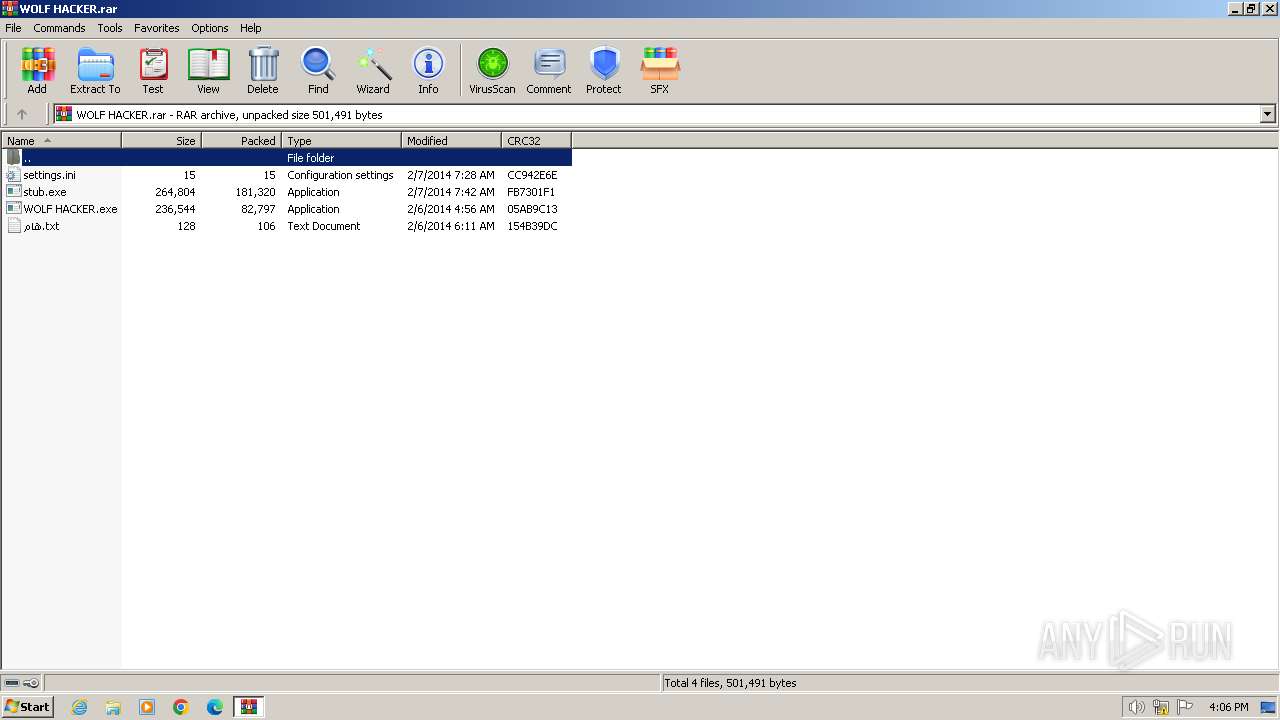
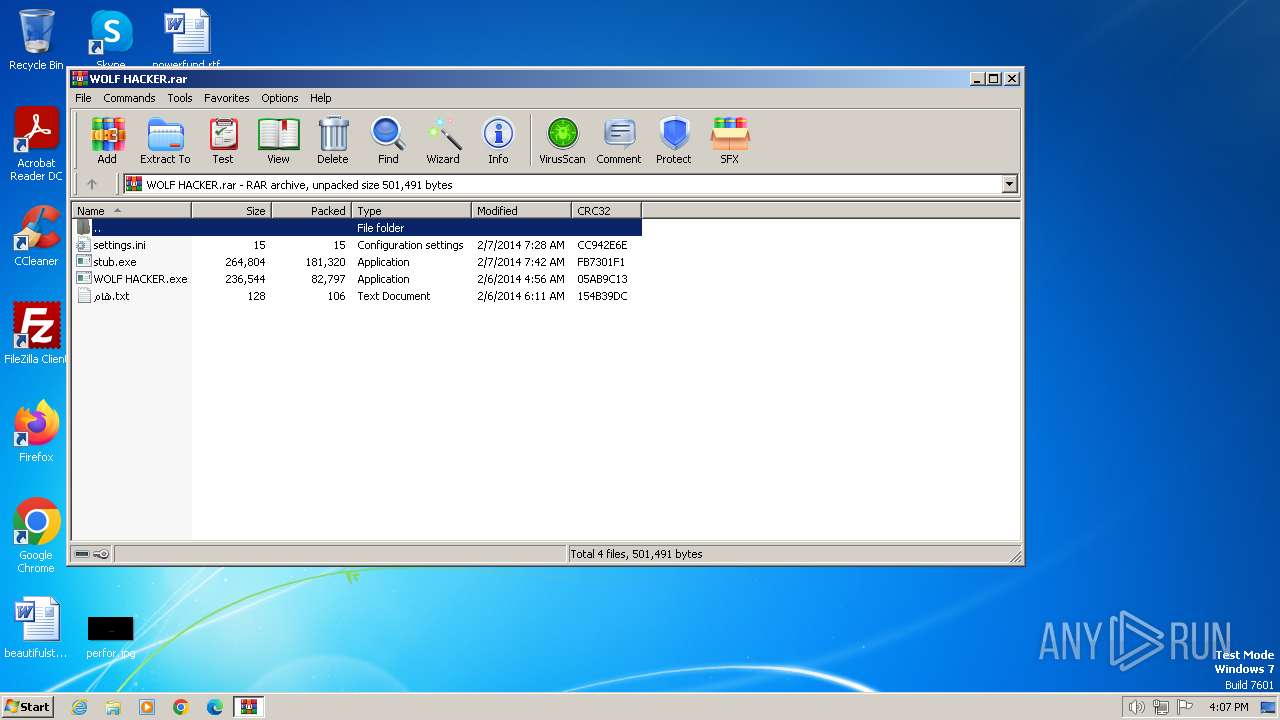
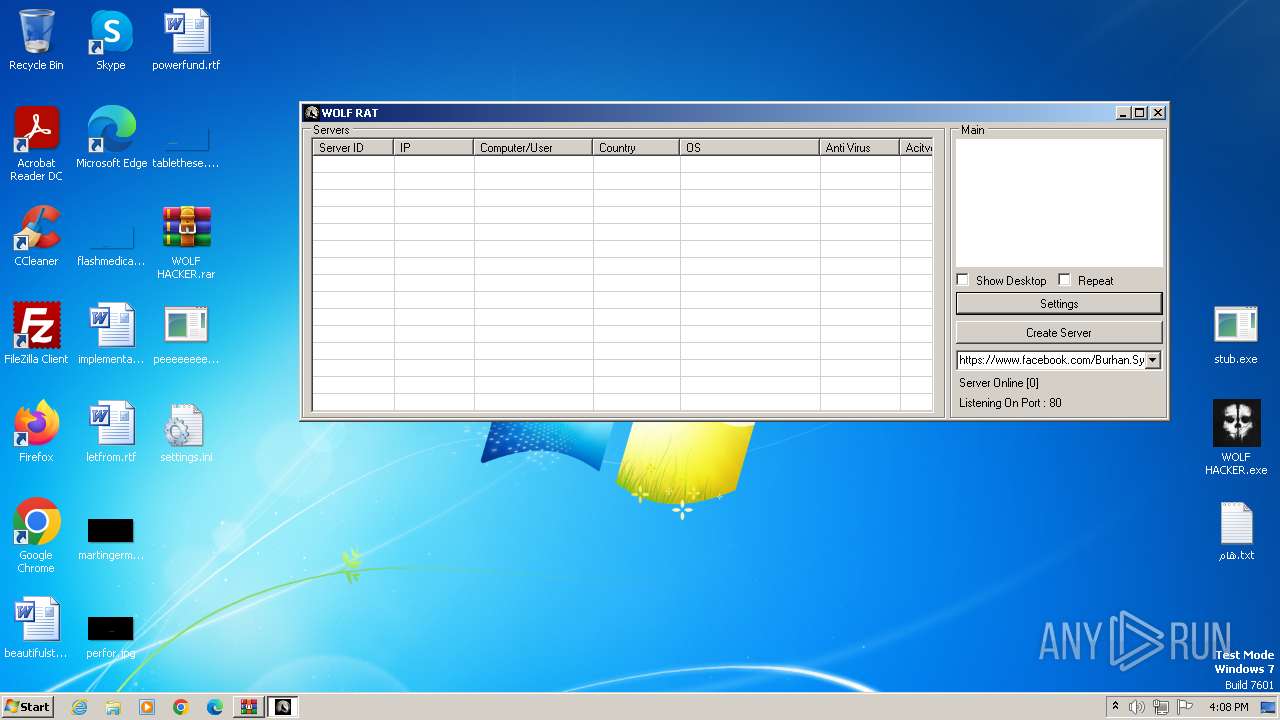
| File name: | WOLF HACKER.rar |
| Full analysis: | https://app.any.run/tasks/7950e084-0892-4dab-aa17-6534b3085d74 |
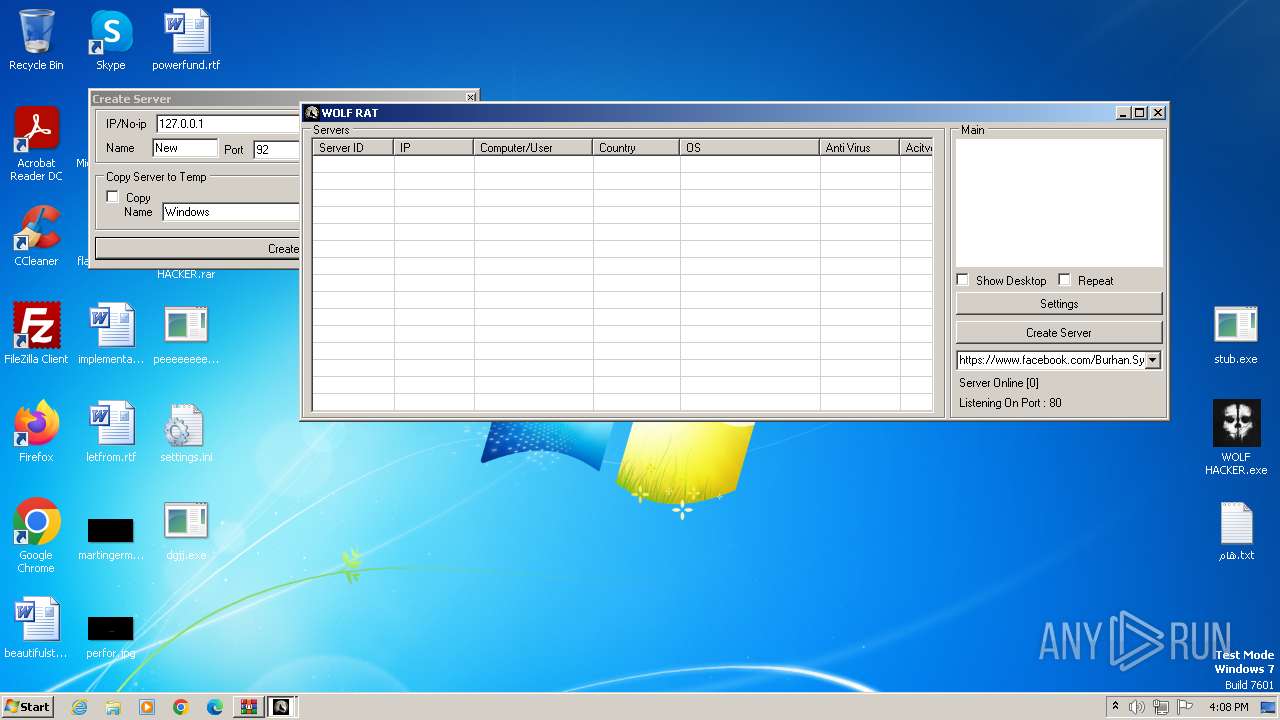
| Verdict: | Malicious activity |
| Analysis date: | August 03, 2024, 15:06:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 59520F069BEAF9DCD10A1E618F51CD55 |
| SHA1: | D89E641DCEBF8AD35FEF1B34207DFB13D638E69D |
| SHA256: | 394E1E835B587C2E292A04A25FF7066971B2A72AEF8990714D05B3746D794BFB |
| SSDEEP: | 6144:hmzmhWips9ZiEv+VbOCFDXVSyXvyUdDARJt0VfF+mlg/S:fW9Zim+VbOWDXVHXv5dDAF8fF+mlg/S |
MALICIOUS
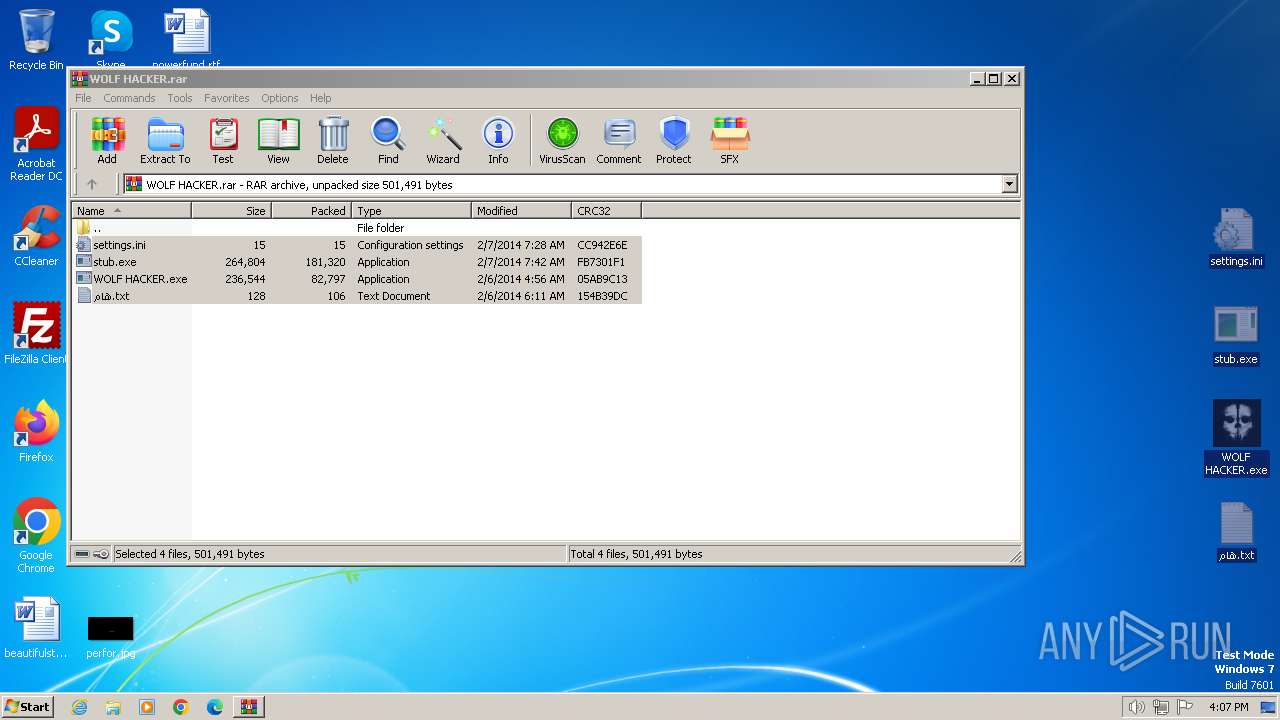
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2472)
- WOLF HACKER.exe (PID: 3488)
SUSPICIOUS
Executable content was dropped or overwritten
- WOLF HACKER.exe (PID: 3488)
Reads the Internet Settings
- WOLF HACKER.exe (PID: 3488)
- peeeeeeeeeeeeeeeeeee.exe (PID: 3032)
- dgjj.exe (PID: 3096)
- peeeeeeeeeeeeeeeeeee.exe (PID: 400)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 2088)
- WOLF HACKER.exe (PID: 3488)
- peeeeeeeeeeeeeeeeeee.exe (PID: 400)
- peeeeeeeeeeeeeeeeeee.exe (PID: 3032)
- dgjj.exe (PID: 3096)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2472)
Manual execution by a user
- wmpnscfg.exe (PID: 2088)
- WOLF HACKER.exe (PID: 3488)
- peeeeeeeeeeeeeeeeeee.exe (PID: 400)
- peeeeeeeeeeeeeeeeeee.exe (PID: 3032)
- dgjj.exe (PID: 3096)
Checks supported languages
- wmpnscfg.exe (PID: 2088)
- WOLF HACKER.exe (PID: 3488)
- peeeeeeeeeeeeeeeeeee.exe (PID: 400)
- peeeeeeeeeeeeeeeeeee.exe (PID: 3032)
- dgjj.exe (PID: 3096)
Reads the machine GUID from the registry
- WOLF HACKER.exe (PID: 3488)
- peeeeeeeeeeeeeeeeeee.exe (PID: 400)
- peeeeeeeeeeeeeeeeeee.exe (PID: 3032)
- dgjj.exe (PID: 3096)
Reads Environment values
- WOLF HACKER.exe (PID: 3488)
- peeeeeeeeeeeeeeeeeee.exe (PID: 400)
- peeeeeeeeeeeeeeeeeee.exe (PID: 3032)
- dgjj.exe (PID: 3096)
Disables trace logs
- peeeeeeeeeeeeeeeeeee.exe (PID: 400)
- peeeeeeeeeeeeeeeeeee.exe (PID: 3032)
- dgjj.exe (PID: 3096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
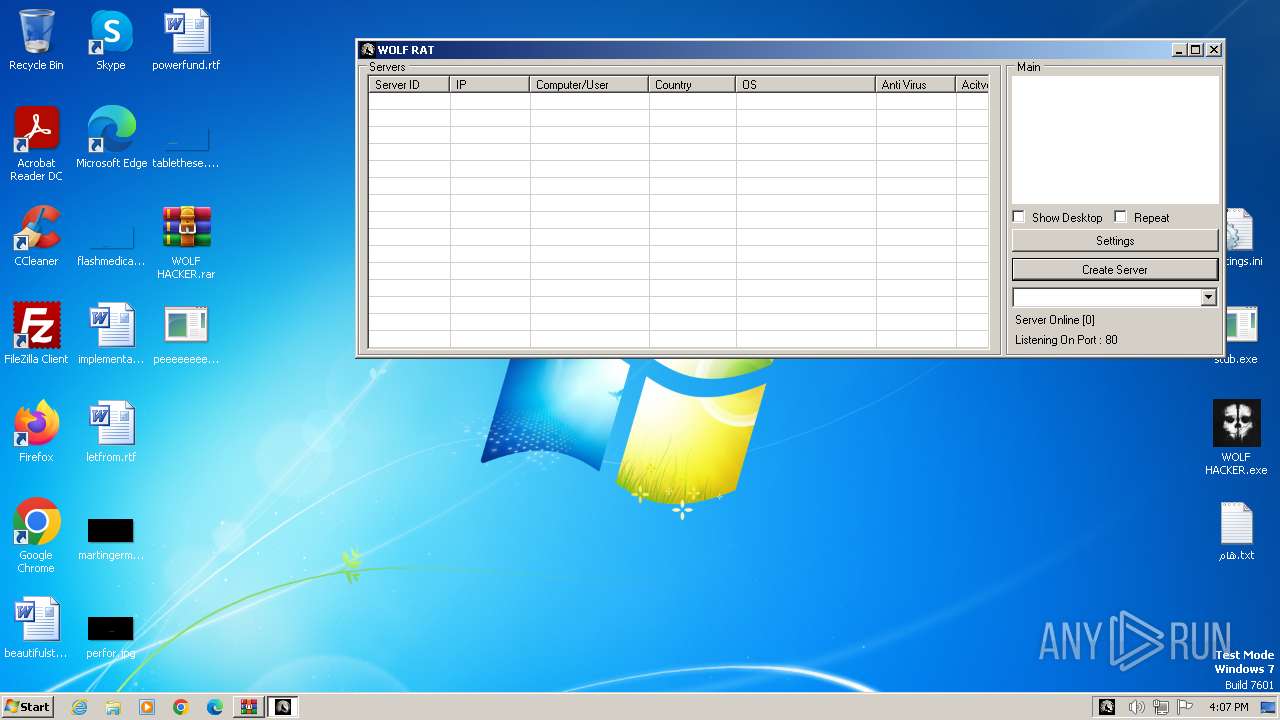
Total processes
50
Monitored processes
7
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
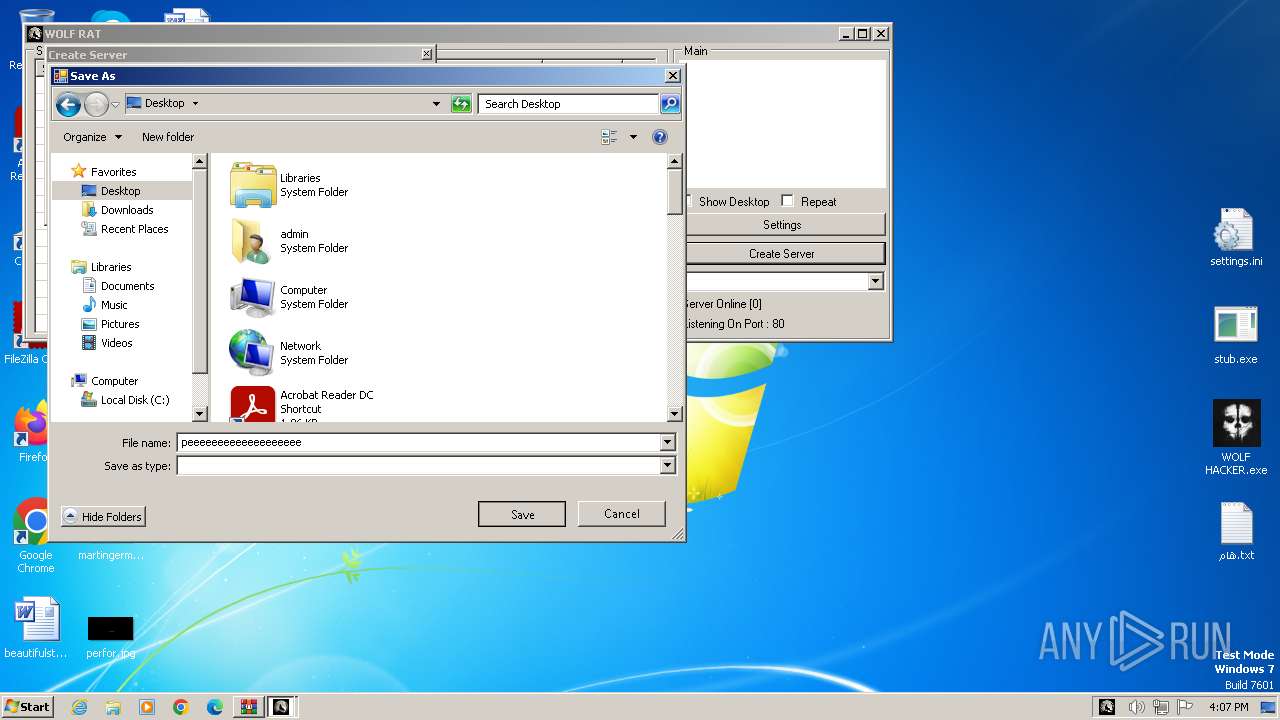
| 400 | "C:\Users\admin\Desktop\peeeeeeeeeeeeeeeeeee.exe" | C:\Users\admin\Desktop\peeeeeeeeeeeeeeeeeee.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: burhan Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) | |||||||||||||||
| 2088 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2472 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\WOLF HACKER.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
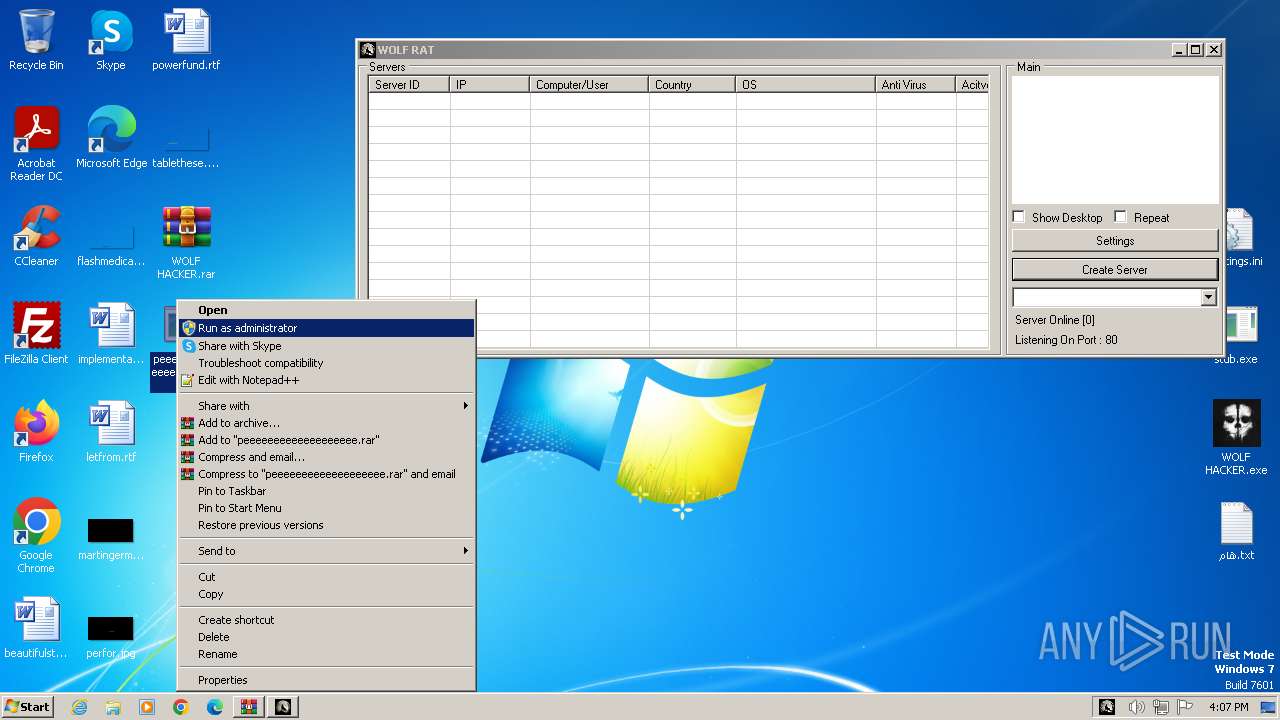
| 3032 | "C:\Users\admin\Desktop\peeeeeeeeeeeeeeeeeee.exe" | C:\Users\admin\Desktop\peeeeeeeeeeeeeeeeeee.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: burhan Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3096 | "C:\Users\admin\Desktop\dgjj.exe" | C:\Users\admin\Desktop\dgjj.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: burhan Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
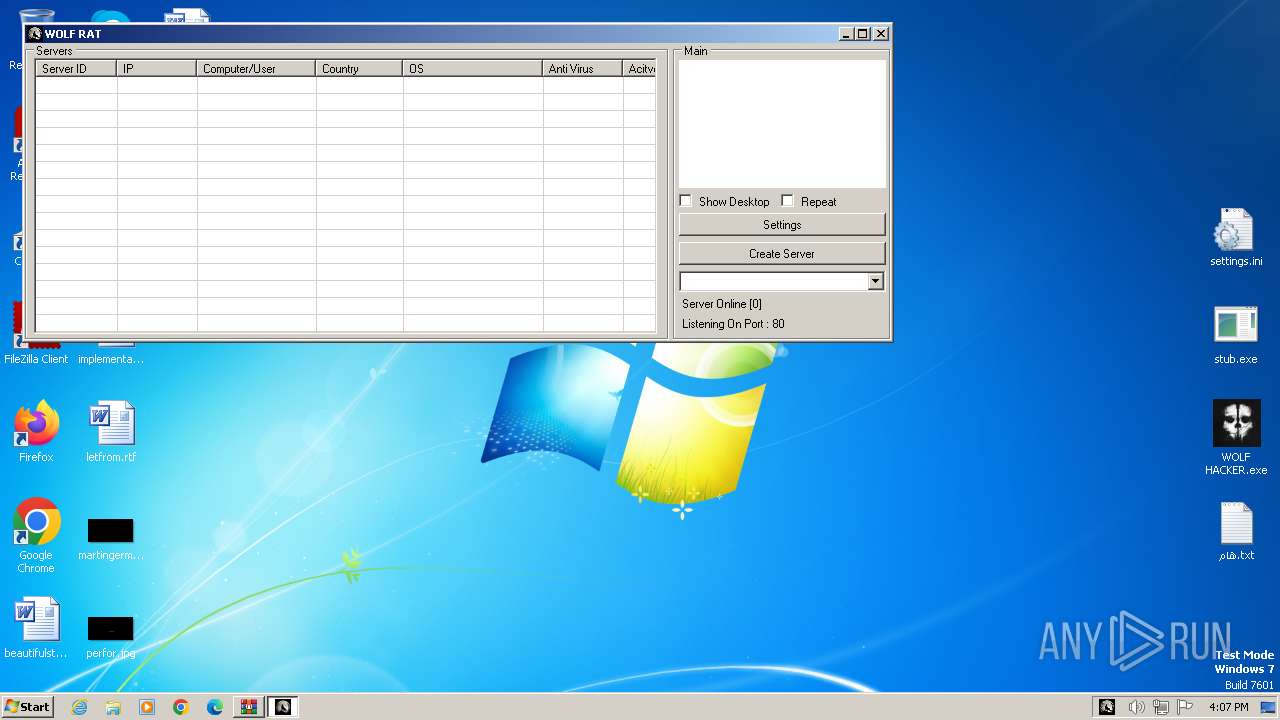
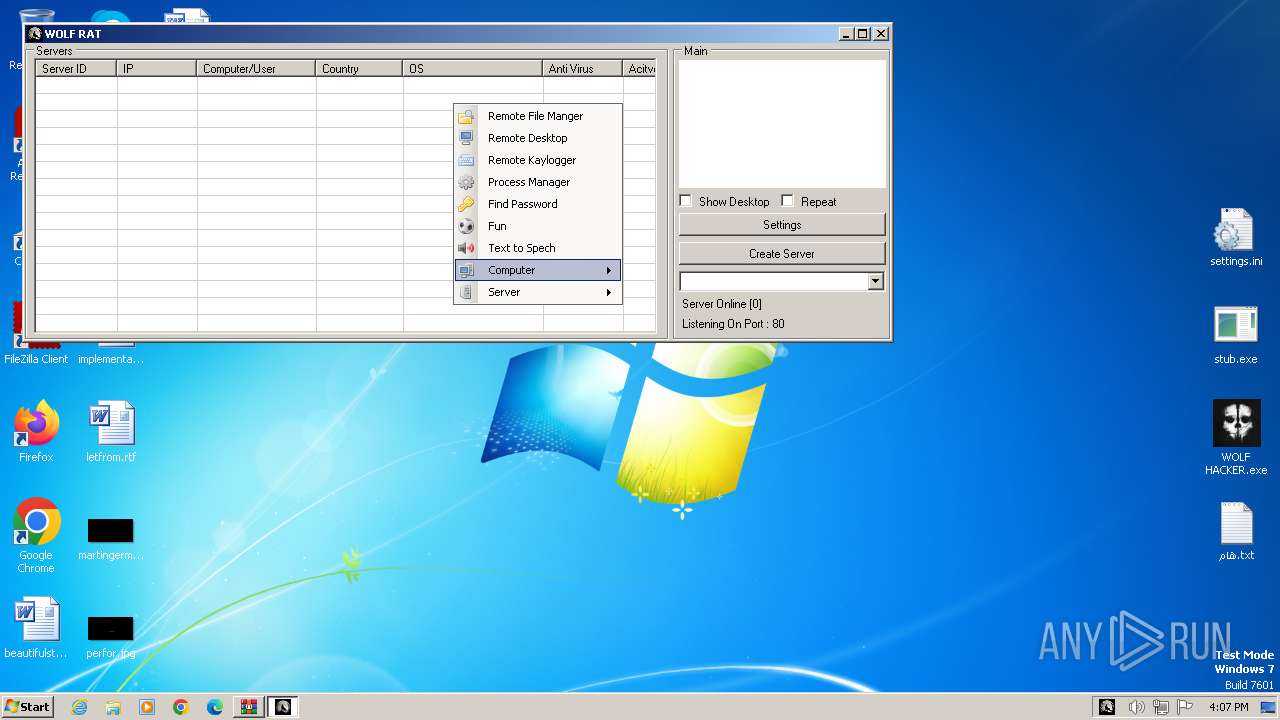
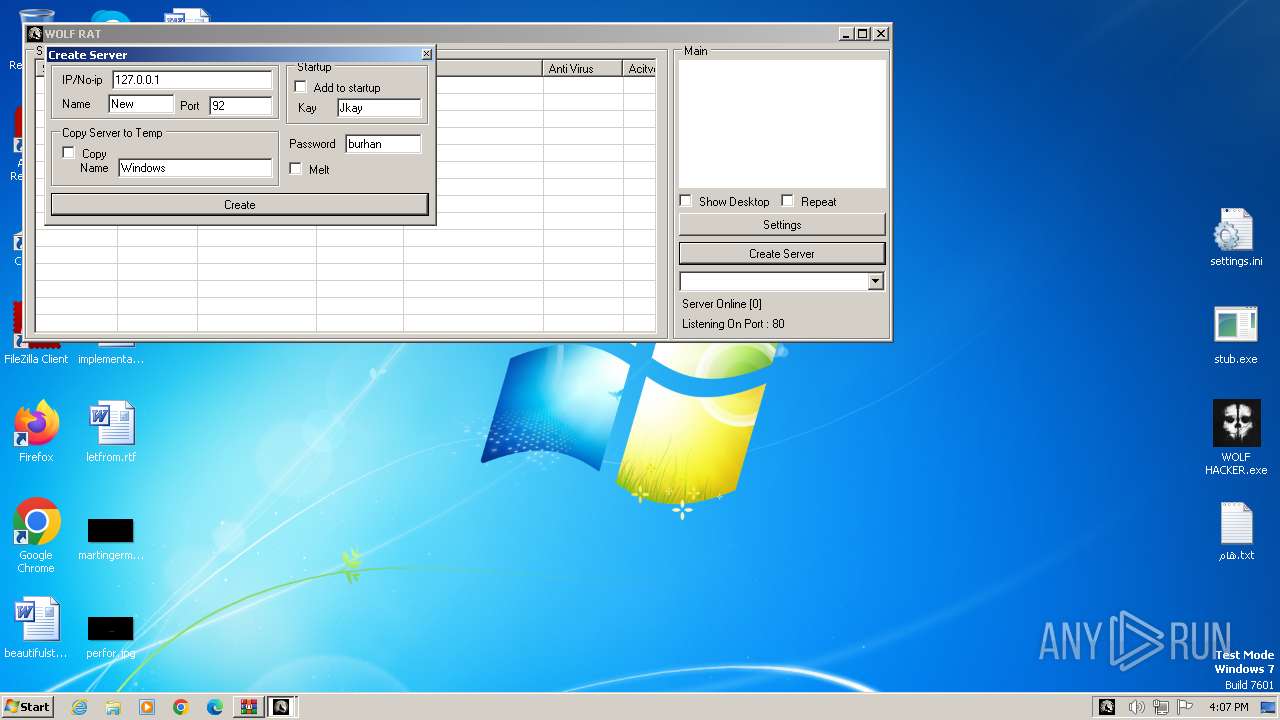
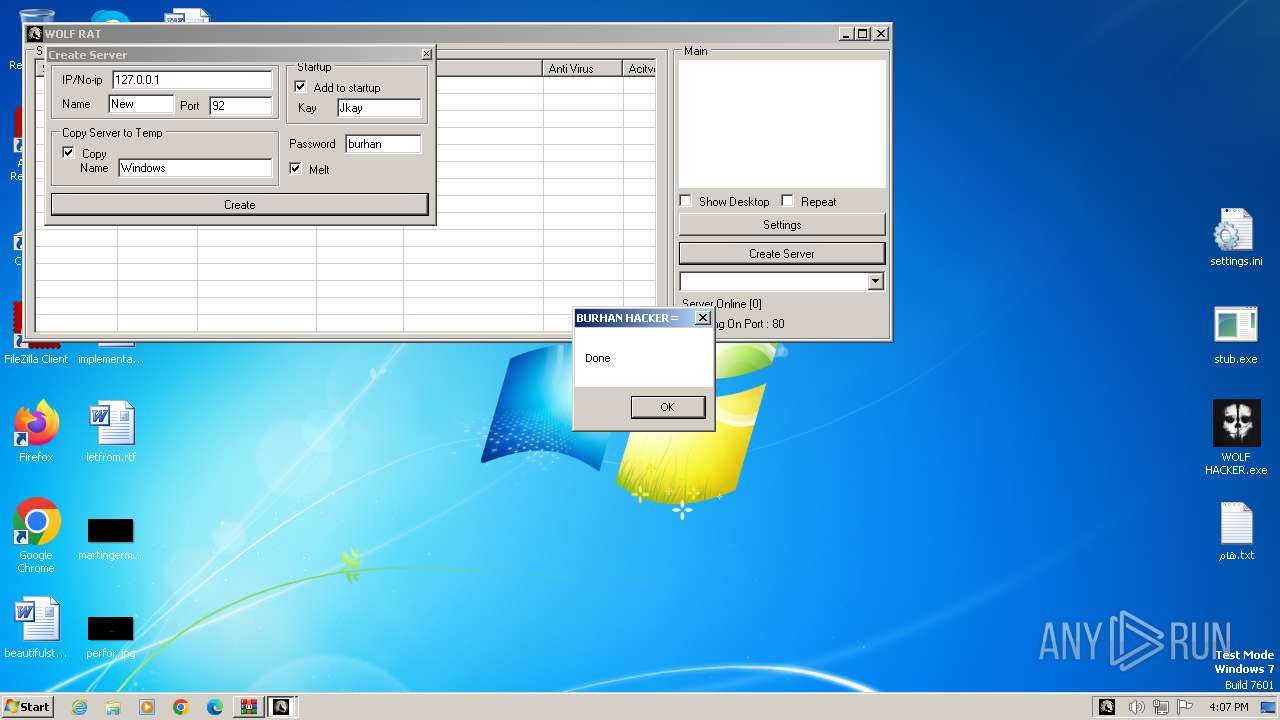
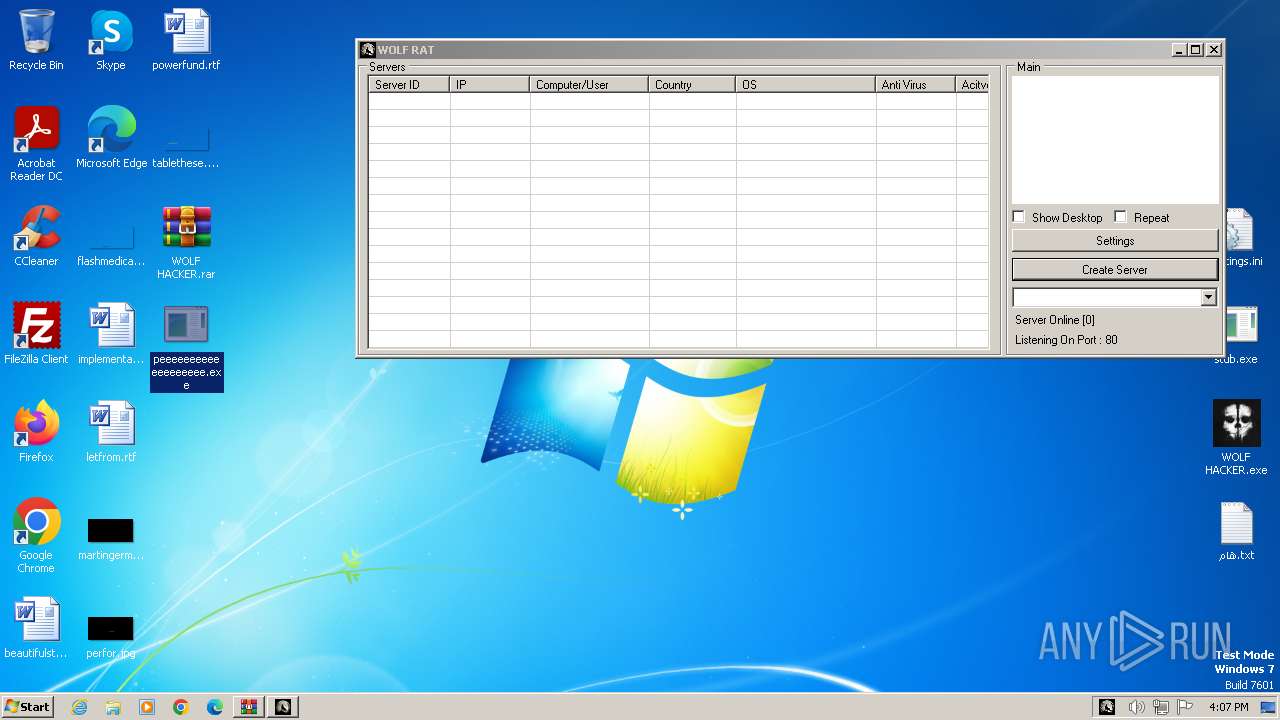
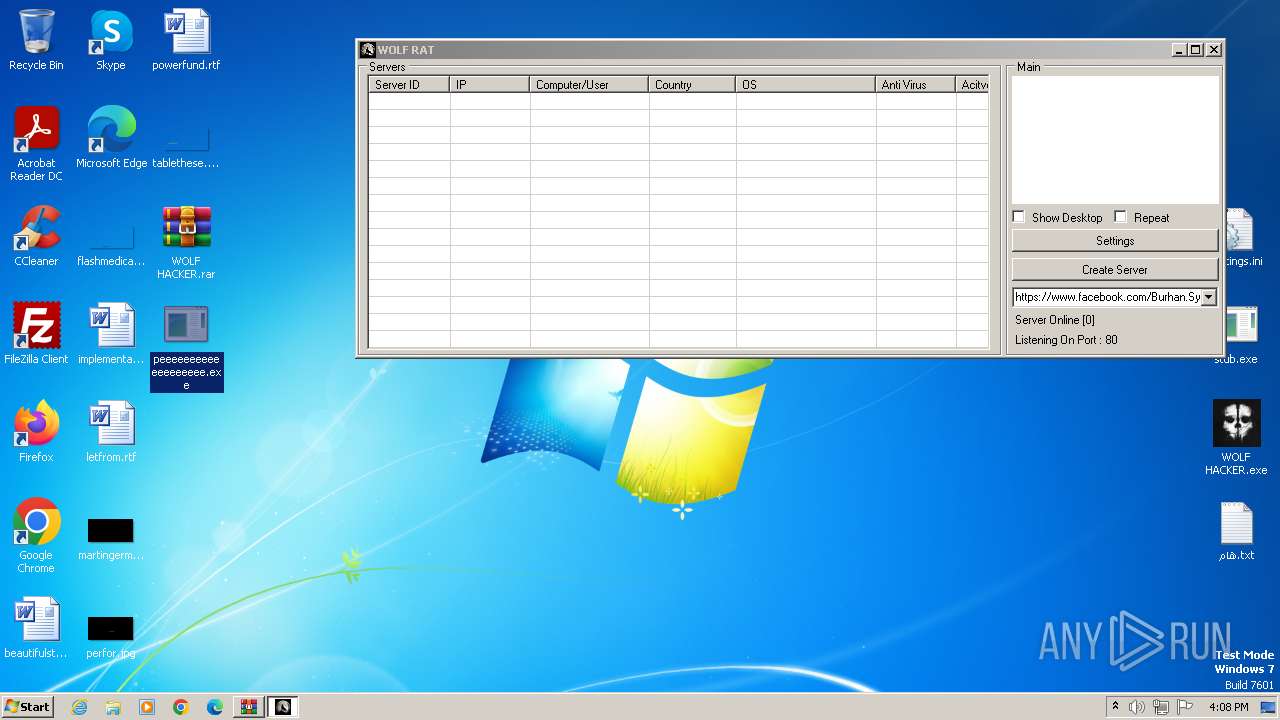
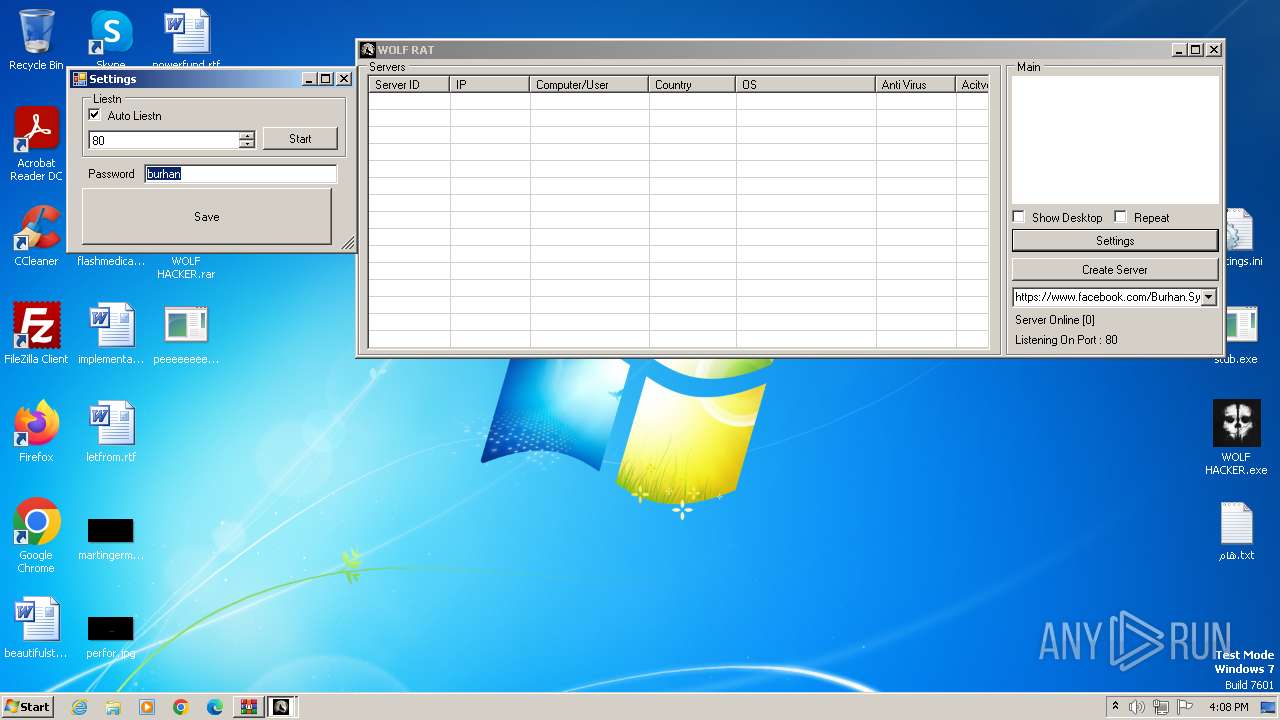
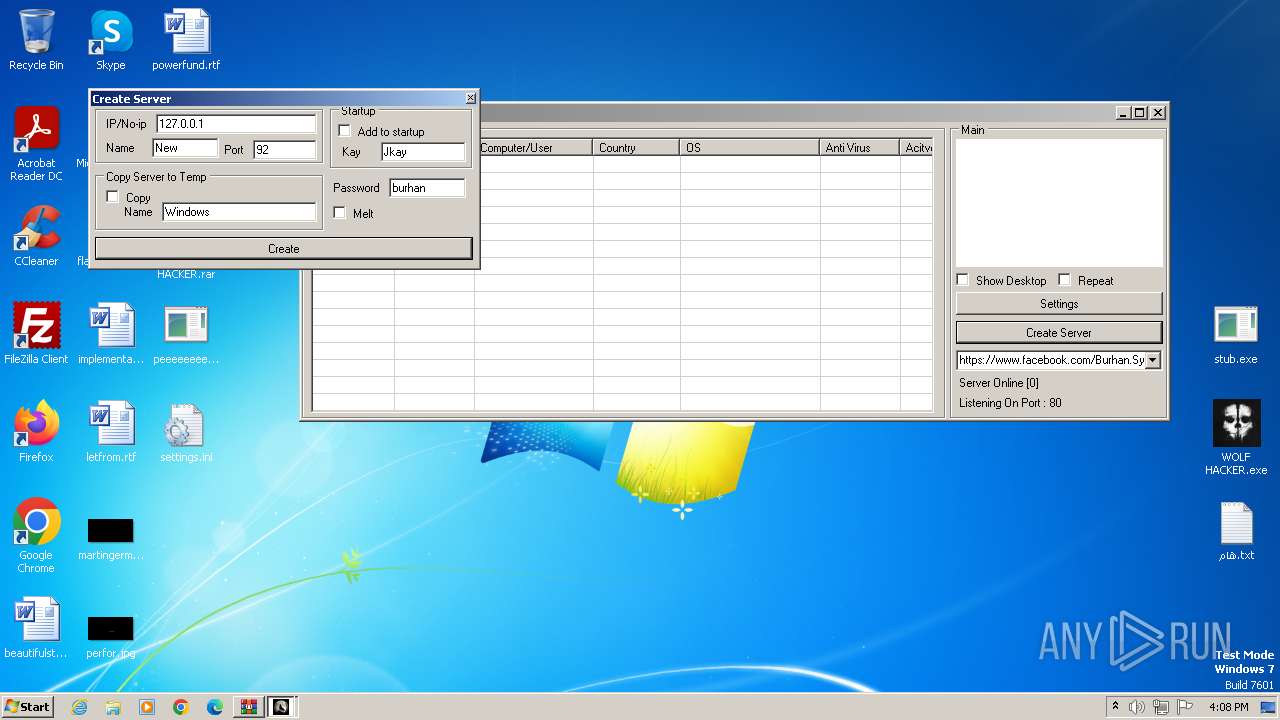
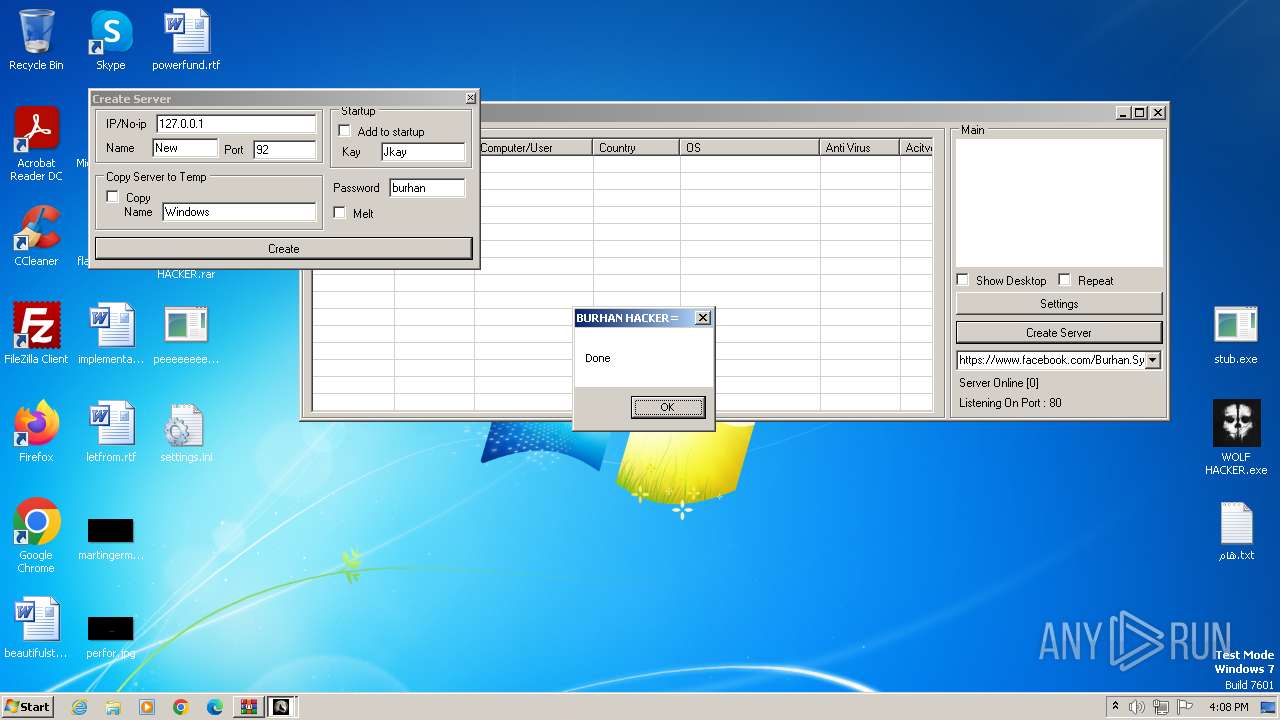
| 3488 | "C:\Users\admin\Desktop\WOLF HACKER.exe" | C:\Users\admin\Desktop\WOLF HACKER.exe | explorer.exe | ||||||||||||
User: admin Company: BURHAN HACKER Integrity Level: MEDIUM Description: WOLF RAT Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
13 620
Read events
13 487
Write events
123
Delete events
10
Modification events
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\WOLF HACKER.rar | |||
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2472) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
4
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
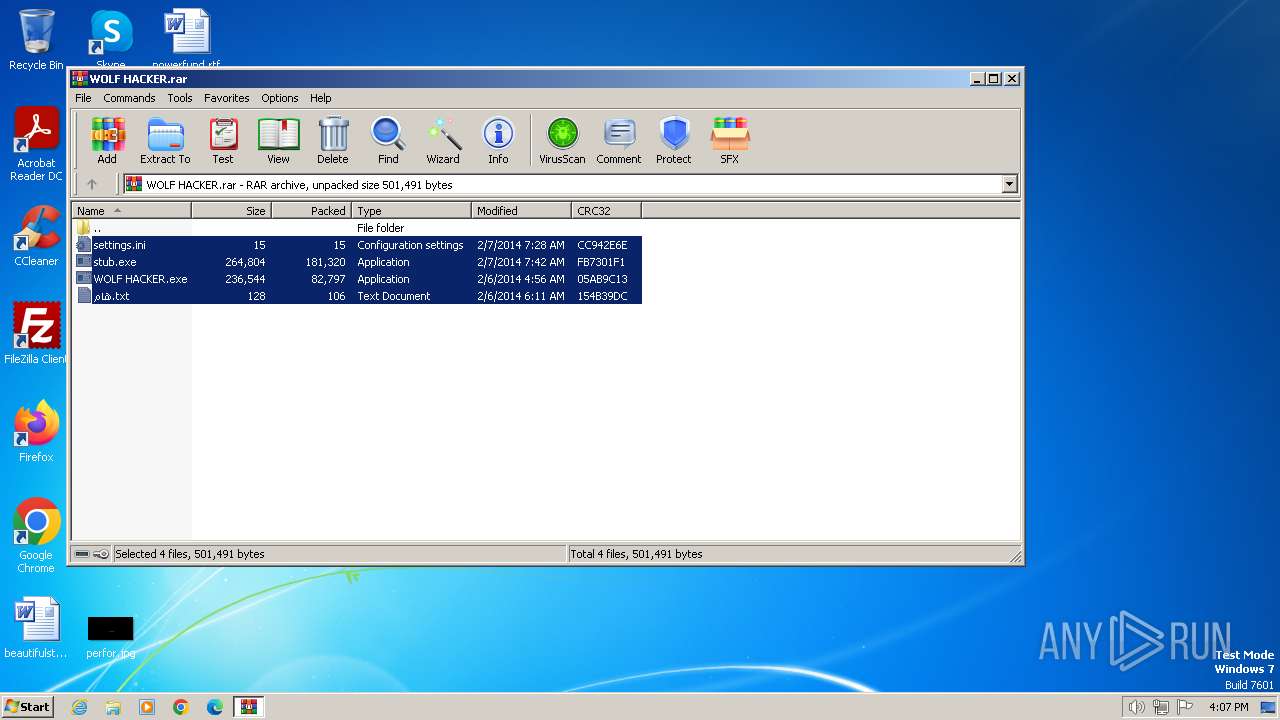
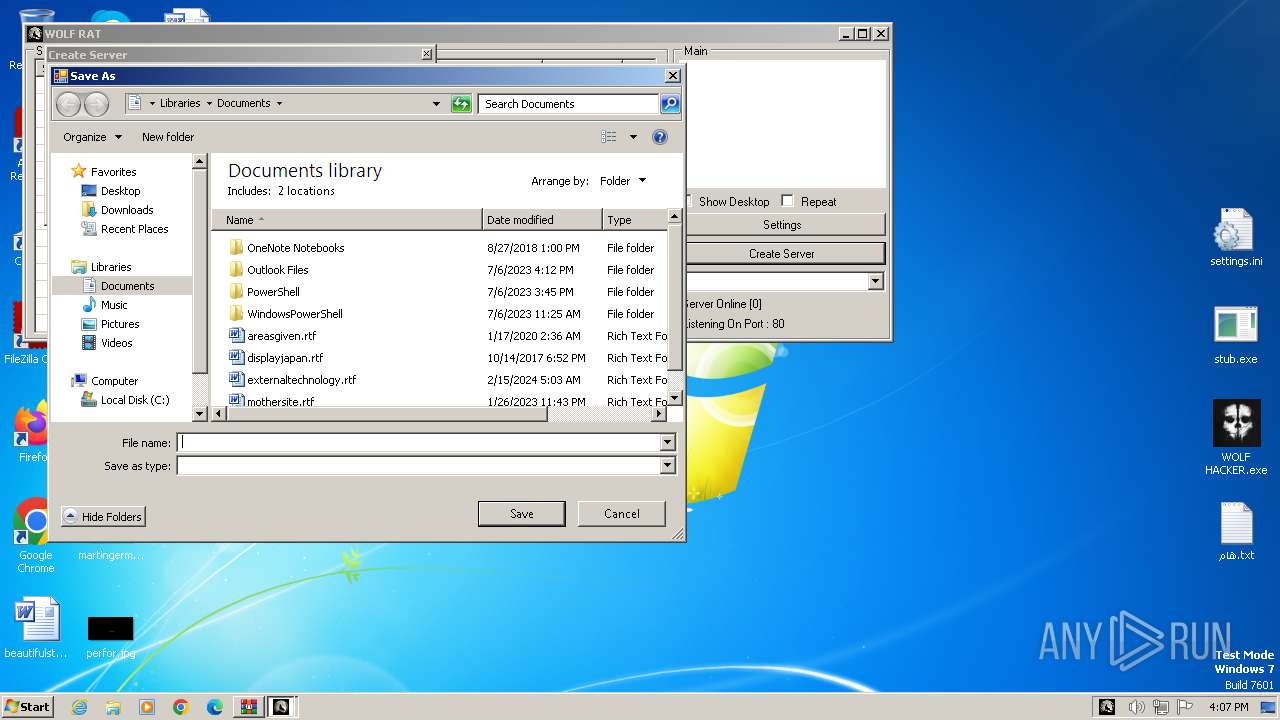
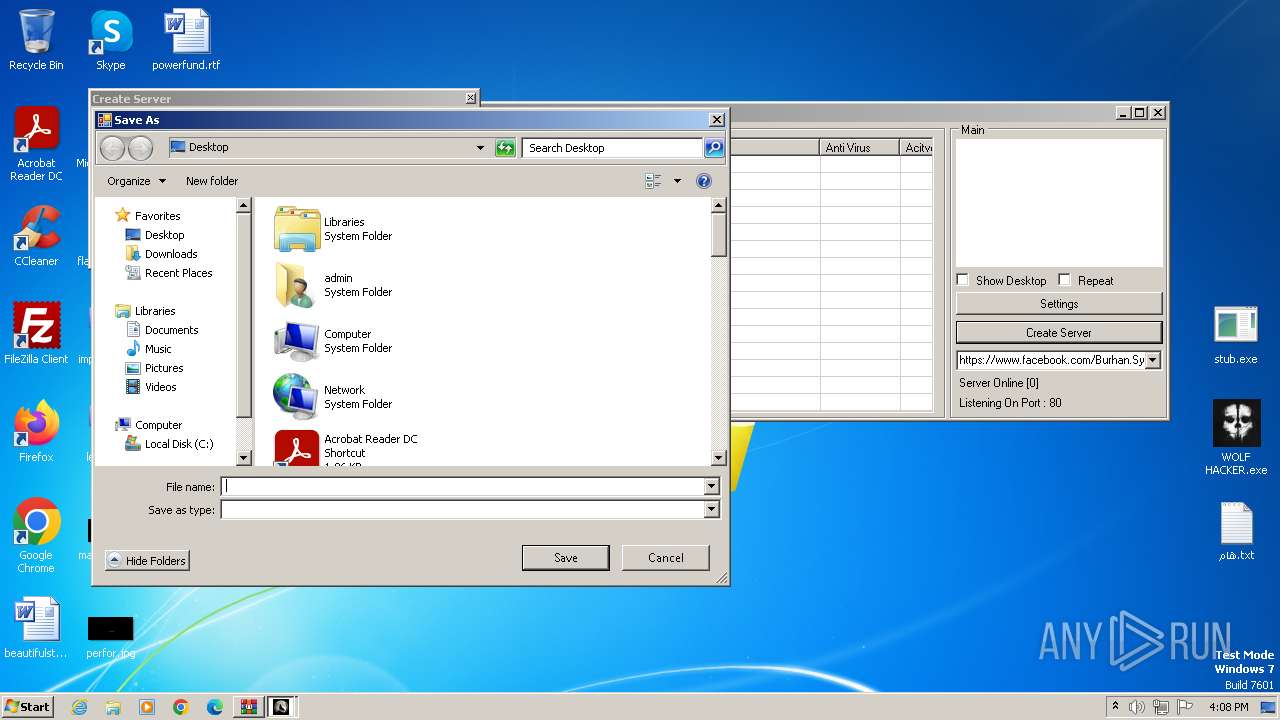
| 2472 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2472.45115\stub.exe | executable | |
MD5:F933C210108EC2ECB25406521FC1FD68 | SHA256:329DC056CE4392DF426071D74AE498CFD83929D9118E2A40D45496A6D097B487 | |||
| 2472 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2472.45115\هام.txt | text | |
MD5:8D4197D734AAEFC3DE739A23947954A0 | SHA256:8D30CFDE3B15F68204DB69B4C8BAA2FD144AB303E7E3EB1D7383DF1CAAFFC6DD | |||
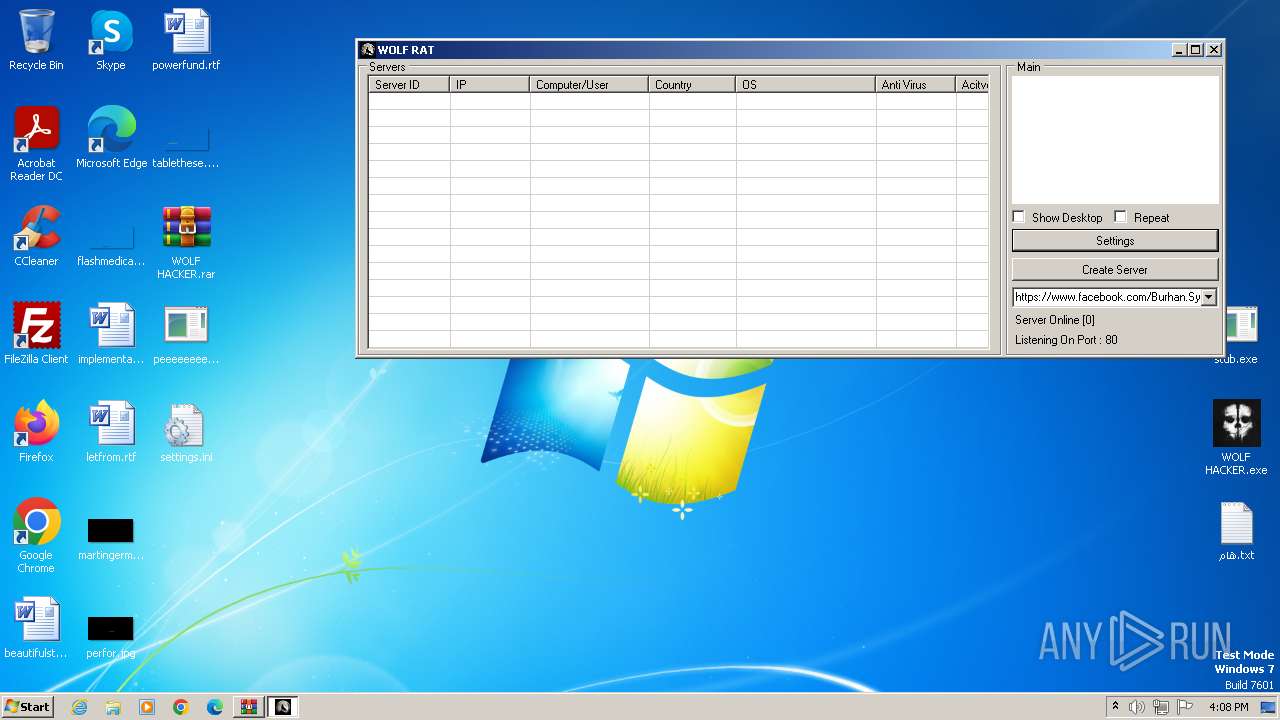
| 3488 | WOLF HACKER.exe | C:\Users\admin\Desktop\settings.ini | text | |
MD5:D04E6E9018AE651E1323967F2AF9AC05 | SHA256:438764F67078574C7641AF9FB0B362BC2CF4BDCAE3F4E34FAED87966DA453DAC | |||
| 2472 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2472.45115\WOLF HACKER.exe | executable | |
MD5:617E511C9B9EBB86FD23161D12D5EC69 | SHA256:ED0E98F1698BE21F2FDFA361337B1CF1CA18177A9004860425A853DB204FE111 | |||
| 3488 | WOLF HACKER.exe | C:\Users\admin\Desktop\dgjj.exe | executable | |
MD5:68E0A33328986DCABFF450ECFD886A64 | SHA256:C3117673AD9582534D502F02D3CE2B76740F2E8A08AADDE5E0CB3A4FC7224F68 | |||
| 3488 | WOLF HACKER.exe | C:\Users\admin\Desktop\peeeeeeeeeeeeeeeeeee.exe | executable | |
MD5:B403F9EA568C1E8E356642BAD4F6B50B | SHA256:111400D45DB15AACA9E9FD49AA8B4FD0A4DC7E61B130CB17C85531822EC41A8B | |||
| 2472 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2472.45115\settings.ini | text | |
MD5:D04E6E9018AE651E1323967F2AF9AC05 | SHA256:438764F67078574C7641AF9FB0B362BC2CF4BDCAE3F4E34FAED87966DA453DAC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
12
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 23.50.131.216:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | whitelisted |
1060 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8f69642324cc87bd | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 23.48.23.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 239.255.255.250:3702 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
1372 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1372 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1372 | svchost.exe | 23.50.131.216:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 23.48.23.138:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.gulfup.com |
| unknown |