| File name: | 1.exe |
| Full analysis: | https://app.any.run/tasks/34e4c49a-1d23-4304-8e64-2f971355d897 |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
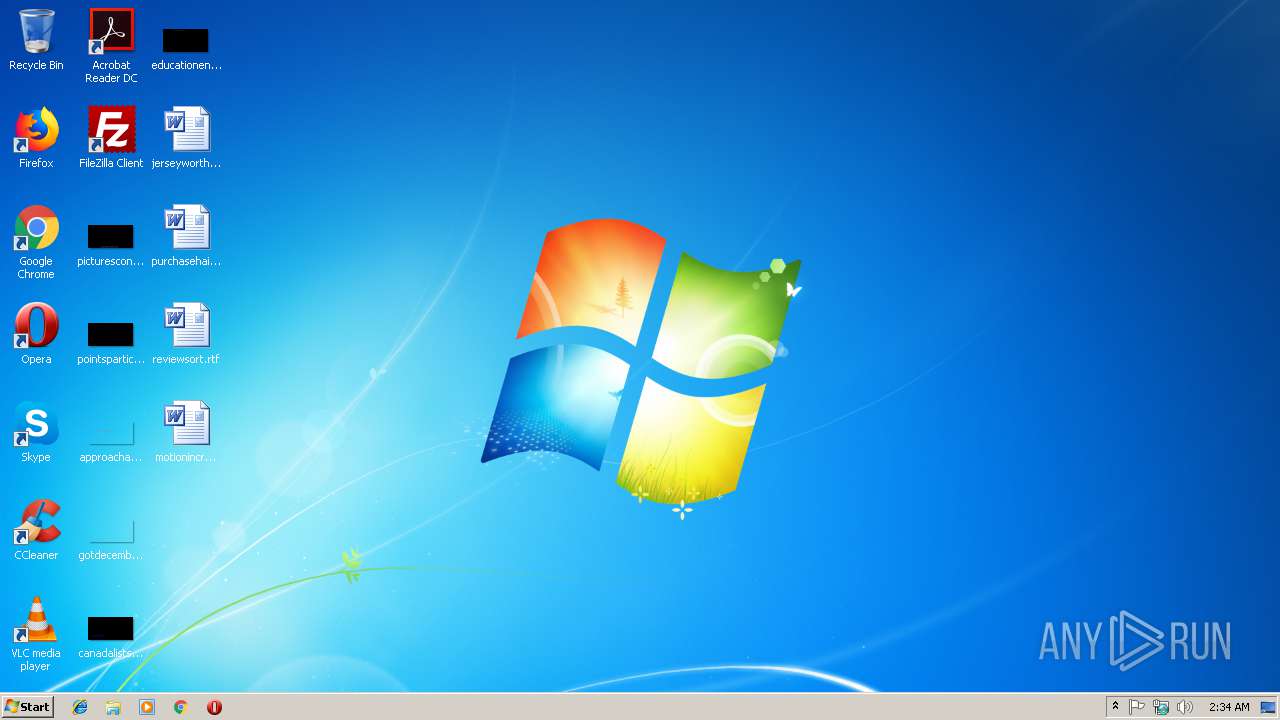
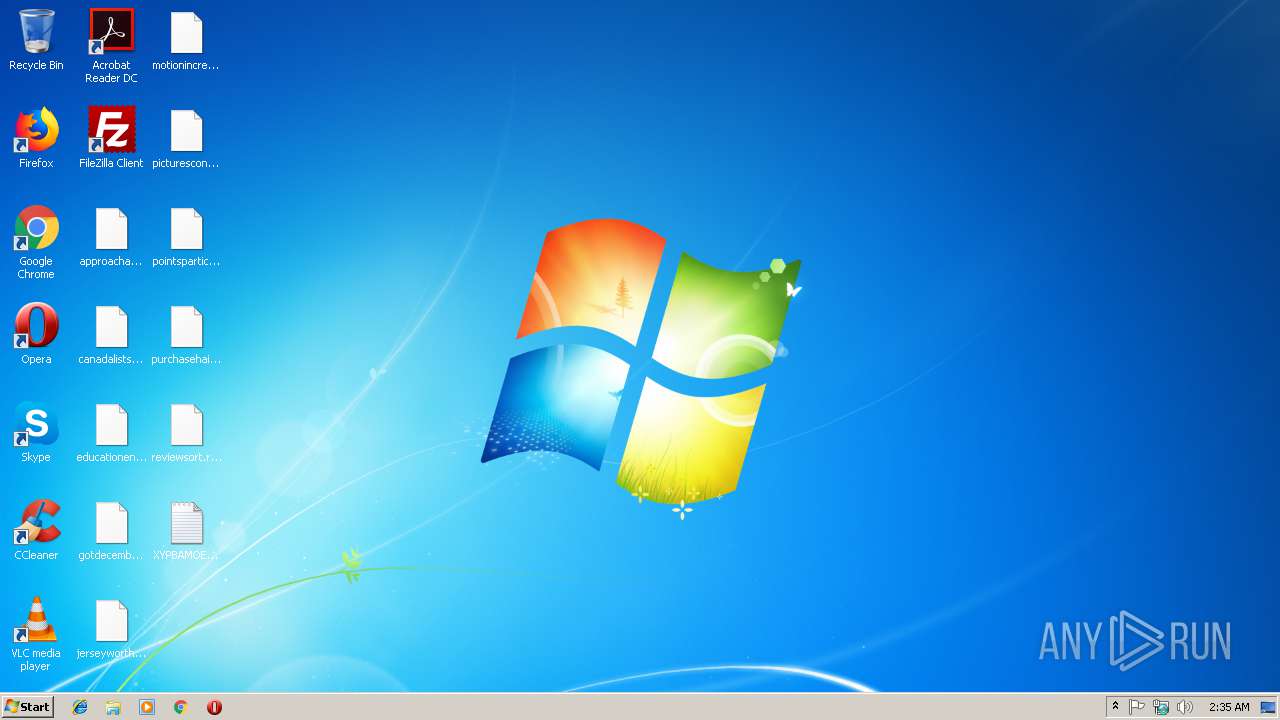
| Analysis date: | January 18, 2019, 02:34:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E387BD817E9B7F02FA9C2511CC345F12 |
| SHA1: | 98B3EC47B64198E3604C738F8C1F4753E0AFA8C7 |
| SHA256: | 39514226B71AEBBE775AA14627C716973282CBA201532DF3F820A209D87F6DF9 |
| SSDEEP: | 3072:06scOhLLGEdJT5GBQ8eTgeOJnflLfe1ndzo9cLvJkXky6GHBTfFhTWkCvaTdmGlB:0ccLLGEsC7v4c1ndzhe0IdfJC6BtZtb |
MALICIOUS
Actions looks like stealing of personal data
- 1.exe (PID: 2800)
GandCrab keys found
- 1.exe (PID: 2800)
Writes file to Word startup folder
- 1.exe (PID: 2800)
Changes settings of System certificates
- 1.exe (PID: 2800)
Renames files like Ransomware
- 1.exe (PID: 2800)
Deletes shadow copies
- 1.exe (PID: 2800)
Dropped file may contain instructions of ransomware
- 1.exe (PID: 2800)
SUSPICIOUS
Creates files in the program directory
- 1.exe (PID: 2800)
Reads the cookies of Mozilla Firefox
- 1.exe (PID: 2800)
Creates files like Ransomware instruction
- 1.exe (PID: 2800)
Adds / modifies Windows certificates
- 1.exe (PID: 2800)
Creates files in the user directory
- 1.exe (PID: 2800)
INFO
Dropped object may contain TOR URL's
- 1.exe (PID: 2800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:07:26 02:54:11+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 65536 |
| InitializedDataSize: | 307200 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5072 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.45.8.4 |
| ProductVersionNumber: | 7.32.568.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.8.39 |
| ProductVersion: | 1.0.8.39 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Jul-2017 00:54:11 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 26-Jul-2017 00:54:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000FEDB | 0x00010000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54749 |
.rdata | 0x00011000 | 0x0000411E | 0x00004200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17141 |
.data | 0x00016000 | 0x0001D2DC | 0x0001B800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.73542 |
.rsrc | 0x00034000 | 0x00028BCA | 0x00028C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.29617 |
.reloc | 0x0005D000 | 0x00001AE0 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.66732 |
Imports
KERNEL32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
156966 | 0x00000000 |
Total processes
35
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1700 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | 1.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2800 | "C:\Users\admin\AppData\Local\Temp\1.exe" | C:\Users\admin\AppData\Local\Temp\1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4016 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
135
Read events
97
Write events
38
Delete events
0
Modification events
| (PID) Process: | (2800) 1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ex_data\data |
| Operation: | write | Name: | ext |
Value: 2E00780079007000620061006D006F00650076000000 | |||
| (PID) Process: | (2800) 1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | public |
Value: 0602000000A400005253413100080000010001002B124442BC555C6FC05A3EFF1D888D2D88F0AE85E89CCA99EE30E4099E31CCDA546A221690E521EA4C1EFCB85FA2C0AC21CA93882CCA91A7B09716B5E4F845592DBF42F1A68B35FB0758F4B8C664B2DE378E7836FB8F9E1E5C1DF6C759E78063187EE8653B4BAE636FFD6D2564C55CBAE07E441F01D168181ED0548229C9851C1E502B3FC6357B170959D24E8F27F006CBF4764FA3F1869B6A5E707B6AAEE3BFE8ED43E6EFC5831EA7B022CFEC34D3E753E3D5456D9BCCAC30FB3246205BE0081C99341C59E973F76F038A0FBFA300CC9D282AB8FB36B404FC3A946724689C94E4916E1285E9C73FF4A8CBF0CAF6635064AF6F2929117BC4F7FA717295E2A5D3 | |||
| (PID) Process: | (2800) 1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | private |
Value: 940400008AC09888085B5952560F0D3D0419E0BF7594F5B1F3F62A0F4B0DD4EBFED503051E7599CFABFD33B6A14406C825826B46924DF1191BE6F85DD03BCA1F2A22AD838BBBEF73C36E20160B7E863AA5A9494630AB5ABDFC367E9B8FAB294EB9DC2CFC9035D17E6C2BFB4CC5F4FFCA6F9BABEA97493E80DE437699AA805F3C53D3F7D3103933AC10BD3AF3CD778BDD8CE6765697335A1C9095430BF052427E87434157786C8EDF11EE10597BED05298EFB23B7B13A7E4C289738DBBCDBD57EB539F6A42459A32AE9ACC6E6C7945E30A7F7E5E6BF166C69EE743FADD7C3508F314493434D6F174A39BA76BE94CA4BF5C1DD7CAC280DC7F6B7F8665A57C34AFB23F8C91F8C2C016BBDE4656449313A13C56F834C73900CCF16F55A880FE2D5AF4177164D5B4F2739A8ED7238E10BB285F5A7F8461B71F0838DA4FE4103AF0358F541FF6CB552FC1358C597B50917595585D6225D93F1E21B11E53921FEF6E94D7666E5D550162D0374226074332620C926BEBC3E7E5D2D4E794CF18057D857F0612559353F94791BF7969FCC227EC50C3B071BD7AE7C0655A116807564CEDB3F0EB292DDEE78DA384DFCA690D960726A09C19E565AD35C80079791D905697C9FF54A51398A2169699B84BE5801FA93163BDF69075137ADF89BD35DE2A74FB93706AC29CB6334E55D76B000B434564C71E32DE83434934D24CA387C14F6CAFBF4676C70400B9D6F165843D85EF59E50EC3E781995FEF7434954EF39764D56C9ED1F54BC76ADAD7376BF9A18343368B8AC615CF0909150A8D252D1AC9C470B81D38883A014A78920B1188B2211B101C5C10C40206A4ED55128D9FE805D3433F8251CA9FAF65E374EC903094824167C6621F6BB0800C53B689276A7A17BD2EF54CA1DE1BC4D1A47117E2EAC785D4189BEC2EB9A1877538EE7907F71FC769C58DECB5EE16CA1163BFCD92773C6BF3A89ECEF43DAD4A6428EA8D59B706DB51D511A89723D5CA092B44AA5ADC5D1605B9AC594FAC744518A97C441C6A4016F75F64A32A5B0EB9715D6A29D4E3C3F18B193F5143D5673E7B23017CB93A7E8DD4E3134D20549E5AAA51446E78B1FAE1836F9491A56E303DC7E8DEBEA0EDEBEDB6EC5F9A27F045B94BA77922C3140153D79A1EC6127AAC3CB063B6E812ED1A3F420E0A0F26B9B7DEA4B2B679C69AB316C59B047ACA5E589F0226264032AD7B38103272DBA61427D9370CF121243100D5CD3E48201FF71EF62B38C806F5F592A61AF9110A5B418BD43BE2CEE120C3FB719202EEF92C63CE8F7FD18D6D52DC1B7ED0930868981A7DB613D0E3C47988FE36A11B898565812D40D5F9F7A8753BB2D3D6EA0C5B28A08185C00A1A35A3972A3B4B10C66458A0CCD2AD2CFC183DE3C5CF7A9363D7E653F133712ACEB11BC0E9DF8D6F1298C52F7D858A4A1B1D2921B1736026A5664B35A2B1E6AFD6A04022890E62D1FD838DA818DC7731D3C8DF48151343BACE0B79E682736CC93EED8016C61DA636436CF837CC74CF959E260004853779A0D0E0BE906F1D73BEBA6FD169AC9E1041BB5AA5428581600F0E359A6B0CB25E372EA7FF8F820BB04232E878B44EAEDE2E1354229F41E4017833C334F27BD092B6CF318BDFA7064D9AF0D9B40389B52073C998390D04B66D5CAC7A9A21D40B140C65E51AC3E97D9925F34FFCE0334271217FEF431D8BDBD2ACC62C32D25E76236204CFE861EC99ABFCFBFD566EB85DCA54FFF66970EF3CF5FE24A2D8645E860EECEEC71A6DFB678B800842612A394DE41059EB1078098FE17F84BB09B8E0417F9089F02CFB2243EC1B636D11471EFB0C198F47FCE1F3F8C3331A0371A728F2BB22FC18FC51D66EFCB595B20E7A3F679E414E43EC8575DB986EDF13D7C1490566F926543A1DCB9DF0E343AEAB59A8CCCF756F6D229C183F731D03A6D9D365A266320AC31C5AF96F0AD4BBDA6A9BD4014EDC689994F7303C046187F9D852921F7489EC70F219000B4375D784B55D3978F1CDA7694CE50FC3601085F37D0DC95FF2DAE6AF5A691A1B327A1E163DD0BF7D142F13619135DC1875298D9FC6EBA4CE01AF3400BB2BB64BDB04AAB8D8CEB03163CBB79D6A7A75398970B0E62B2705E6AAE17748D56B53290F8089C9563892BEC0E72A723E655B2DED4E5878EA16769BD50C311BD237F40F1B6984CC85AB415DB43918E112AB07AA060602410CE426A0AD9908D8AAC305972AEDEC84BE40DC4E2F20B7380473967E2FCB18054A5B2E8318EE1B6622C0A8D69091CD430E04E8BC176FC5388D375AC67B976C17D2035D007362CFBCB2EE1D266B8F048750F7F9234FAD7B4501840AEFE67CC424B3E9DA3D4D26E404D30D10D148DBF920DF4C76F33583340A72411A86405708C4E | |||
| (PID) Process: | (2800) 1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2800) 1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2800) 1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\1_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2800) 1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\1_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2800) 1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\1_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2800) 1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\1_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2800) 1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\1_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
425
Text files
318
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2800 | 1.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 2800 | 1.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.xypbamoev | — | |
MD5:— | SHA256:— | |||
| 2800 | 1.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 2800 | 1.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{05ed3515-06b3-48f6-8cf2-bf24b1bf0727}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2800 | 1.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{16d74681-6bc3-4c44-97f0-8b8dfefe2355}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2800 | 1.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{38e8535f-27d0-4352-aa3a-ce4178930102}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2800 | 1.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{3cc0f82b-873a-4e59-b89f-689fbdf88af9}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2800 | 1.exe | C:\PerfLogs\Admin\XYPBAMOEV-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 2800 | 1.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{5c4beaff-a038-4df7-9b35-072a18f8e3d6}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2800 | 1.exe | C:\Config.Msi\XYPBAMOEV-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2800 | 1.exe | GET | 301 | 138.201.162.99:80 | http://www.kakaocorp.link/ | DE | html | 162 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2800 | 1.exe | 138.201.162.99:80 | www.kakaocorp.link | Hetzner Online GmbH | DE | malicious |
2800 | 1.exe | 138.201.162.99:443 | www.kakaocorp.link | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kakaocorp.link |
| malicious |