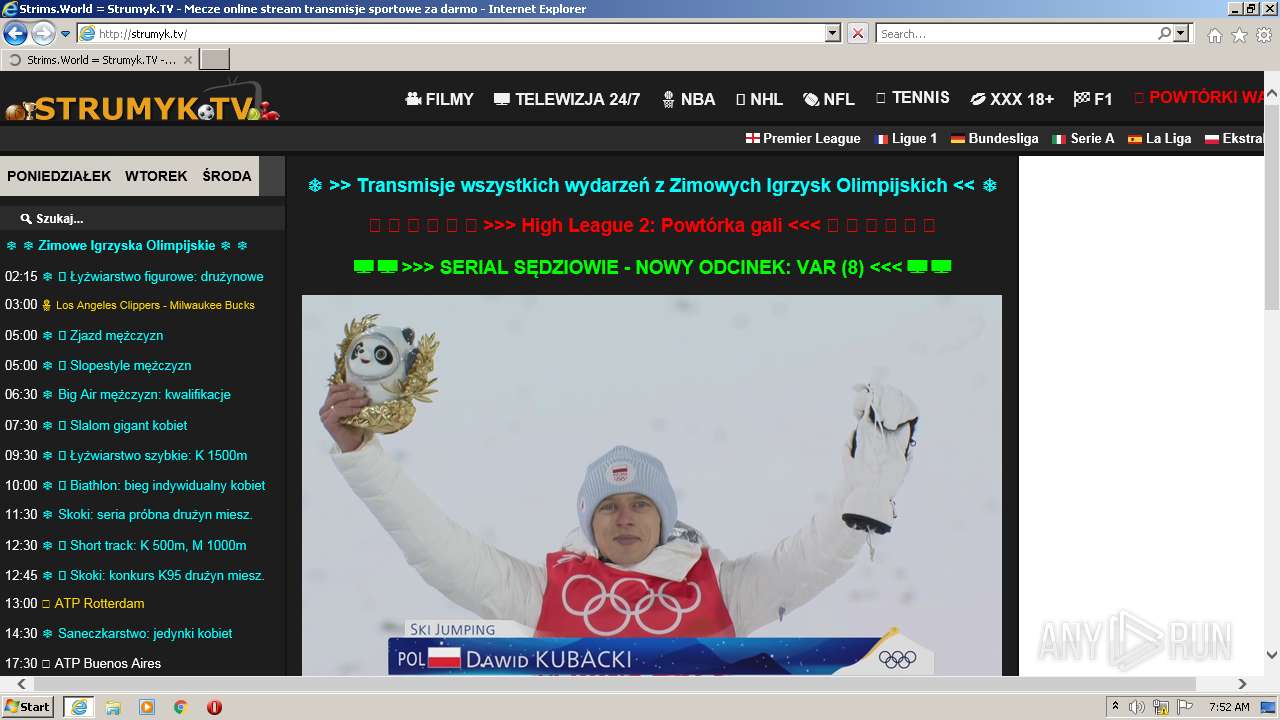
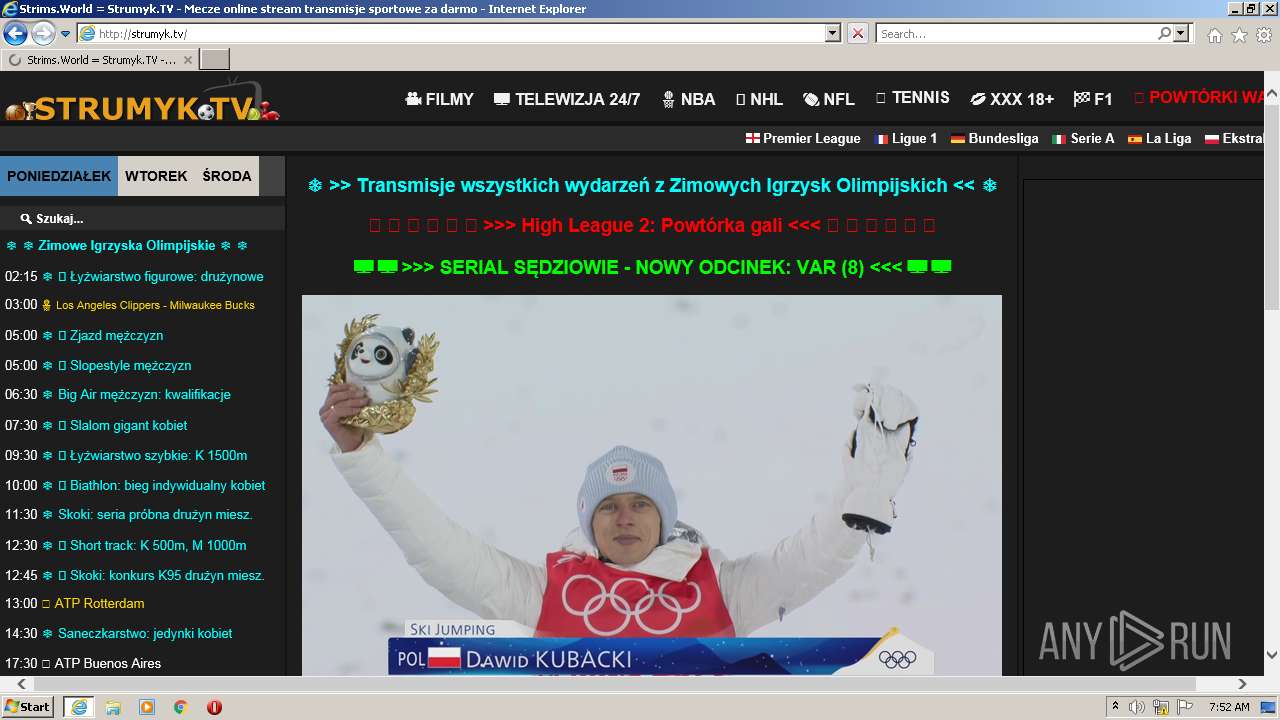
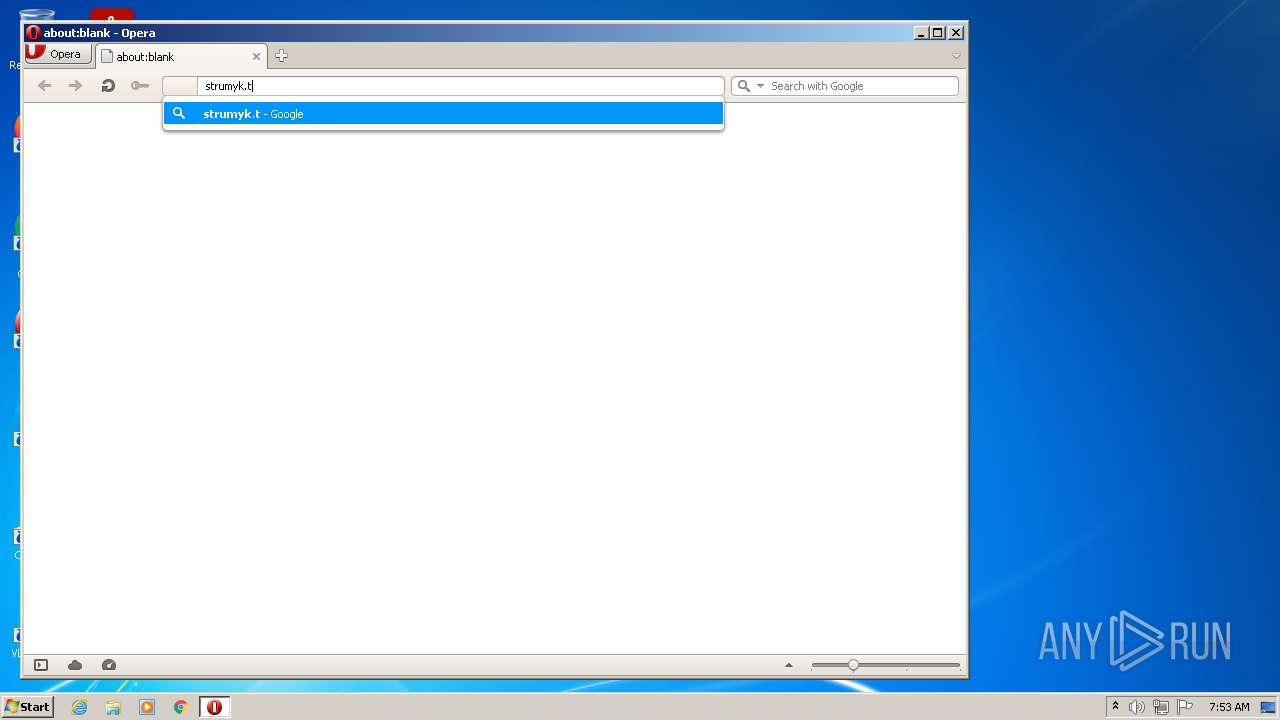
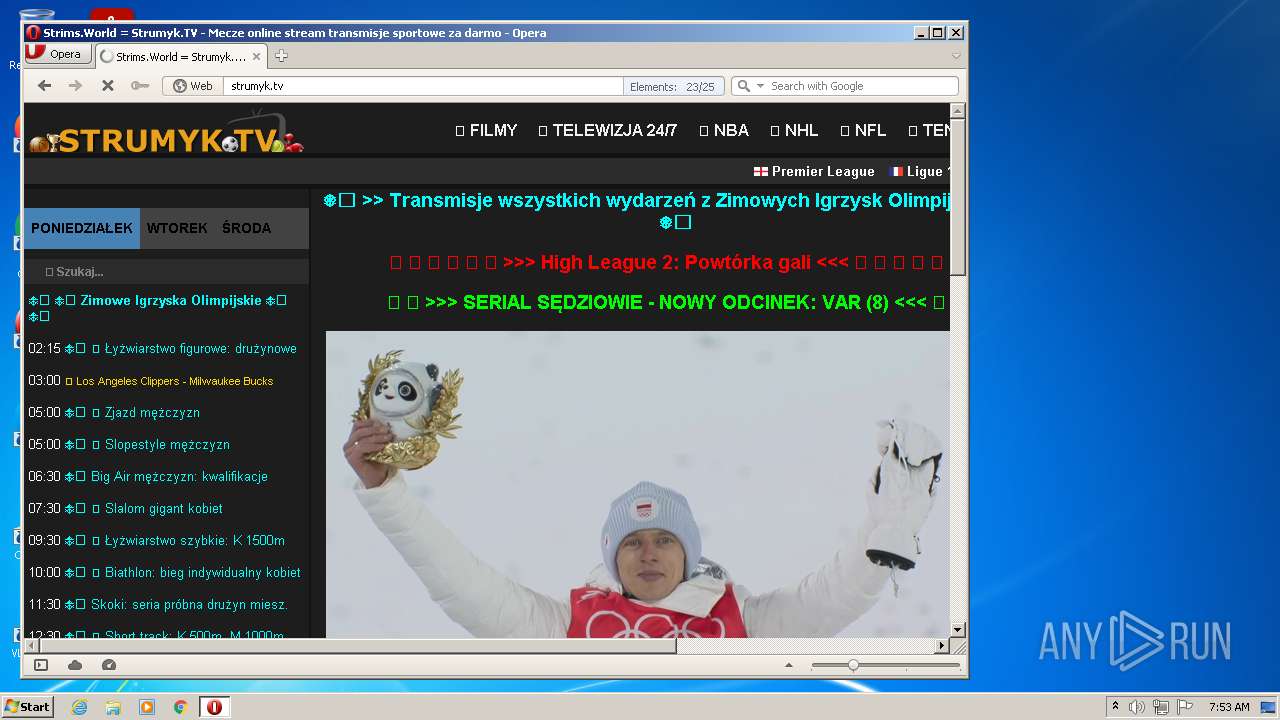
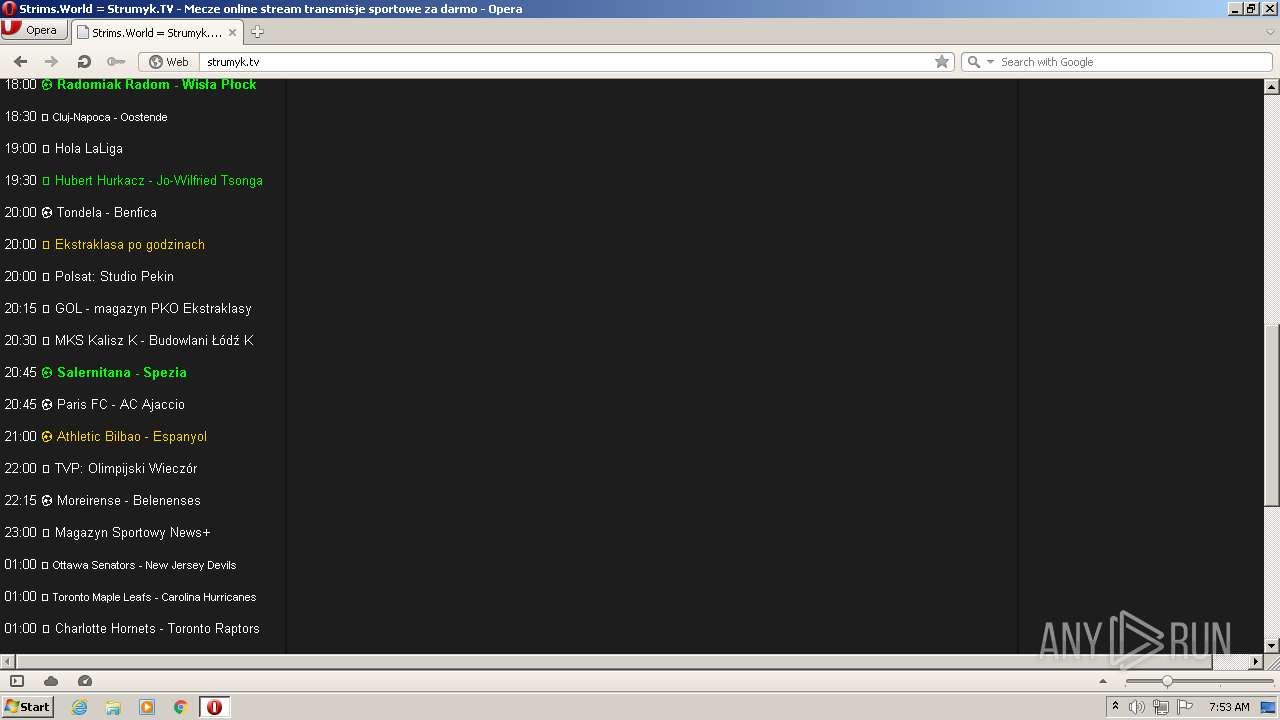
| URL: | http://strumyk.tv |
| Full analysis: | https://app.any.run/tasks/6f3cdc71-dcb4-405d-9182-053fea496865 |
| Verdict: | Malicious activity |
| Analysis date: | February 07, 2022, 07:51:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D8C3E0ACBAE26F678BA46B28DBE758AB |
| SHA1: | FB355B66416EEDD81734ABF282C56D339D5D9E99 |
| SHA256: | 38C8554B23D6564C011A9F8DF0C1D112D6ACE7CDE8735554A7B06E437A0F2403 |
| SSDEEP: | 3:N1KNRtcOJ:CBcOJ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 3748)
INFO
Checks supported languages
- iexplore.exe (PID: 3748)
- iexplore.exe (PID: 3340)
- opera.exe (PID: 764)
Reads the computer name
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 3748)
- opera.exe (PID: 764)
Changes internet zones settings
- iexplore.exe (PID: 3748)
Reads settings of System Certificates
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 3748)
Application launched itself
- iexplore.exe (PID: 3748)
Checks Windows Trust Settings
- iexplore.exe (PID: 3748)
- iexplore.exe (PID: 3340)
Creates files in the user directory
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 3748)
- opera.exe (PID: 764)
Reads internet explorer settings
- iexplore.exe (PID: 3340)
Changes settings of System certificates
- iexplore.exe (PID: 3748)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3748)
Reads the date of Windows installation
- iexplore.exe (PID: 3748)
- opera.exe (PID: 764)
Manual execution by user
- opera.exe (PID: 764)
Check for Java to be installed
- opera.exe (PID: 764)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 764 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | Explorer.EXE | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 3340 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3748 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3748 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://strumyk.tv" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
26 770
Read events
26 517
Write events
250
Delete events
3
Modification events
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30940151 | |||
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30940151 | |||
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
58
Text files
179
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\HZ9TT2A5.htm | html | |
MD5:76F3FD55D373EA28A40A23D9593F74F6 | SHA256:118477B395B8DFDA8D856CC7EA5F0DC9467083163CE2271F2AD929D6813E3A45 | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\style[1].css | text | |
MD5:81C54464270554A33EBAA0DD64A35E8F | SHA256:801A2FB5B49CA8D6D58ACDFF785FE893C8A5875F94E7A6C2B4307C4B8AE77510 | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | der | |
MD5:BC0715DD8E0429ED15D110A2B32FEFF6 | SHA256:EAE19636E3EEF043B5FEA17584468DCF16FFEF5FD6D513B88F724F11A6832E4B | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:9C1B45D0E47A68E832B3B7F8C08C9F36 | SHA256:6CB809CCEDB3111BFA62E2BDA9CA5DD45D74C0A850FA47046329E0CD16FEC054 | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | binary | |
MD5:2611E283A13209B8B48591A01C158948 | SHA256:F3B58CB24651DB91EB0BBB24C46C97E2930CD4C560C4CE59418A67391095B921 | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:3F3517B31B655CCD92F780EF8D2FED7B | SHA256:B41CAE391A5BD0CDAF3B4267FEF7D8CF6131A53952CE3D0D593900DE2CF2572E | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:ED3FF9BAC46CA1A61C8AFDE9704F84CE | SHA256:F5CA38F94BF03C448CC078C8E0B485C821954B59D9CA495F18402AA03B7E8942 | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:0D029B83564CC3E2C7E3EEFF357CD56F | SHA256:80162FF00221C0A074B36EF8A8F38E4847920D08BEA9336AFC34E8E38A26CB36 | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\gq8tKXg[1].png | image | |
MD5:E124C160F9DA7E05D28B9B12DBC4C8AB | SHA256:318BE34B0D2EAC78DC3EB92C1E81A6FB66A855092E72A89D0517B2E3B292E482 | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:64E9B8BB98E2303717538CE259BEC57D | SHA256:76BD459EC8E467EFC3E3FB94CB21B9C77A2AA73C9D4C0F3FAF823677BE756331 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
113
TCP/UDP connections
258
DNS requests
64
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3340 | iexplore.exe | GET | 200 | 52.222.232.82:80 | http://d36zfztxfflmqo.cloudfront.net/?tzfzd=795152 | US | text | 111 Kb | whitelisted |
3340 | iexplore.exe | GET | 200 | 172.67.190.162:80 | http://strumyk.tv/ | US | html | 6.68 Kb | suspicious |
3340 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3340 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9c7e846ea2b4418e | US | compressed | 4.70 Kb | whitelisted |
3340 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3340 | iexplore.exe | GET | 200 | 172.67.190.162:80 | http://strumyk.tv/layout/style.css?v=181120214 | US | compressed | 1.08 Kb | suspicious |
3340 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?aea0d1d884b99870 | US | compressed | 4.70 Kb | whitelisted |
3340 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?692528cdc0fca6c4 | US | compressed | 4.70 Kb | whitelisted |
3340 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7e6fafe10a4e2fa2 | US | compressed | 4.70 Kb | whitelisted |
3340 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?dcafb0653b166d02 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3340 | iexplore.exe | 172.67.190.162:80 | strumyk.tv | — | US | malicious |
3340 | iexplore.exe | 142.250.181.234:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3340 | iexplore.exe | 151.101.12.193:443 | i.imgur.com | Fastly | US | malicious |
3340 | iexplore.exe | 104.16.125.175:443 | unpkg.com | Cloudflare Inc | US | shared |
3340 | iexplore.exe | 52.222.232.82:80 | d36zfztxfflmqo.cloudfront.net | Amazon.com, Inc. | US | whitelisted |
3340 | iexplore.exe | 216.58.212.136:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3340 | iexplore.exe | 23.109.82.38:80 | malinesmanses.com | — | NL | unknown |
3340 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3340 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3748 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
strumyk.tv |
| suspicious |
ajax.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
unpkg.com |
| whitelisted |
i.imgur.com |
| malicious |
d36zfztxfflmqo.cloudfront.net |
| whitelisted |
malinesmanses.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
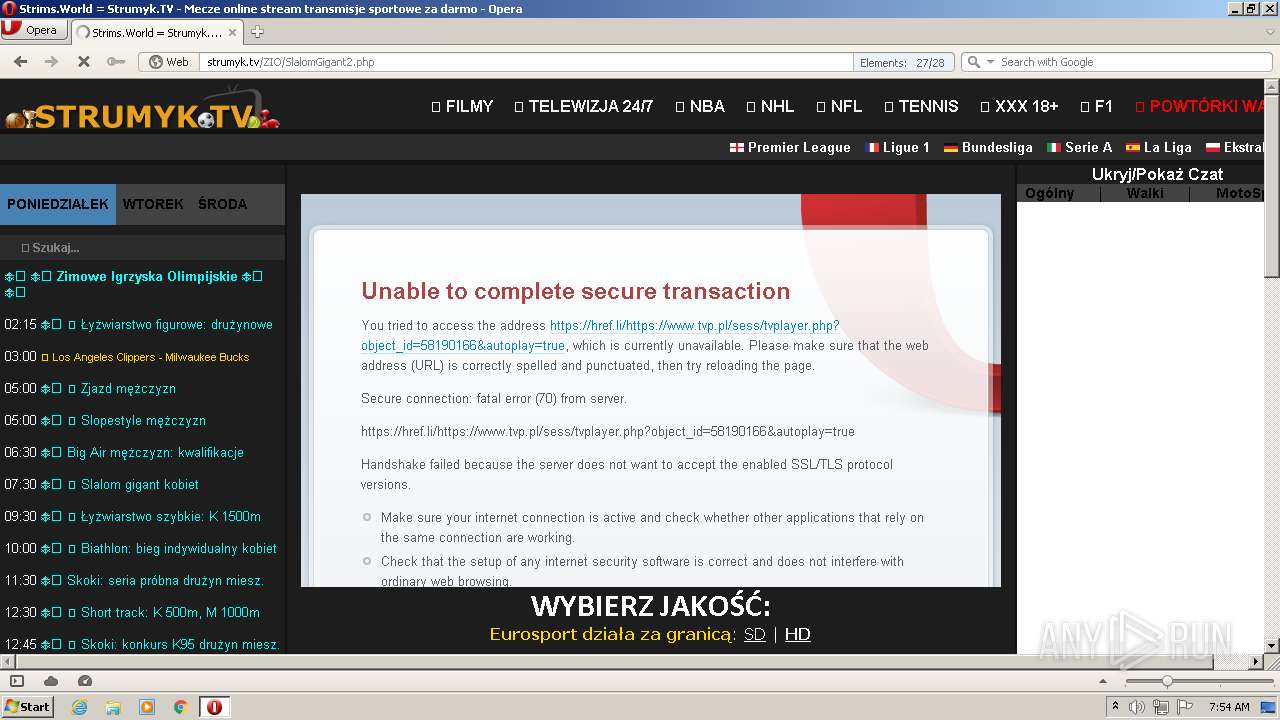
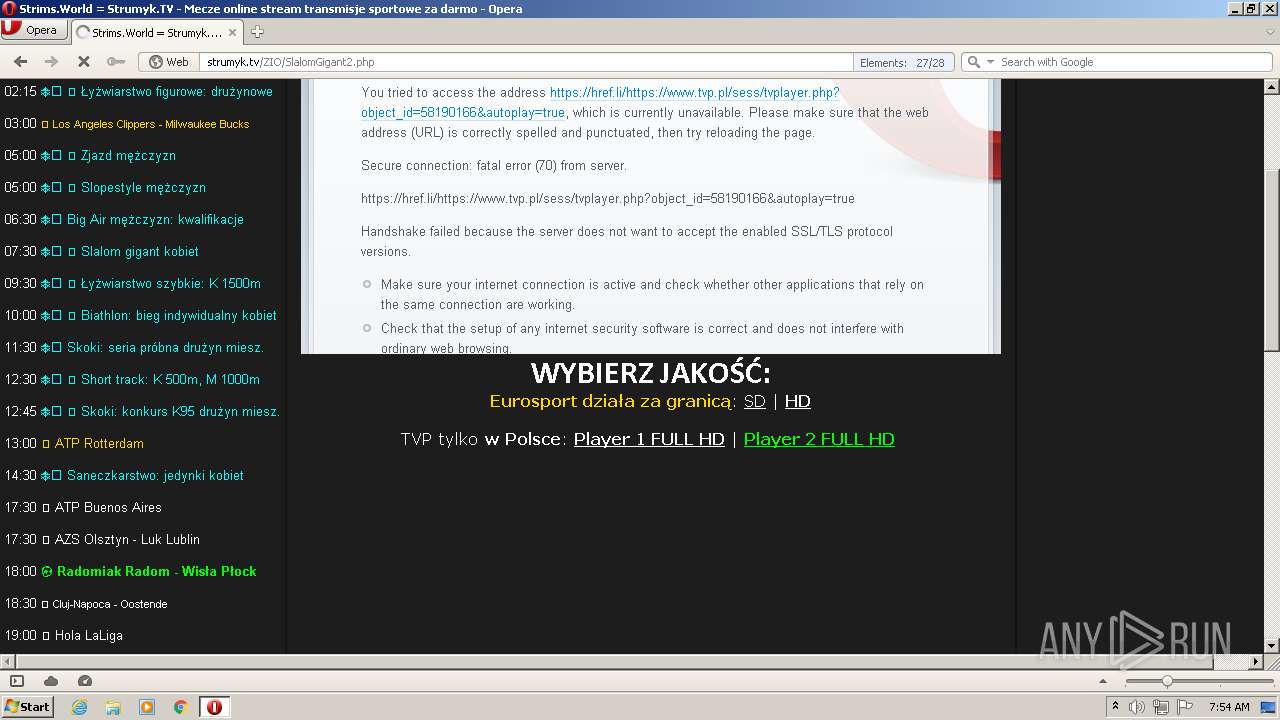
764 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
764 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
764 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
764 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
764 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
764 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
764 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
764 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
764 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
764 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |