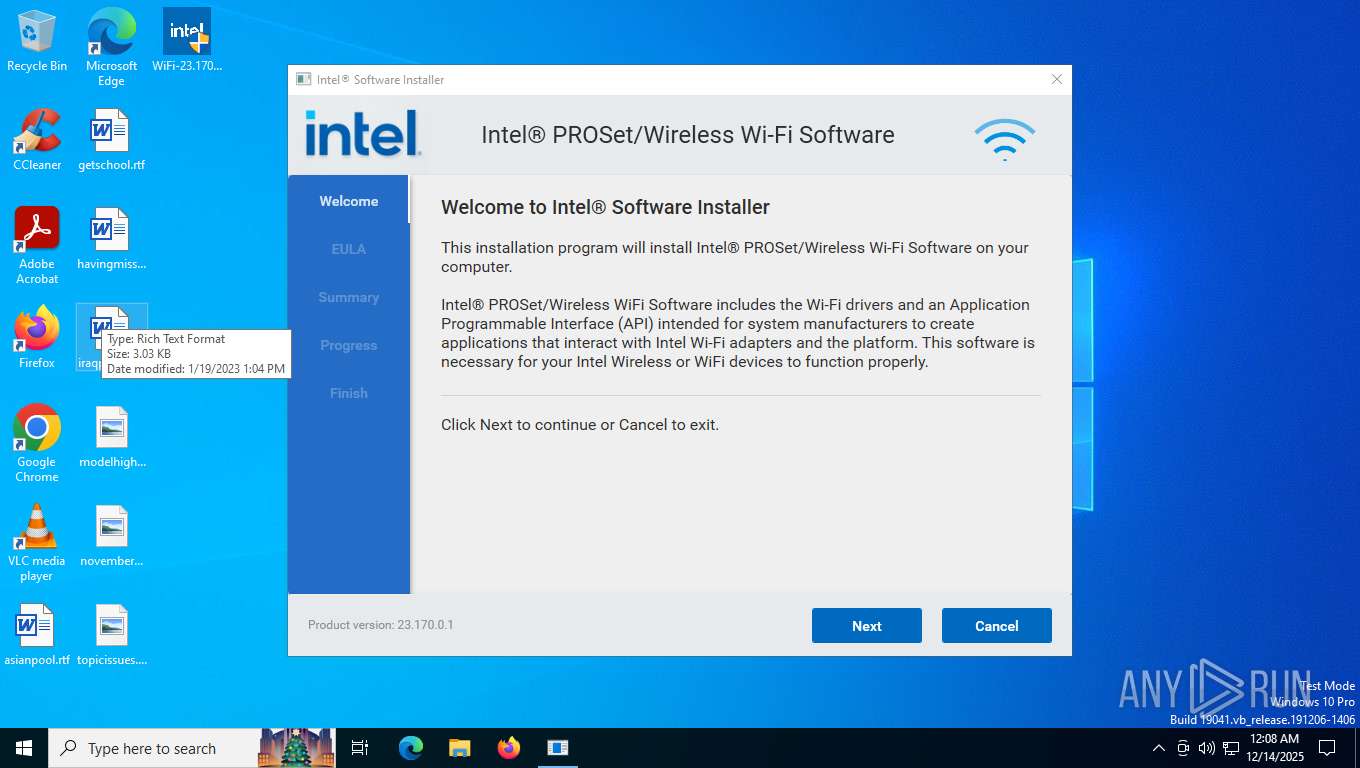
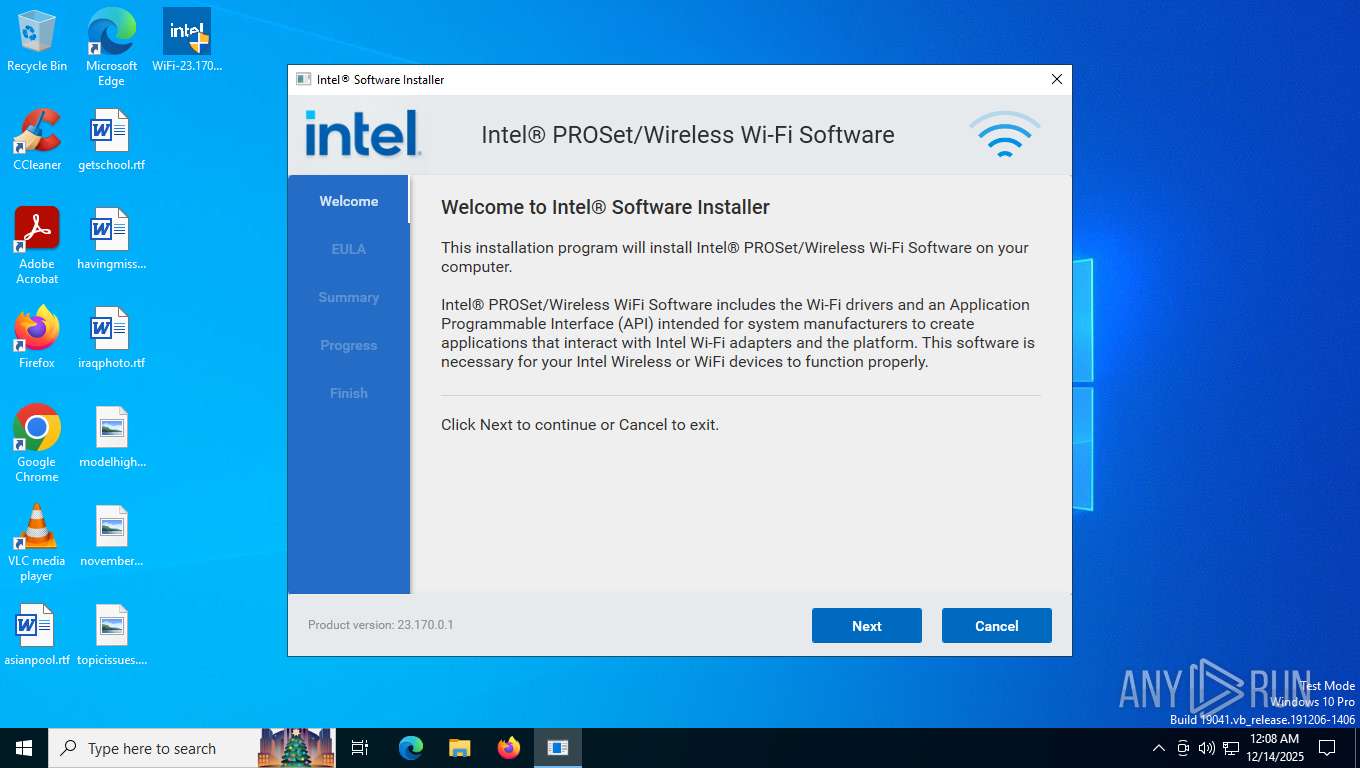
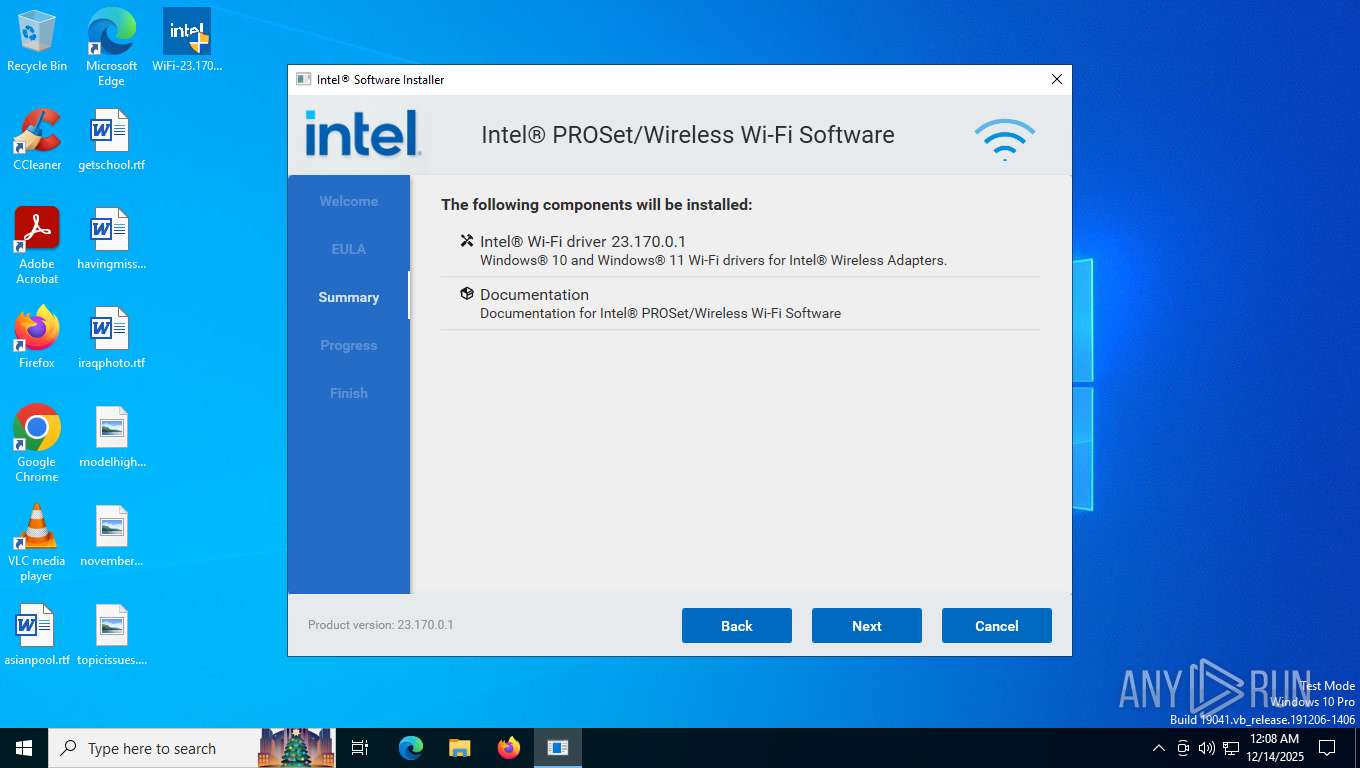
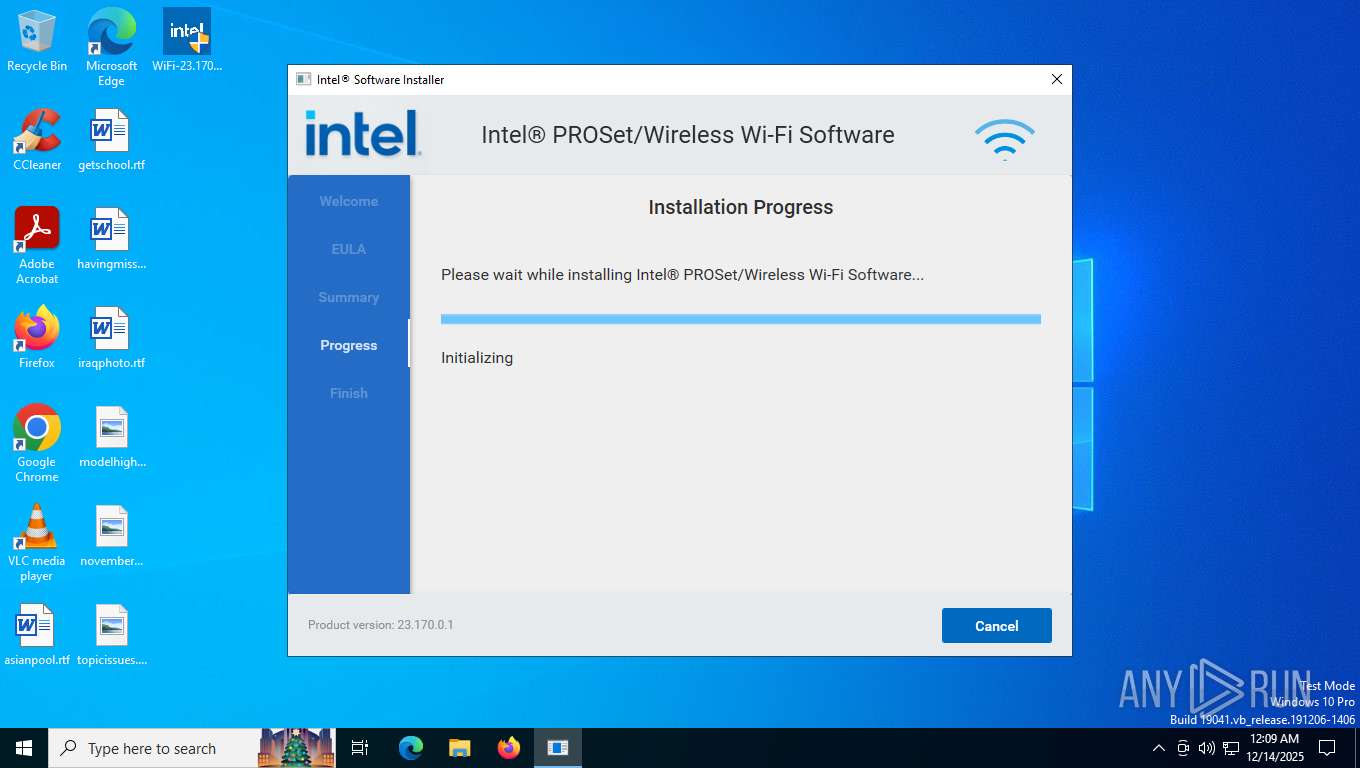
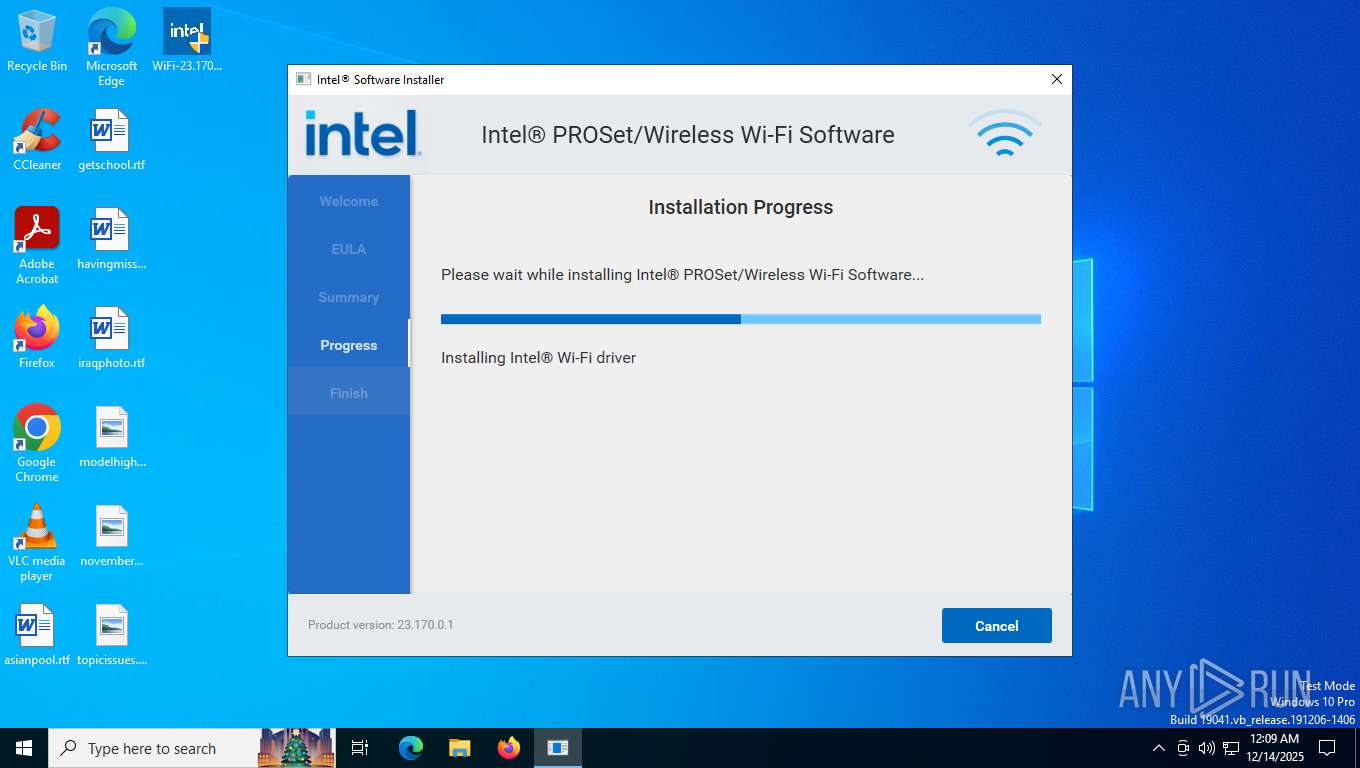
| File name: | WiFi-23.170.0-Driver64-Win10-Win11.exe |
| Full analysis: | https://app.any.run/tasks/a8845ff9-cb67-4ca5-ad64-018ccb3ee74f |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2025, 00:08:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 7A98342A7A5C1B1F6B61518B554CB9E8 |
| SHA1: | A394E9E1E50D48BC7CFBEF82D63BAE4E1456293C |
| SHA256: | 38CC0F2D4C3939134AE8E6F6270B2A55AC03D7ECD55E79C8D8CBCCCF63E039B8 |
| SSDEEP: | 393216:cAMV5aJFf25gKXKQloxDHNgwsOWCOPACtYPi6bwz:cAY5qV1wDKywVWv9tgi3 |
MALICIOUS
Changes settings of System certificates
- CoreBA.exe (PID: 7924)
MENORAH has been detected (YARA)
- CoreBA.exe (PID: 7924)
SUSPICIOUS
Reads security settings of Internet Explorer
- CoreBA.exe (PID: 7924)
- WirelessSetup.exe (PID: 7892)
Searches for installed software
- WirelessSetup.exe (PID: 7892)
- WirelessSetup.exe (PID: 8100)
Adds/modifies Windows certificates
- CoreBA.exe (PID: 7924)
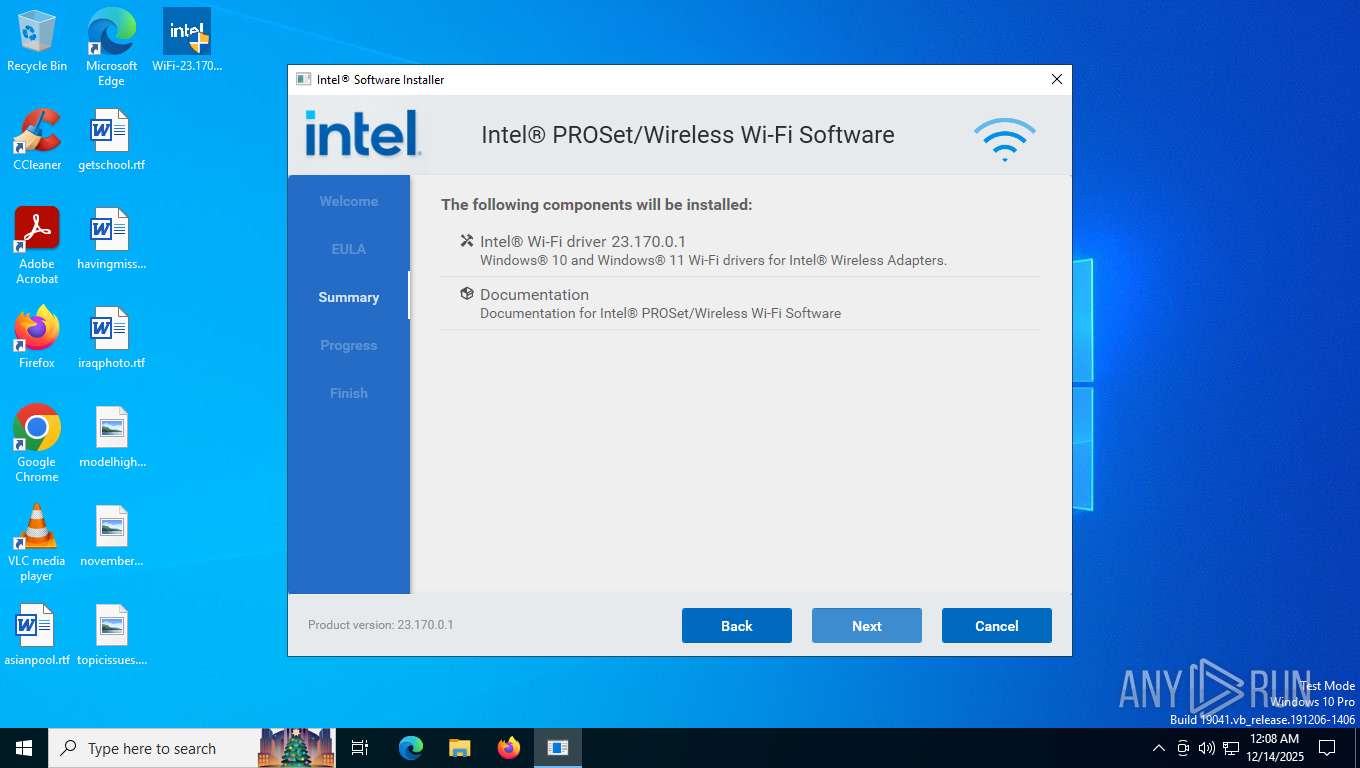
Executable content was dropped or overwritten
- WirelessSetup.exe (PID: 7892)
- WirelessSetup.exe (PID: 8100)
- pnputil.exe (PID: 7404)
- pnputil.exe (PID: 5888)
There is functionality for taking screenshot (YARA)
- WirelessSetup.exe (PID: 7892)
Executes as Windows Service
- VSSVC.exe (PID: 8156)
Drops a system driver (possible attempt to evade defenses)
- WirelessSetup.exe (PID: 8100)
- pnputil.exe (PID: 7404)
- drvinst.exe (PID: 7492)
- pnputil.exe (PID: 5888)
- drvinst.exe (PID: 7588)
Reads the date of Windows installation
- WirelessSetup.exe (PID: 7892)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4572)
INFO
Create files in a temporary directory
- WiFi-23.170.0-Driver64-Win10-Win11.exe (PID: 7868)
- WirelessSetup.exe (PID: 7892)
- WirelessSetup.exe (PID: 8100)
- PreInstallUtility.exe (PID: 7232)
- pnputil.exe (PID: 5888)
- PnPInstaller.exe (PID: 2364)
- pnputil.exe (PID: 7404)
The sample compiled with english language support
- WiFi-23.170.0-Driver64-Win10-Win11.exe (PID: 7868)
- WirelessSetup.exe (PID: 7892)
- WirelessSetup.exe (PID: 8100)
- drvinst.exe (PID: 7492)
- pnputil.exe (PID: 5888)
- drvinst.exe (PID: 7588)
- pnputil.exe (PID: 7404)
Reads the computer name
- WiFi-23.170.0-Driver64-Win10-Win11.exe (PID: 7868)
- CoreBA.exe (PID: 7924)
- WirelessSetup.exe (PID: 7892)
- WirelessSetup.exe (PID: 8100)
- PreInstallUtility.exe (PID: 7232)
- drvinst.exe (PID: 7492)
- PnPInstaller.exe (PID: 2364)
- msiexec.exe (PID: 4572)
- identity_helper.exe (PID: 8028)
- drvinst.exe (PID: 7588)
Checks proxy server information
- CoreBA.exe (PID: 7924)
- slui.exe (PID: 7668)
Creates files or folders in the user directory
- CoreBA.exe (PID: 7924)
- msiexec.exe (PID: 4572)
Reads the machine GUID from the registry
- CoreBA.exe (PID: 7924)
- drvinst.exe (PID: 7492)
- msiexec.exe (PID: 4572)
- drvinst.exe (PID: 7588)
Checks supported languages
- WiFi-23.170.0-Driver64-Win10-Win11.exe (PID: 7868)
- WirelessSetup.exe (PID: 7892)
- CoreBA.exe (PID: 7924)
- WirelessSetup.exe (PID: 8100)
- PreInstallUtility.exe (PID: 7232)
- PnPInstaller.exe (PID: 2364)
- drvinst.exe (PID: 7492)
- drvinst.exe (PID: 7588)
- identity_helper.exe (PID: 8028)
- msiexec.exe (PID: 4572)
Reads Environment values
- CoreBA.exe (PID: 7924)
- identity_helper.exe (PID: 8028)
Process checks computer location settings
- WirelessSetup.exe (PID: 7892)
Manages system restore points
- SrTasks.exe (PID: 7176)
Creates files in the program directory
- PreInstallUtility.exe (PID: 7232)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4572)
Manual execution by a user
- msedge.exe (PID: 8016)
- msedge.exe (PID: 5636)
- msedge.exe (PID: 6920)
- msedge.exe (PID: 6056)
- msedge.exe (PID: 3376)
- msedge.exe (PID: 7208)
- msedge.exe (PID: 2124)
- msedge.exe (PID: 7976)
- msedge.exe (PID: 3060)
- msedge.exe (PID: 8220)
- msedge.exe (PID: 7156)
Creates a software uninstall entry
- msiexec.exe (PID: 4572)
Application launched itself
- msedge.exe (PID: 8016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:06:03 10:44:02+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 330240 |
| InitializedDataSize: | 238080 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x272c0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 23.170.0.1 |
| ProductVersionNumber: | 23.170.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Intel Corporation |
| FileDescription: | - |
| FileVersion: | 1.0.0.1 |
| InternalName: | SFX.exe |
| LegalCopyright: | Copyright (C) 2023-2025 Intel Corporation |
| OriginalFileName: | SFX.exe |
| ProductVersion: | 1.0.0.1 |
Total processes
194
Monitored processes
62
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1148 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6880,i,3530607581092328200,13547921113529575997,262144 --variations-seed-version --mojo-platform-channel-handle=6436 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1288 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5184,i,3530607581092328200,13547921113529575997,262144 --variations-seed-version --mojo-platform-channel-handle=5248 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1568 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1784 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=4576,i,3530607581092328200,13547921113529575997,262144 --variations-seed-version --mojo-platform-channel-handle=5296 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1792 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=22 --always-read-main-dll --field-trial-handle=7516,i,3530607581092328200,13547921113529575997,262144 --variations-seed-version --mojo-platform-channel-handle=7500 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1908 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=8152,i,3530607581092328200,13547921113529575997,262144 --variations-seed-version --mojo-platform-channel-handle=8100 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
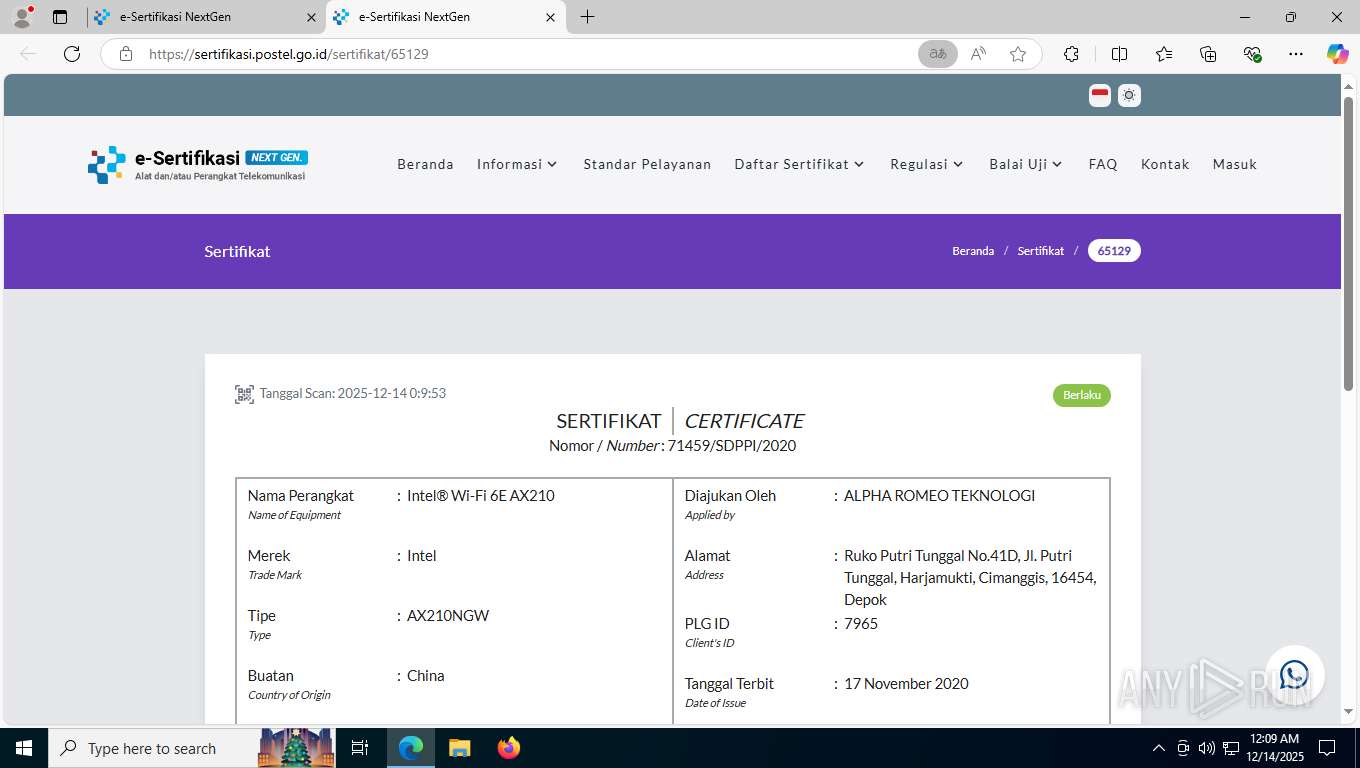
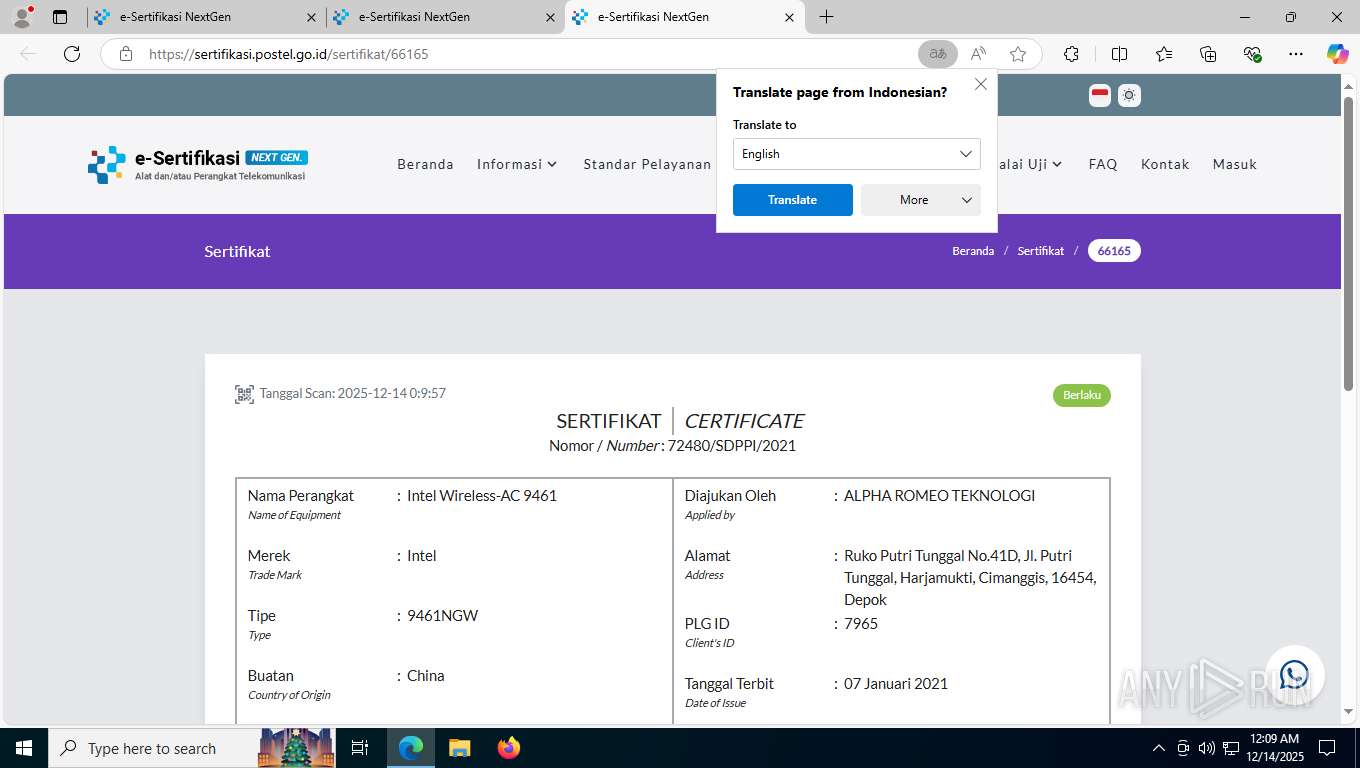
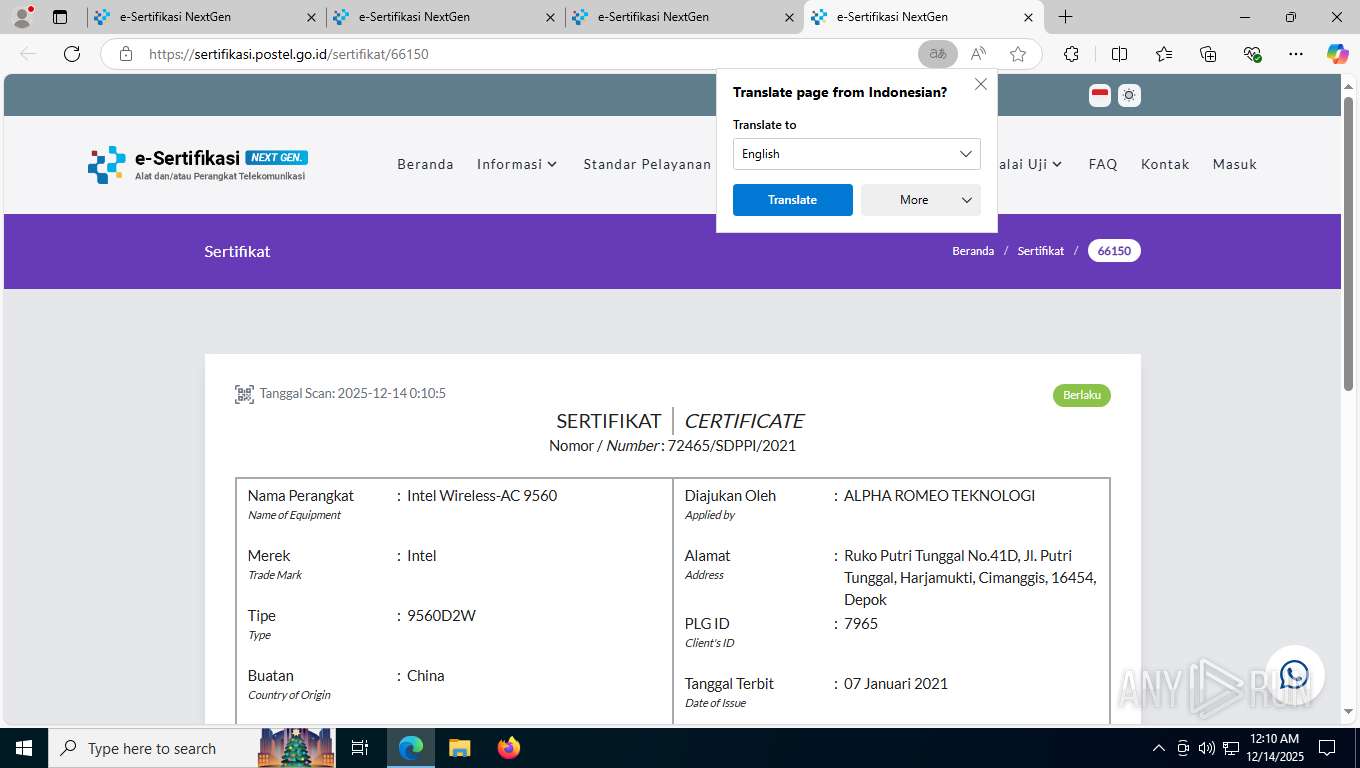
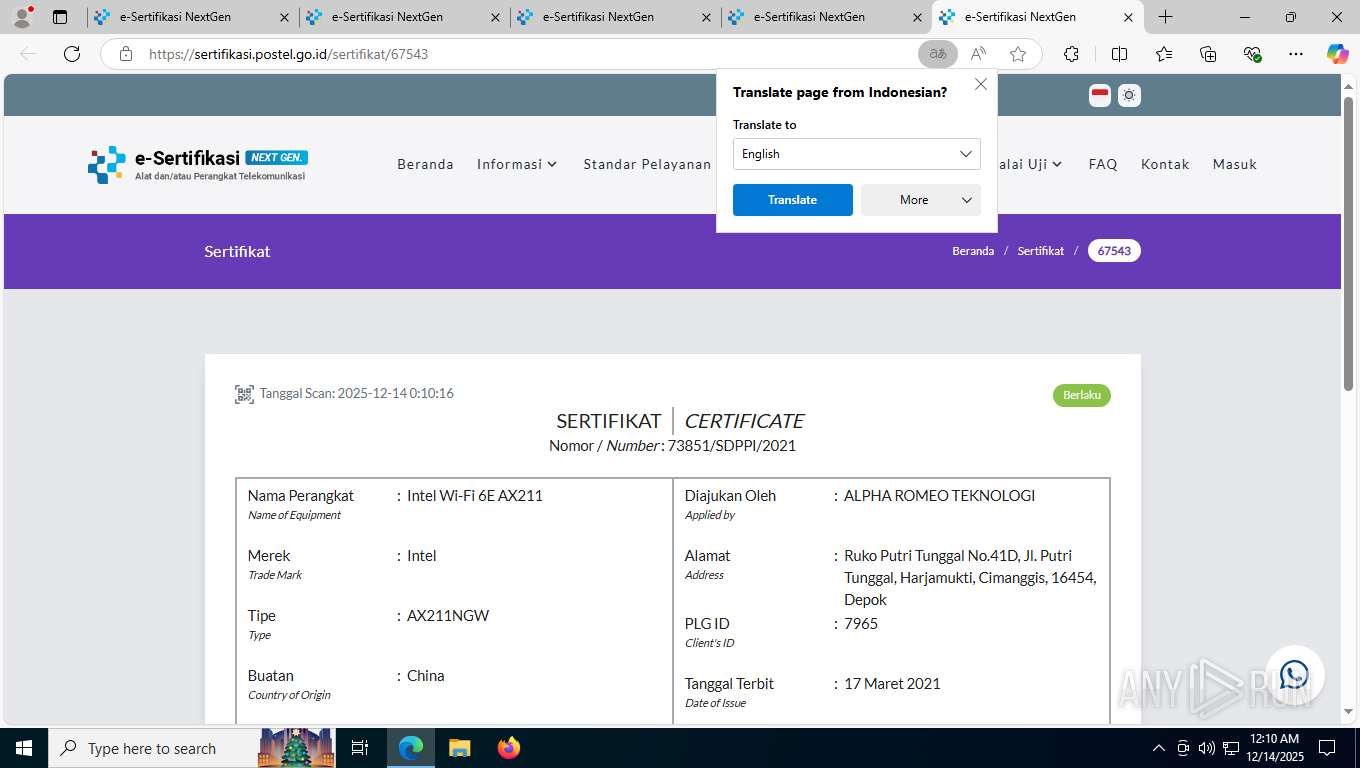
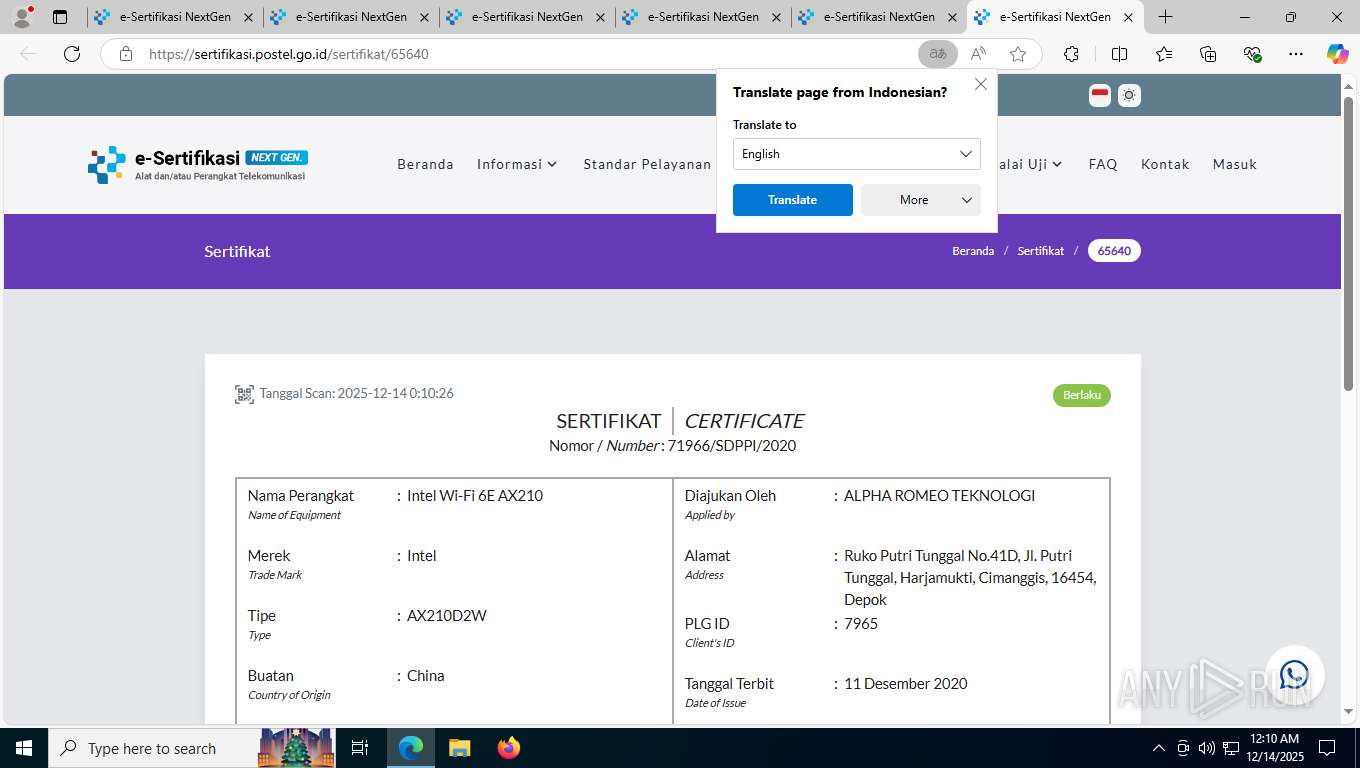
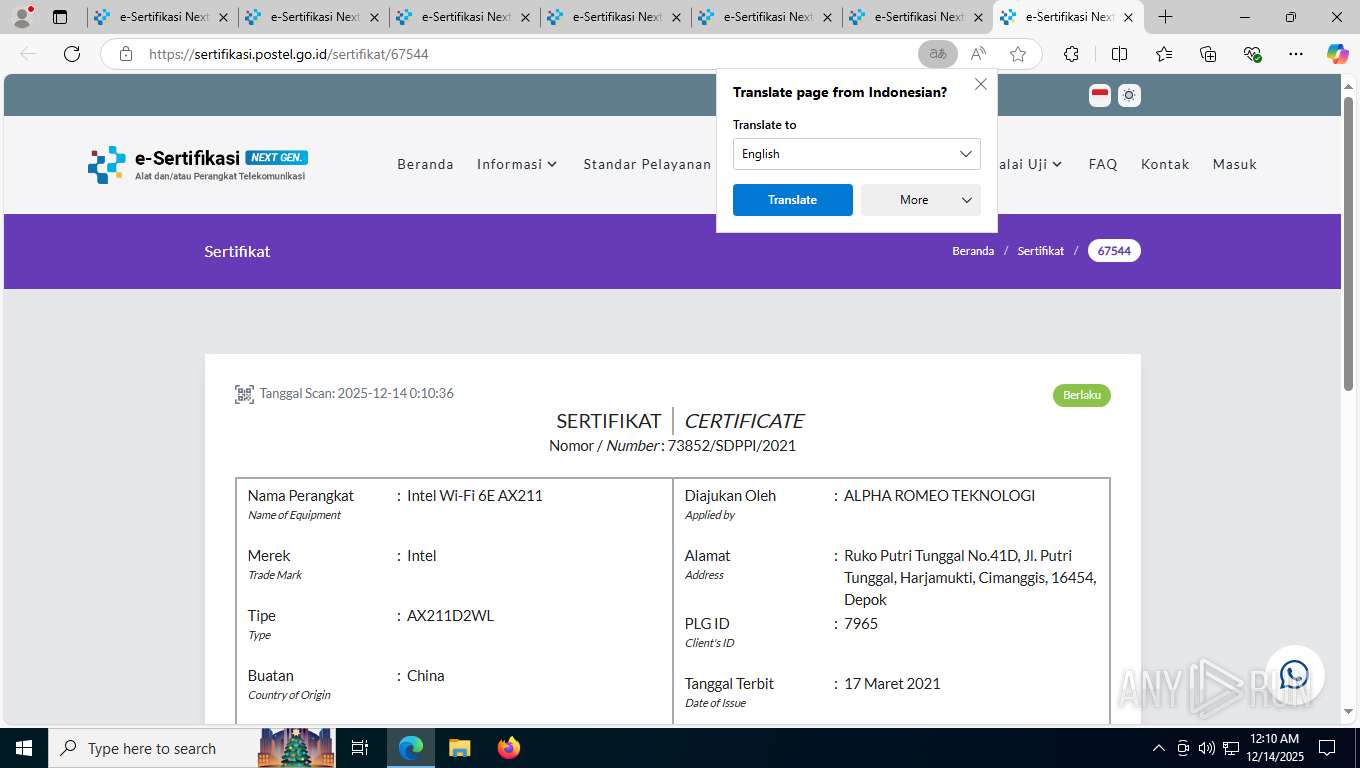
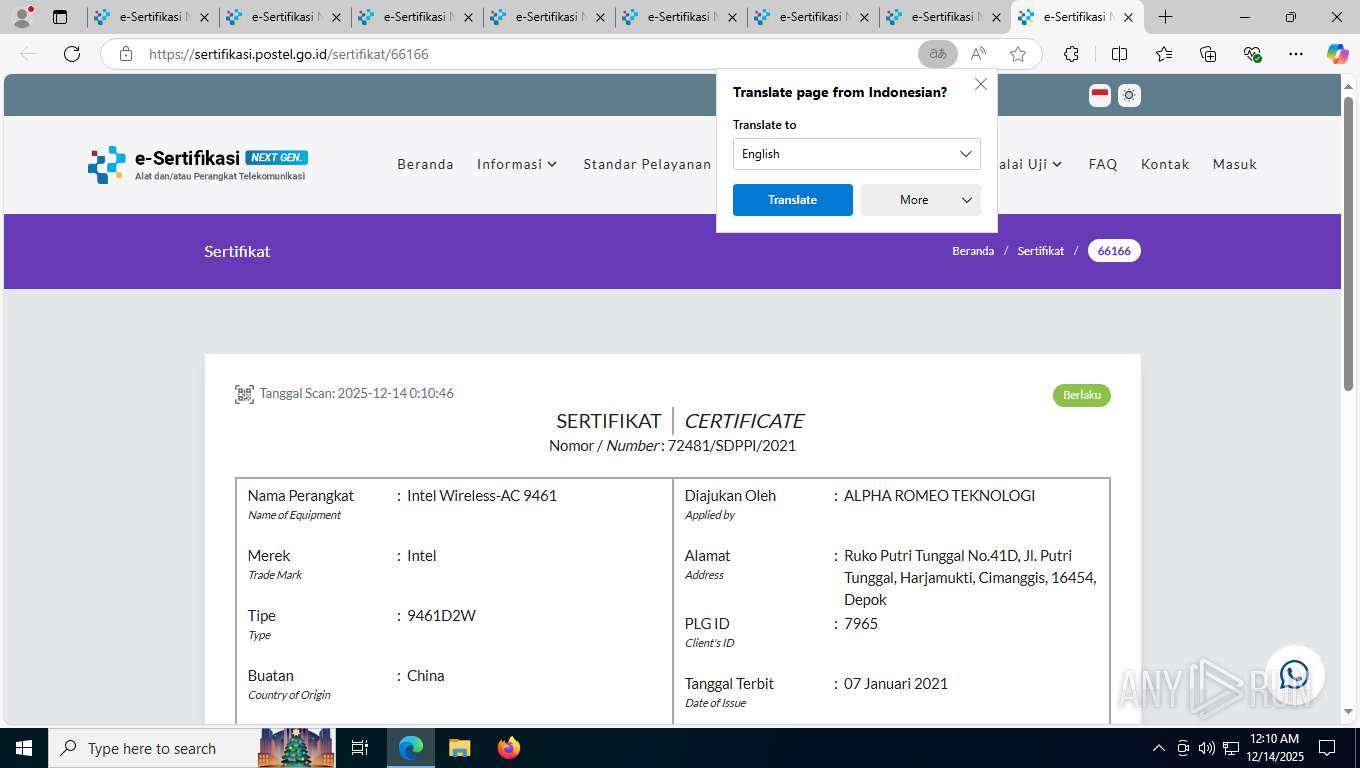
| 2124 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" https://sertifikasi.postel.go.id/valid?section=eb95c8e9258730e280b250bd38bb95a4S3r103234S3reb95c8e9258730e280b250bd38bb95a4 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2148 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=19 --always-read-main-dll --field-trial-handle=1140,i,3530607581092328200,13547921113529575997,262144 --variations-seed-version --mojo-platform-channel-handle=5860 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2364 | "C:\ProgramData\Package Cache\fb933b4b-640e-43aa-9ad8-0d8d2e9fb3f6\PnPInstaller.exe" -pi WIFI_Driver -bc "C:\ProgramData\Package Cache\{A15B0CFC-06F1-4222-BB64-F608289B7C41}" -f "'WiFiDriver\Netwtw08.INF','WiFiDriver\Netwtw6e.INF'" -i -l "C:\Users\admin\AppData\Local\Temp\Intel®_Software_Installer_20251214000849_001_WIFI_Driver.log" | C:\ProgramData\Package Cache\fb933b4b-640e-43aa-9ad8-0d8d2e9fb3f6\PnPInstaller.exe | — | WirelessSetup.exe | |||||||||||
User: admin Company: Intel Corporation Integrity Level: HIGH Description: PnPInstaller Exit code: 0 Version: 23.160.0.0 Modules
| |||||||||||||||
| 2416 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | PnPInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
24 556
Read events
24 080
Write events
448
Delete events
28
Modification events
| (PID) Process: | (7924) CoreBA.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates |
| Operation: | delete value | Name: | 2B8F1B57330DBBA2D07A6C51F70EE90DDAB9AD8E |
Value: | |||
| (PID) Process: | (7924) CoreBA.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\2B8F1B57330DBBA2D07A6C51F70EE90DDAB9AD8E |
| Operation: | write | Name: | Blob |
Value: 0400000001000000100000001BFE69D191B71933A372A80FE155E5B51D0000000100000010000000885010358D29A38F059B028559C95F90620000000100000020000000E793C9B02FD8AA13E21C31228ACCB08119643B749C898964B1746D46C3D4CBD2090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B060105050703080F000000010000003000000066B764A96581128168CF208E374DDA479D54E311F32457F4AEE0DBD2A6C8D171D531289E1CD22BFDBBD4CFD9796254830300000001000000140000002B8F1B57330DBBA2D07A6C51F70EE90DDAB9AD8E190000000100000010000000EA6089055218053DD01E37E1D806EEDF53000000010000004300000030413022060C2B06010401B231010201050130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C01400000001000000140000005379BF5AAA2B4ACF5480E1D89BC09DF2B20366CB0B00000001000000100000005300650063007400690067006F0000002000000001000000E2050000308205DE308203C6A003020102021001FD6D30FCA3CA51A81BBC640E35032D300D06092A864886F70D01010C0500308188310B3009060355040613025553311330110603550408130A4E6577204A6572736579311430120603550407130B4A65727365792043697479311E301C060355040A131554686520555345525452555354204E6574776F726B312E302C06035504031325555345525472757374205253412043657274696669636174696F6E20417574686F72697479301E170D3130303230313030303030305A170D3338303131383233353935395A308188310B3009060355040613025553311330110603550408130A4E6577204A6572736579311430120603550407130B4A65727365792043697479311E301C060355040A131554686520555345525452555354204E6574776F726B312E302C06035504031325555345525472757374205253412043657274696669636174696F6E20417574686F7269747930820222300D06092A864886F70D01010105000382020F003082020A028202010080126517360EC3DB08B3D0AC570D76EDCD27D34CAD508361E2AA204D092D6409DCCE899FCC3DA9ECF6CFC1DCF1D3B1D67B3728112B47DA39C6BC3A19B45FA6BD7D9DA36342B676F2A93B2B91F8E26FD0EC162090093EE2E874C918B491D46264DB7FA306F188186A90223CBCFE13F087147BF6E41F8ED4E451C61167460851CB8614543FBC33FE7E6C9CFF169D18BD518E35A6A766C87267DB2166B1D49B7803C0503AE8CCF0DCBC9E4CFEAF0596351F575AB7FFCEF93DB72CB6F654DDC8E7123A4DAE4C8AB75C9AB4B7203DCA7F2234AE7E3B68660144E7014E46539B3360F794BE5337907343F332C353EFDBAAFE744E69C76B8C6093DEC4C70CDFE132AECC933B517895678BEE3D56FE0CD0690F1B0FF325266B336DF76E47FA7343E57E0EA566B1297C3284635589C40DC19354301913ACD37D37A7EB5D3A6C355CDB41D712DAA9490BDFD8808A0993628EB566CF2588CD84B8B13FA4390FD9029EEB124C957CF36B05A95E1683CCB867E2E8139DCC5B82D34CB3ED5BFFDEE573AC233B2D00BF3555740949D849581A7F9236E651920EF3267D1C4D17BCC9EC4326D0BF415F40A94444F499E757879E501F5754A83EFD74632FB1506509E658422E431A4CB4F0254759FA041E93D426464A5081B2DEBE78B7FC6715E1C957841E0F63D6E962BAD65F552EEA5CC62808042539B80E2BA9F24C971C073F0D52F5EDEF2F820F0203010001A3423040301D0603551D0E041604145379BF5AAA2B4ACF5480E1D89BC09DF2B20366CB300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF300D06092A864886F70D01010C050003820201005CD47C0DCFF7017D4199650C73C5529FCBF8CF99067F1BDA43159F9E0255579614F1523C27879428ED1F3A0137A276FC5350C0849BC66B4EBA8C214FA28E556291F36915D8BC88E3C4AA0BFDEFA8E94B552A06206D55782919EE5F305C4B241155FF249A6E5E2A2BEE0B4D9F7FF70138941495430709FB60A9EE1CAB128CA09A5EA7986A596D8B3F08FBC8D145AF18156490120F73282EC5E2244EFC58ECF0F445FE22B3EB2F8ED2D9456105C1976FA876728F8B8C36AFBF0D05CE718DE6A66F1F6CA67162C5D8D083720CF16711890C9C134C7234DFBCD571DFAA71DDE1B96C8C3C125D65DABD5712B6436BFFE5DE4D661151CF99AEEC17B6E871918CDE49FEDD3571A21527941CCF61E326BB6FA36725215DE6DD1D0B2E681B3B82AFEC836785D4985174B1B9998089FF7F78195C794A602E9240AE4C372A2CC9C762C80E5DF7365BCAE0252501B4DD1A079C77003FD0DCD5EC3DD4FABB3FCC85D66F7FA92DDFB902F7F5979AB535DAC367B0874AA9289E238EFF5C276BE1B04FF307EE002ED45987CB524195EAF447D7EE6441557C8D590295DD629DC2B9EE5A287484A59BB790C70C07DFF589367432D628C1B0B00BE09C4CC31CD6FCE369B54746812FA282ABD3634470C48DFF2D33BAAD8F7BB57088AE3E19CF4028D8FCC890BB5D9922F552E658C51F883143EE881DD7C68E3C436A1DA718DE7D3D16F162F9CA90A8FD | |||
| (PID) Process: | (7924) CoreBA.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\2B8F1B57330DBBA2D07A6C51F70EE90DDAB9AD8E |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000001000000B00000001000000100000005300650063007400690067006F0000001400000001000000140000005379BF5AAA2B4ACF5480E1D89BC09DF2B20366CB53000000010000004300000030413022060C2B06010401B231010201050130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C0190000000100000010000000EA6089055218053DD01E37E1D806EEDF0300000001000000140000002B8F1B57330DBBA2D07A6C51F70EE90DDAB9AD8E0F000000010000003000000066B764A96581128168CF208E374DDA479D54E311F32457F4AEE0DBD2A6C8D171D531289E1CD22BFDBBD4CFD979625483090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B06010505070308620000000100000020000000E793C9B02FD8AA13E21C31228ACCB08119643B749C898964B1746D46C3D4CBD21D0000000100000010000000885010358D29A38F059B028559C95F900400000001000000100000001BFE69D191B71933A372A80FE155E5B52000000001000000E2050000308205DE308203C6A003020102021001FD6D30FCA3CA51A81BBC640E35032D300D06092A864886F70D01010C0500308188310B3009060355040613025553311330110603550408130A4E6577204A6572736579311430120603550407130B4A65727365792043697479311E301C060355040A131554686520555345525452555354204E6574776F726B312E302C06035504031325555345525472757374205253412043657274696669636174696F6E20417574686F72697479301E170D3130303230313030303030305A170D3338303131383233353935395A308188310B3009060355040613025553311330110603550408130A4E6577204A6572736579311430120603550407130B4A65727365792043697479311E301C060355040A131554686520555345525452555354204E6574776F726B312E302C06035504031325555345525472757374205253412043657274696669636174696F6E20417574686F7269747930820222300D06092A864886F70D01010105000382020F003082020A028202010080126517360EC3DB08B3D0AC570D76EDCD27D34CAD508361E2AA204D092D6409DCCE899FCC3DA9ECF6CFC1DCF1D3B1D67B3728112B47DA39C6BC3A19B45FA6BD7D9DA36342B676F2A93B2B91F8E26FD0EC162090093EE2E874C918B491D46264DB7FA306F188186A90223CBCFE13F087147BF6E41F8ED4E451C61167460851CB8614543FBC33FE7E6C9CFF169D18BD518E35A6A766C87267DB2166B1D49B7803C0503AE8CCF0DCBC9E4CFEAF0596351F575AB7FFCEF93DB72CB6F654DDC8E7123A4DAE4C8AB75C9AB4B7203DCA7F2234AE7E3B68660144E7014E46539B3360F794BE5337907343F332C353EFDBAAFE744E69C76B8C6093DEC4C70CDFE132AECC933B517895678BEE3D56FE0CD0690F1B0FF325266B336DF76E47FA7343E57E0EA566B1297C3284635589C40DC19354301913ACD37D37A7EB5D3A6C355CDB41D712DAA9490BDFD8808A0993628EB566CF2588CD84B8B13FA4390FD9029EEB124C957CF36B05A95E1683CCB867E2E8139DCC5B82D34CB3ED5BFFDEE573AC233B2D00BF3555740949D849581A7F9236E651920EF3267D1C4D17BCC9EC4326D0BF415F40A94444F499E757879E501F5754A83EFD74632FB1506509E658422E431A4CB4F0254759FA041E93D426464A5081B2DEBE78B7FC6715E1C957841E0F63D6E962BAD65F552EEA5CC62808042539B80E2BA9F24C971C073F0D52F5EDEF2F820F0203010001A3423040301D0603551D0E041604145379BF5AAA2B4ACF5480E1D89BC09DF2B20366CB300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF300D06092A864886F70D01010C050003820201005CD47C0DCFF7017D4199650C73C5529FCBF8CF99067F1BDA43159F9E0255579614F1523C27879428ED1F3A0137A276FC5350C0849BC66B4EBA8C214FA28E556291F36915D8BC88E3C4AA0BFDEFA8E94B552A06206D55782919EE5F305C4B241155FF249A6E5E2A2BEE0B4D9F7FF70138941495430709FB60A9EE1CAB128CA09A5EA7986A596D8B3F08FBC8D145AF18156490120F73282EC5E2244EFC58ECF0F445FE22B3EB2F8ED2D9456105C1976FA876728F8B8C36AFBF0D05CE718DE6A66F1F6CA67162C5D8D083720CF16711890C9C134C7234DFBCD571DFAA71DDE1B96C8C3C125D65DABD5712B6436BFFE5DE4D661151CF99AEEC17B6E871918CDE49FEDD3571A21527941CCF61E326BB6FA36725215DE6DD1D0B2E681B3B82AFEC836785D4985174B1B9998089FF7F78195C794A602E9240AE4C372A2CC9C762C80E5DF7365BCAE0252501B4DD1A079C77003FD0DCD5EC3DD4FABB3FCC85D66F7FA92DDFB902F7F5979AB535DAC367B0874AA9289E238EFF5C276BE1B04FF307EE002ED45987CB524195EAF447D7EE6441557C8D590295DD629DC2B9EE5A287484A59BB790C70C07DFF589367432D628C1B0B00BE09C4CC31CD6FCE369B54746812FA282ABD3634470C48DFF2D33BAAD8F7BB57088AE3E19CF4028D8FCC890BB5D9922F552E658C51F883143EE881DD7C68E3C436A1DA718DE7D3D16F162F9CA90A8FD | |||
| (PID) Process: | (7924) CoreBA.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates |
| Operation: | delete value | Name: | D1EB23A46D17D68FD92564C2F1F1601764D8E349 |
Value: | |||
| (PID) Process: | (7924) CoreBA.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\D1EB23A46D17D68FD92564C2F1F1601764D8E349 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000497904B0EB8719AC47B0BC11519B74D0140000000100000014000000A0110A233E96F107ECE2AF29EF82A57FD030A4B4620000000100000020000000D7A7A0FB5D7E2731D771E9484EBCDEF71D5F0C3E0A2948782BC83EE0EA699EF4090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B060105050703080F00000001000000140000003E8E6487F8FD27D322A269A71EDAAC5D57811286030000000100000014000000D1EB23A46D17D68FD92564C2F1F1601764D8E3491900000001000000100000002AA1C05E2AE606F198C2C5E937C97AA253000000010000004300000030413022060C2B06010401B231010201050130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C00B000000010000001C0000005300650063007400690067006F0020002800410041004100290000001D00000001000000100000002E0D6875874A44C820912E85E964CFDB200000000100000036040000308204323082031AA003020102020101300D06092A864886F70D0101050500307B310B3009060355040613024742311B301906035504080C1247726561746572204D616E636865737465723110300E06035504070C0753616C666F7264311A3018060355040A0C11436F6D6F646F204341204C696D697465643121301F06035504030C18414141204365727469666963617465205365727669636573301E170D3034303130313030303030305A170D3238313233313233353935395A307B310B3009060355040613024742311B301906035504080C1247726561746572204D616E636865737465723110300E06035504070C0753616C666F7264311A3018060355040A0C11436F6D6F646F204341204C696D697465643121301F06035504030C1841414120436572746966696361746520536572766963657330820122300D06092A864886F70D01010105000382010F003082010A0282010100BE409DF46EE1EA76871C4D45448EBE46C883069DC12AFE181F8EE402FAF3AB5D508A16310B9A06D0C57022CD492D5463CCB66E68460B53EACB4C24C0BC724EEAF115AEF4549A120AC37AB23360E2DA8955F32258F3DEDCCFEF8386A28C944F9F68F29890468427C776BFE3CC352C8B5E07646582C048B0A891F9619F762050A891C766B5EB78620356F08A1A13EA31A31EA099FD38F6F62732586F07F56BB8FB142BAFB7AACCD6635F738CDA0599A838A8CB17783651ACE99EF4783A8DCF0FD942E2980CAB2F9F0E01DEEF9F9949F12DDFAC744D1B98B547C5E529D1F99018C7629CBE83C7267B3E8A25C7C0DD9DE6356810209D8FD8DED2C3849C0D5EE82FC90203010001A381C03081BD301D0603551D0E04160414A0110A233E96F107ECE2AF29EF82A57FD030A4B4300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF307B0603551D1F047430723038A036A0348632687474703A2F2F63726C2E636F6D6F646F63612E636F6D2F414141436572746966696361746553657276696365732E63726C3036A034A0328630687474703A2F2F63726C2E636F6D6F646F2E6E65742F414141436572746966696361746553657276696365732E63726C300D06092A864886F70D010105050003820101000856FC02F09BE8FFA4FAD67BC64480CE4FC4C5F60058CCA6B6BC1449680476E8E6EE5DEC020F60D68D50184F264E01E3E6B0A5EEBFBC745441BFFDFC12B8C74F5AF48960057F60B7054AF3F6F1C2BFC4B97486B62D7D6BCCD2F346DD2FC6E06AC3C334032C7D96DD5AC20EA70A99C1058BAB0C2FF35C3ACF6C37550987DE53406C58EFFCB6AB656E04F61BDC3CE05A15C69ED9F15948302165036CECE92173EC9B03A1E037ADA015188FFABA02CEA72CA910132CD4E50826AB229760F8905E74D4A29A53BDF2A968E0A26EC2D76CB1A30F9EBFEB68E756F2AEF2E32B383A0981B56B85D7BE2DED3F1AB7B263E2F5622C82D46A004150F139839F95E93696986E | |||
| (PID) Process: | (7924) CoreBA.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\D1EB23A46D17D68FD92564C2F1F1601764D8E349 |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000000800001D00000001000000100000002E0D6875874A44C820912E85E964CFDB0B000000010000001C0000005300650063007400690067006F00200028004100410041002900000053000000010000004300000030413022060C2B06010401B231010201050130123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C01900000001000000100000002AA1C05E2AE606F198C2C5E937C97AA2030000000100000014000000D1EB23A46D17D68FD92564C2F1F1601764D8E3490F00000001000000140000003E8E6487F8FD27D322A269A71EDAAC5D57811286090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B06010505070308620000000100000020000000D7A7A0FB5D7E2731D771E9484EBCDEF71D5F0C3E0A2948782BC83EE0EA699EF4140000000100000014000000A0110A233E96F107ECE2AF29EF82A57FD030A4B4040000000100000010000000497904B0EB8719AC47B0BC11519B74D0200000000100000036040000308204323082031AA003020102020101300D06092A864886F70D0101050500307B310B3009060355040613024742311B301906035504080C1247726561746572204D616E636865737465723110300E06035504070C0753616C666F7264311A3018060355040A0C11436F6D6F646F204341204C696D697465643121301F06035504030C18414141204365727469666963617465205365727669636573301E170D3034303130313030303030305A170D3238313233313233353935395A307B310B3009060355040613024742311B301906035504080C1247726561746572204D616E636865737465723110300E06035504070C0753616C666F7264311A3018060355040A0C11436F6D6F646F204341204C696D697465643121301F06035504030C1841414120436572746966696361746520536572766963657330820122300D06092A864886F70D01010105000382010F003082010A0282010100BE409DF46EE1EA76871C4D45448EBE46C883069DC12AFE181F8EE402FAF3AB5D508A16310B9A06D0C57022CD492D5463CCB66E68460B53EACB4C24C0BC724EEAF115AEF4549A120AC37AB23360E2DA8955F32258F3DEDCCFEF8386A28C944F9F68F29890468427C776BFE3CC352C8B5E07646582C048B0A891F9619F762050A891C766B5EB78620356F08A1A13EA31A31EA099FD38F6F62732586F07F56BB8FB142BAFB7AACCD6635F738CDA0599A838A8CB17783651ACE99EF4783A8DCF0FD942E2980CAB2F9F0E01DEEF9F9949F12DDFAC744D1B98B547C5E529D1F99018C7629CBE83C7267B3E8A25C7C0DD9DE6356810209D8FD8DED2C3849C0D5EE82FC90203010001A381C03081BD301D0603551D0E04160414A0110A233E96F107ECE2AF29EF82A57FD030A4B4300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF307B0603551D1F047430723038A036A0348632687474703A2F2F63726C2E636F6D6F646F63612E636F6D2F414141436572746966696361746553657276696365732E63726C3036A034A0328630687474703A2F2F63726C2E636F6D6F646F2E6E65742F414141436572746966696361746553657276696365732E63726C300D06092A864886F70D010105050003820101000856FC02F09BE8FFA4FAD67BC64480CE4FC4C5F60058CCA6B6BC1449680476E8E6EE5DEC020F60D68D50184F264E01E3E6B0A5EEBFBC745441BFFDFC12B8C74F5AF48960057F60B7054AF3F6F1C2BFC4B97486B62D7D6BCCD2F346DD2FC6E06AC3C334032C7D96DD5AC20EA70A99C1058BAB0C2FF35C3ACF6C37550987DE53406C58EFFCB6AB656E04F61BDC3CE05A15C69ED9F15948302165036CECE92173EC9B03A1E037ADA015188FFABA02CEA72CA910132CD4E50826AB229760F8905E74D4A29A53BDF2A968E0A26EC2D76CB1A30F9EBFEB68E756F2AEF2E32B383A0981B56B85D7BE2DED3F1AB7B263E2F5622C82D46A004150F139839F95E93696986E | |||
| (PID) Process: | (8100) WirelessSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000067F8DCD78D6CDC01A41F0000A81F0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8100) WirelessSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000008F46DDD78D6CDC01A41F0000A81F0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8100) WirelessSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000403526D88D6CDC01A41F0000A81F0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8100) WirelessSetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000435C26D88D6CDC01A41F0000A81F0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
144
Suspicious files
258
Text files
348
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7868 | WiFi-23.170.0-Driver64-Win10-Win11.exe | C:\Windows\Temp\{CEEE5B22-FDD7-40EE-9A04-FC9F4FA8BACD}\WirelessSetup.exe | — | |
MD5:— | SHA256:— | |||
| 7892 | WirelessSetup.exe | C:\Windows\Temp\{DC82C482-81B3-4F07-AF5A-E91909436A80}\.ba\Core\CustomBAConfig\Data\Schema\BundleSettingsSchema.xsd | xml | |
MD5:3543268DBBEA7CA61A1A6661D7B22B15 | SHA256:2B531E8EFF92ADA9ED484349C8EDC403165F9F1C5D0C763E9C20F1D0CEF277EC | |||
| 7868 | WiFi-23.170.0-Driver64-Win10-Win11.exe | C:\Users\admin\AppData\Local\Temp\WiFi-23.170.0-Driver64-Win10-Win11_20251214000848.log | text | |
MD5:E60B72FFDFB783E73454C615F131222A | SHA256:75C7250C0560A0C2F63A2734A358AF4C5384631AE1A8E0CC1CE8E50F43947E6F | |||
| 7892 | WirelessSetup.exe | C:\Windows\Temp\{DC82C482-81B3-4F07-AF5A-E91909436A80}\.ba\Config\Data\Schema\BundleDefinitionSchema.xsd | xml | |
MD5:C39655B49D97B27668AB76CA410D7E3A | SHA256:586B9C37D0A39A4AA3E89C018AF89D8A8C9A63B0ED4DA5E7AC5ABD6161D5C433 | |||
| 7868 | WiFi-23.170.0-Driver64-Win10-Win11.exe | C:\Windows\Temp\{CEEE5B22-FDD7-40EE-9A04-FC9F4FA8BACD}\setup.xml | xml | |
MD5:6CA34A6E37B58C8FDE2C3B56DCF96BC2 | SHA256:BEEE1C57E062089F8E55A3F39AC1BD66E42EC828886D022208E0D87A76C4F069 | |||
| 7892 | WirelessSetup.exe | C:\Windows\Temp\{DC82C482-81B3-4F07-AF5A-E91909436A80}\.ba\Core\Localization\Data\LocalizationXml\CoreBA_en-US.xml | xml | |
MD5:6B10CECAEFE040ACEC5D9C5349988CAF | SHA256:CEF6685DFE352745AC4C47E0F53BAE64521CF792898D5C41EC4A2455311A3953 | |||
| 7892 | WirelessSetup.exe | C:\Windows\Temp\{DC82C482-81B3-4F07-AF5A-E91909436A80}\.ba\Core\Localization\Data\LocalizationXml\CoreBA_es-ES.xml | xml | |
MD5:3D8C27660CE8E24DFF07085C2E76BACC | SHA256:3D554900E847D04B80C67C9F01BBE43ABD0AD8D897885D1B464074A563749A7C | |||
| 7892 | WirelessSetup.exe | C:\Windows\Temp\{DC82C482-81B3-4F07-AF5A-E91909436A80}\.ba\Core\Localization\Data\LocalizationXml\CoreBA_cs-CZ.xml | xml | |
MD5:CFAD4044001DCF60794C05E9C7C481C0 | SHA256:024264C006BDE04DADD44F2D6867992B89A400AA01BB6AF258E679C5A3715B1B | |||
| 7892 | WirelessSetup.exe | C:\Windows\Temp\{DC82C482-81B3-4F07-AF5A-E91909436A80}\.ba\Core\Localization\Data\LocalizationXml\CoreBA_fr-FR.xml | xml | |
MD5:1703DA07022659F7838AE0DC67C40193 | SHA256:19675E65C537E8DCFEA51FA1E8668CEC1FF29A70342EB8A2C43903B9AC11B4A7 | |||
| 7892 | WirelessSetup.exe | C:\Windows\Temp\{DC82C482-81B3-4F07-AF5A-E91909436A80}\.ba\Core\Localization\Data\LocalizationXml\CoreBA_fr-CA.xml | xml | |
MD5:8D355CC75E5778F5CA37FE8ABA56CFC8 | SHA256:A1BD3BF47DE4CAB9E0499D841BB0B37E7C490313DC4F458990002B2C83DA40B7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
319
TCP/UDP connections
71
DNS requests
55
Threats
66
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6056 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6056 | svchost.exe | GET | 200 | 72.246.29.11:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 72.246.29.11:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 72.246.29.11:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7924 | CoreBA.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
7924 | CoreBA.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEDPXCKiRQFMZ4qW70zm5rW4%3D | unknown | — | — | whitelisted |
7924 | CoreBA.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCEQDbThdTmC1PA13Y7ddfVTrZ | unknown | — | — | whitelisted |
4572 | msiexec.exe | GET | — | 104.18.38.233:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCEQC0IDbw1ckGjNkBYYlyQBm9 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6056 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6056 | svchost.exe | 72.246.29.11:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 72.246.29.11:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 72.246.29.11:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
crl.sectigo.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
Process | Message |
|---|---|
WiFi-23.170.0-Driver64-Win10-Win11.exe | [07868:07872][14.12.2025 00:08:48.676][SAFEMACROS ][VERBOSE] CommonUtils_CPP::SafeDeleteDeleter<class CommonUtils_CPP:: >>
|
WiFi-23.170.0-Driver64-Win10-Win11.exe | [07868:07872][14.12.2025 00:08:48.676][SAFEMACROS ][INFO ] CommonUtils_CPP::SafeCloseHandleDeleter<void *>::operator attempt to CloseHandle 0x000000000000015C
|
WiFi-23.170.0-Driver64-Win10-Win11.exe | [07868:07872][14.12.2025 00:08:48.676][SFX ][VERBOSE] wWinMain >>
|
WiFi-23.170.0-Driver64-Win10-Win11.exe | [07868:07872][14.12.2025 00:08:48.676][COMMONUTILS ][VERBOSE] CommonUtils_CPP::OsFiles::OsFiles >>
|
WiFi-23.170.0-Driver64-Win10-Win11.exe | [07868:07872][14.12.2025 00:08:48.676][SFXLIBRARY ][VERBOSE] SFXBuilder_Library::SFXPacker::SFXPacker >>
|
WiFi-23.170.0-Driver64-Win10-Win11.exe | [07868:07872][14.12.2025 00:08:48.676][SAFEMACROS ][INFO ] CommonUtils_CPP::SafeDeleteDeleter<class CommonUtils_CPP:: attempt to delete 0x00000299FB2E4B90
|
WiFi-23.170.0-Driver64-Win10-Win11.exe | [07868:07872][14.12.2025 00:08:48.676][SAFEMACROS ][VERBOSE] CommonUtils_CPP::SafeDeleteDeleter<class CommonUtils_CPP:: <<
|
WiFi-23.170.0-Driver64-Win10-Win11.exe | [07868:07872][14.12.2025 00:08:48.676][SFX ][VERBOSE] SFXBuilder_Library::SFX::Run >>
|
WiFi-23.170.0-Driver64-Win10-Win11.exe | [07868:07872][14.12.2025 00:08:48.676][COMMONUTILS ][VERBOSE] CommonUtils_CPP::OsExecute::OsExecute >>
|
WiFi-23.170.0-Driver64-Win10-Win11.exe | [07868:07872][14.12.2025 00:08:48.676][COMMONUTILS ][INFO ] CommonUtils_CPP::OsFiles::GetSystemTempFolder Temp directory: C:\WINDOWS\Temp
|