| File name: | GetWindows10-sds_____________.exe |
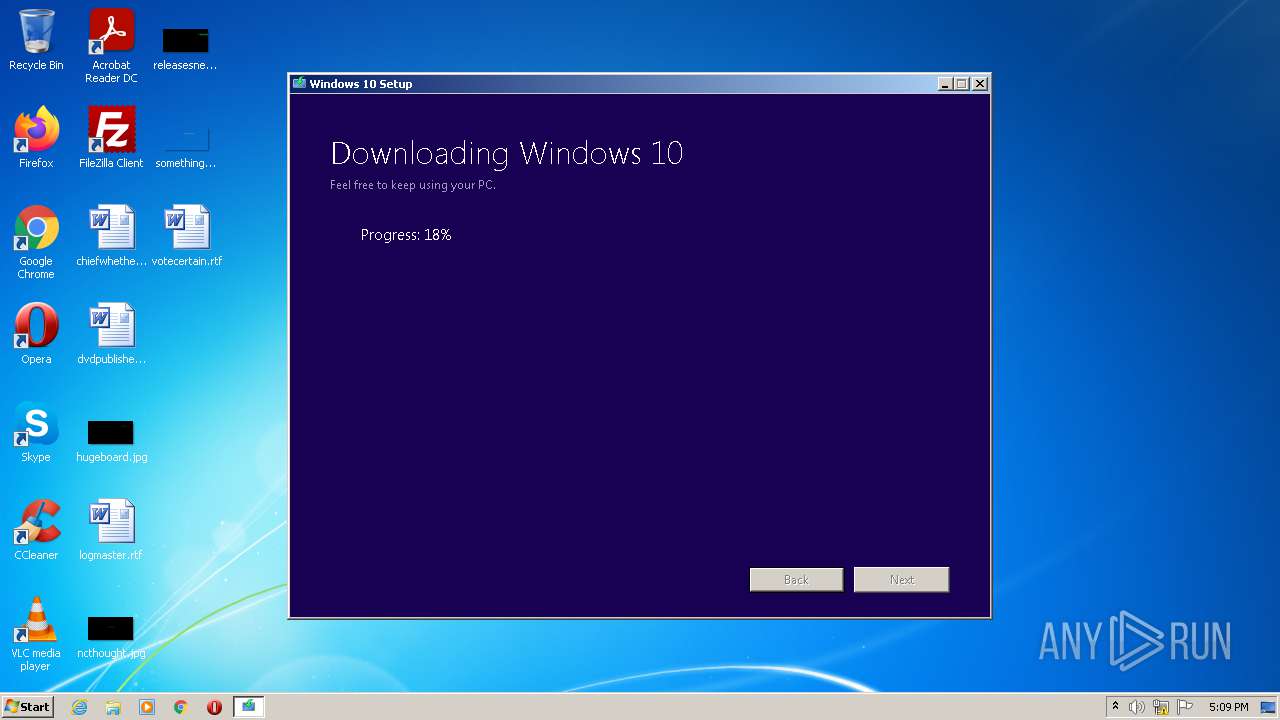
| Full analysis: | https://app.any.run/tasks/b0325dad-666a-4023-8379-b76959a0df24 |
| Verdict: | Malicious activity |
| Analysis date: | August 22, 2021, 16:04:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InstallShield self-extracting archive |
| MD5: | 35D60FD322B1A61AAE7ADF909B6C0B26 |
| SHA1: | 15FF049E49E8B8B0C27AD57E00ABDFD68100EE37 |
| SHA256: | 38C68871831E8B88B2B7165640A2ADC90C0B3EEEA5F1CFDD4CB441817F64BD9A |
| SSDEEP: | 196608:TNwhFDBWruQBvSihWZoeT9PCjTiDYV10NGvb2NqHodyWzYq5SZX3FBwv:T8FDEi6Kiha9qjq81gGKNqHoohmmXVB |
MALICIOUS
Application was dropped or rewritten from another process
- MediaCreationTool.exe (PID: 1592)
- MediaCreationTool.exe (PID: 3212)
- SetupHost.Exe (PID: 3560)
Drops executable file immediately after starts
- MediaCreationTool.exe (PID: 3212)
- GetWindows10-sds_____________.exe (PID: 2736)
Loads dropped or rewritten executable
- SetupHost.Exe (PID: 3560)
SUSPICIOUS
Checks supported languages
- GetWindows10-sds_____________.exe (PID: 2736)
- SetupHost.Exe (PID: 3560)
- MediaCreationTool.exe (PID: 3212)
Drops a file that was compiled in debug mode
- MediaCreationTool.exe (PID: 3212)
- GetWindows10-sds_____________.exe (PID: 2736)
Reads Environment values
- SetupHost.Exe (PID: 3560)
- GetWindows10-sds_____________.exe (PID: 2736)
Executed via COM
- vdsldr.exe (PID: 408)
Reads the computer name
- SetupHost.Exe (PID: 3560)
- MediaCreationTool.exe (PID: 3212)
- GetWindows10-sds_____________.exe (PID: 2736)
Creates files in the Windows directory
- SetupHost.Exe (PID: 3560)
- MediaCreationTool.exe (PID: 3212)
Executable content was dropped or overwritten
- GetWindows10-sds_____________.exe (PID: 2736)
- MediaCreationTool.exe (PID: 3212)
INFO
Dropped object may contain Bitcoin addresses
- MediaCreationTool.exe (PID: 3212)
Checks supported languages
- vdsldr.exe (PID: 408)
Reads the computer name
- vdsldr.exe (PID: 408)
Reads settings of System Certificates
- SetupHost.Exe (PID: 3560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| ProductVersion: | 6.3.9600.18124 |
|---|---|
| ProductName: | Microsoft® Windows® Operating System |
| OriginalFileName: | GWXWebWindows.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| InternalName: | GWXWebWindows.exe |
| FileVersion: | 6.3.9600.18124 (winblue_ltsb.151109-1247) |
| FileDescription: | GWX WEB WINDOWS |
| CompanyName: | Microsoft Corporation |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 6.3.9600.18124 |
| FileVersionNumber: | 6.3.9600.18124 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6.1 |
| ImageVersion: | 6.3 |
| OSVersion: | 6.3 |
| EntryPoint: | 0x89f0 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 10752 |
| CodeSize: | 34304 |
| LinkerVersion: | 11 |
| PEType: | PE32 |
| TimeStamp: | 2015:11:10 00:36:53+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Nov-2015 23:36:53 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | GWX WEB WINDOWS |
| FileVersion: | 6.3.9600.18124 (winblue_ltsb.151109-1247) |
| InternalName: | GWXWebWindows.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | GWXWebWindows.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.3.9600.18124 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 09-Nov-2015 23:36:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000084D4 | 0x00008600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35626 |
.data | 0x0000A000 | 0x000003FC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.249053 |
.idata | 0x0000B000 | 0x00000C84 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.88689 |
.boxloadP | 0x0000C000 | 0x00000050 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.835156 |
.rsrc | 0x0000D000 | 0x00000CD8 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.41267 |
.reloc | 0x0000E000 | 0x00000680 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.99086 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.61793 | 932 | UNKNOWN | English - United States | RT_VERSION |
Imports
ADVAPI32.dll |
Cabinet.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WIMGAPI.DLL |
msvcrt.dll |
ntdll.dll |
ole32.dll |
Total processes
43
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | C:\Windows\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Virtual Disk Service Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1592 | "C:\$Windows.~GWX\Sources\MediaCreationTool.exe" /Action UpgradeNow /ClientID web.sds_____________ | C:\$Windows.~GWX\Sources\MediaCreationTool.exe | — | GetWindows10-sds_____________.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows 10 Setup Exit code: 3221226540 Version: 10.0.10586.0 (th2_release.151029-1700) Modules
| |||||||||||||||
| 2736 | "C:\Users\admin\AppData\Local\Temp\GetWindows10-sds_____________.exe" | C:\Users\admin\AppData\Local\Temp\GetWindows10-sds_____________.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: GWX WEB WINDOWS Exit code: 0 Version: 6.3.9600.18124 (winblue_ltsb.151109-1247) Modules
| |||||||||||||||
| 3212 | "C:\$Windows.~GWX\Sources\MediaCreationTool.exe" /Action UpgradeNow /ClientID web.sds_____________ | C:\$Windows.~GWX\Sources\MediaCreationTool.exe | GetWindows10-sds_____________.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows 10 Setup Exit code: 0 Version: 10.0.10586.0 (th2_release.151029-1700) Modules
| |||||||||||||||
| 3560 | "C:\$Windows.~WS\Sources\SetupHost.Exe" /Download /Web /ProcessId 3212 "/Action" "UpgradeNow" "/ClientID" "web.sds_____________" /SuccessId 80e68fae-b197-4b7f-9e04-c4c13e8f0541 | C:\$Windows.~WS\Sources\SetupHost.Exe | MediaCreationTool.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Modern Setup Host Exit code: 0 Version: 10.0.10586.0 (th2_release.151029-1700) Modules
| |||||||||||||||
Total events
3 346
Read events
3 265
Write events
81
Delete events
0
Modification events
| (PID) Process: | (2736) GetWindows10-sds_____________.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2736) GetWindows10-sds_____________.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2736) GetWindows10-sds_____________.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2736) GetWindows10-sds_____________.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3212) MediaCreationTool.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\VolumeCaches\Temporary Setup Files |
| Operation: | write | Name: | SetupDirectories |
Value: $Windows.~BT;$Windows.~LS;$Windows.~WS | |||
| (PID) Process: | (3560) SetupHost.Exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\MoSetup |
| Operation: | write | Name: | CorrelationVector |
Value: 4L+tAveROk6wHAND.0 | |||
| (PID) Process: | (3560) SetupHost.Exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3560) SetupHost.Exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\MoSetup\Volatile |
| Operation: | write | Name: | InstallTicks |
Value: 1 | |||
| (PID) Process: | (3560) SetupHost.Exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\MoSetup\Volatile |
| Operation: | write | Name: | InstallTicks |
Value: 2 | |||
| (PID) Process: | (3560) SetupHost.Exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\MoSetup\Volatile |
| Operation: | write | Name: | InstallTicks |
Value: 3 | |||
Executable files
39
Suspicious files
0
Text files
5
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3212 | MediaCreationTool.exe | C:\$Windows.~WS\Sources\Diager.dll | executable | |
MD5:— | SHA256:— | |||
| 3212 | MediaCreationTool.exe | C:\$Windows.~WS\Sources\api-ms-win-core-apiquery-l1-1-0.dll | executable | |
MD5:— | SHA256:— | |||
| 2736 | GetWindows10-sds_____________.exe | C:\$Windows.~GWX\Sources\MediaCreationTool.exe | executable | |
MD5:— | SHA256:— | |||
| 3212 | MediaCreationTool.exe | C:\$Windows.~WS\Sources\DiagTrackRunner.exe | executable | |
MD5:76F30A1E149792D2542A253B920CBEF6 | SHA256:488CBC8330952DD13B797BB40E4E30610ED03483C25919C39555F7B334A3C159 | |||
| 3212 | MediaCreationTool.exe | C:\$Windows.~WS\Sources\api-ms-win-downlevel-advapi32-l2-1-0.dll | executable | |
MD5:— | SHA256:— | |||
| 3212 | MediaCreationTool.exe | C:\$Windows.~WS\Sources\api-ms-win-downlevel-advapi32-l1-1-0.dll | executable | |
MD5:— | SHA256:— | |||
| 3212 | MediaCreationTool.exe | C:\$Windows.~WS\Sources\Diagnostic.dll | executable | |
MD5:— | SHA256:— | |||
| 3212 | MediaCreationTool.exe | C:\$Windows.~WS\Sources\DU.dll | executable | |
MD5:— | SHA256:— | |||
| 3212 | MediaCreationTool.exe | C:\$Windows.~WS\Sources\DiagTrack.dll | executable | |
MD5:6C3F6A6BC5EDE978E9DFE1ACCE386339 | SHA256:B55D66F2943F1C63EA9B39DAE88AA2A4F91775CEFFFEFD263BD302866A7BD91C | |||
| 3212 | MediaCreationTool.exe | C:\$Windows.~WS\Sources\api-ms-win-downlevel-advapi32-l4-1-0.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
896 | svchost.exe | HEAD | 200 | 67.26.81.254:80 | http://fg.ds.b1.download.windowsupdate.com/d/updt/2016/05/10586.0.160426-1409.th2_refresh_clientmulti_ret_x86fre_en-us_504531540613228d6c6417ef6853c82e6bea41b4.esd | US | — | — | whitelisted |
896 | svchost.exe | GET | — | 67.26.81.254:80 | http://fg.ds.b1.download.windowsupdate.com/d/updt/2016/05/10586.0.160426-1409.th2_refresh_clientmulti_ret_x86fre_en-us_504531540613228d6c6417ef6853c82e6bea41b4.esd | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3560 | SetupHost.Exe | 104.111.218.212:443 | wscont.apps.microsoft.com | Akamai International B.V. | NL | unknown |
896 | svchost.exe | 67.26.81.254:80 | fg.ds.b1.download.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3560 | SetupHost.Exe | 104.111.242.51:443 | go.microsoft.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
wscont.apps.microsoft.com |
| whitelisted |
fg.ds.b1.download.windowsupdate.com |
| whitelisted |