| URL: | https://test.com |
| Full analysis: | https://app.any.run/tasks/e047483c-f4fb-463d-830b-9f4a51e65e09 |
| Verdict: | Malicious activity |
| Analysis date: | December 13, 2024, 22:15:29 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 33FAA711A94A2028B5BAE1778126AEC0 |
| SHA1: | BA1598F6CF5E8512CD7D776D5DD8A5F79A4FED39 |
| SHA256: | 396936BD0BF0603D6784B65D03E96DAE90566C36B62661F28D4116C516524BCC |
| SSDEEP: | 3:N8IHKIn:2IqIn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 4648)
- powershell.exe (PID: 7264)
- powershell.exe (PID: 6344)
- powershell.exe (PID: 6004)
- powershell.exe (PID: 7676)
- powershell.exe (PID: 5872)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 4648)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4648)
- powershell.exe (PID: 7264)
- powershell.exe (PID: 6344)
- powershell.exe (PID: 6004)
- powershell.exe (PID: 7676)
- powershell.exe (PID: 5872)
Executing commands from ".cmd" file
- powershell.exe (PID: 4648)
- cmd.exe (PID: 6588)
- powershell.exe (PID: 7568)
- cmd.exe (PID: 4624)
- powershell.exe (PID: 936)
- cmd.exe (PID: 6456)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 4648)
- cmd.exe (PID: 6588)
- cmd.exe (PID: 7504)
- powershell.exe (PID: 7568)
- cmd.exe (PID: 4624)
- cmd.exe (PID: 6308)
- powershell.exe (PID: 936)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 6456)
Starts SC.EXE for service management
- cmd.exe (PID: 6588)
- cmd.exe (PID: 4624)
- cmd.exe (PID: 6456)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6588)
- cmd.exe (PID: 4624)
- cmd.exe (PID: 6456)
Application launched itself
- cmd.exe (PID: 6588)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 6308)
- cmd.exe (PID: 4624)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 6456)
- powershell.exe (PID: 6900)
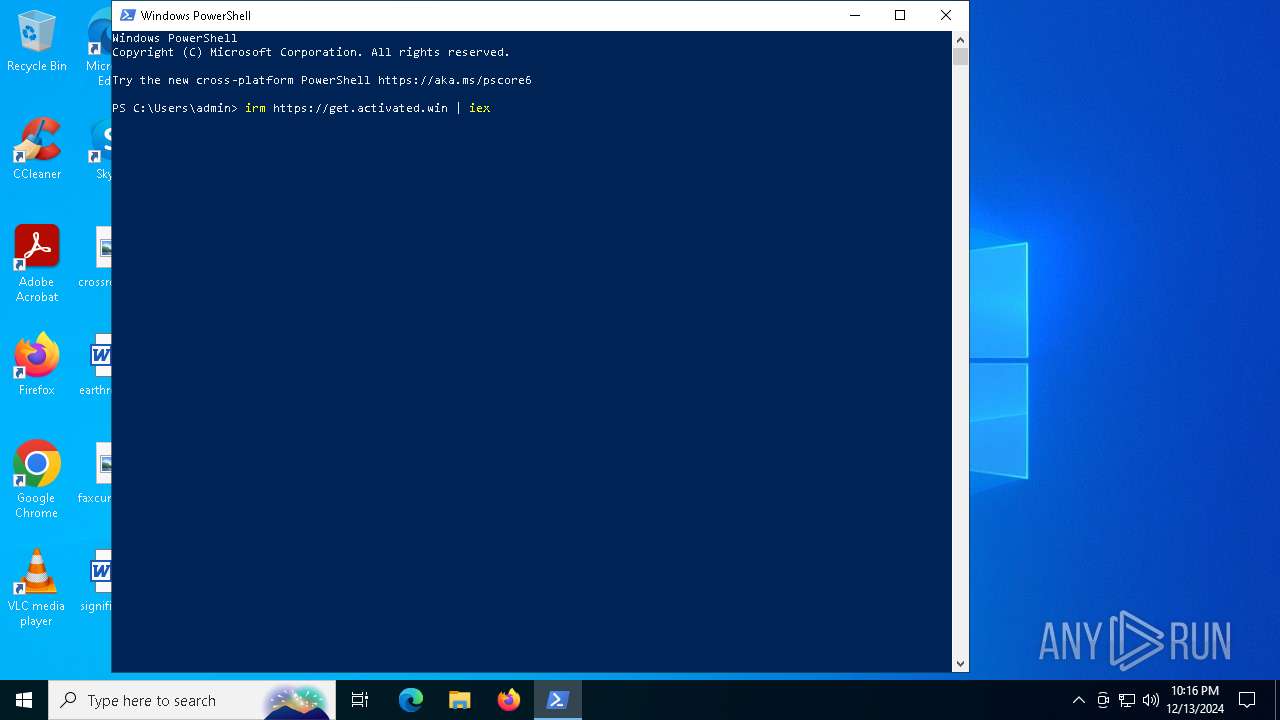
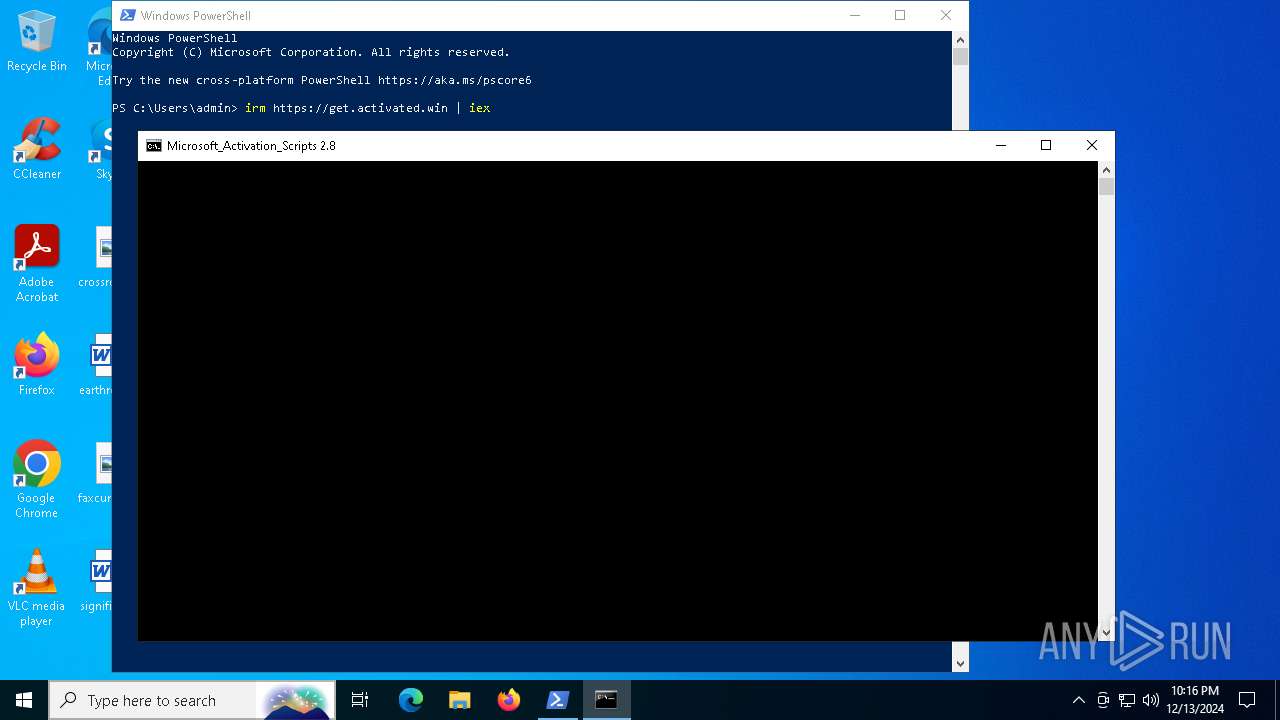
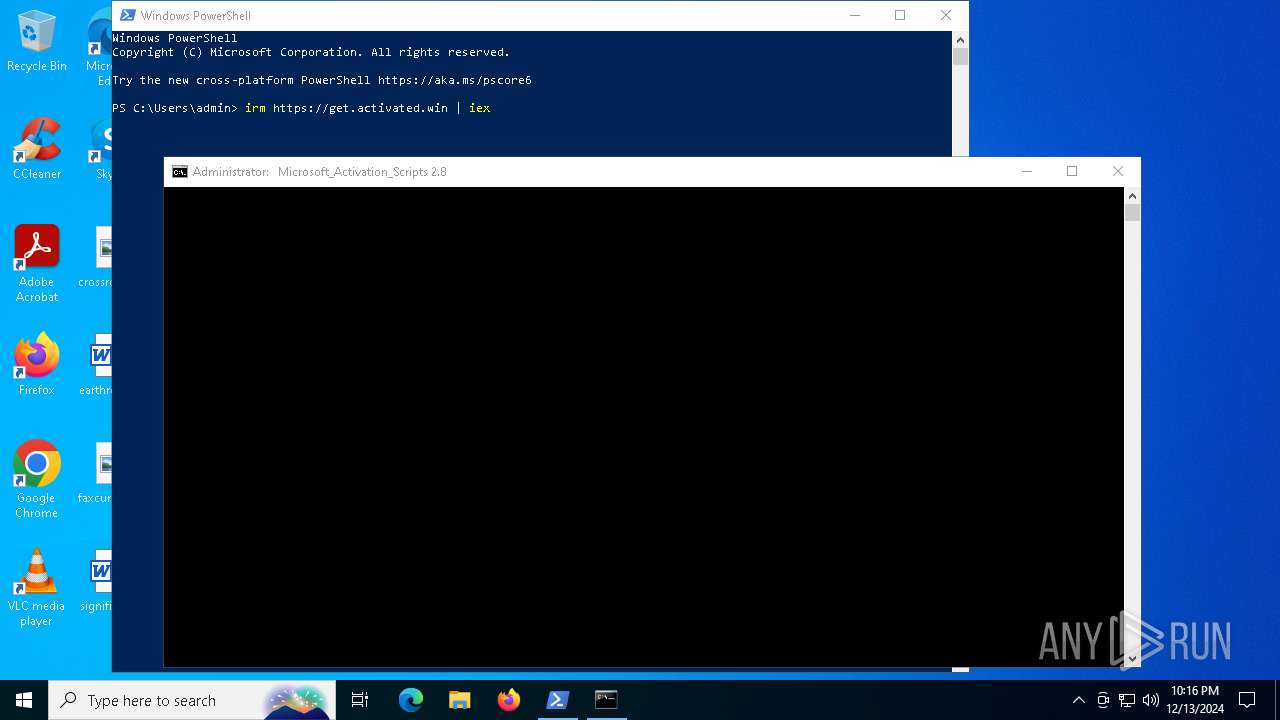
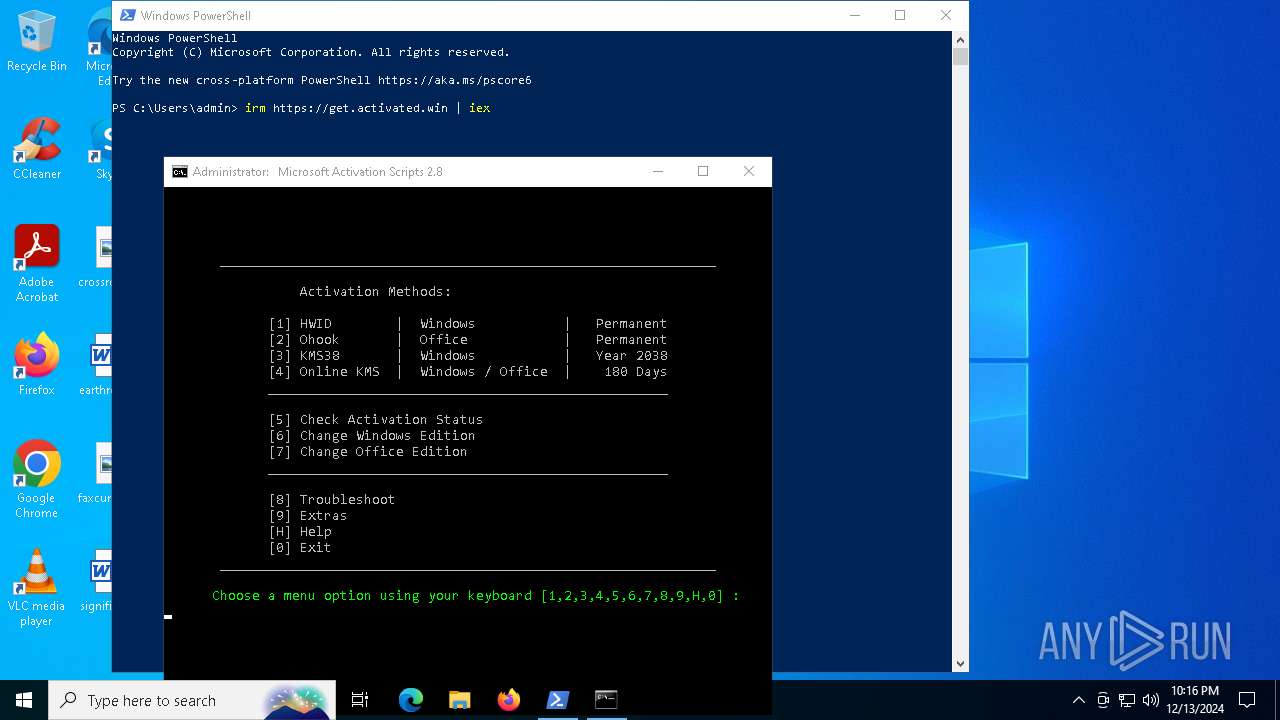
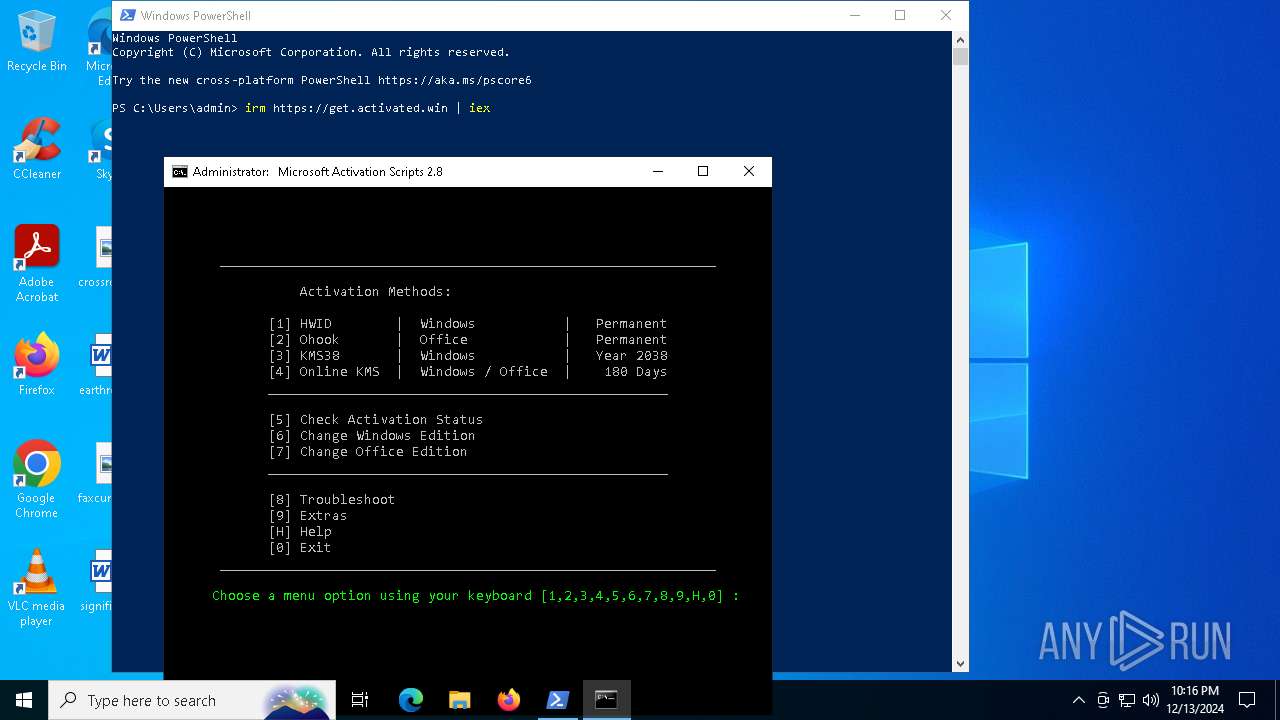
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 6984)
- cmd.exe (PID: 6324)
- cmd.exe (PID: 7656)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 6664)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 4648)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6588)
- cmd.exe (PID: 6984)
- cmd.exe (PID: 4624)
- cmd.exe (PID: 6324)
- cmd.exe (PID: 7656)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 6476)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 6664)
- powershell.exe (PID: 6900)
- cmd.exe (PID: 5648)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 6984)
- cmd.exe (PID: 6324)
- cmd.exe (PID: 7656)
- cmd.exe (PID: 6456)
- cmd.exe (PID: 6664)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6456)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 7048)
- cmd.exe (PID: 6456)
Hides command output
- cmd.exe (PID: 7680)
- cmd.exe (PID: 7624)
- cmd.exe (PID: 6664)
- cmd.exe (PID: 2792)
- cmd.exe (PID: 4228)
- cmd.exe (PID: 7112)
- cmd.exe (PID: 6244)
- cmd.exe (PID: 5648)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 6900)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 7624)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6456)
- cmd.exe (PID: 6244)
- cmd.exe (PID: 2792)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 6900)
INFO
Checks supported languages
- identity_helper.exe (PID: 7772)
- identity_helper.exe (PID: 4640)
- SearchApp.exe (PID: 5064)
- mode.com (PID: 7712)
Reads the computer name
- identity_helper.exe (PID: 4640)
- identity_helper.exe (PID: 7772)
Reads Environment values
- identity_helper.exe (PID: 4640)
- identity_helper.exe (PID: 7772)
Application launched itself
- msedge.exe (PID: 5572)
- msedge.exe (PID: 3420)
Reads the software policy settings
- SearchApp.exe (PID: 5064)
Process checks computer location settings
- SearchApp.exe (PID: 5064)
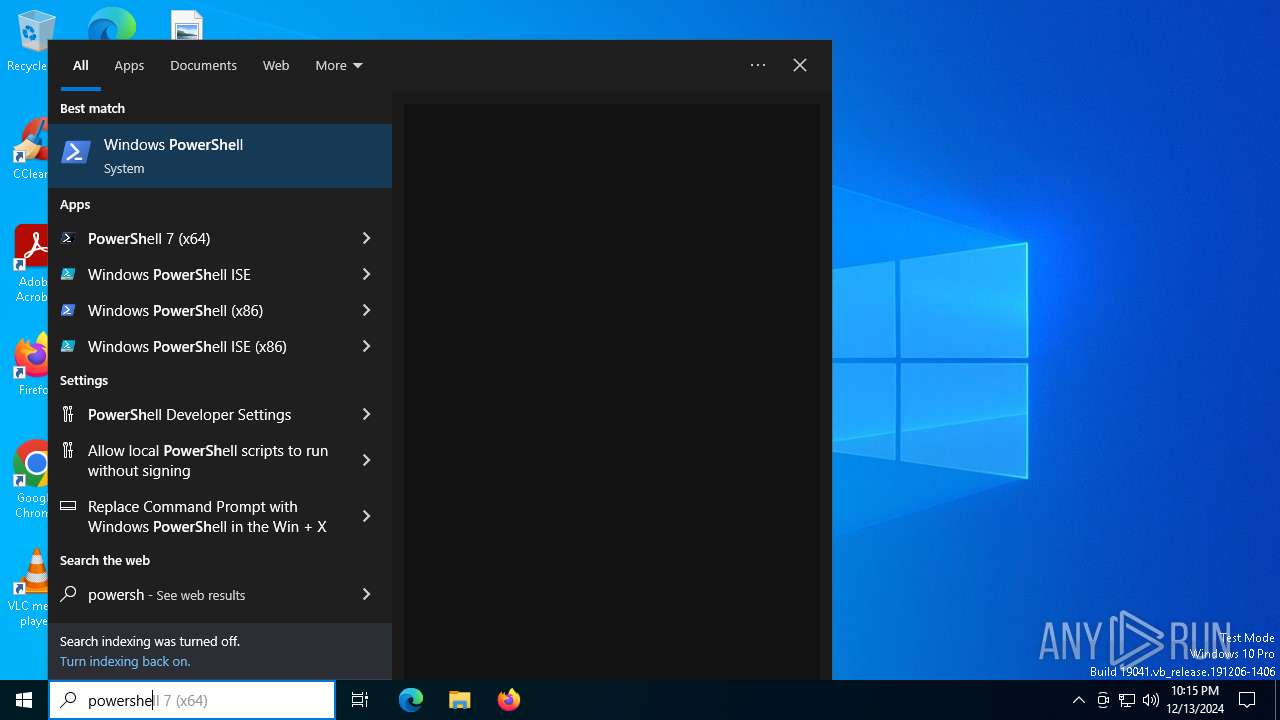
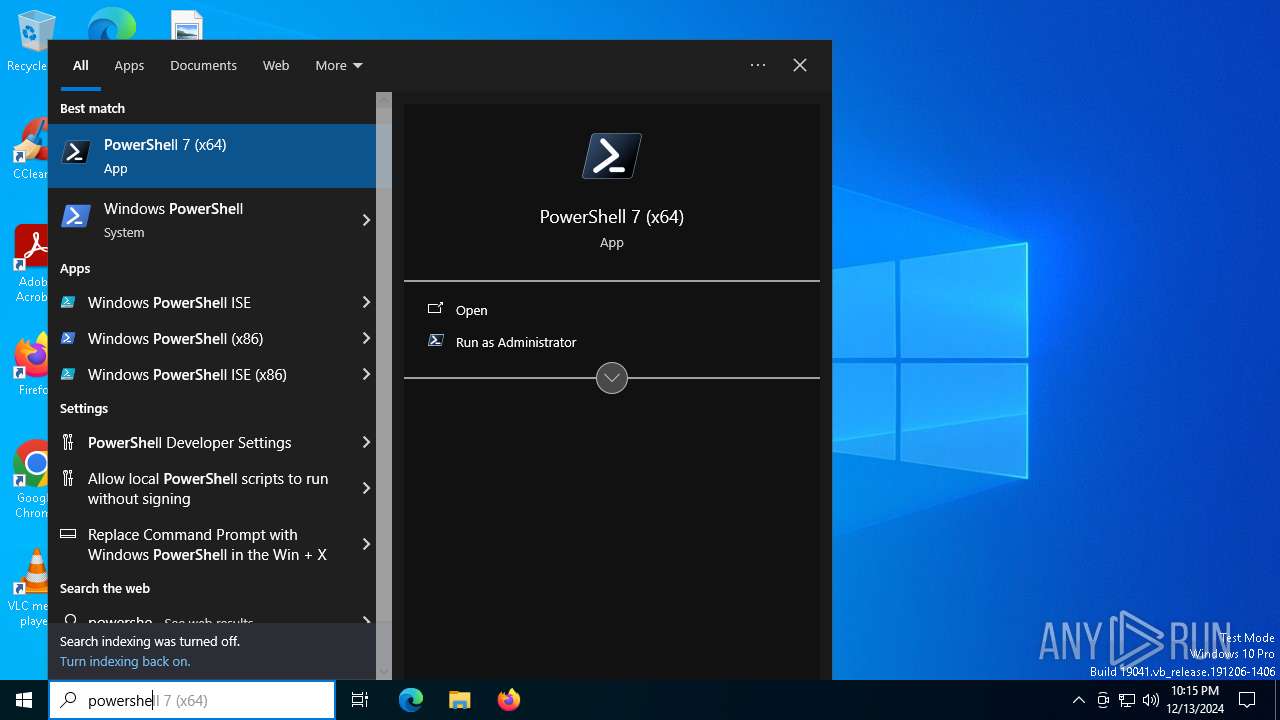
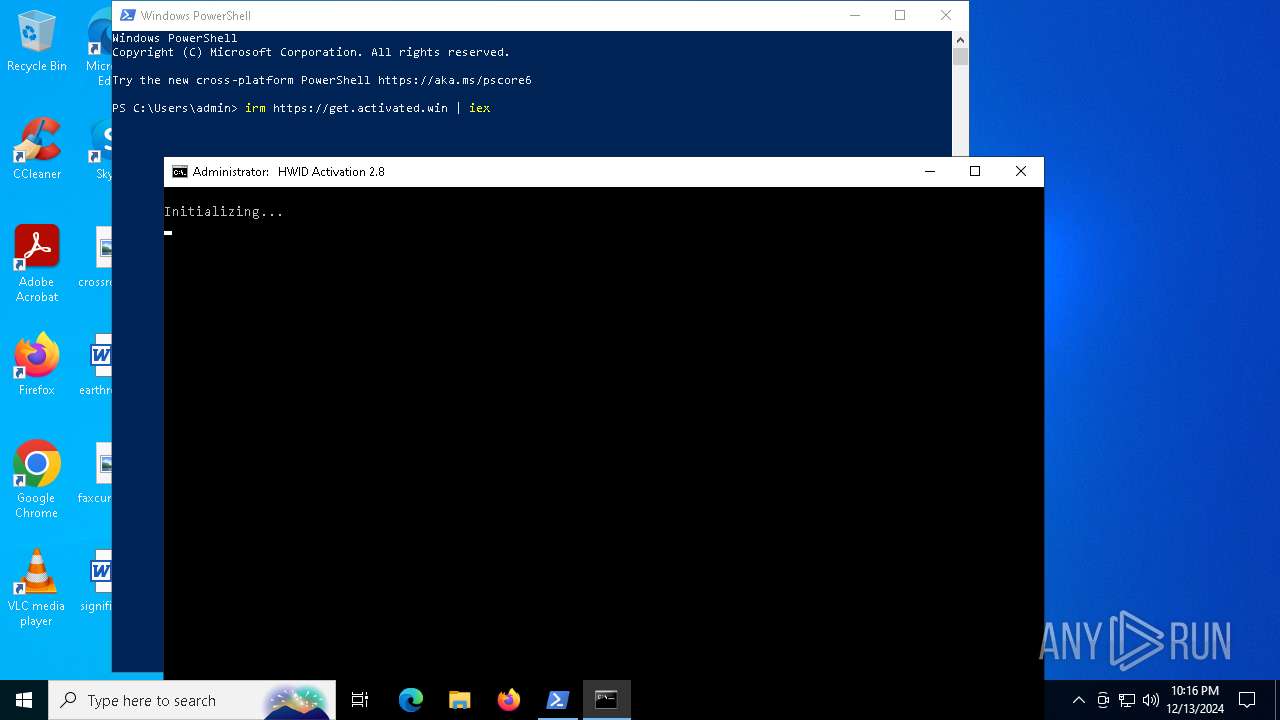
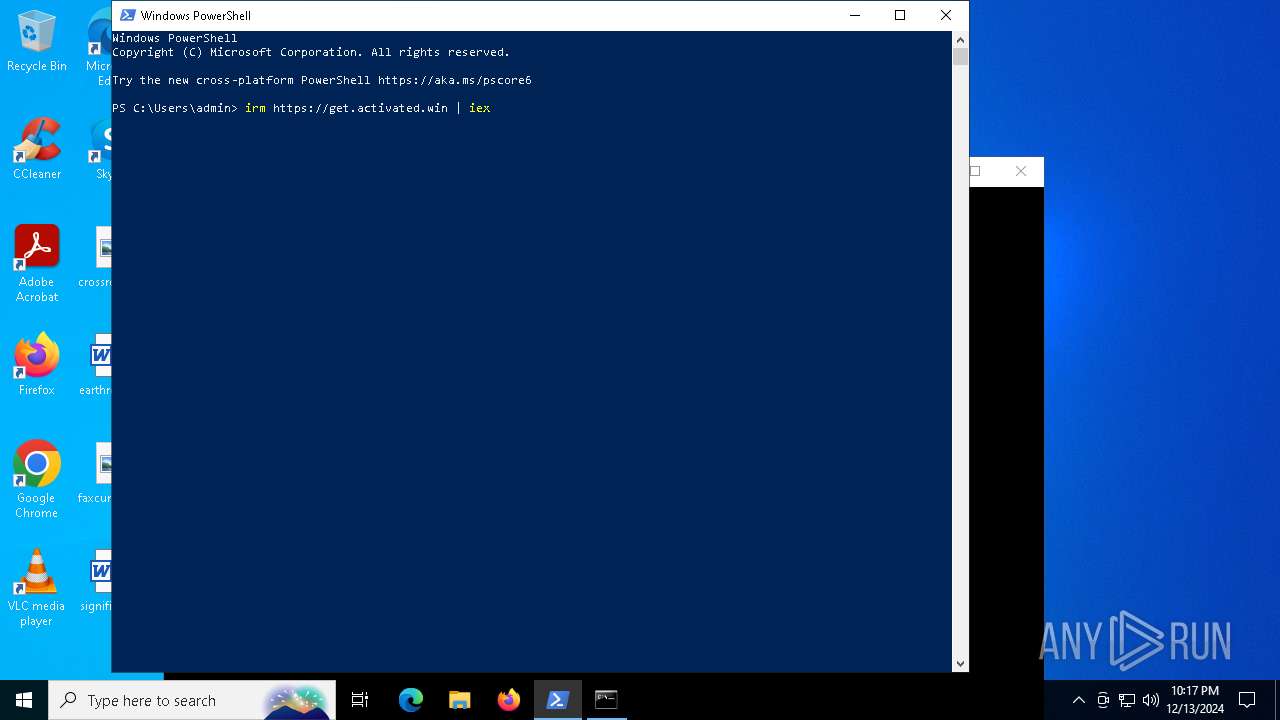
Manual execution by a user
- powershell.exe (PID: 4648)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 5064)
Disables trace logs
- powershell.exe (PID: 4648)
Checks proxy server information
- powershell.exe (PID: 4648)
Checks current location (POWERSHELL)
- powershell.exe (PID: 4648)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 4648)
- powershell.exe (PID: 7264)
- powershell.exe (PID: 6344)
- powershell.exe (PID: 6004)
- powershell.exe (PID: 7676)
- powershell.exe (PID: 5872)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 4648)
- powershell.exe (PID: 7264)
- powershell.exe (PID: 6344)
- powershell.exe (PID: 6004)
- powershell.exe (PID: 7676)
- powershell.exe (PID: 5872)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4648)
- powershell.exe (PID: 7264)
- powershell.exe (PID: 6344)
- powershell.exe (PID: 6004)
- powershell.exe (PID: 7676)
- powershell.exe (PID: 5872)
Checks operating system version
- cmd.exe (PID: 6588)
- cmd.exe (PID: 4624)
- cmd.exe (PID: 6456)
The process uses the downloaded file
- powershell.exe (PID: 7568)
Starts MODE.COM to configure console settings
- mode.com (PID: 5588)
- mode.com (PID: 7712)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6544)
- WMIC.exe (PID: 3540)
- WMIC.exe (PID: 5776)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
434
Monitored processes
297
Malicious processes
6
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | reg query "HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders" /v Desktop | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "AMD64 " " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 308 | reg query HKLM\SYSTEM\CurrentControlSet\Services\Winmgmt /v Type | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 448 | find /i "RUNNING" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5476 --field-trial-handle=2380,i,10155728705167781383,12101738802399141466,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 540 | find /i "True" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | powershell.exe "$TB = [AppDomain]::CurrentDomain.DefineDynamicAssembly(4, 1).DefineDynamicModule(2, $False).DefineType(0); [void]$TB.DefinePInvokeMethod('GetConsoleWindow', 'kernel32.dll', 22, 1, [IntPtr], @(), 1, 3).SetImplementationFlags(128); [void]$TB.DefinePInvokeMethod('SendMessageW', 'user32.dll', 22, 1, [IntPtr], @([IntPtr], [UInt32], [IntPtr], [IntPtr]), 1, 3).SetImplementationFlags(128); $hIcon = $TB.CreateType(); $hWnd = $hIcon::GetConsoleWindow(); echo $($hIcon::SendMessageW($hWnd, 127, 0, 0) -ne [IntPtr]::Zero);" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | find /i "Subscription_is_activated" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 648 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6616 --field-trial-handle=2380,i,10155728705167781383,12101738802399141466,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 848 | find /i "/S" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
111 198
Read events
111 057
Write events
137
Delete events
4
Modification events
| (PID) Process: | (5572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5572) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 60DEE473C4872F00 | |||
| (PID) Process: | (5572) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 51CBED73C4872F00 | |||
| (PID) Process: | (5572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\524798 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DD505151-3474-457E-B89F-40CF39752779} | |||
| (PID) Process: | (5572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\524798 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {18FA3839-15CE-48AC-BE3F-71AC85DEC3B0} | |||
| (PID) Process: | (5572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\524798 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D429476E-3B77-405D-B5B3-7FDEF68D1B28} | |||
| (PID) Process: | (5572) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\524798 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7D31A8D5-5F66-440E-BA97-15656470BBA1} | |||
Executable files
8
Suspicious files
450
Text files
343
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135130.TMP | — | |
MD5:— | SHA256:— | |||
| 5572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135130.TMP | — | |
MD5:— | SHA256:— | |||
| 5572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135130.TMP | — | |
MD5:— | SHA256:— | |||
| 5572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135130.TMP | — | |
MD5:— | SHA256:— | |||
| 5572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135140.TMP | — | |
MD5:— | SHA256:— | |||
| 5572 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
207
DNS requests
278
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6412 | msedge.exe | GET | 200 | 40.143.178.190:80 | http://certs.securetrust.com/issuers/VCOVCA_L1.crt | unknown | — | — | unknown |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
7140 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7140 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2420 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b806c448-80ea-4147-beb1-8efa415f05dd?P1=1734637759&P2=404&P3=2&P4=KLEVjOyiz4BPAYEl9tNjw0SYKtxSSNMc63oZL9Bl6JTyRJ7XEgkKlUZbashx8T6Aoq35y7UkPGy4u%2b1kO69VKw%3d%3d | unknown | — | — | whitelisted |
6428 | SIHClient.exe | GET | 200 | 88.221.125.143:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1684 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6412 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5572 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6412 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
test.com |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |
6412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |
6412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6412 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |