| URL: | https://nine100.com |
| Full analysis: | https://app.any.run/tasks/1eedad21-d125-4a17-9791-bdab7e9e065b |
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2024, 10:07:28 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| MD5: | 3874EAD604F2EDB00A51C9EB298E32E9 |
| SHA1: | 6B4B7CD27FC537608BF6878E99B3415D1DFDFF8E |
| SHA256: | 38908278CA3A37D37C382A8D151FE1DD10251DD005B15FBC94CC0B7A47BAB3B6 |
| SSDEEP: | 3:N8i+:2X |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
303
Monitored processes
84
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 9261 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome \"https://nine100\.com\" " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN | ||||
| 9262 | sudo -iu user google-chrome https://nine100.com | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN | ||||
| 9263 | /usr/bin/google-chrome https://nine100.com | /opt/google/chrome/chrome | — | sudo |
User: user Integrity Level: UNKNOWN | ||||
| 9264 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9265 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9266 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9267 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9268 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 9269 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 9270 | /opt/google/chrome/chrome | — | chrome | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 9263 | chrome | /9263/fd/63 | — | |
MD5:— | SHA256:— | |||
| 9263 | chrome | /home/user/.config/google-chrome/BrowserMetrics/BrowserMetrics-661BAAE6-242F.pma | — | |
MD5:— | SHA256:— | |||
| 9263 | chrome | /.com.google.Chrome.3W6Rza | — | |
MD5:— | SHA256:— | |||
| 9263 | chrome | /home/user/.config/google-chrome/Default/Sync Data/LevelDB/LOG | — | |
MD5:— | SHA256:— | |||
| 9263 | chrome | /.com.google.Chrome.3MuWA7 | — | |
MD5:— | SHA256:— | |||
| 9263 | chrome | /.com.google.Chrome.BykFXc | — | |
MD5:— | SHA256:— | |||
| 9263 | chrome | /.com.google.Chrome.OWAJfw | — | |
MD5:— | SHA256:— | |||
| 9263 | chrome | /home/user/.config/google-chrome/Default/Site Characteristics Database/LOG | — | |
MD5:— | SHA256:— | |||
| 9263 | chrome | /home/user/.config/google-chrome/Default/commerce_subscription_db/LOG | — | |
MD5:— | SHA256:— | |||
| 9263 | chrome | /home/user/.config/google-chrome/Default/discounts_db/LOG | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
42
DNS requests
64
Threats
19
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.188.55:443 | — | Canonical Group Limited | GB | unknown |
— | — | 239.255.255.250:1900 | — | — | — | unknown |
— | — | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
— | — | 188.114.97.3:443 | nine100.com | — | — | unknown |
— | — | 142.250.186.35:443 | clientservices.googleapis.com | GOOGLE | US | unknown |
— | — | 188.114.96.3:443 | nine100.com | — | — | unknown |
— | — | 142.250.185.163:443 | fonts.gstatic.com | GOOGLE | US | unknown |
— | — | 193.106.175.140:443 | apistoragecache.com | IQHost Ltd | RU | unknown |
— | — | 142.250.186.78:443 | www.google-analytics.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.snapcraft.io |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
nine100.com |
| unknown |
apistoragecache.com |
| unknown |
secure.gdcstatic.com |
| unknown |
fonts.gstatic.com |
| whitelisted |
cdn.specialtaskevents.com |
| unknown |
bind.bestresulttostart.com |
| unknown |
stake.libertariancounterpoint.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
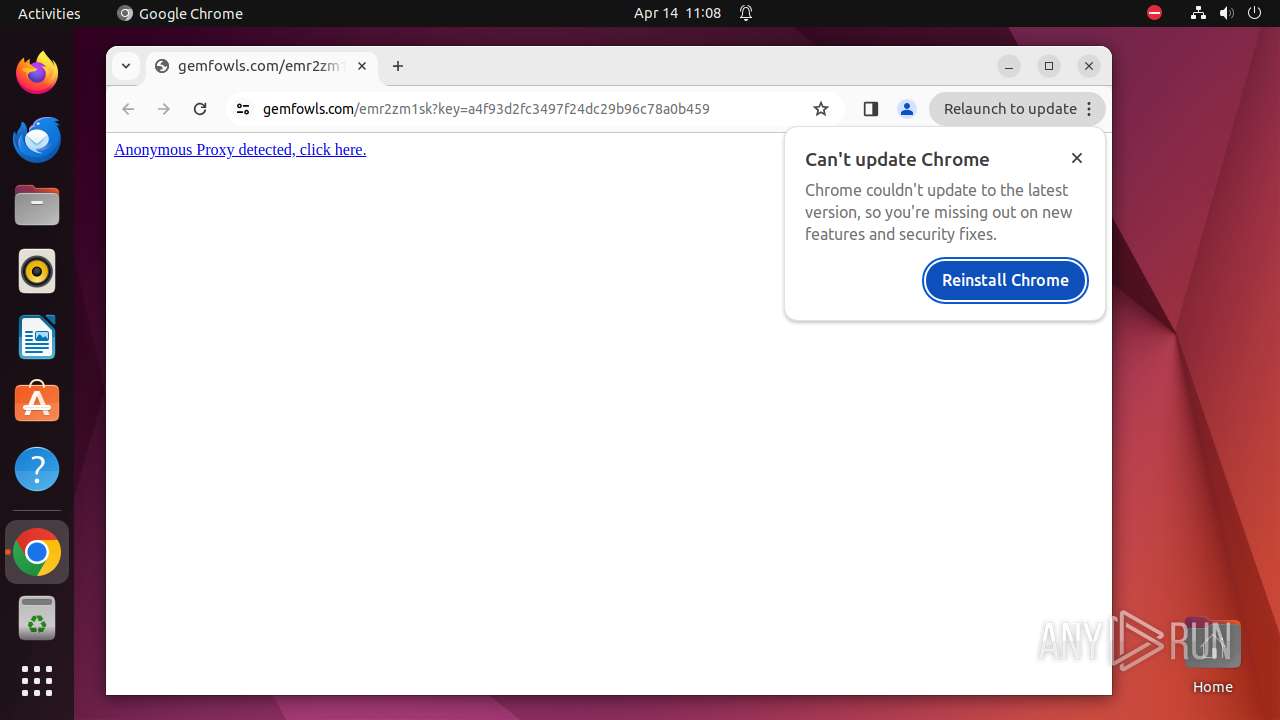
— | — | Exploit Kit Activity Detected | ET EXPLOIT_KIT TA569 Keitaro TDS Domain in DNS Lookup (apistoragecache .com) |
— | — | Exploit Kit Activity Detected | ET EXPLOIT_KIT TA569 Keitaro TDS Domain in DNS Lookup (apistoragecache .com) |
— | — | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 36 |
— | — | Exploit Kit Activity Detected | ET EXPLOIT_KIT TA569 Keitaro TDS Domain in TLS SNI (apistoragecache .com) |
— | — | Exploit Kit Activity Detected | ET EXPLOIT_KIT Balada Domain in DNS Lookup (specialtaskevents .com) |
— | — | Exploit Kit Activity Detected | ET EXPLOIT_KIT Balada Domain in DNS Lookup (specialtaskevents .com) |
— | — | Exploit Kit Activity Detected | ET EXPLOIT_KIT Balada Domain in DNS Lookup (bestresulttostart .com) |
— | — | Exploit Kit Activity Detected | ET EXPLOIT_KIT Balada Domain in DNS Lookup (bestresulttostart .com) |
— | — | A Network Trojan was detected | ET MALWARE SocGholish Domain in DNS Lookup (stake .libertariancounterpoint .com) |
— | — | A Network Trojan was detected | ET MALWARE SocGholish Domain in DNS Lookup (stake .libertariancounterpoint .com) |