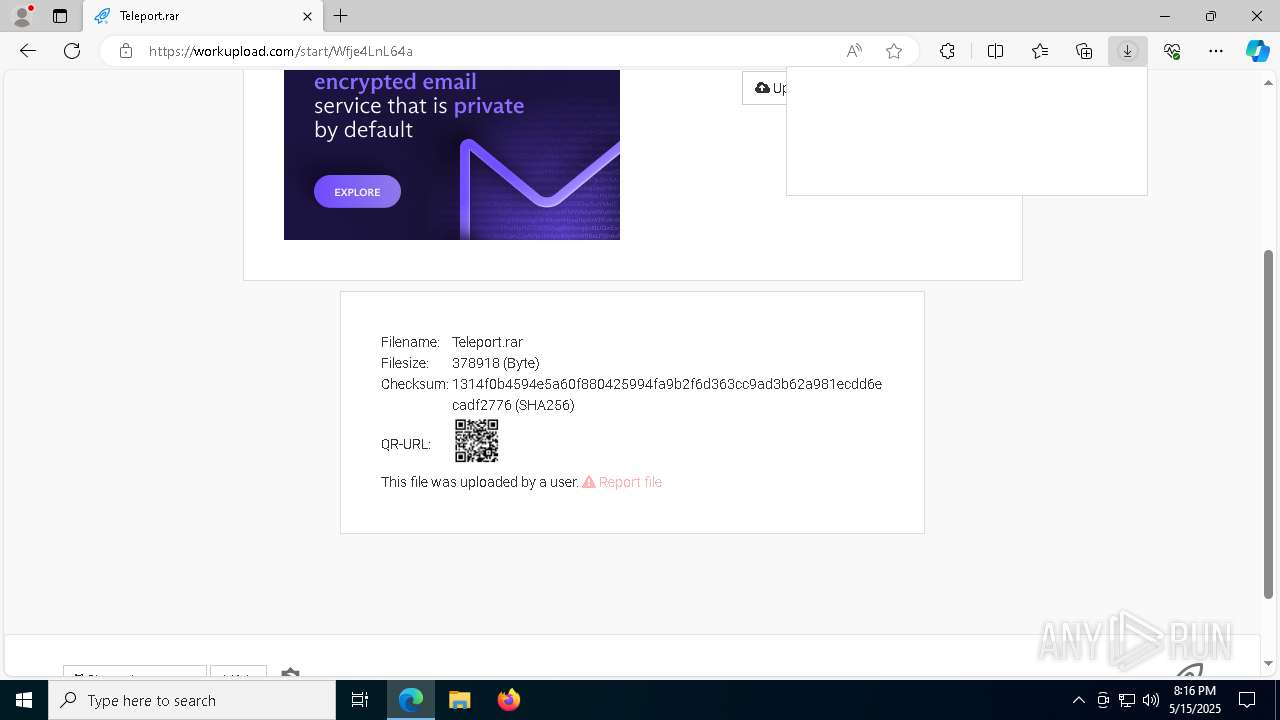
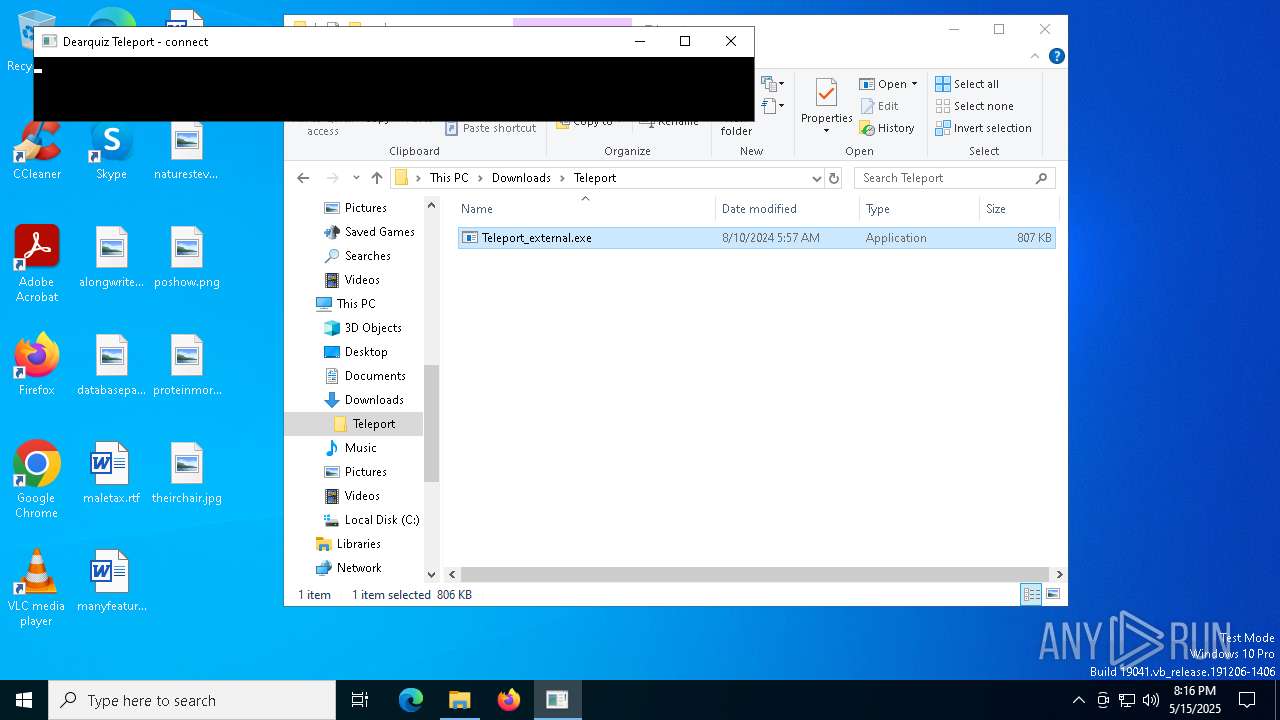
| URL: | https://f94.workupload.com/download/Wfje4LnL64a |
| Full analysis: | https://app.any.run/tasks/e1209818-c812-4bb3-a701-29c24a85fae8 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 20:16:02 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 1A8F643562E98DC12B7F6F5BD4C2DDEC |
| SHA1: | A8DE1C8B43B647D0B5DDDE0B276F6A5C80F48DC2 |
| SHA256: | 3882B1F3AA9648B948AB9F00C83F90347D21F11B204C0BA79B56C0D13B51D9E4 |
| SSDEEP: | 3:N8uREQ2ZBLQQEn:2uXYBsn |
MALICIOUS
Uses TASKKILL.EXE to kill security tools
- cmd.exe (PID: 5084)
- cmd.exe (PID: 780)
- cmd.exe (PID: 7508)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 6048)
- cmd.exe (PID: 6436)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 2564)
- cmd.exe (PID: 7540)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 6264)
- cmd.exe (PID: 8024)
- cmd.exe (PID: 7652)
- cmd.exe (PID: 1388)
Starts NET.EXE for service management
- cmd.exe (PID: 7968)
- net.exe (PID: 7748)
- cmd.exe (PID: 812)
- cmd.exe (PID: 8000)
- net.exe (PID: 7944)
- cmd.exe (PID: 7340)
- net.exe (PID: 644)
- net.exe (PID: 7256)
- cmd.exe (PID: 7576)
- net.exe (PID: 4528)
- cmd.exe (PID: 7440)
- net.exe (PID: 5984)
- cmd.exe (PID: 1228)
- net.exe (PID: 7492)
- cmd.exe (PID: 5384)
- net.exe (PID: 6300)
SUSPICIOUS
Hides command output
- cmd.exe (PID: 5084)
- cmd.exe (PID: 780)
- cmd.exe (PID: 7340)
- cmd.exe (PID: 7968)
- cmd.exe (PID: 812)
- cmd.exe (PID: 8000)
- cmd.exe (PID: 536)
- cmd.exe (PID: 7192)
- cmd.exe (PID: 6572)
- cmd.exe (PID: 3100)
- cmd.exe (PID: 7508)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 2148)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 7736)
- cmd.exe (PID: 7524)
- cmd.exe (PID: 7476)
- cmd.exe (PID: 7328)
- cmd.exe (PID: 5352)
- cmd.exe (PID: 6048)
- cmd.exe (PID: 6436)
- cmd.exe (PID: 6640)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 5408)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 7932)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 2148)
- cmd.exe (PID: 7256)
- cmd.exe (PID: 1328)
- cmd.exe (PID: 5064)
- cmd.exe (PID: 7316)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 5332)
- cmd.exe (PID: 7372)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 2284)
- cmd.exe (PID: 5384)
- cmd.exe (PID: 1660)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 7324)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 7716)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 5600)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 8012)
- cmd.exe (PID: 4300)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 7564)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 6736)
- cmd.exe (PID: 616)
- cmd.exe (PID: 7464)
- cmd.exe (PID: 7968)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 7560)
- cmd.exe (PID: 7216)
- cmd.exe (PID: 5352)
- cmd.exe (PID: 7180)
- cmd.exe (PID: 6744)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 7448)
- cmd.exe (PID: 7432)
- cmd.exe (PID: 4452)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 4112)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 1228)
- cmd.exe (PID: 6572)
- cmd.exe (PID: 7332)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 4620)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 7540)
- cmd.exe (PID: 2564)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 5384)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 7440)
- cmd.exe (PID: 1228)
- cmd.exe (PID: 7464)
- cmd.exe (PID: 2240)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 7676)
- cmd.exe (PID: 7184)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 6264)
- cmd.exe (PID: 7276)
- cmd.exe (PID: 4740)
- cmd.exe (PID: 2560)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 4784)
- cmd.exe (PID: 7652)
- cmd.exe (PID: 6640)
- cmd.exe (PID: 7328)
- cmd.exe (PID: 7508)
- cmd.exe (PID: 8024)
- cmd.exe (PID: 7848)
- cmd.exe (PID: 7320)
- cmd.exe (PID: 7396)
- cmd.exe (PID: 8012)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 7248)
- cmd.exe (PID: 1388)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 7548)
- cmd.exe (PID: 6136)
- cmd.exe (PID: 924)
- cmd.exe (PID: 7172)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 4300)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 7516)
- cmd.exe (PID: 7556)
- cmd.exe (PID: 7852)
- cmd.exe (PID: 2560)
- cmd.exe (PID: 968)
- cmd.exe (PID: 6620)
- cmd.exe (PID: 4408)
- cmd.exe (PID: 7524)
- cmd.exe (PID: 4452)
- cmd.exe (PID: 7676)
- cmd.exe (PID: 8164)
- cmd.exe (PID: 2148)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 7172)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 7284)
- cmd.exe (PID: 3888)
- cmd.exe (PID: 8000)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 7860)
- cmd.exe (PID: 7400)
- cmd.exe (PID: 872)
- cmd.exe (PID: 4776)
- cmd.exe (PID: 1328)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 7876)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 7540)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 4784)
- cmd.exe (PID: 7236)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 5056)
- cmd.exe (PID: 1452)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 5156)
- cmd.exe (PID: 7780)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 4896)
- cmd.exe (PID: 6300)
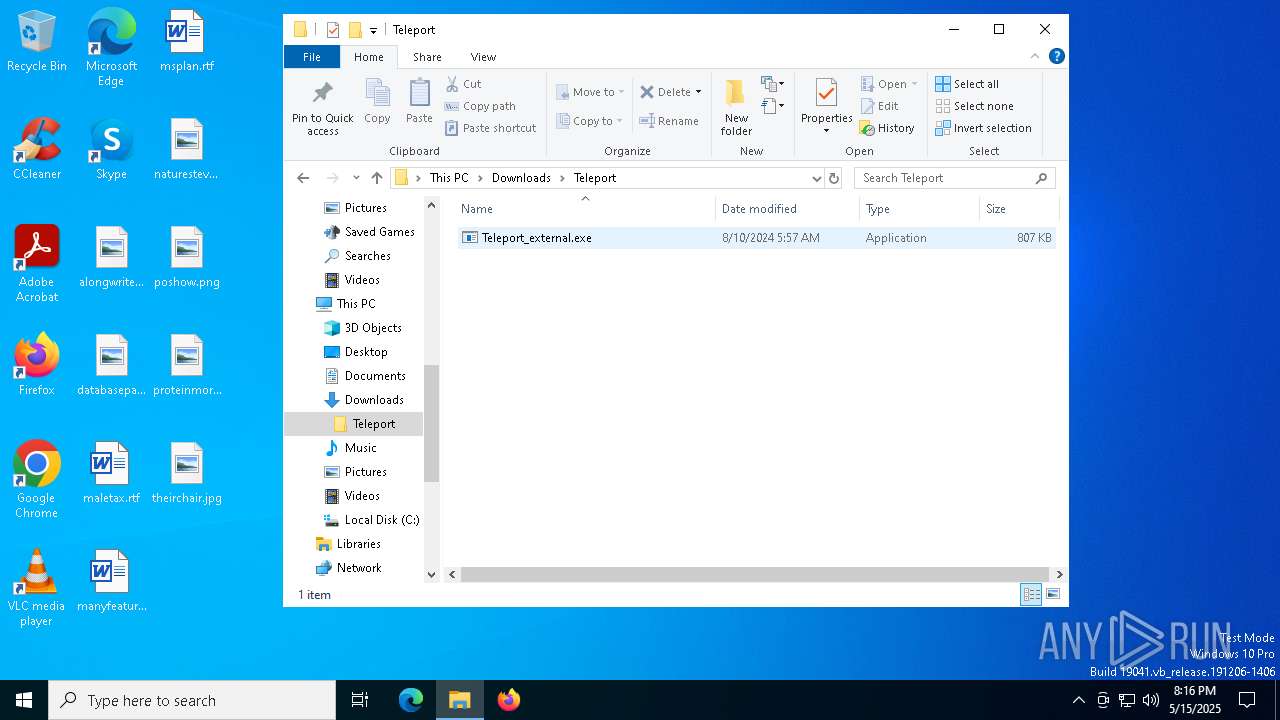
Starts CMD.EXE for commands execution
- Teleport_external.exe (PID: 7204)
- Teleport_external.exe (PID: 5064)
Starts SC.EXE for service management
- cmd.exe (PID: 536)
- cmd.exe (PID: 6572)
- cmd.exe (PID: 7192)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 3100)
- cmd.exe (PID: 7476)
- cmd.exe (PID: 2148)
- cmd.exe (PID: 7524)
- cmd.exe (PID: 7736)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 7328)
- cmd.exe (PID: 5352)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 1228)
- cmd.exe (PID: 4620)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 6572)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 7464)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 7676)
- cmd.exe (PID: 2240)
- cmd.exe (PID: 7648)
- cmd.exe (PID: 7276)
- cmd.exe (PID: 2560)
- cmd.exe (PID: 4784)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 4740)
- cmd.exe (PID: 6640)
- cmd.exe (PID: 7320)
- cmd.exe (PID: 7848)
- cmd.exe (PID: 7548)
- cmd.exe (PID: 7396)
- cmd.exe (PID: 1452)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 7236)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 4784)
- cmd.exe (PID: 5056)
- cmd.exe (PID: 6300)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 7780)
- cmd.exe (PID: 5156)
- cmd.exe (PID: 4896)
Stops a currently running service
- sc.exe (PID: 5592)
- sc.exe (PID: 4428)
- sc.exe (PID: 2284)
- sc.exe (PID: 1452)
- sc.exe (PID: 4620)
- sc.exe (PID: 6584)
- sc.exe (PID: 7492)
- sc.exe (PID: 7404)
- sc.exe (PID: 7596)
- sc.exe (PID: 7636)
- sc.exe (PID: 7256)
- sc.exe (PID: 1272)
- sc.exe (PID: 1244)
- sc.exe (PID: 8164)
- sc.exe (PID: 5072)
- sc.exe (PID: 1184)
- sc.exe (PID: 7392)
- sc.exe (PID: 7776)
- sc.exe (PID: 7832)
- sc.exe (PID: 7464)
- sc.exe (PID: 5136)
- sc.exe (PID: 7340)
- sc.exe (PID: 6964)
- sc.exe (PID: 7936)
- sc.exe (PID: 7260)
- sc.exe (PID: 7220)
- sc.exe (PID: 7480)
- sc.exe (PID: 1388)
- sc.exe (PID: 5136)
- sc.exe (PID: 8068)
- sc.exe (PID: 7396)
- sc.exe (PID: 2420)
- sc.exe (PID: 2236)
- sc.exe (PID: 7324)
- sc.exe (PID: 7208)
- sc.exe (PID: 7312)
- sc.exe (PID: 7400)
- sc.exe (PID: 5212)
- sc.exe (PID: 8164)
- sc.exe (PID: 5956)
- sc.exe (PID: 3884)
- sc.exe (PID: 7416)
- sc.exe (PID: 1672)
- sc.exe (PID: 6108)
- sc.exe (PID: 7156)
- sc.exe (PID: 7380)
- sc.exe (PID: 7848)
- sc.exe (PID: 7012)
- sc.exe (PID: 2416)
- sc.exe (PID: 6228)
- sc.exe (PID: 2284)
- sc.exe (PID: 744)
- sc.exe (PID: 3884)
- sc.exe (PID: 4008)
- sc.exe (PID: 5204)
- sc.exe (PID: 7328)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6640)
- cmd.exe (PID: 5408)
- cmd.exe (PID: 7932)
- cmd.exe (PID: 2148)
- cmd.exe (PID: 7256)
- cmd.exe (PID: 1328)
- cmd.exe (PID: 5064)
- cmd.exe (PID: 7316)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 5332)
- cmd.exe (PID: 7372)
- cmd.exe (PID: 2284)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 5384)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 1660)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 7324)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 6736)
- cmd.exe (PID: 616)
- cmd.exe (PID: 5600)
- cmd.exe (PID: 8012)
- cmd.exe (PID: 4300)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 7564)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 7716)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 7464)
- cmd.exe (PID: 7968)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 7560)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 7216)
- cmd.exe (PID: 5352)
- cmd.exe (PID: 7180)
- cmd.exe (PID: 7332)
- cmd.exe (PID: 7432)
- cmd.exe (PID: 4112)
- cmd.exe (PID: 4452)
- cmd.exe (PID: 6744)
- cmd.exe (PID: 7448)
- cmd.exe (PID: 7328)
- cmd.exe (PID: 7508)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 6136)
- cmd.exe (PID: 8012)
- cmd.exe (PID: 7248)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 924)
- cmd.exe (PID: 7172)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 4300)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 968)
- cmd.exe (PID: 7516)
- cmd.exe (PID: 7852)
- cmd.exe (PID: 2560)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 2148)
- cmd.exe (PID: 6620)
- cmd.exe (PID: 7676)
- cmd.exe (PID: 7524)
- cmd.exe (PID: 4452)
- cmd.exe (PID: 4408)
- cmd.exe (PID: 8164)
- cmd.exe (PID: 7556)
- cmd.exe (PID: 7400)
- cmd.exe (PID: 3888)
- cmd.exe (PID: 872)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 7172)
- cmd.exe (PID: 7284)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 7860)
- cmd.exe (PID: 1328)
- cmd.exe (PID: 4776)
- cmd.exe (PID: 7540)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 7876)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 8000)
- cmd.exe (PID: 4688)
INFO
Reads Environment values
- identity_helper.exe (PID: 6476)
- identity_helper.exe (PID: 5800)
Checks supported languages
- identity_helper.exe (PID: 6476)
- identity_helper.exe (PID: 5800)
- mode.com (PID: 7300)
- Teleport_external.exe (PID: 7204)
Application launched itself
- msedge.exe (PID: 1760)
- msedge.exe (PID: 4608)
Reads the computer name
- identity_helper.exe (PID: 5800)
- identity_helper.exe (PID: 6476)
- Teleport_external.exe (PID: 7204)
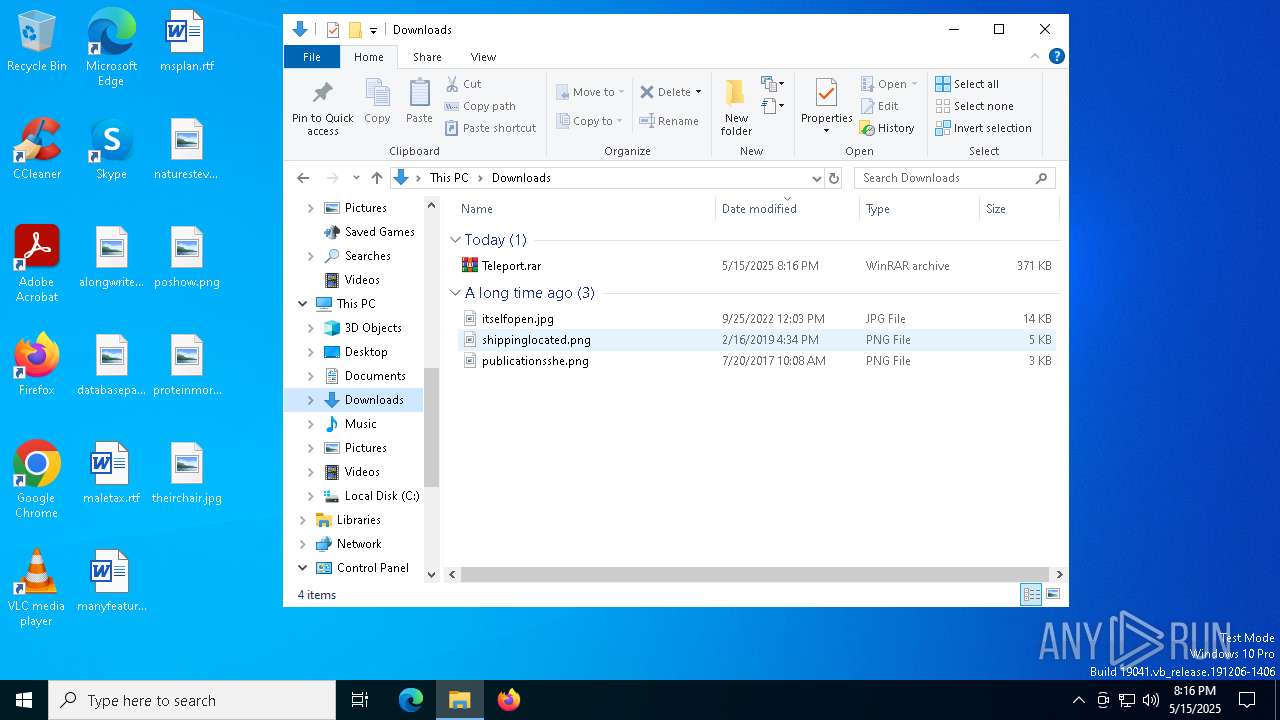
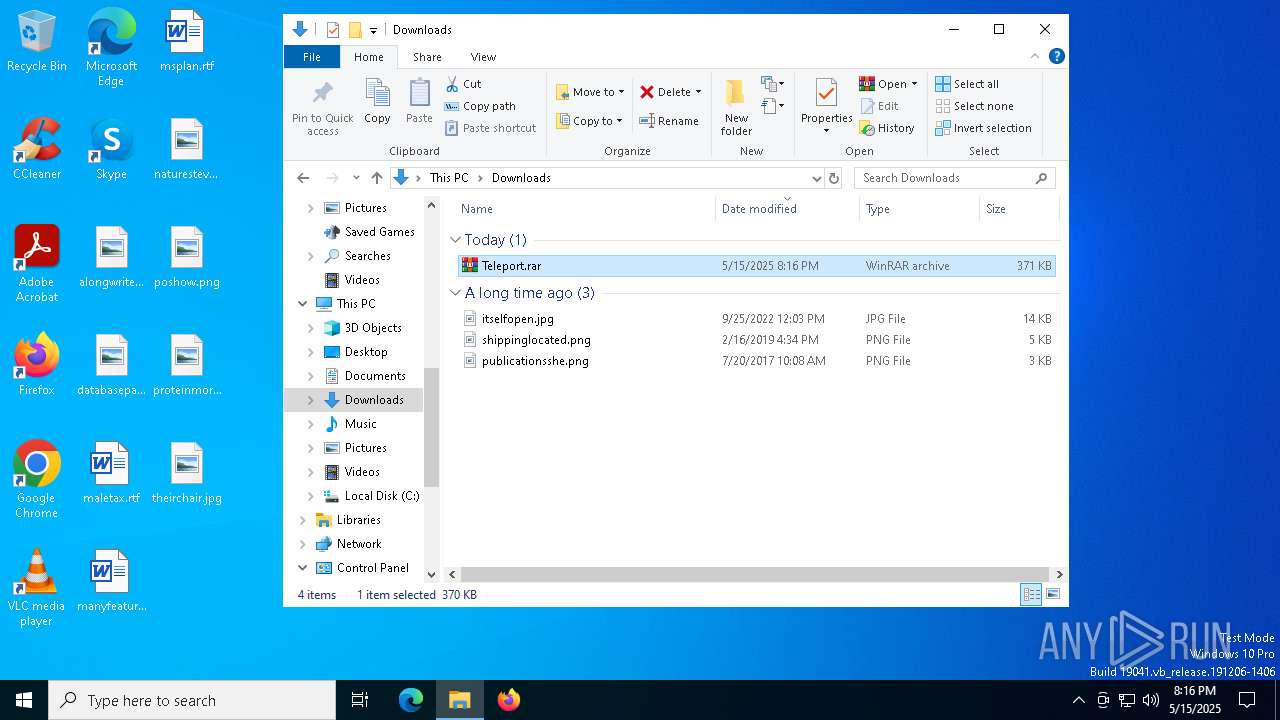
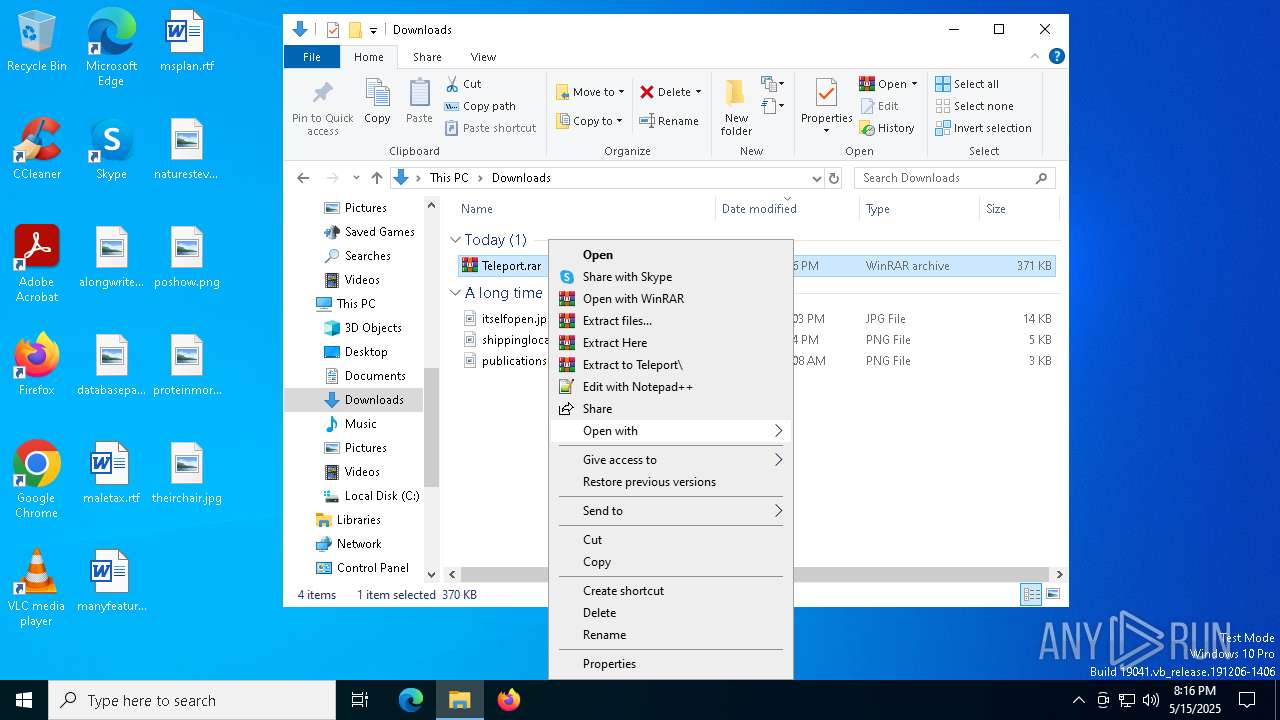
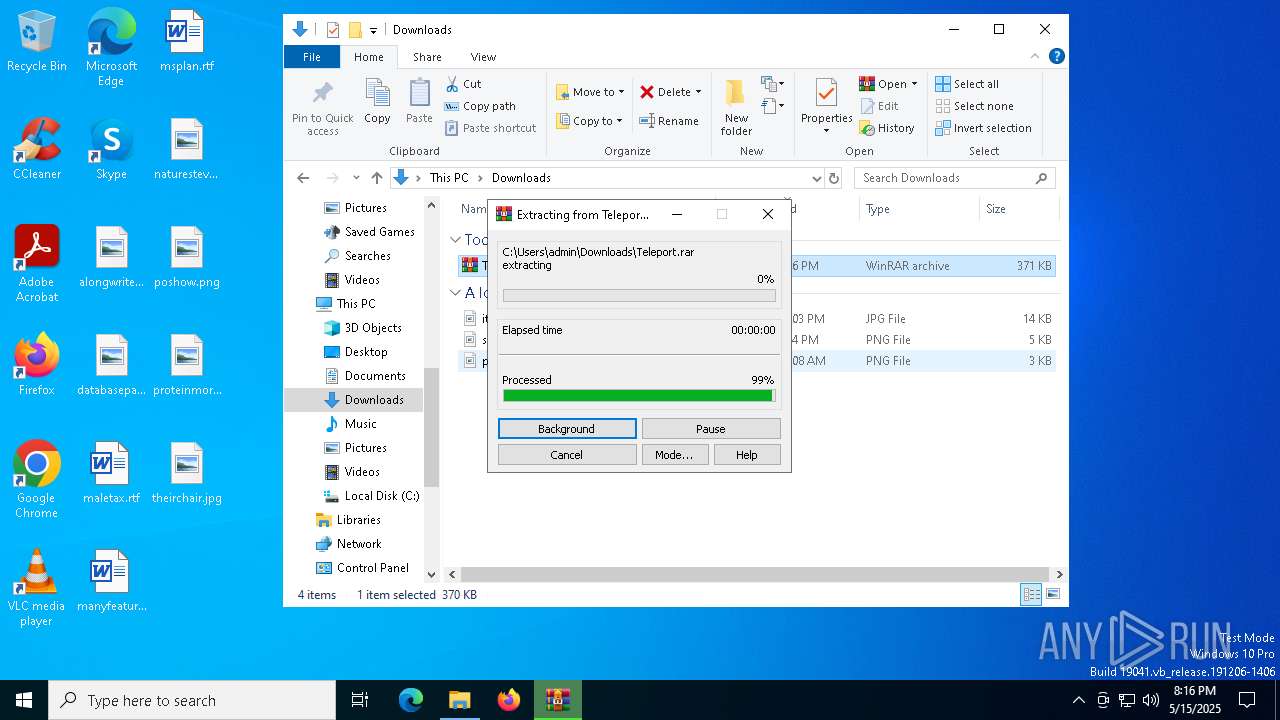
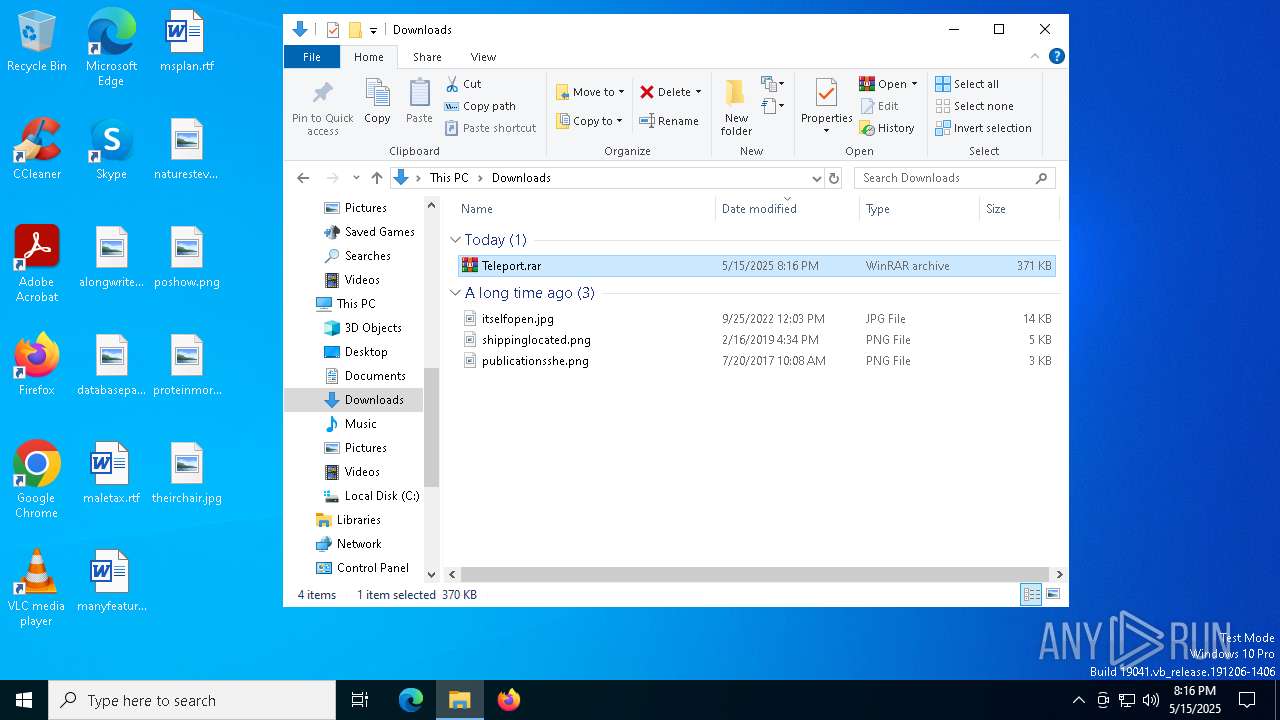
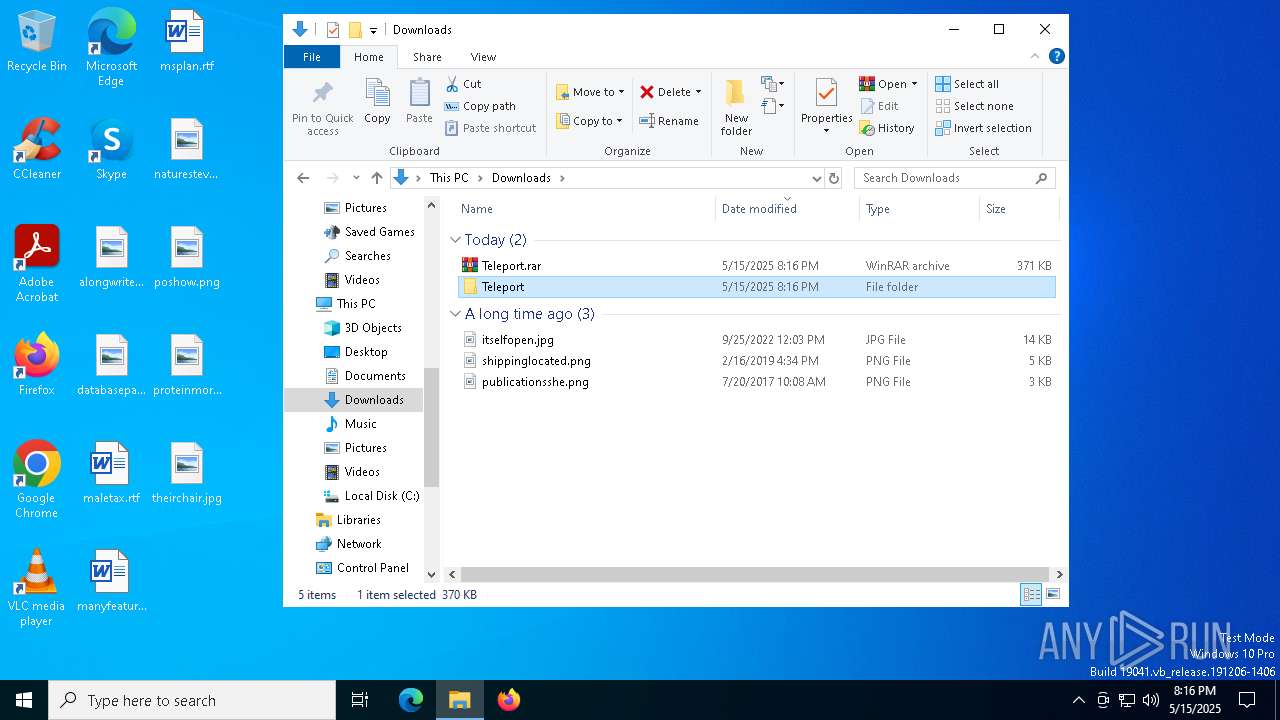
Executable content was dropped or overwritten
- WinRAR.exe (PID: 536)
Manual execution by a user
- WinRAR.exe (PID: 536)
- Teleport_external.exe (PID: 7204)
- Teleport_external.exe (PID: 5064)
Gets the hash of the file via CERTUTIL.EXE
- certutil.exe (PID: 7636)
- certutil.exe (PID: 7332)
Starts MODE.COM to configure console settings
- mode.com (PID: 7300)
- mode.com (PID: 7400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
549
Monitored processes
421
Malicious processes
2
Suspicious processes
55
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\Teleport.rar" C:\Users\admin\Downloads\Teleport\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 536 | C:\WINDOWS\system32\cmd.exe /c sc stop HTTPDebuggerPro >nul 2>&1 | C:\Windows\System32\cmd.exe | — | Teleport_external.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | C:\WINDOWS\system32\cmd.exe /c taskkill /FI "IMAGENAME eq ProcessHacker*" /IM * /F /T >nul 2>&1 | C:\Windows\System32\cmd.exe | — | Teleport_external.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | taskkill /f /im HTTPDebuggerUI.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | net stop ESEADriver2 | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x300,0x304,0x308,0x274,0x310,0x7ffc881c5fd8,0x7ffc881c5fe4,0x7ffc881c5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 684 | taskkill /FI "IMAGENAME eq httpdebugger*" /IM * /F /T | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 744 | taskkill /FI "IMAGENAME eq charles*" /IM * /F /T | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 744 | sc stop npf | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | C:\WINDOWS\system32\cmd.exe /c taskkill /f /im HTTPDebuggerUI.exe >nul 2>&1 | C:\Windows\System32\cmd.exe | — | Teleport_external.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 297
Read events
21 258
Write events
39
Delete events
0
Modification events
| (PID) Process: | (1760) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1760) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1760) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1760) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1760) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 10327F9EC8932F00 | |||
| (PID) Process: | (1760) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A5D6869EC8932F00 | |||
| (PID) Process: | (1760) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A0A28AF4-71D8-4846-A49C-006097A09500} | |||
| (PID) Process: | (1760) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E84C450A-979B-4827-9C68-0EC9EE38B17C} | |||
| (PID) Process: | (1760) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {11E4684E-7552-4256-8249-5CA7AAFBABDC} | |||
| (PID) Process: | (1760) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5AE3BF24-F00B-4DED-8F14-2A3B0FEE5A9C} | |||
Executable files
12
Suspicious files
193
Text files
60
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b74c.TMP | — | |
MD5:— | SHA256:— | |||
| 1760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b74c.TMP | — | |
MD5:— | SHA256:— | |||
| 1760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b74c.TMP | — | |
MD5:— | SHA256:— | |||
| 1760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b76b.TMP | — | |
MD5:— | SHA256:— | |||
| 1760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b76b.TMP | — | |
MD5:— | SHA256:— | |||
| 1760 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
137
DNS requests
101
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 104.124.11.58:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.124.11.58:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8036 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8036 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 104.124.11.58:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 104.124.11.58:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1760 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7280 | msedge.exe | 142.250.185.162:443 | googleads.g.doubleclick.net | — | — | whitelisted |
7280 | msedge.exe | 142.250.185.226:443 | pagead2.googlesyndication.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
f94.workupload.com |
| whitelisted |
business.bing.com |
| whitelisted |
workupload.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain in DNS Lookup (keyauth .win) |
7204 | Teleport_external.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |
5064 | Teleport_external.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |