| File name: | 3941c59fae1fdb75f1abd2d527e496e32a5601330b5b3a05da1c81a40454761e |
| Full analysis: | https://app.any.run/tasks/6f8134e7-0650-4721-8725-2c5d7ee7ff03 |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2025, 22:30:56 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 05E67AB66A493266F2B72F6C99AEF290 |
| SHA1: | D0F8A4C19A44B845E2666ABA5FE540D24343069A |
| SHA256: | 3941C59FAE1FDB75F1ABD2D527E496E32A5601330B5B3A05DA1C81A40454761E |
| SSDEEP: | 24576:nWo/GQUCC1Qrk/LICnLlgu0yBszURztR:nWo/GQUCCark/LICnLlgu0yBsARztR |
MALICIOUS
PYKSPA mutex has been found
- hajwhnbjdnd.exe (PID: 4136)
- zbmqv.exe (PID: 4244)
- zbmqv.exe (PID: 4764)
- hajwhnbjdnd.exe (PID: 5868)
- zbmqv.exe (PID: 6032)
- hajwhnbjdnd.exe (PID: 5964)
- zbmqv.exe (PID: 6024)
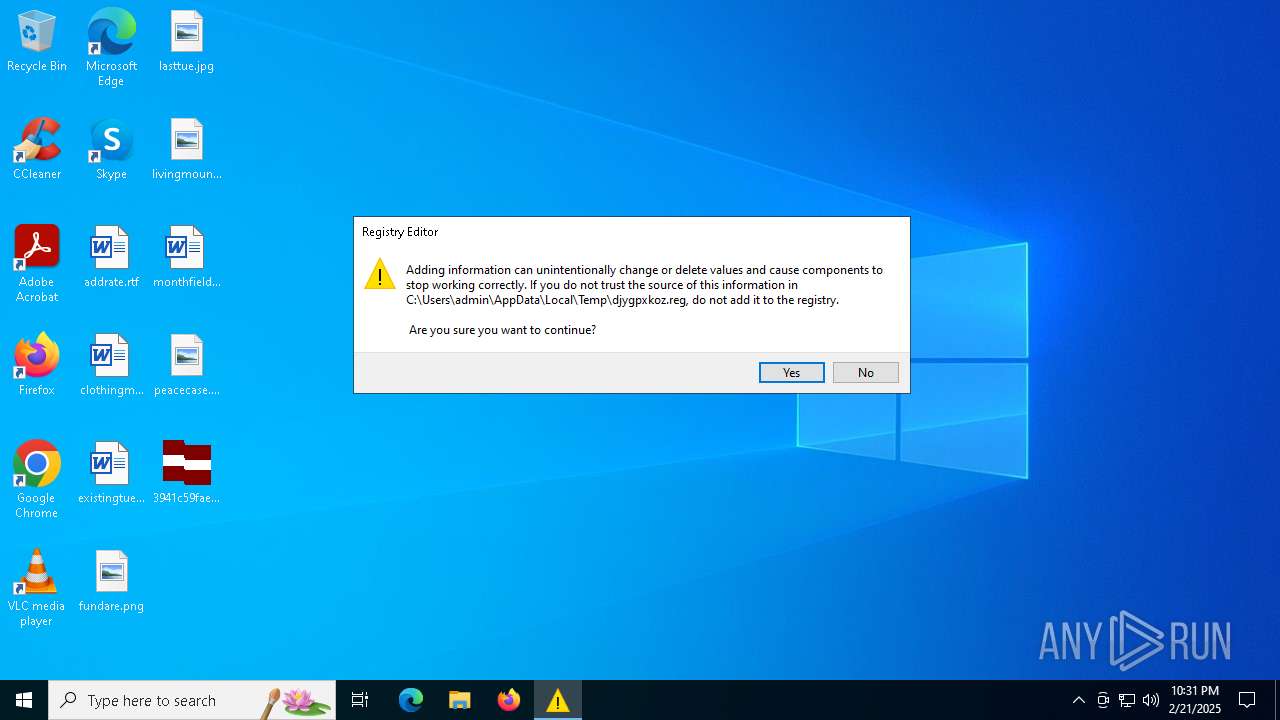
UAC/LUA settings modification
- hajwhnbjdnd.exe (PID: 4136)
- zbmqv.exe (PID: 4764)
- zbmqv.exe (PID: 4244)
- regedit.exe (PID: 3700)
- hajwhnbjdnd.exe (PID: 5868)
- zbmqv.exe (PID: 6032)
- zbmqv.exe (PID: 6024)
Changes the autorun value in the registry
- hajwhnbjdnd.exe (PID: 4136)
- zbmqv.exe (PID: 4764)
- zbmqv.exe (PID: 4244)
- hajwhnbjdnd.exe (PID: 5868)
- zbmqv.exe (PID: 6024)
- zbmqv.exe (PID: 6032)
Changes appearance of the Explorer extensions
- zbmqv.exe (PID: 4764)
- hajwhnbjdnd.exe (PID: 4136)
- zbmqv.exe (PID: 4244)
- hajwhnbjdnd.exe (PID: 5868)
- zbmqv.exe (PID: 6024)
- zbmqv.exe (PID: 6032)
Modify registry editing tools (regedit)
- zbmqv.exe (PID: 6032)
- zbmqv.exe (PID: 6024)
PYKSPA has been detected (SURICATA)
- zbmqv.exe (PID: 6032)
SUSPICIOUS
Reads security settings of Internet Explorer
- 3941c59fae1fdb75f1abd2d527e496e32a5601330b5b3a05da1c81a40454761e.exe (PID: 2928)
- hajwhnbjdnd.exe (PID: 4136)
- zbmqv.exe (PID: 4764)
- ShellExperienceHost.exe (PID: 1804)
- xnmexpmavcdupiwsikc.exe (PID: 5900)
- mbzqizviciiyskxshi.exe (PID: 5824)
- hajwhnbjdnd.exe (PID: 5868)
Executable content was dropped or overwritten
- 3941c59fae1fdb75f1abd2d527e496e32a5601330b5b3a05da1c81a40454761e.exe (PID: 2928)
- hajwhnbjdnd.exe (PID: 4136)
- hajwhnbjdnd.exe (PID: 5868)
- zbmqv.exe (PID: 6032)
Detected use of alternative data streams (AltDS)
- svchost.exe (PID: 2260)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 1120)
Searches for installed software
- svchost.exe (PID: 5192)
Checks for external IP
- zbmqv.exe (PID: 6032)
- svchost.exe (PID: 2188)
Potential Corporate Privacy Violation
- zbmqv.exe (PID: 6032)
Connects to unusual port
- zbmqv.exe (PID: 6032)
Suspicious files were dropped or overwritten
- zbmqv.exe (PID: 6032)
Creates file in the systems drive root
- zbmqv.exe (PID: 6032)
INFO
Create files in a temporary directory
- 3941c59fae1fdb75f1abd2d527e496e32a5601330b5b3a05da1c81a40454761e.exe (PID: 2928)
- hajwhnbjdnd.exe (PID: 4136)
- zbmqv.exe (PID: 4764)
- zbmqv.exe (PID: 6032)
Checks supported languages
- 3941c59fae1fdb75f1abd2d527e496e32a5601330b5b3a05da1c81a40454761e.exe (PID: 2928)
- hajwhnbjdnd.exe (PID: 4136)
- zbmqv.exe (PID: 4764)
- zbmqv.exe (PID: 4244)
- ShellExperienceHost.exe (PID: 1804)
- OfficeClickToRun.exe (PID: 2936)
- PLUGScheduler.exe (PID: 1120)
- mbzqizviciiyskxshi.exe (PID: 5824)
- zbmqv.exe (PID: 6024)
- zbmqv.exe (PID: 6032)
- hajwhnbjdnd.exe (PID: 5868)
- hajwhnbjdnd.exe (PID: 5964)
- xnmexpmavcdupiwsikc.exe (PID: 5900)
Process checks whether UAC notifications are on
- hajwhnbjdnd.exe (PID: 4136)
- zbmqv.exe (PID: 4764)
- zbmqv.exe (PID: 4244)
- hajwhnbjdnd.exe (PID: 5868)
- zbmqv.exe (PID: 6032)
- zbmqv.exe (PID: 6024)
Reads the computer name
- 3941c59fae1fdb75f1abd2d527e496e32a5601330b5b3a05da1c81a40454761e.exe (PID: 2928)
- hajwhnbjdnd.exe (PID: 4136)
- zbmqv.exe (PID: 4764)
- zbmqv.exe (PID: 4244)
- ShellExperienceHost.exe (PID: 1804)
- OfficeClickToRun.exe (PID: 2936)
- mbzqizviciiyskxshi.exe (PID: 5824)
- PLUGScheduler.exe (PID: 1120)
- hajwhnbjdnd.exe (PID: 5868)
- xnmexpmavcdupiwsikc.exe (PID: 5900)
- zbmqv.exe (PID: 6032)
- hajwhnbjdnd.exe (PID: 5964)
- zbmqv.exe (PID: 6024)
Process checks computer location settings
- 3941c59fae1fdb75f1abd2d527e496e32a5601330b5b3a05da1c81a40454761e.exe (PID: 2928)
- hajwhnbjdnd.exe (PID: 4136)
- zbmqv.exe (PID: 4764)
- mbzqizviciiyskxshi.exe (PID: 5824)
- hajwhnbjdnd.exe (PID: 5868)
- xnmexpmavcdupiwsikc.exe (PID: 5900)
Creates files or folders in the user directory
- zbmqv.exe (PID: 4764)
- zbmqv.exe (PID: 6032)
Manual execution by a user
- svchost.exe (PID: 2580)
- svchost.exe (PID: 2524)
- svchost.exe (PID: 2532)
- svchost.exe (PID: 2556)
- spoolsv.exe (PID: 2564)
- svchost.exe (PID: 2684)
- svchost.exe (PID: 2852)
- svchost.exe (PID: 2956)
- svchost.exe (PID: 2964)
- svchost.exe (PID: 2996)
- OfficeClickToRun.exe (PID: 2936)
- svchost.exe (PID: 2116)
- svchost.exe (PID: 2408)
- svchost.exe (PID: 2644)
- svchost.exe (PID: 2692)
- svchost.exe (PID: 3272)
- svchost.exe (PID: 3700)
- svchost.exe (PID: 3724)
- svchost.exe (PID: 3828)
- svchost.exe (PID: 3884)
- svchost.exe (PID: 2260)
- svchost.exe (PID: 2348)
- svchost.exe (PID: 4200)
- svchost.exe (PID: 2924)
- svchost.exe (PID: 3044)
- svchost.exe (PID: 4420)
- svchost.exe (PID: 4720)
- svchost.exe (PID: 4548)
- mbzqizviciiyskxshi.exe (PID: 5824)
- svchost.exe (PID: 4088)
- svchost.exe (PID: 3112)
- xnmexpmavcdupiwsikc.exe (PID: 5900)
- svchost.exe (PID: 6104)
- svchost.exe (PID: 5192)
- svchost.exe (PID: 5988)
- svchost.exe (PID: 2536)
- svchost.exe (PID: 872)
Reads the time zone
- svchost.exe (PID: 2556)
- svchost.exe (PID: 2964)
- svchost.exe (PID: 5988)
Disables trace logs
- svchost.exe (PID: 3272)
Reads the machine GUID from the registry
- OfficeClickToRun.exe (PID: 2936)
Reads Microsoft Office registry keys
- OfficeClickToRun.exe (PID: 2936)
Reads security settings of Internet Explorer
- svchost.exe (PID: 2556)
- svchost.exe (PID: 4088)
- svchost.exe (PID: 3112)
- svchost.exe (PID: 3044)
Checks proxy server information
- OfficeClickToRun.exe (PID: 2936)
- svchost.exe (PID: 4088)
Reads the software policy settings
- OfficeClickToRun.exe (PID: 2936)
Creates files in the program directory
- PLUGScheduler.exe (PID: 1120)
- zbmqv.exe (PID: 6032)
- svchost.exe (PID: 5988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2008:12:30 15:40:22+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 28672 |
| InitializedDataSize: | 1007616 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x41d2 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
249
Monitored processes
52
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 776 | "regedit.exe" "C:\Users\admin\AppData\Local\Temp\djygpxkoz.reg" | C:\Windows\SysWOW64\regedit.exe | — | zbmqv.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | C:\WINDOWS\system32\svchost.exe -k wusvcs -p -s WaaSMedicSvc | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1120 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1804 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2116 | C:\WINDOWS\system32\svchost.exe -k LocalService -p -s SstpSvc | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2188 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2260 | C:\WINDOWS\System32\svchost.exe -k LocalSystemNetworkRestricted -p -s TrkWks | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2348 | C:\WINDOWS\system32\svchost.exe -k netsvcs -p -s WpnService | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2408 | C:\WINDOWS\system32\svchost.exe -k netsvcs -p -s LanmanServer | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2524 | C:\WINDOWS\System32\svchost.exe -k NetworkService -p -s DoSvc | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
58 449
Read events
57 700
Write events
662
Delete events
87
Modification events
| (PID) Process: | (4136) hajwhnbjdnd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wjfukztewaymeufy |
Value: droevlgslqpexoaui.exe . | |||
| (PID) Process: | (4136) hajwhnbjdnd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (4136) hajwhnbjdnd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | oxpamxnuiicm |
Value: zrsmhbaqnwzspkayquooa.exe | |||
| (PID) Process: | (4136) hajwhnbjdnd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | nxqcpbsapqlwl |
Value: droevlgslqpexoaui.exe . | |||
| (PID) Process: | (4136) hajwhnbjdnd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | rdymbpisjmjwncm |
Value: wjfukztewaymeufy.exe | |||
| (PID) Process: | (4136) hajwhnbjdnd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | droevlgslqpexoaui |
Value: C:\Users\admin\AppData\Local\Temp\xnmexpmavcdupiwsikc.exe . | |||
| (PID) Process: | (4136) hajwhnbjdnd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | oxpamxnuiicm |
Value: C:\Users\admin\AppData\Local\Temp\mbzqizviciiyskxshi.exe | |||
| (PID) Process: | (4136) hajwhnbjdnd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | nxqcpbsapqlwl |
Value: C:\Users\admin\AppData\Local\Temp\mbzqizviciiyskxshi.exe . | |||
| (PID) Process: | (4136) hajwhnbjdnd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | mbzqizviciiyskxshi |
Value: C:\Users\admin\AppData\Local\Temp\zrsmhbaqnwzspkayquooa.exe | |||
| (PID) Process: | (4136) hajwhnbjdnd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorUser |
Value: 0 | |||
Executable files
34
Suspicious files
64
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | svchost.exe | C:\Windows\System32\sru\SRUDB.dat | — | |
MD5:— | SHA256:— | |||
| 2928 | 3941c59fae1fdb75f1abd2d527e496e32a5601330b5b3a05da1c81a40454761e.exe | C:\Users\admin\AppData\Local\Temp\hajwhnbjdnd.exe | executable | |
MD5:21AB312957B808003AA631A1E8392B4C | SHA256:74E29C21F9DF8B5D2CC262B214A89E0211B4803E495C0EB7B8762D5A4C72B33E | |||
| 4136 | hajwhnbjdnd.exe | C:\Users\admin\AppData\Local\Temp\wjfukztewaymeufy.exe | executable | |
MD5:05E67AB66A493266F2B72F6C99AEF290 | SHA256:3941C59FAE1FDB75F1ABD2D527E496E32A5601330B5B3A05DA1C81A40454761E | |||
| 4136 | hajwhnbjdnd.exe | C:\Users\admin\AppData\Local\Temp\droevlgslqpexoaui.exe | executable | |
MD5:05E67AB66A493266F2B72F6C99AEF290 | SHA256:3941C59FAE1FDB75F1ABD2D527E496E32A5601330B5B3A05DA1C81A40454761E | |||
| 4136 | hajwhnbjdnd.exe | C:\Users\admin\AppData\Local\Temp\xnmexpmavcdupiwsikc.exe | executable | |
MD5:05E67AB66A493266F2B72F6C99AEF290 | SHA256:3941C59FAE1FDB75F1ABD2D527E496E32A5601330B5B3A05DA1C81A40454761E | |||
| 4136 | hajwhnbjdnd.exe | C:\Users\admin\AppData\Local\Temp\zrsmhbaqnwzspkayquooa.exe | executable | |
MD5:05E67AB66A493266F2B72F6C99AEF290 | SHA256:3941C59FAE1FDB75F1ABD2D527E496E32A5601330B5B3A05DA1C81A40454761E | |||
| 4136 | hajwhnbjdnd.exe | C:\Users\admin\AppData\Local\Temp\qjlgcxxomwausofexcxylp.exe | executable | |
MD5:05E67AB66A493266F2B72F6C99AEF290 | SHA256:3941C59FAE1FDB75F1ABD2D527E496E32A5601330B5B3A05DA1C81A40454761E | |||
| 4764 | zbmqv.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\SysWOW64\edlmopvswmwwaczedopwpzno.zhi | binary | |
MD5:EB9D971DB7CE48DE04D41486D771E747 | SHA256:775B0076AB35EDFBB511AEA0B2EC8063F427FA7BD85AF1B013B81E6C9B9A7B61 | |||
| 4136 | hajwhnbjdnd.exe | C:\Users\admin\AppData\Local\Temp\mbzqizviciiyskxshi.exe | executable | |
MD5:05E67AB66A493266F2B72F6C99AEF290 | SHA256:3941C59FAE1FDB75F1ABD2D527E496E32A5601330B5B3A05DA1C81A40454761E | |||
| 4764 | zbmqv.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\edlmopvswmwwaczedopwpzno.zhi | binary | |
MD5:EB9D971DB7CE48DE04D41486D771E747 | SHA256:775B0076AB35EDFBB511AEA0B2EC8063F427FA7BD85AF1B013B81E6C9B9A7B61 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
51
DNS requests
1 108
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
244 | RUXIMICS.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1488 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
244 | RUXIMICS.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1488 | svchost.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.126.37.137:443 | https://www.bing.com/rp/-F7bYnjk9S0ADBYML9L8EdympNE.br.js | unknown | binary | 545 Kb | whitelisted |
— | — | GET | 200 | 104.126.37.178:443 | https://www.bing.com/rp/-iNIzuEypRdgRJ6xnyVHizZ3bpM.br.js | unknown | binary | 17.0 Kb | whitelisted |
— | — | GET | 200 | 104.126.37.130:443 | https://www.bing.com/rb/6j/ortl,cc,nc/QNBBNqWD9F_Blep-UqQSqnMp-FI.css?bu=AcEK&or=w | unknown | text | 6 b | whitelisted |
— | — | GET | 200 | 104.126.37.177:443 | https://www.bing.com/rp/-qTk-xd3hr6_MvhbKhSjoMFFRjQ.br.js | unknown | binary | 131 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
244 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1488 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
244 | RUXIMICS.exe | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1488 | svchost.exe | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
244 | RUXIMICS.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
1488 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.whatismyip.com |
| shared |
www.whatismyip.ca |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6032 | zbmqv.exe | Attempted Information Leak | ET INFO IP Check Domain (whatismyip in HTTP Host) |
6032 | zbmqv.exe | A Network Trojan was detected | ET MALWARE Win32/Pykspa.C Public IP Check |
6032 | zbmqv.exe | Potential Corporate Privacy Violation | ET INFO IP Check Domain (showmyipaddress .com in HTTP Host) |
6032 | zbmqv.exe | A Network Trojan was detected | ET MALWARE Win32/Pykspa.C Public IP Check |
2188 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (whatismyipaddress .com) |
6032 | zbmqv.exe | A Network Trojan was detected | ET MALWARE Win32/Pykspa.C Public IP Check |
6032 | zbmqv.exe | Potential Corporate Privacy Violation | ET INFO IP Check Domain (showmyipaddress .com in HTTP Host) |
6032 | zbmqv.exe | A Network Trojan was detected | ET MALWARE Win32/Pykspa.C Public IP Check |
6032 | zbmqv.exe | Attempted Information Leak | ET INFO IP Check Domain (whatismyip in HTTP Host) |
6032 | zbmqv.exe | A Network Trojan was detected | ET MALWARE Win32/Pykspa.C Public IP Check |