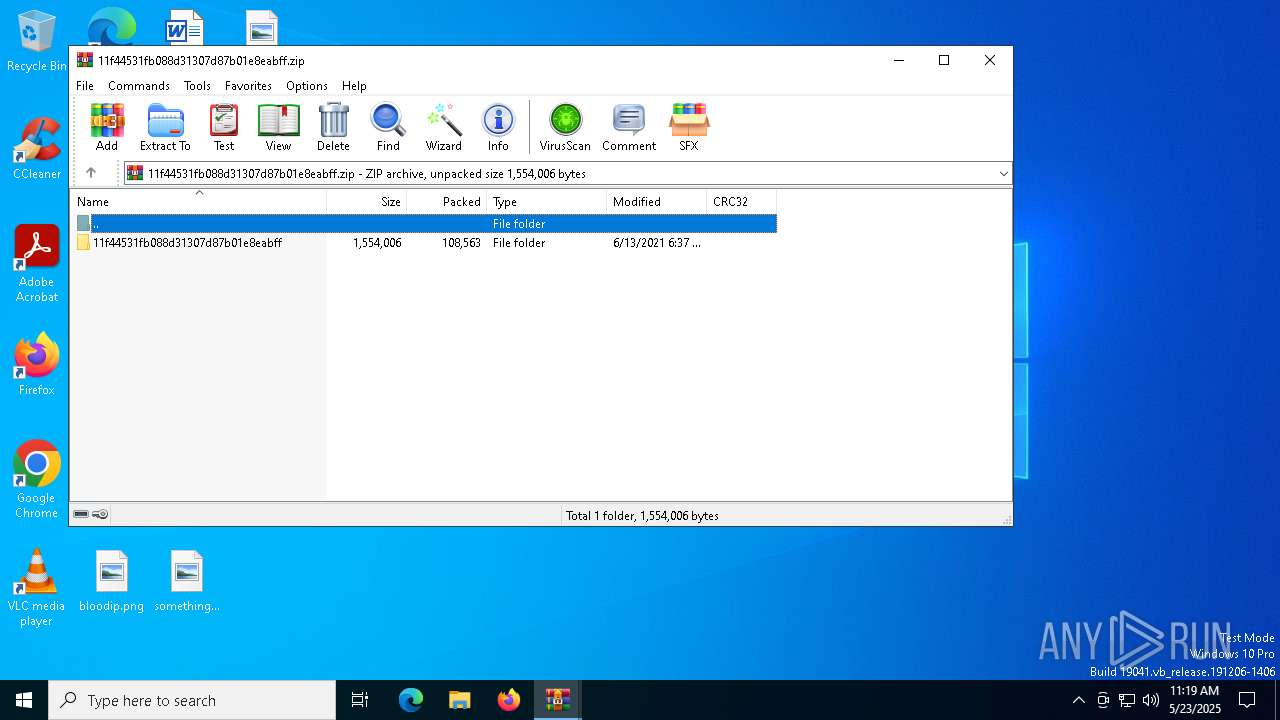
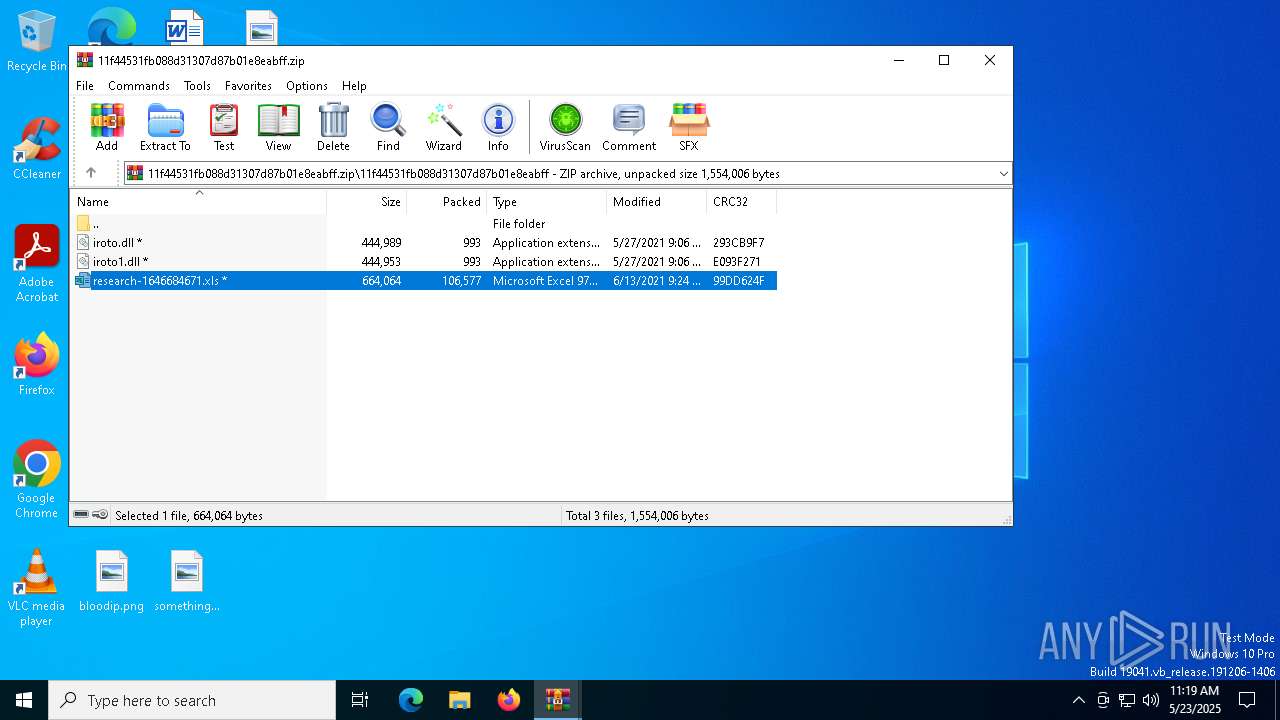
| File name: | 11f44531fb088d31307d87b01e8eabff.zip.zip |
| Full analysis: | https://app.any.run/tasks/f4fbbe7d-685c-4694-8f96-7c8efb167dfa |
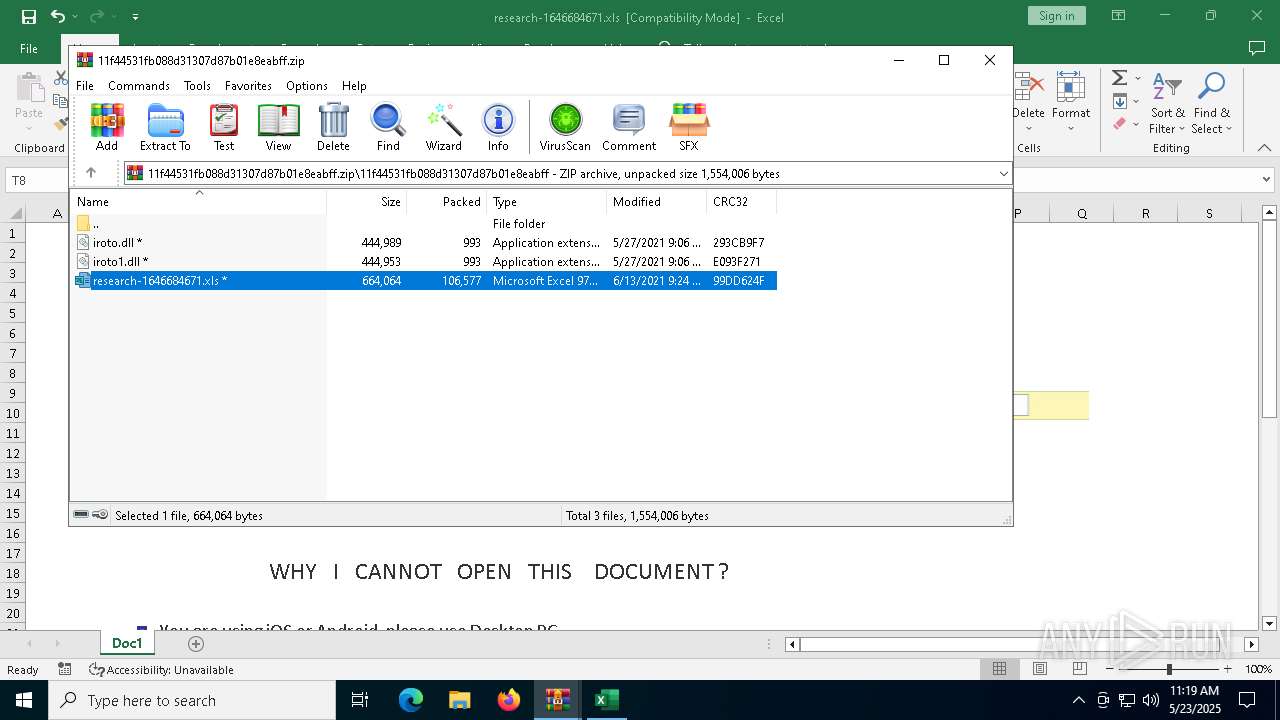
| Verdict: | Malicious activity |
| Analysis date: | May 23, 2025, 11:19:04 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
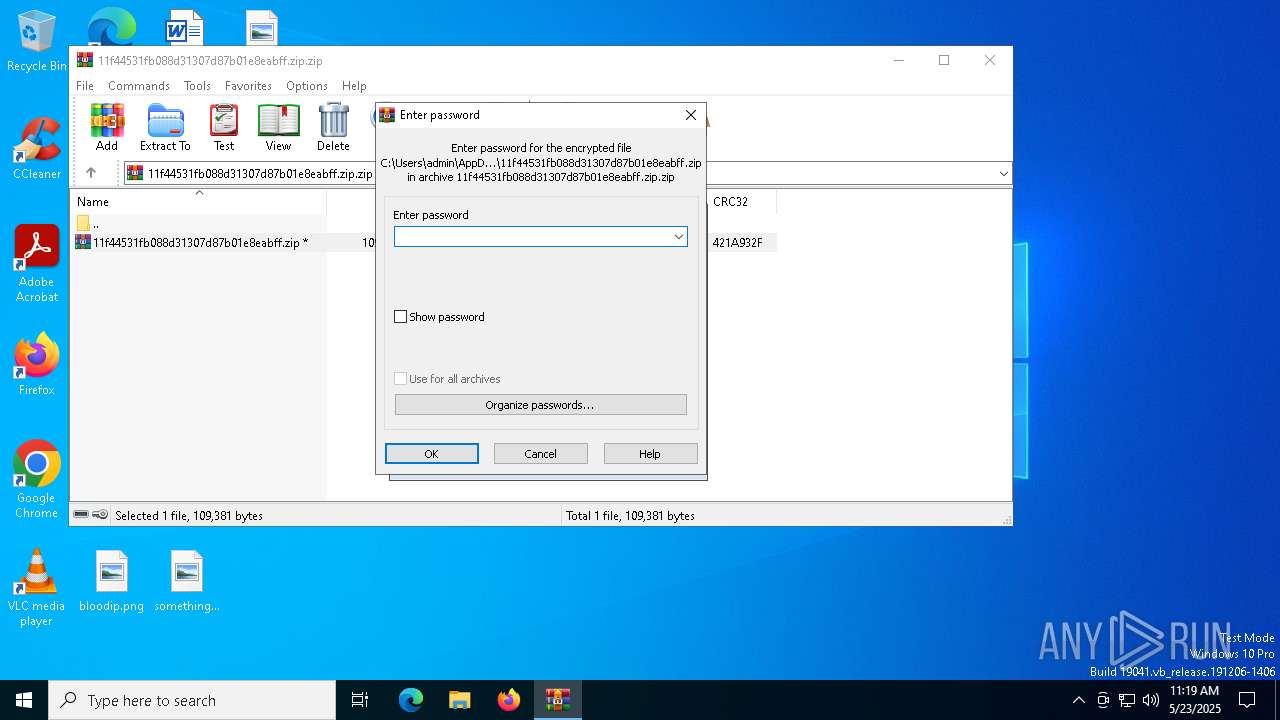
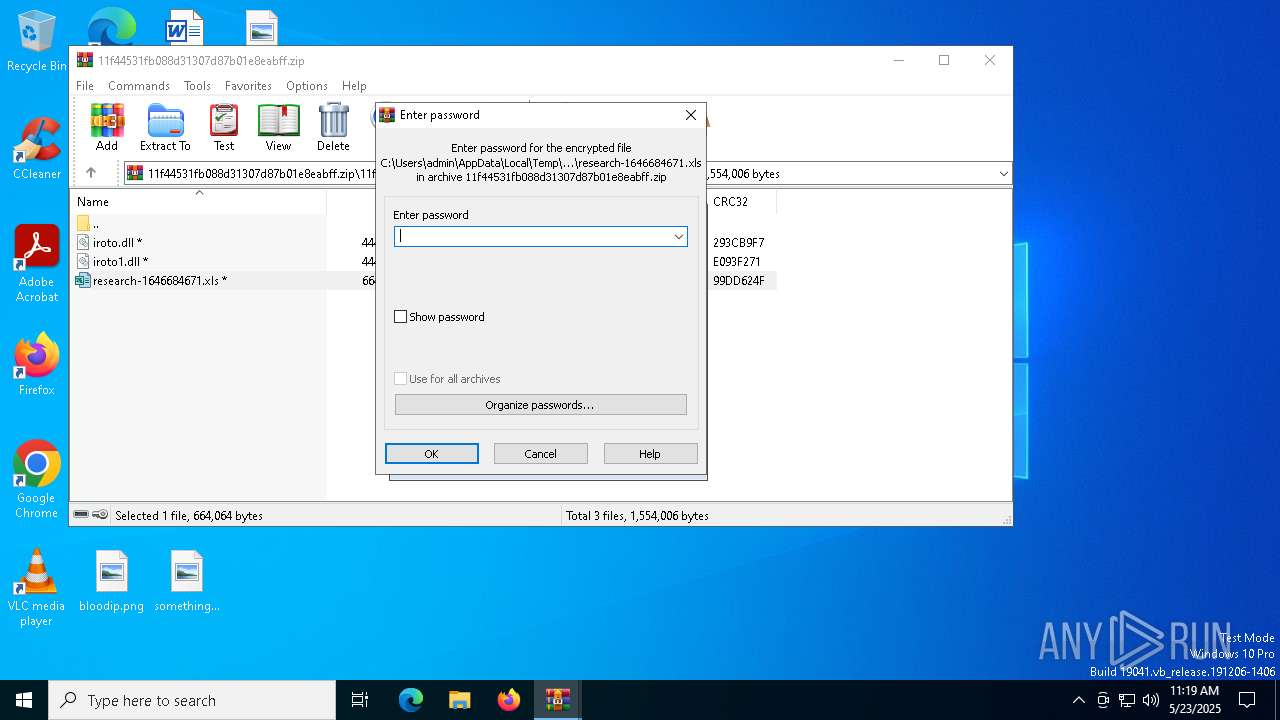
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 0CBEDE8A169ECBBABD533AA9202D9015 |
| SHA1: | 6C75C16101B222CDFAD0044B30B4C490D3D37097 |
| SHA256: | 38B01A12B8DCD39EBDCF9E97772E848237330EB227E1CCEE80125564B27377E5 |
| SSDEEP: | 3072:h8xXZyytZ551PJxnd+HEOA2ewGGetw/Ycw8lEbbvBjFUQlqnV:Cl9B2HQRwG9a/JEbDJFgV |
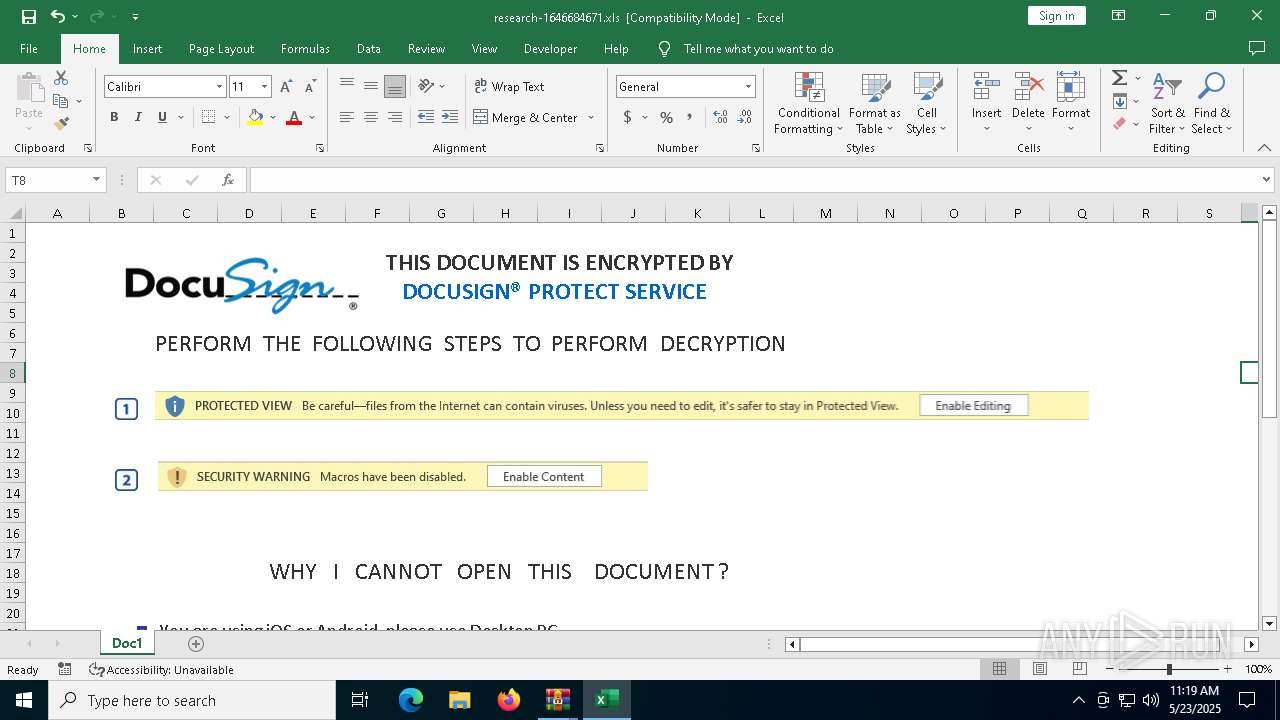
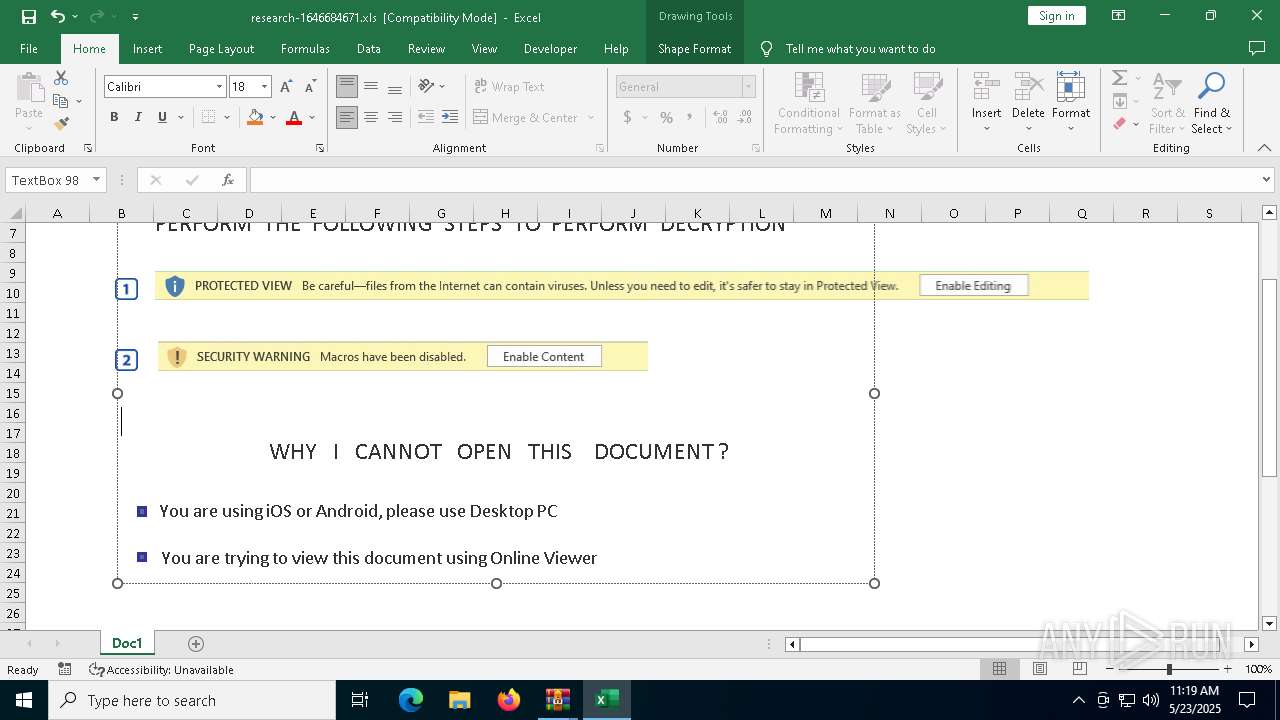
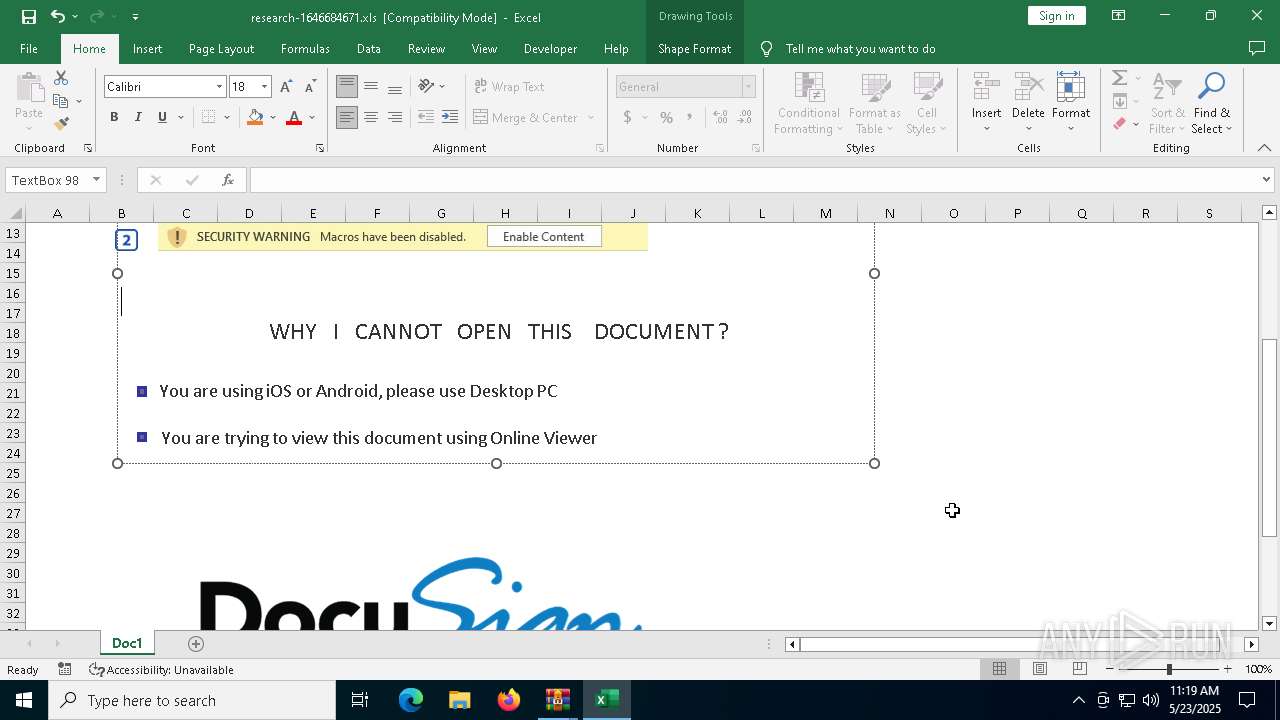
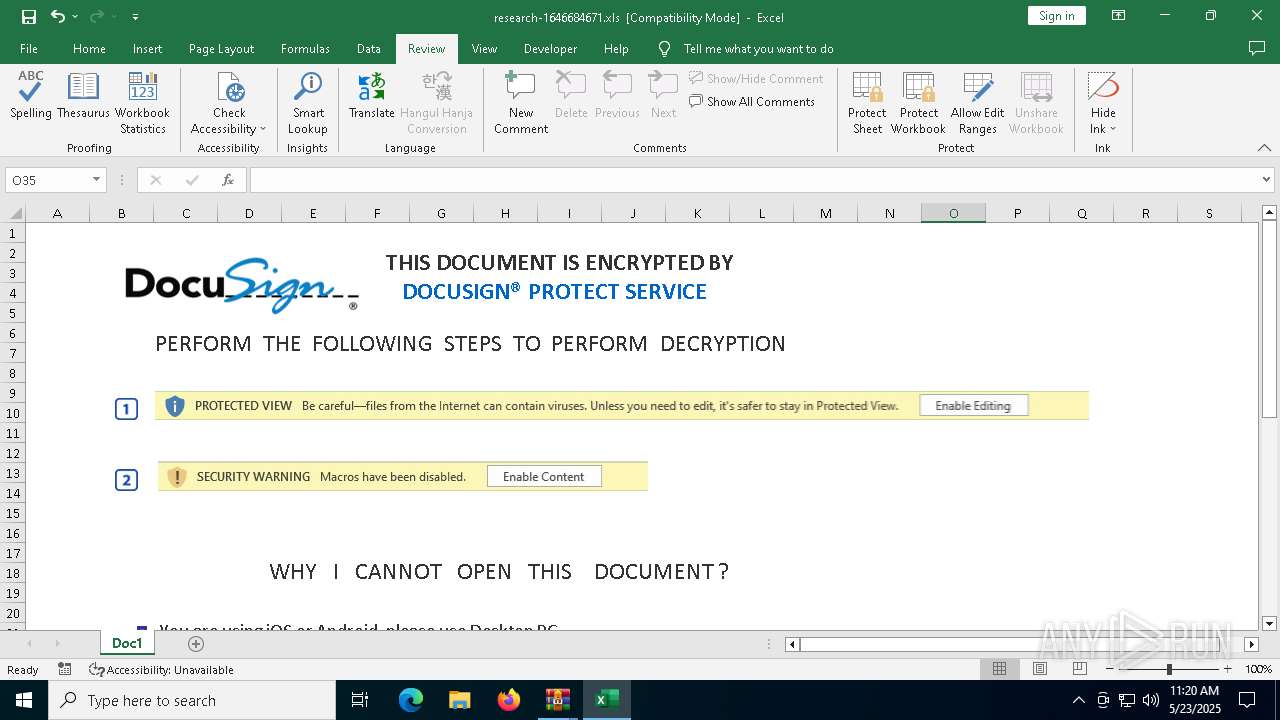
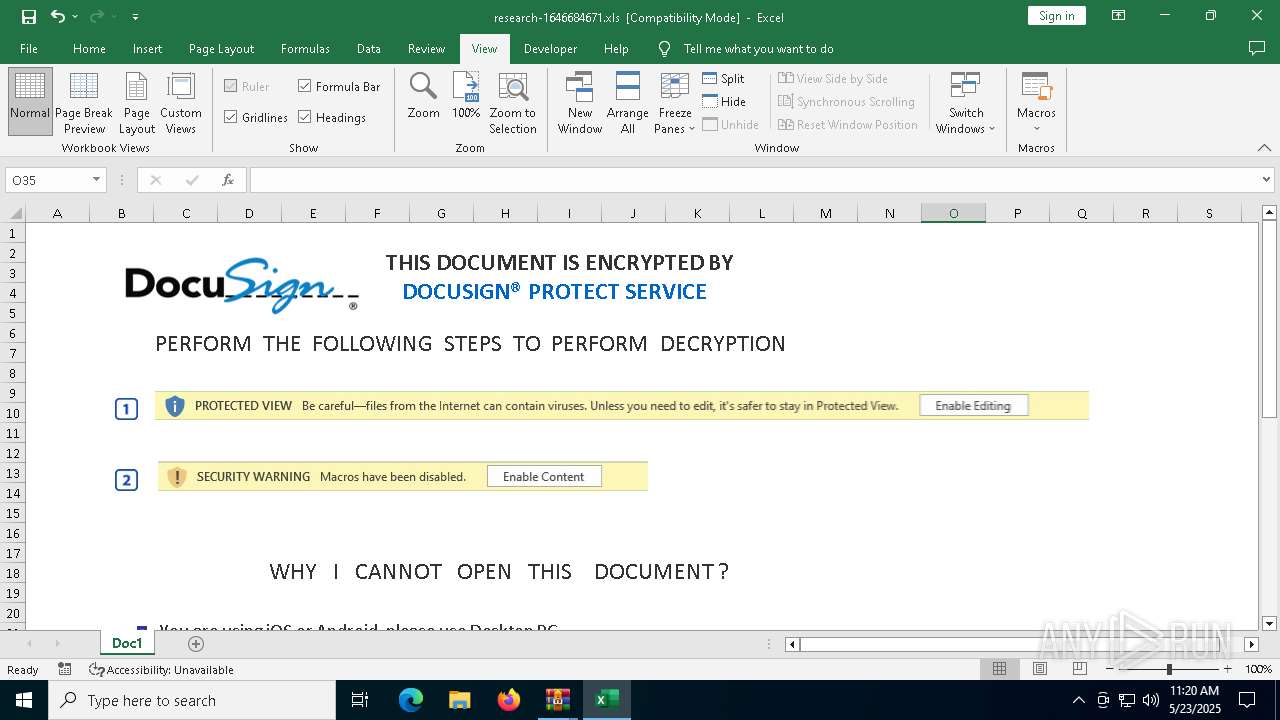
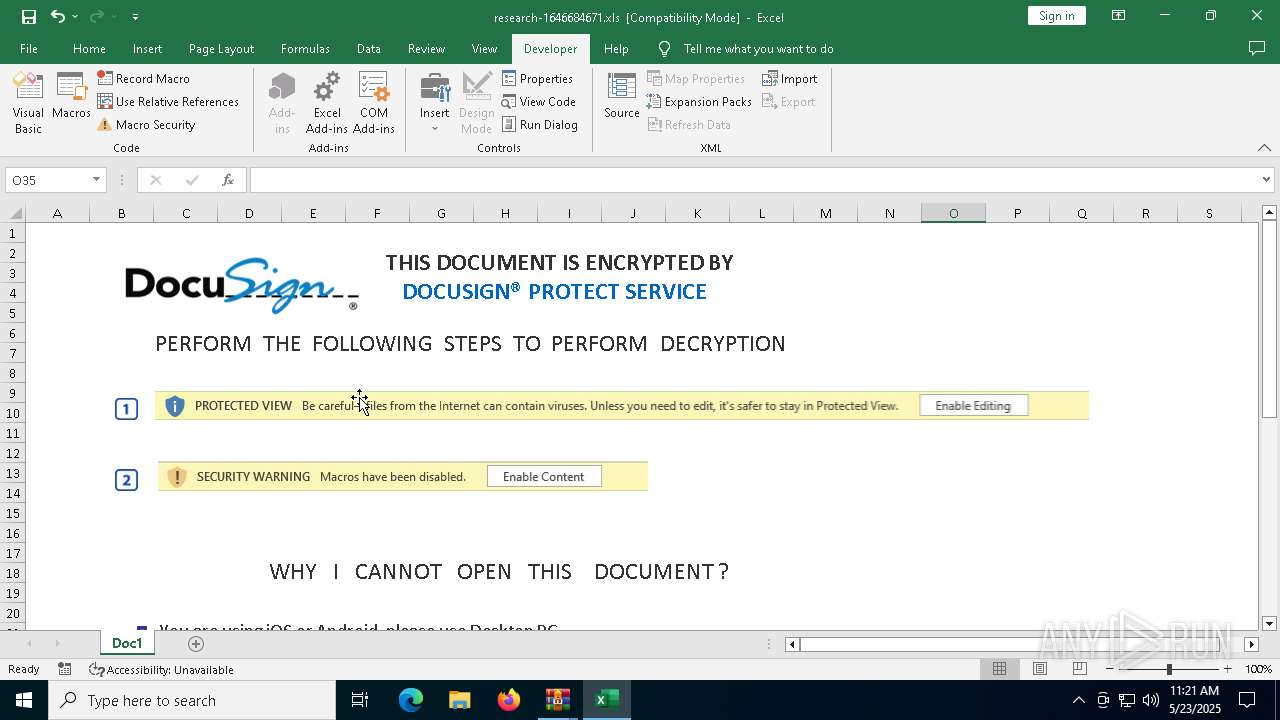
MALICIOUS
GENERIC has been found (auto)
- WinRAR.exe (PID: 7408)
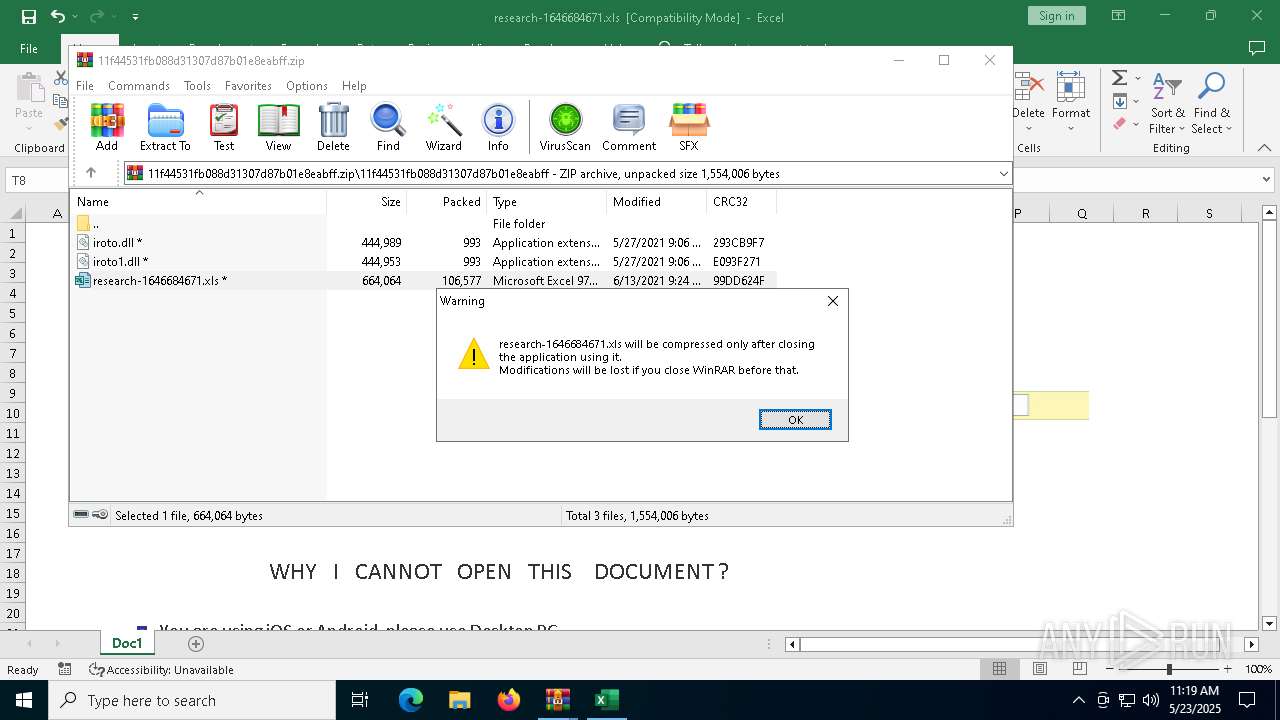
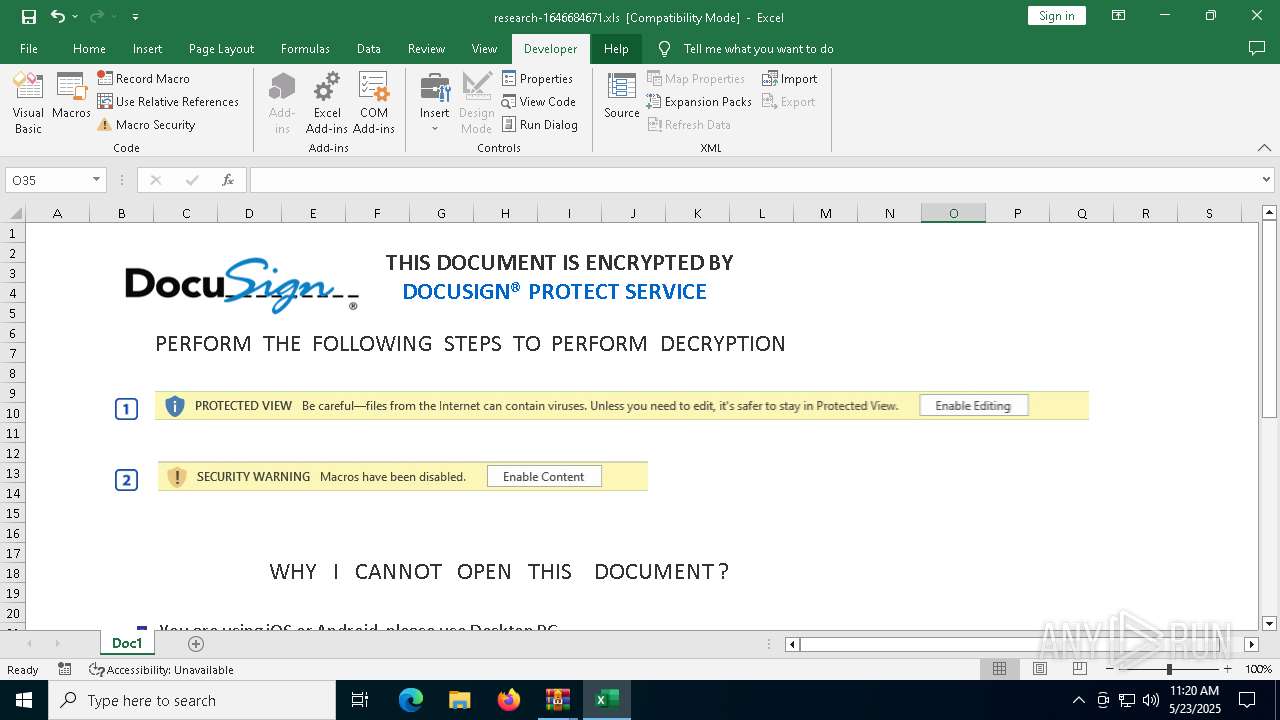
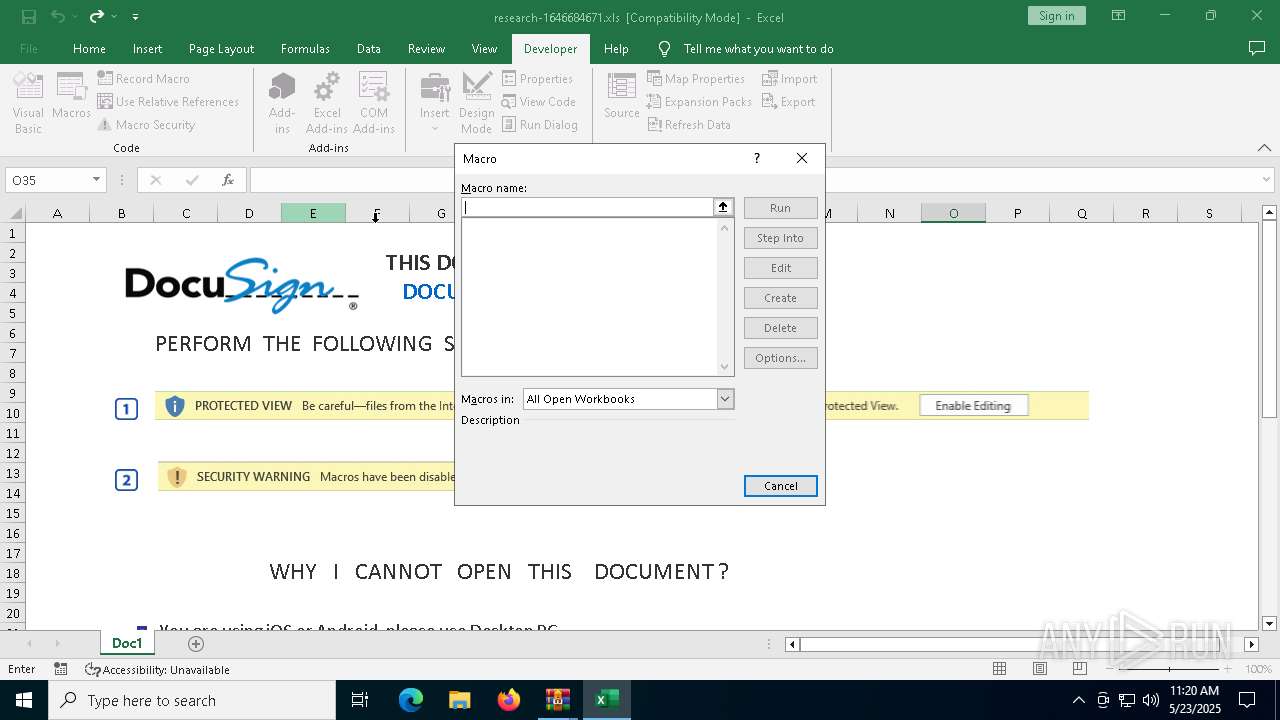
Calls Win API functions (MACROS)
- EXCEL.EXE (PID: 7904)
Unusual execution from MS Office
- EXCEL.EXE (PID: 7904)
Registers / Runs the DLL via REGSVR32.EXE
- EXCEL.EXE (PID: 7904)
SUSPICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7408)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7748)
- WinRAR.exe (PID: 7408)
Application launched itself
- WinRAR.exe (PID: 7408)
Sets XML DOM element text (SCRIPT)
- splwow64.exe (PID: 1188)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 7748)
Reads the software policy settings
- slui.exe (PID: 7652)
Reads security settings of Internet Explorer
- splwow64.exe (PID: 1188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
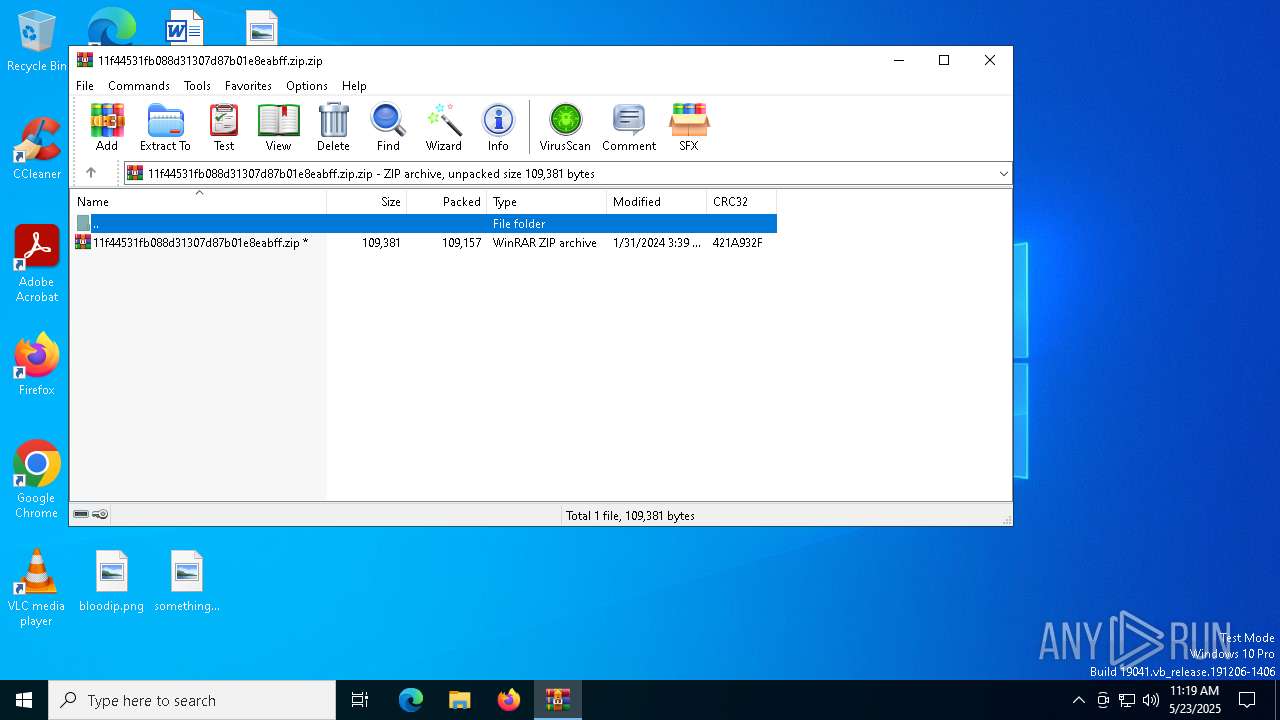
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2024:01:31 15:39:40 |
| ZipCRC: | 0x421a932f |
| ZipCompressedSize: | 109157 |
| ZipUncompressedSize: | 109381 |
| ZipFileName: | 11f44531fb088d31307d87b01e8eabff.zip |
Total processes
143
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 896 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 1188 | C:\WINDOWS\splwow64.exe 8192 | C:\Windows\splwow64.exe | — | EXCEL.EXE |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Print driver host for applications Version: 10.0.19041.3636 (WinBuild.160101.0800) | ||||
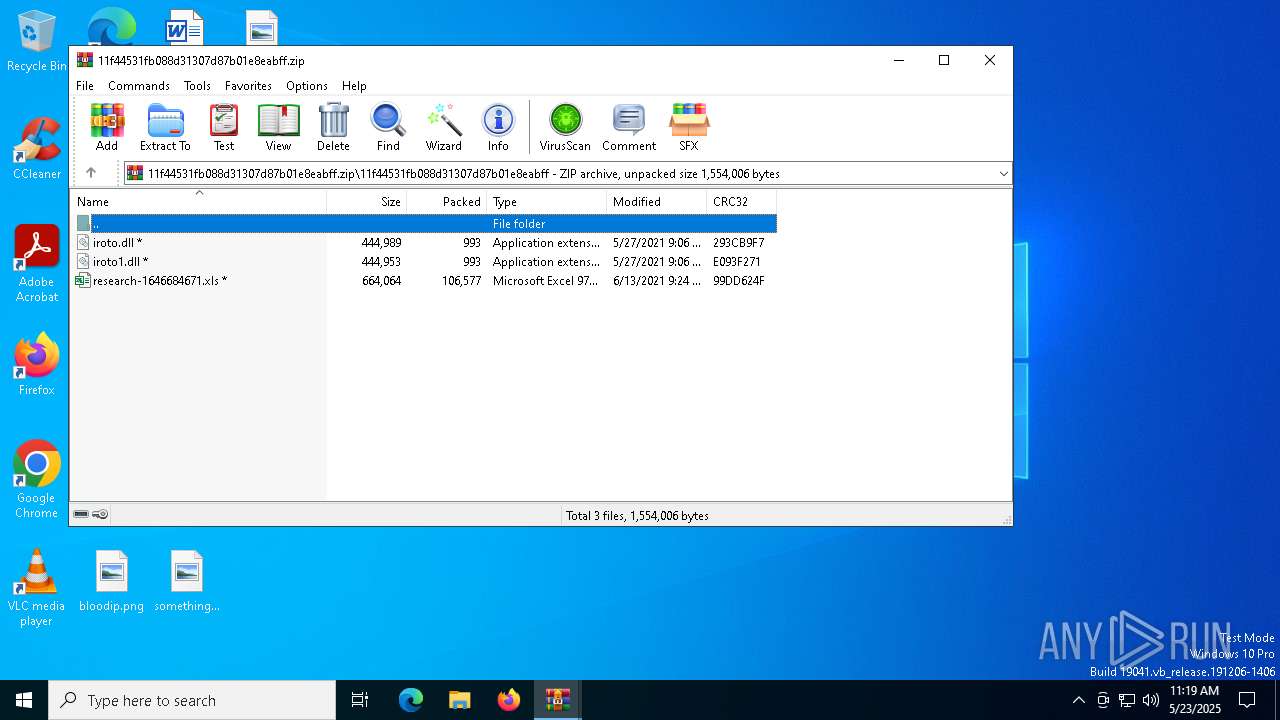
| 5968 | regsvr32 -s ..\iroto.dll | C:\Windows\System32\regsvr32.exe | — | EXCEL.EXE |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 3 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 6828 | regsvr32 -s ..\iroto1.dll | C:\Windows\System32\regsvr32.exe | — | EXCEL.EXE |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 3 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
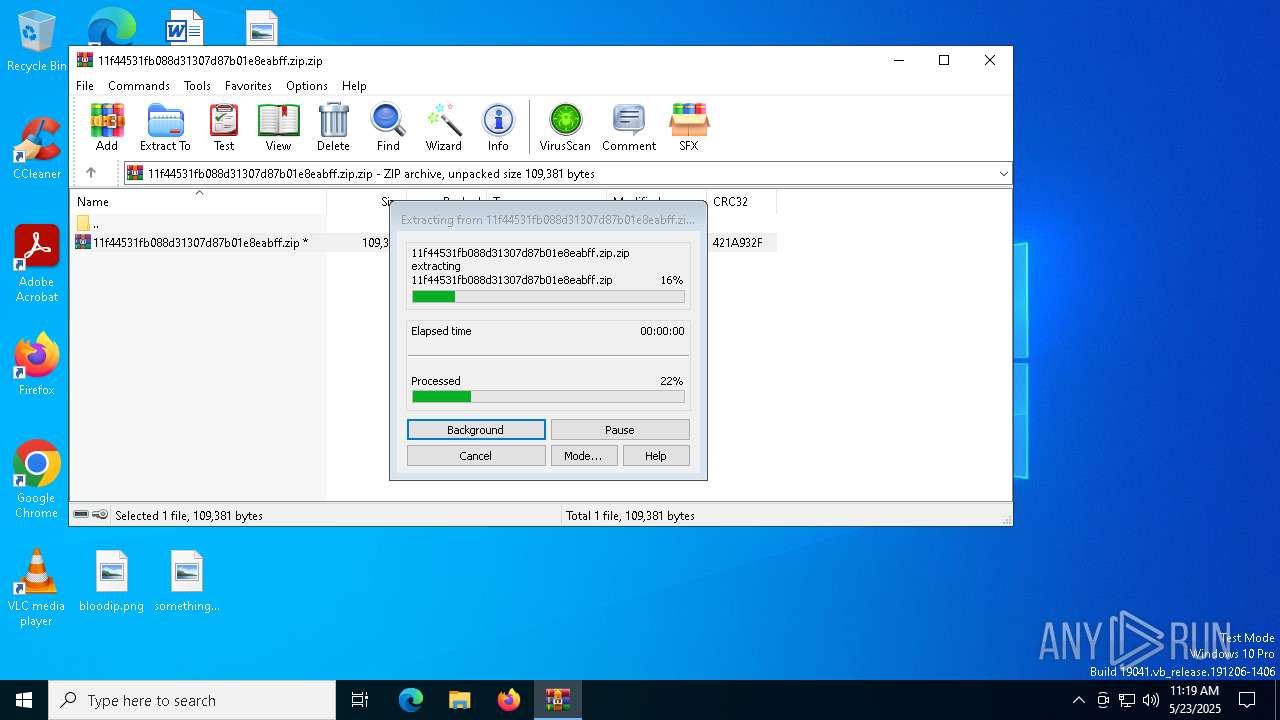
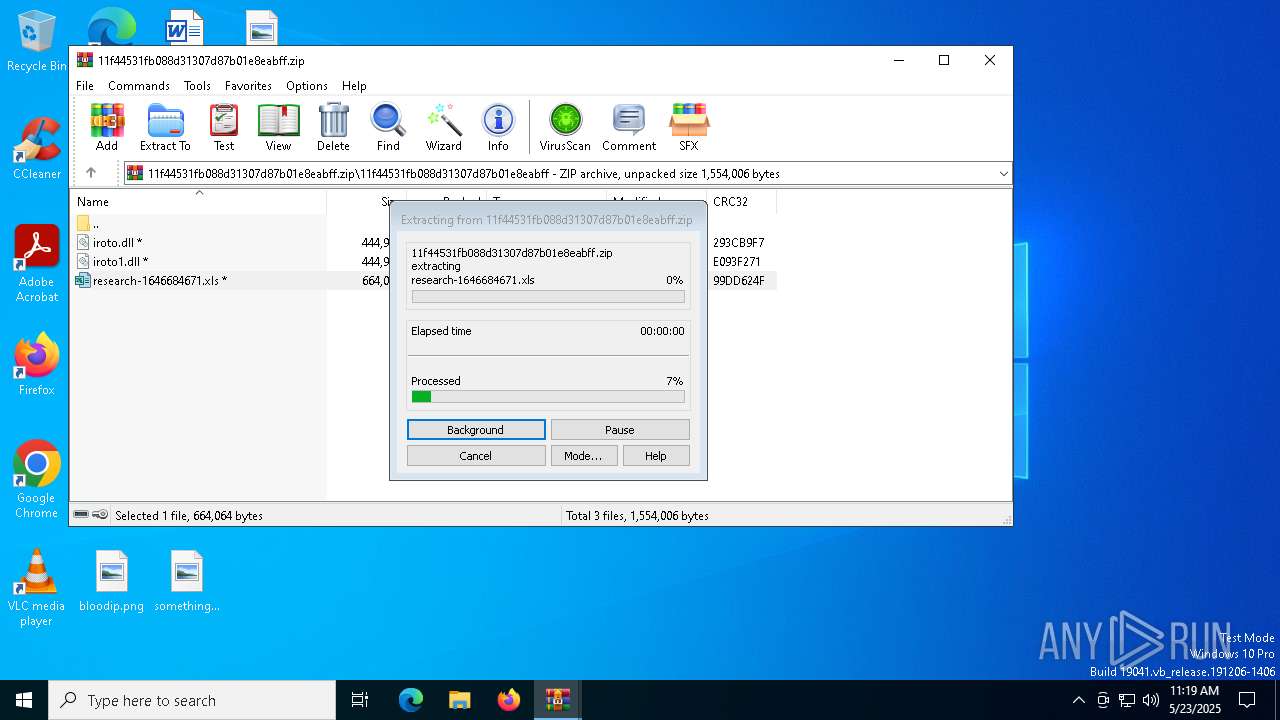
| 7408 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\11f44531fb088d31307d87b01e8eabff.zip.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe |
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 | ||||
| 7620 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe |
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) | ||||
| 7652 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | |
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 7748 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIb7408.46516\11f44531fb088d31307d87b01e8eabff.zip | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe |
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 | ||||
| 7904 | "C:\Program Files\Microsoft Office\Root\Office16\EXCEL.EXE" "C:\Users\admin\AppData\Local\Temp\Rar$DIb7748.47777\research-1646684671.xls" | C:\Program Files\Microsoft Office\root\Office16\EXCEL.EXE | WinRAR.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Version: 16.0.16026.20146 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
18
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7748 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb7748.47777\research-1646684671.xls | document | |
MD5:B775CD8BE83696CA37B2FE00BCB40574 | SHA256:1DF68D55968BB9D2DB4D0D18155188A03A442850FF543C8595166AC6987DF820 | |||
| 7904 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:524741401626660C8F189DC49DAEAC1E | SHA256:A23F556853D09FC4A4680038960452A51EBCBB92995F98BA6067FF9ECDDFB41E | |||
| 7904 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:D9422B60DC0E9D49E09CCB45B63D81DE | SHA256:3702C785862C38FD5AA2EE2D8E8B40F921ABDE53D9AF140501A965AE3E0BD9B3 | |||
| 7904 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:3247839F10D41AF99F26A4C84F17B253 | SHA256:6F93C9A3DE45A03826B175BEAD8D005D7A8500575BA1D2FA9F515B42B25D7E75 | |||
| 7904 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Personalization\Governance\Anonymous\floodgatecampaigns.json | binary | |
MD5:BC62041B7D4A7E1350226C538498DA6D | SHA256:E1D4562765D71DDBB85ABA01D8567489C70B1A21E49C97E132229113BA162D10 | |||
| 7904 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\Personalization\Governance\Anonymous\floodgatecampaigns.json.tmp | binary | |
MD5:BC62041B7D4A7E1350226C538498DA6D | SHA256:E1D4562765D71DDBB85ABA01D8567489C70B1A21E49C97E132229113BA162D10 | |||
| 7904 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\48GBX87AIAQ3CXCQR8G2.temp | binary | |
MD5:4FCB2A3EE025E4A10D21E1B154873FE2 | SHA256:90BF6BAA6F968A285F88620FBF91E1F5AA3E66E2BAD50FD16F37913280AD8228 | |||
| 7904 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | binary | |
MD5:FD5594ABA2D5D8428CE2E0AFBE7F2C58 | SHA256:5826E1CD895D20532DDE48E1DA4BCF311A42660F6F5EC6BEB9226F253B05E023 | |||
| 7904 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\SmartLookupCache\dictionary_words_bloom_filter.data | binary | |
MD5:A4AF96BCD3EE55F0CB99B37C806A82A5 | SHA256:1BE6D822C31EDC308903E04B986F13388B216DB44019E2BCC3C060284B480BA6 | |||
| 7904 | EXCEL.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_0FB9553B978E7F00C6B2309507DEB64A | binary | |
MD5:DF5D4D2ECFAEB99F572BB42026761F43 | SHA256:7318326CCA9F881C361997F46A6EEE5739233A22E64522CA0790A0E8D957A156 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
34
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7948 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7904 | EXCEL.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7904 | EXCEL.EXE | GET | 200 | 2.19.105.127:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
7948 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7904 | EXCEL.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7000 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5796 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.31.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |