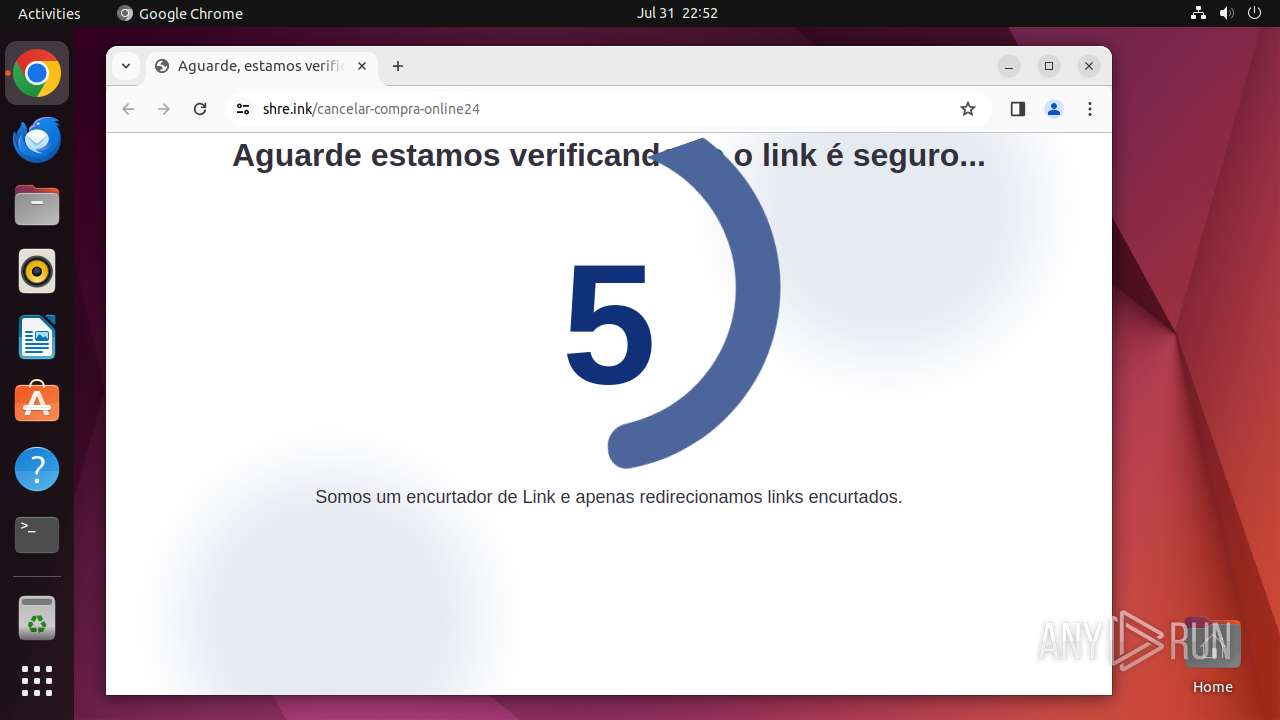
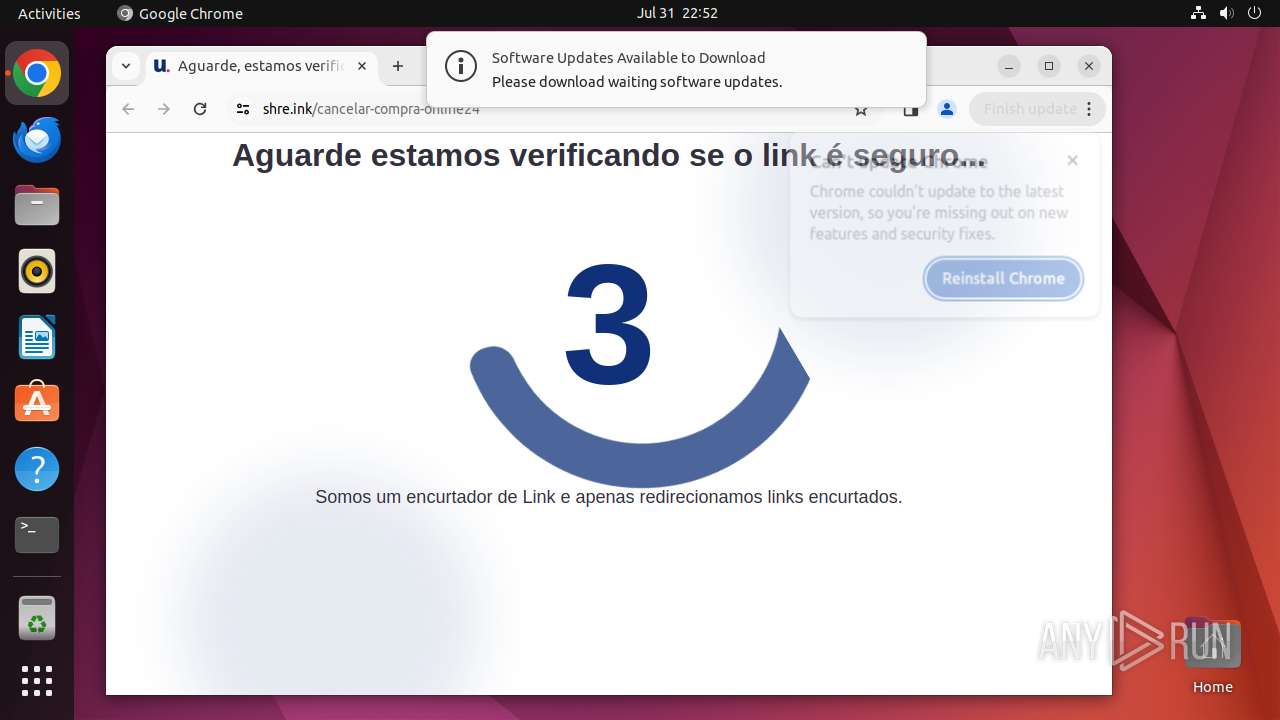
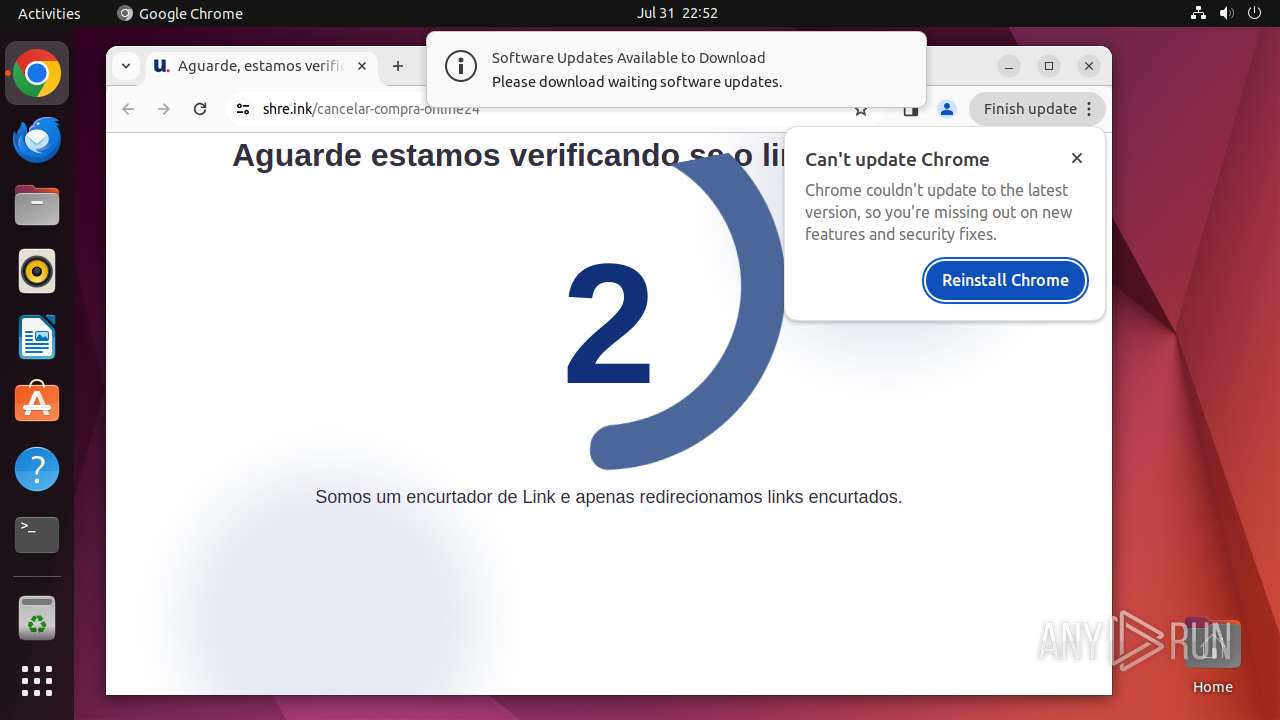
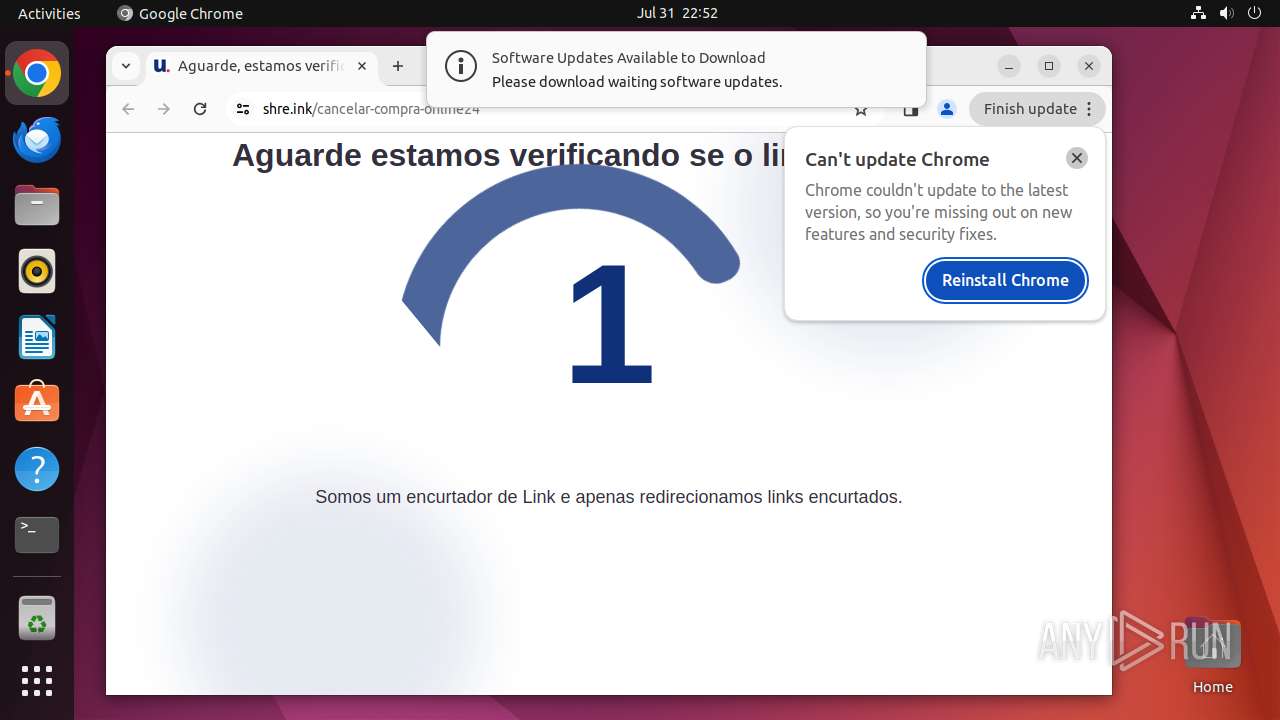
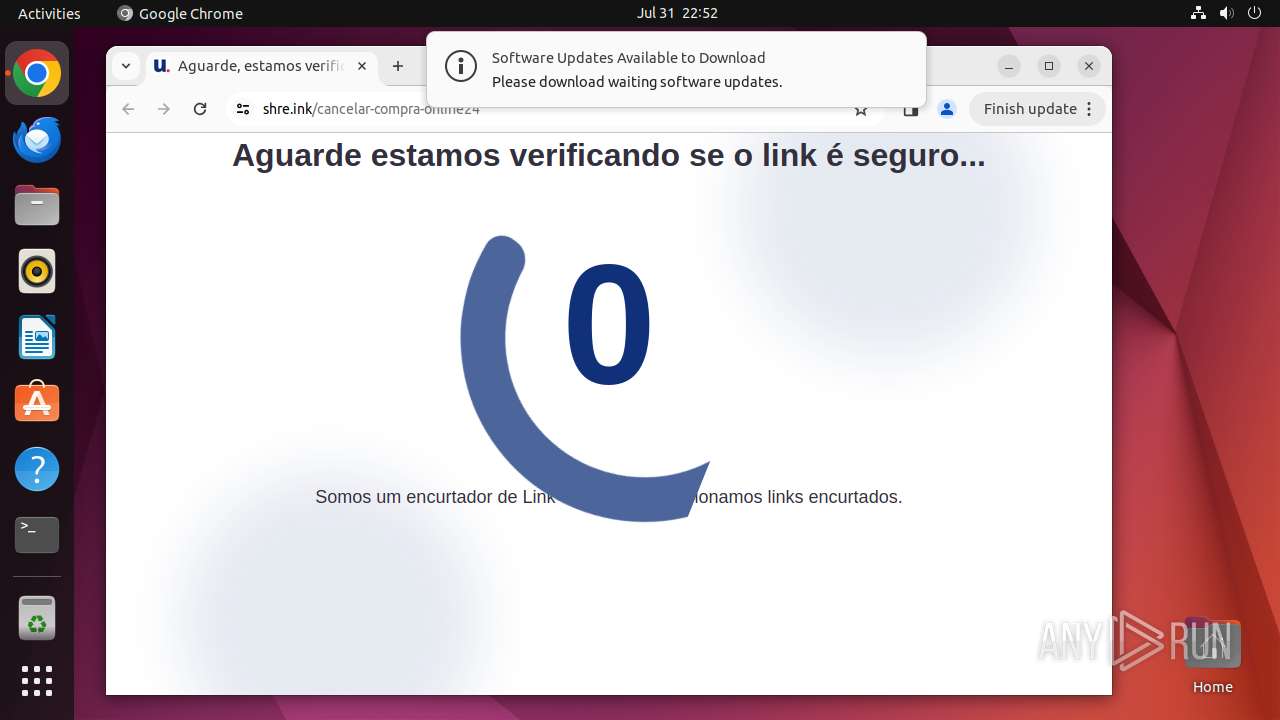
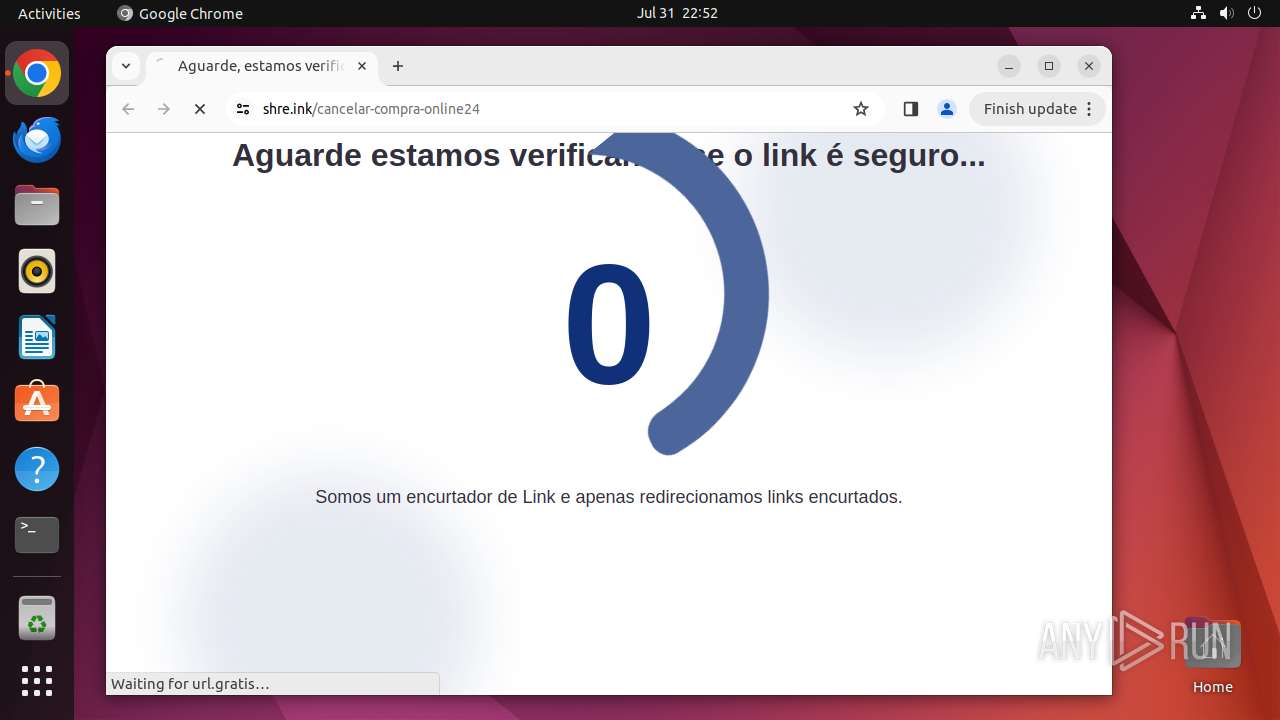
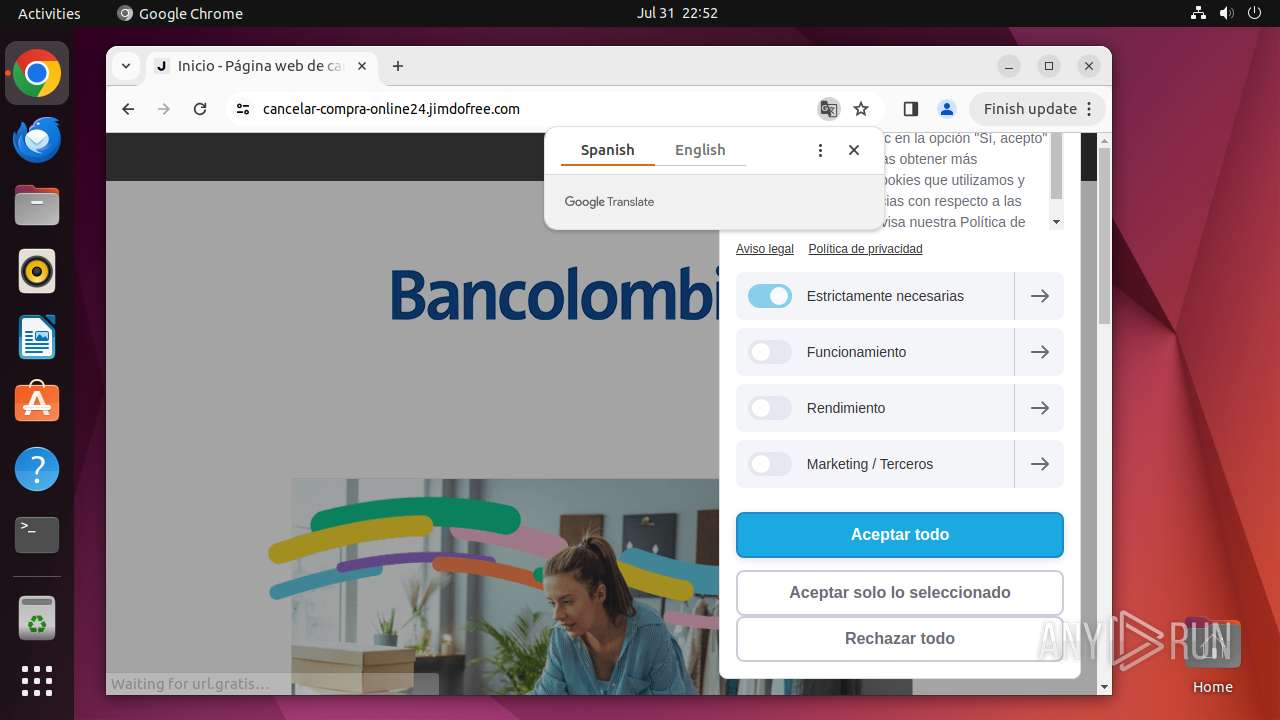
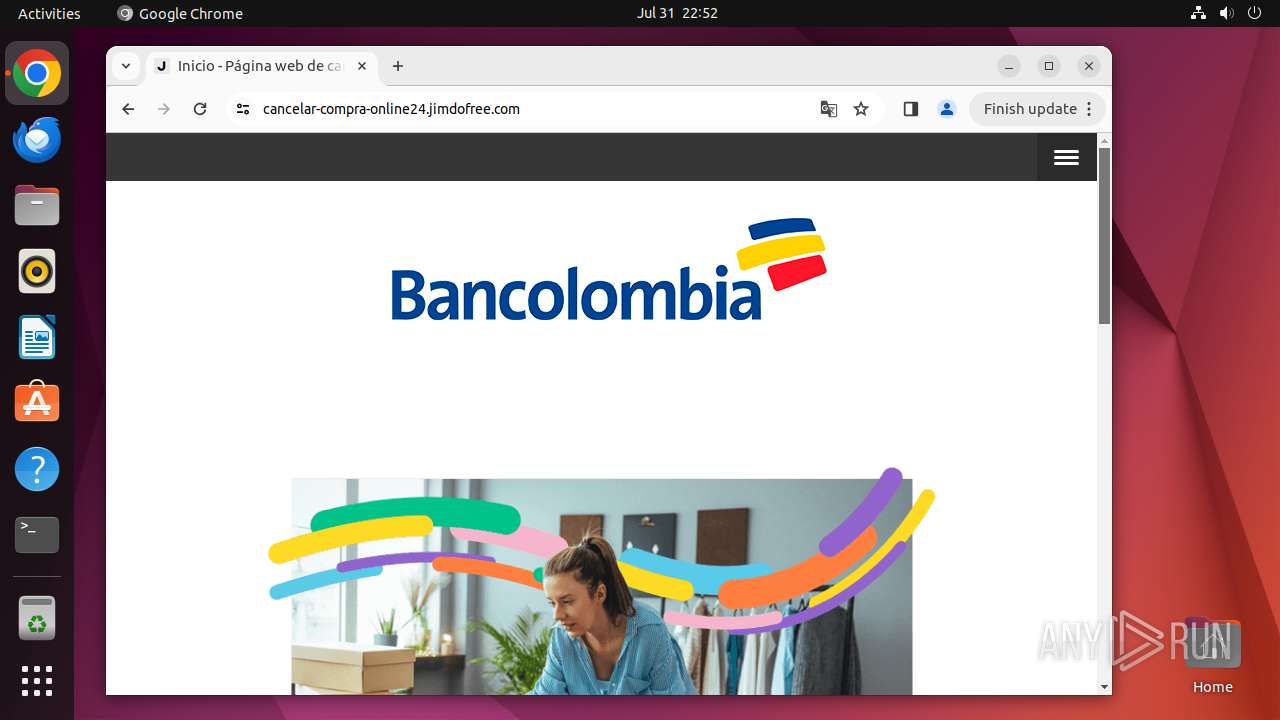
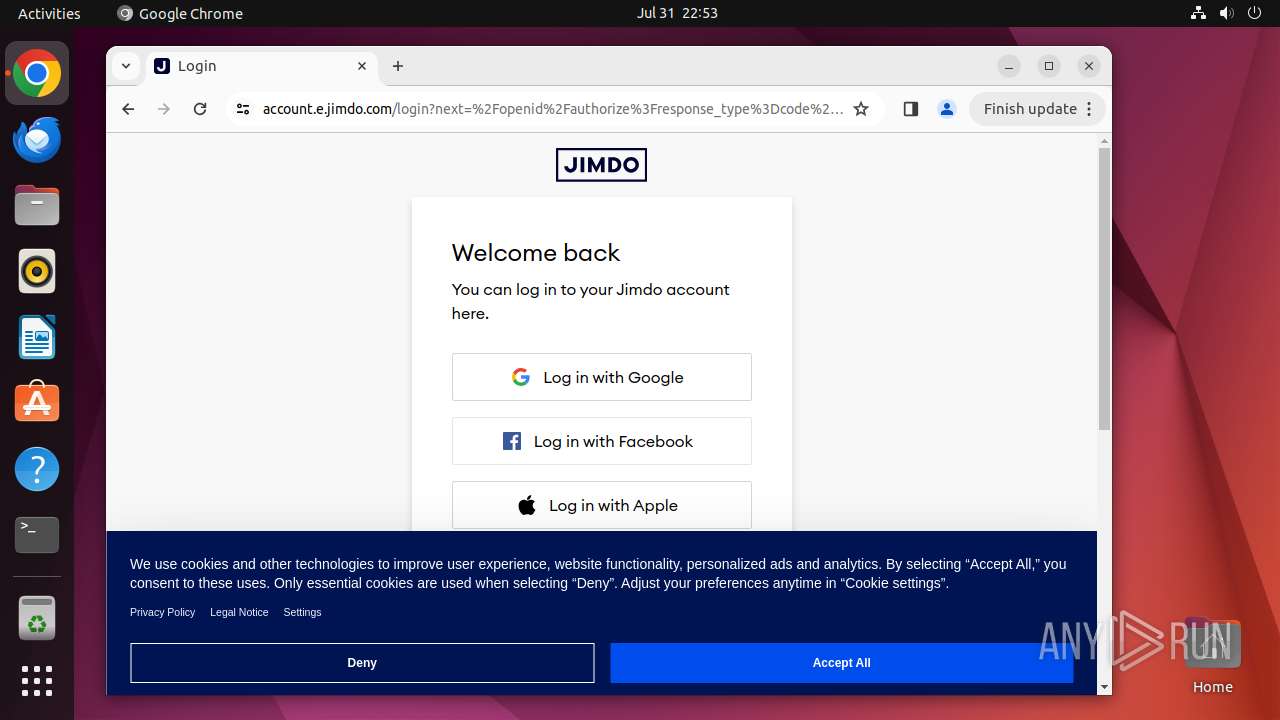
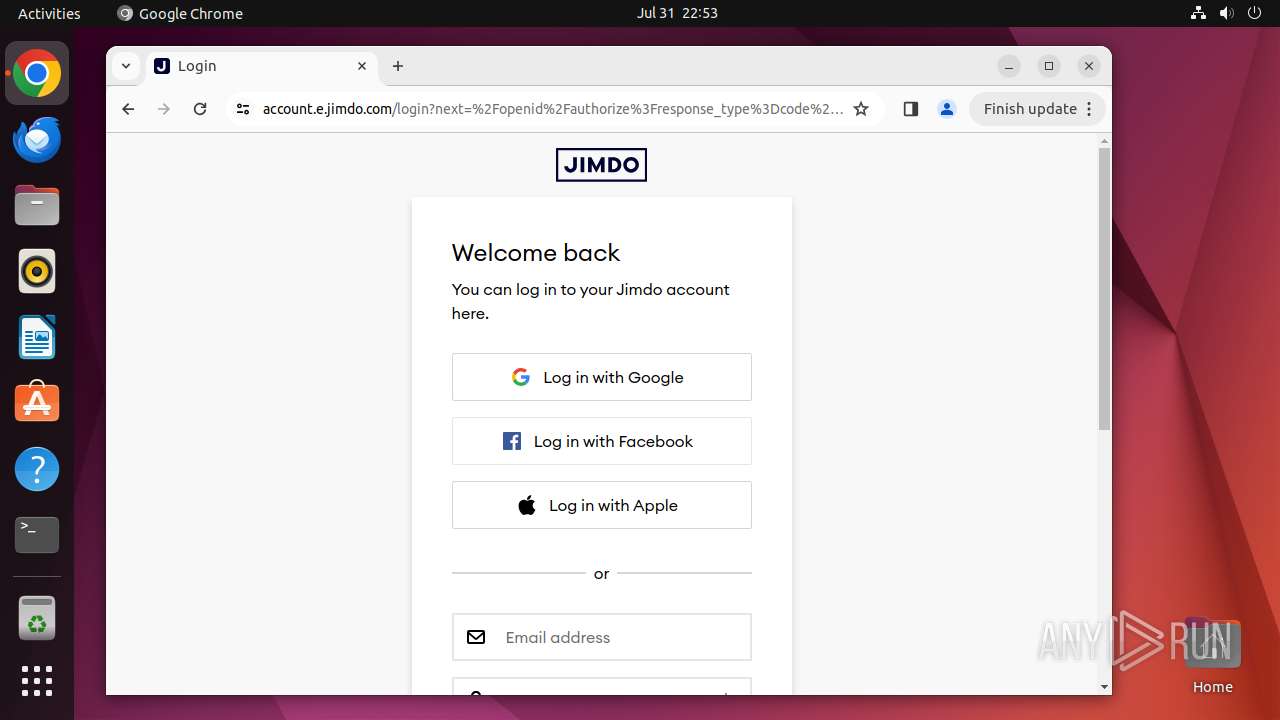
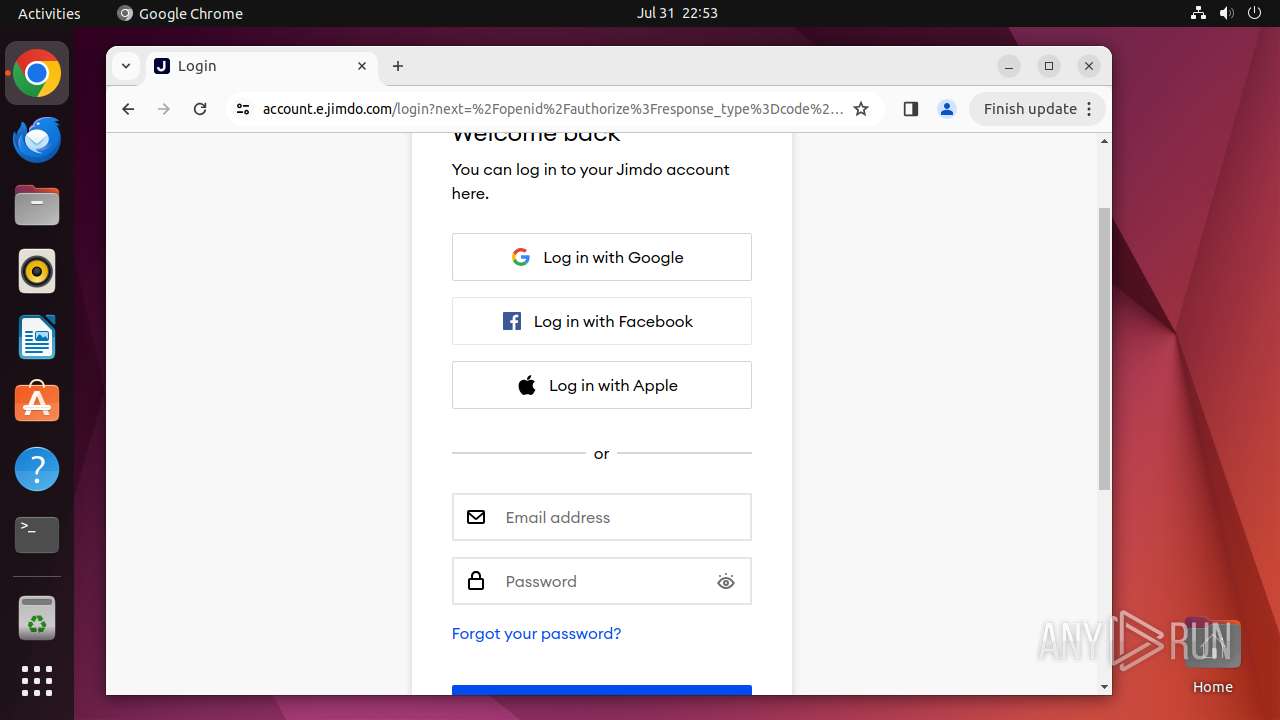
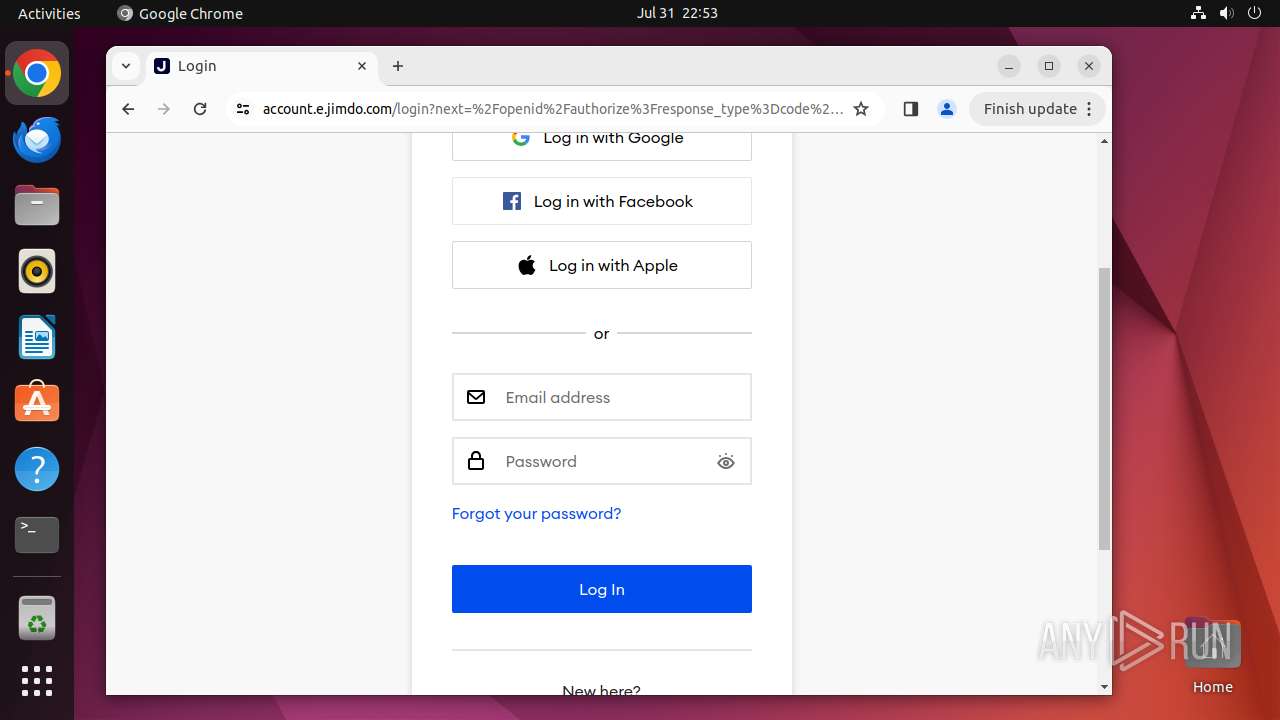
| URL: | https://shre.ink/cancelar-compra-online24 |
| Full analysis: | https://app.any.run/tasks/e345c5e7-370e-41ff-9aa3-8b5acf1ef65a |
| Verdict: | Malicious activity |
| Analysis date: | July 31, 2024, 21:52:12 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| MD5: | AA1DF0B51F20BD94231FFA3F43D90B26 |
| SHA1: | 2D573CD77A5C9ABB23446F9FAB54B06BF93C356A |
| SHA256: | 38CEB653E32CFD49F41370D01055F9F75CC790F4D23B4B72EA7304C58101CE2A |
| SSDEEP: | 3:N8AeKOGszKEC:2AupKP |
MALICIOUS
PHISHING has been detected (SURICATA)
- systemd-resolved (PID: 425)
SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
300
Monitored processes
88
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 425 | /lib/systemd/systemd-resolved | /usr/lib/systemd/systemd-resolved | systemd | |
User: systemd-resolve Integrity Level: UNKNOWN | ||||
| 12921 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome https://shre\.ink/cancelar-compra-online24 " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 12922 | sudo -iu user google-chrome https://shre.ink/cancelar-compra-online24 | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN | ||||
| 12923 | /usr/bin/google-chrome https://shre.ink/cancelar-compra-online24 | /opt/google/chrome/chrome | sudo | |
User: user Integrity Level: UNKNOWN | ||||
| 12924 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12925 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12926 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12927 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 12928 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 12929 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
Executable files
0
Suspicious files
98
Text files
2
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 12923 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12923 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 12923 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 12923 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12923 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 12923 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 12923 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 12923 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 12923 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 12966 | chrome | /home/user/.cache/mesa_shader_cache/index | koa | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
56
DNS requests
138
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.49:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.190.18:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | unknown |
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.49:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | unknown |
— | — | 195.181.175.40:443 | odrs.gnome.org | Datacamp Limited | DE | unknown |
— | — | 142.250.185.195:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
12923 | chrome | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | unknown |
— | — | 142.250.186.74:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
— | — | 54.87.217.210:443 | shre.ink | AMAZON-AES | US | unknown |
— | — | 151.101.193.91:443 | google-ohttp-relay-safebrowsing.fastly-edge.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
shre.ink |
| unknown |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
www.googletagmanager.com |
| whitelisted |
scripts.cleverwebserver.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
425 | systemd-resolved | Misc activity | ET INFO DNS Query to Online Application Hosting Domain (glitch .me) |
425 | systemd-resolved | Misc activity | ET INFO DNS Query to Online Application Hosting Domain (glitch .me) |
425 | systemd-resolved | Possible Social Engineering Attempted | ET HUNTING Suspicious Glitch Hosted DNS Request - Possible Phishing Landing |
425 | systemd-resolved | Possible Social Engineering Attempted | ET HUNTING Suspicious Glitch Hosted DNS Request - Possible Phishing Landing |
— | — | Misc activity | ET INFO Observed Online Application Hosting Domain (glitch .me in TLS SNI) |
— | — | Misc activity | ET INFO Observed Online Application Hosting Domain (glitch .me in TLS SNI) |
— | — | Possible Social Engineering Attempted | ET HUNTING Suspicious Glitch Hosted TLS SNI Request - Possible Phishing Landing |
— | — | Possible Social Engineering Attempted | ET HUNTING Suspicious Glitch Hosted TLS SNI Request - Possible Phishing Landing |
— | — | Misc activity | ET INFO Observed Online Application Hosting Domain (glitch .me in TLS SNI) |
425 | systemd-resolved | Misc activity | ET INFO DNS Query to Online Application Hosting Domain (glitch .me) |