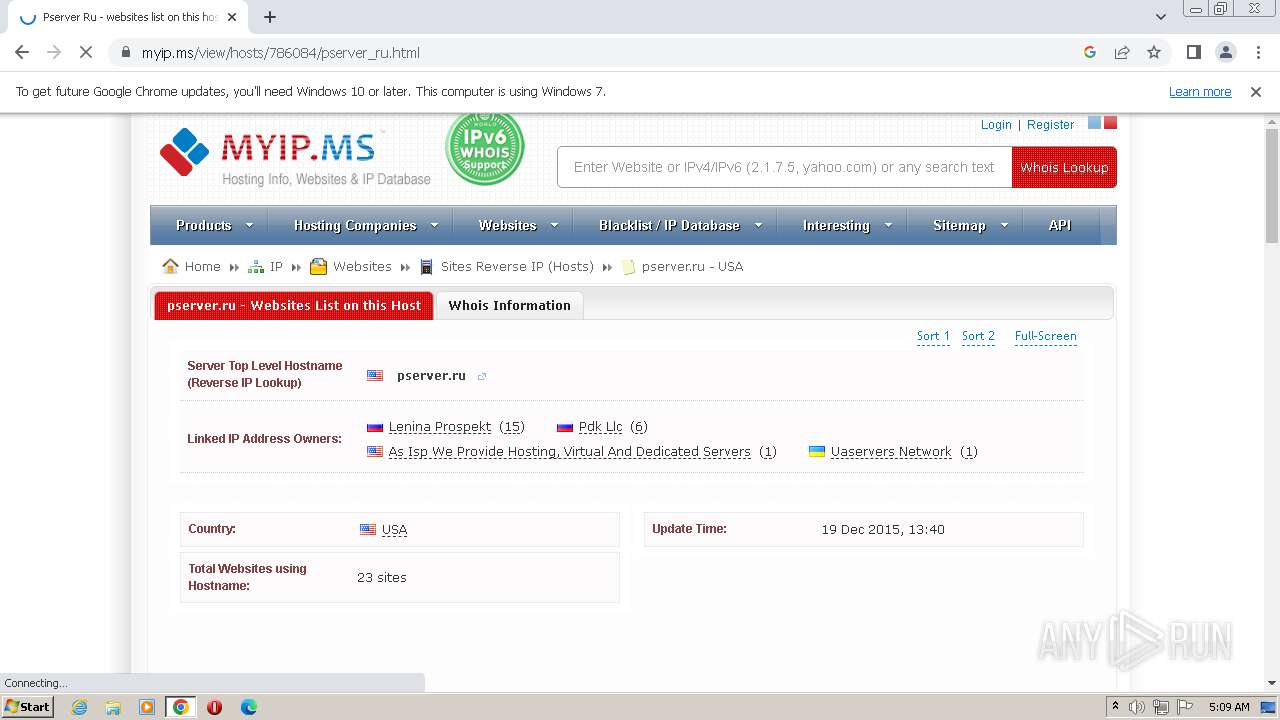
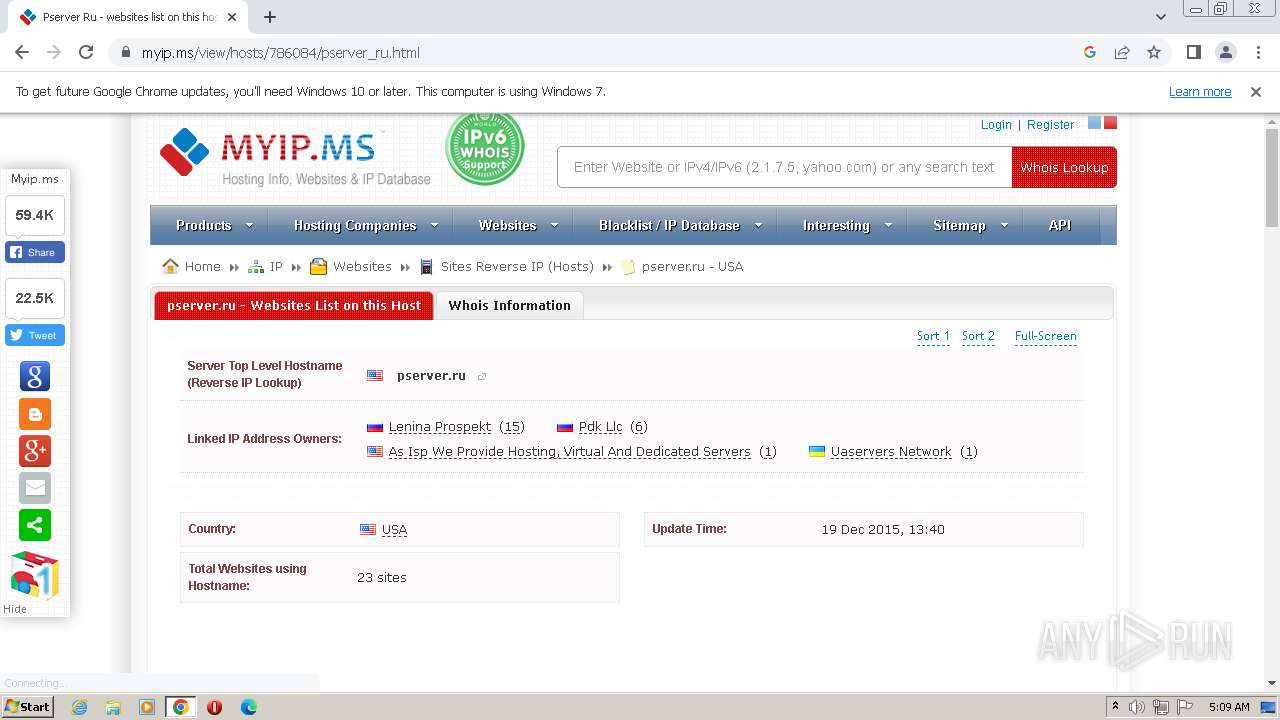
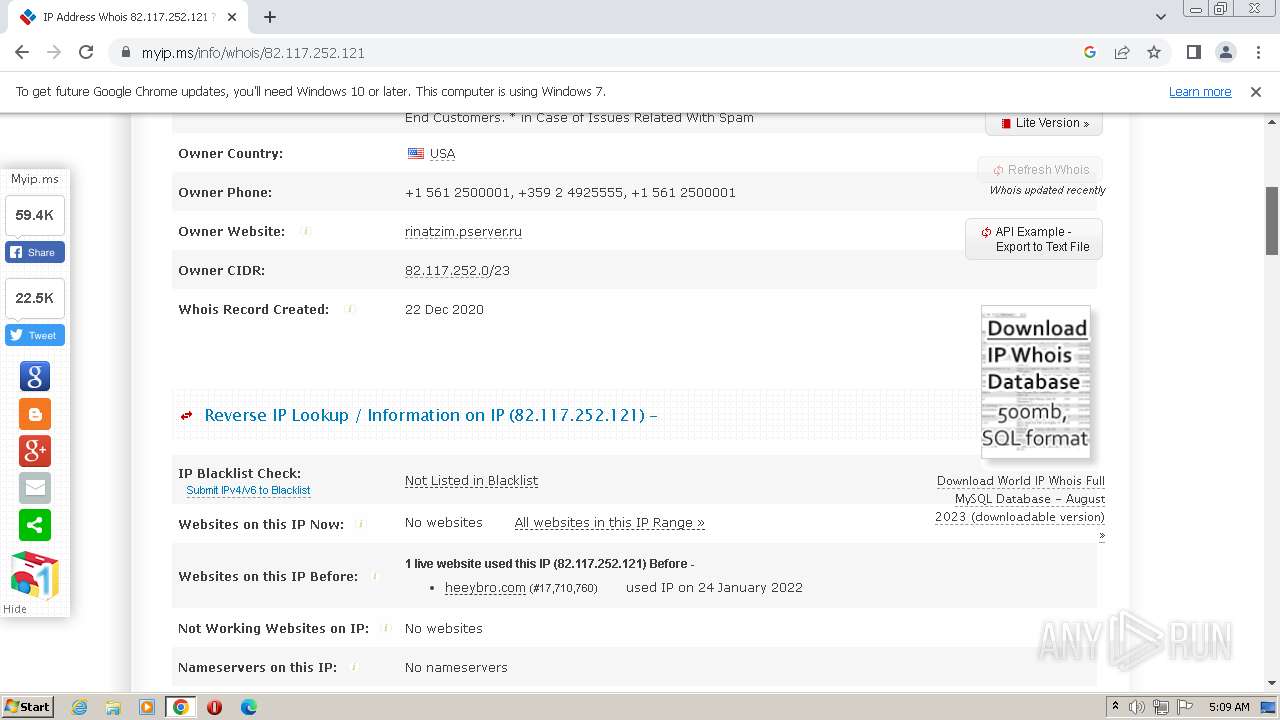
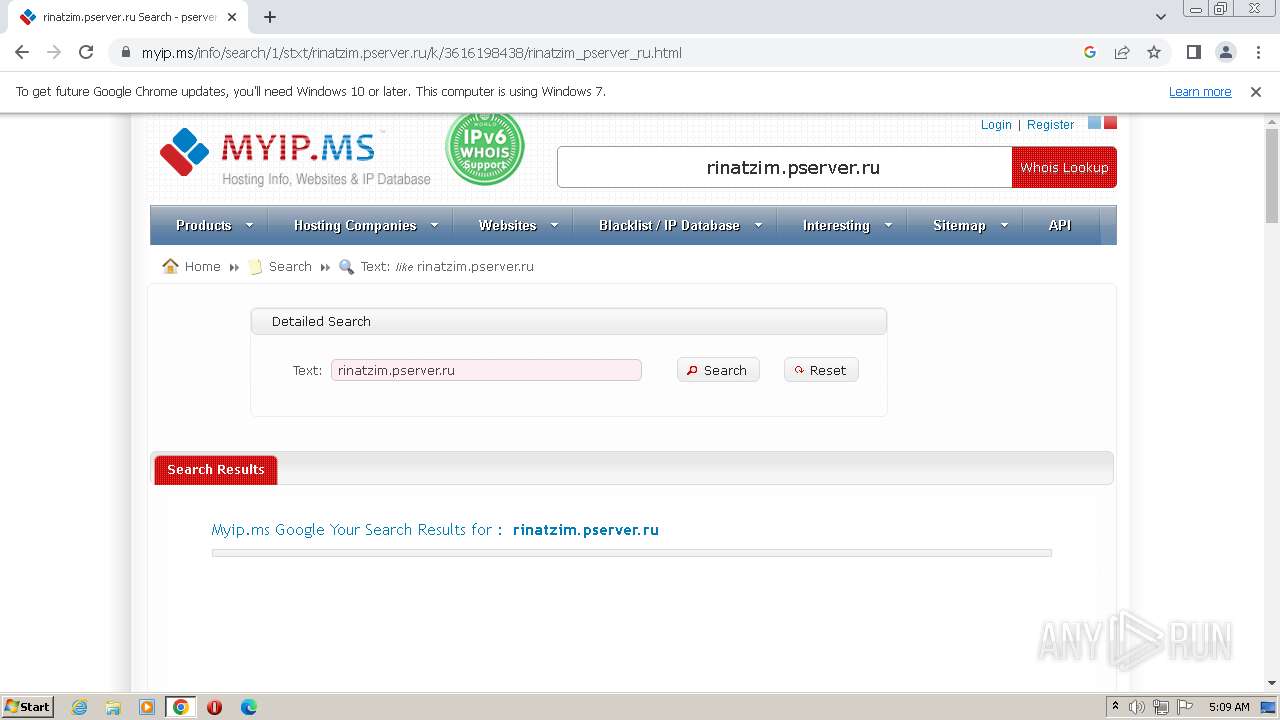
| URL: | http://rinatzim.pserver.ru |
| Full analysis: | https://app.any.run/tasks/e7417703-c964-414d-80dc-3c165c87fc2e |
| Verdict: | Malicious activity |
| Analysis date: | August 21, 2023, 04:08:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 50062A23883BA2CD3D3444F3123FACAC |
| SHA1: | 684B068E91093FC8ACC12E8C9EA6F2F22ACBD127 |
| SHA256: | 39703BA215F11AD6A9DF59E53CE86220D9575548428687DD5148576B26E1C808 |
| SSDEEP: | 3:N1KMf5PTA8:CMF7 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
The process uses the downloaded file
- chrome.exe (PID: 2388)
- chrome.exe (PID: 3984)
- chrome.exe (PID: 664)
Reads the computer name
- wmpnscfg.exe (PID: 4048)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 4048)
Application launched itself
- chrome.exe (PID: 3500)
Checks supported languages
- wmpnscfg.exe (PID: 4048)
Manual execution by a user
- wmpnscfg.exe (PID: 4048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
82
Monitored processes
48
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --mojo-platform-channel-handle=3916 --field-trial-handle=1176,i,13732802018480874372,12012089409349266808,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=28 --mojo-platform-channel-handle=4212 --field-trial-handle=1176,i,13732802018480874372,12012089409349266808,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3228 --field-trial-handle=1176,i,13732802018480874372,12012089409349266808,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --mojo-platform-channel-handle=1020 --field-trial-handle=1176,i,13732802018480874372,12012089409349266808,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3856 --field-trial-handle=1176,i,13732802018480874372,12012089409349266808,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=36 --mojo-platform-channel-handle=1008 --field-trial-handle=1176,i,13732802018480874372,12012089409349266808,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=37 --mojo-platform-channel-handle=4272 --field-trial-handle=1176,i,13732802018480874372,12012089409349266808,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6f238b38,0x6f238b48,0x6f238b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4176 --field-trial-handle=1176,i,13732802018480874372,12012089409349266808,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1432 --field-trial-handle=1176,i,13732802018480874372,12012089409349266808,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
5 254
Read events
5 134
Write events
116
Delete events
4
Modification events
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
8
Suspicious files
123
Text files
97
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFf967a.TMP | — | |
MD5:— | SHA256:— | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:B806171F9E7C87423595645872D869B0 | SHA256:851A8D533BEBF6A69C5518375396E97463302C1E2031D04F8EB5851C5C82CEB9 | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFf99a7.TMP | — | |
MD5:— | SHA256:— | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:E91E138A25FD7E5BCA5E60111F39C91A | SHA256:B1F7E3537A31A4B847F862858E5D2581993CC9372F19ABF19EA2A9185FE42A4F | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFf97a3.TMP | text | |
MD5:561161B0FF5BCA89BF47F8AC972A7499 | SHA256:ECCA5CCFA0BEED7581B39FCE03D0FD3B694DF0F92BFFF780F702118AD51FC17D | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFf9830.TMP | text | |
MD5:99EC94B2503FAD33EDAF99779EBA5BC8 | SHA256:DC554AB7EDCAD375F39ED106CA1EF9A89FB8D9063A4D08F377F2C80D66799D7E | |||
| 3500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\optimization_guide_hint_cache_store\LOG.old~RFfaa02.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
166
DNS requests
166
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | US | binary | 738 Kb | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | US | binary | 20.4 Kb | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | US | binary | 9.50 Kb | whitelisted |
868 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | US | — | — | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | US | binary | 9.73 Kb | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | US | binary | 43.3 Kb | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | US | binary | 85.7 Kb | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adalhupuujb3b4dixa2kdqxnyy3a_118.0.5956.0/jamhcnnkihinmdlkakkaopbjbbcngflc_118.0.5956.0_all_adbogfp66qhwrkq5secj6it77wva.crx3 | US | binary | 810 Kb | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adalhupuujb3b4dixa2kdqxnyy3a_118.0.5956.0/jamhcnnkihinmdlkakkaopbjbbcngflc_118.0.5956.0_all_adbogfp66qhwrkq5secj6it77wva.crx3 | US | binary | 278 Kb | whitelisted |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adasgb6qzo3kp62542i5hyaakdua_30.2/imefjhfbkmcmebodilednhmaccmincoa_30.2_win_kwiu22sehztwd3bii7gzgq4vri.crx3 | US | binary | 51.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
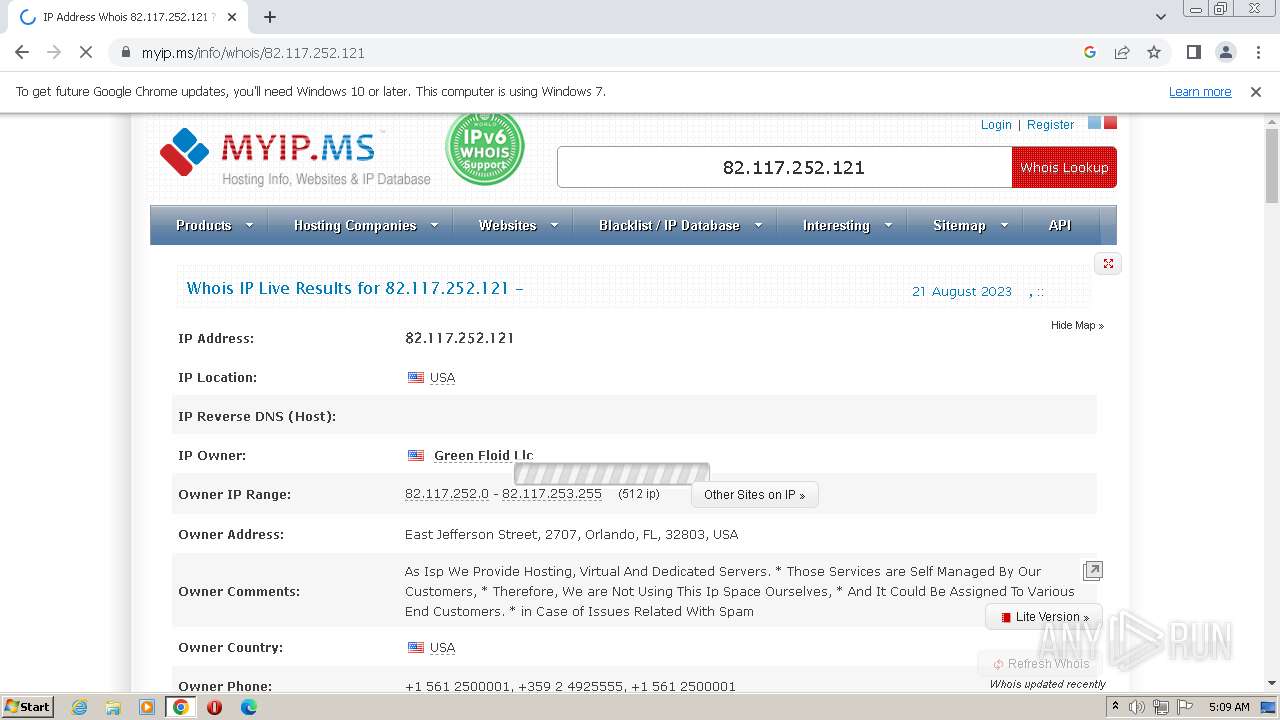
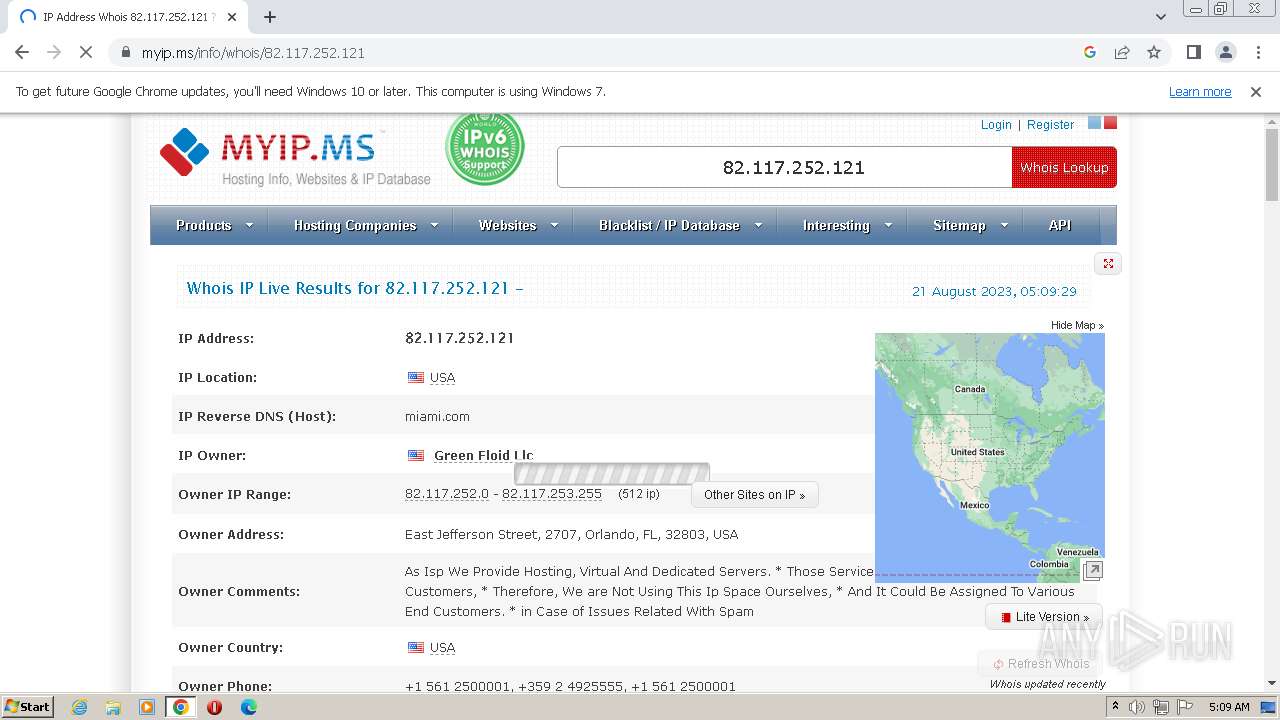
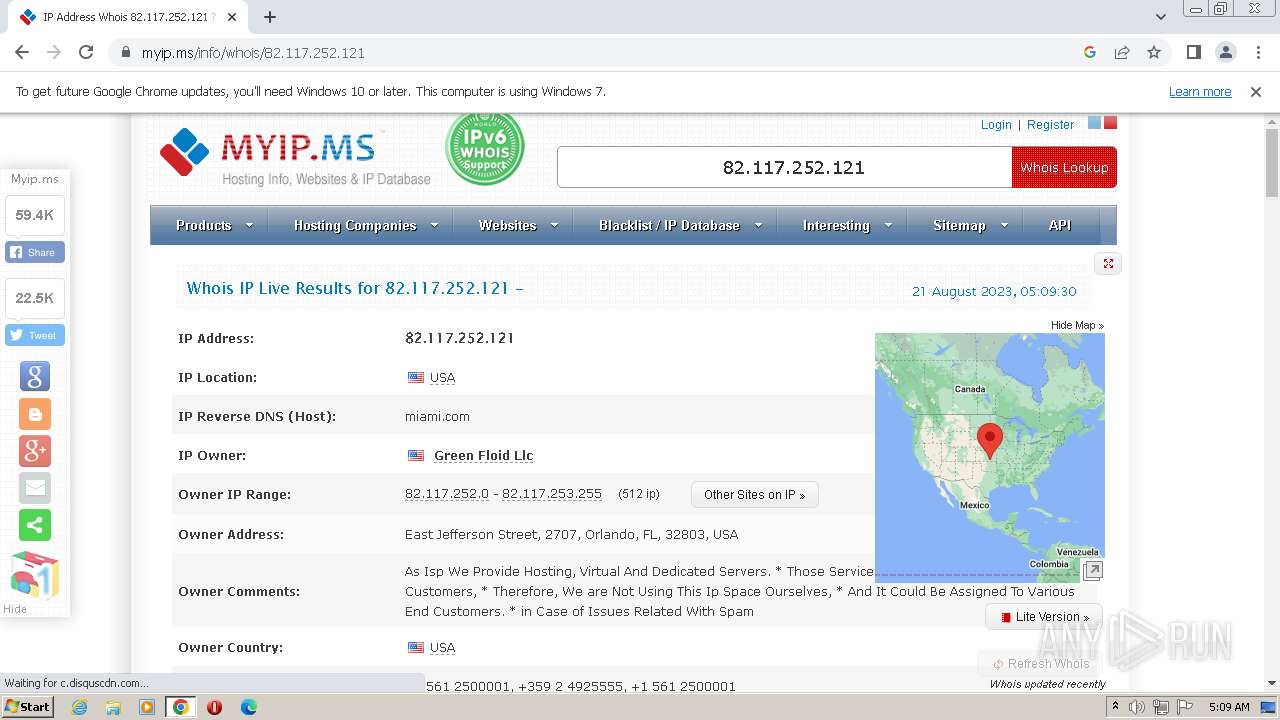
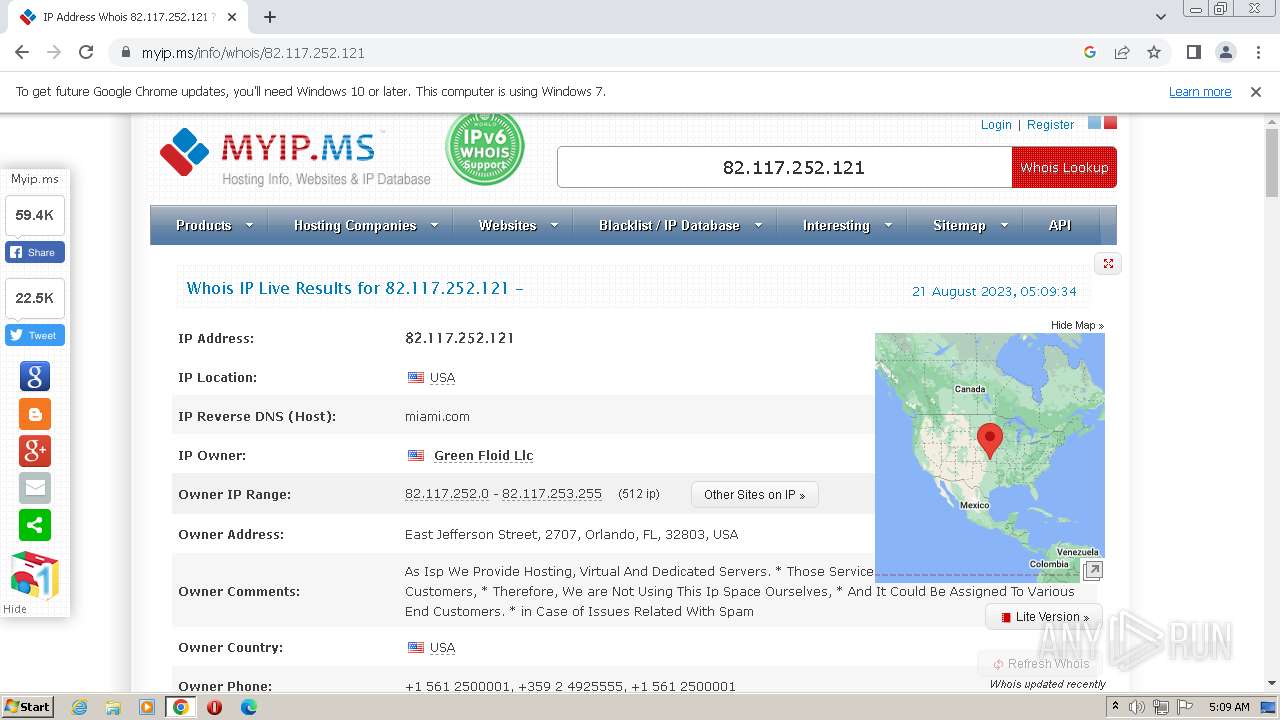
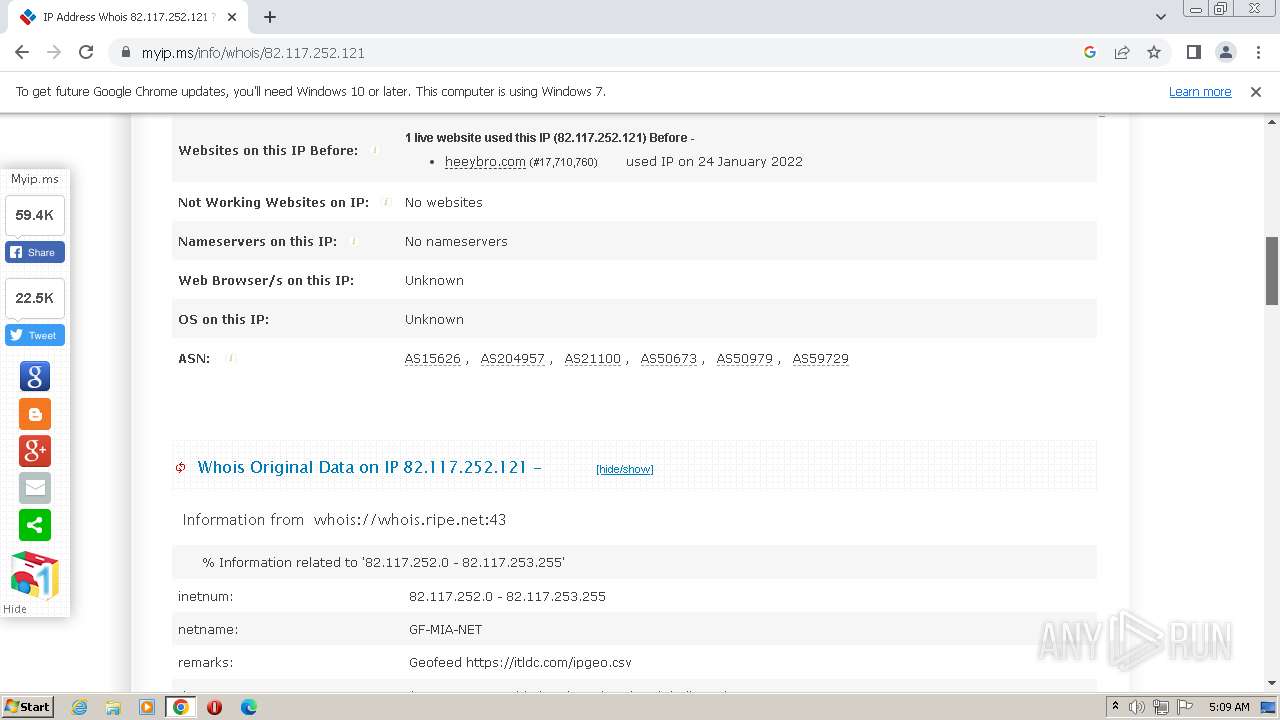
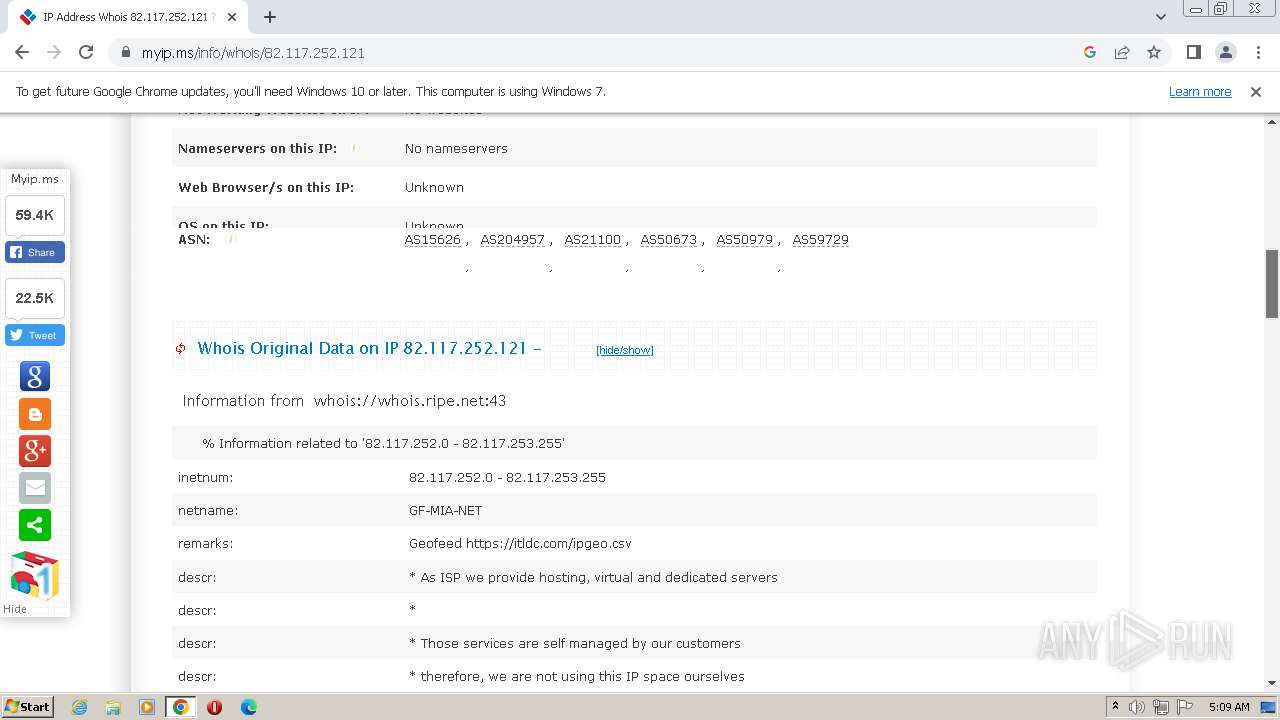
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2896 | chrome.exe | 172.217.18.13:443 | accounts.google.com | GOOGLE | US | whitelisted |
3500 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
2896 | chrome.exe | 142.250.185.132:443 | www.google.com | GOOGLE | US | whitelisted |
2896 | chrome.exe | 216.58.206.46:443 | consent.google.com | GOOGLE | US | whitelisted |
2896 | chrome.exe | 172.217.16.195:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
2896 | chrome.exe | 142.250.186.163:443 | www.gstatic.com | GOOGLE | US | whitelisted |
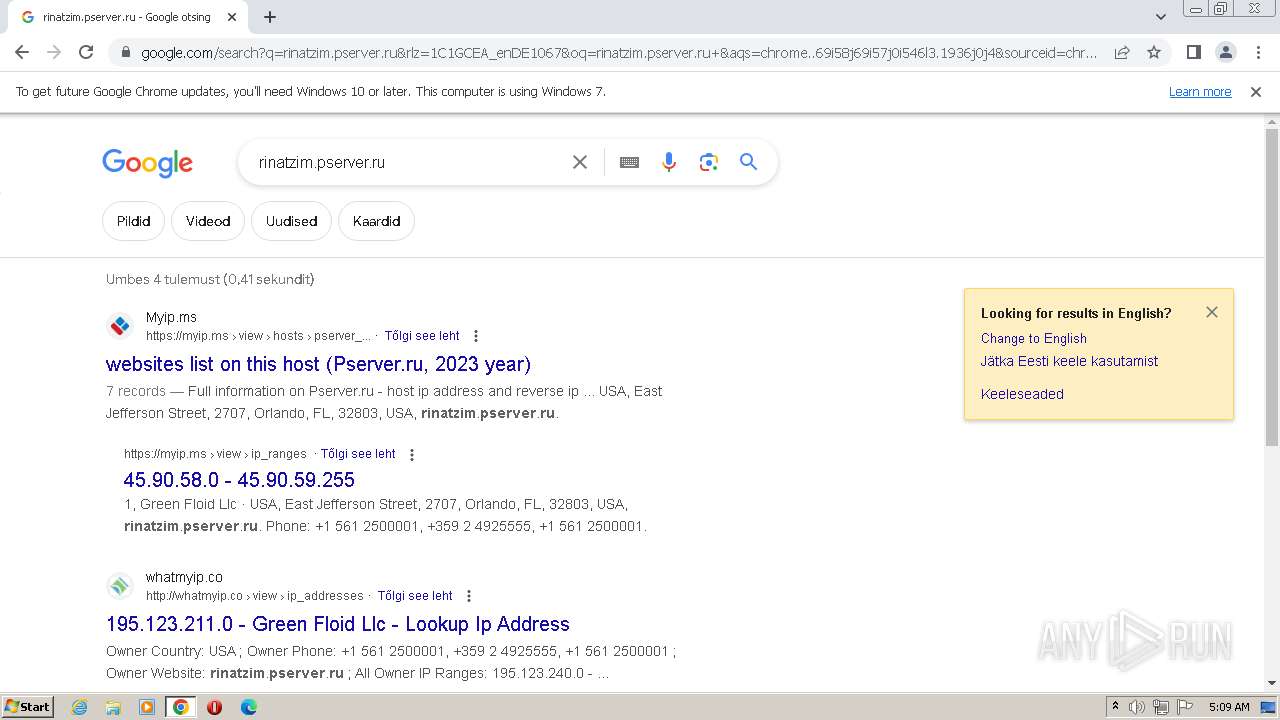
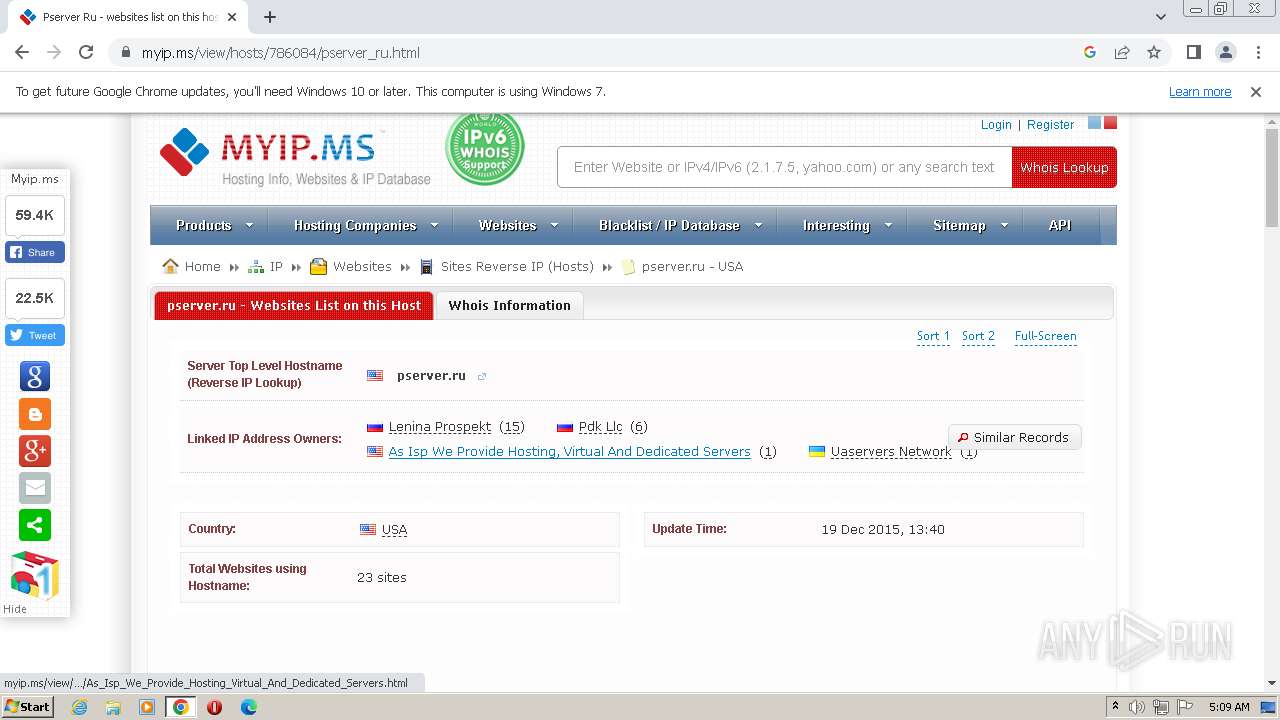
2896 | chrome.exe | 146.59.166.237:443 | myip.ms | OVH SAS | FR | suspicious |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2896 | chrome.exe | 216.58.206.42:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
2896 | chrome.exe | 13.32.99.10:443 | ws.sharethis.com | AMAZON-02 | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
rinatzim.pserver.ru |
| unknown |
google.com |
| malicious |
www.google.com |
| malicious |
fonts.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
consent.google.com |
| shared |
apis.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |