| URL: | https://rainway.cloud/setup-dl.php |
| Full analysis: | https://app.any.run/tasks/87fd5002-f288-4f0f-a731-c1f41ec27de4 |
| Verdict: | Malicious activity |
| Analysis date: | March 16, 2024, 17:23:59 |
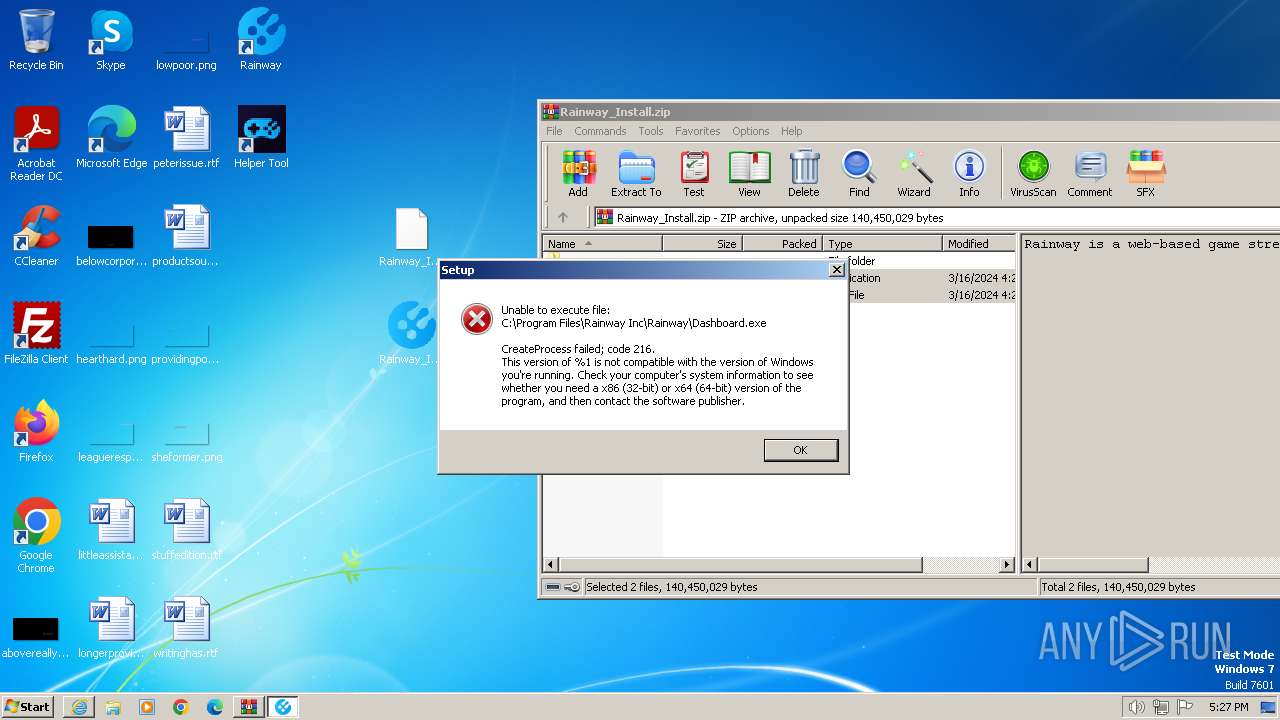
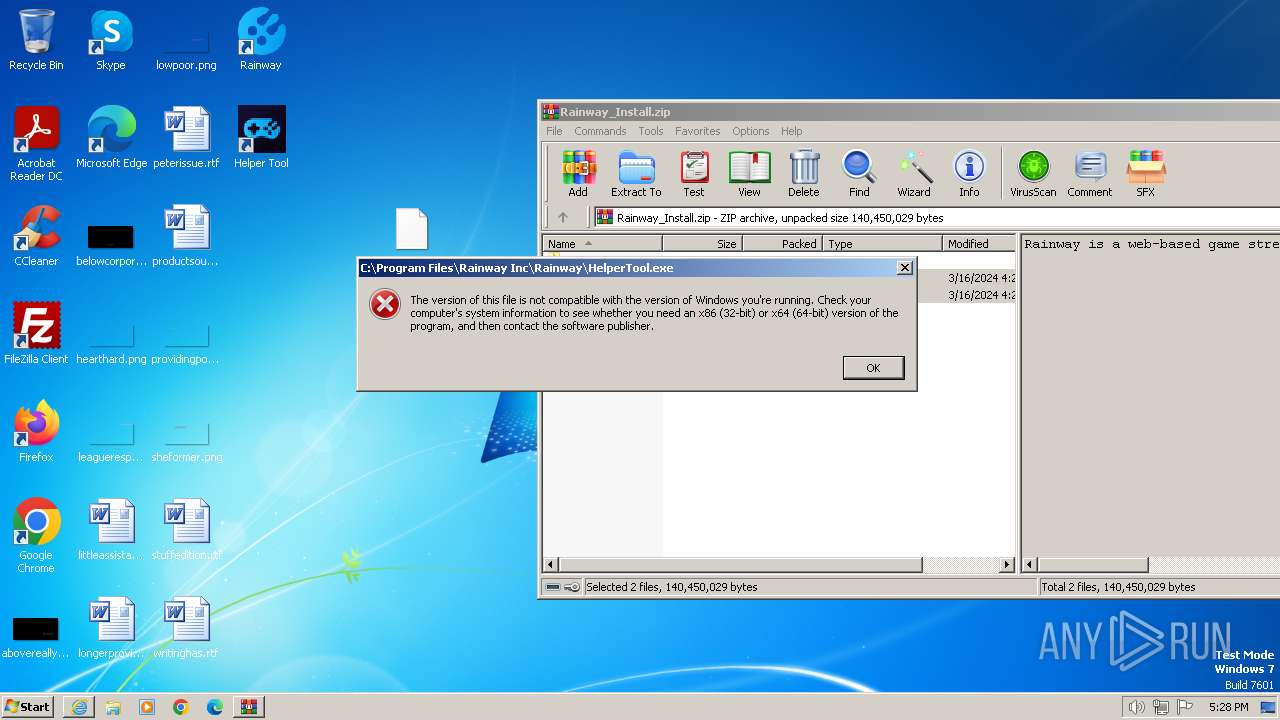
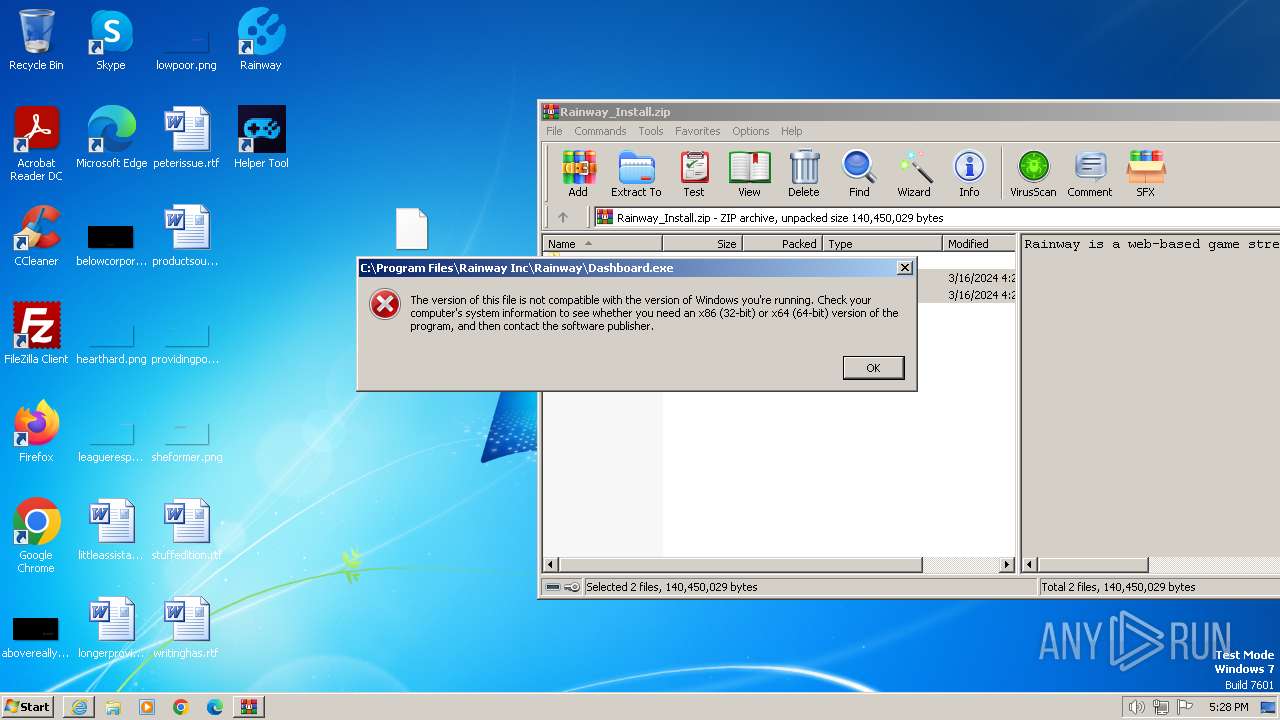
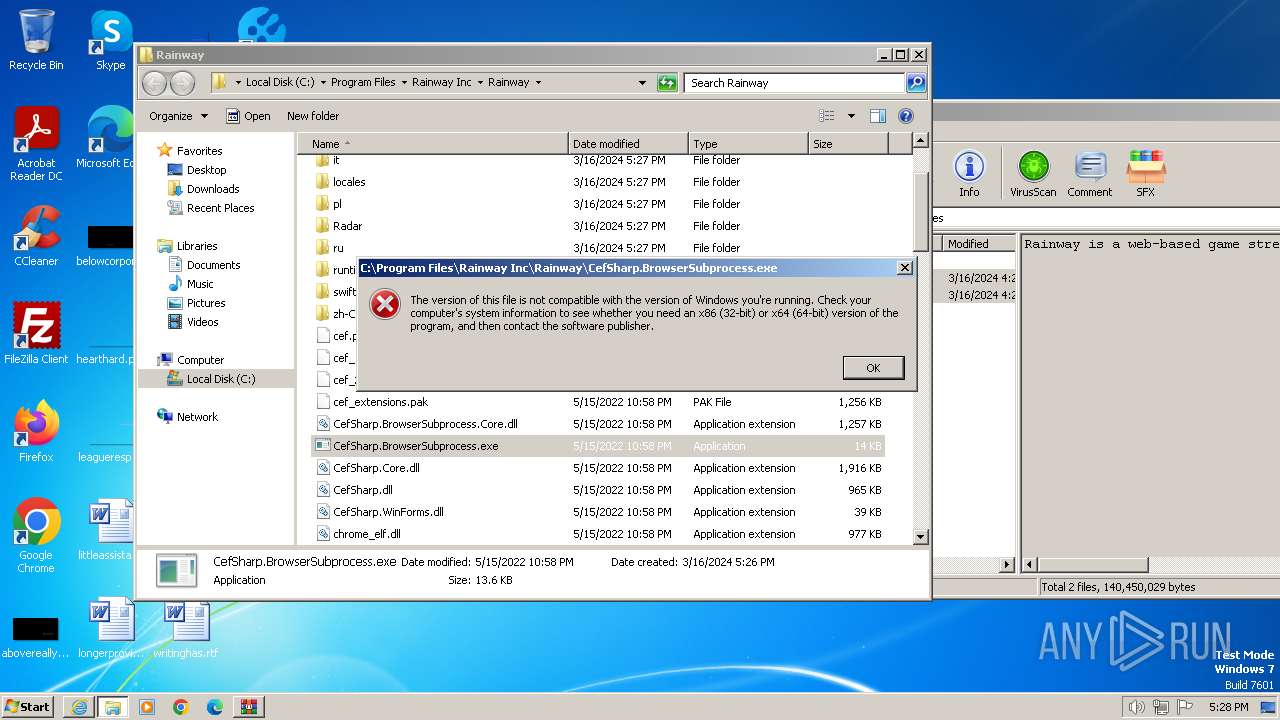
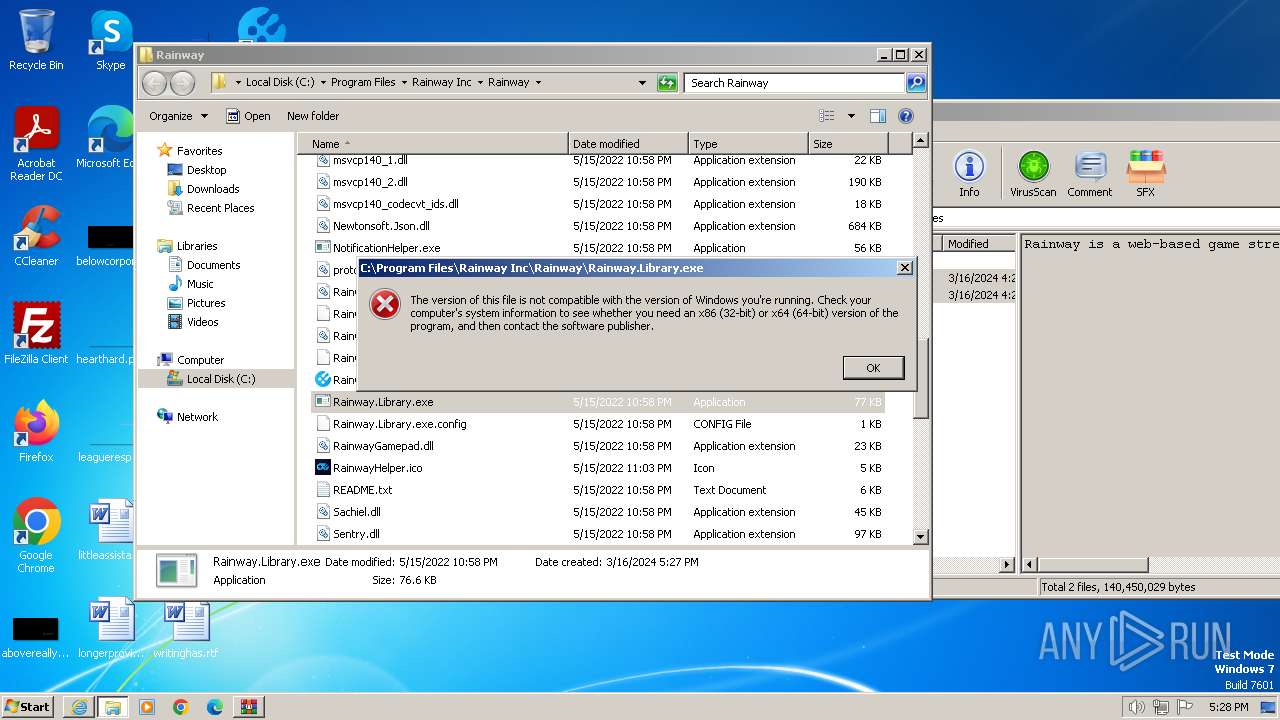
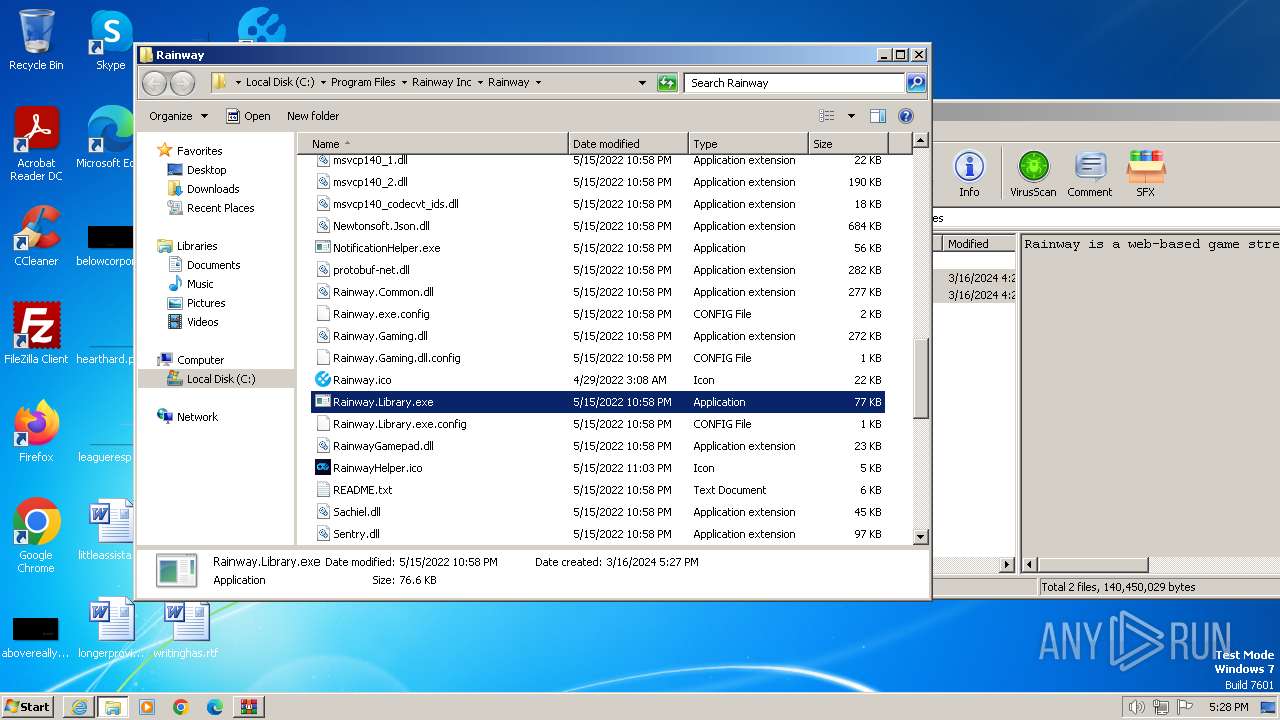
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 39160148613AB82C09510468ECA252C0 |
| SHA1: | DFB4A585334F788DBC55062BFE31B8AD88CAC82A |
| SHA256: | 38778A374D53542359140F3A240B4605AB15E85BD7E2AB9DD583153603961147 |
| SSDEEP: | 3:N8TteBFV:2To/ |
MALICIOUS
Drops the executable file immediately after the start
- Rainway_Install.exe (PID: 1840)
- Rainway_Install.exe (PID: 948)
- unins000.exe (PID: 2104)
- Rainway_Install.tmp (PID: 3260)
SUSPICIOUS
Executable content was dropped or overwritten
- Rainway_Install.exe (PID: 1840)
- Rainway_Install.exe (PID: 948)
- Rainway_Install.tmp (PID: 3260)
- unins000.exe (PID: 2104)
Reads the Windows owner or organization settings
- Rainway_Install.tmp (PID: 3260)
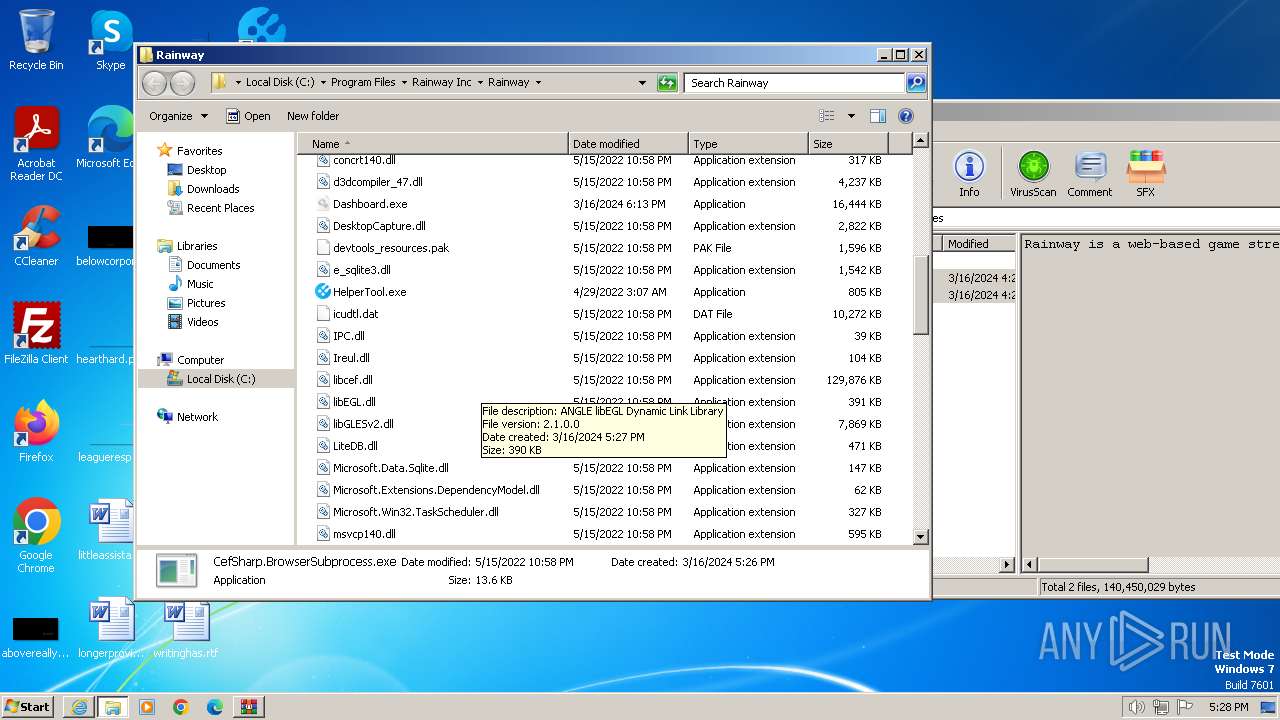
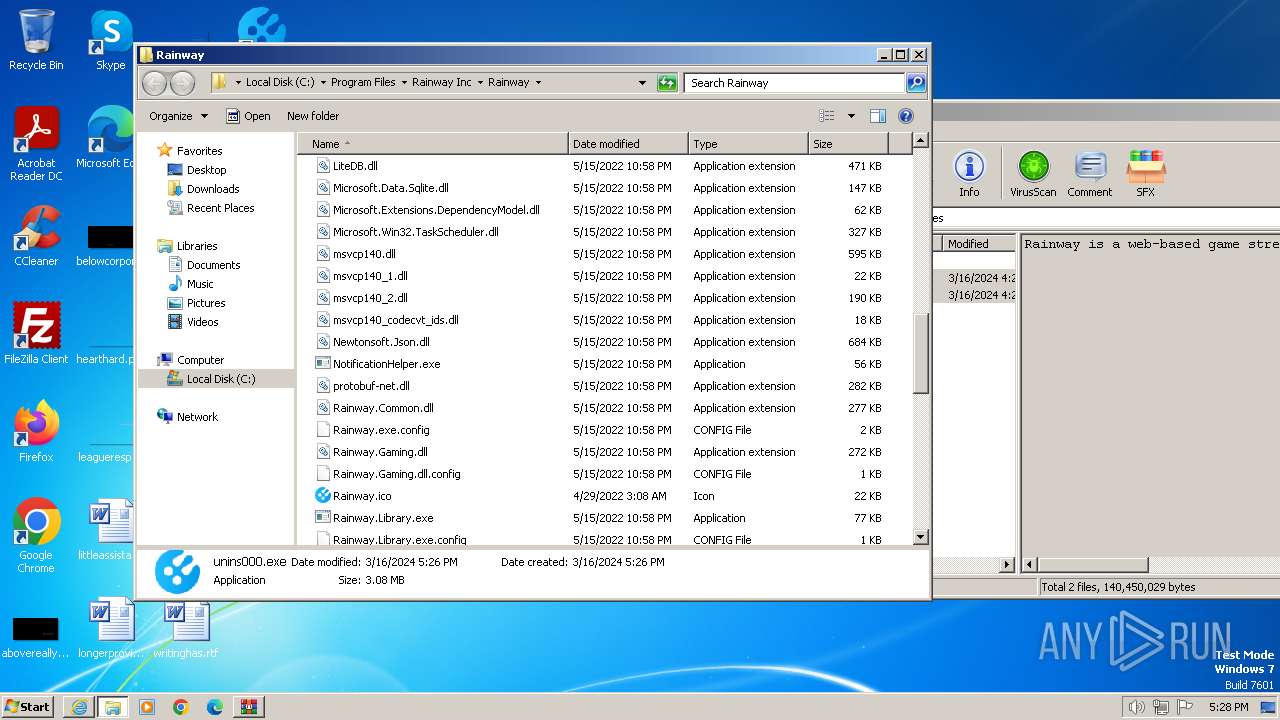
Process drops legitimate windows executable
- Rainway_Install.tmp (PID: 3260)
Non-standard symbols in registry
- Rainway_Install.tmp (PID: 3260)
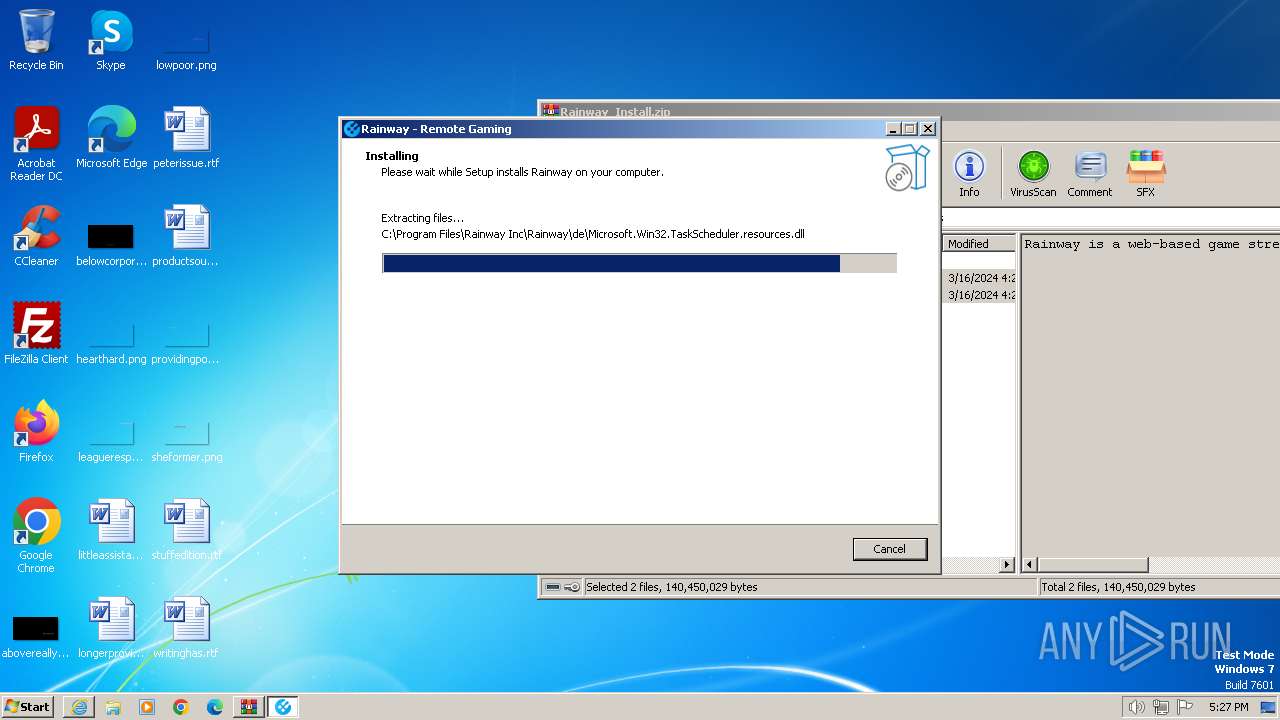
The process drops C-runtime libraries
- Rainway_Install.tmp (PID: 3260)
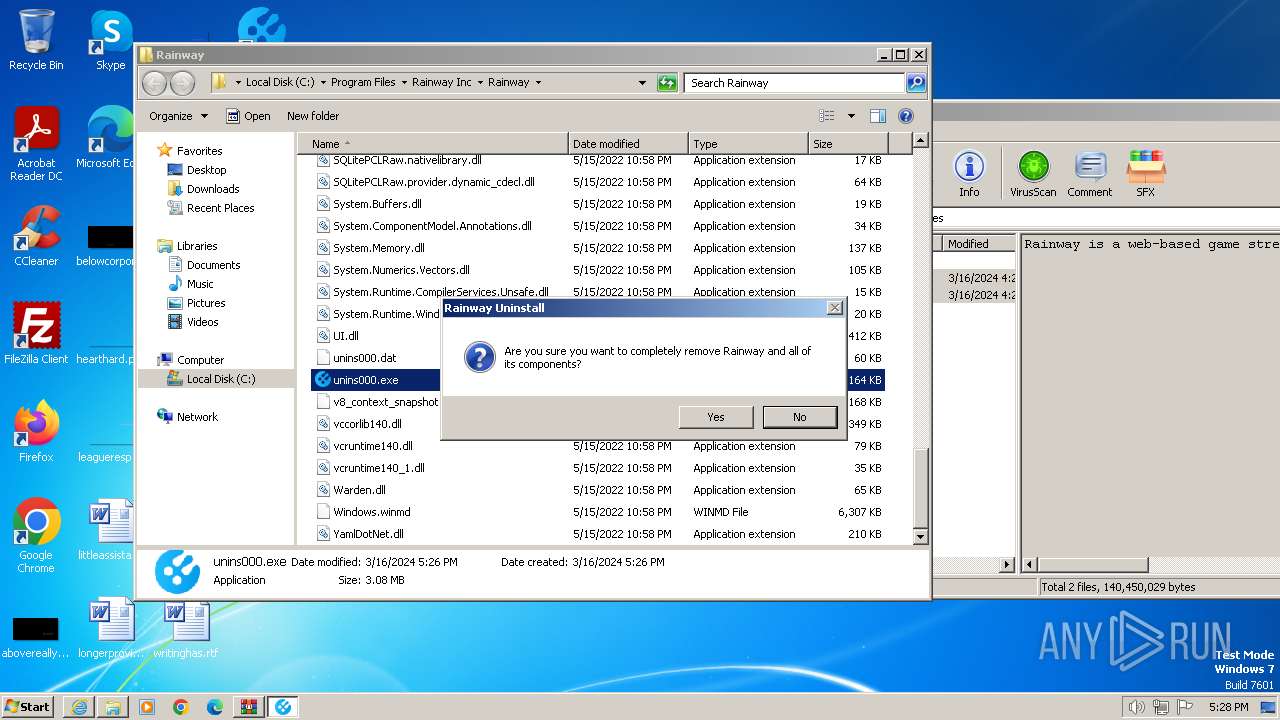
Application launched itself
- unins000.exe (PID: 3044)
Drops a system driver (possible attempt to evade defenses)
- Rainway_Install.tmp (PID: 3260)
Starts itself from another location
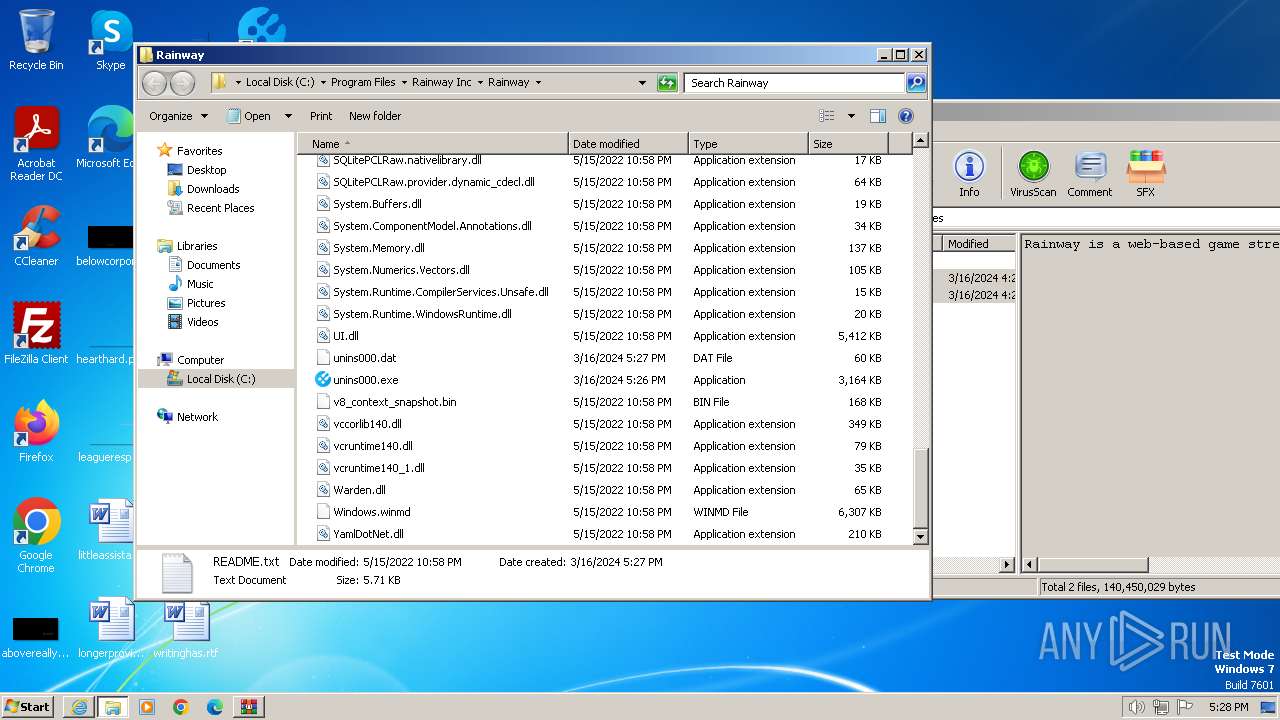
- unins000.exe (PID: 2104)
Starts application with an unusual extension
- unins000.exe (PID: 2104)
INFO
Create files in a temporary directory
- Rainway_Install.exe (PID: 1840)
- Rainway_Install.exe (PID: 948)
- unins000.exe (PID: 2104)
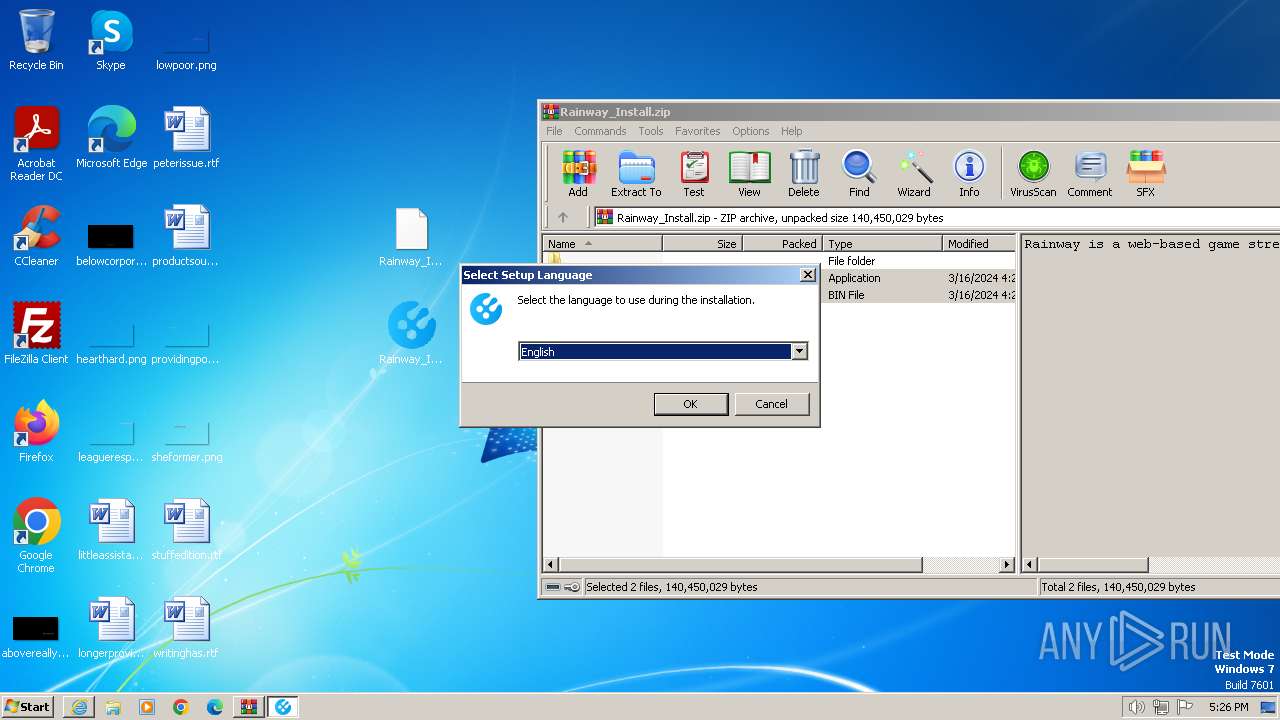
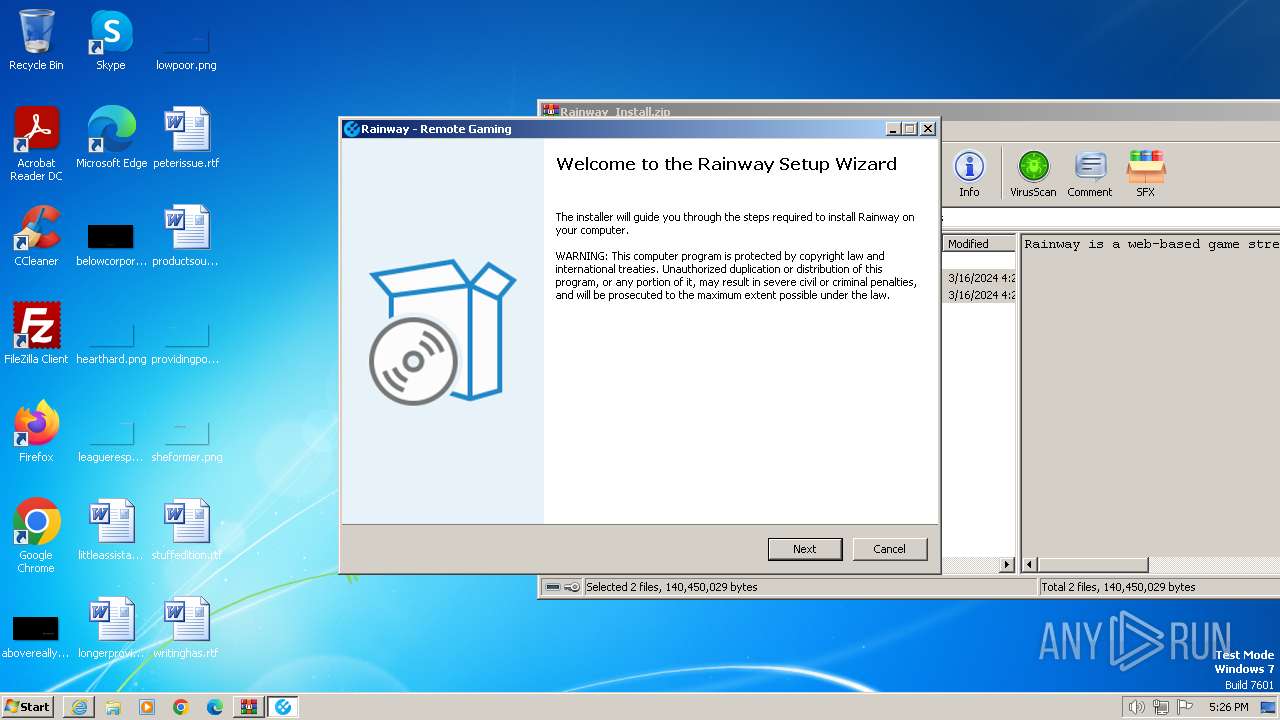
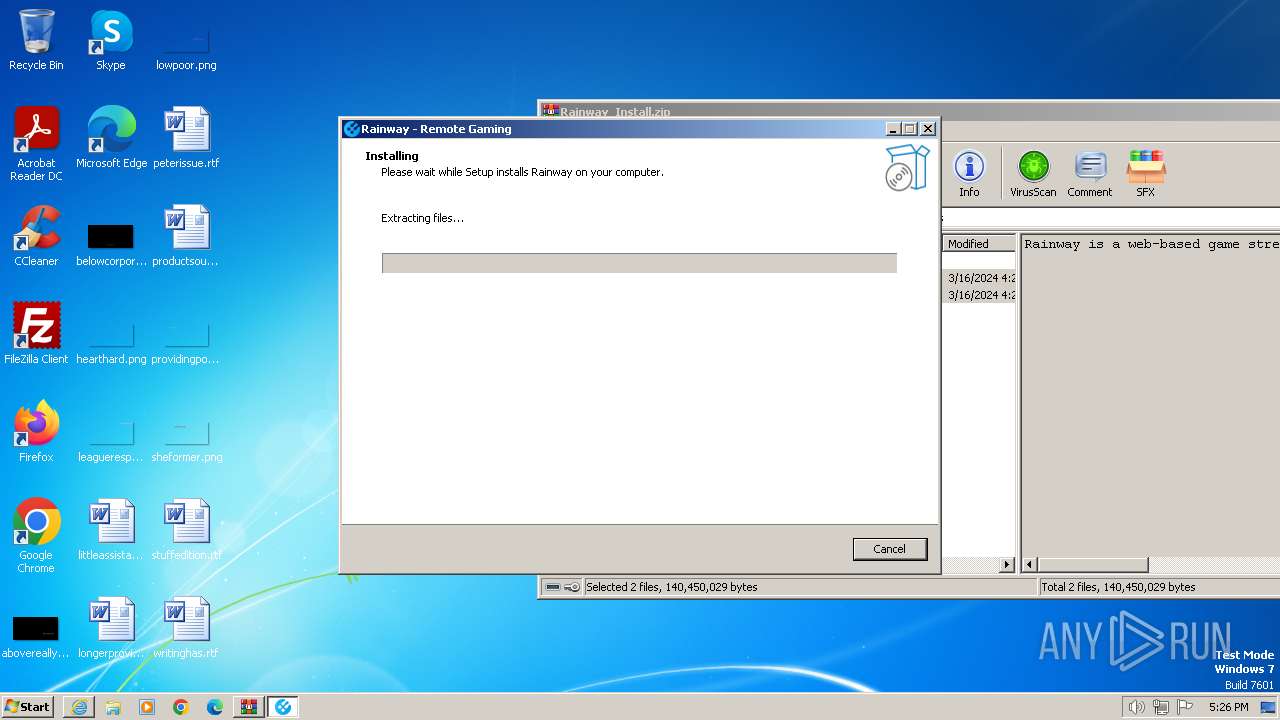
Manual execution by a user
- Rainway_Install.exe (PID: 1840)
- notepad.exe (PID: 2380)
- unins000.exe (PID: 3044)
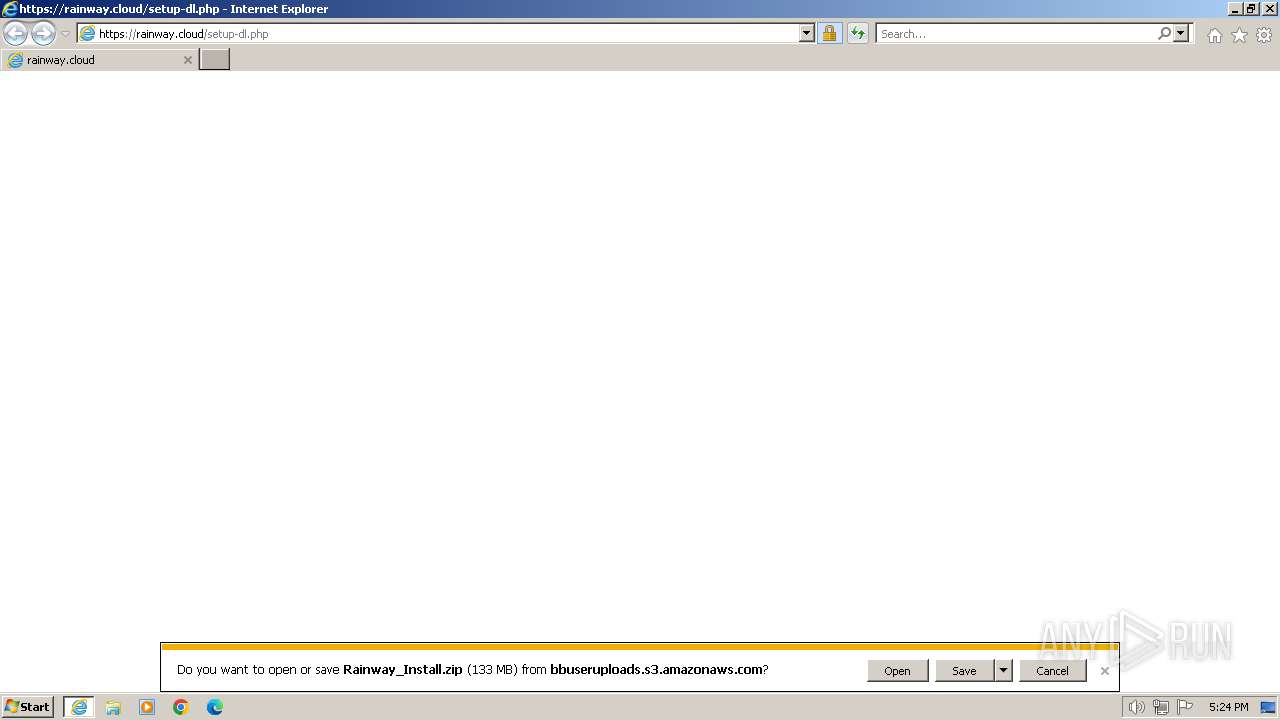
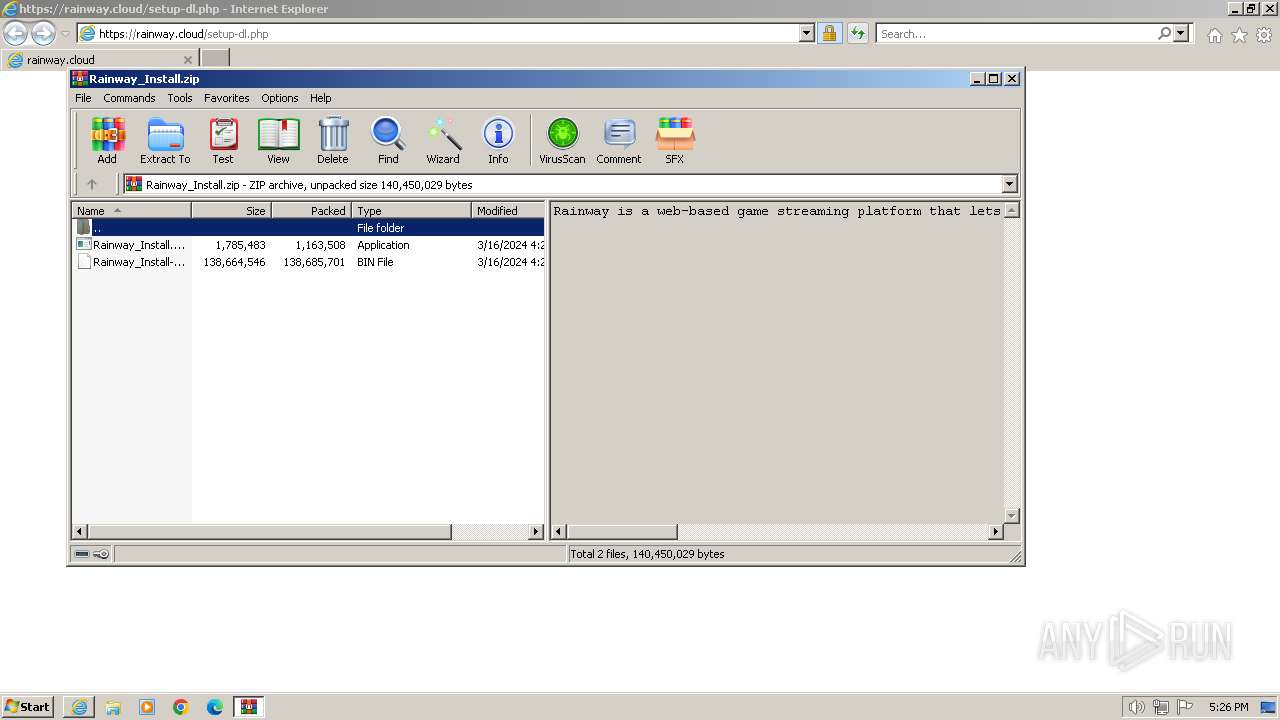
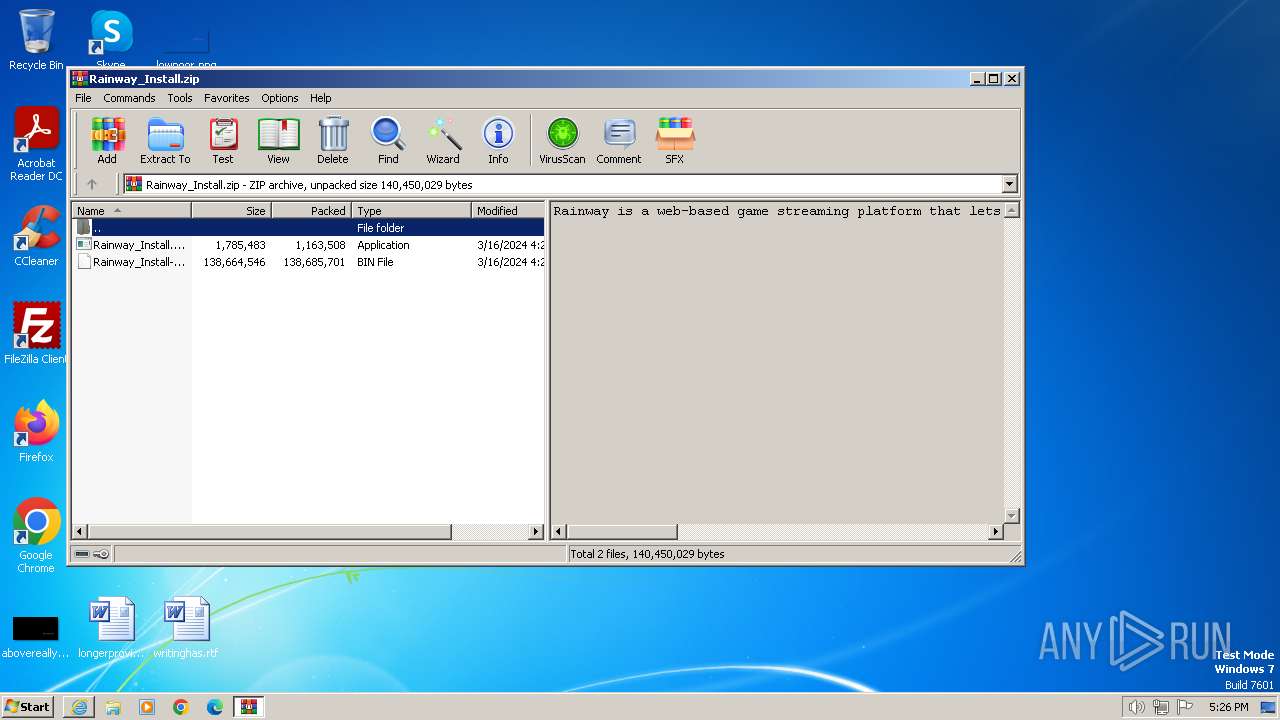
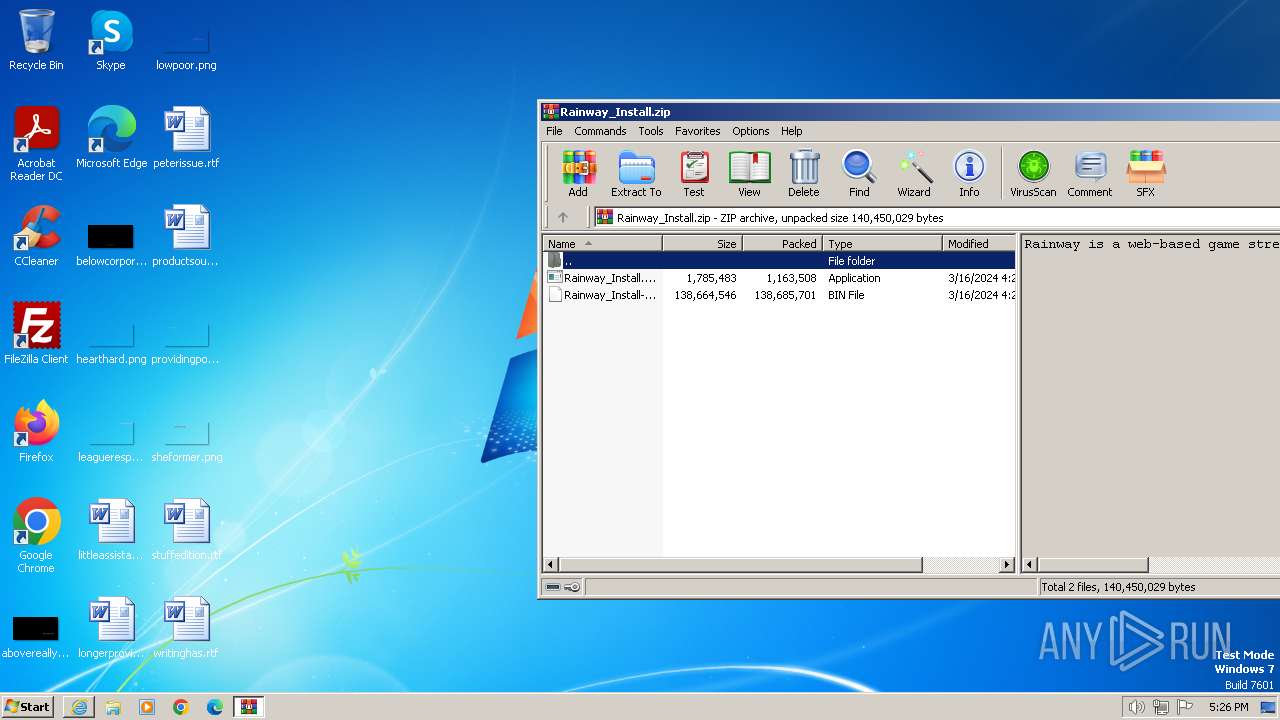
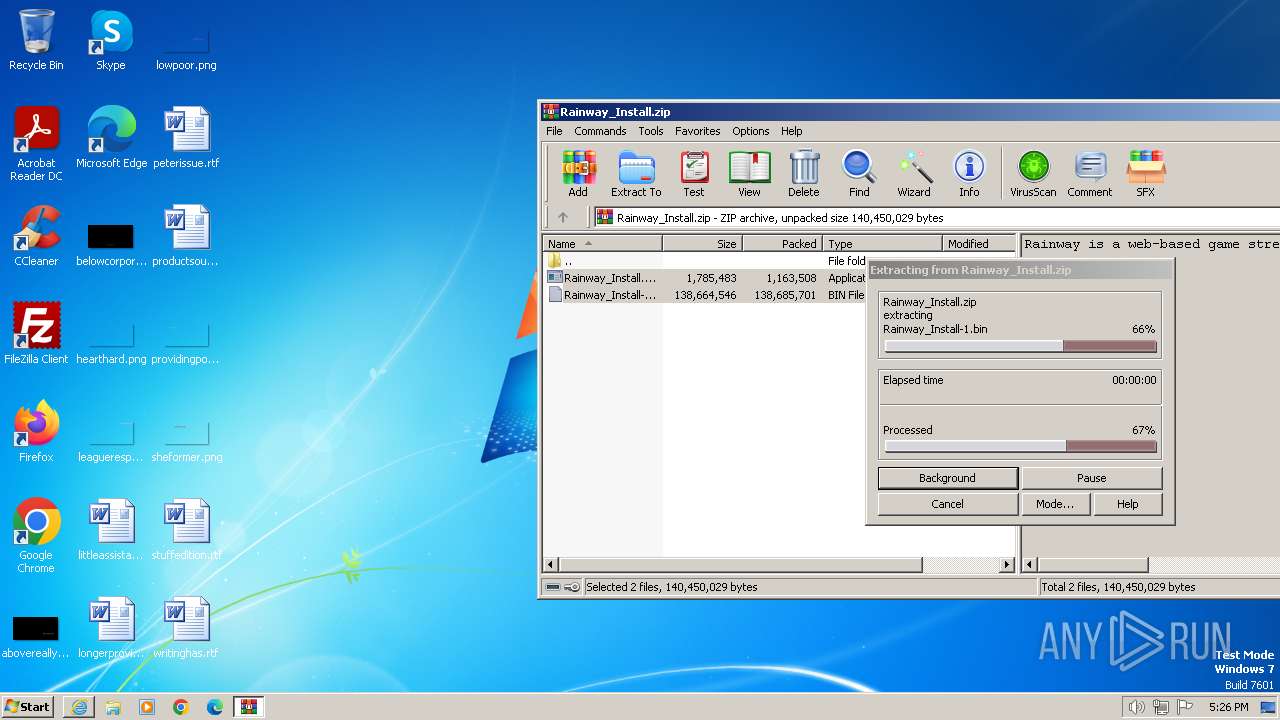
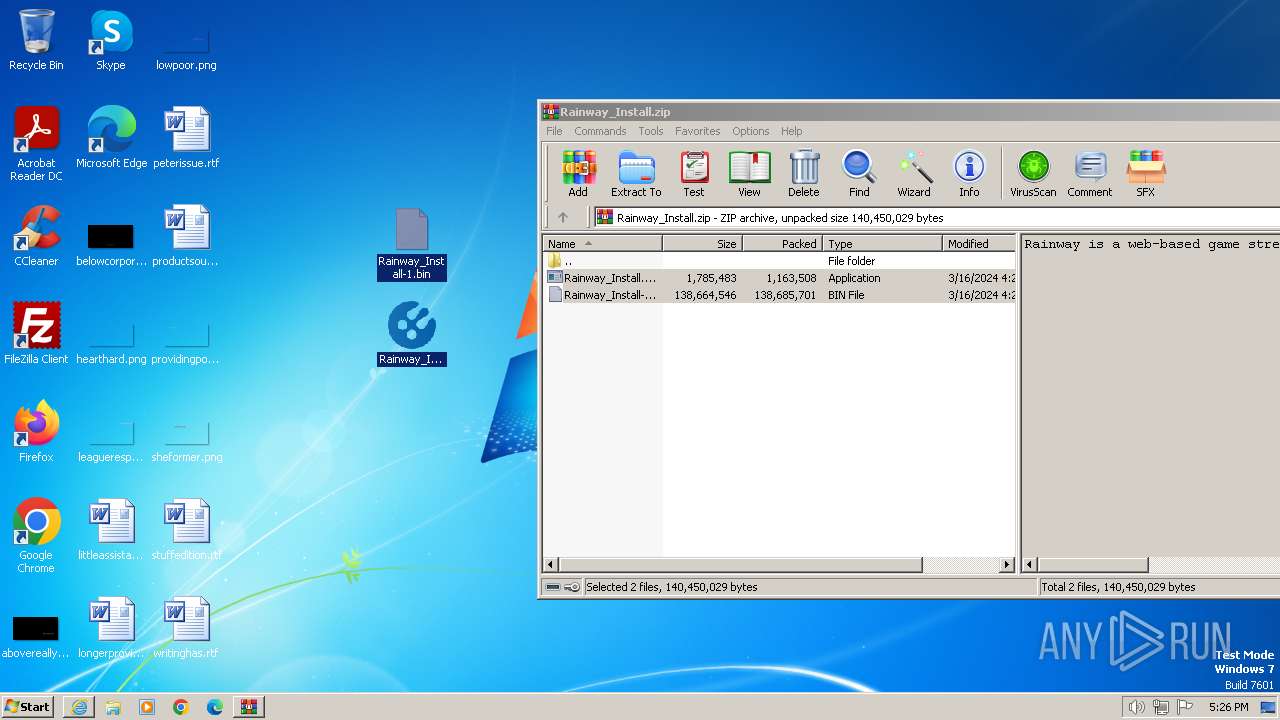
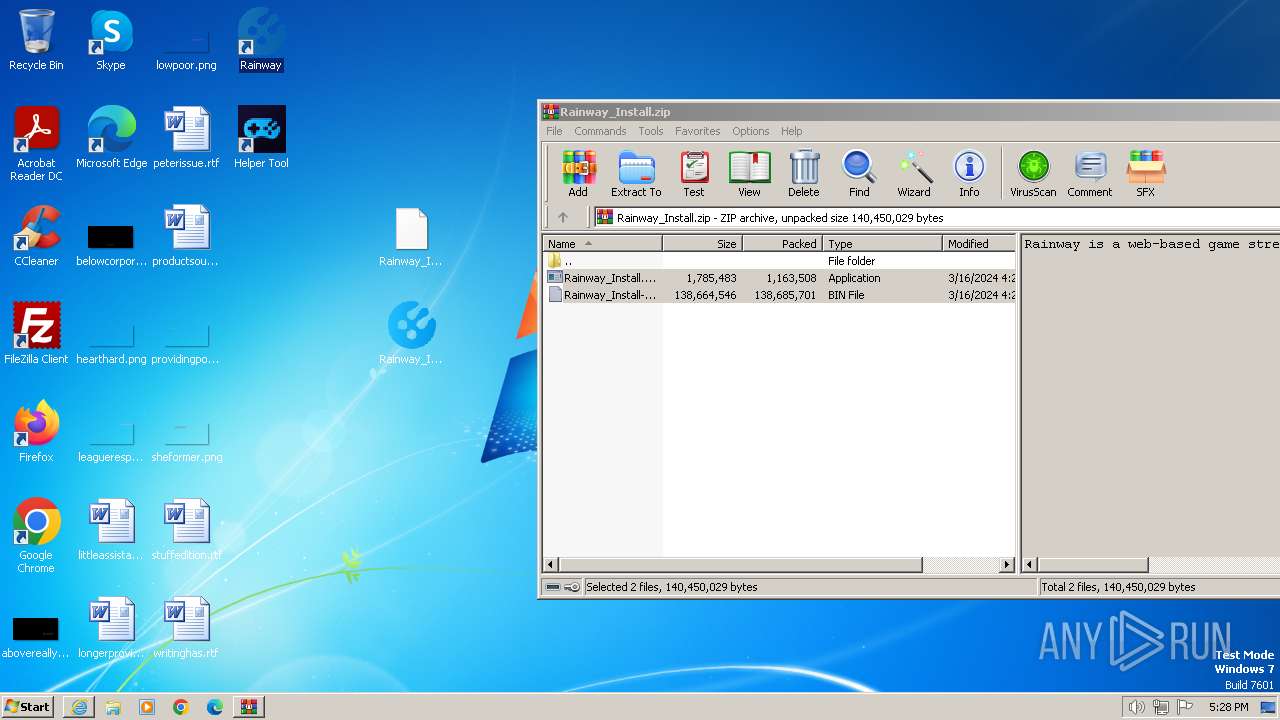
The process uses the downloaded file
- WinRAR.exe (PID: 2384)
- iexplore.exe (PID: 4008)
Application launched itself
- iexplore.exe (PID: 4008)
Modifies the phishing filter of IE
- iexplore.exe (PID: 4008)
Reads the computer name
- Rainway_Install.tmp (PID: 1936)
- Rainway_Install.tmp (PID: 3260)
- unins000.exe (PID: 3044)
- unins000.exe (PID: 2104)
- _unins.tmp (PID: 3748)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2384)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2384)
Checks supported languages
- Rainway_Install.exe (PID: 948)
- Rainway_Install.exe (PID: 1840)
- Rainway_Install.tmp (PID: 1936)
- Rainway_Install.tmp (PID: 3260)
- unins000.exe (PID: 2104)
- unins000.exe (PID: 3044)
- _unins.tmp (PID: 3748)
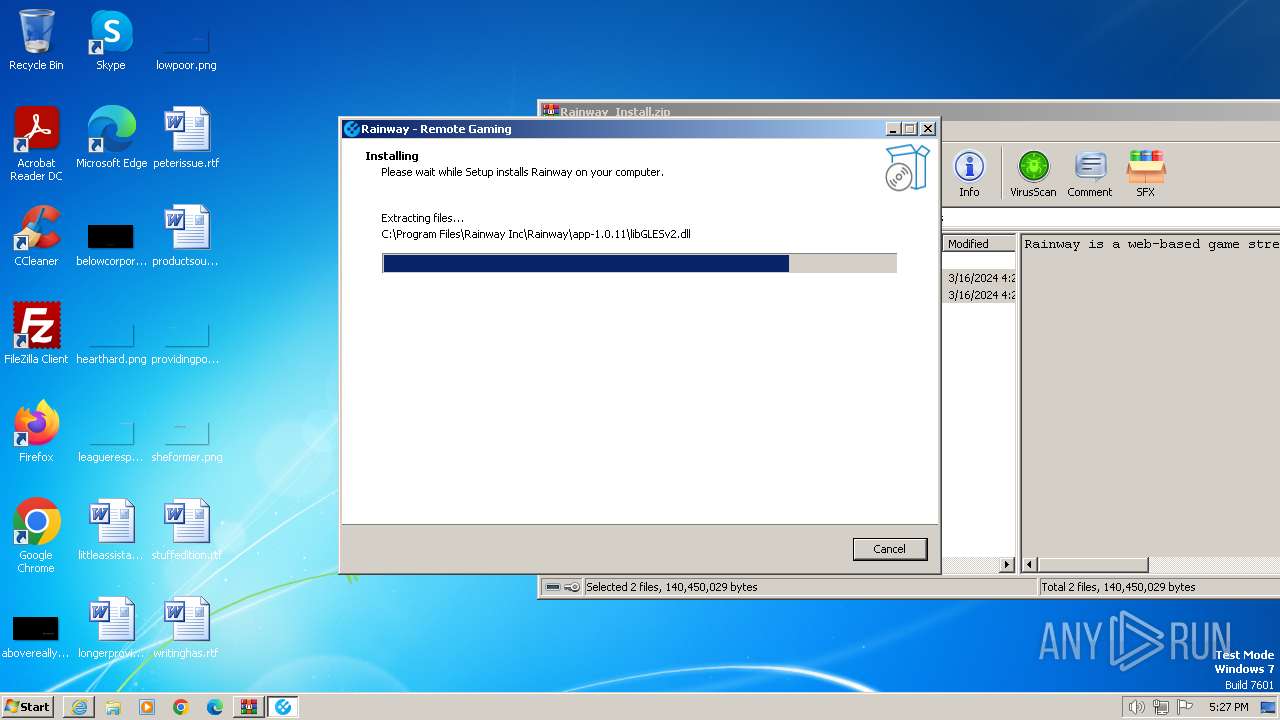
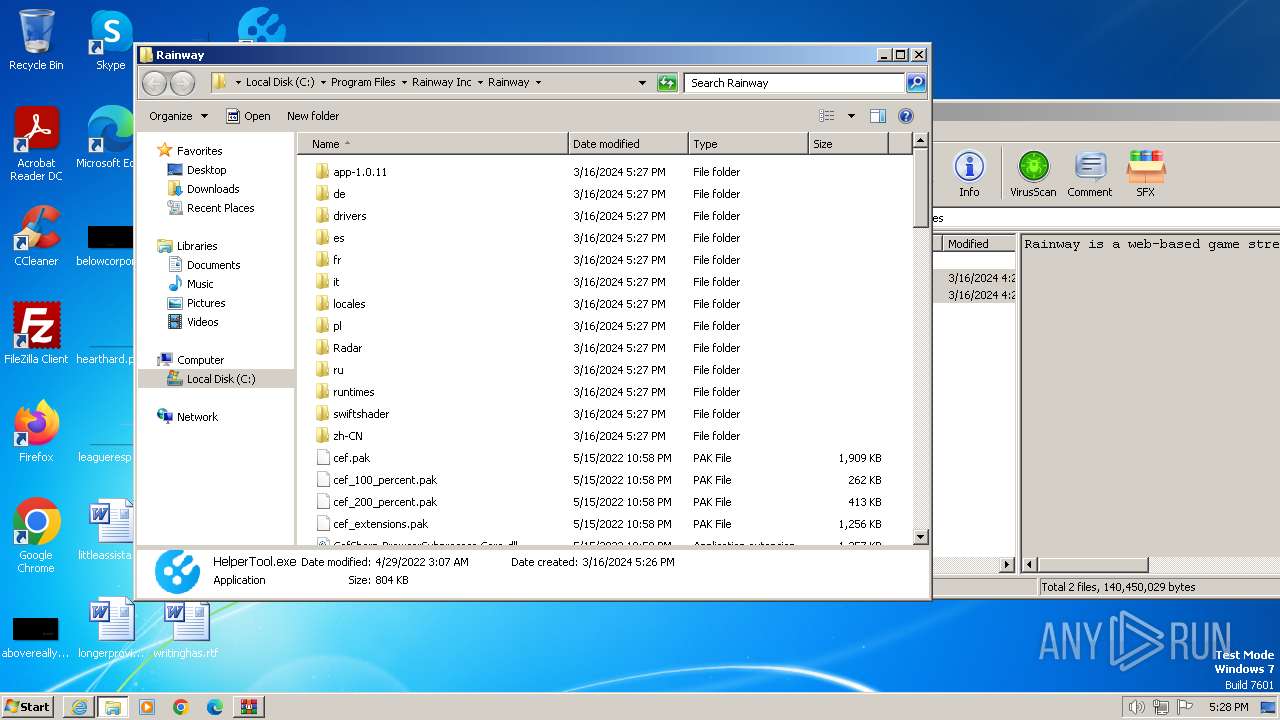
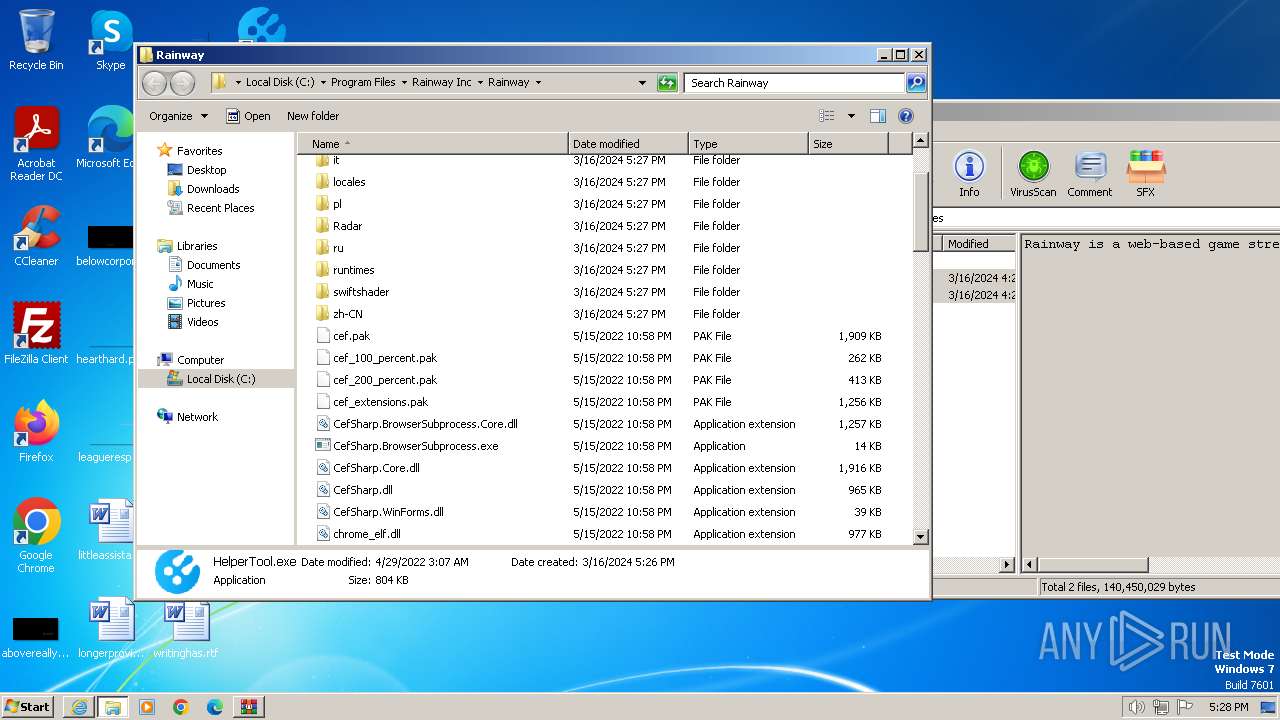
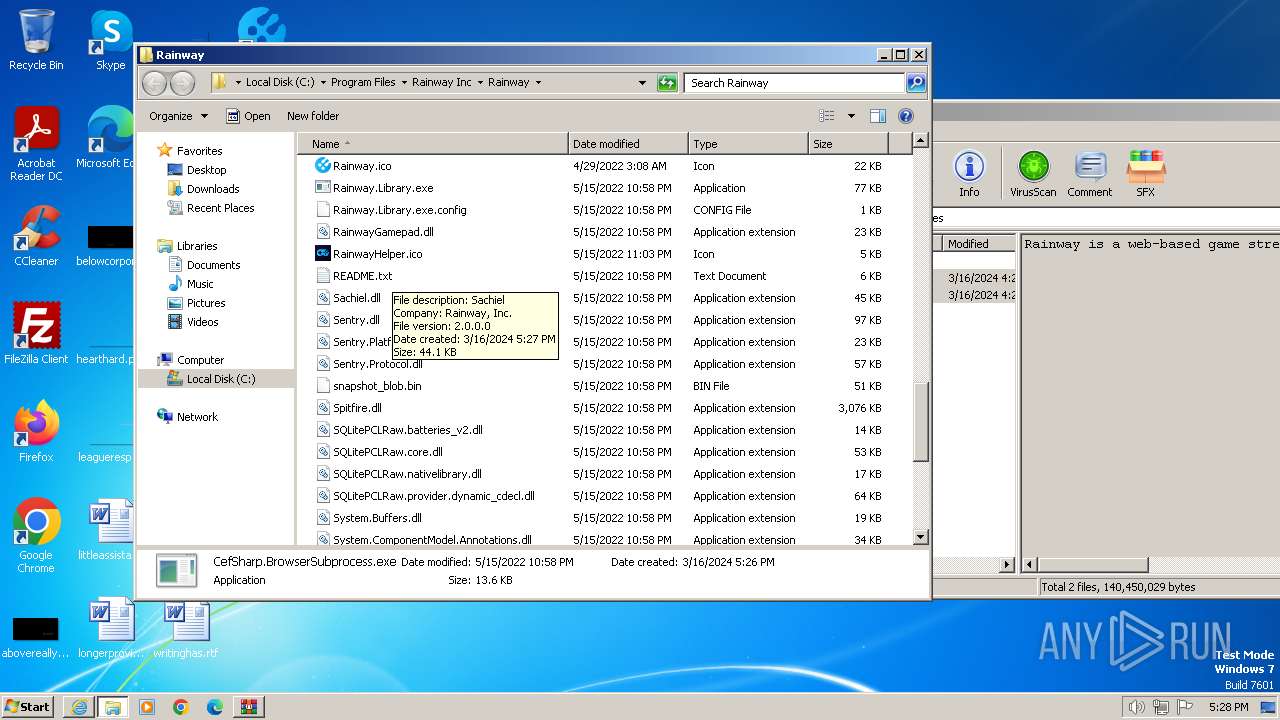
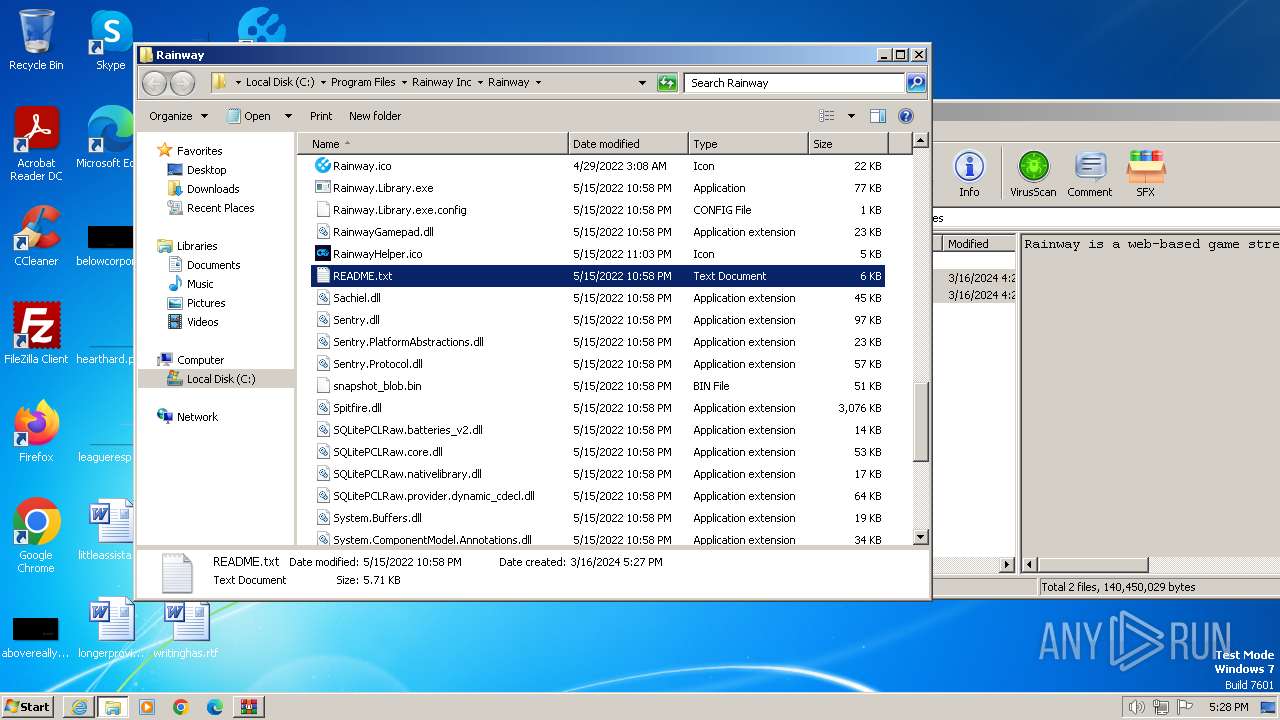
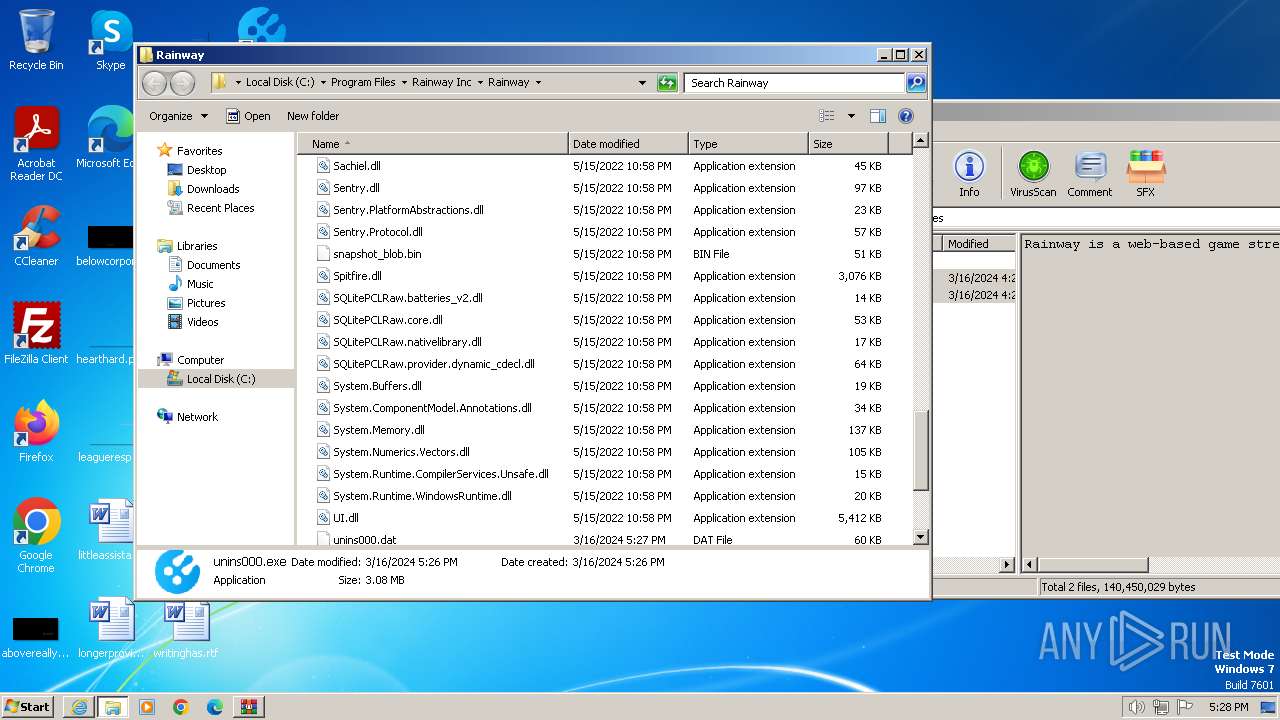
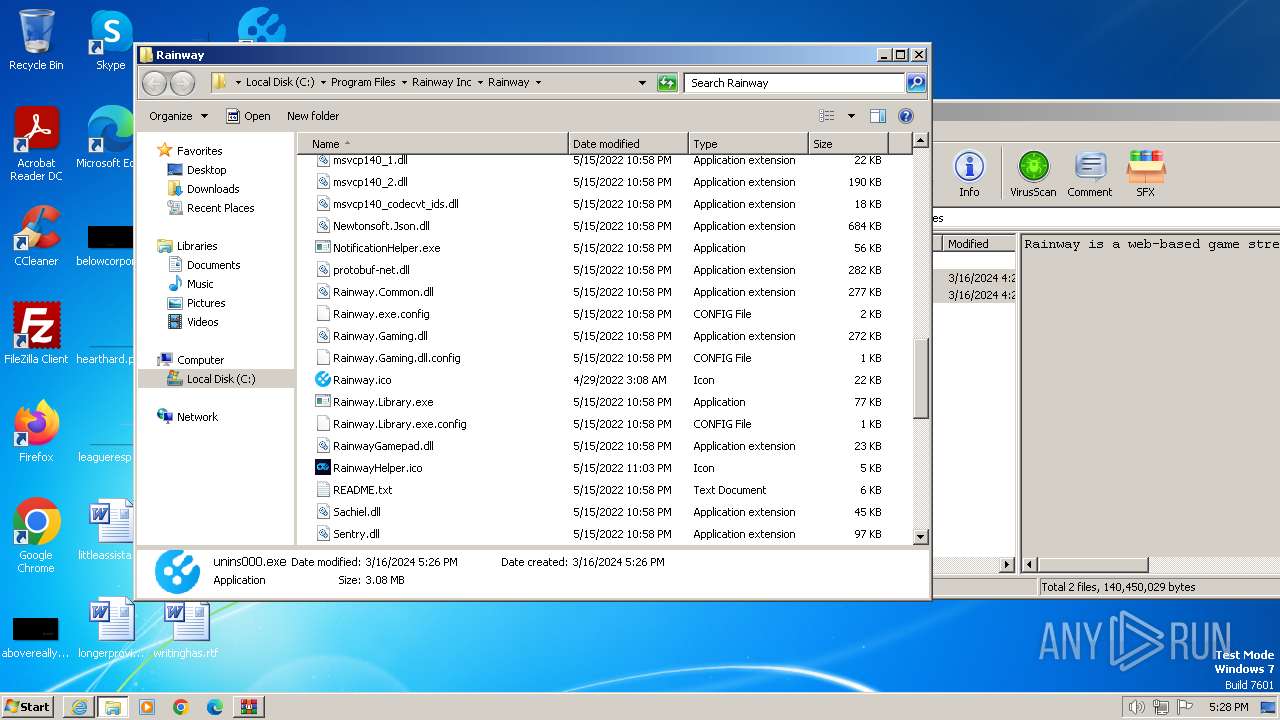
Creates files in the program directory
- Rainway_Install.tmp (PID: 3260)
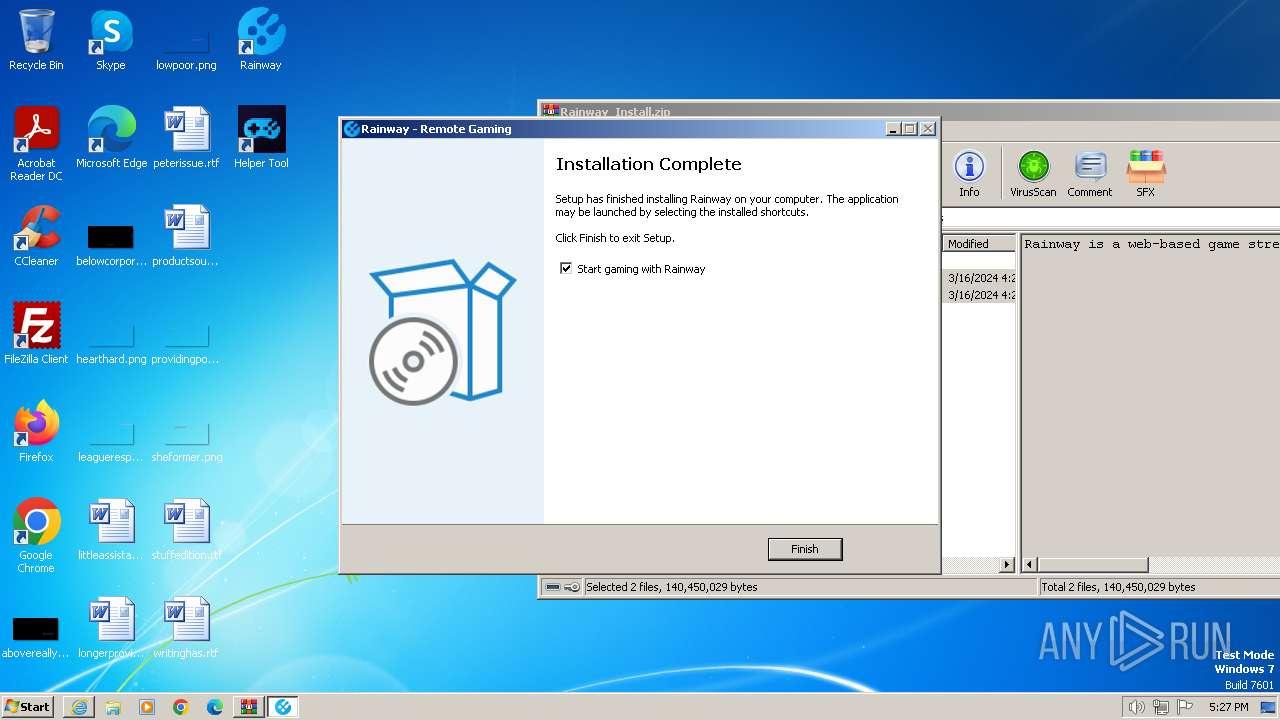
Creates a software uninstall entry
- Rainway_Install.tmp (PID: 3260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
11
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 948 | "C:\Users\admin\Desktop\Rainway_Install.exe" /SPAWNWND=$601F0 /NOTIFYWND=$7025C | C:\Users\admin\Desktop\Rainway_Install.exe | Rainway_Install.tmp | ||||||||||||
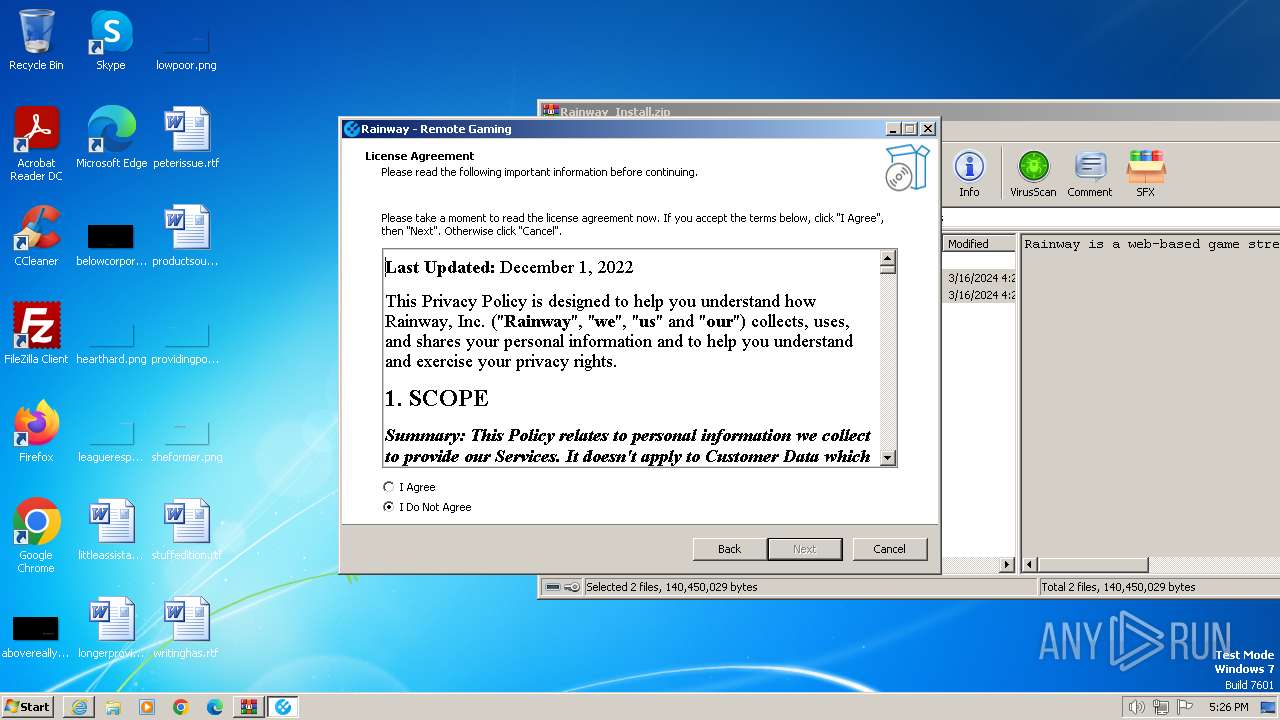
User: admin Company: CLOUD GAMING SOLUTIONS Integrity Level: HIGH Description: Rainway Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1840 | "C:\Users\admin\Desktop\Rainway_Install.exe" | C:\Users\admin\Desktop\Rainway_Install.exe | explorer.exe | ||||||||||||
User: admin Company: CLOUD GAMING SOLUTIONS Integrity Level: MEDIUM Description: Rainway Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1936 | "C:\Users\admin\AppData\Local\Temp\is-H9321.tmp\Rainway_Install.tmp" /SL5="$7025C,882176,0,C:\Users\admin\Desktop\Rainway_Install.exe" | C:\Users\admin\AppData\Local\Temp\is-H9321.tmp\Rainway_Install.tmp | — | Rainway_Install.exe | |||||||||||
User: admin Company: CLOUD GAMING SOLUTIONS Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Rainway Inc\Rainway\unins000.exe" /INITPROCWND=$100172 | C:\Program Files\Rainway Inc\Rainway\unins000.exe | unins000.exe | ||||||||||||
User: admin Company: CLOUD GAMING SOLUTIONS Integrity Level: HIGH Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
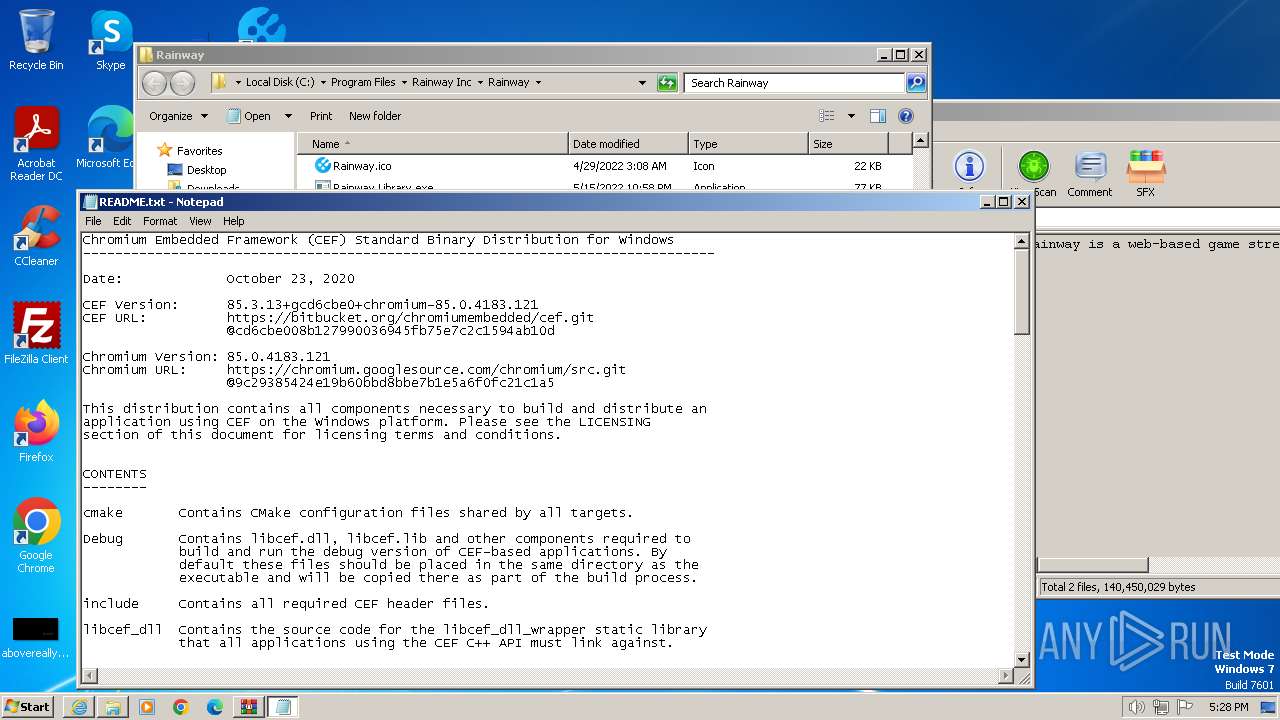
| 2380 | "C:\Windows\system32\NOTEPAD.EXE" C:\Program Files\Rainway Inc\Rainway\README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2384 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\Rainway_Install.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3044 | "C:\Program Files\Rainway Inc\Rainway\unins000.exe" | C:\Program Files\Rainway Inc\Rainway\unins000.exe | — | explorer.exe | |||||||||||
User: admin Company: CLOUD GAMING SOLUTIONS Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3260 | "C:\Users\admin\AppData\Local\Temp\is-CKBTD.tmp\Rainway_Install.tmp" /SL5="$701EE,882176,0,C:\Users\admin\Desktop\Rainway_Install.exe" /SPAWNWND=$601F0 /NOTIFYWND=$7025C | C:\Users\admin\AppData\Local\Temp\is-CKBTD.tmp\Rainway_Install.tmp | Rainway_Install.exe | ||||||||||||
User: admin Company: CLOUD GAMING SOLUTIONS Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3276 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4008 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3748 | "C:\Users\admin\AppData\Local\Temp\iu-14D2N.tmp\_unins.tmp" /SECONDPHASE="C:\Program Files\Rainway Inc\Rainway\unins000.exe" /FIRSTPHASEWND=$50276 /INITPROCWND=$100172 | C:\Users\admin\AppData\Local\Temp\iu-14D2N.tmp\_unins.tmp | — | unins000.exe | |||||||||||
User: admin Company: CLOUD GAMING SOLUTIONS Integrity Level: HIGH Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
26 174
Read events
25 979
Write events
147
Delete events
48
Modification events
| (PID) Process: | (4008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (4008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (4008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31094726 | |||
| (PID) Process: | (4008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (4008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31094726 | |||
| (PID) Process: | (4008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4008) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
397
Suspicious files
284
Text files
50
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4008 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 4008 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:0C637474CCCC83C16B8DDE5025D978C9 | SHA256:9107CD4E9A5743DA4B926CCFE6803E45EF07D258EC0EB4DC98B8225899B4D227 | |||
| 3276 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\298B71D6992EC2049F9CD4EAB7F99E71 | binary | |
MD5:92F710EF1D47416CB5724AABD919C368 | SHA256:4DD393542C7715DD1C5D737E94E11AA7FA160E3C2E0AEF0D9344FD3CEE78C2C3 | |||
| 3276 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C31B2498754E340573F1336DE607D619 | der | |
MD5:260D774F4B728A36B6F75C4023A5EF9B | SHA256:C6DECD57E51CA9EFBFC451E7EC14FBD5D8738A313ECB3B5DE60DFDD2C1F6F96E | |||
| 4008 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:0B1477142EE1F0309A8D0D1295C23AB2 | SHA256:D398B1961291A6EFF852019C8C09A5E91706E66A77782F1A11079D464CF8DB25 | |||
| 3276 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\298B71D6992EC2049F9CD4EAB7F99E71 | binary | |
MD5:3F7E919FE0B0ACB5E8450FEEC75EDC51 | SHA256:9BA3E573F5C789D6EFB5B08778B215FF4344D8DD8291E934F6BE0C4044C8644F | |||
| 3276 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2650.tmp | cat | |
MD5:DD73CEAD4B93366CF3465C8CD32E2796 | SHA256:A6752B7851B591550E4625B832A393AABCC428DE18D83E8593CD540F7D7CAE22 | |||
| 3276 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:753DF6889FD7410A2E9FE333DA83A429 | SHA256:B42DC237E44CBC9A43400E7D3F9CBD406DBDEFD62BFE87328F8663897D69DF78 | |||
| 3276 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:822467B728B7A66B081C91795373789A | SHA256:AF2343382B88335EEA72251AD84949E244FF54B6995063E24459A7216E9576B9 | |||
| 3276 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:DEF52CA1DCDB521916564D461B69B322 | SHA256:8FF7E1E458B8EC54BDB3EC541EB6D3FCA82C65C2CAABEE00058E1802896BBBFF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
38
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3276 | iexplore.exe | GET | 304 | 88.221.110.65:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7f30423e8f7249ff | DE | — | — | unknown |
3276 | iexplore.exe | GET | 200 | 95.101.54.99:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgNRrjyjD1tDCmImFIl6ZqUA1A%3D%3D | DE | binary | 503 b | unknown |
3276 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | binary | 471 b | unknown |
3276 | iexplore.exe | GET | 304 | 2.16.100.169:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5259f1aa84763c8c | DE | — | — | unknown |
4008 | iexplore.exe | GET | 304 | 2.16.100.169:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?aeb32cb922858c96 | DE | — | — | unknown |
4008 | iexplore.exe | GET | 304 | 2.16.100.169:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e55f0cb727843010 | DE | — | — | unknown |
4008 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | US | binary | 312 b | unknown |
3276 | iexplore.exe | GET | 200 | 18.65.41.80:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | binary | 1.49 Kb | unknown |
3276 | iexplore.exe | GET | 200 | 108.138.26.102:80 | http://s.ss2.us/r.crl | US | binary | 486 b | unknown |
3276 | iexplore.exe | GET | 200 | 18.245.39.64:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwdzEjgLnWaIozse2b%2BczaaODg8%3D | US | binary | 1.37 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
3276 | iexplore.exe | 5.42.64.83:443 | rainway.cloud | CJSC Kolomna-Sviaz TV | RU | unknown |
3276 | iexplore.exe | 2.16.100.169:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3276 | iexplore.exe | 88.221.110.65:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3276 | iexplore.exe | 2.23.197.184:80 | x1.c.lencr.org | CW Vodafone Group PLC | GB | unknown |
3276 | iexplore.exe | 95.101.54.99:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
4008 | iexplore.exe | 5.42.64.83:443 | rainway.cloud | CJSC Kolomna-Sviaz TV | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rainway.cloud |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
bitbucket.org |
| shared |
ocsp.digicert.com |
| whitelisted |
bbuseruploads.s3.amazonaws.com |
| shared |
o.ss2.us |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |