| File name: | Cheat.Space.1.4.3.msi |
| Full analysis: | https://app.any.run/tasks/69aa4c5e-1b56-4288-b017-8f5d3711c5d2 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2023, 10:00:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.3, MSI Installer, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Sep 18 15:06:51 2020, Security: 0, Code page: 1252, Revision Number: {9FE10983-D7A2-4C66-A3B6-6C49C70386F7}, Number of Words: 2, Subject: Cheat Space, Author: Cheat Space Inc., Name of Creating Application: Cheat Space, Template: ;1033, Comments: This installer database contains the logic and data required to install Cheat Space., Title: Installation Database, Keywords: Installer, MSI, Database, Number of Pages: 200 |
| MD5: | 59F433E9F11F86EB53F8D08AB5CA593D |
| SHA1: | DECA4FC3822946BA0CCF97147FCF8213E64105FA |
| SHA256: | 39055333661DCB5D7656F182ECDDE893D427D15ADC06F7450EC9EFDF201A7186 |
| SSDEEP: | 98304:0Lw/iJOTeorMXXiyP4Pr8f97XotBef1Rm+DNwNenuLCIutvZ3Igbr+bmt:TRBuTo |
MALICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 3816)
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 3344)
Bypass execution policy to execute commands
- powershell.exe (PID: 1276)
Adds extension to the Windows Defender exclusion list
- powershell.exe (PID: 1276)
SUSPICIOUS
Reads the Internet Settings
- msiexec.exe (PID: 1884)
- msiexec.exe (PID: 684)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 3344)
The process executes Powershell scripts
- msiexec.exe (PID: 3344)
Script adds exclusion path to Windows Defender
- powershell.exe (PID: 1276)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 3344)
- powershell.exe (PID: 1276)
Powershell version downgrade attack
- powershell.exe (PID: 1276)
- powershell.exe (PID: 2072)
Script adds exclusion extension to Windows Defender
- powershell.exe (PID: 1276)
Application launched itself
- powershell.exe (PID: 1276)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 3344)
INFO
Checks supported languages
- msiexec.exe (PID: 3816)
- msiexec.exe (PID: 1884)
- msiexec.exe (PID: 684)
- msiexec.exe (PID: 3344)
- msiexec.exe (PID: 3316)
- wmpnscfg.exe (PID: 1696)
Reads the computer name
- msiexec.exe (PID: 3816)
- msiexec.exe (PID: 1884)
- msiexec.exe (PID: 684)
- msiexec.exe (PID: 3344)
- msiexec.exe (PID: 3316)
- wmpnscfg.exe (PID: 1696)
Reads the machine GUID from the registry
- msiexec.exe (PID: 3816)
- msiexec.exe (PID: 1884)
- msiexec.exe (PID: 684)
- msiexec.exe (PID: 3344)
- msiexec.exe (PID: 3316)
Drops the executable file immediately after the start
- msiexec.exe (PID: 2412)
- msiexec.exe (PID: 604)
Application launched itself
- msiexec.exe (PID: 3816)
- msiexec.exe (PID: 1884)
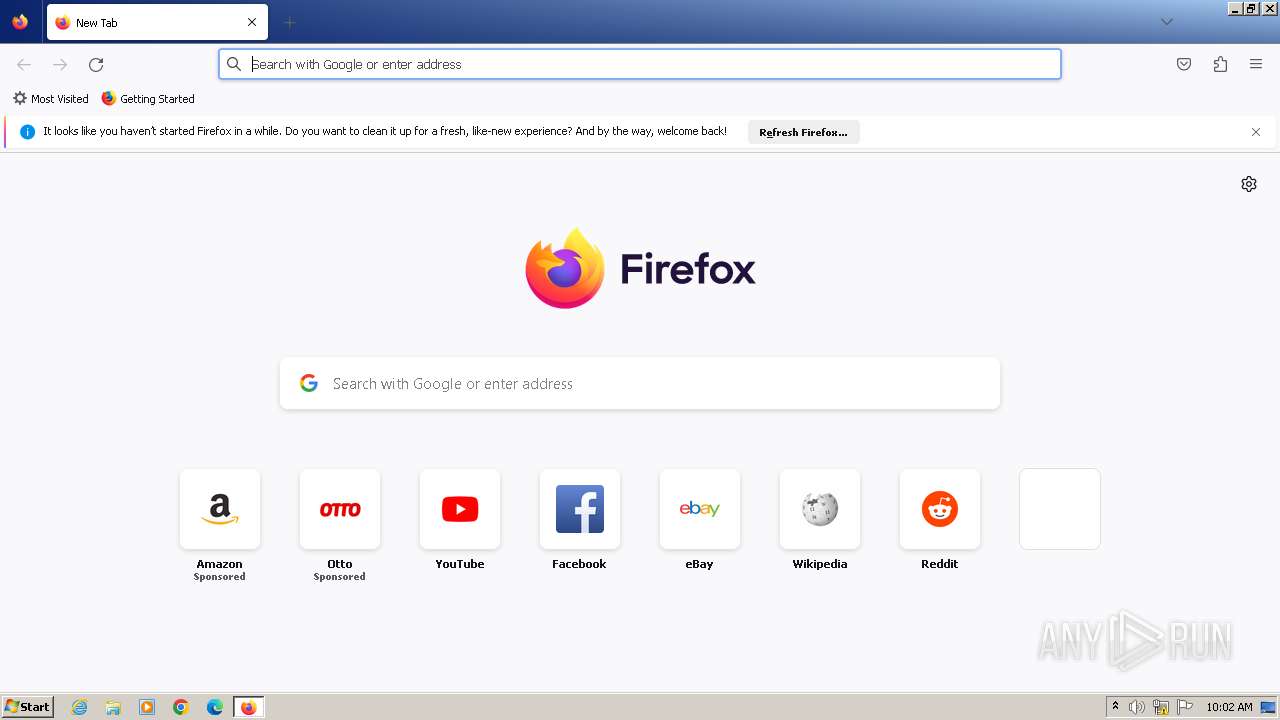
- firefox.exe (PID: 3736)
- firefox.exe (PID: 1984)
Create files in a temporary directory
- msiexec.exe (PID: 3816)
- msiexec.exe (PID: 3344)
Reads Environment values
- msiexec.exe (PID: 3344)
Manual execution by a user
- firefox.exe (PID: 1984)
- wmpnscfg.exe (PID: 1696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| LastPrinted: | 2009:12:11 11:47:44 |
|---|---|
| CreateDate: | 2009:12:11 11:47:44 |
| ModifyDate: | 2020:09:18 14:06:51 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {9FE10983-D7A2-4C66-A3B6-6C49C70386F7} |
| Words: | 2 |
| Subject: | Cheat Space |
| Author: | Cheat Space Inc. |
| LastModifiedBy: | - |
| Software: | Cheat Space |
| Template: | ;1033 |
| Comments: | This installer database contains the logic and data required to install Cheat Space. |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| Pages: | 200 |
Total processes
58
Monitored processes
19
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | "C:\Windows\system32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Cheat.Space.1.4.3.msi" | C:\Windows\System32\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 684 | C:\Windows\system32\MsiExec.exe -Embedding A09917CFC451F488A715A174D056B263 C | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 888 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3736.5.1494924843\1229622869" -childID 4 -isForBrowser -prefsHandle 3992 -prefMapHandle 3932 -prefsLen 29209 -prefMapSize 244195 -jsInitHandle 884 -jsInitLen 240908 -parentBuildID 20230710165010 -appDir "C:\Program Files\Mozilla Firefox\browser" - {57f297ea-53ae-4d37-a01b-e57dcf1b17e4} 3736 "\\.\pipe\gecko-crash-server-pipe.3736" 3644 213386d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 1276 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss7650.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msi763D.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scr764E.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scr764F.txt" -propSep " :<->: " -testPrefix "_testValue." | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3736.0.887880372\810957678" -parentBuildID 20230710165010 -prefsHandle 1104 -prefMapHandle 1096 -prefsLen 28523 -prefMapSize 244195 -appDir "C:\Program Files\Mozilla Firefox\browser" - {6efd28aa-158b-46e1-938d-3de48576acc6} 3736 "\\.\pipe\gecko-crash-server-pipe.3736" 1208 d2a7350 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 1 Version: 115.0.2 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1884 | C:\Windows\system32\MsiExec.exe -Embedding 431557ADC786518C3481B20E0EA32E0C C | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1984 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 115.0.2 Modules
| |||||||||||||||
| 2072 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Command "& { & 'Add-MpPreference' -ExclusionExtension '.dll', '.exe' -ExclusionPath C: -Force }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2412 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Cheat.Space.1.4.3.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1602 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
13 170
Read events
12 993
Write events
161
Delete events
16
Modification events
| (PID) Process: | (1884) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1884) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1884) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1884) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1276) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2072) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3816) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MUI\StringCacheSettings |
| Operation: | write | Name: | StringCacheGeneration |
Value: 383 | |||
| (PID) Process: | (3816) msiexec.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3816) msiexec.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\17F |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3816) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | delete value | Name: | C:\Config.Msi\20745b.rbs |
Value: 31073542 | |||
Executable files
21
Suspicious files
103
Text files
25
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3344 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msi763D.txt | — | |
MD5:— | SHA256:— | |||
| 3344 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scr764E.ps1 | — | |
MD5:— | SHA256:— | |||
| 3344 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scr764F.txt | — | |
MD5:— | SHA256:— | |||
| 3344 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pss7650.ps1 | — | |
MD5:— | SHA256:— | |||
| 604 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI6A66.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
| 604 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI6B55.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
| 604 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI6AC5.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
| 2412 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI68A1.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
| 604 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI6AF6.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
| 604 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI6AD6.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
24
DNS requests
64
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3736 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | text | 90 b | unknown |
3736 | firefox.exe | POST | 200 | 184.24.77.67:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
3736 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | text | 8 b | unknown |
3736 | firefox.exe | POST | 200 | 184.24.77.67:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
3736 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3 | unknown | binary | 472 b | unknown |
3736 | firefox.exe | POST | 200 | 13.32.26.76:80 | http://ocsp.r2m02.amazontrust.com/ | unknown | binary | 471 b | unknown |
3736 | firefox.exe | POST | 200 | 184.24.77.67:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
3736 | firefox.exe | POST | 200 | 184.24.77.67:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
3736 | firefox.exe | POST | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3 | unknown | binary | 472 b | unknown |
3736 | firefox.exe | POST | 200 | 184.24.77.67:80 | http://r3.o.lencr.org/ | unknown | binary | 503 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3736 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
3736 | firefox.exe | 34.117.237.239:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
3736 | firefox.exe | 34.233.191.125:443 | spocs.getpocket.com | AMAZON-AES | US | unknown |
3736 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | unknown |
3736 | firefox.exe | 184.24.77.67:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
3736 | firefox.exe | 142.250.184.234:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| shared |
proxyserverecs-1736642167.us-east-1.elb.amazonaws.com |
| shared |
firefox.settings.services.mozilla.com |
| whitelisted |
r3.o.lencr.org |
| shared |
prod.remote-settings.prod.webservices.mozgcp.net |
| whitelisted |