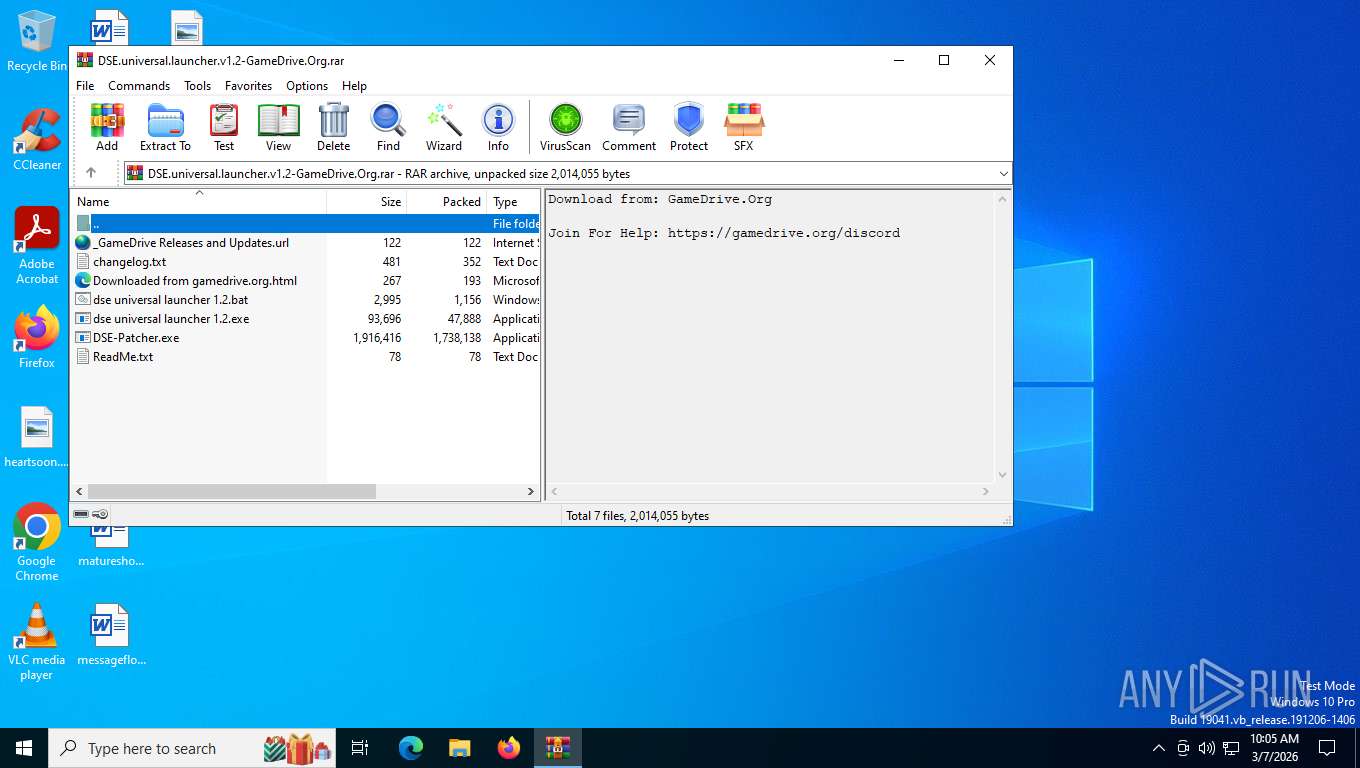
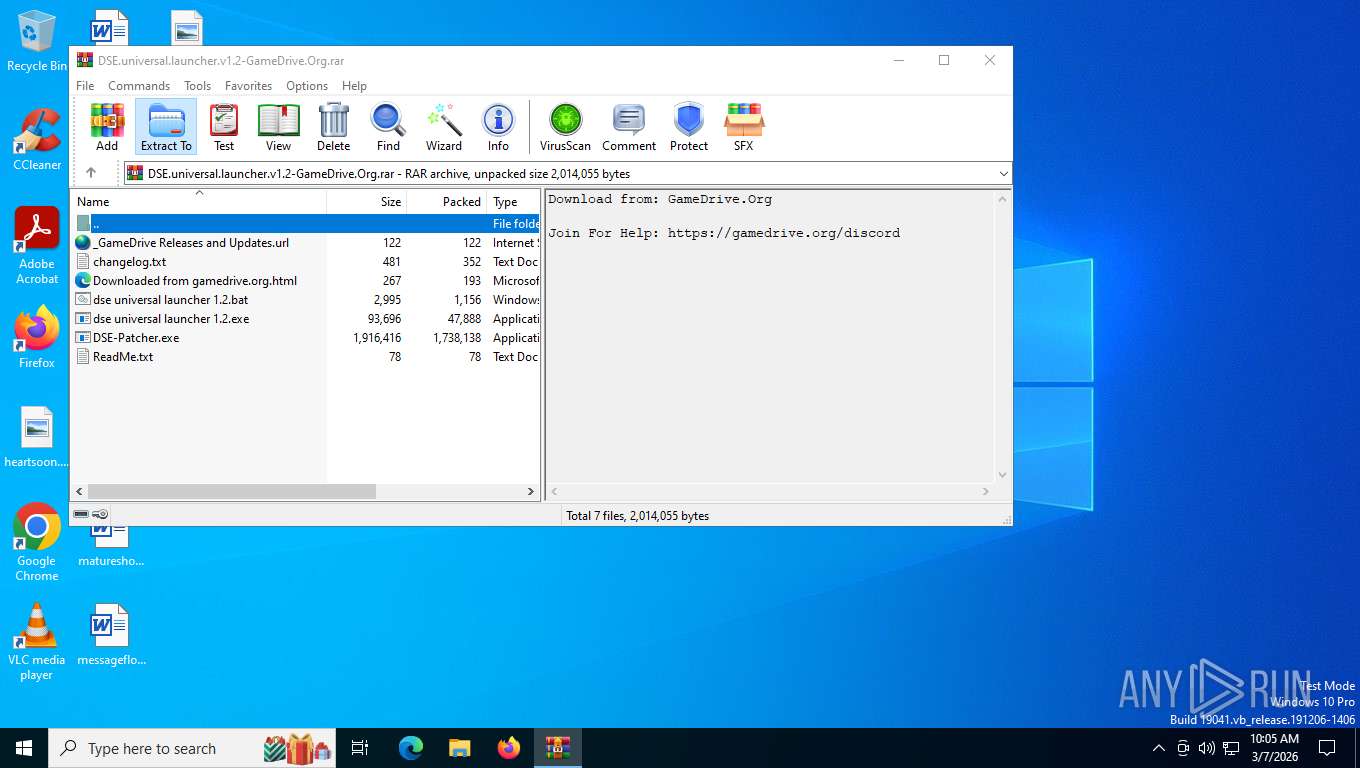
| File name: | DSE.universal.launcher.v1.2-GameDrive.Org.rar |
| Full analysis: | https://app.any.run/tasks/9893de03-df00-4118-91ff-dca1e27a9905 |
| Verdict: | Malicious activity |
| Analysis date: | March 07, 2026, 15:05:39 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | B0DC34A77B62496E72E27A82C28777C7 |
| SHA1: | 4C47D11D4BD236A2FDA3C9A0D7811B6E02F4566E |
| SHA256: | 390444EB9341F3B44E9D5C81ADF3D284E021DEEA8AC9C07D7D37E4F103227602 |
| SSDEEP: | 98304:9LzM6Oberah+nOYQr6QhEBz+G8uWSSFVokz27FkD4MtRHazJiMJm1CinQVyxbTp+:Bwm |
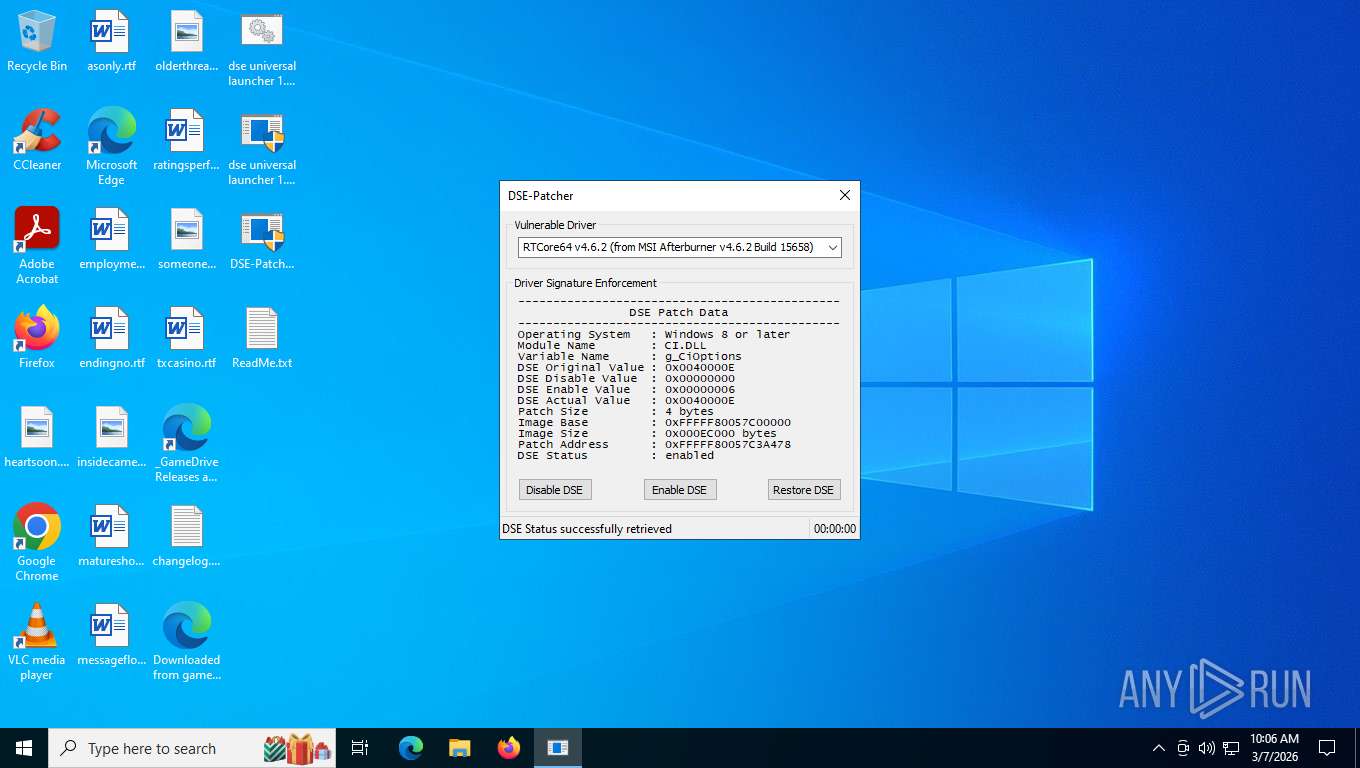
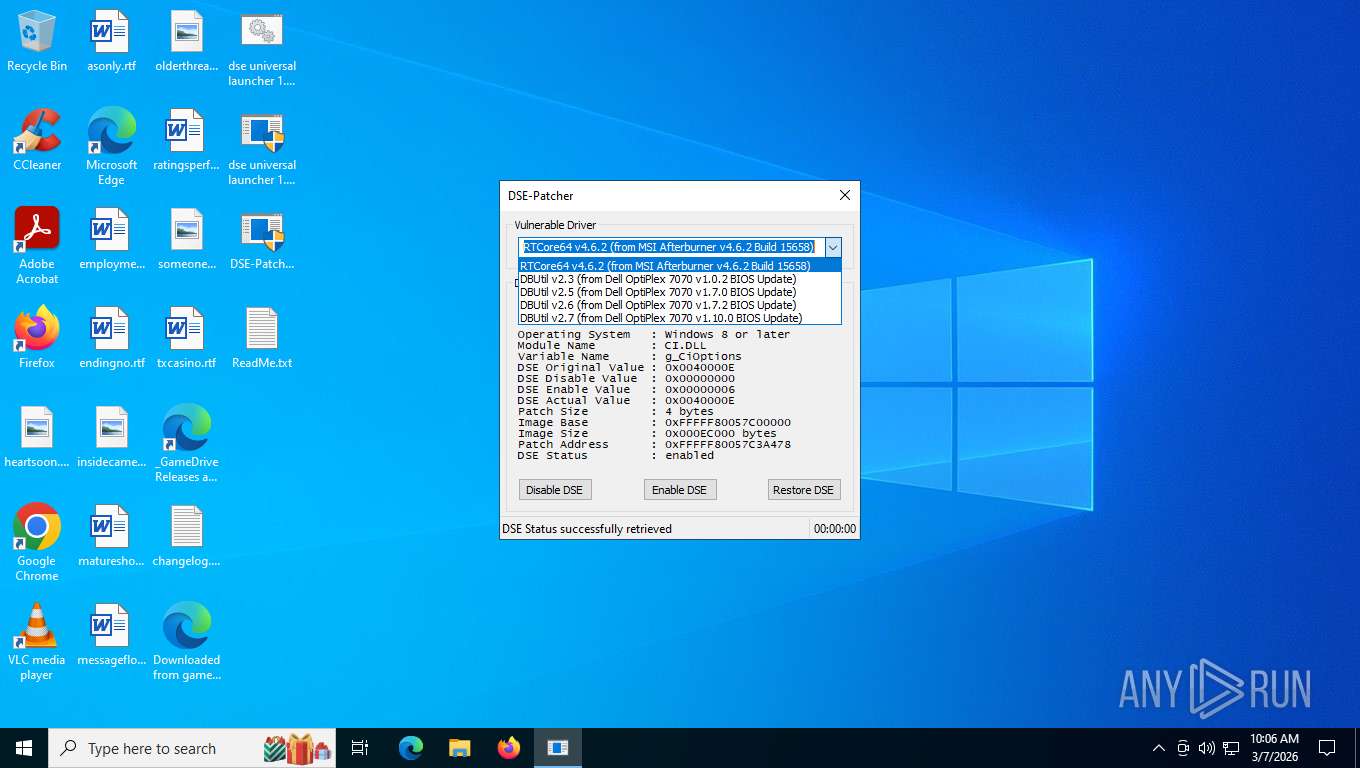
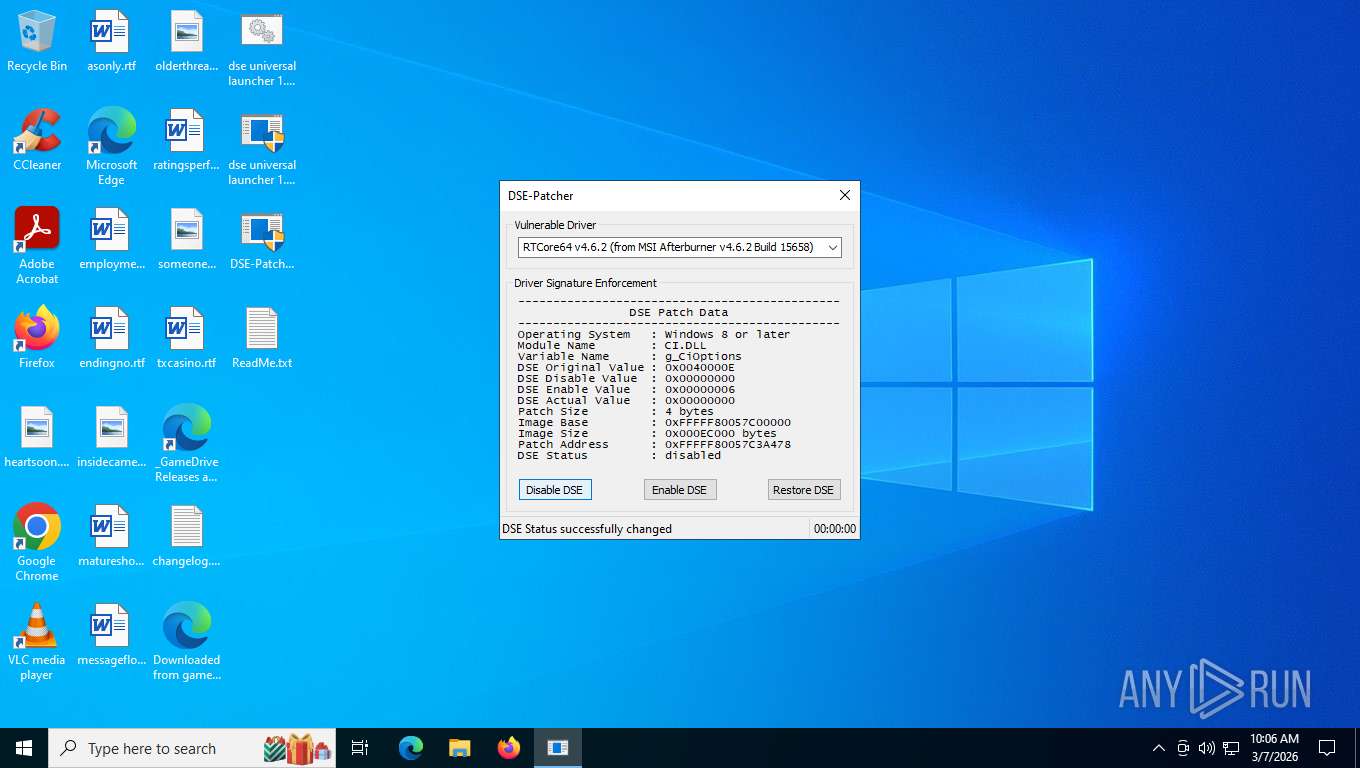
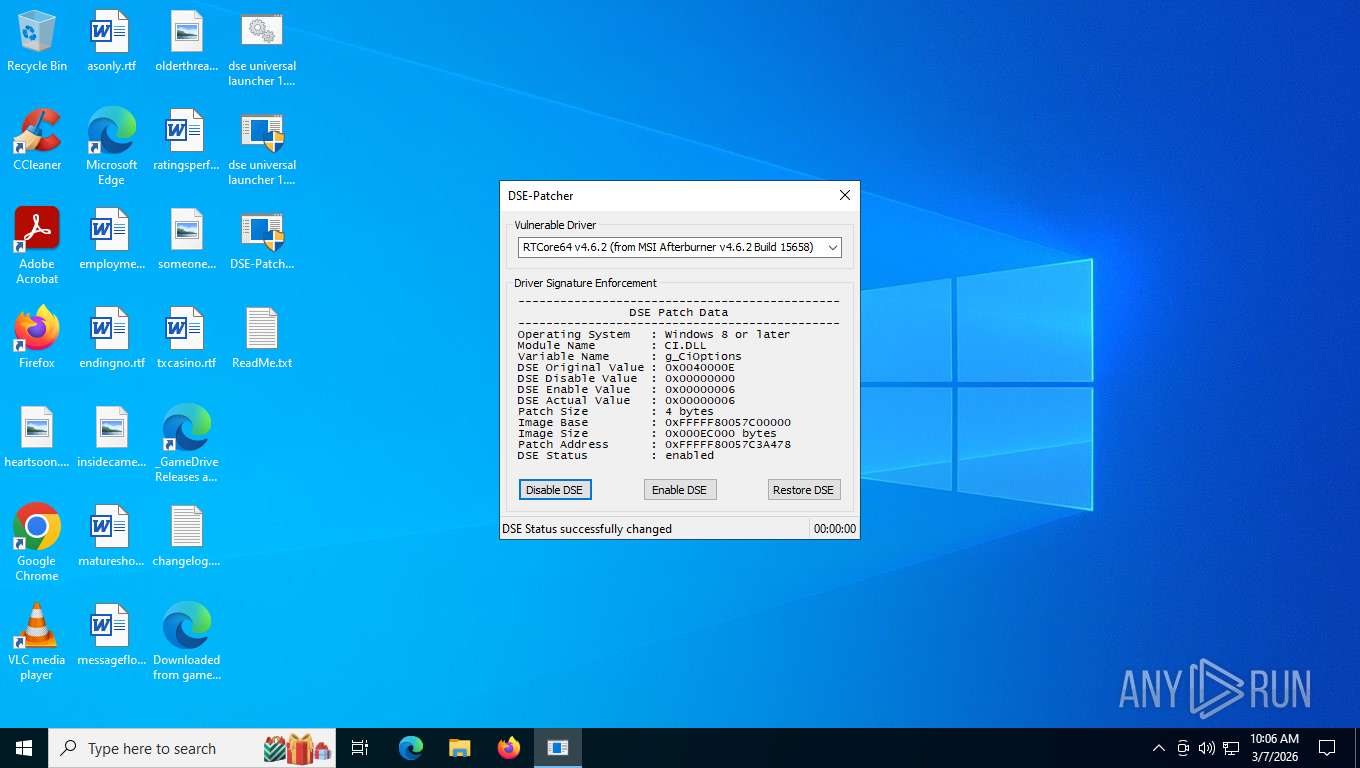
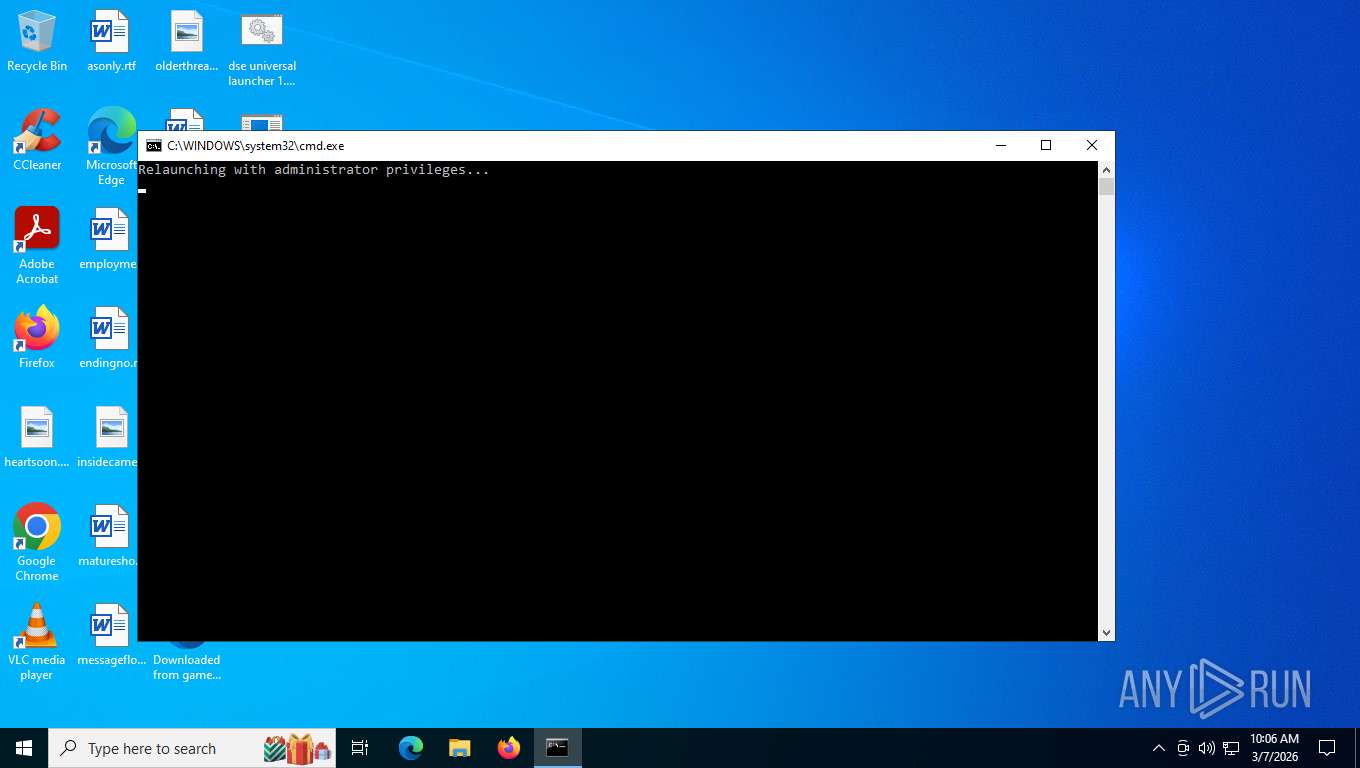
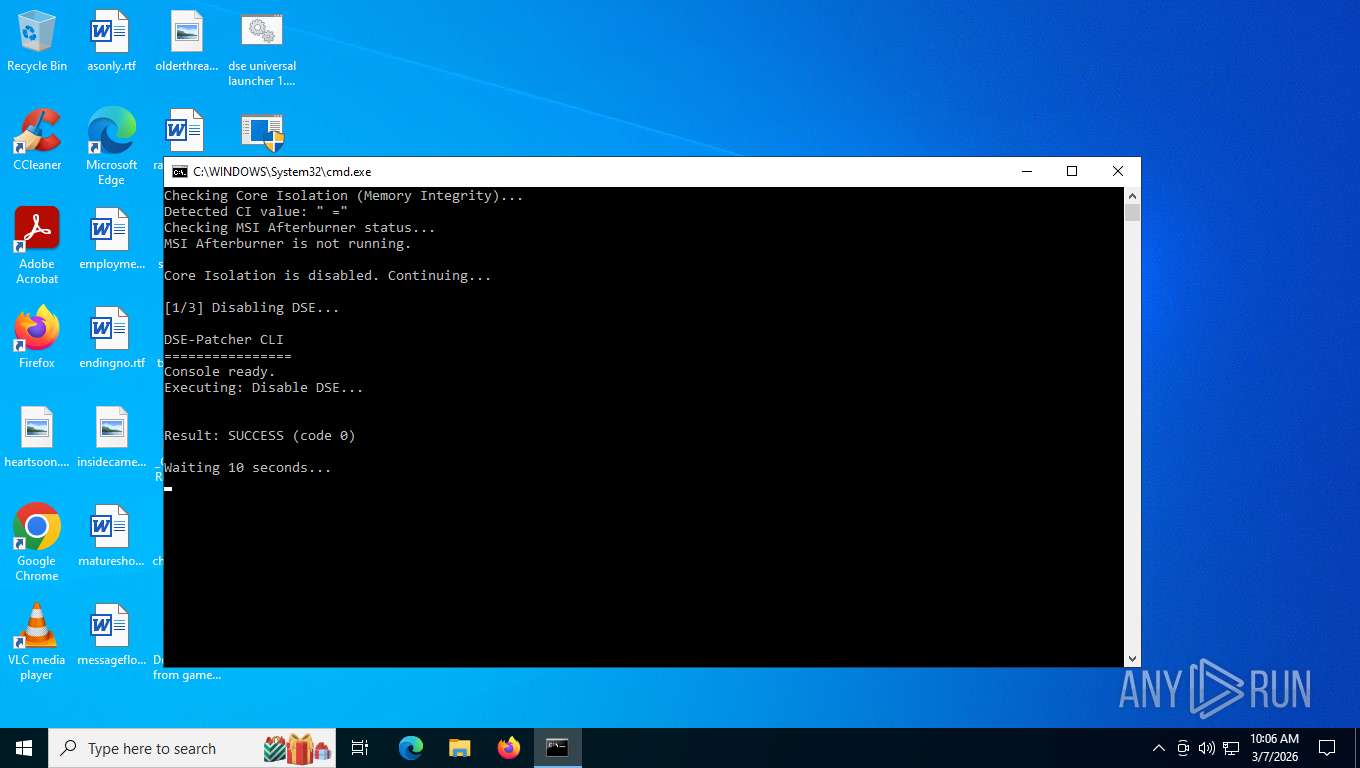
MALICIOUS
Vulnerable driver has been detected
- DSE-Patcher.exe (PID: 6720)
- DSE-Patcher.exe (PID: 6936)
SUSPICIOUS
Creates or modifies Windows services
- DSE-Patcher.exe (PID: 6720)
- DSE-Patcher.exe (PID: 6936)
Drops a system driver (possible attempt to evade defenses)
- DSE-Patcher.exe (PID: 6720)
- DSE-Patcher.exe (PID: 6936)
Executable content was dropped or overwritten
- DSE-Patcher.exe (PID: 6720)
- DSE-Patcher.exe (PID: 6936)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 9184)
- net.exe (PID: 6212)
- cmd.exe (PID: 5548)
- net.exe (PID: 7812)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 9184)
Starts process via Powershell
- powershell.exe (PID: 5716)
Executing commands from a ".bat" file
- powershell.exe (PID: 5716)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 5716)
- cmd.exe (PID: 5548)
Hides command output
- cmd.exe (PID: 5708)
Application launched itself
- cmd.exe (PID: 5548)
Get information on the list of running processes
- cmd.exe (PID: 5548)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5548)
INFO
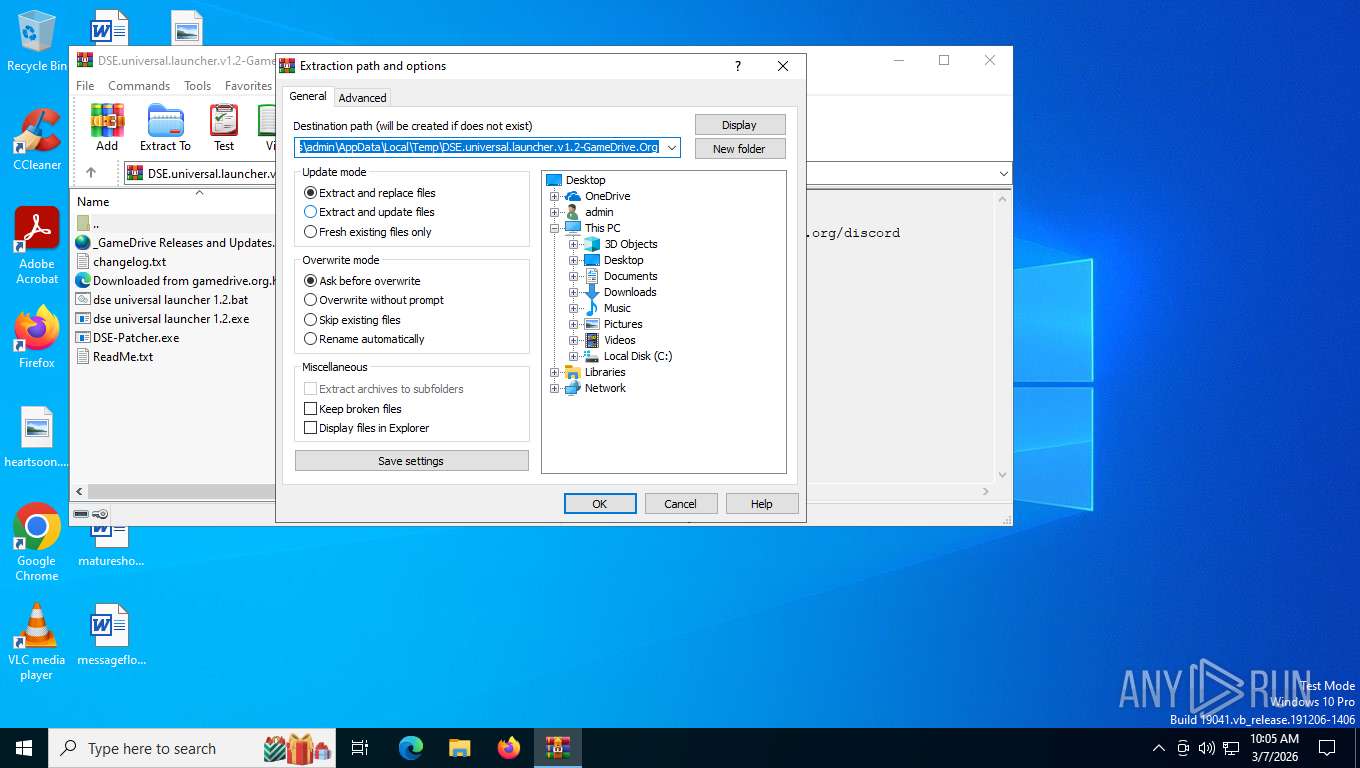
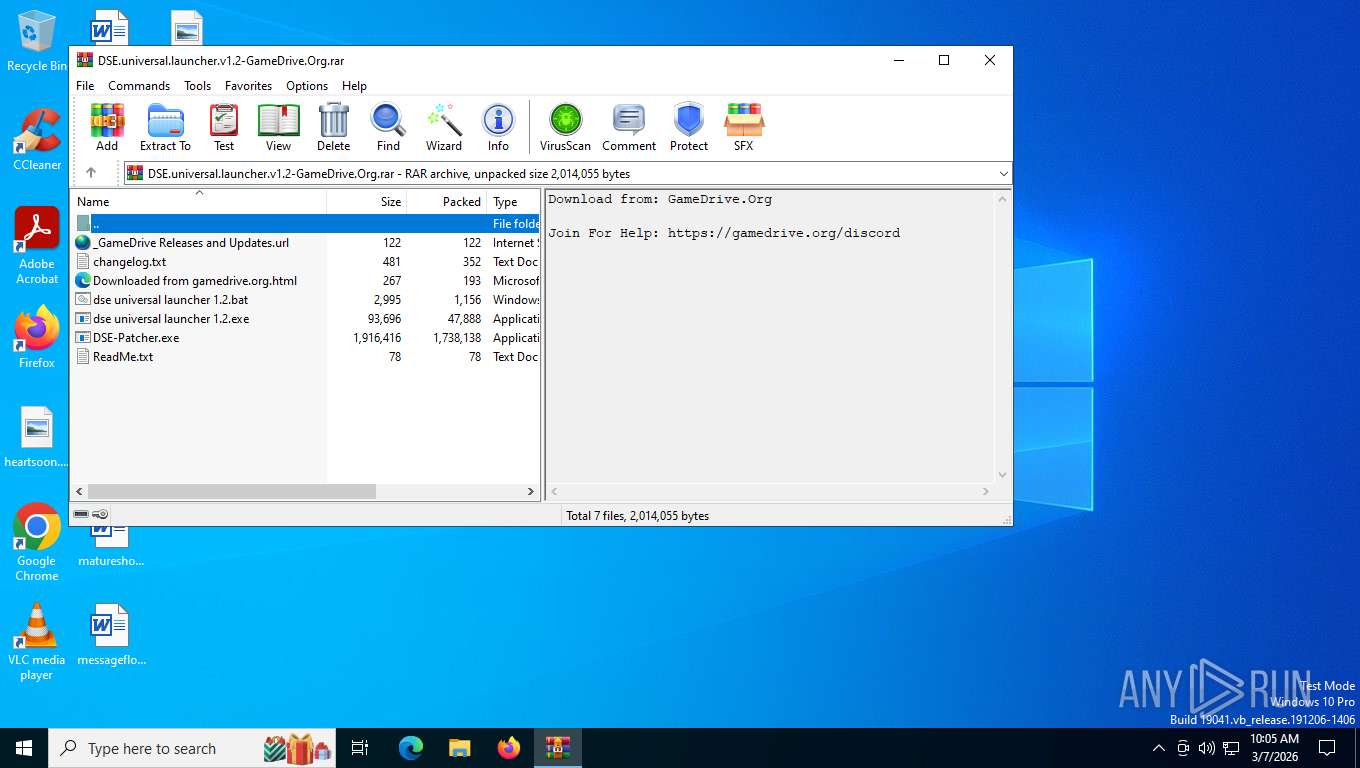
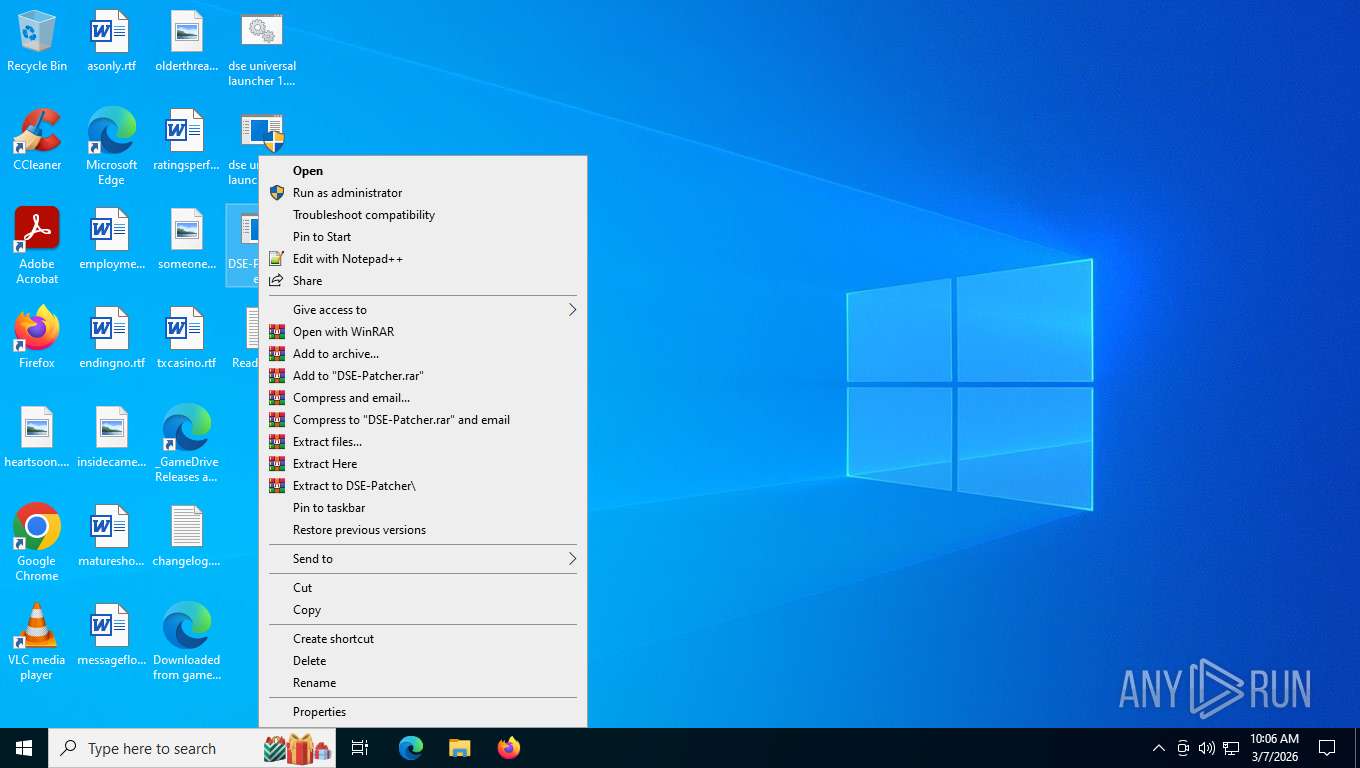
Generic archive extractor
- WinRAR.exe (PID: 8316)
Local mutex for internet shortcut management
- WinRAR.exe (PID: 8316)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8316)
Manual execution by a user
- DSE-Patcher.exe (PID: 6720)
- cmd.exe (PID: 9184)
Reads the computer name
- DSE-Patcher.exe (PID: 6720)
- DSE-Patcher.exe (PID: 6936)
The sample compiled with english language support
- WinRAR.exe (PID: 8316)
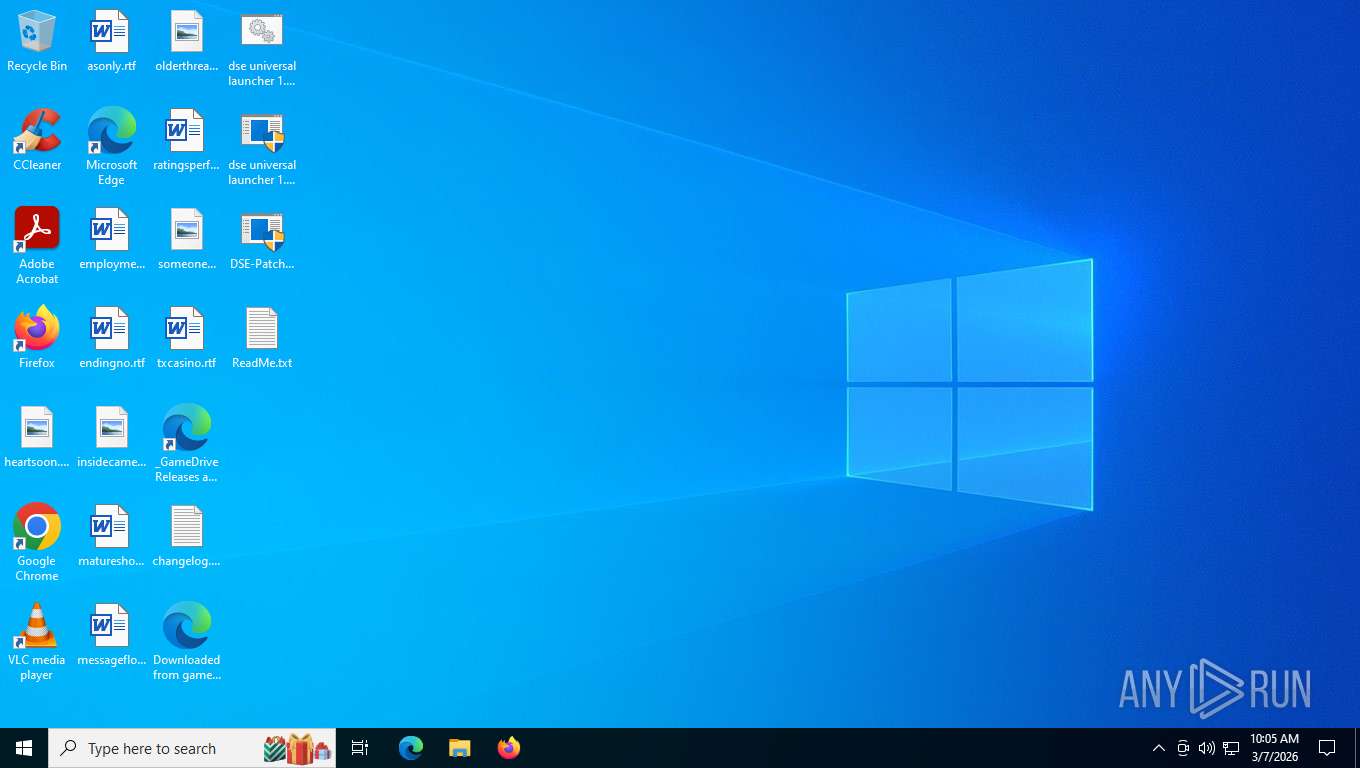
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8316)
Checks supported languages
- DSE-Patcher.exe (PID: 6720)
- DSE-Patcher.exe (PID: 6936)
Search a value from a registry key
- reg.exe (PID: 5284)
- cmd.exe (PID: 5708)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|
Total processes
166
Monitored processes
19
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5284 | reg query "HKLM\SYSTEM\CurrentControlSet\Control\DeviceGuard\Scenarios\HypervisorEnforcedCodeIntegrity" /v Enabled | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5544 | find /I "MSIAfterburner.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5548 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Desktop\dse universal launcher 1.2.bat" | C:\Windows\System32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5708 | C:\WINDOWS\system32\cmd.exe /c reg query "HKLM\SYSTEM\CurrentControlSet\Control\DeviceGuard\Scenarios\HypervisorEnforcedCodeIntegrity" /v Enabled 2>nul | find /i "Enabled" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5716 | powershell -Command "Start-Process 'C:\Users\admin\Desktop\dse universal launcher 1.2.bat' -Verb RunAs" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6212 | net session | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6396 | C:\WINDOWS\system32\net1 session | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6404 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6440 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6720 | "C:\Users\admin\Desktop\DSE-Patcher.exe" | C:\Users\admin\Desktop\DSE-Patcher.exe | explorer.exe | ||||||||||||
User: admin Company: Kai Schtrom Integrity Level: HIGH Description: DSE-Patcher Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
10 494
Read events
10 451
Write events
30
Delete events
13
Modification events
| (PID) Process: | (8316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (8316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (8316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (8316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\DSE.universal.launcher.v1.2-GameDrive.Org.rar | |||
| (PID) Process: | (8316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8316) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
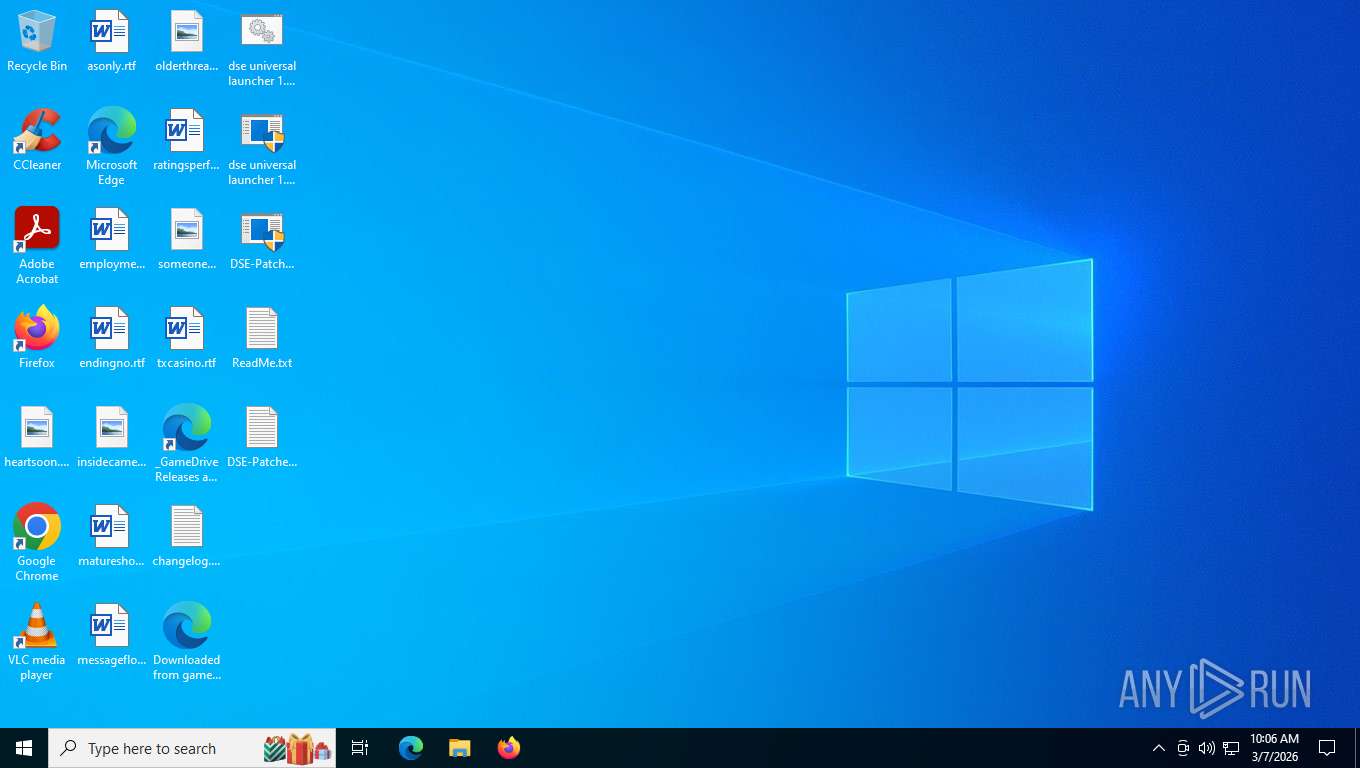
Executable files
4
Suspicious files
2
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5716 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gxxn4i3x.thi.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8316 | WinRAR.exe | C:\Users\admin\Desktop\_GameDrive Releases and Updates.url | binary | |
MD5:C067CE404BA30707B6C9941E3FE8485D | SHA256:6E66FCBD786A838FE5159F96C01BBDA836DB04C80D5A19B705D602EEF545EC31 | |||
| 8316 | WinRAR.exe | C:\Users\admin\Desktop\dse universal launcher 1.2.exe | executable | |
MD5:FF9E72F6A32DC8E91E9B60D17DC57F58 | SHA256:C80E0C7337049DBE0E20D9071767DB5335D394C342D5BA2A75EA45FFAA0DEA86 | |||
| 8316 | WinRAR.exe | C:\Users\admin\Desktop\DSE-Patcher.exe | executable | |
MD5:EBB746D8A79E9E178A1E90716FAE4012 | SHA256:4243A07A064A798FBE49A4B33E667530038D78A4544CC0089900E3A2F470340F | |||
| 8316 | WinRAR.exe | C:\Users\admin\Desktop\Downloaded from gamedrive.org.html | html | |
MD5:1B8148285257CBEED17D507CC454493D | SHA256:02AD65872EB18023256C3058A52DF8649A31025932CBACEBFC80A2B621B12176 | |||
| 6720 | DSE-Patcher.exe | C:\Users\admin\Desktop\RTCore64.sys | executable | |
MD5:2D8E4F38B36C334D0A32A7324832501D | SHA256:01AA278B07B58DC46C84BD0B1B5C8E9EE4E62EA0BF7A695862444AF32E87F1FD | |||
| 8316 | WinRAR.exe | C:\Users\admin\Desktop\changelog.txt | text | |
MD5:EDD5477F8511A2E04EE4F8F66F6BCCC4 | SHA256:03F3950BD048039082416BBE0FEB4954949900BDF8ED5952BCC28F94FFF1B048 | |||
| 5716 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zow3d3l3.2va.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8316 | WinRAR.exe | C:\Users\admin\Desktop\ReadMe.txt | text | |
MD5:B50059A02729804514BD4599F0013F4F | SHA256:2D1BFA0EABF4DDFB4061359B01CAA8FA690AF1EDA954027C3C556F801406D27D | |||
| 5716 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:68CE417F7261158046A7DAFD714E19C0 | SHA256:10801C6ED6FDC445263320D47810BBA1A1DFE5FA56BEACED7F3B6C0C5DF48EA9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
23
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
3208 | svchost.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 959 b | whitelisted |
356 | svchost.exe | POST | 200 | 40.126.32.136:443 | https://login.live.com/RST2.srf | US | xml | 1.24 Kb | whitelisted |
— | — | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | US | binary | 313 b | whitelisted |
356 | svchost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | US | binary | 471 b | whitelisted |
356 | svchost.exe | POST | 400 | 40.126.32.136:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
6272 | SIHClient.exe | GET | 304 | 74.179.77.204:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
6272 | SIHClient.exe | GET | 200 | 135.232.92.97:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
6272 | SIHClient.exe | GET | 200 | 74.179.77.204:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
3208 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7240 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.241.207:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 172.66.2.5:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
356 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3208 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |