| File name: | IxWare.exe |
| Full analysis: | https://app.any.run/tasks/aa45a95f-7f68-460a-9568-ebd3be68351e |
| Verdict: | Malicious activity |
| Analysis date: | April 02, 2021, 09:21:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 69AD56CF63F0060694CF6AB5E357DDCF |
| SHA1: | 3A8D3FEF4AEAA898692F7BD7353A4B8415173AB5 |
| SHA256: | 3886EC3D1025721F3E477489690678A3920429DF2DD2E751F8CEAF413D55494A |
| SSDEEP: | 768:TmU/LvGC/psbn5zZSUxUFNexniifTTTryTTTT/TTTTWTTTryTTTT/TTTTdpWpGT0:CC/psbn5VSA6QJiLYT |
MALICIOUS
No malicious indicators.SUSPICIOUS
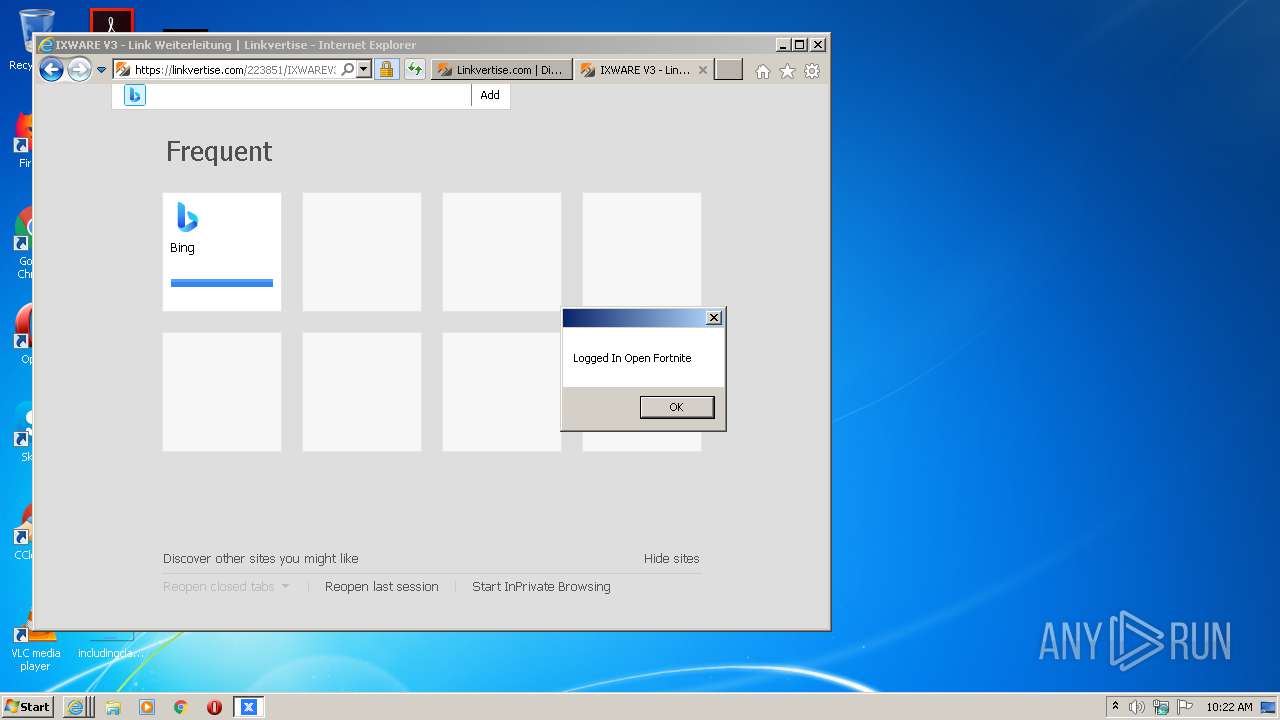
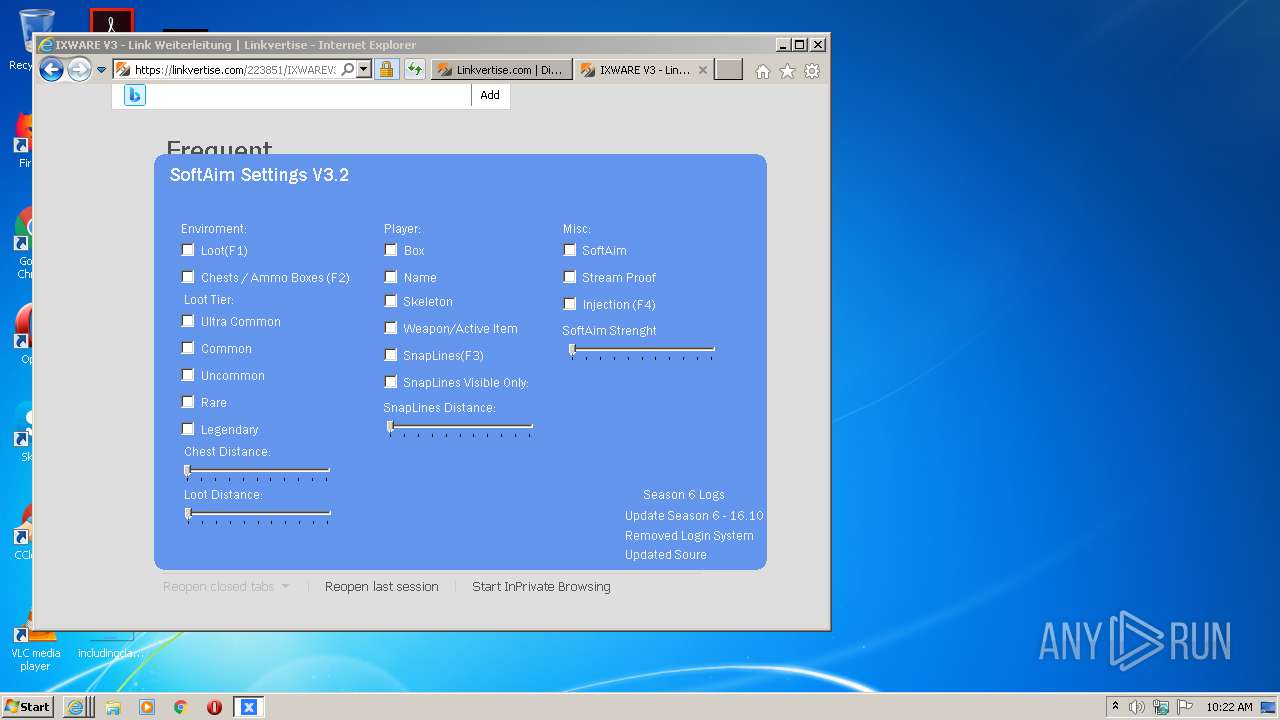
Starts Internet Explorer
- IxWare.exe (PID: 3412)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 592)
INFO
Reads settings of System Certificates
- iexplore.exe (PID: 3620)
- iexplore.exe (PID: 2304)
- iexplore.exe (PID: 272)
- iexplore.exe (PID: 1356)
Changes internet zones settings
- iexplore.exe (PID: 272)
- iexplore.exe (PID: 2304)
Application launched itself
- iexplore.exe (PID: 2304)
- iexplore.exe (PID: 272)
Creates files in the user directory
- iexplore.exe (PID: 1076)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 592)
- iexplore.exe (PID: 272)
Reads internet explorer settings
- iexplore.exe (PID: 3620)
- iexplore.exe (PID: 1076)
- iexplore.exe (PID: 1356)
Changes settings of System certificates
- iexplore.exe (PID: 2304)
- iexplore.exe (PID: 272)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2304)
- iexplore.exe (PID: 272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (81) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.2) |
| .exe | | | Win32 Executable (generic) (4.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.2) |
| .exe | | | Generic Win/DOS Executable (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:03:25 19:19:37+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 29696 |
| InitializedDataSize: | 6656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9356 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | WindowsFormsApp33 |
| FileVersion: | 1.0.0.0 |
| InternalName: | IxWare.exe |
| LegalCopyright: | Copyright © 2021 |
| LegalTrademarks: | - |
| OriginalFileName: | IxWare.exe |
| ProductName: | WindowsFormsApp33 |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Mar-2021 18:19:37 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | WindowsFormsApp33 |
| FileVersion: | 1.0.0.0 |
| InternalName: | IxWare.exe |
| LegalCopyright: | Copyright © 2021 |
| LegalTrademarks: | - |
| OriginalFilename: | IxWare.exe |
| ProductName: | WindowsFormsApp33 |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 25-Mar-2021 18:19:37 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0000735C | 0x00007400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.69682 |
.rsrc | 0x0000A000 | 0x00001710 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.95526 |
.reloc | 0x0000C000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
32512 | 1.7815 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
44
Monitored processes
7
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Internet Explorer\iexplore.exe" https://link-to.net/223851/IXWAREV3 | C:\Program Files\Internet Explorer\iexplore.exe | IxWare.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 592 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:272 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:272 CREDAT:2954506 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.youtube.com/watch?v=ry1wSsvzPTY | C:\Program Files\Internet Explorer\iexplore.exe | IxWare.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3412 | "C:\Users\admin\AppData\Local\Temp\IxWare.exe" | C:\Users\admin\AppData\Local\Temp\IxWare.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WindowsFormsApp33 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3620 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2304 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 934
Read events
1 672
Write events
257
Delete events
5
Modification events
| (PID) Process: | (272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3010398104 | |||
| (PID) Process: | (272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30877601 | |||
| (PID) Process: | (272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3412) IxWare.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 0100000000000000BA2A73A1A127D701 | |||
| (PID) Process: | (272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (272) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
114
Text files
88
Unknown types
64
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1076 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab9376.tmp | — | |
MD5:— | SHA256:— | |||
| 1076 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar9377.tmp | — | |
MD5:— | SHA256:— | |||
| 1076 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 1076 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
| 1076 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 1076 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 1076 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\polyfills-es5.481e21a15f8209d0e3d2[1].js | text | |
MD5:— | SHA256:— | |||
| 1076 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\ads[1].js | text | |
MD5:— | SHA256:— | |||
| 1076 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\UKYACPJQ.txt | text | |
MD5:— | SHA256:— | |||
| 1076 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
132
DNS requests
58
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1076 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1076 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
1076 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
1076 | iexplore.exe | GET | 200 | 13.32.23.215:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
1076 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCECoWm2VW%2FUZXBQAAAACHo2g%3D | US | der | 471 b | whitelisted |
1076 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
1076 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
1076 | iexplore.exe | GET | 200 | 13.32.23.204:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
1076 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCECoWm2VW%2FUZXBQAAAACHo2g%3D | US | der | 471 b | whitelisted |
1076 | iexplore.exe | GET | 200 | 13.32.23.204:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1076 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1076 | iexplore.exe | 172.67.180.38:443 | linkvertise.com | — | US | unknown |
1076 | iexplore.exe | 142.250.185.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1076 | iexplore.exe | 104.16.18.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
1076 | iexplore.exe | 195.181.175.55:443 | maxst.icons8.com | Datacamp Limited | DE | suspicious |
1076 | iexplore.exe | 104.18.10.207:443 | stackpath.bootstrapcdn.com | Cloudflare Inc | US | suspicious |
1076 | iexplore.exe | 65.9.66.105:443 | js.chargebee.com | AT&T Services, Inc. | US | suspicious |
1076 | iexplore.exe | 2.18.235.93:443 | contextual.media.net | Akamai International B.V. | — | whitelisted |
3620 | iexplore.exe | 142.250.74.206:443 | www.youtube.com | Google Inc. | US | whitelisted |
1076 | iexplore.exe | 104.21.35.84:443 | link-to.net | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youtube.com |
| whitelisted |
link-to.net |
| malicious |
ocsp.digicert.com |
| whitelisted |
linkvertise.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
maxst.icons8.com |
| whitelisted |
stackpath.bootstrapcdn.com |
| whitelisted |
js.chargebee.com |
| shared |
contextual.media.net |
| shared |