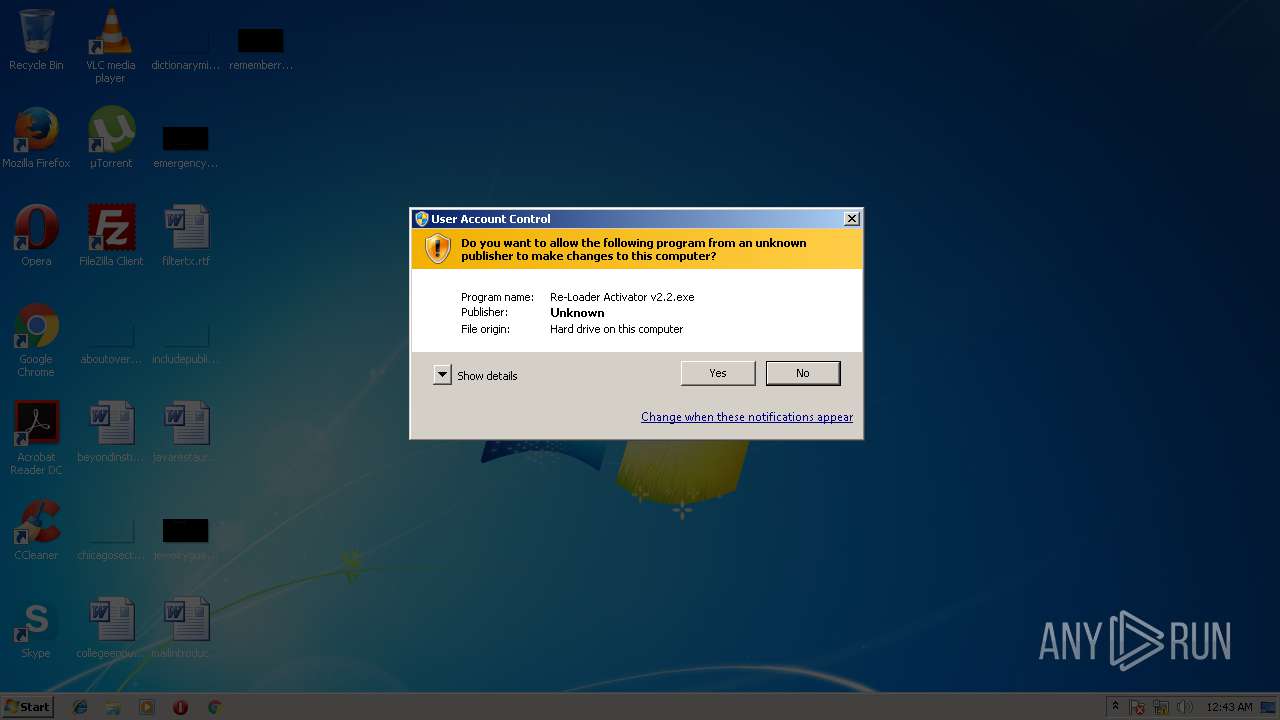
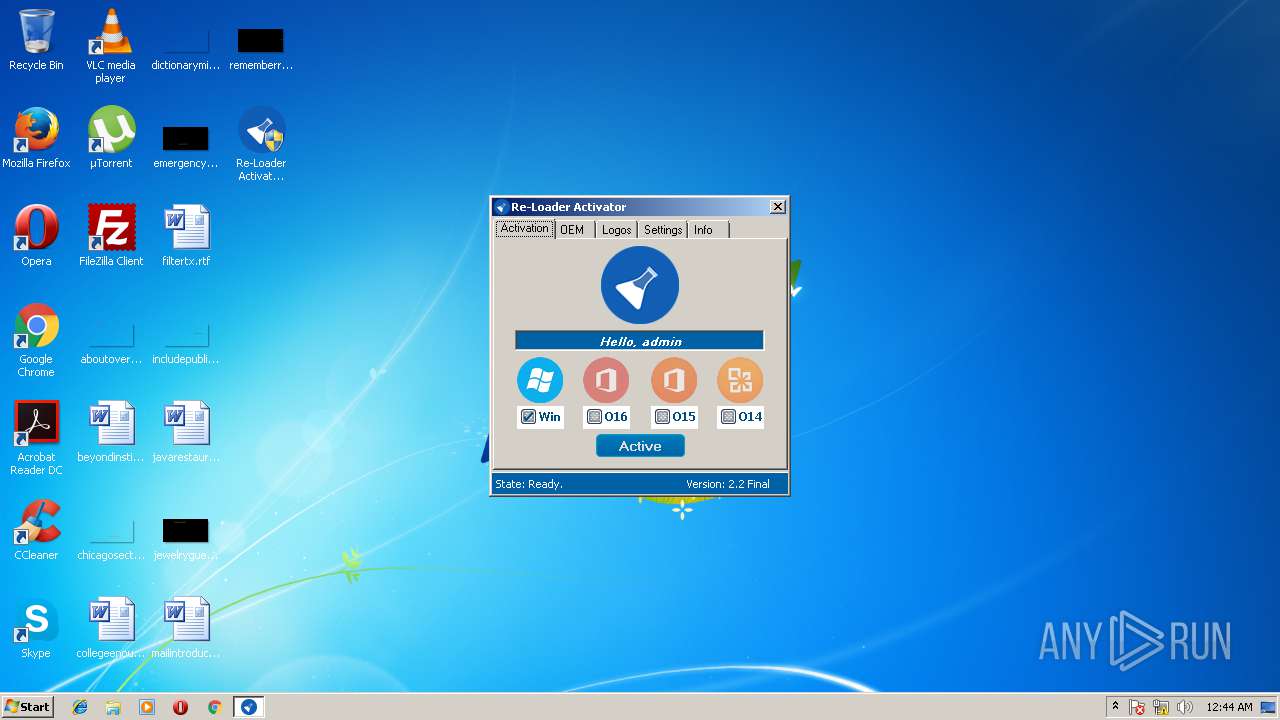
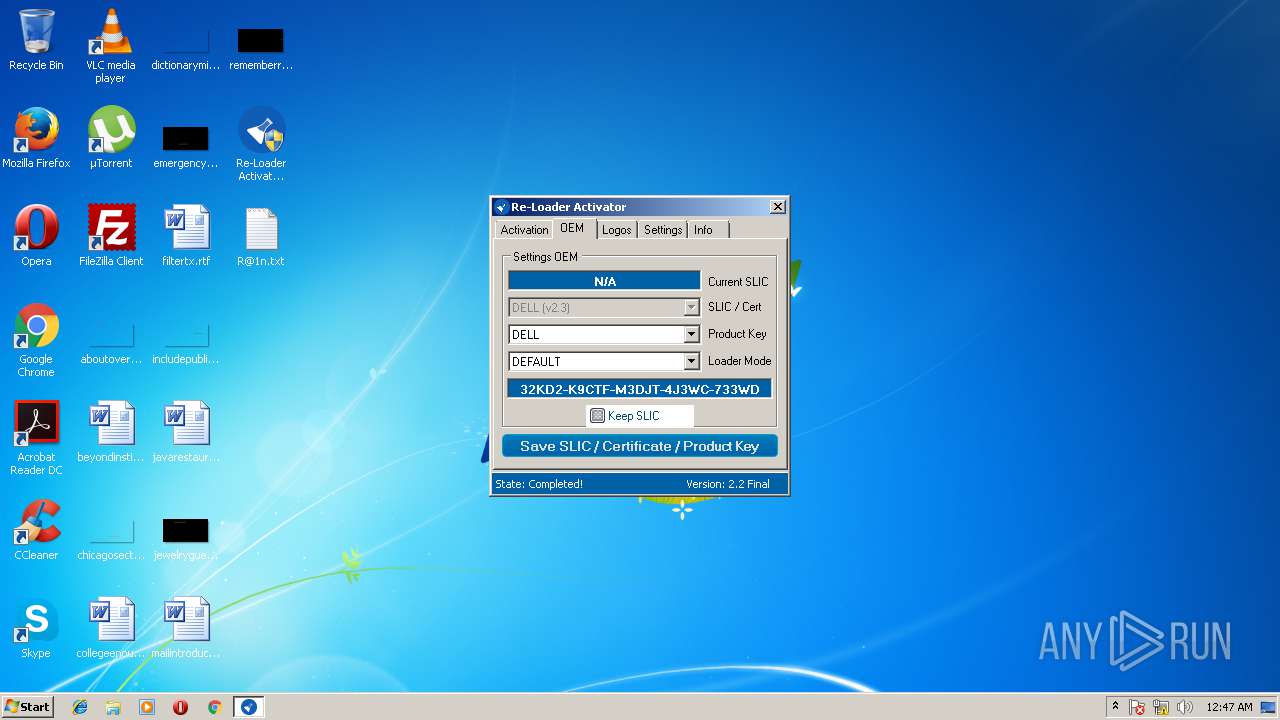
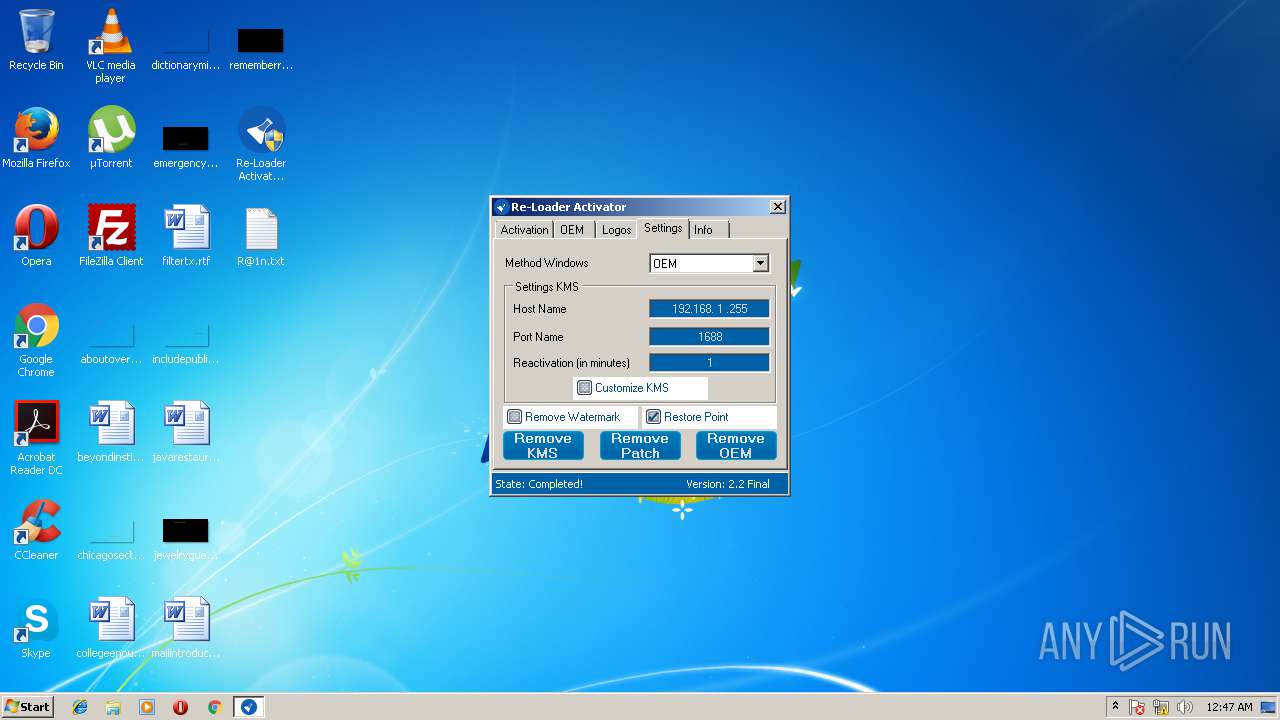
| File name: | Re-Loader Activator v2.2.exe |
| Full analysis: | https://app.any.run/tasks/6fa1595b-0b9f-40ec-9cd3-d92604f4ae3d |
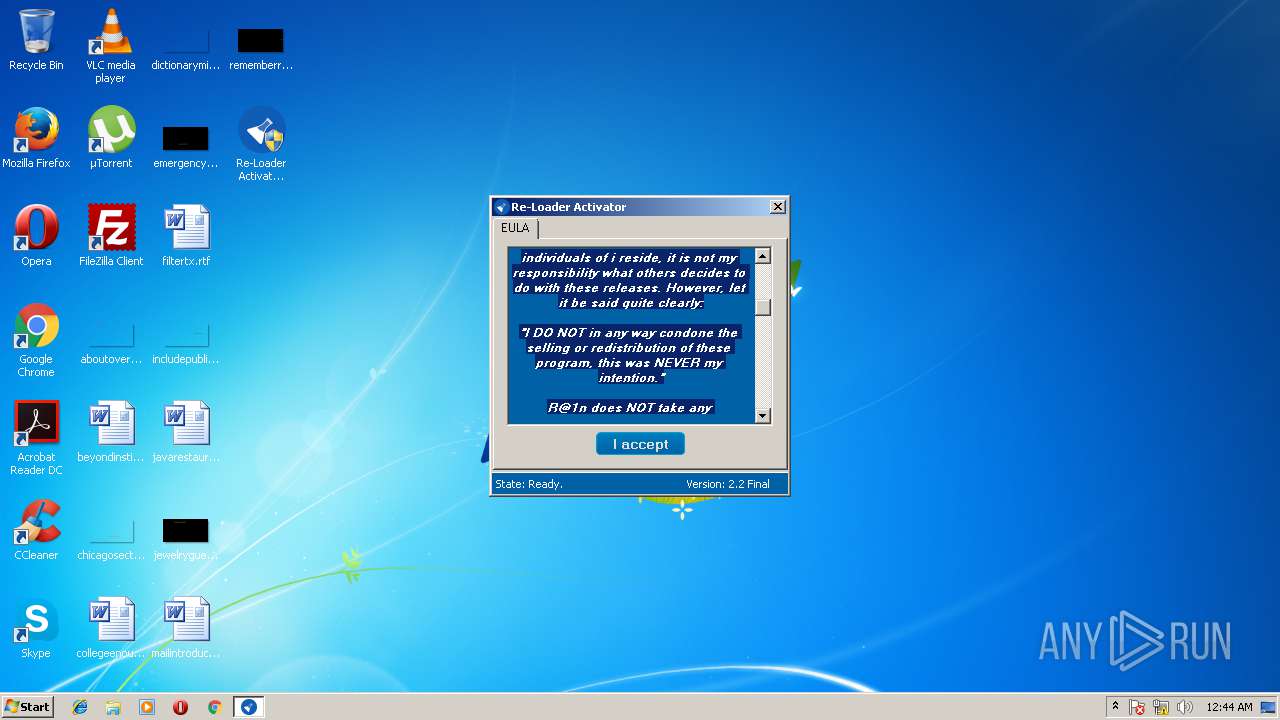
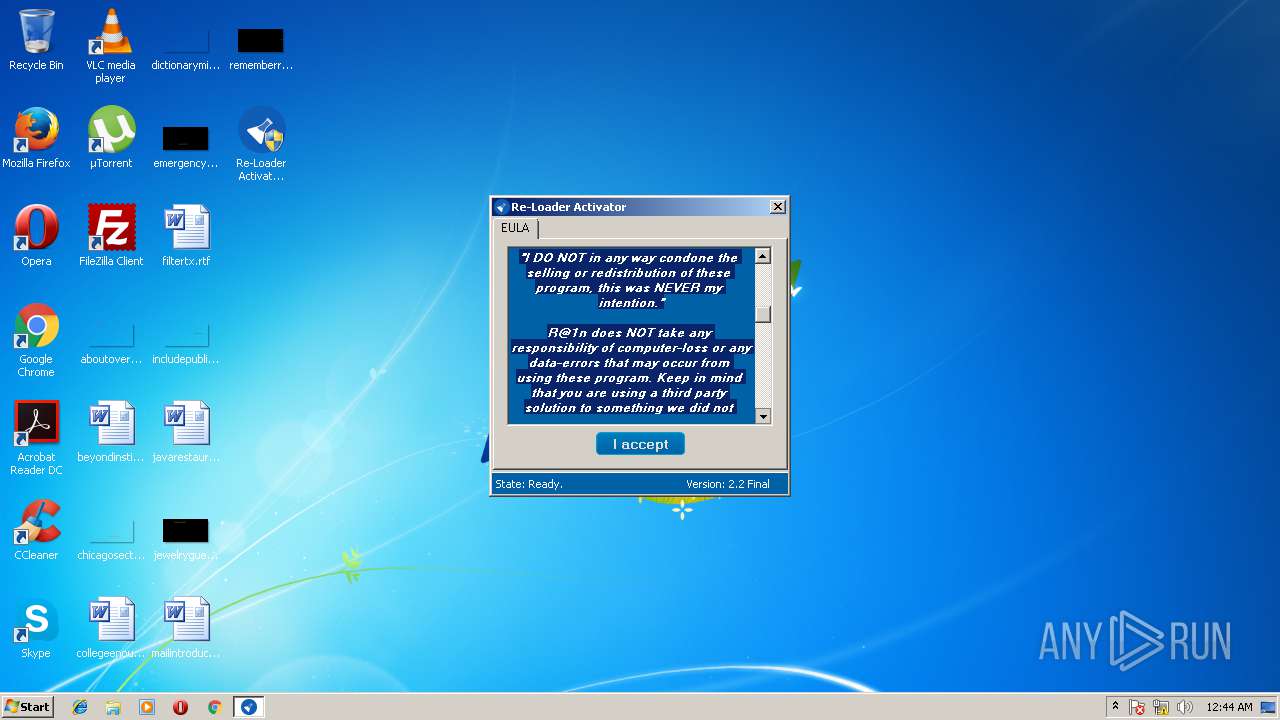
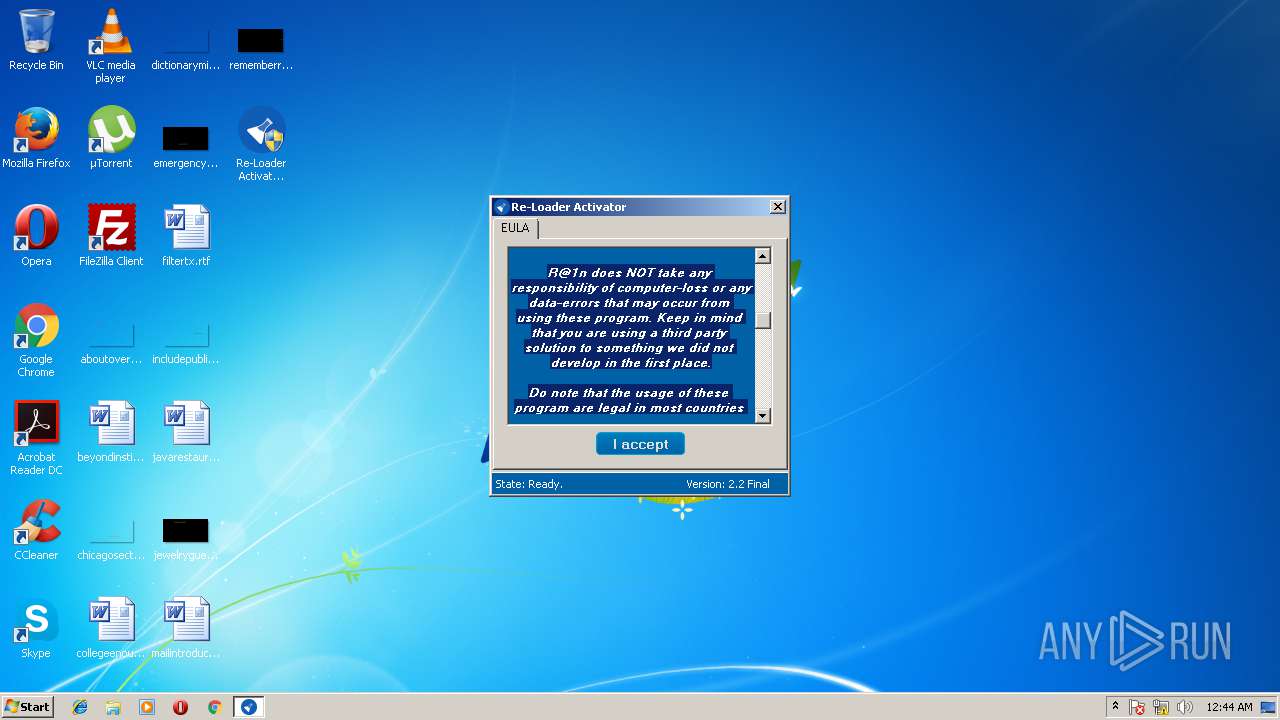
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2018, 00:43:28 |
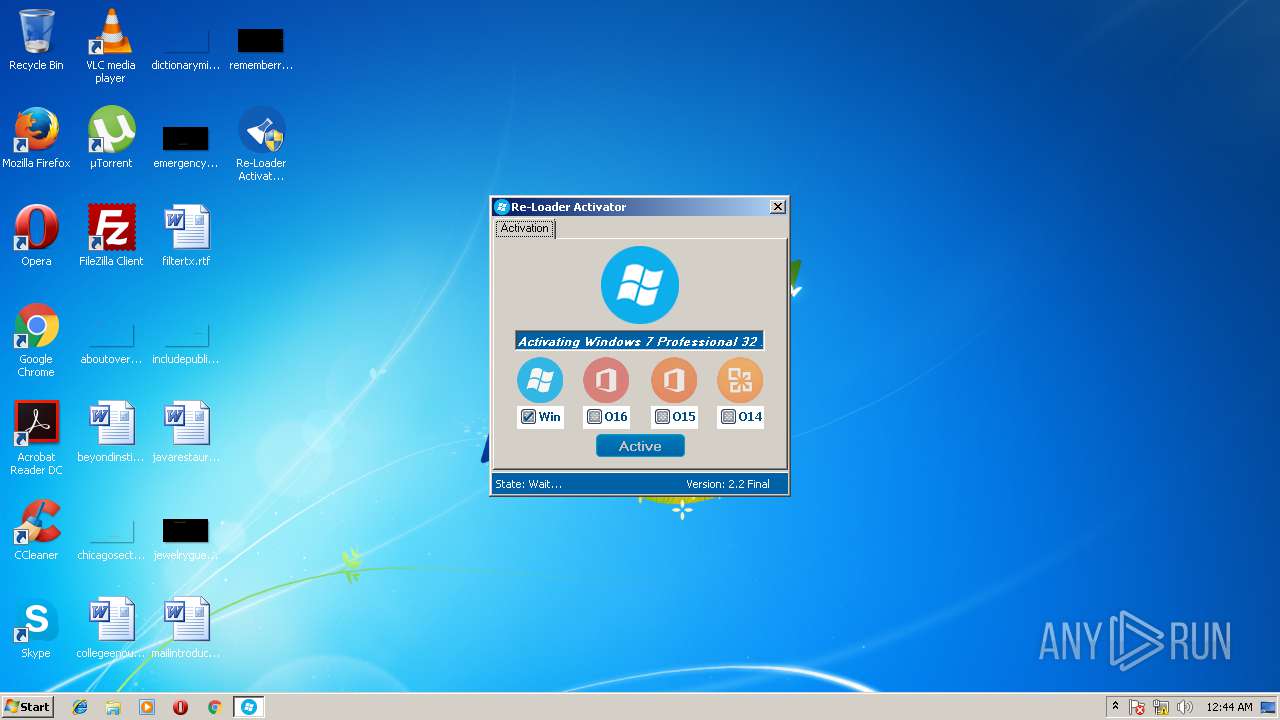
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | MS-DOS executable, MZ for MS-DOS |
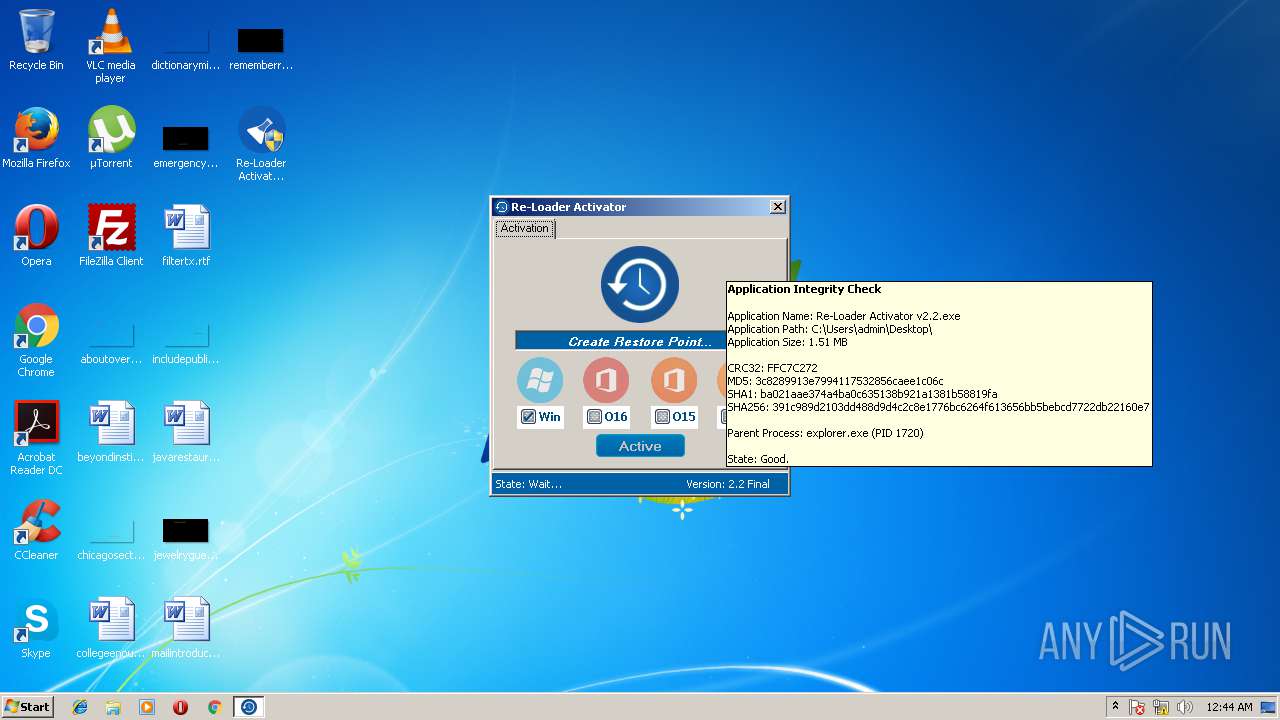
| MD5: | 3C8289913E7994117532856CAEE1C06C |
| SHA1: | BA021AAE374A4BA0C635138B921A1381B58819FA |
| SHA256: | 391C989D2103DD488D9D4C2C8E1776BC6264F613656BB5BEBCD7722DB22160E7 |
| SSDEEP: | 24576:KQxv6TwvjBtCz0N6NqdsYKsHQhbpGWLb0V++gXgEjIIxF+XqU3VGEqgLc7Vg:KMuwr9yWshhbS8wCtU3V/q0YVg |
MALICIOUS
Application was dropped or rewritten from another process
- brset.exe (PID: 2728)
- bootsect.exe (PID: 2920)
SUSPICIOUS
Low-level read access rights to disk partition
- bootsect.exe (PID: 2920)
- brset.exe (PID: 2728)
- vssvc.exe (PID: 3172)
Modifies files in the system directory
- vssvc.exe (PID: 3172)
Creates or modifies windows services
- DllHost.exe (PID: 3600)
- vssvc.exe (PID: 3172)
INFO
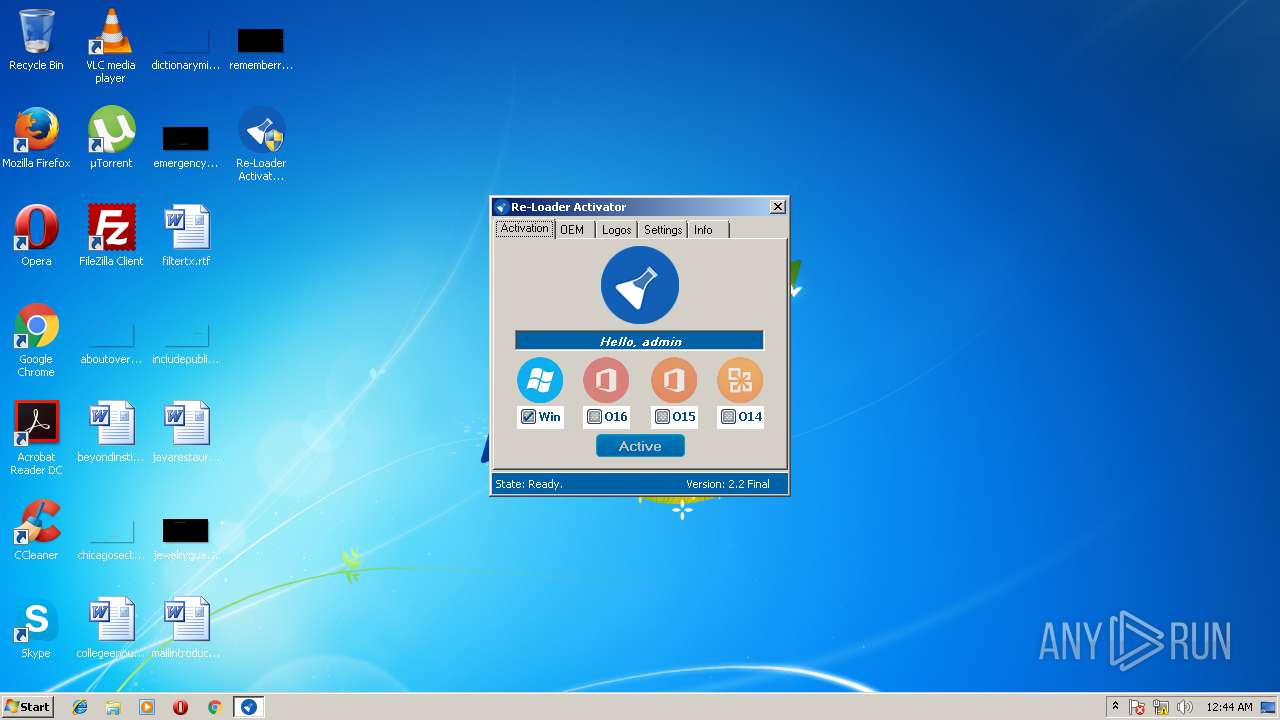
Loads the .NET runtime environment
- Re-Loader Activator v2.2.exe (PID: 3044)
Reads Microsoft Office registry keys
- Re-Loader Activator v2.2.exe (PID: 3044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:12:09 19:58:13+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 4096 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e5e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.3.0 |
| ProductVersionNumber: | 2.2.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Activator |
| FileVersion: | 2.2.3.0 |
| InternalName: | Activator.exe |
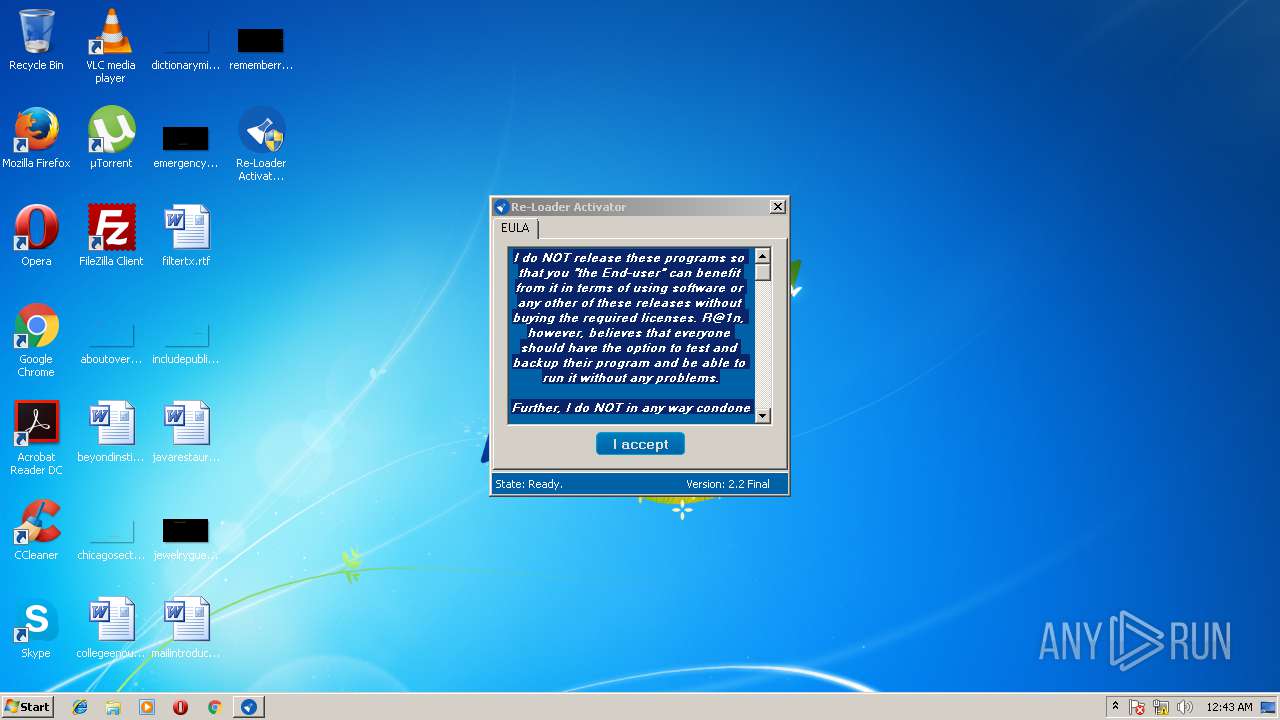
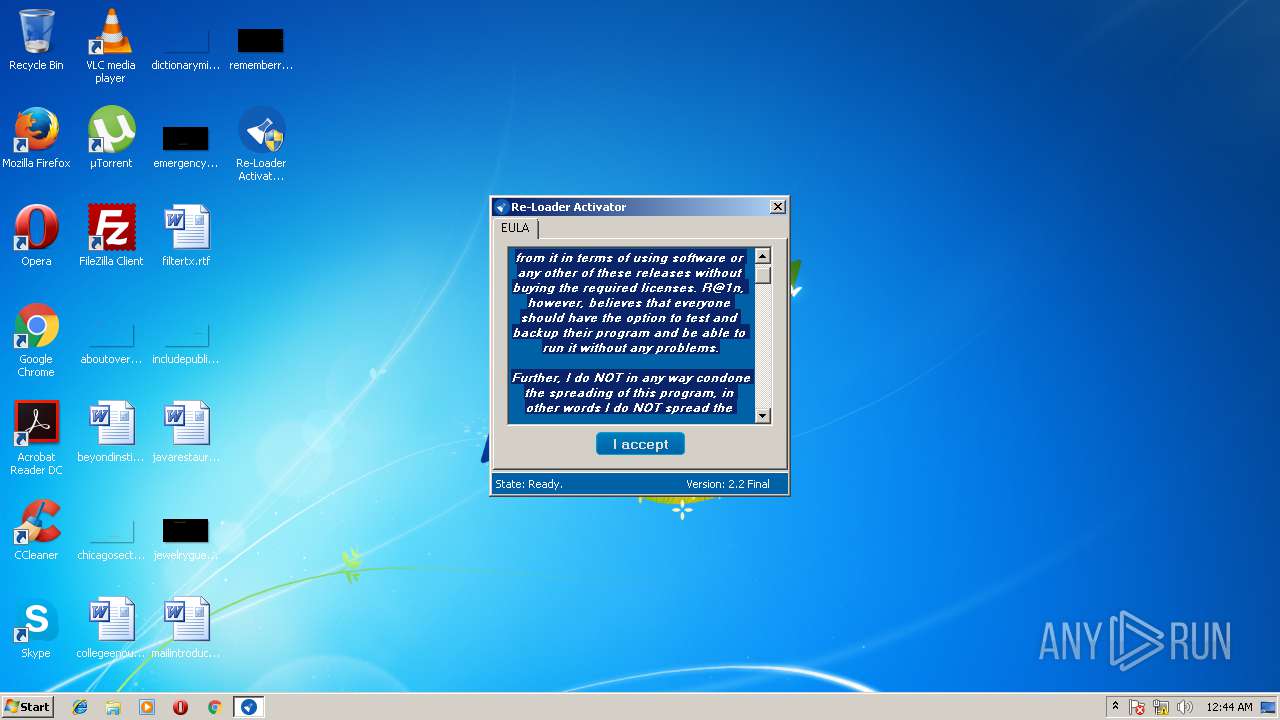
| LegalCopyright: | Copyright © By R@1n 2015 |
| LegalTrademarks: | - |
| OriginalFileName: | Activator.exe |
| ProductName: | Re-Loader By R@1n |
| ProductVersion: | 2.2.3.0 |
| AssemblyVersion: | 2.2.3.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Dec-2010 18:58:13 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Activator |
| FileVersion: | 2.2.3.0 |
| InternalName: | Activator.exe |
| LegalCopyright: | Copyright © By R@1n 2015 |
| LegalTrademarks: | - |
| OriginalFilename: | Activator.exe |
| ProductName: | Re-Loader By R@1n |
| ProductVersion: | 2.2.3.0 |
| Assembly Version: | 2.2.3.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0040 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0002 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0xB400 |
| OEM information: | 0xCD09 |
| Address of NE header: | 0x00000040 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 09-Dec-2010 18:58:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00000E64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.26735 |
.rsrc | 0x00004000 | 0x00008FA8 | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.43592 |
.reloc | 0x0000E000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.35837 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00727 | 3463 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.8639 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.0782 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.60895 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.62308 | 62 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
49
Monitored processes
6
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2728 | "C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\brset.exe" /nt60 SYS /force | C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\brset.exe | — | Re-Loader Activator v2.2.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2920 | "C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\bootsect.exe" /nt52 SYS /force | C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\bootsect.exe | — | Re-Loader Activator v2.2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Sector Manipulation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3040 | "C:\Users\admin\Desktop\Re-Loader Activator v2.2.exe" | C:\Users\admin\Desktop\Re-Loader Activator v2.2.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Activator Exit code: 3221226540 Version: 2.2.3.0 | |||||||||||||||
| 3044 | "C:\Users\admin\Desktop\Re-Loader Activator v2.2.exe" | C:\Users\admin\Desktop\Re-Loader Activator v2.2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Activator Exit code: 0 Version: 2.2.3.0 Modules
| |||||||||||||||
| 3172 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3600 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
249
Read events
111
Write events
138
Delete events
0
Modification events
| (PID) Process: | (3044) Re-Loader Activator v2.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3044) Re-Loader Activator v2.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3600) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000F53795CFADC0D301100E0000040B0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3600) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 47 | |||
| (PID) Process: | (3600) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000AB33F2CFADC0D301100E0000040B0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3600) DllHost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000000596F4CFADC0D301100E0000D00A0000E8030000010000000000000000000000906FCA45EA622B4BAC2CAF5CA45260F30000000000000000 | |||
| (PID) Process: | (3172) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C78100D0ADC0D301640C0000D40E0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3172) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C78100D0ADC0D301640C0000DC0E0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3172) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C78100D0ADC0D301640C0000B8080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3172) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C78100D0ADC0D301640C0000B00B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
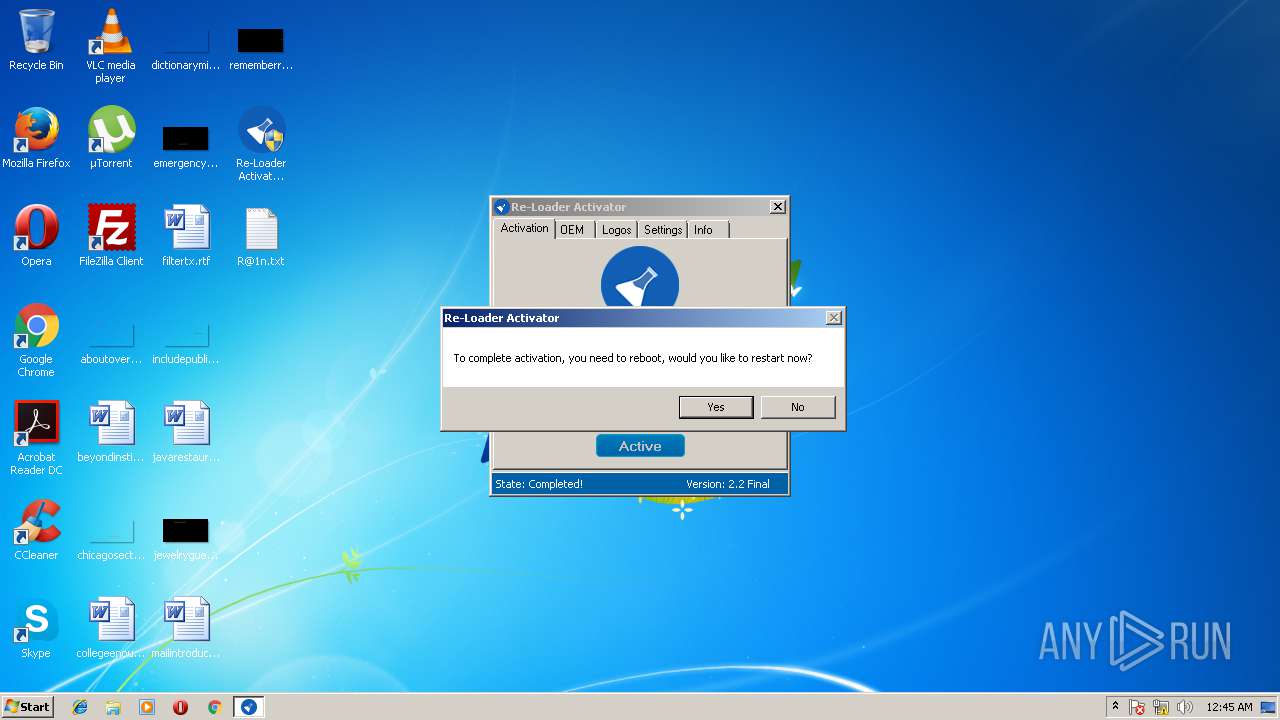
Executable files
1
Suspicious files
3
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3600 | DllHost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3044 | Re-Loader Activator v2.2.exe | C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\brset.exe | — | |
MD5:— | SHA256:— | |||
| 2728 | brset.exe | \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963} | — | |
MD5:— | SHA256:— | |||
| 3044 | Re-Loader Activator v2.2.exe | \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963}\6OXIY | — | |
MD5:— | SHA256:— | |||
| 2920 | bootsect.exe | \\?\Volume{e1a82db3-a9f0-11e7-b142-806e6f6e6963} | — | |
MD5:— | SHA256:— | |||
| 3172 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 3600 | DllHost.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{45ca6f90-62ea-4b2b-ac2c-af5ca45260f3}_OnDiskSnapshotProp | binary | |
MD5:F6F8FC46439C45CB0259102943349FDD | SHA256:957CF7D588732E9AA01E0747C62AB8EFC8361EAF23788E673DB51914F1718464 | |||
| 3600 | DllHost.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:F6F8FC46439C45CB0259102943349FDD | SHA256:957CF7D588732E9AA01E0747C62AB8EFC8361EAF23788E673DB51914F1718464 | |||
| 3044 | Re-Loader Activator v2.2.exe | C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\bootsect.exe | executable | |
MD5:C72D27CA3A06B92C5BF1FABE2D3DA7C3 | SHA256:27E1F93786F5029E88FAD92FA82E5DDF7A06E2AAF53EE4D4CCE31C90E9C76EDB | |||
| 3044 | Re-Loader Activator v2.2.exe | C:\Users\admin\AppData\Local\Temp\Re-Loader\OEM\SLIC\6OXIY | binary | |
MD5:49864D91EDA705BB680AF048D74AD0A5 | SHA256:730DF9B3FFB7D69476D81EF8A20D4F845797B0344233F9C49EB962A378F7518C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report