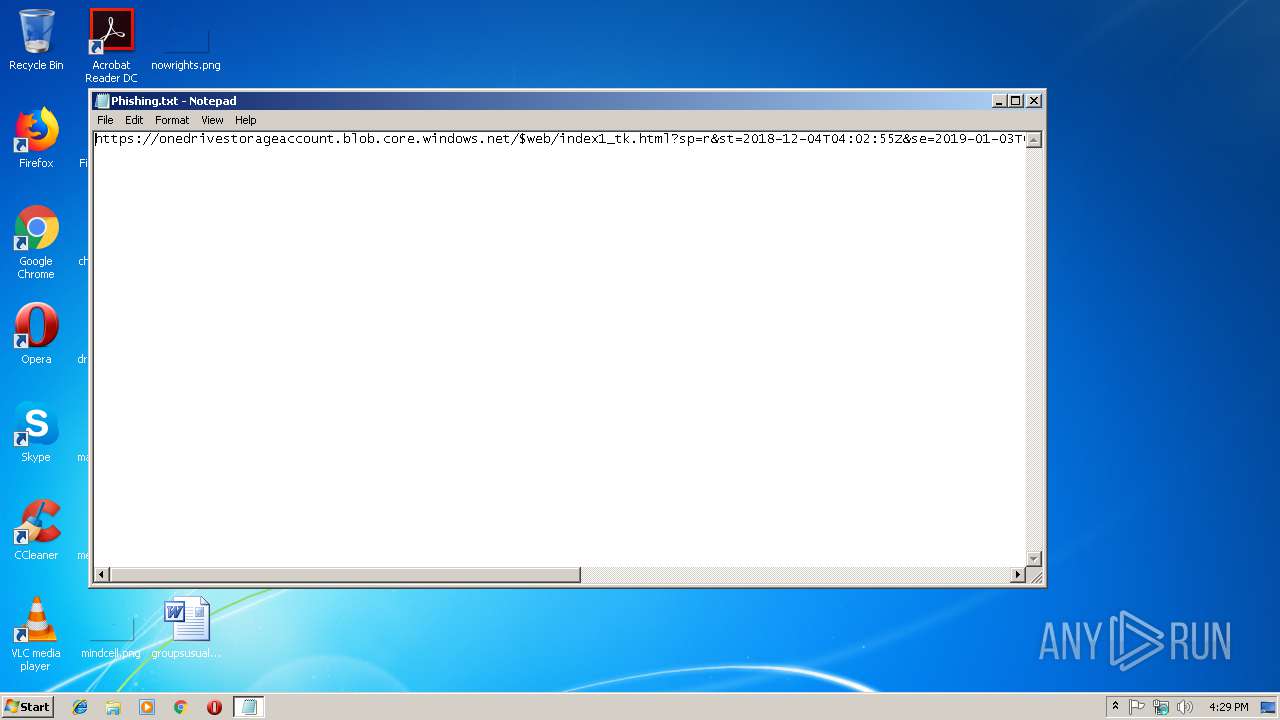
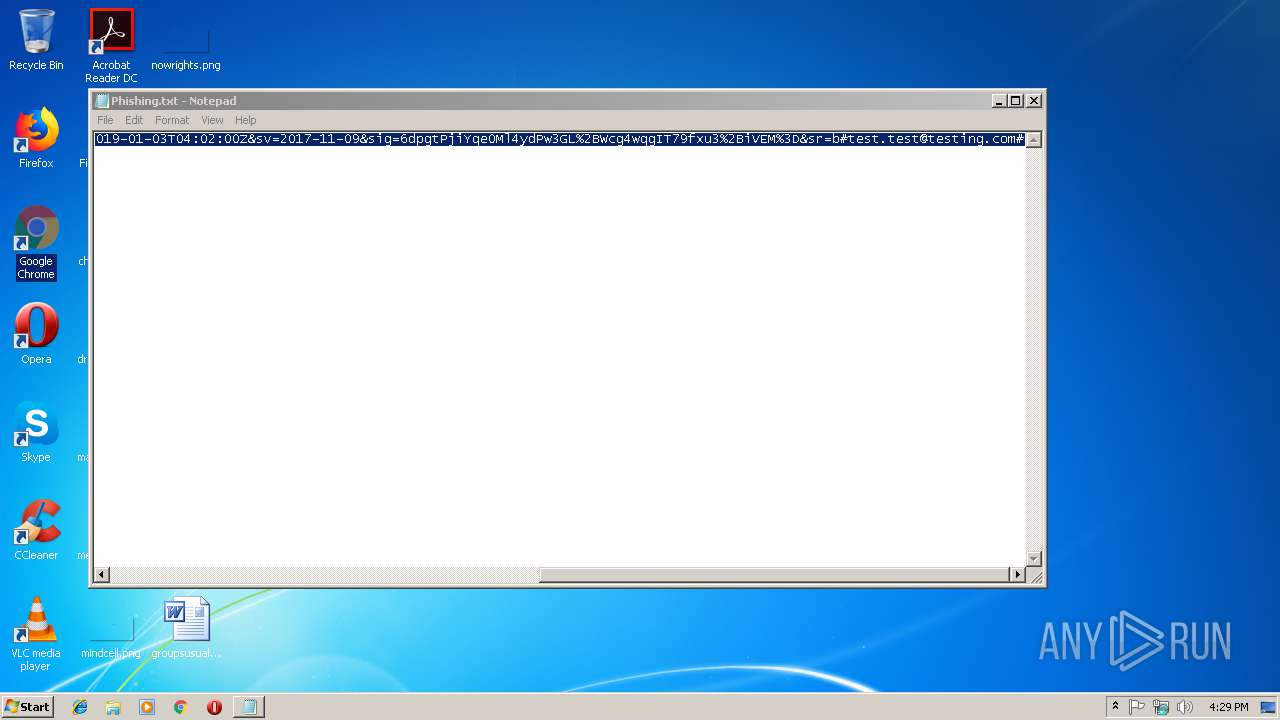
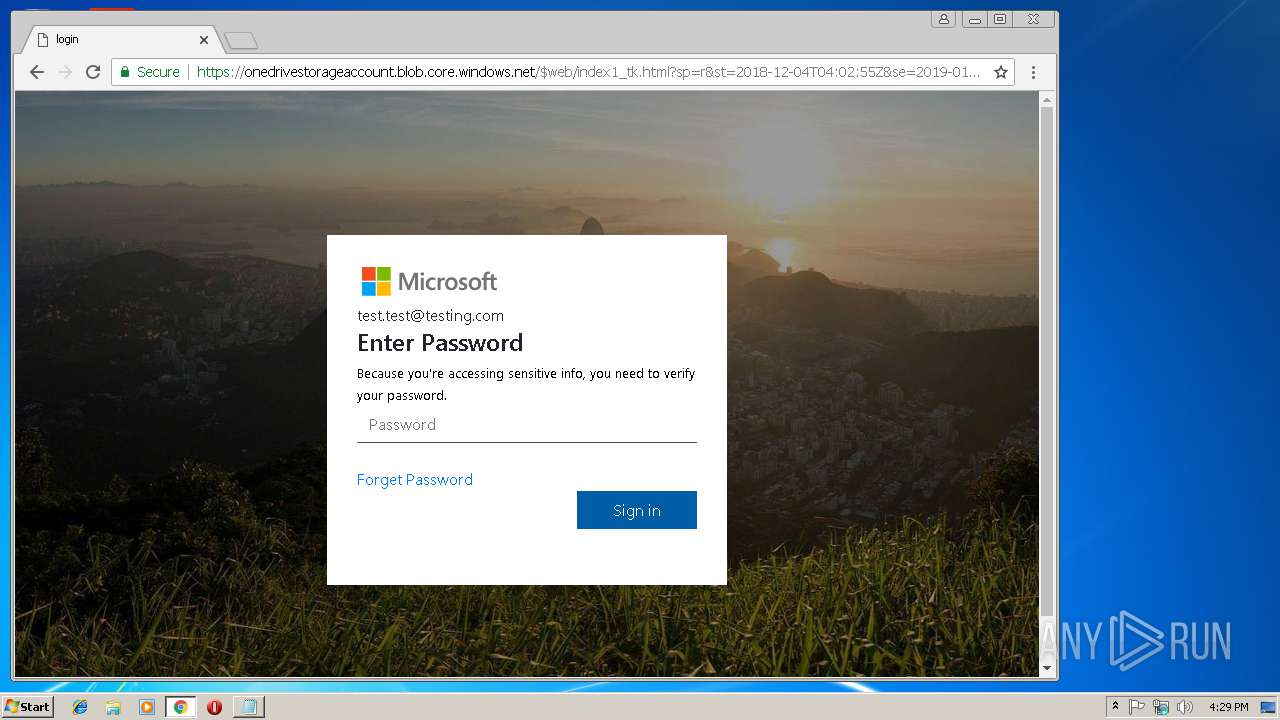
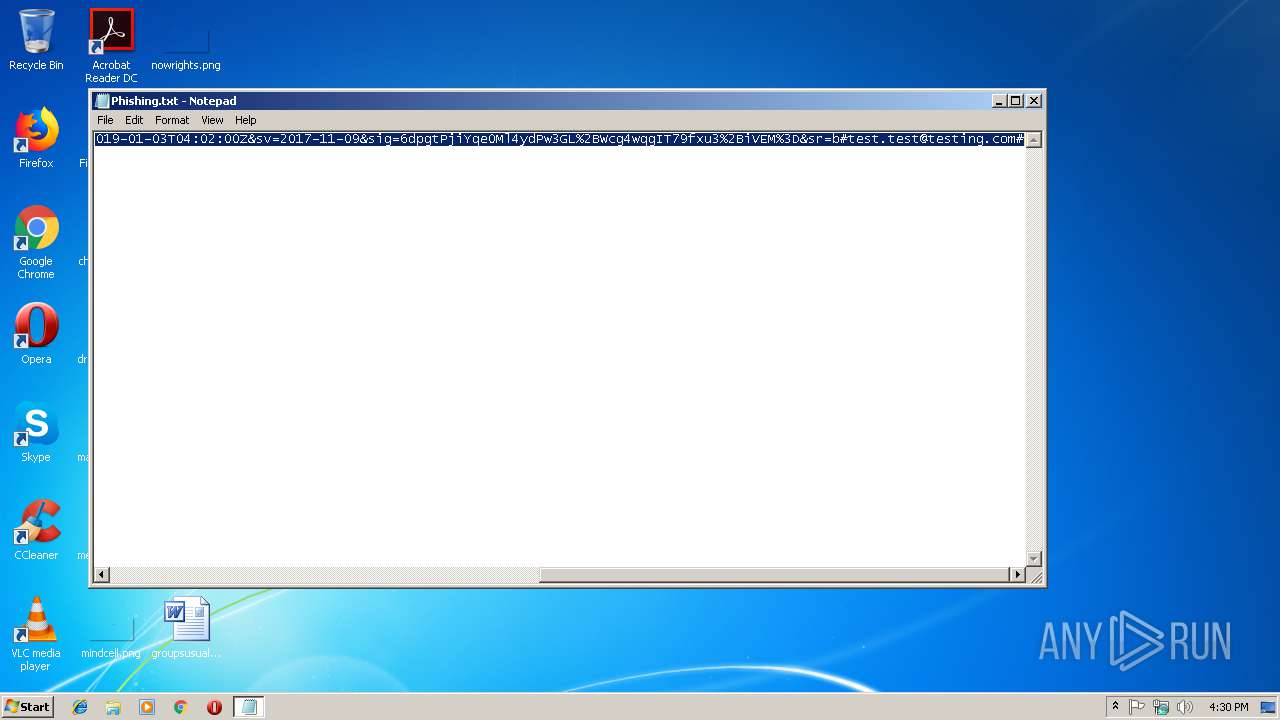
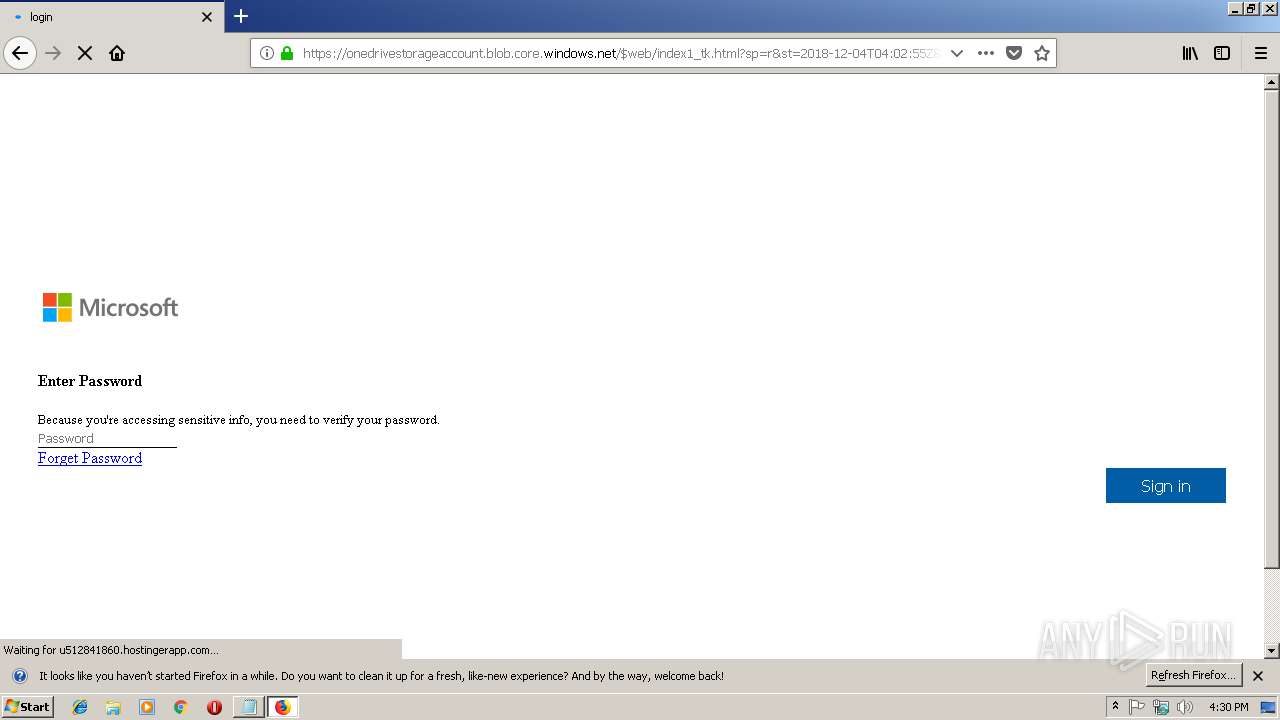
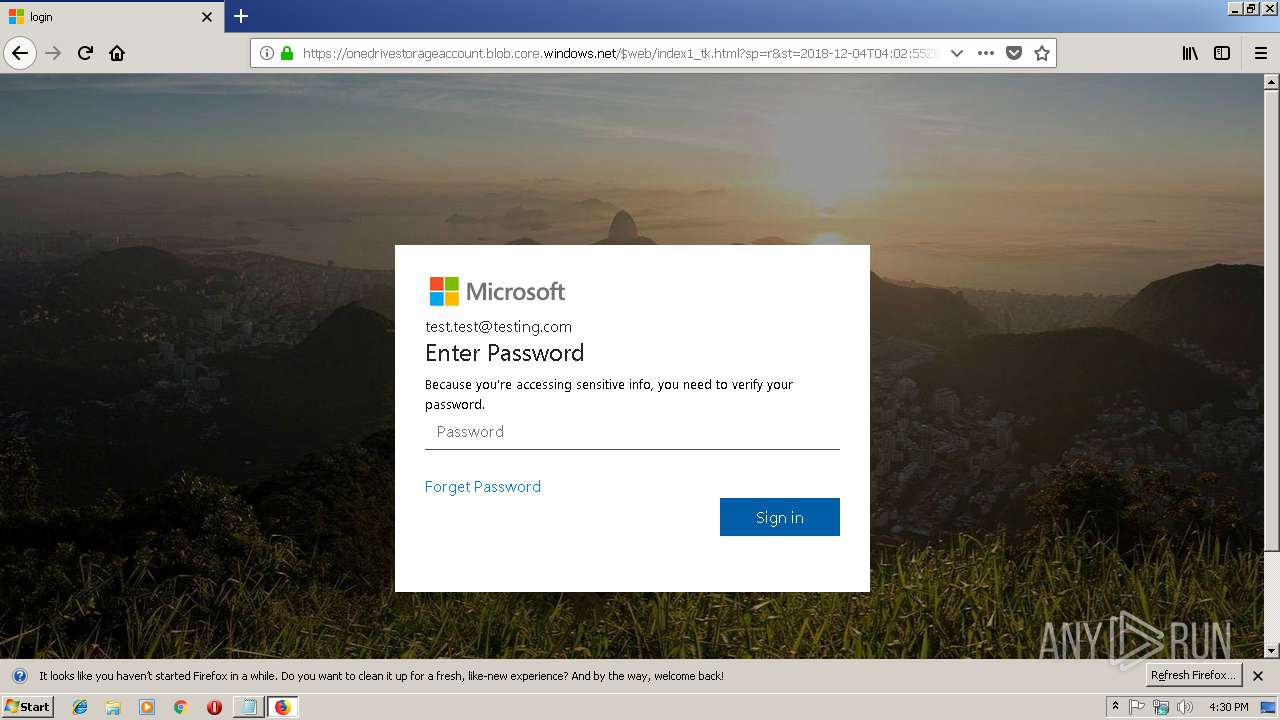
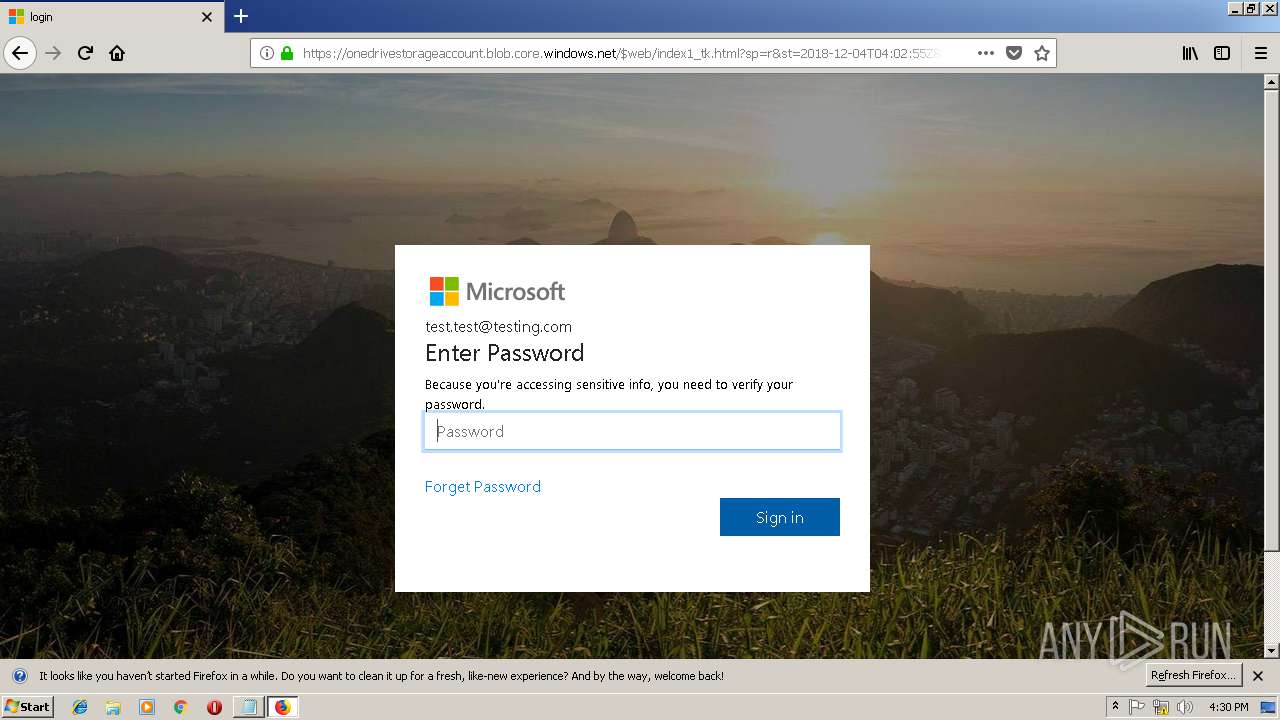
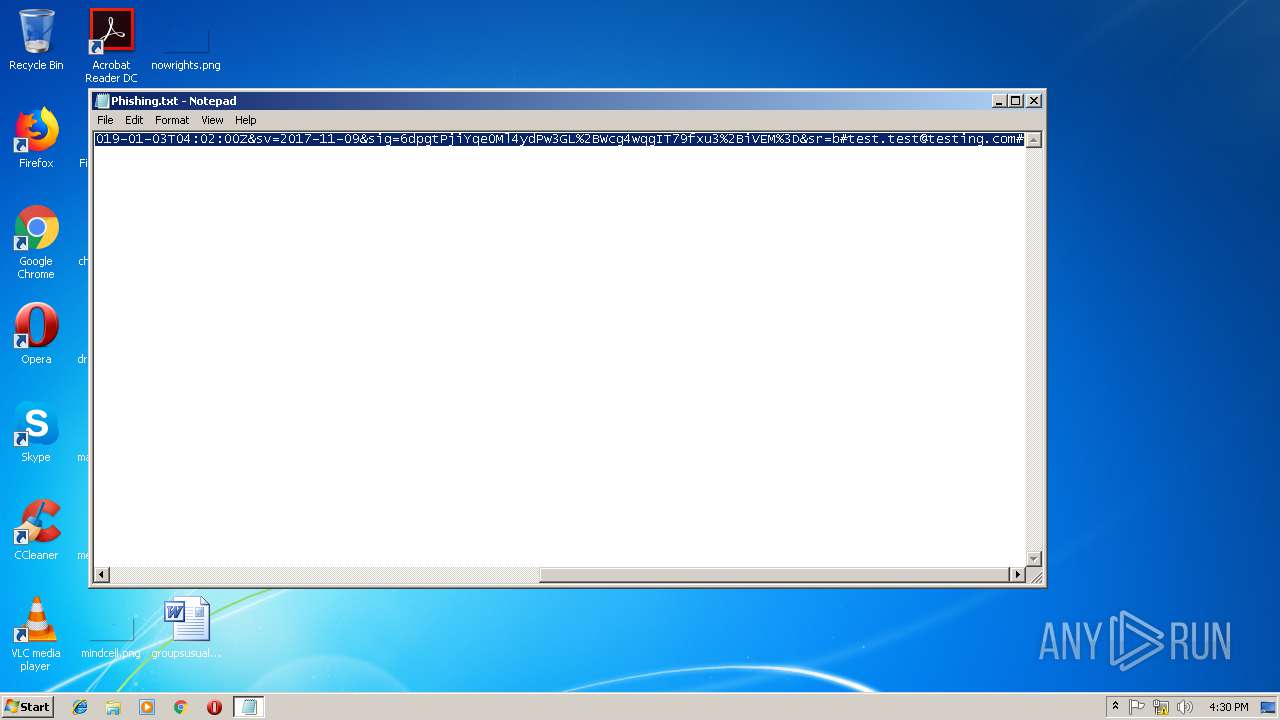
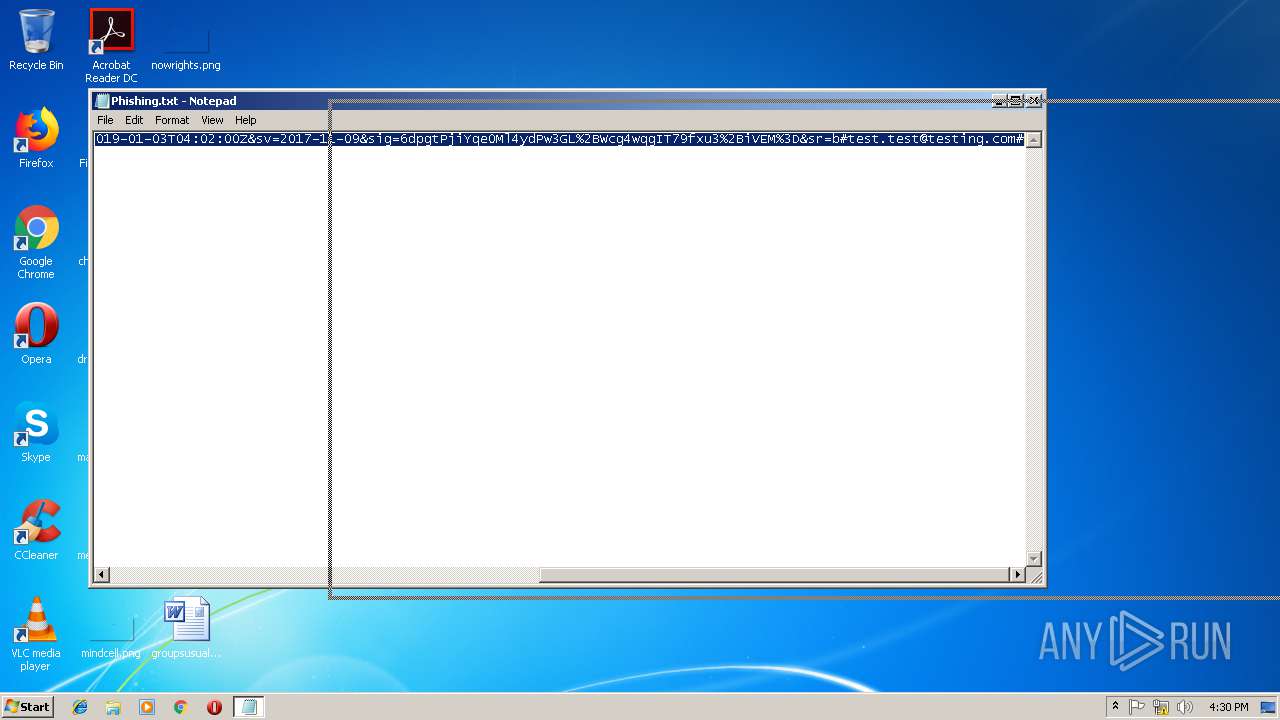
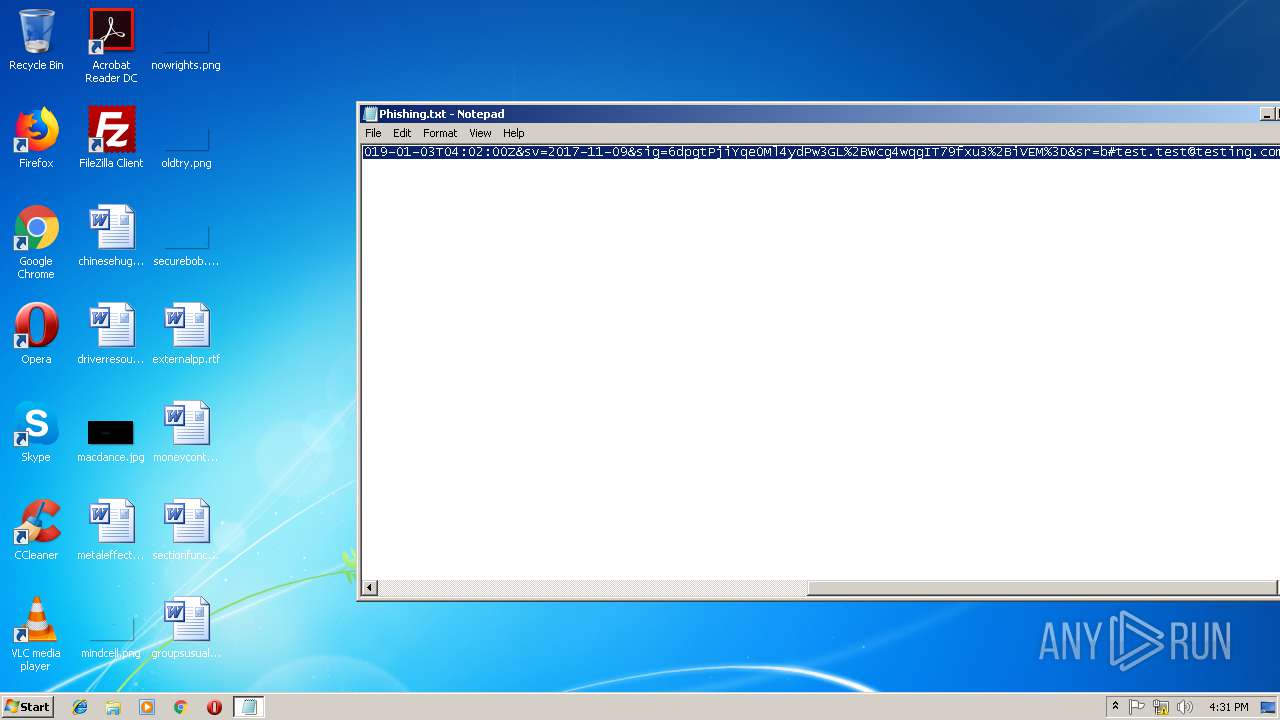
| File name: | Phishing.txt |
| Full analysis: | https://app.any.run/tasks/bcf90a82-20f6-4745-8b29-527939665ffe |
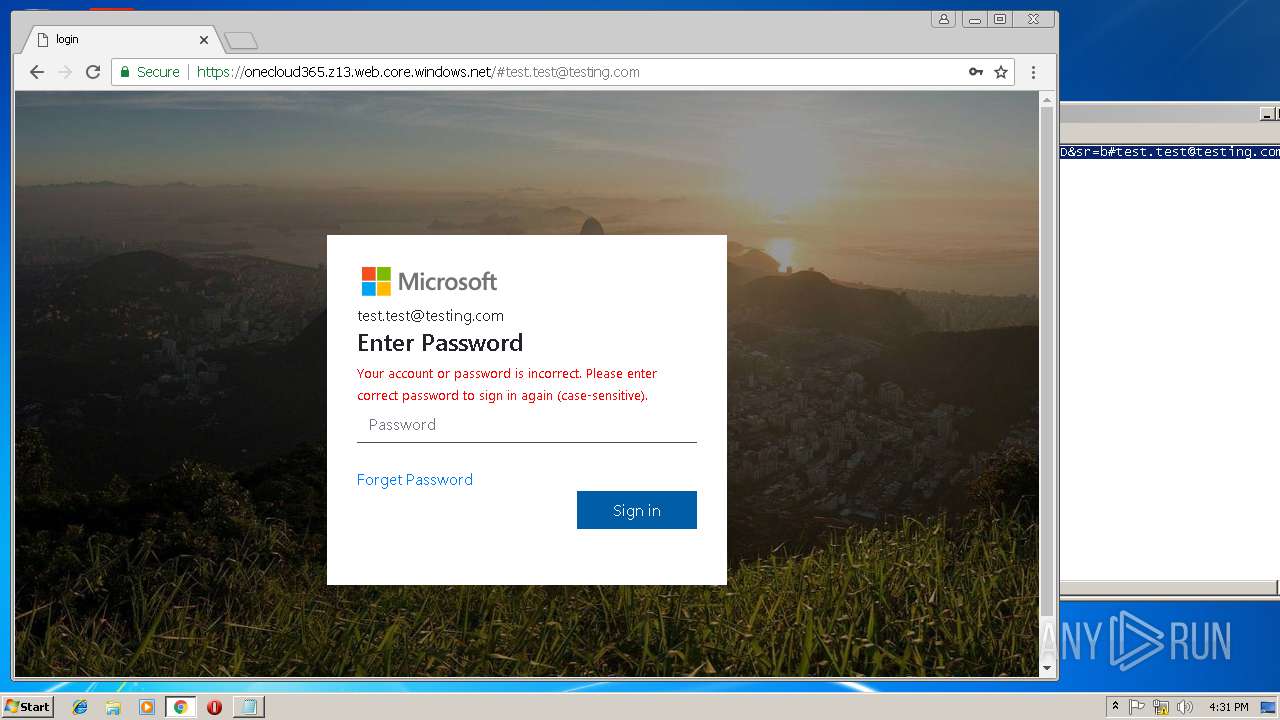
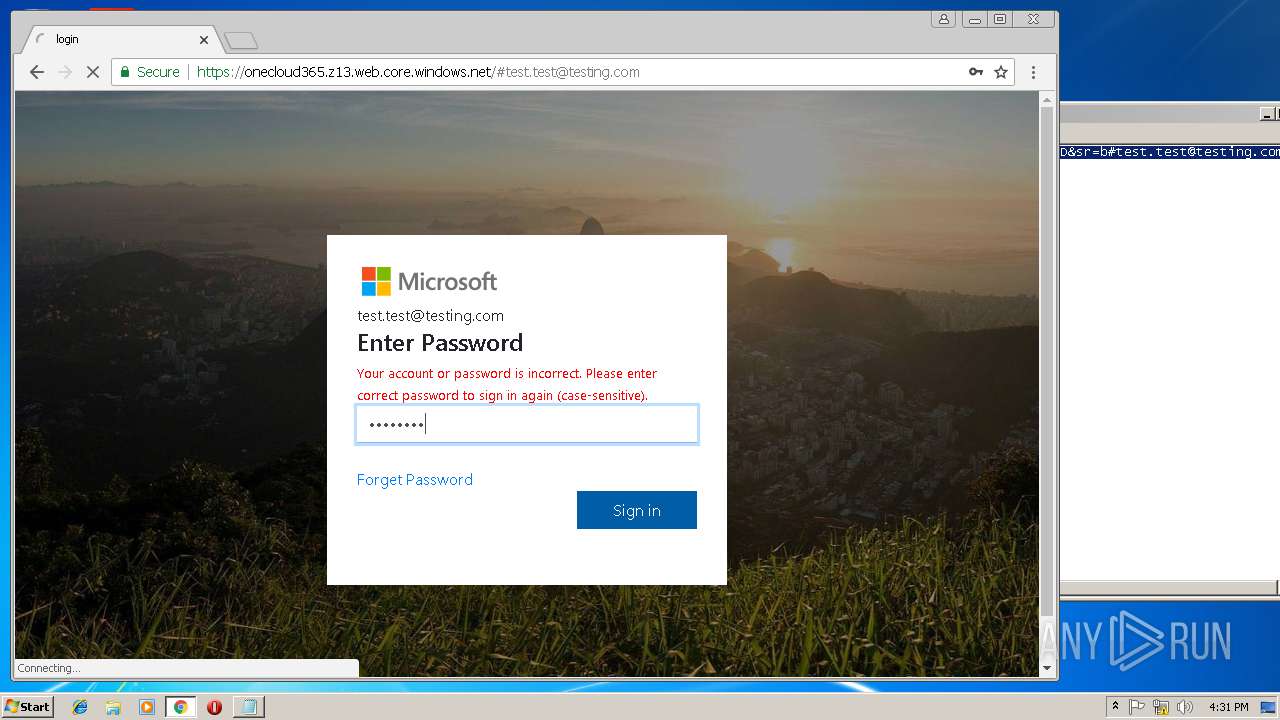
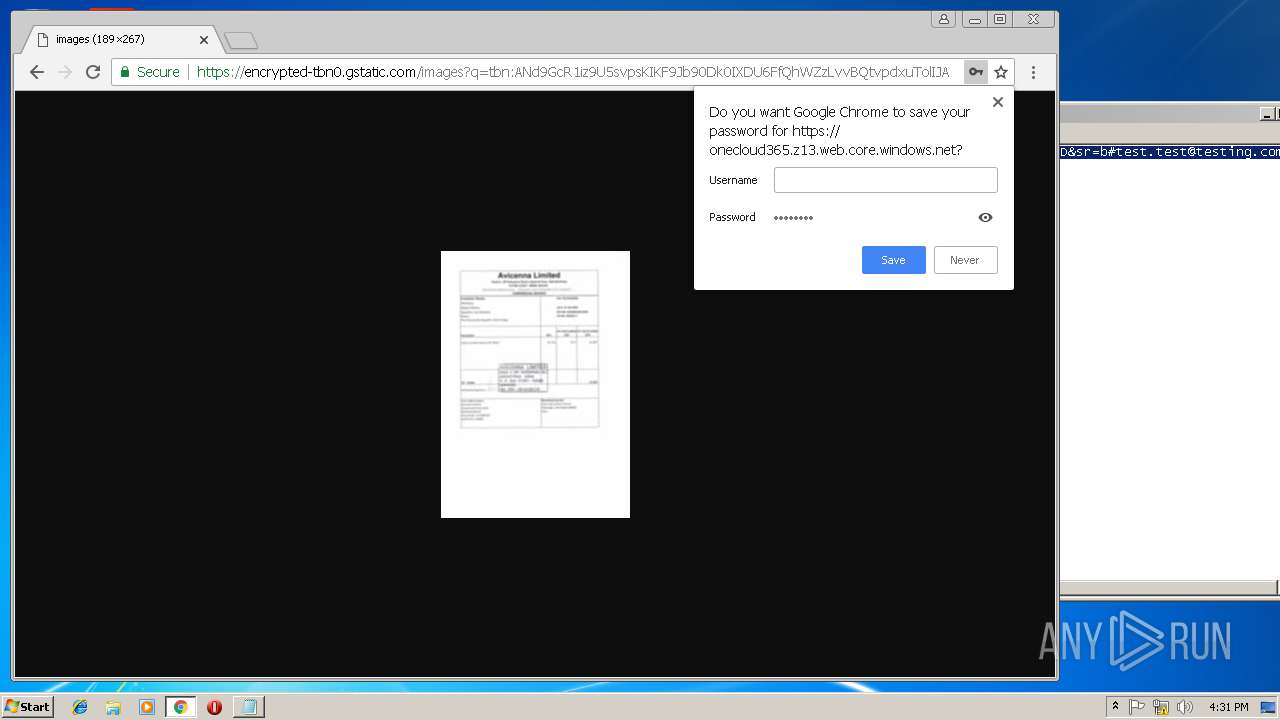
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2018, 16:29:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | C037732A001A1DD687F3A3A170751E9F |
| SHA1: | 96D6C065768FFA99FF9C511373678E03B632C405 |
| SHA256: | 392A43F1007DC6C71EF69C2DA548C45B265CB7ACB6CBA2E51C10E636D254B28C |
| SSDEEP: | 6:2CkqIKDwPVoWRL42XwrEM6KwmpOHe1CxlB7d:2dt1oq42Xsl6KO0sl1d |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
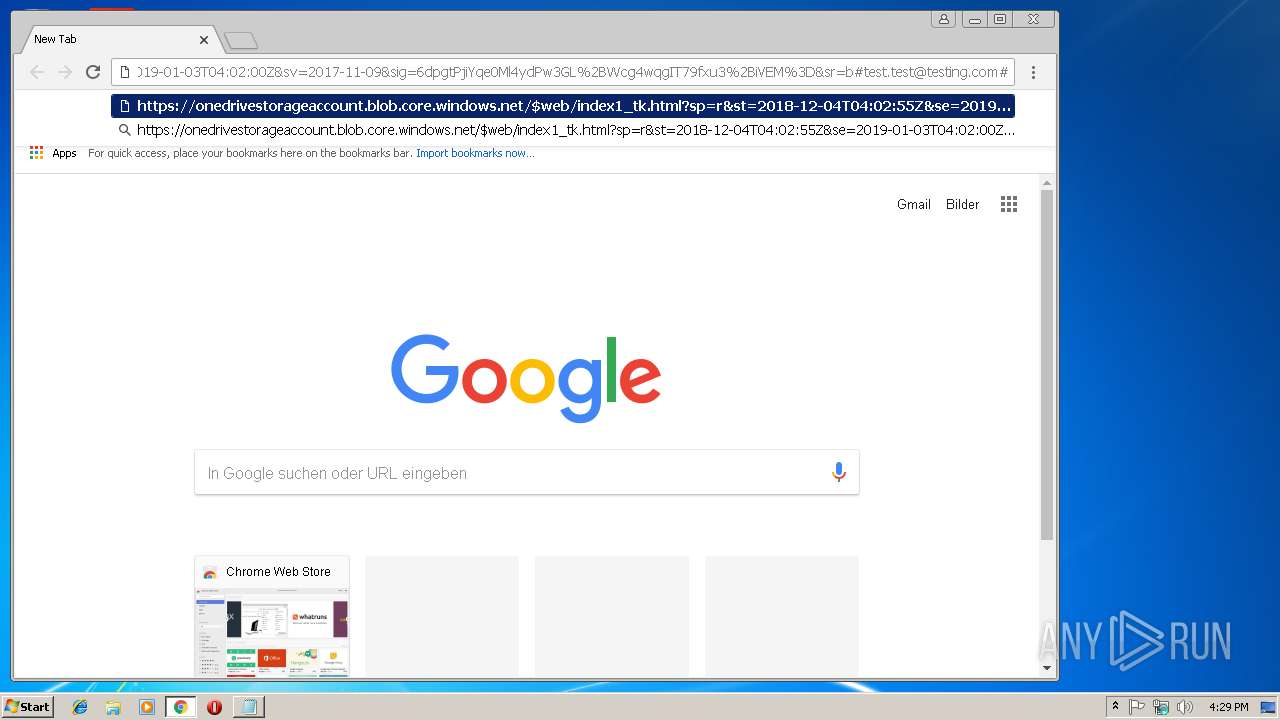
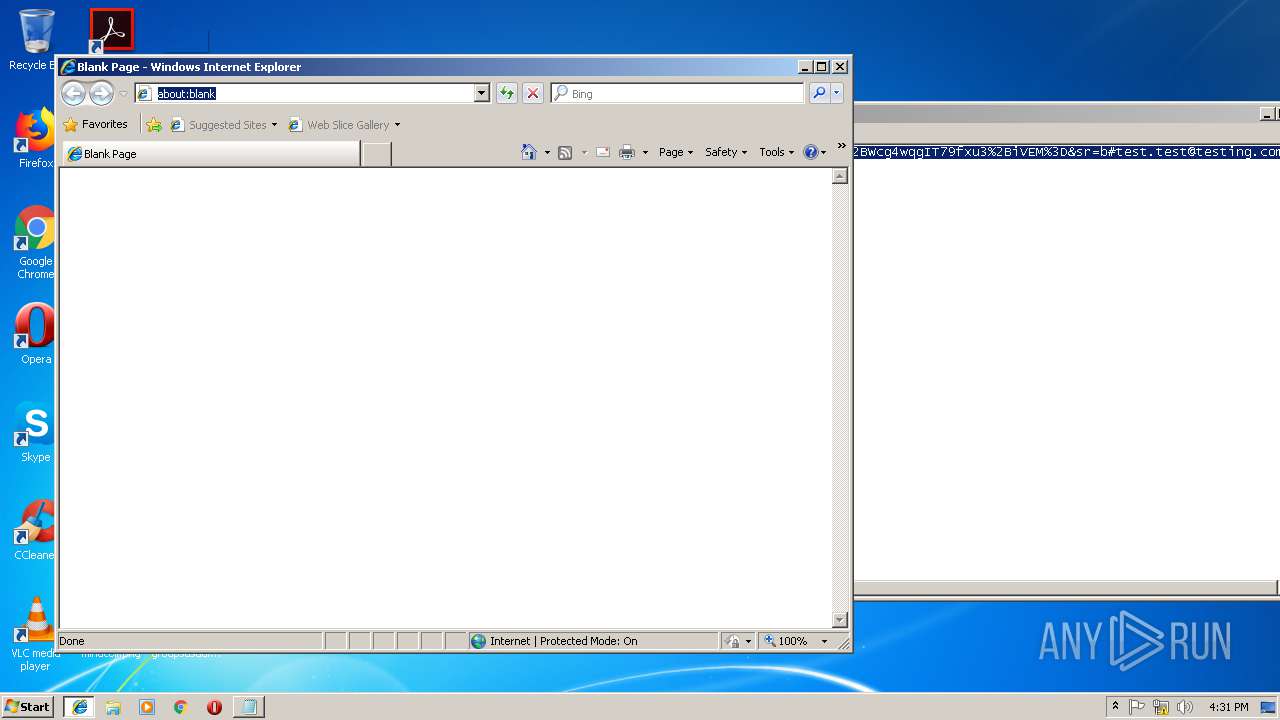
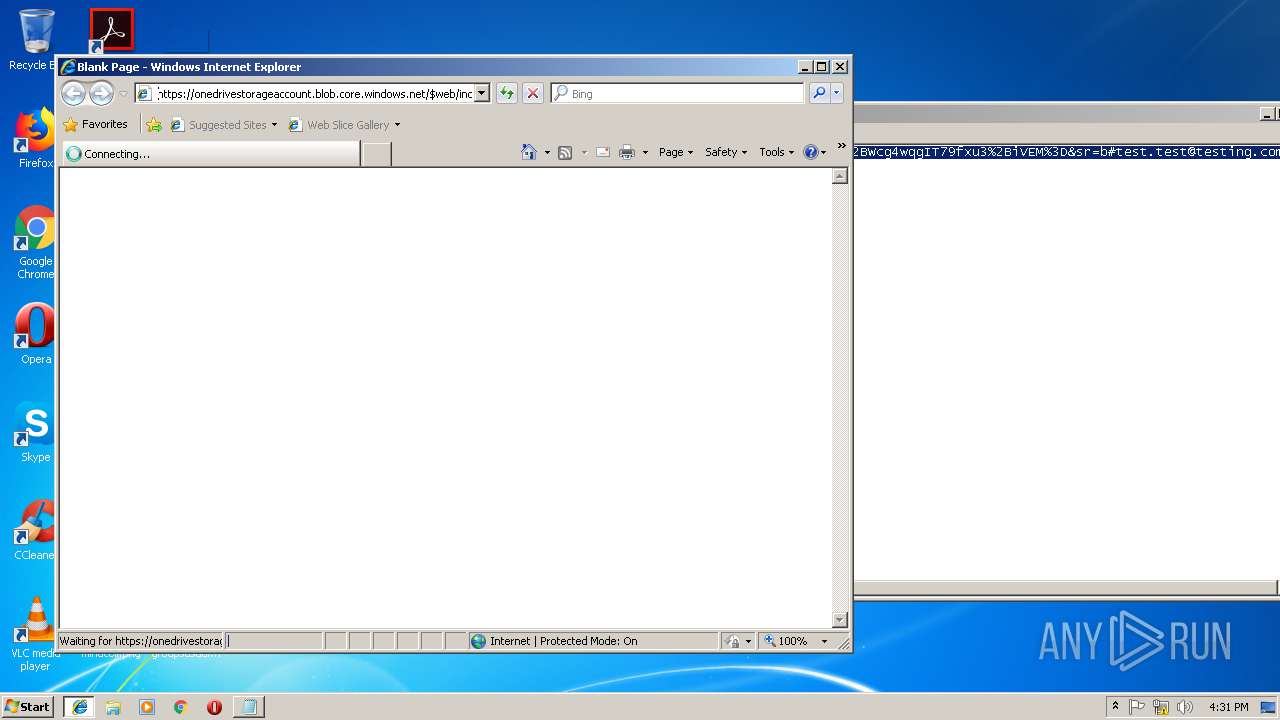
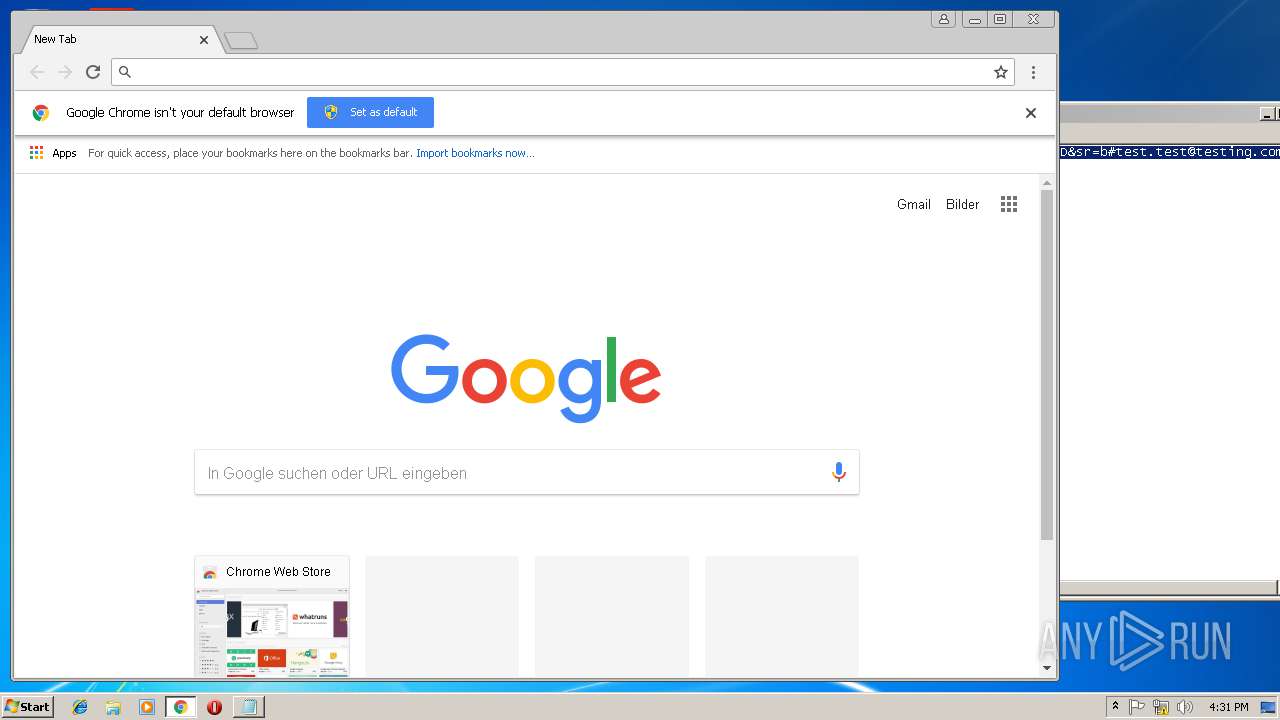
Application launched itself
- chrome.exe (PID: 2584)
- firefox.exe (PID: 3748)
- iexplore.exe (PID: 3784)
- iexplore.exe (PID: 2928)
- chrome.exe (PID: 2184)
Reads settings of System Certificates
- chrome.exe (PID: 2584)
Reads CPU info
- firefox.exe (PID: 3748)
- firefox.exe (PID: 1524)
- firefox.exe (PID: 504)
- firefox.exe (PID: 1172)
Creates files in the user directory
- firefox.exe (PID: 3748)
- iexplore.exe (PID: 3784)
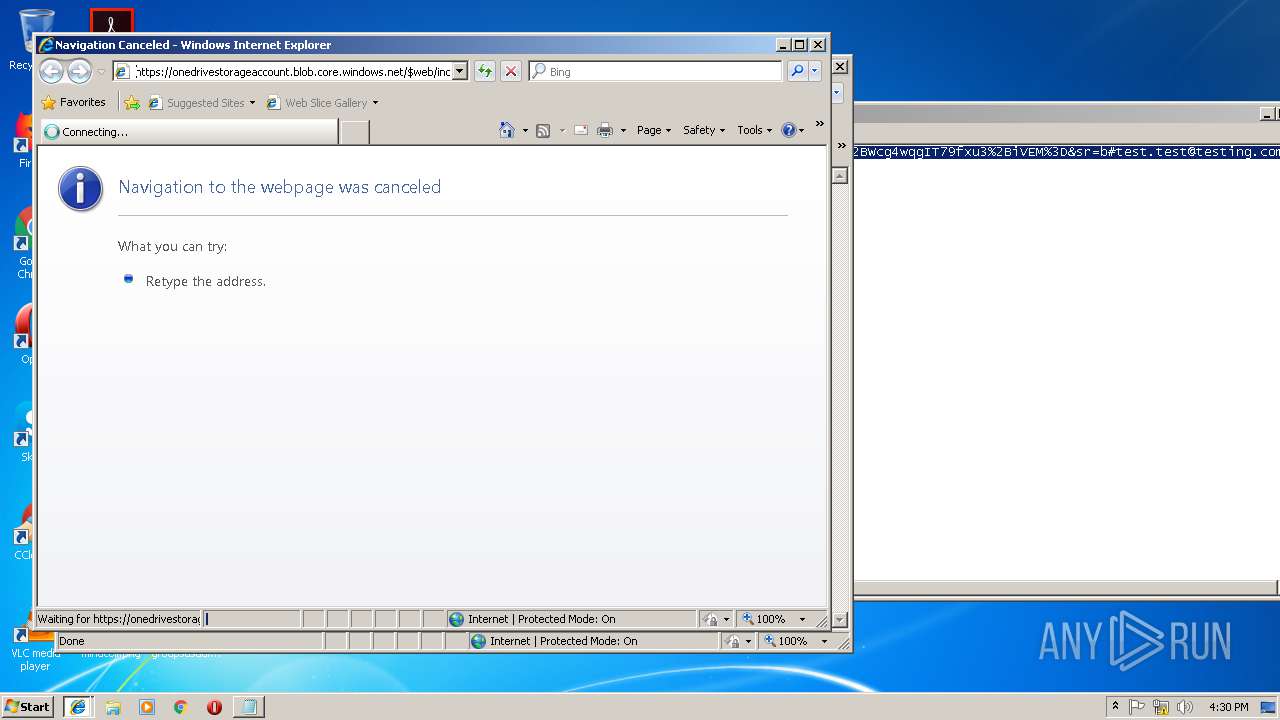
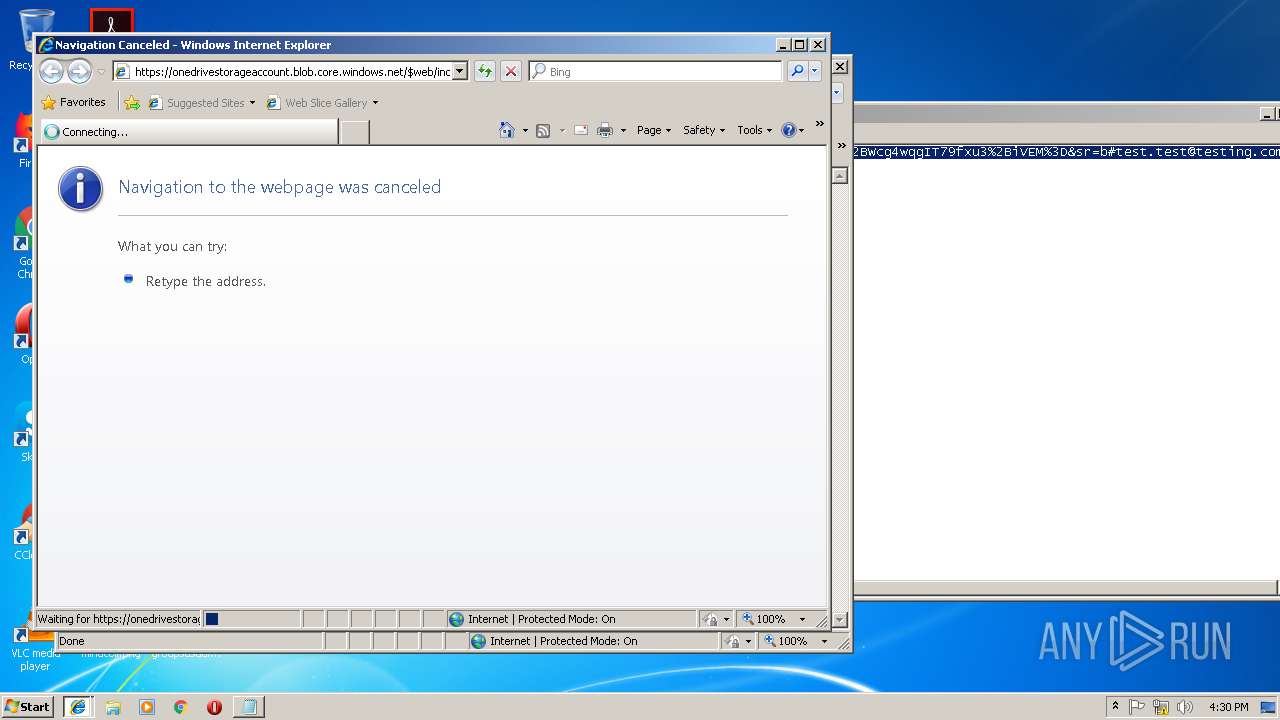
Changes internet zones settings
- iexplore.exe (PID: 3784)
- iexplore.exe (PID: 2928)
Reads Internet Cache Settings
- iexplore.exe (PID: 2264)
- iexplore.exe (PID: 3576)
- iexplore.exe (PID: 3720)
Reads internet explorer settings
- iexplore.exe (PID: 3576)
- iexplore.exe (PID: 2264)
- iexplore.exe (PID: 3720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
36
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 504 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3748.6.107631883\282686109" -childID 2 -isForBrowser -prefsHandle 2324 -prefsLen 11442 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3748 "\\.\pipe\gecko-crash-server-pipe.3748" 2416 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,3983595437042692550,13459915071405777847,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=60DDB16A1B490B5E4C99D63A00A37AB5 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=60DDB16A1B490B5E4C99D63A00A37AB5 --renderer-client-id=7 --mojo-platform-channel-handle=3772 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=844,62994257348173356,102073729790818604,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=DD588FD72D1F2936A8D5682C9423E186 --mojo-platform-channel-handle=896 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3748.12.878167317\311610170" -childID 3 -isForBrowser -prefsHandle 2964 -prefsLen 11808 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3748 "\\.\pipe\gecko-crash-server-pipe.3748" 2988 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3748.0.1362720629\1741951759" -childID 1 -isForBrowser -prefsHandle 1332 -prefsLen 8309 -schedulerPrefs 0001,2 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3748 "\\.\pipe\gecko-crash-server-pipe.3748" 1464 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 61.0.2 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=844,62994257348173356,102073729790818604,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=B67B73845E02F71405BDEAB303544834 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B67B73845E02F71405BDEAB303544834 --renderer-client-id=12 --mojo-platform-channel-handle=4148 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=844,62994257348173356,102073729790818604,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=88D58CEA459588703DDFEA422304269C --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=88D58CEA459588703DDFEA422304269C --renderer-client-id=11 --mojo-platform-channel-handle=2724 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2264 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3784 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,3983595437042692550,13459915071405777847,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=B109343BAE9B40A5631362B423E01A8F --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B109343BAE9B40A5631362B423E01A8F --renderer-client-id=9 --mojo-platform-channel-handle=3904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 743
Read events
1 520
Write events
215
Delete events
8
Modification events
| (PID) Process: | (2604) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2584-13188587382794375 |
Value: 259 | |||
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2584-13188587382794375 |
Value: 259 | |||
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
140
Text files
155
Unknown types
53
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\764faa01-01a1-4eb0-a865-bba051a282af.tmp | — | |
MD5:— | SHA256:— | |||
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f0fe0131-b245-4382-a5e0-7c92bcb99cb4.tmp | — | |
MD5:— | SHA256:— | |||
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF13e90b.TMP | text | |
MD5:— | SHA256:— | |||
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Translate Ranker Model | binary | |
MD5:— | SHA256:— | |||
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\LOG.old~RF13e8dc.TMP | text | |
MD5:8CA4BA2B95D7089861A48ED69FDE6561 | SHA256:AA64C14D0C68B62BBAB62A6D6FA4662FF89E1FBC7B337C926AC213C191D6406C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
74
DNS requests
92
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3748 | firefox.exe | POST | 200 | 92.122.53.18:80 | http://ocsp.comodoca.com/ | unknown | der | 471 b | whitelisted |
3748 | firefox.exe | POST | 200 | 172.217.168.14:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 463 b | whitelisted |
3748 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3748 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2928 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3748 | firefox.exe | GET | 200 | 2.16.186.50:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
3784 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2928 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3748 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2584 | chrome.exe | 172.217.168.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2584 | chrome.exe | 172.217.168.35:443 | www.google.de | Google Inc. | US | whitelisted |
2584 | chrome.exe | 172.217.168.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2584 | chrome.exe | 172.217.168.14:443 | apis.google.com | Google Inc. | US | whitelisted |
2584 | chrome.exe | 172.217.168.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2584 | chrome.exe | 172.217.168.36:443 | www.google.com | Google Inc. | US | whitelisted |
2584 | chrome.exe | 172.217.20.67:443 | www.google.at | Google Inc. | US | whitelisted |
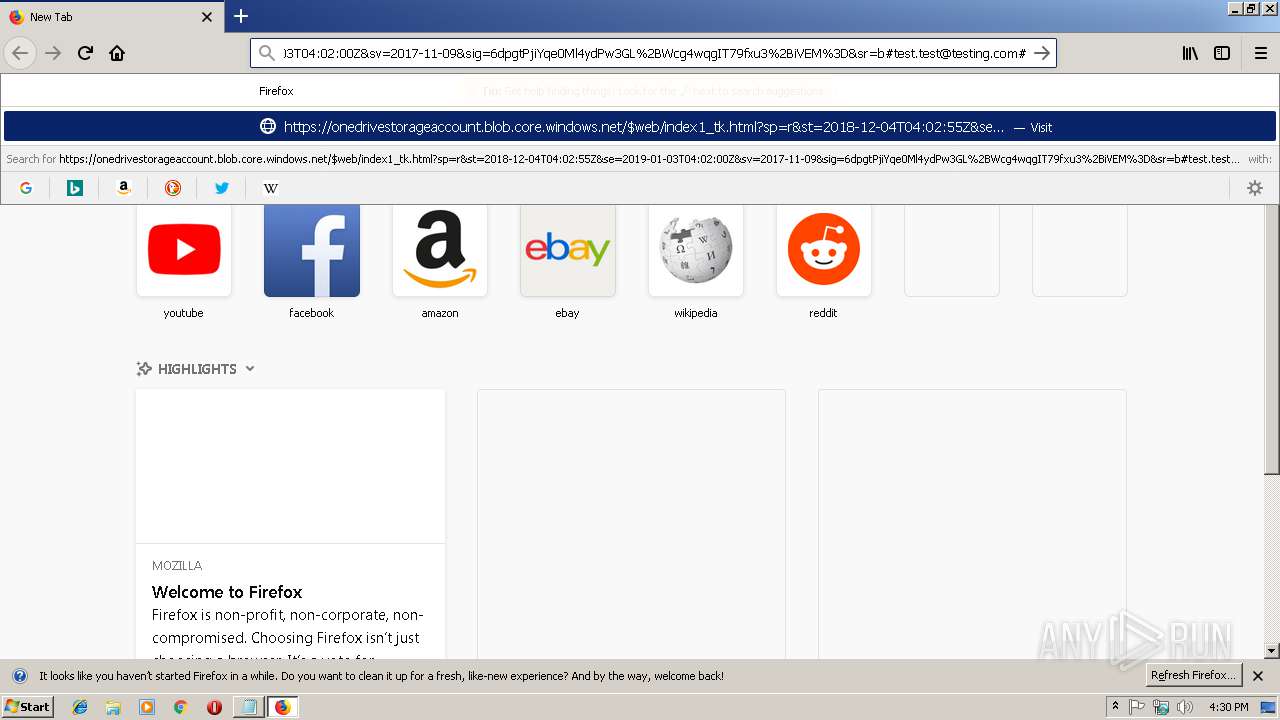
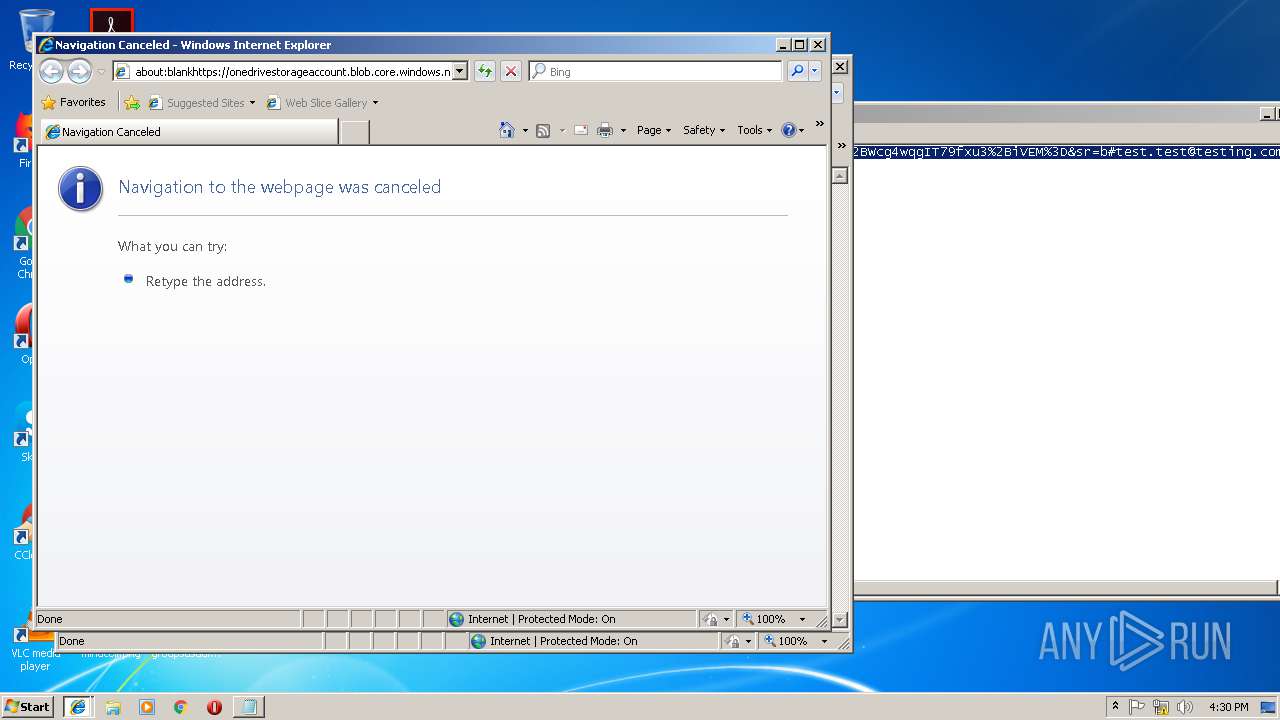
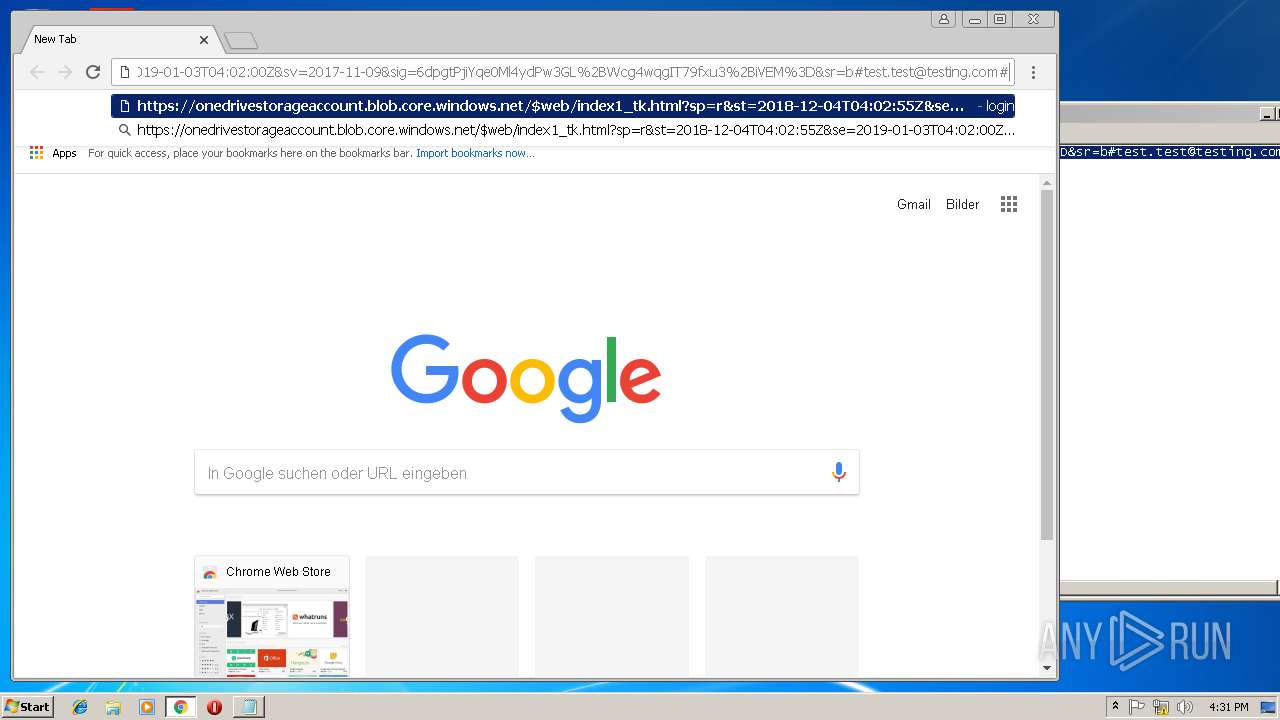
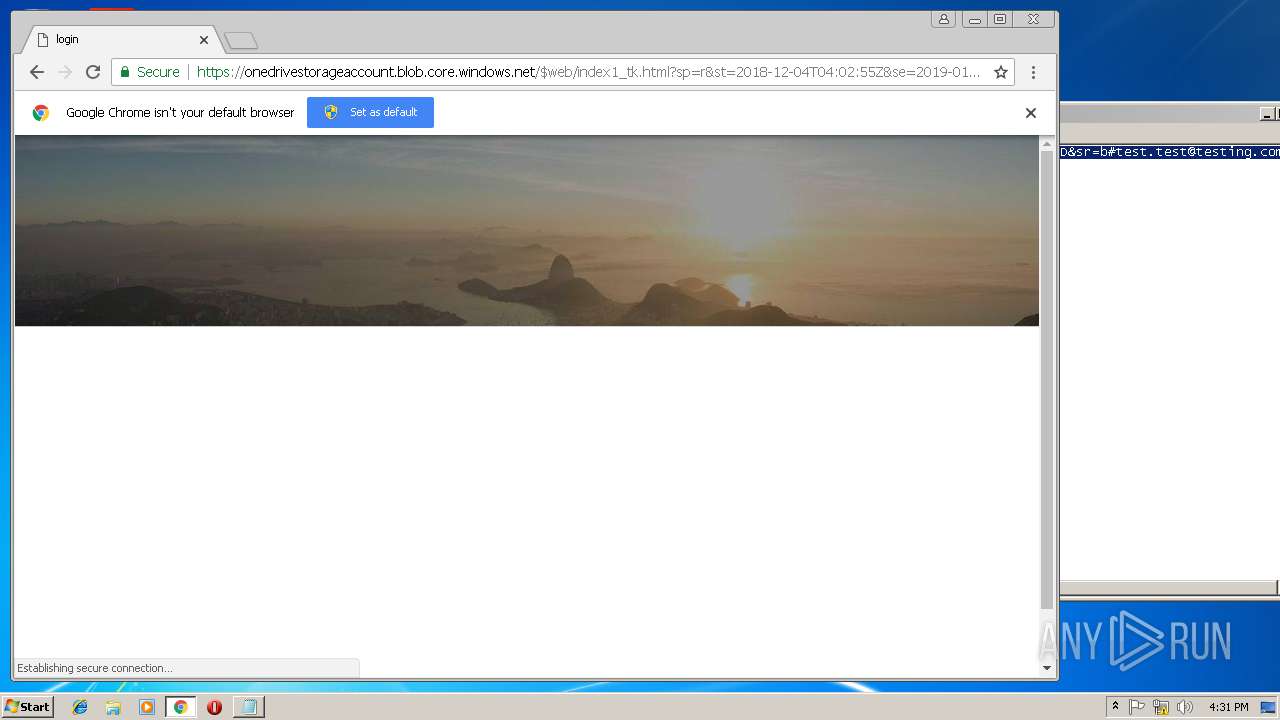
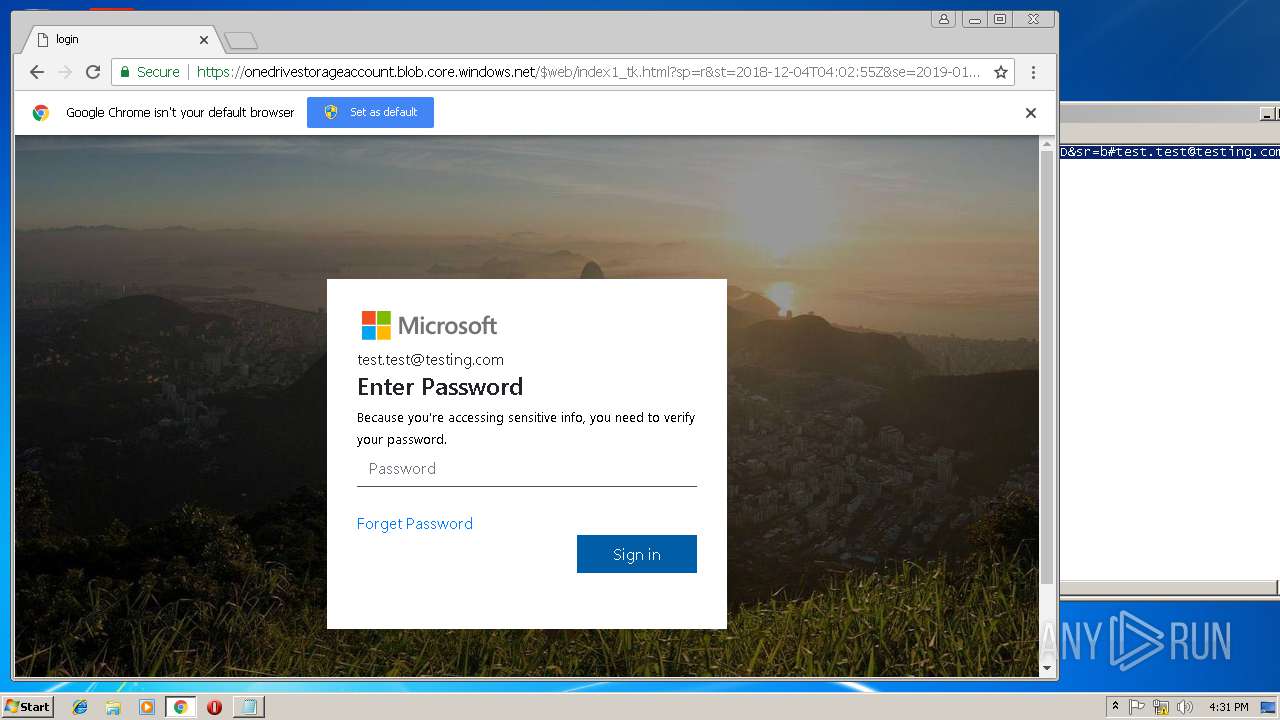
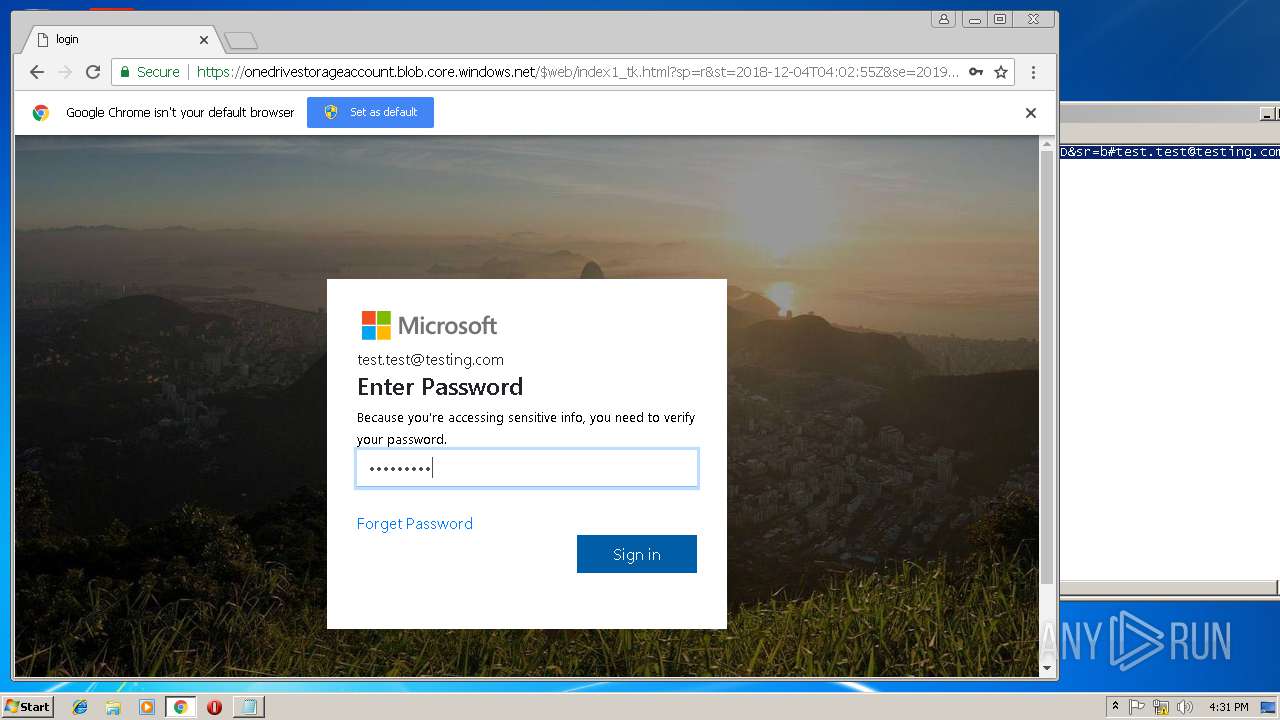
2584 | chrome.exe | 185.224.138.34:443 | u512841860.hostingerapp.com | — | — | unknown |
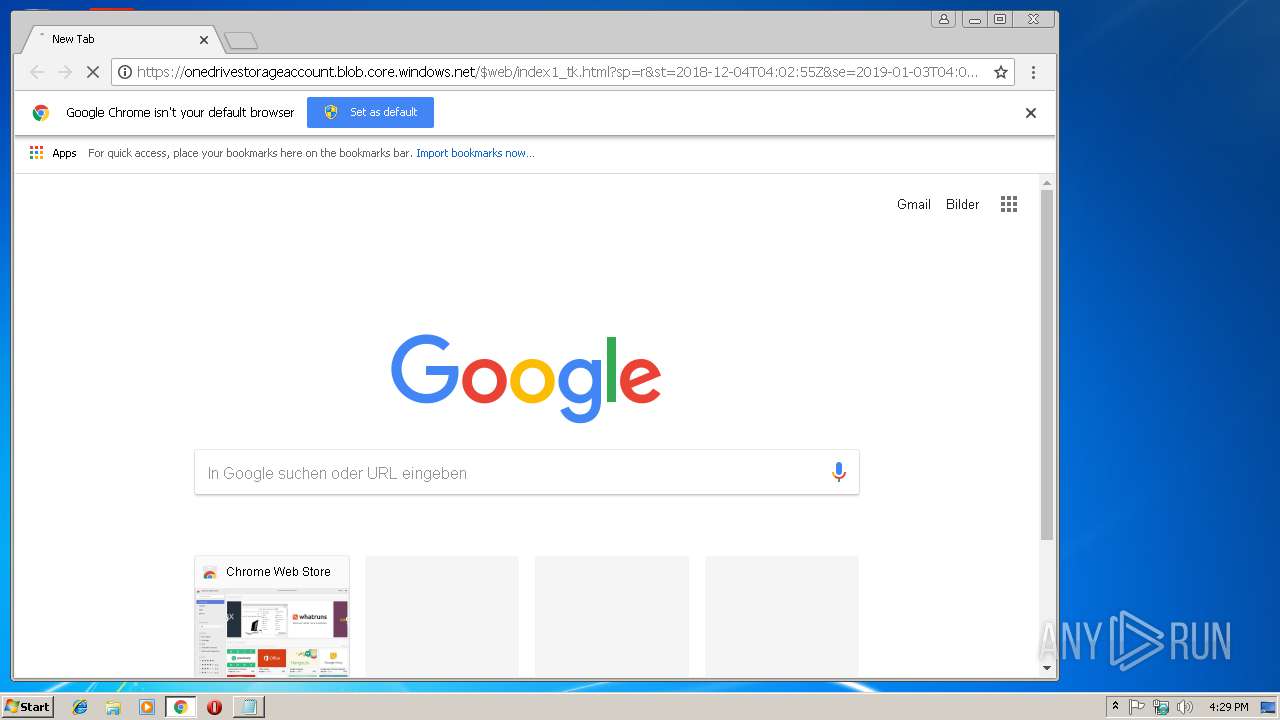
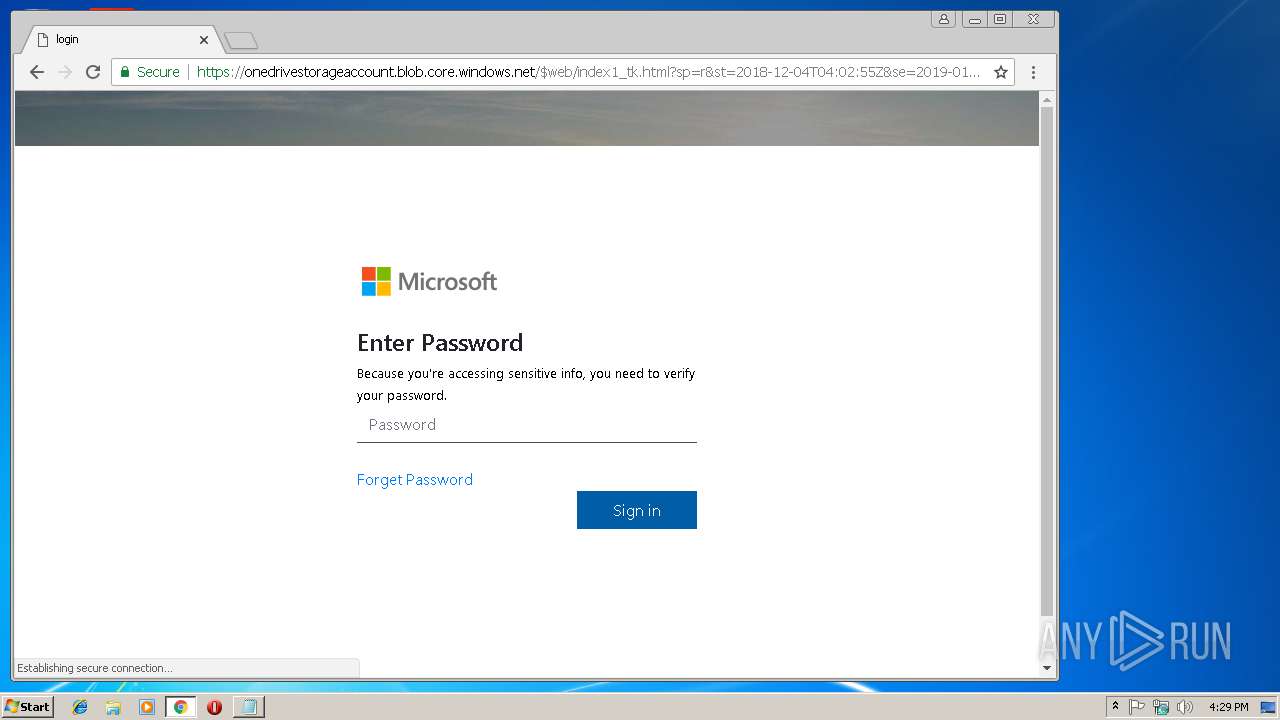
2584 | chrome.exe | 13.68.165.64:443 | onedrivestorageaccount.blob.core.windows.net | Microsoft Corporation | US | whitelisted |
3748 | firefox.exe | 2.16.186.50:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
onedrivestorageaccount.blob.core.windows.net |
| unknown |
www.google.com |
| malicious |
www.google.at |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
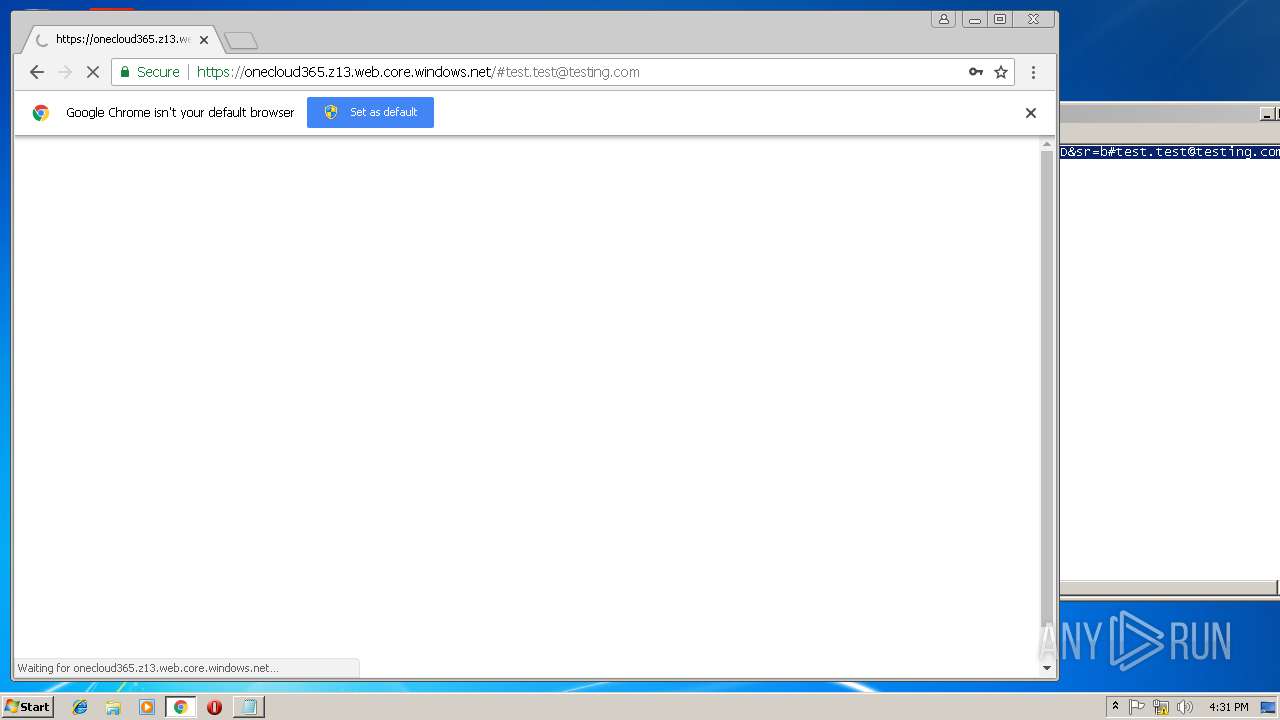
1052 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Lookup for Possible Common Brand Phishing Hosted on Legitimate Windows Service |
1052 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Lookup for Possible Common Brand Phishing Hosted on Legitimate Windows Service |
1052 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Lookup for Possible Common Brand Phishing Hosted on Legitimate Windows Service |