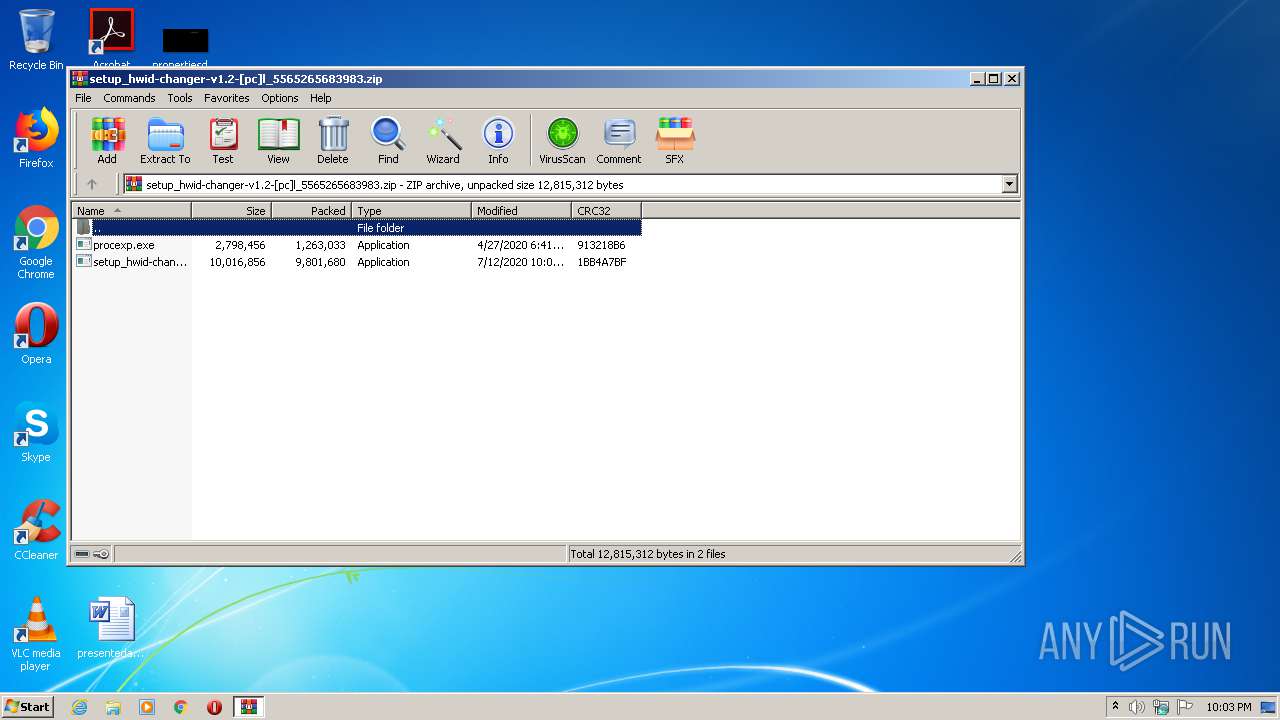
| File name: | setup_hwid-changer-v1.2-[pc]l_5565265683983.zip |
| Full analysis: | https://app.any.run/tasks/c46a94eb-dfea-4927-9a12-4298a83e2f33 |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 21:02:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 32249D44B284950C76AE9FF174DB9217 |
| SHA1: | 4F0758D80668F317D7893FC2D42EA3A9DB69D483 |
| SHA256: | 395C2EEB6EAD252E84122CAE73266EFEFFD085ABFEAAFEF958E4C8BC4D0C4C5D |
| SSDEEP: | 196608:rvSPoX84G8SKWBbvEzfNTEunMHimYyqJl1fFEt8NRvj4rntIK4SUPPXyTKvo:rvSPCcXnTKNnJe2HfFEt83j4rntMXxvo |
MALICIOUS
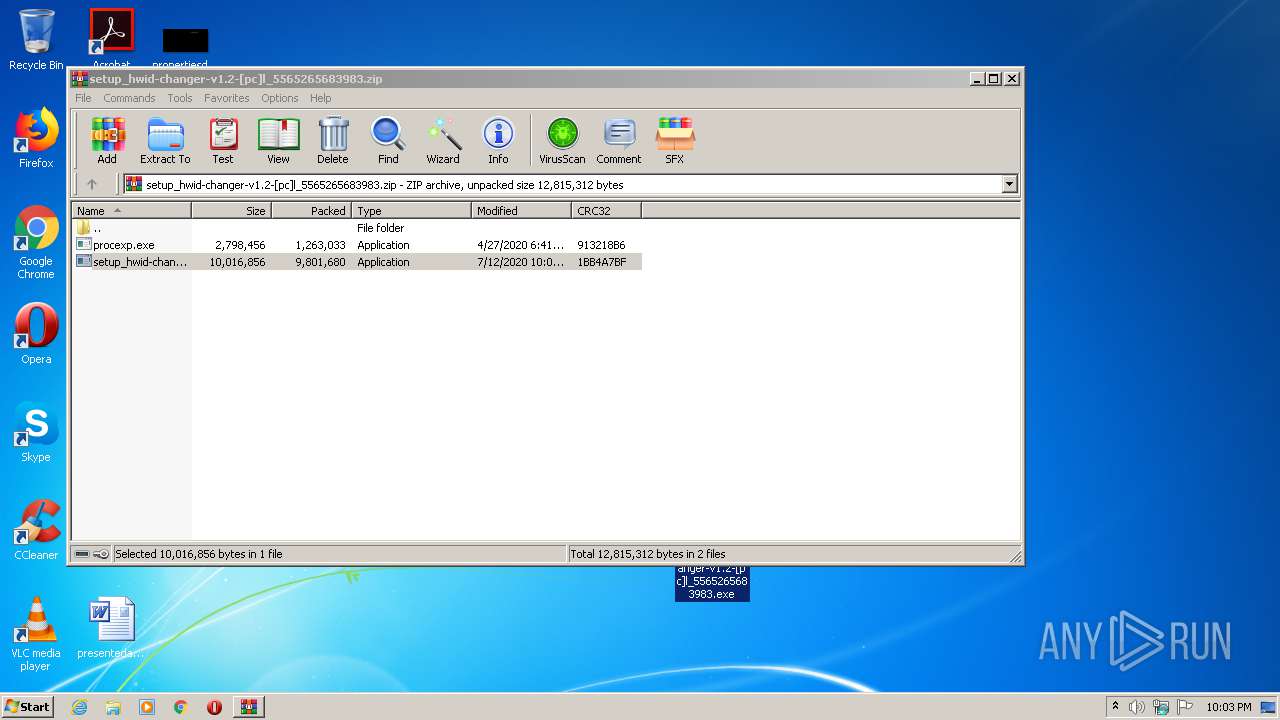
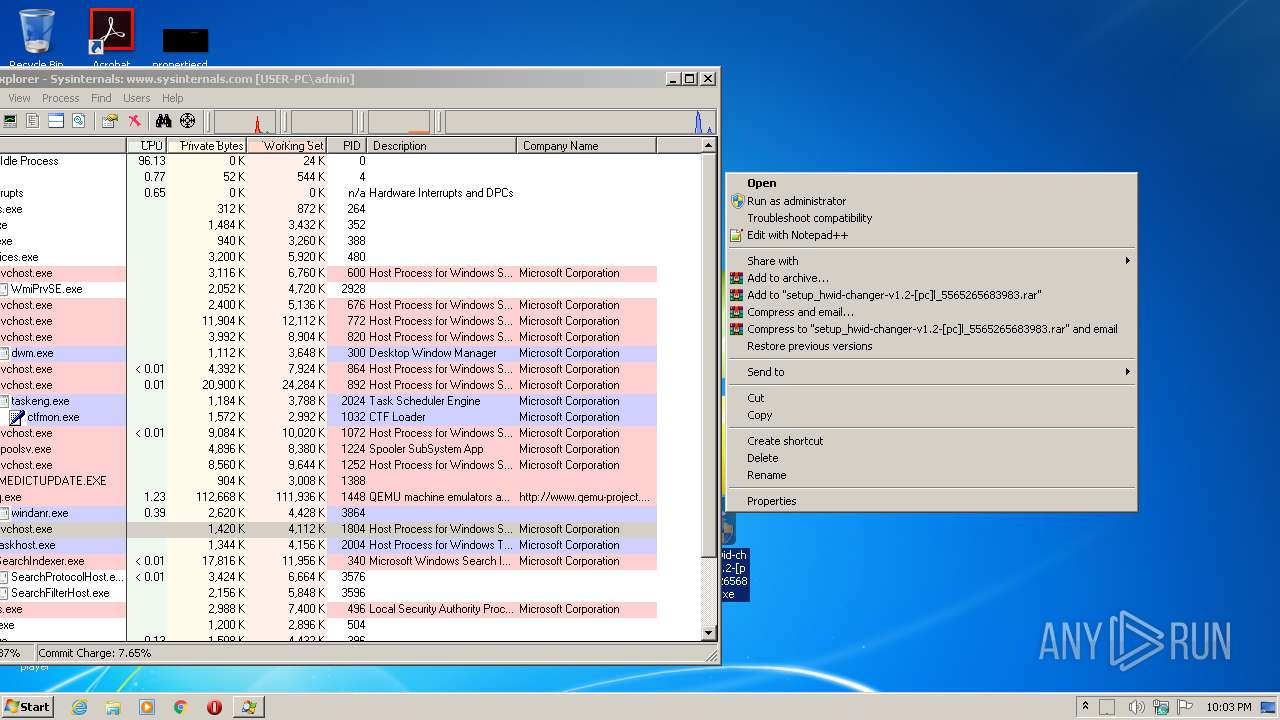
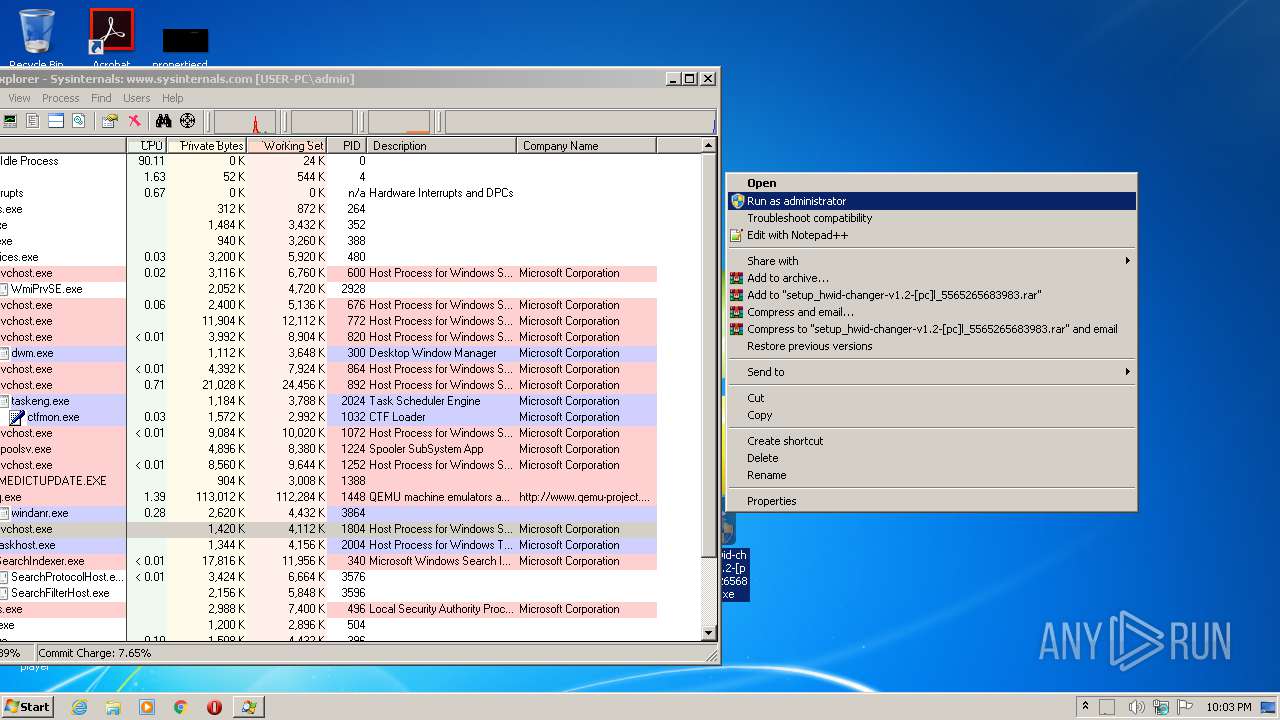
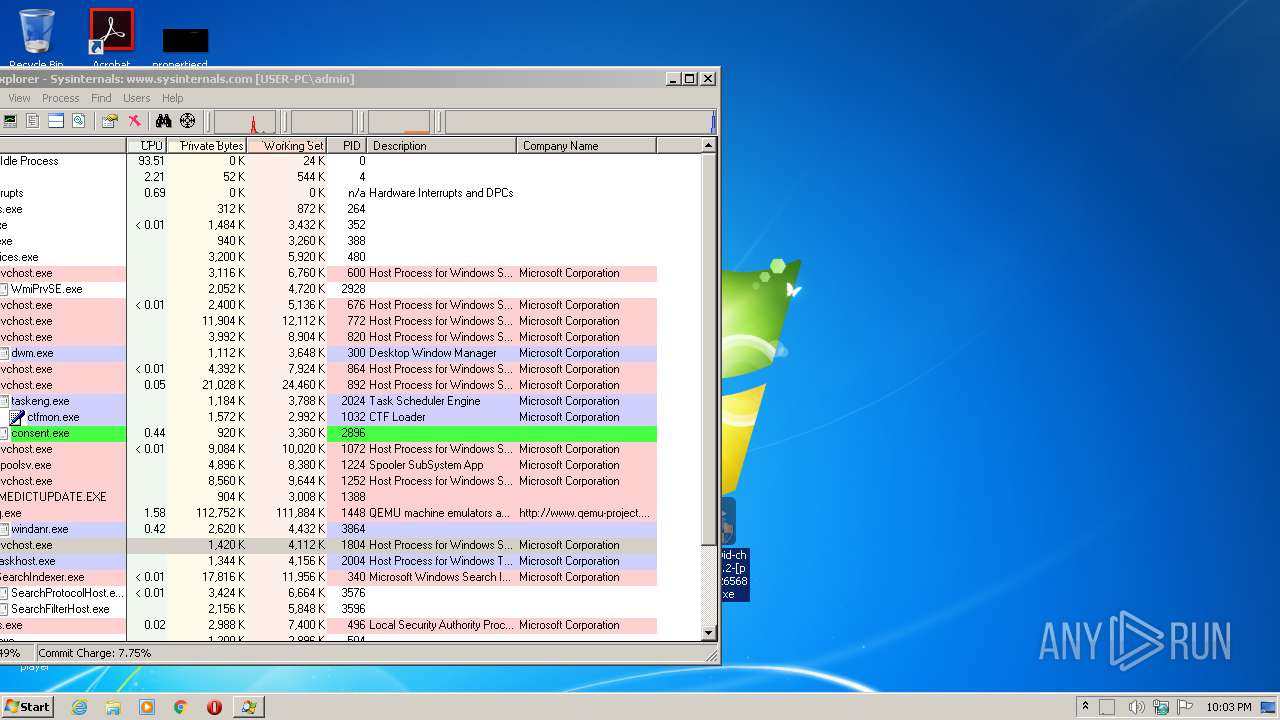
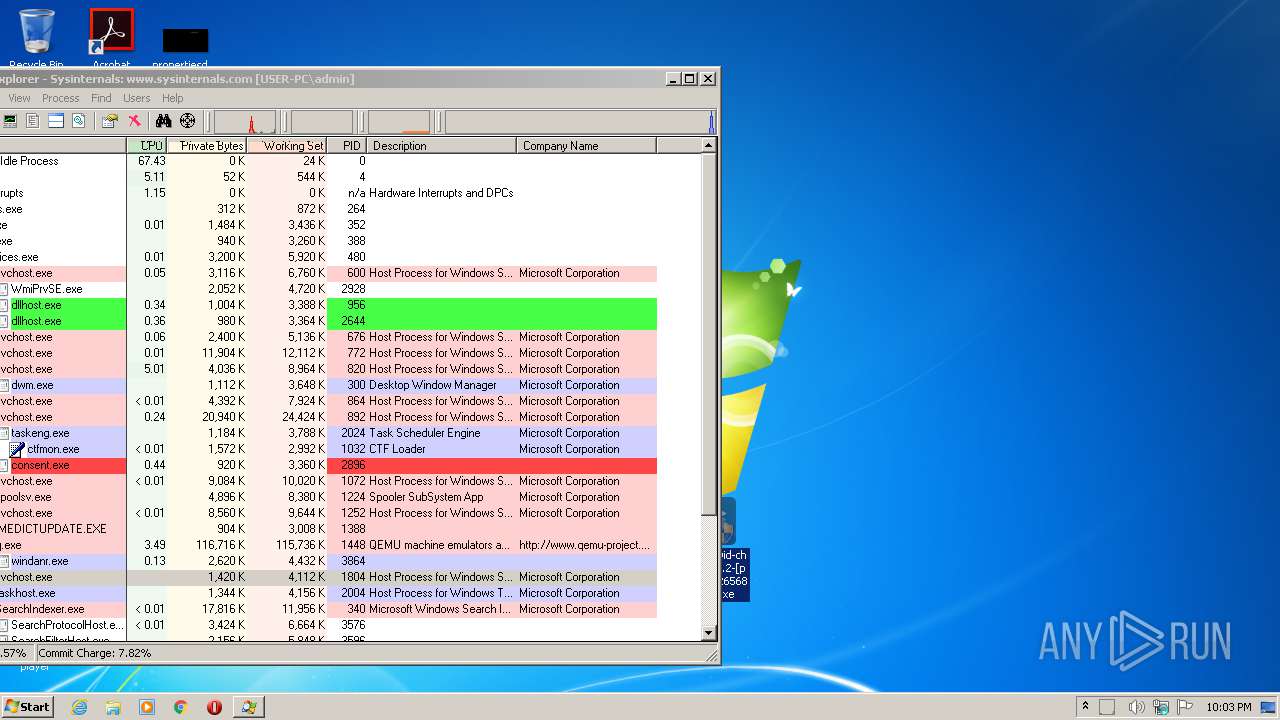
Application was dropped or rewritten from another process
- setup_hwid-changer-v1.2-[pc]l_5565265683983.exe (PID: 2980)
- setup_hwid-changer-v1.2-[pc]l_5565265683983.exe (PID: 1832)
- procexp.exe (PID: 1772)
- setup_hwid-changer-v1.2-[pc]l_5565265683983.exe (PID: 3948)
- setup_hwid-changer-v1.2-[pc]l_5565265683983.exe (PID: 412)
- setup_hwid-changer-v1.2-[pc]l_5565265683983.exe (PID: 4008)
Loads the Task Scheduler COM API
- procexp.exe (PID: 1772)
SUSPICIOUS
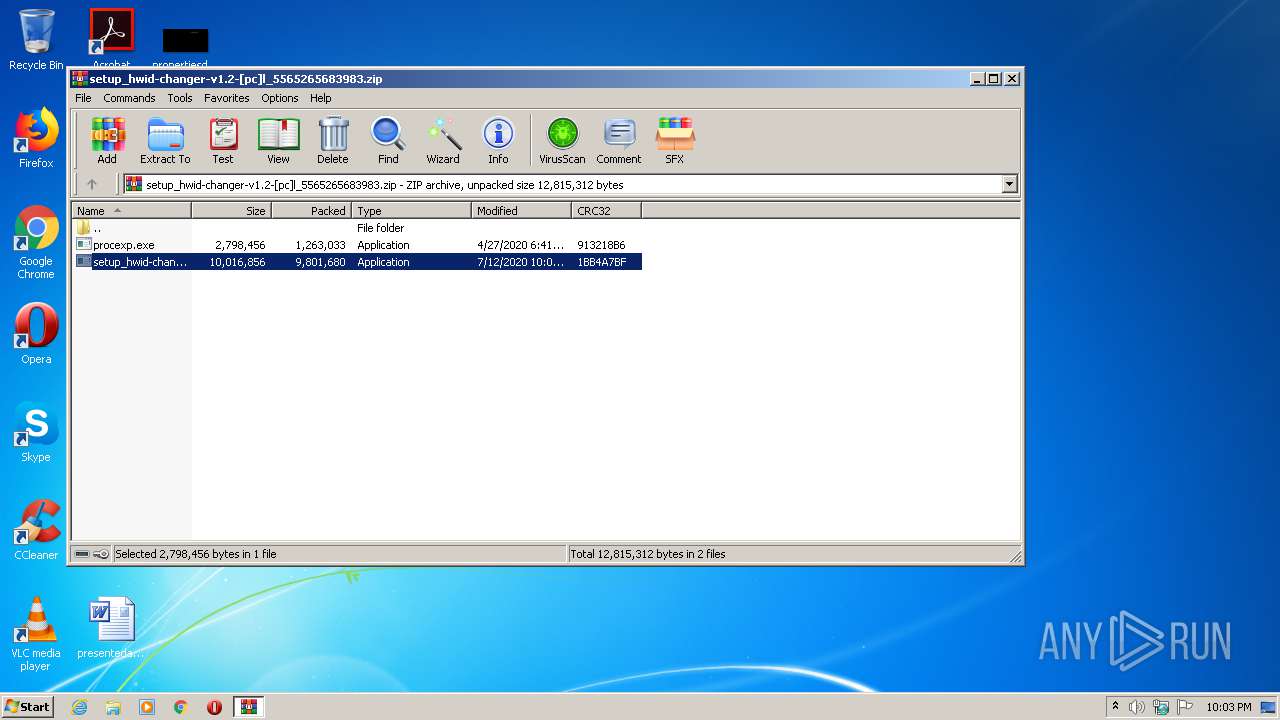
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2352)
INFO
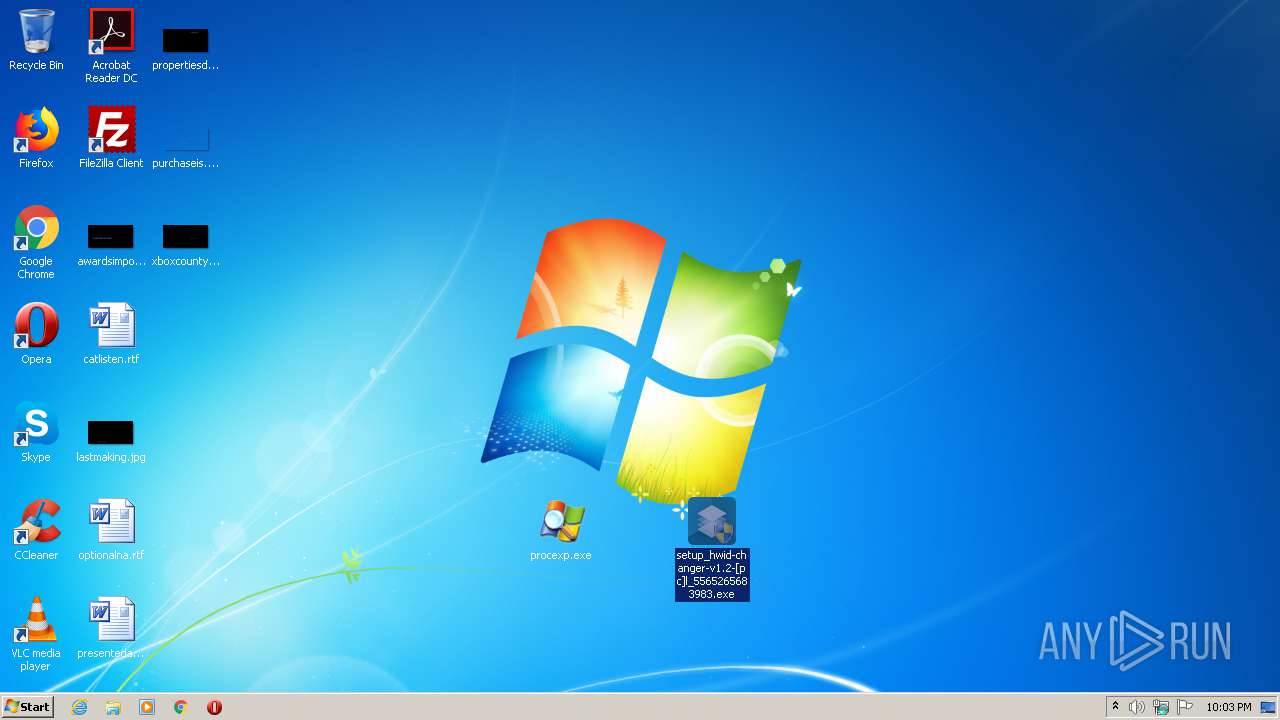
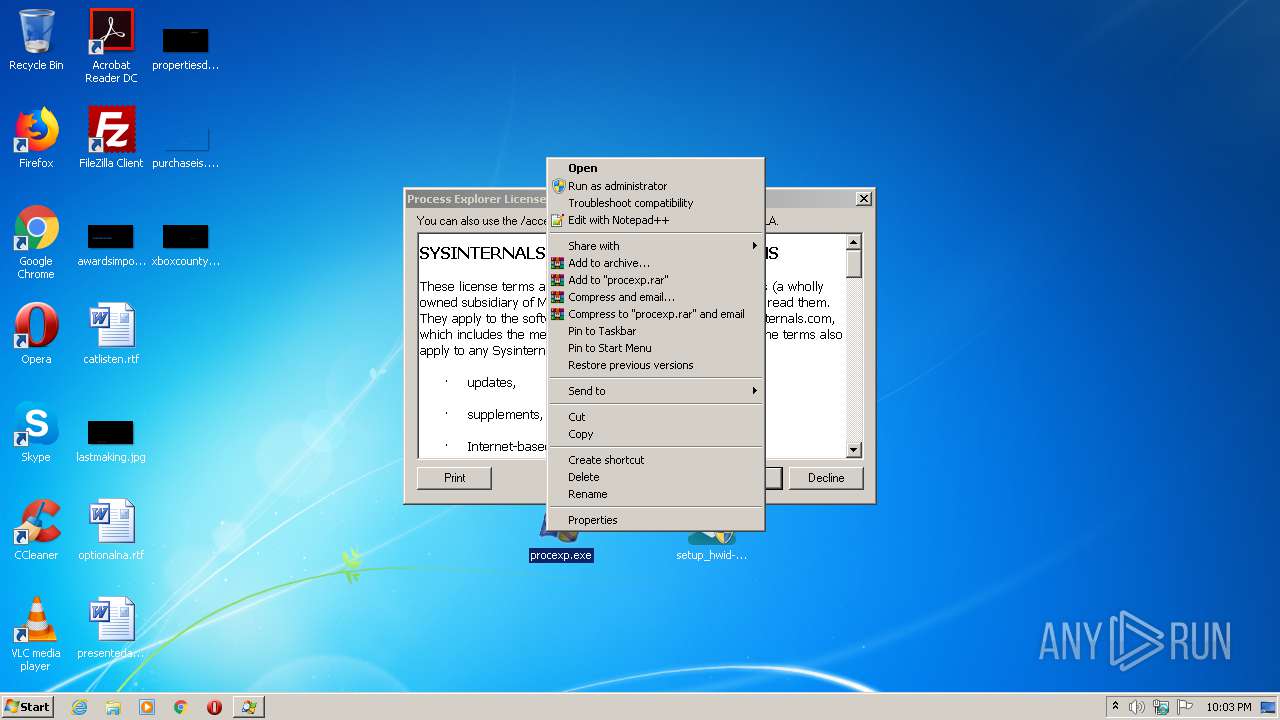
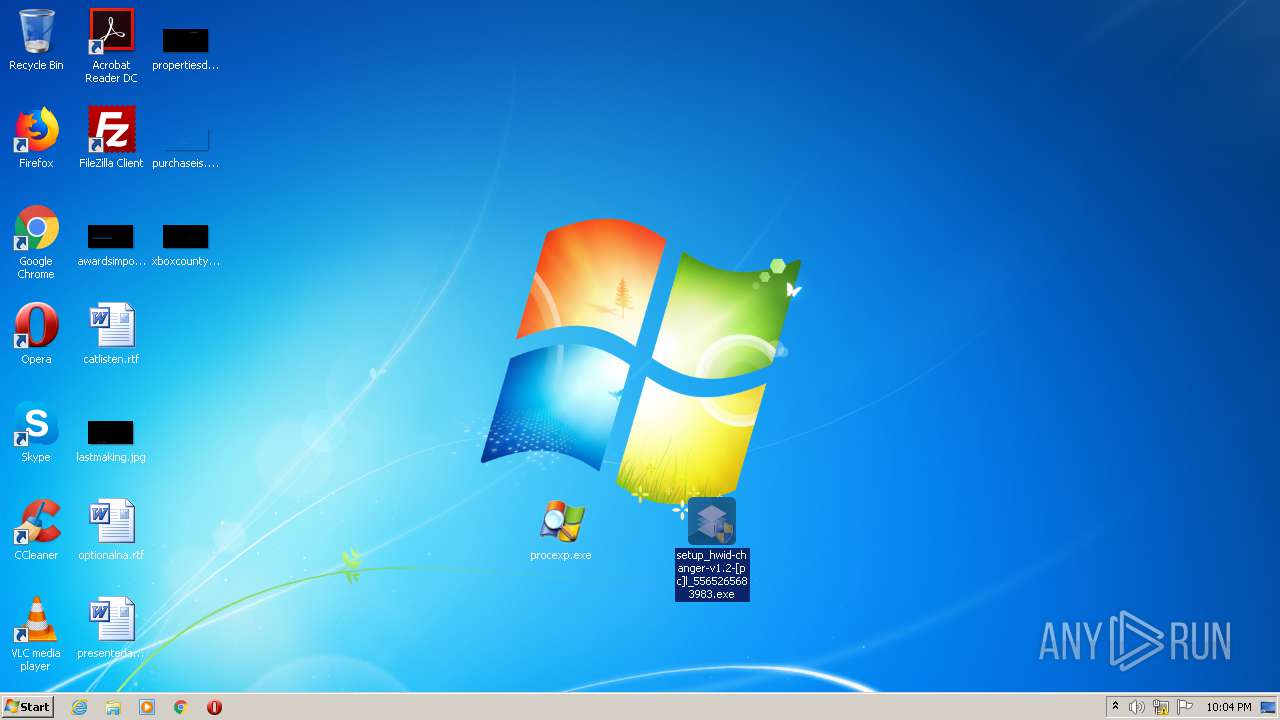
Manual execution by user
- setup_hwid-changer-v1.2-[pc]l_5565265683983.exe (PID: 1832)
- setup_hwid-changer-v1.2-[pc]l_5565265683983.exe (PID: 2980)
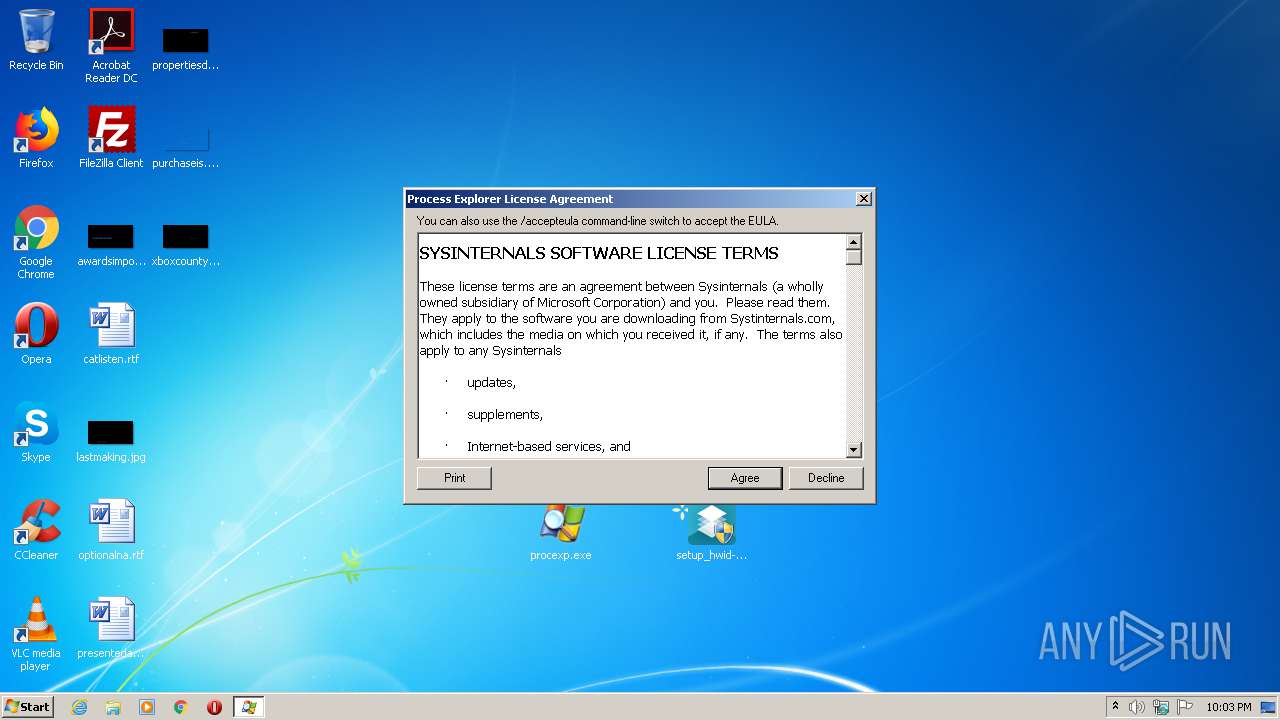
- procexp.exe (PID: 1772)
- setup_hwid-changer-v1.2-[pc]l_5565265683983.exe (PID: 3948)
- setup_hwid-changer-v1.2-[pc]l_5565265683983.exe (PID: 412)
- setup_hwid-changer-v1.2-[pc]l_5565265683983.exe (PID: 4008)
Reads settings of System Certificates
- procexp.exe (PID: 1772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:07:13 00:01:23 |
| ZipCRC: | 0x1bb4a7bf |
| ZipCompressedSize: | 9801680 |
| ZipUncompressedSize: | 10016856 |
| ZipFileName: | setup_hwid-changer-v1.2-[pc]l_5565265683983.exe |
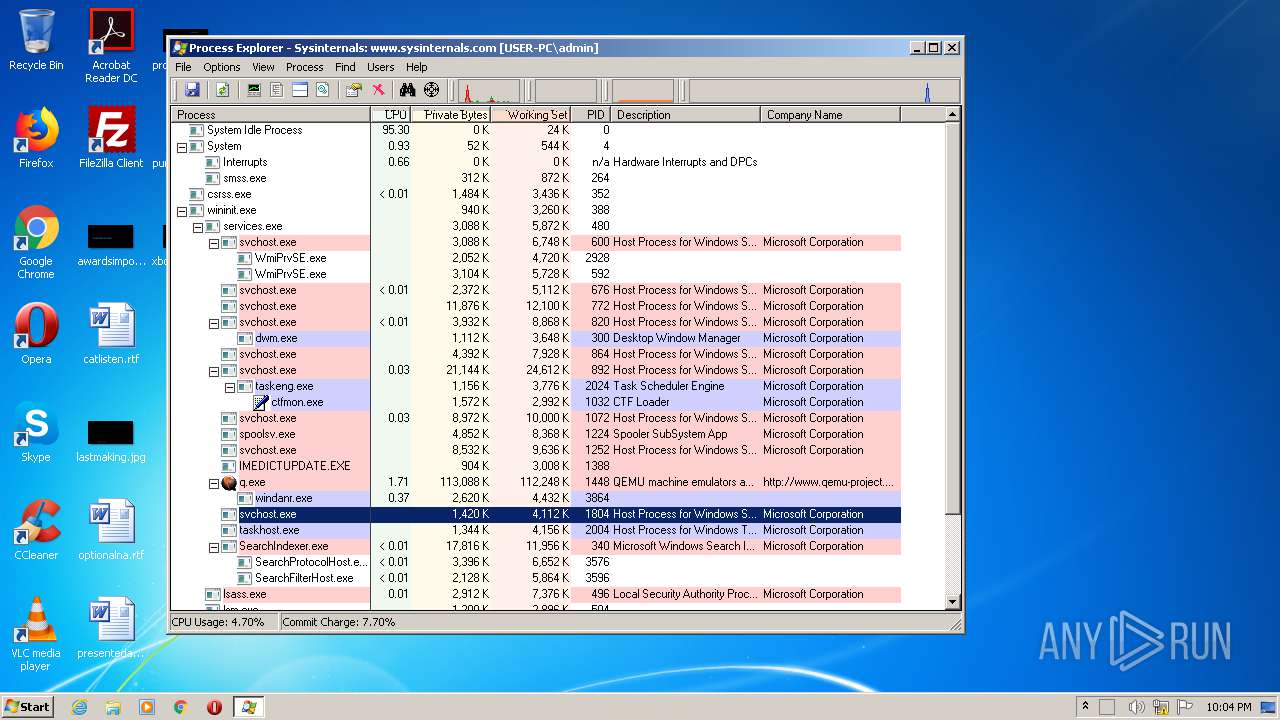
Total processes
51
Monitored processes
7
Malicious processes
3
Suspicious processes
1
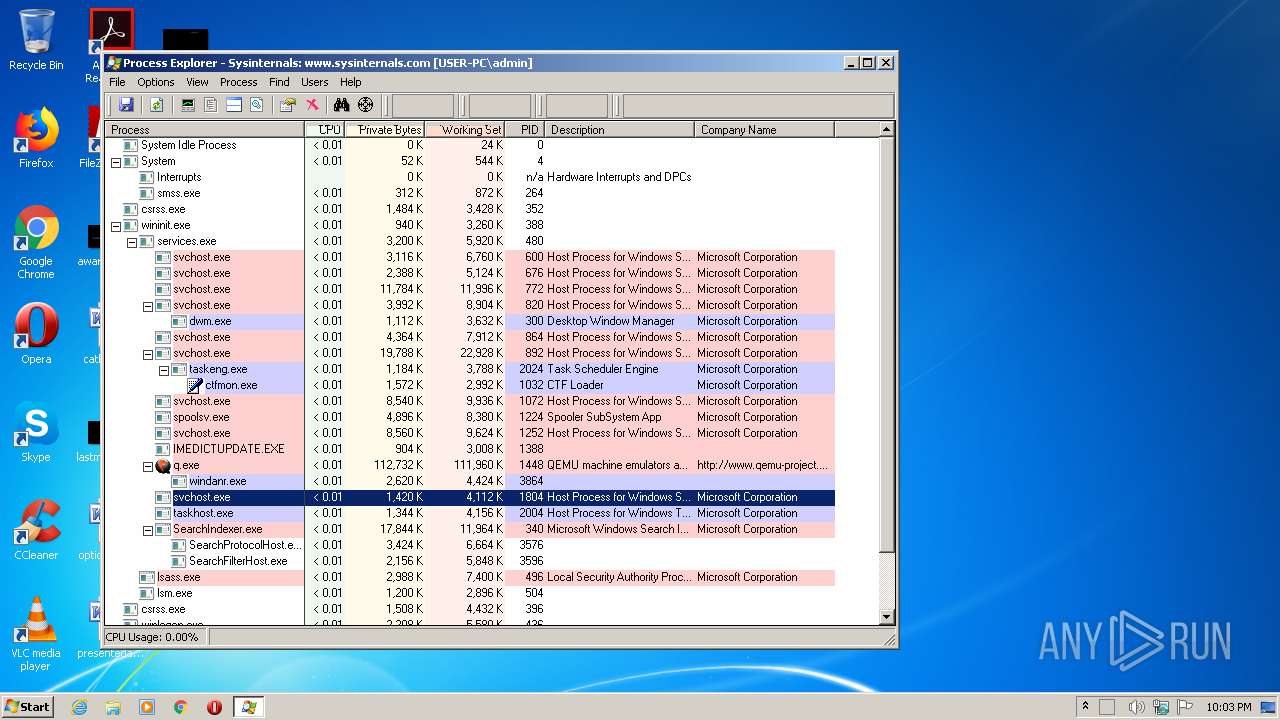
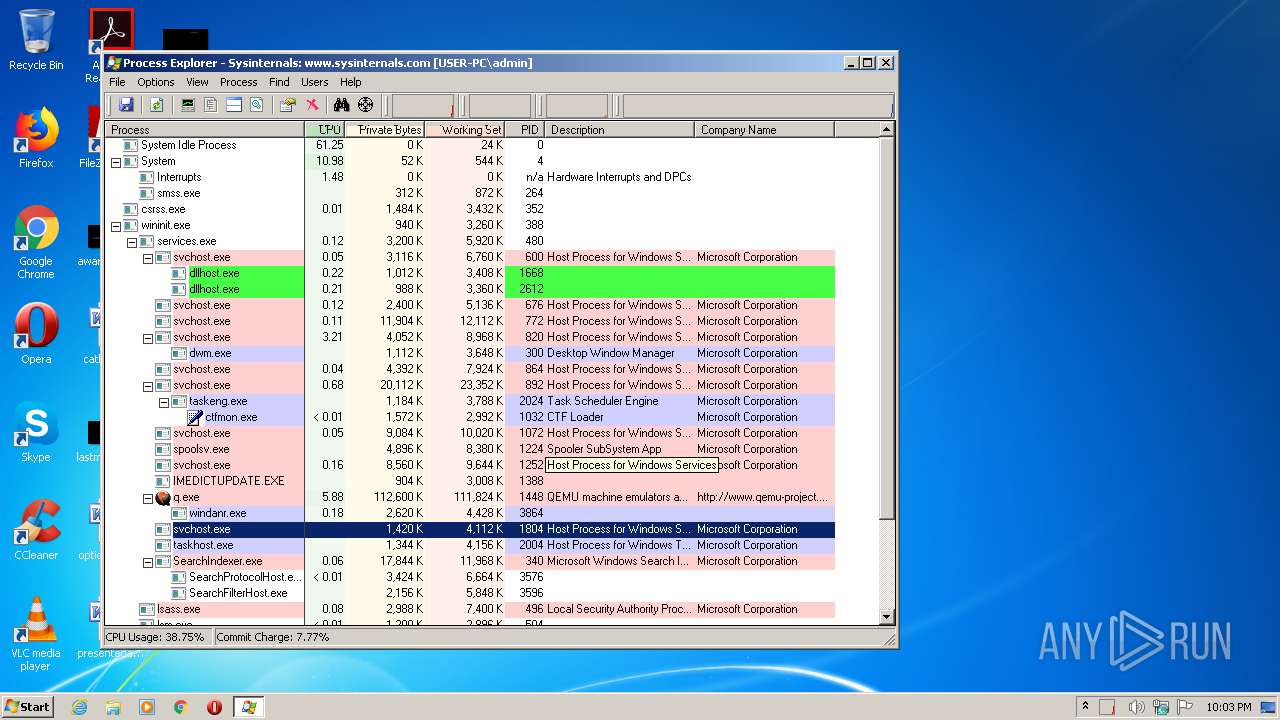
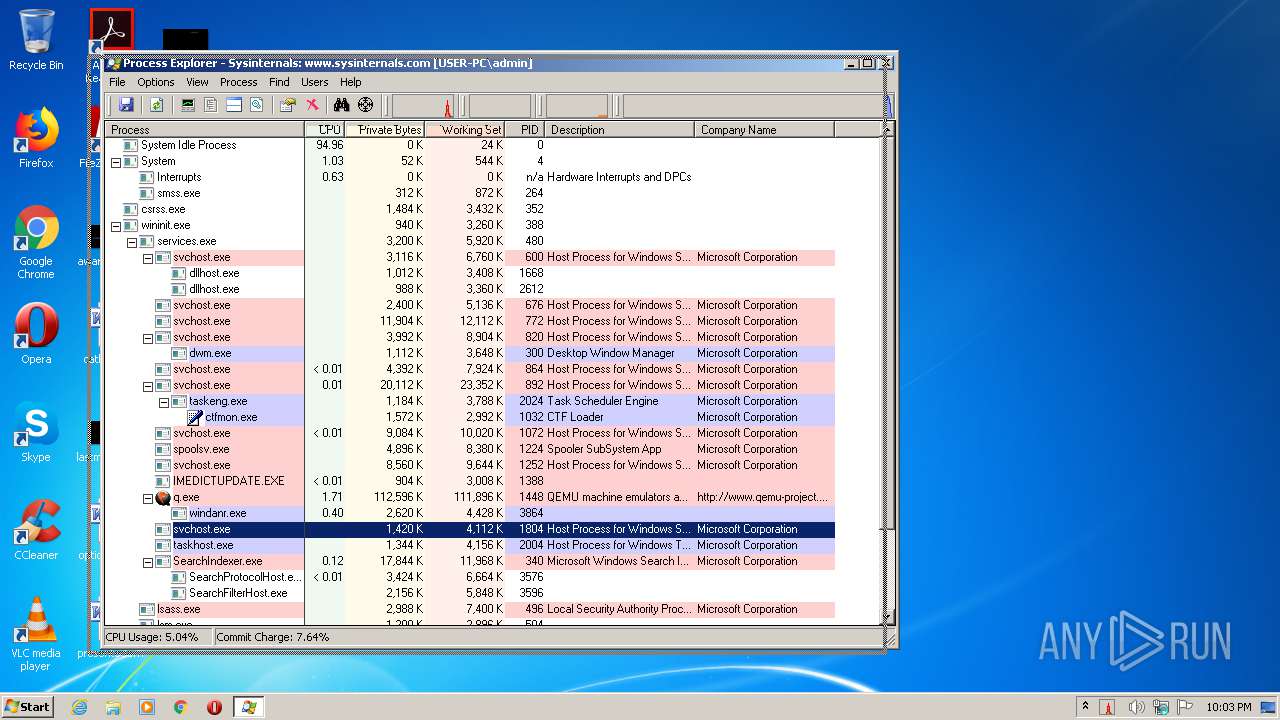
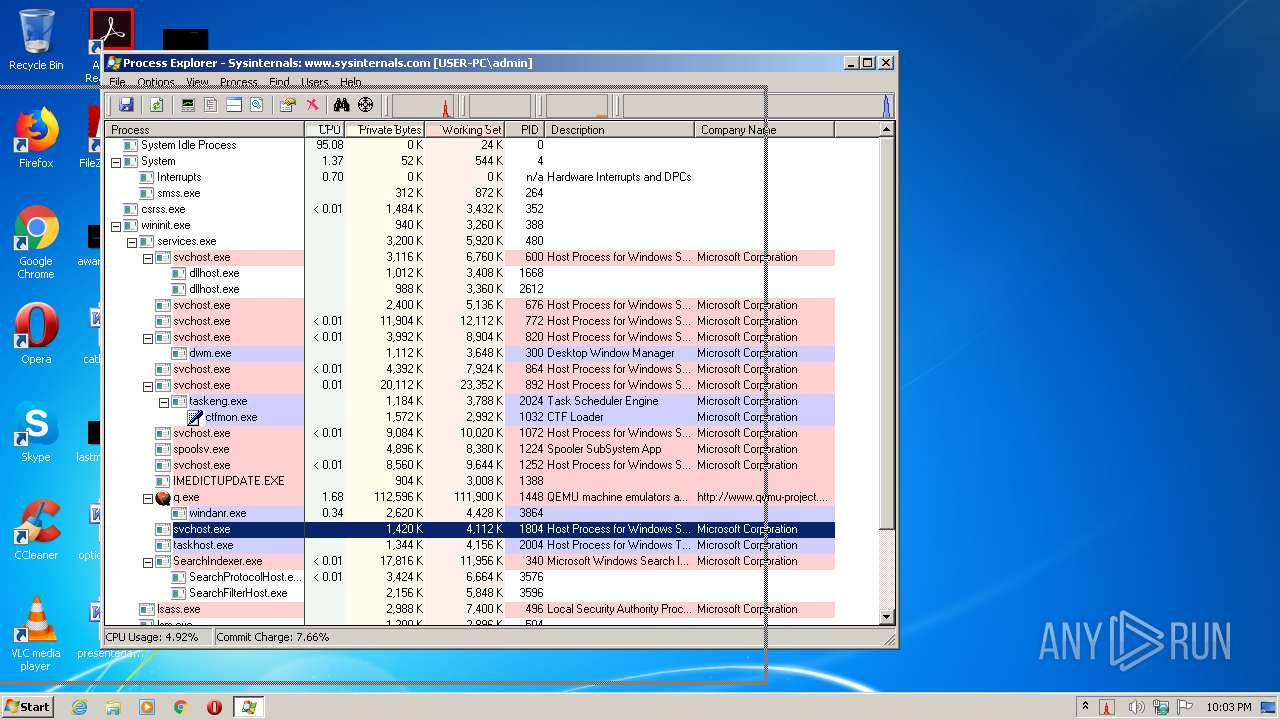
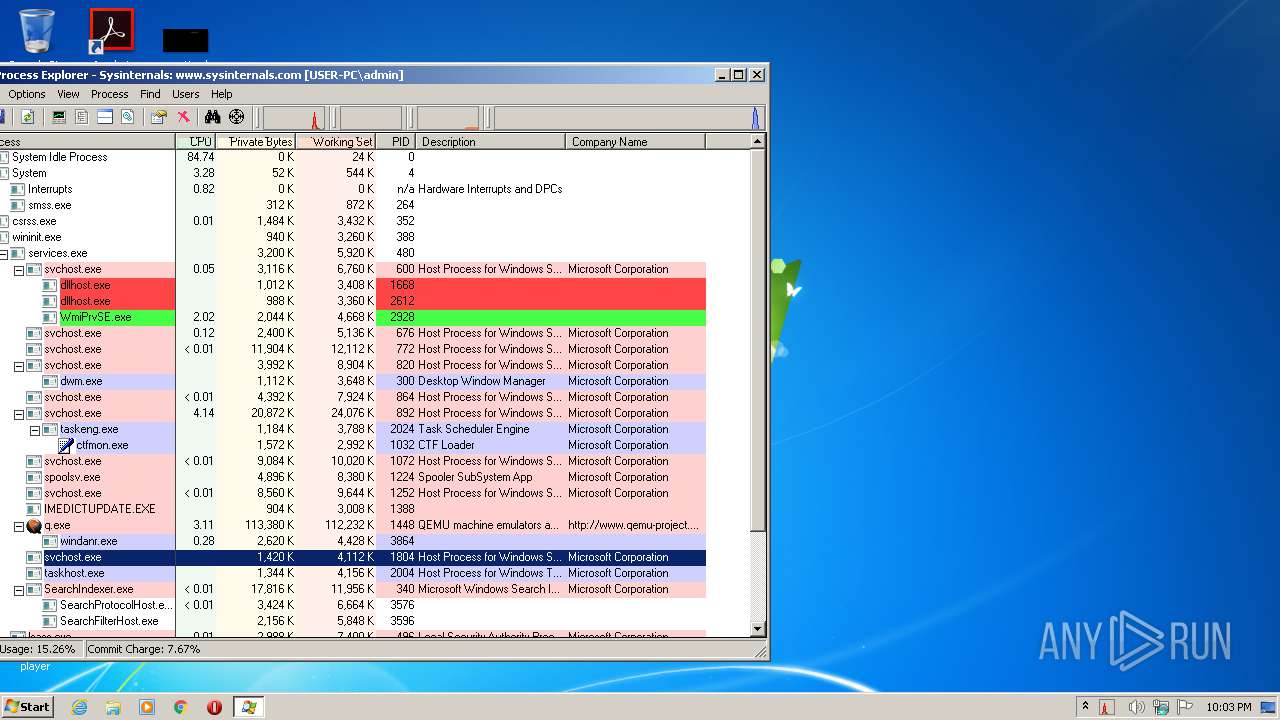
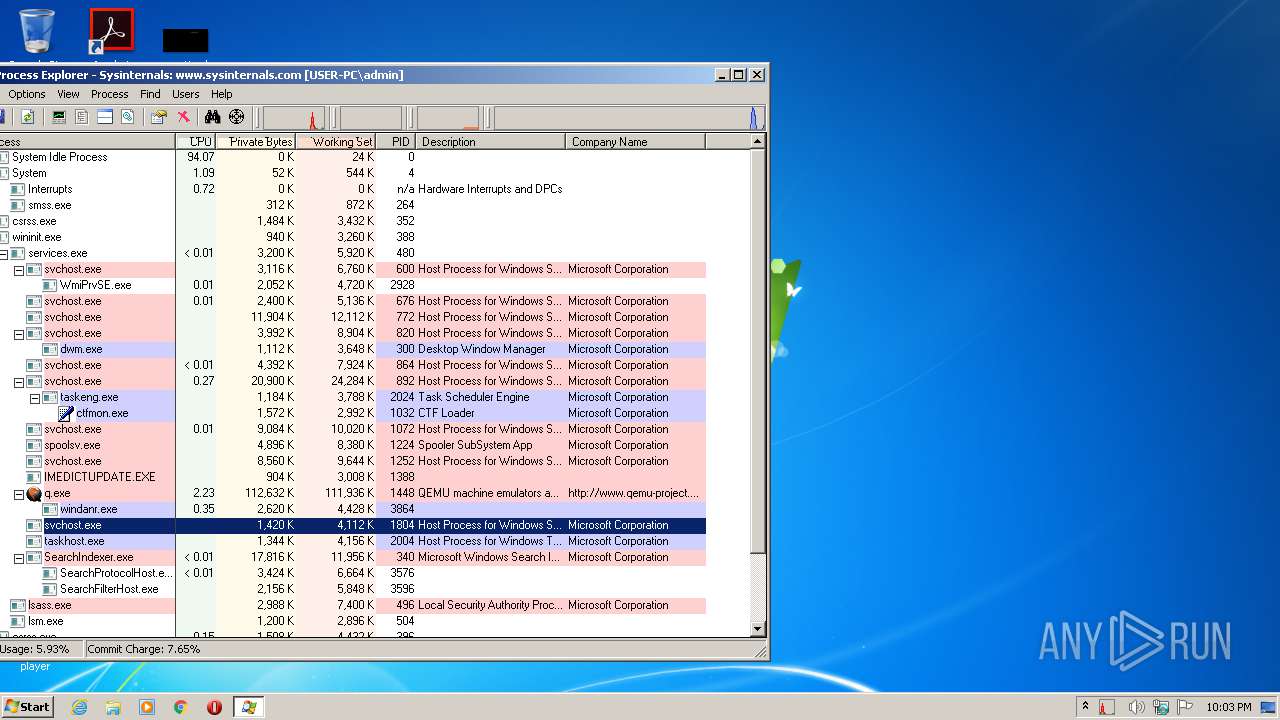
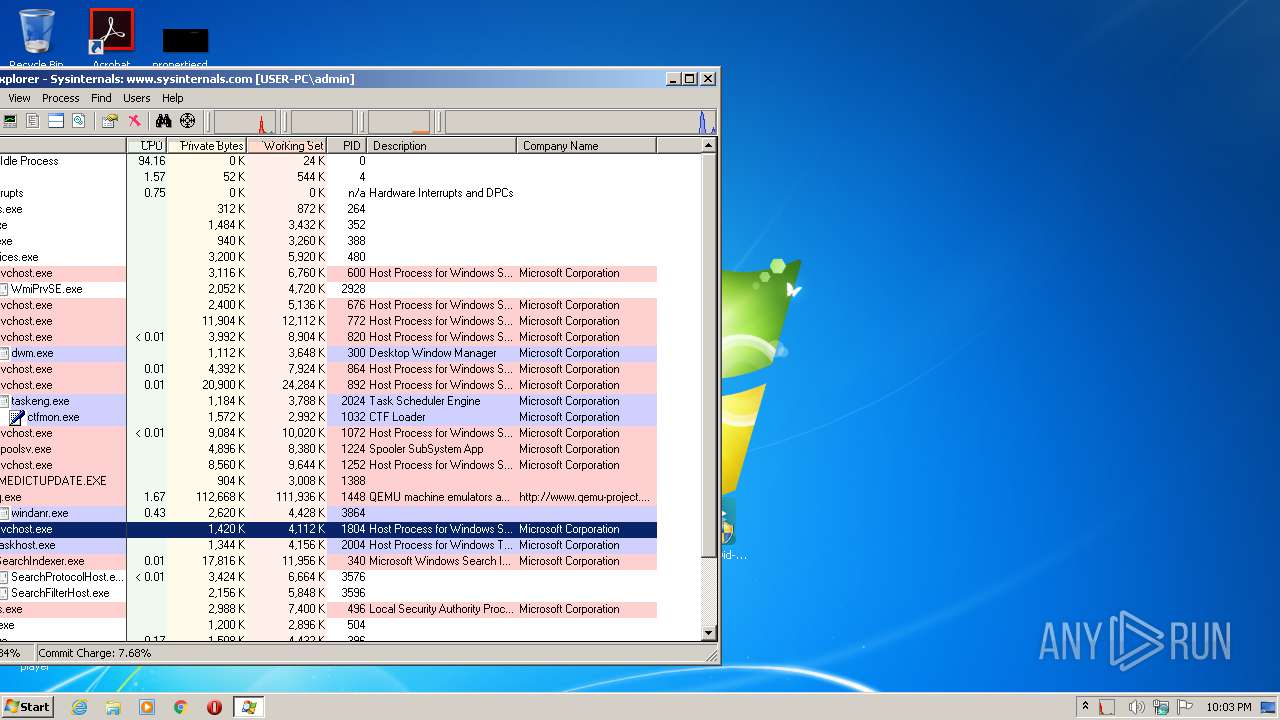
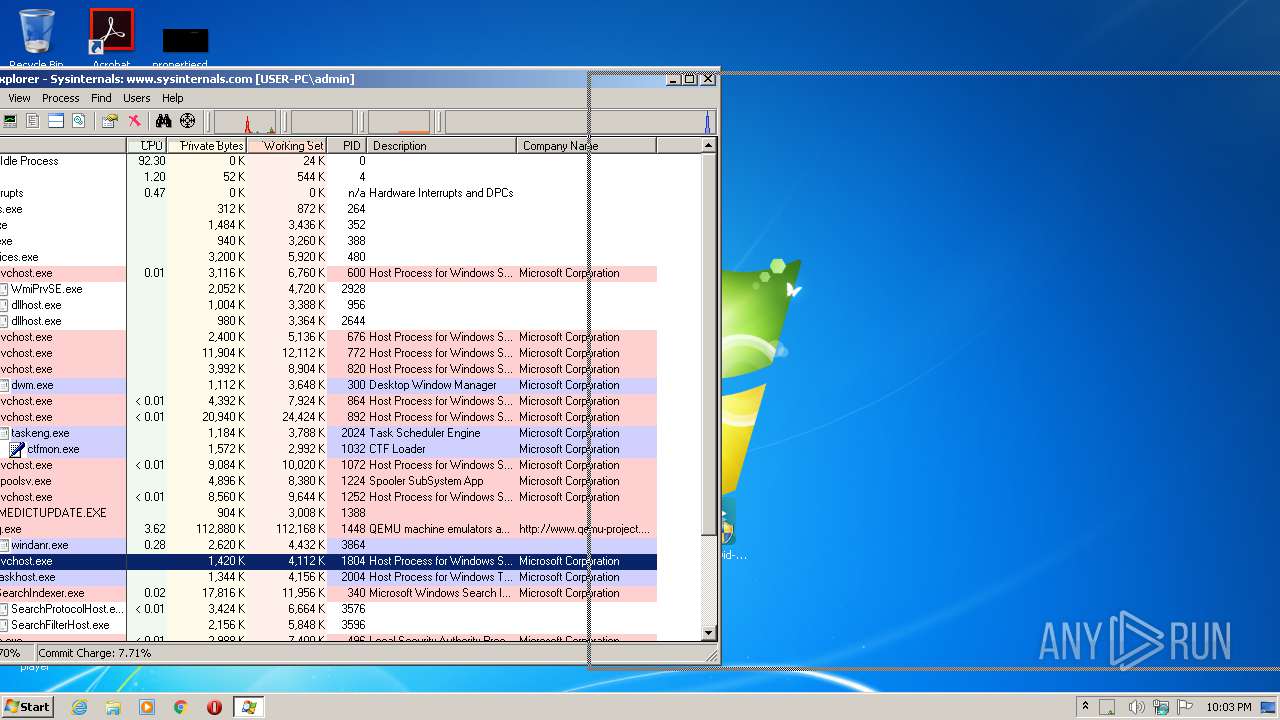
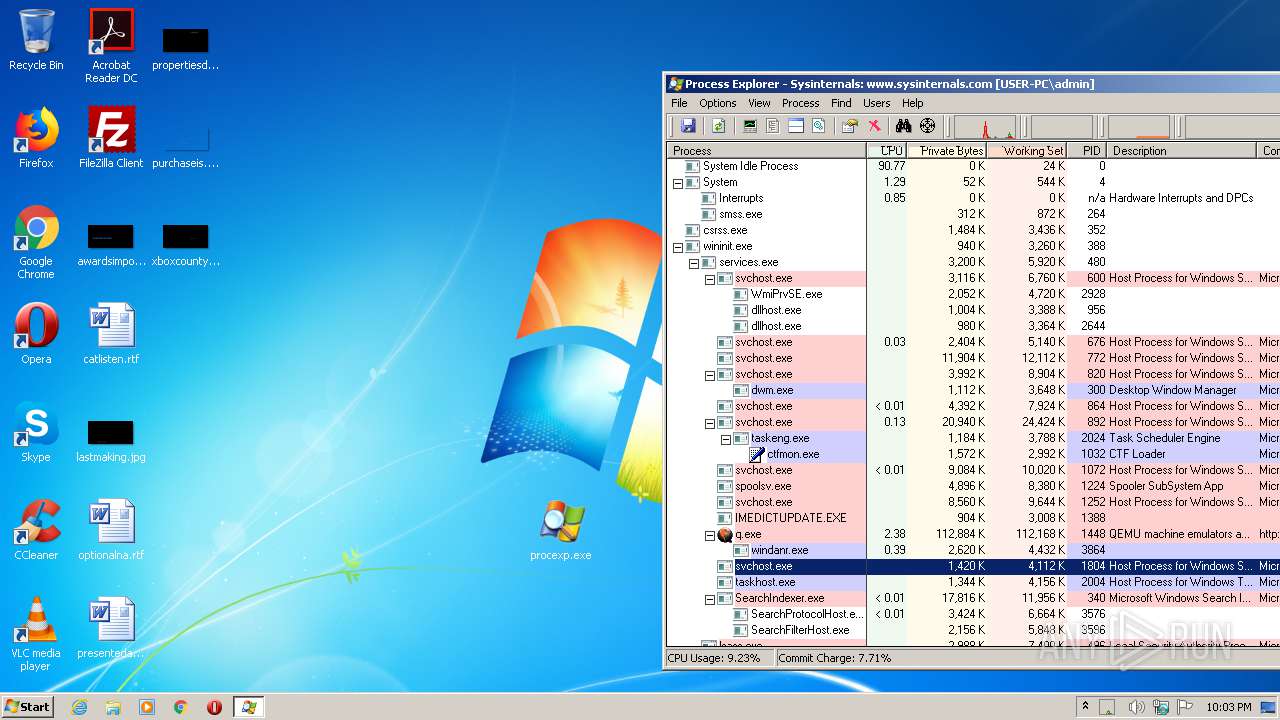
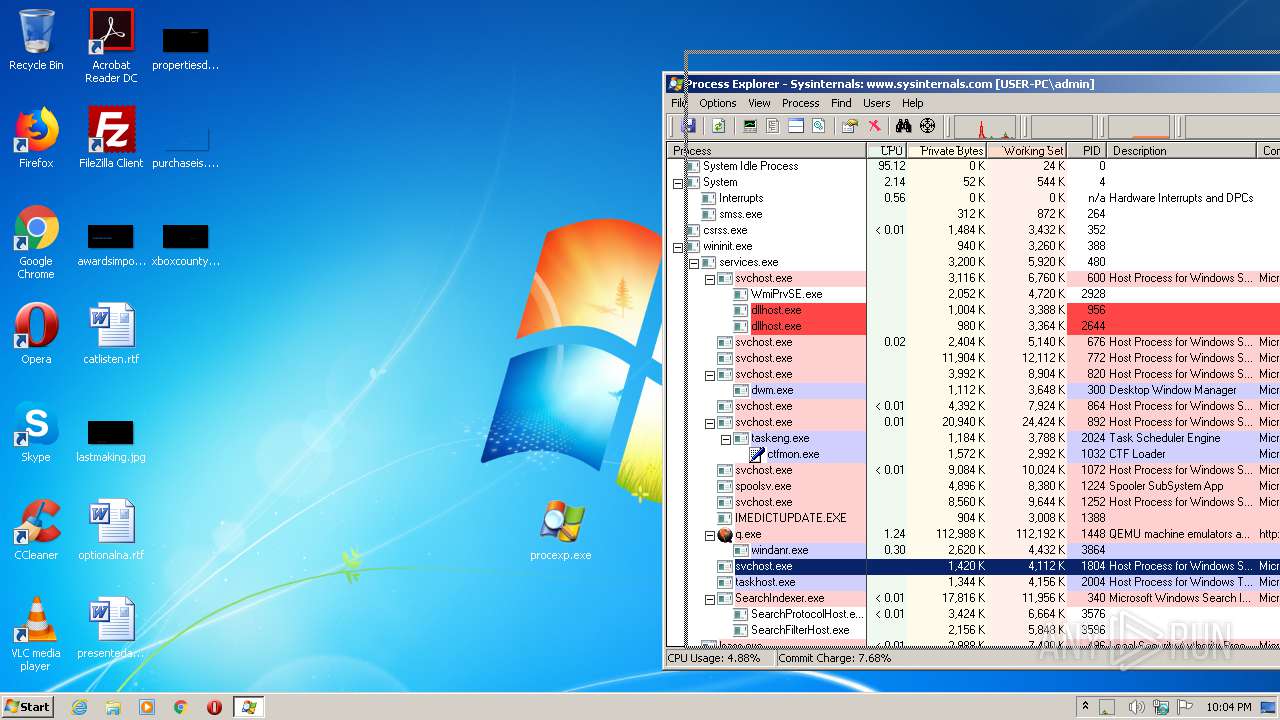
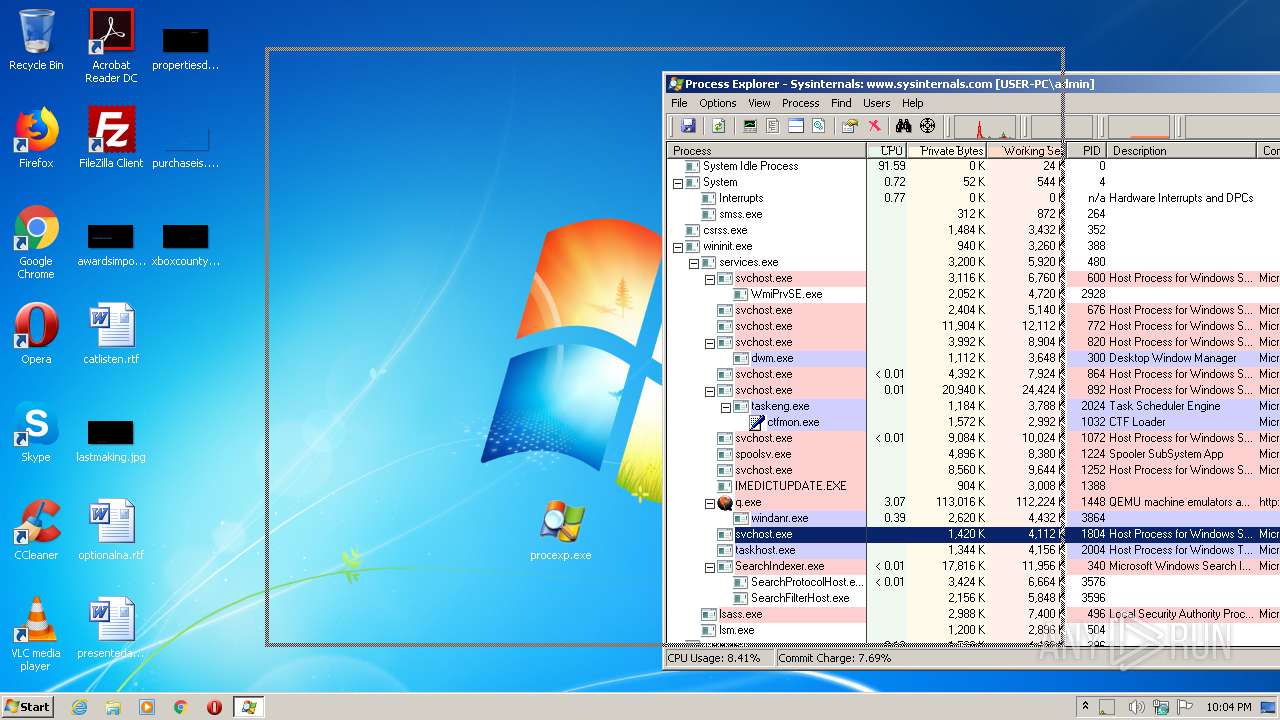
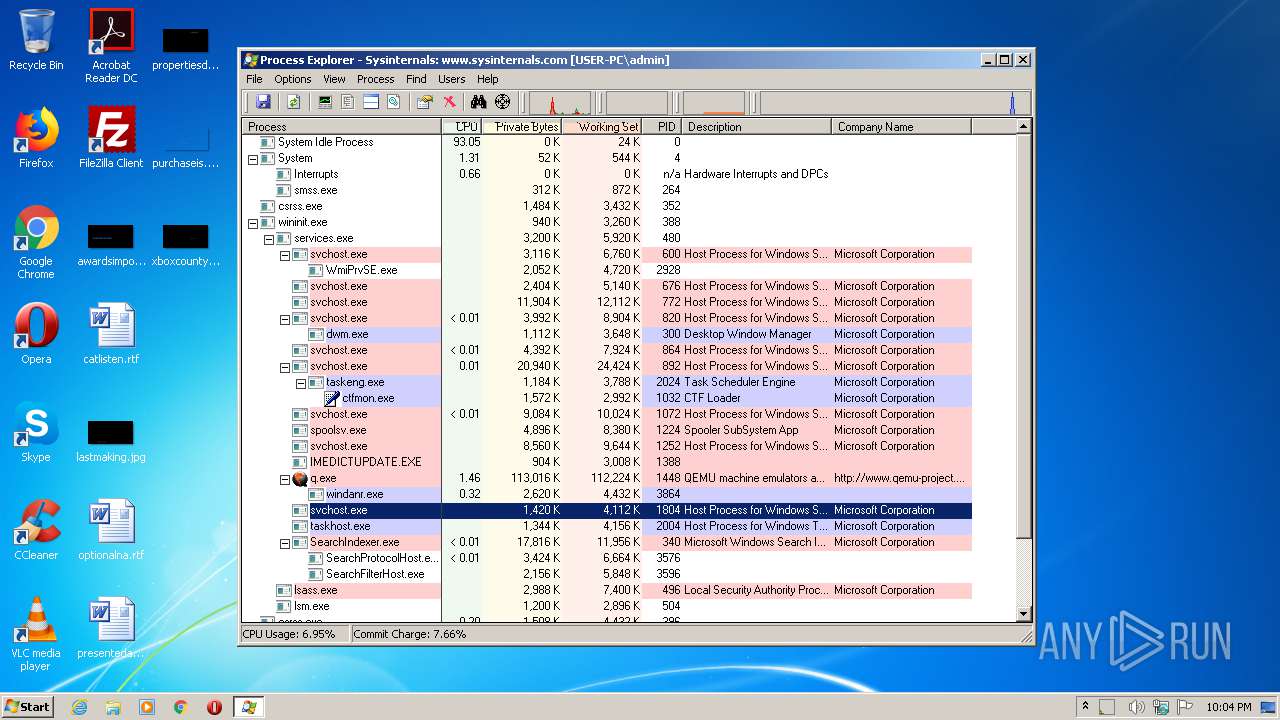
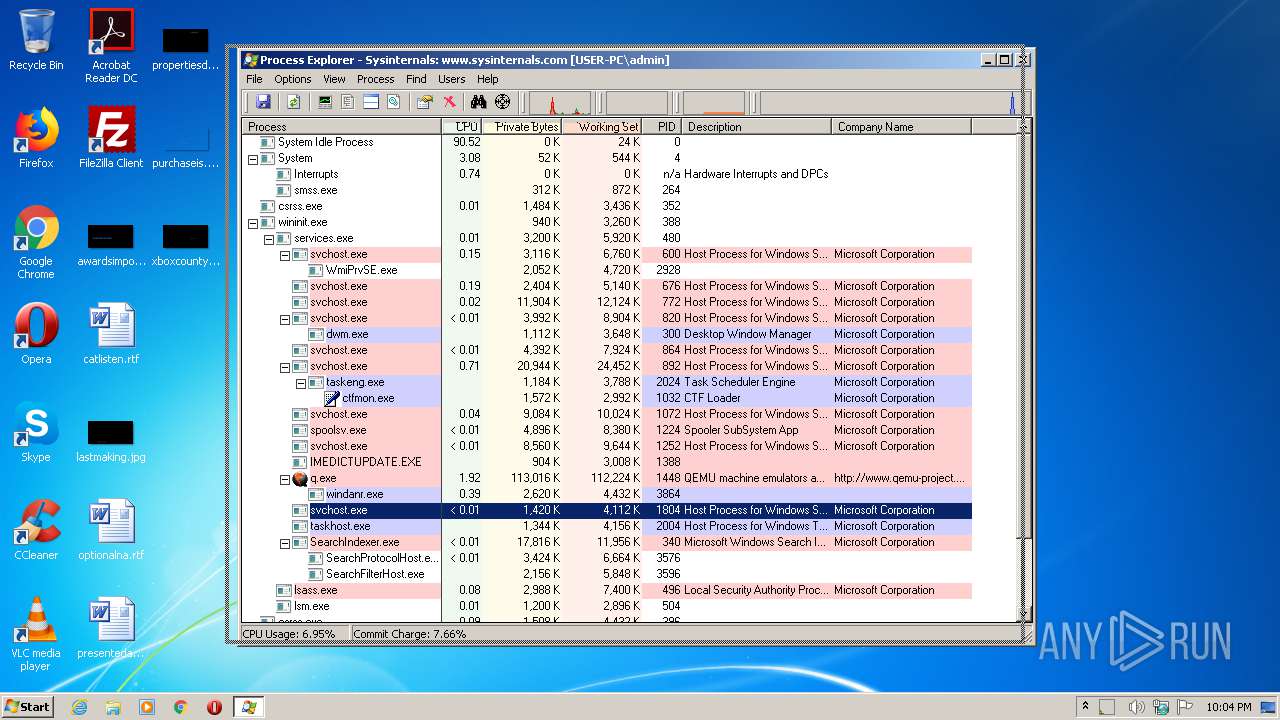
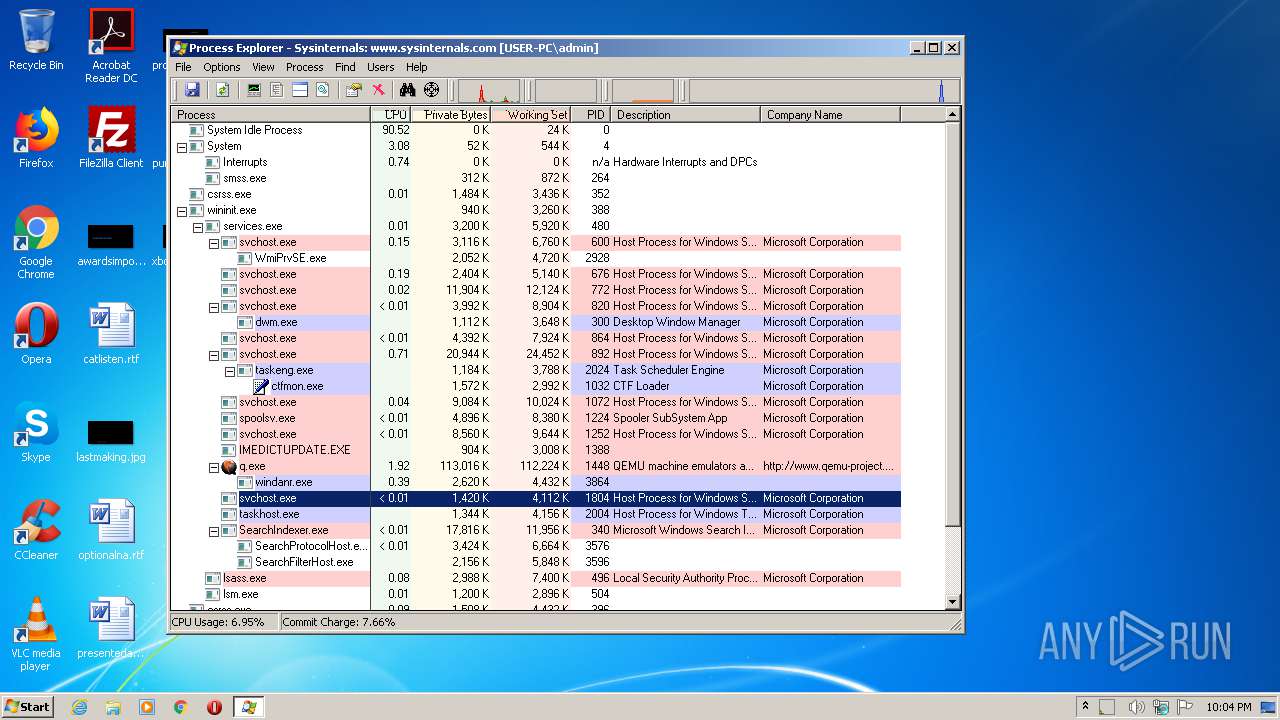
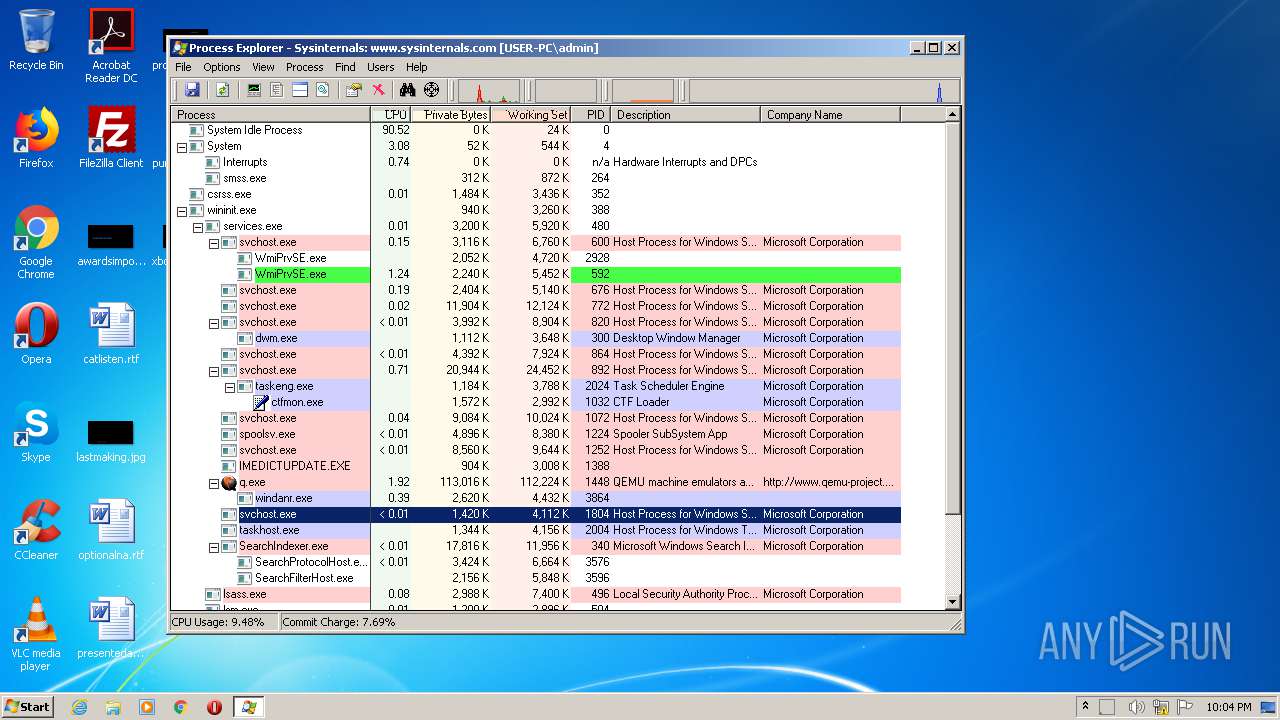
Behavior graph
Click at the process to see the details
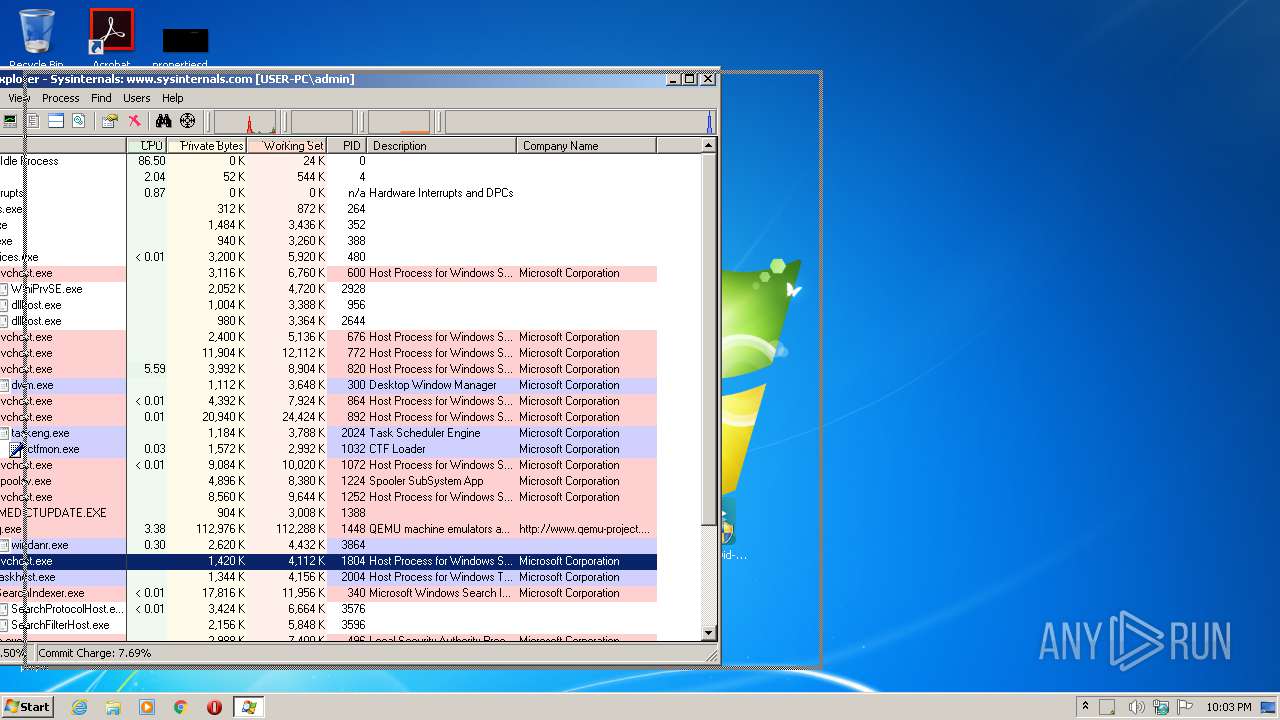
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 412 | "C:\Users\admin\Desktop\setup_hwid-changer-v1.2-[pc]l_5565265683983.exe" | C:\Users\admin\Desktop\setup_hwid-changer-v1.2-[pc]l_5565265683983.exe | explorer.exe | ||||||||||||
User: admin Company: Auslogics Integrity Level: HIGH Description: Auslogics Registry Cleaner Installation File Exit code: 3735929054 Version: 8.x Modules
| |||||||||||||||
| 1772 | "C:\Users\admin\Desktop\procexp.exe" | C:\Users\admin\Desktop\procexp.exe | explorer.exe | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Sysinternals Process Explorer Exit code: 0 Version: 16.32 Modules
| |||||||||||||||
| 1832 | "C:\Users\admin\Desktop\setup_hwid-changer-v1.2-[pc]l_5565265683983.exe" | C:\Users\admin\Desktop\setup_hwid-changer-v1.2-[pc]l_5565265683983.exe | explorer.exe | ||||||||||||
User: admin Company: Auslogics Integrity Level: HIGH Description: Auslogics Registry Cleaner Installation File Exit code: 3735929054 Version: 8.x Modules
| |||||||||||||||
| 2352 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\setup_hwid-changer-v1.2-[pc]l_5565265683983.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2980 | "C:\Users\admin\Desktop\setup_hwid-changer-v1.2-[pc]l_5565265683983.exe" | C:\Users\admin\Desktop\setup_hwid-changer-v1.2-[pc]l_5565265683983.exe | — | explorer.exe | |||||||||||
User: admin Company: Auslogics Integrity Level: MEDIUM Description: Auslogics Registry Cleaner Installation File Exit code: 3221226540 Version: 8.x Modules
| |||||||||||||||
| 3948 | "C:\Users\admin\Desktop\setup_hwid-changer-v1.2-[pc]l_5565265683983.exe" | C:\Users\admin\Desktop\setup_hwid-changer-v1.2-[pc]l_5565265683983.exe | — | explorer.exe | |||||||||||
User: admin Company: Auslogics Integrity Level: MEDIUM Description: Auslogics Registry Cleaner Installation File Exit code: 3221226540 Version: 8.x Modules
| |||||||||||||||
| 4008 | "C:\Users\admin\Desktop\setup_hwid-changer-v1.2-[pc]l_5565265683983.exe" | C:\Users\admin\Desktop\setup_hwid-changer-v1.2-[pc]l_5565265683983.exe | explorer.exe | ||||||||||||
User: admin Company: Auslogics Integrity Level: HIGH Description: Auslogics Registry Cleaner Installation File Exit code: 3735929054 Version: 8.x Modules
| |||||||||||||||
Total events
797
Read events
657
Write events
140
Delete events
0
Modification events
| (PID) Process: | (2352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2352) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2352) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\setup_hwid-changer-v1.2-[pc]l_5565265683983.zip | |||
| (PID) Process: | (2352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
1
Suspicious files
6
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2352 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2352.13801\setup_hwid-changer-v1.2-[pc]l_5565265683983.exe | — | |
MD5:— | SHA256:— | |||
| 1772 | procexp.exe | C:\Users\admin\AppData\Local\Temp\PROCEXP152.SYS | — | |
MD5:— | SHA256:— | |||
| 1772 | procexp.exe | C:\Users\admin\AppData\Local\Temp\CabF86E.tmp | — | |
MD5:— | SHA256:— | |||
| 1772 | procexp.exe | C:\Users\admin\AppData\Local\Temp\TarF86F.tmp | — | |
MD5:— | SHA256:— | |||
| 1772 | procexp.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\696F3DE637E6DE85B458996D49D759AD | der | |
MD5:— | SHA256:— | |||
| 1772 | procexp.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\696F3DE637E6DE85B458996D49D759AD | binary | |
MD5:— | SHA256:— | |||
| 1772 | procexp.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B8CC409ACDBF2A2FE04C56F2875B1FD6 | der | |
MD5:5E275DB761AA5A23AC651AF8F6C4A000 | SHA256:3B9B2F75B724FE5354D24A0EF729B8A2AAA8A9313166EAFB1F73B07CF1A745EF | |||
| 1772 | procexp.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F90F18257CBB4D84216AC1E1F3BB2C76 | der | |
MD5:— | SHA256:— | |||
| 1772 | procexp.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B8CC409ACDBF2A2FE04C56F2875B1FD6 | binary | |
MD5:— | SHA256:— | |||
| 1772 | procexp.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\F90F18257CBB4D84216AC1E1F3BB2C76 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1772 | procexp.exe | GET | 200 | 2.21.242.227:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | NL | der | 550 b | whitelisted |
1772 | procexp.exe | GET | 200 | 2.21.242.227:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | NL | der | 781 b | whitelisted |
1772 | procexp.exe | GET | 200 | 2.21.242.227:80 | http://crl.microsoft.com/pki/crl/products/WinPCA.crl | NL | der | 530 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1772 | procexp.exe | 2.21.242.227:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |