| File name: | MEMZ.exe |
| Full analysis: | https://app.any.run/tasks/2db00e8e-1023-4e9b-942d-ed1a7bf1f1a1 |
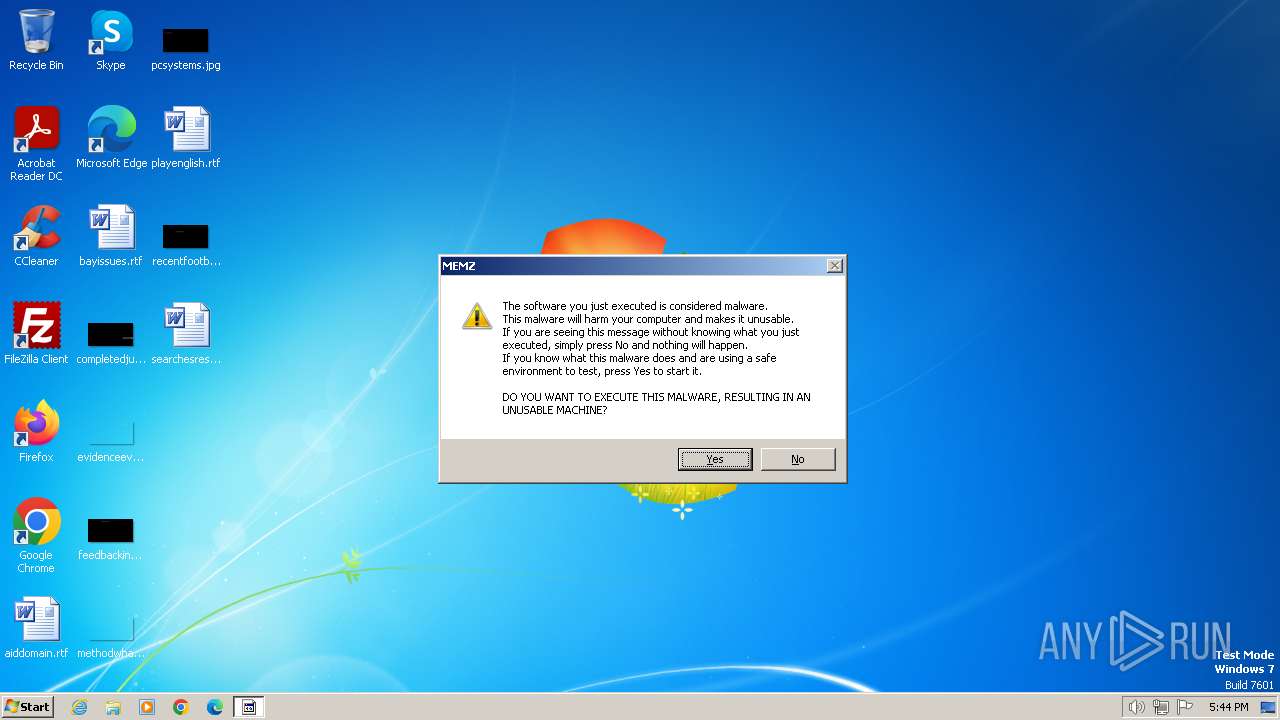
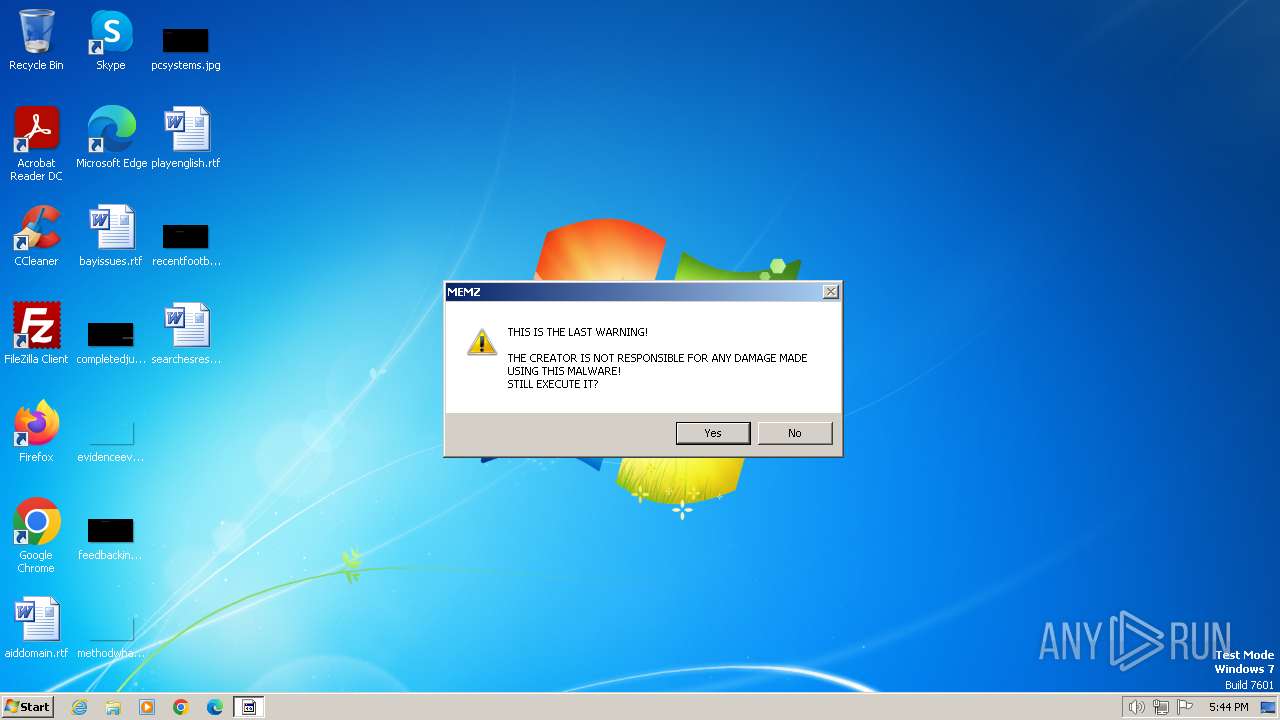
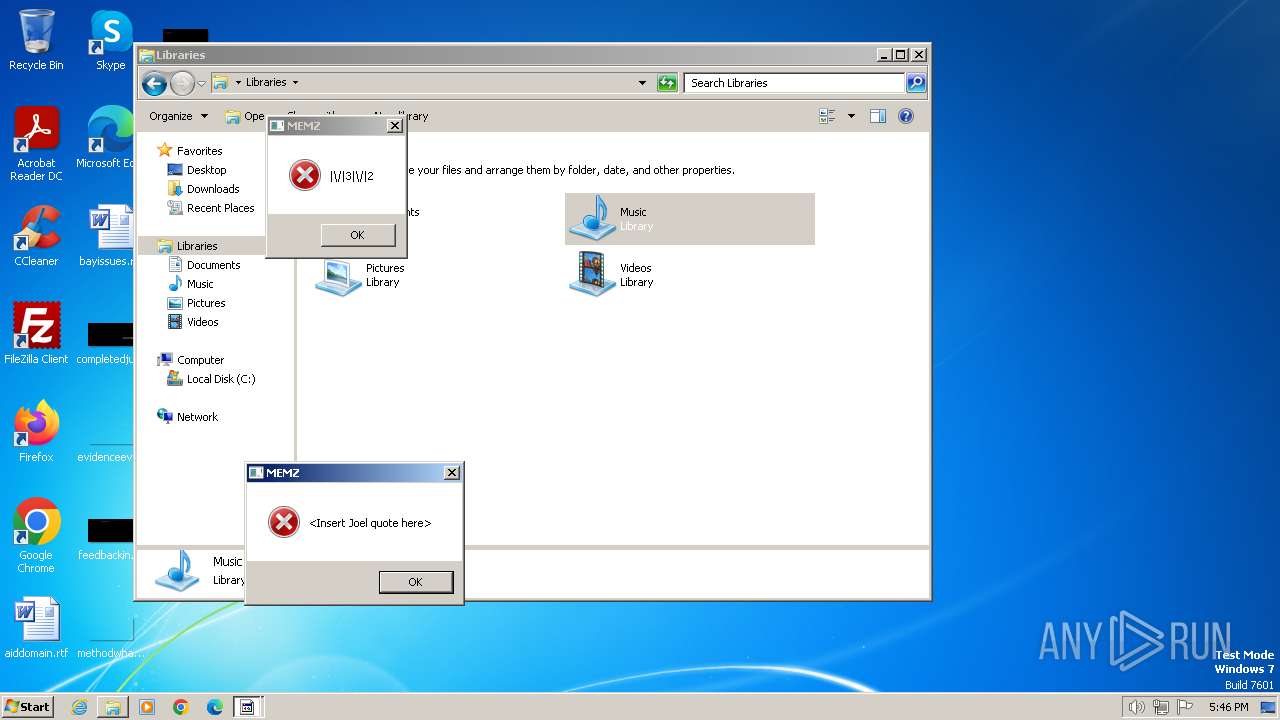
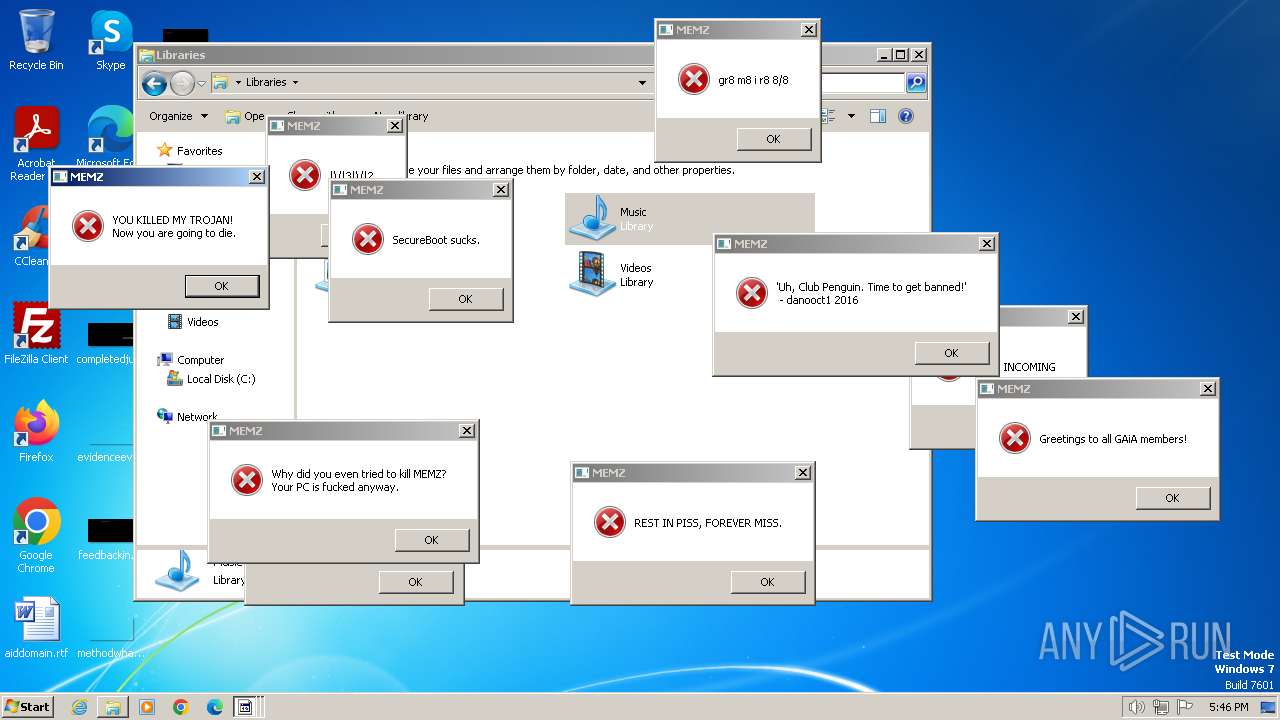
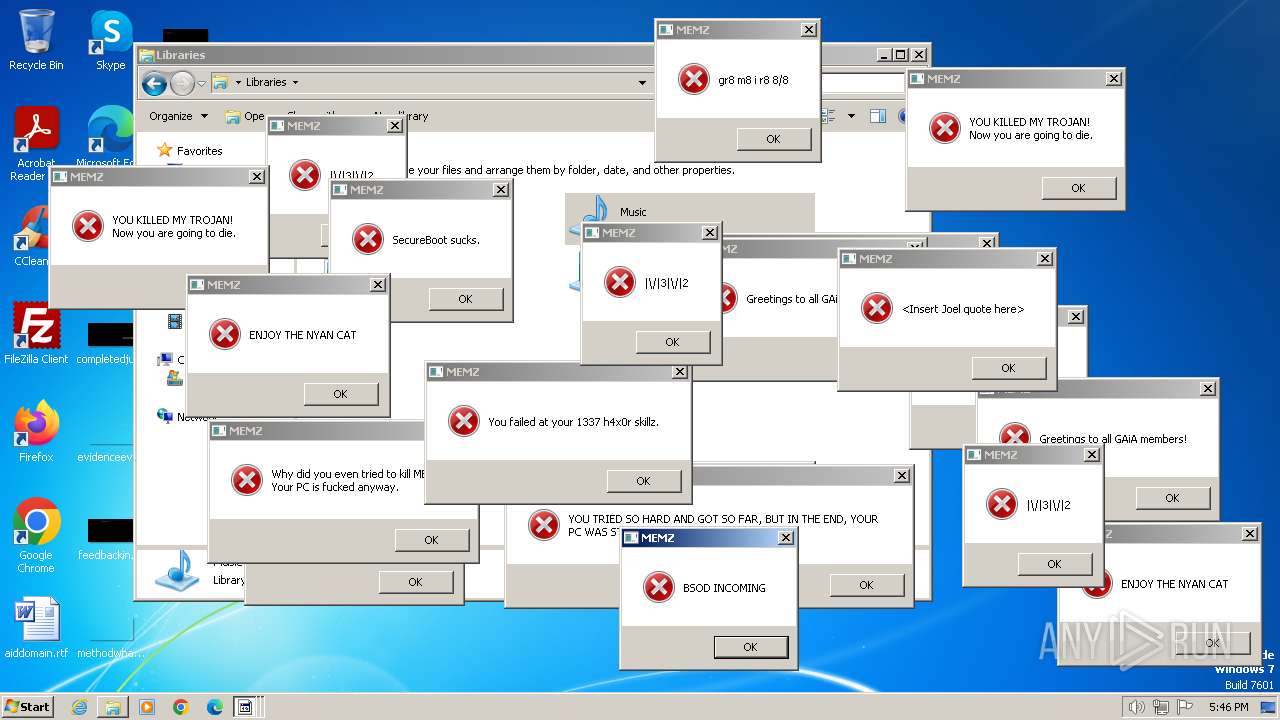
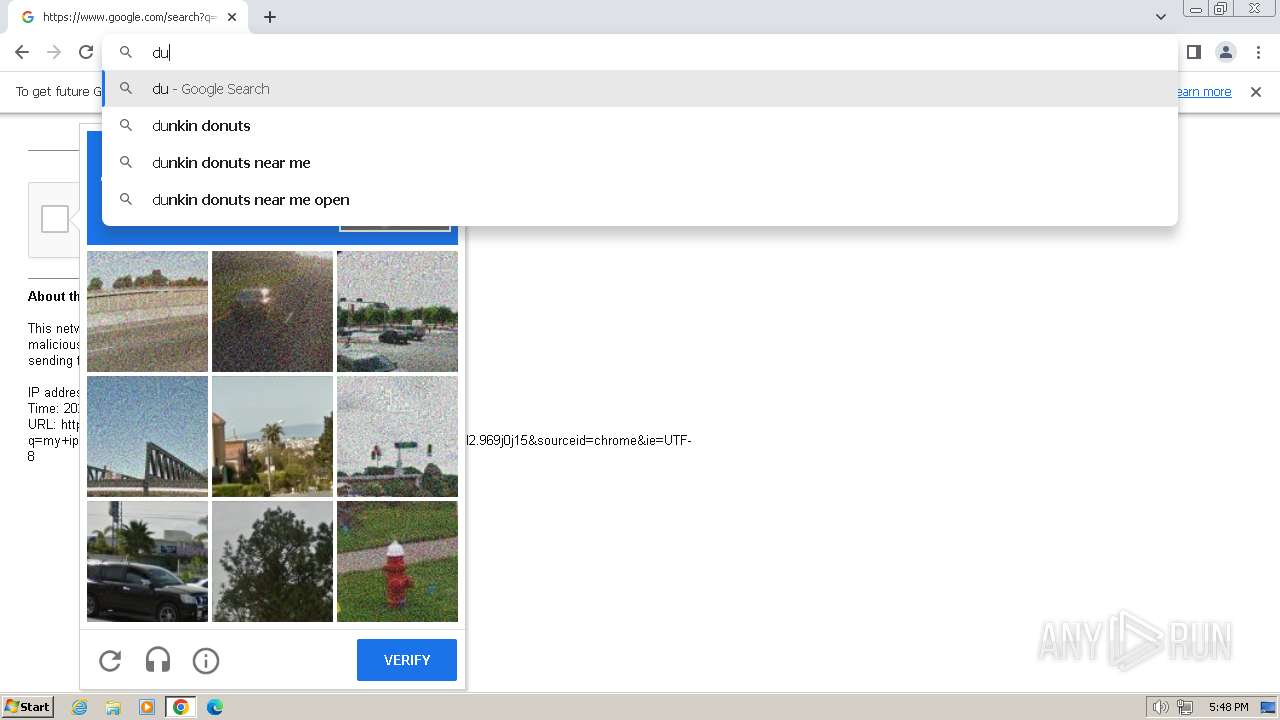
| Verdict: | Malicious activity |
| Analysis date: | January 15, 2024, 17:44:48 |
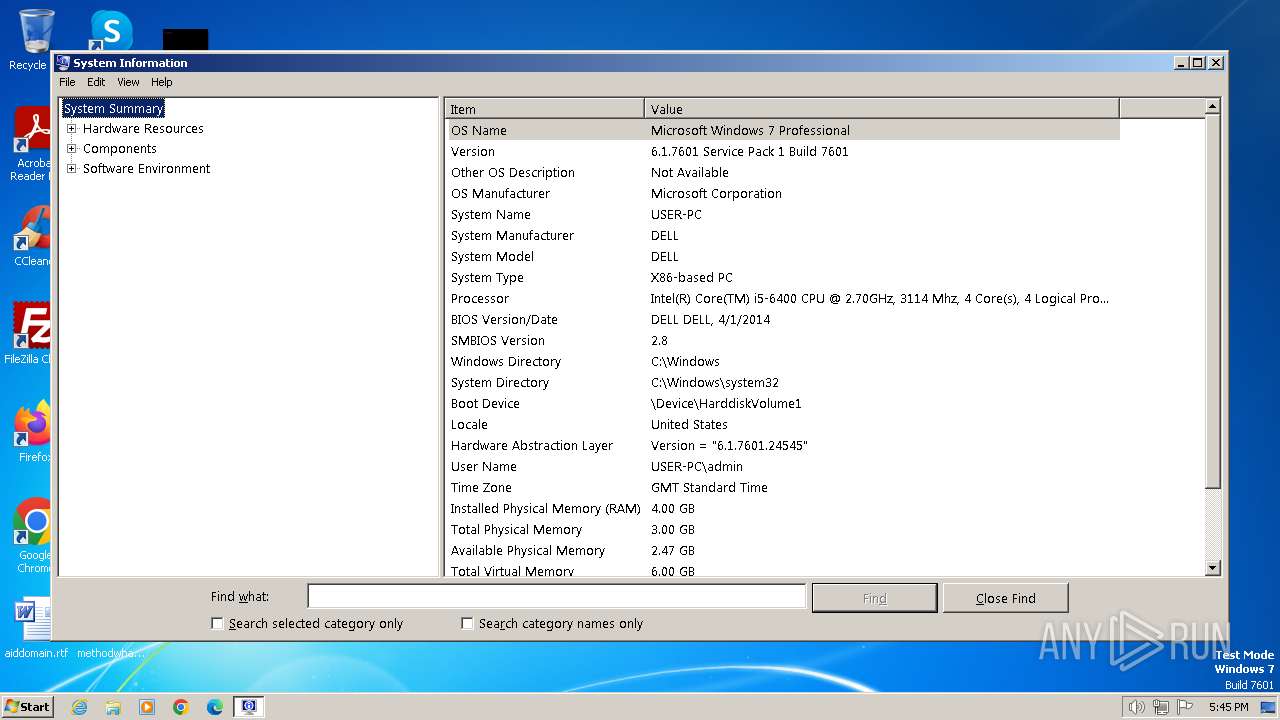
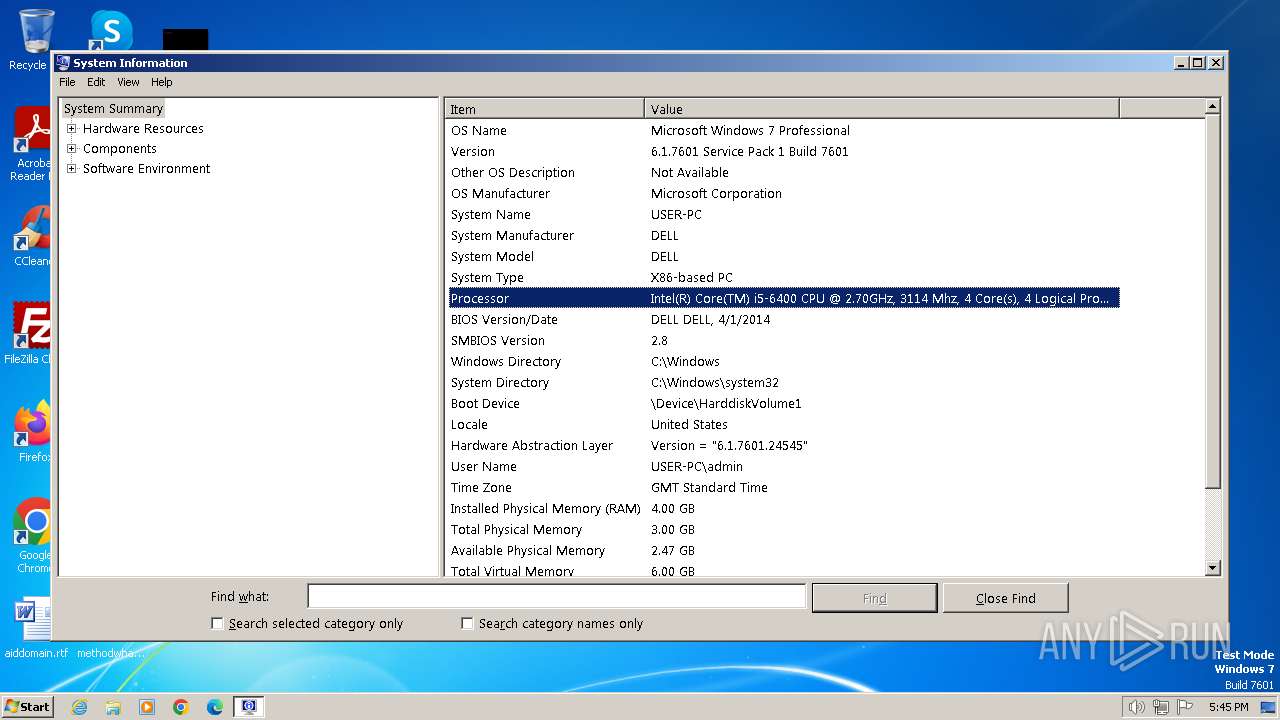
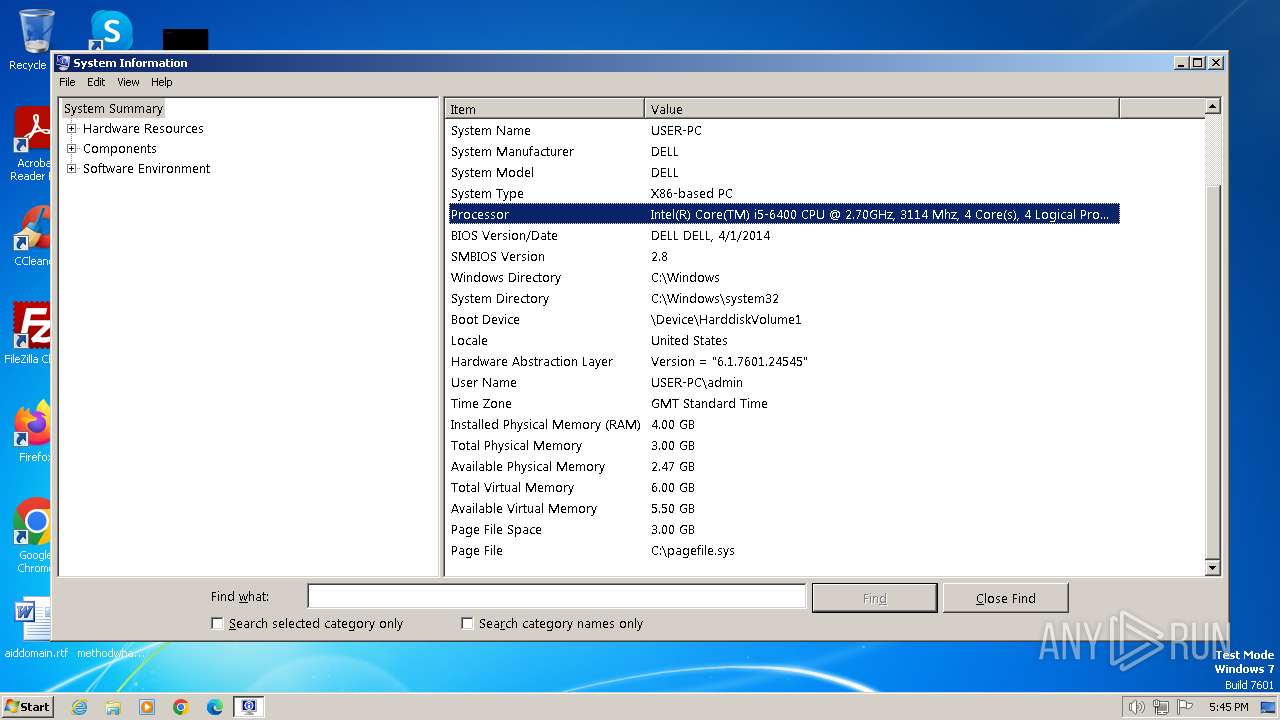
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1D5AD9C8D3FEE874D0FEB8BFAC220A11 |
| SHA1: | CA6D3F7E6C784155F664A9179CA64E4034DF9595 |
| SHA256: | 3872C12D31FC9825E8661AC01ECEE2572460677AFBC7093F920A8436A42E28FF |
| SSDEEP: | 192:M2WgyvSW8gRc6olcIEiwqZKBkDFR43xWTM3LHf26gFrcx3sNqa:JWgnSmFlcIqq3agmLH+6gF23sNj |
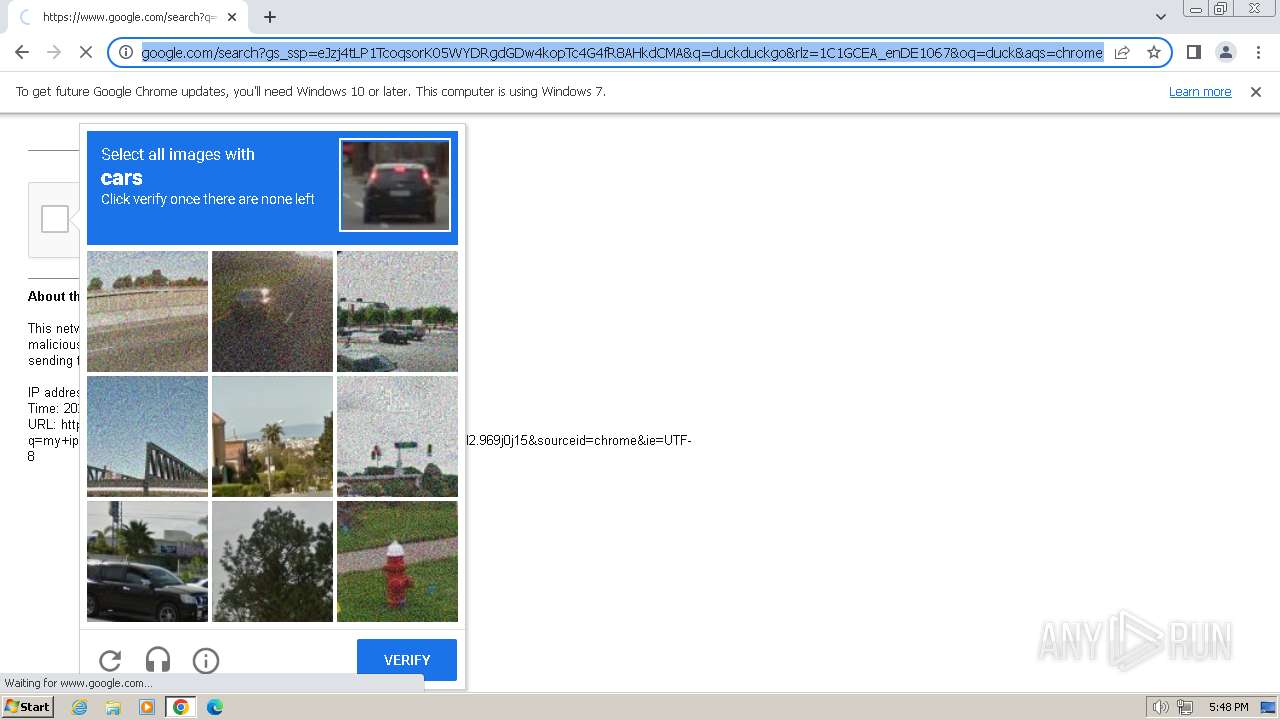
MALICIOUS
Drops the executable file immediately after the start
- MEMZ.exe (PID: 2124)
SUSPICIOUS
The process executes via Task Scheduler
- ctfmon.exe (PID: 1816)
- sipnotify.exe (PID: 604)
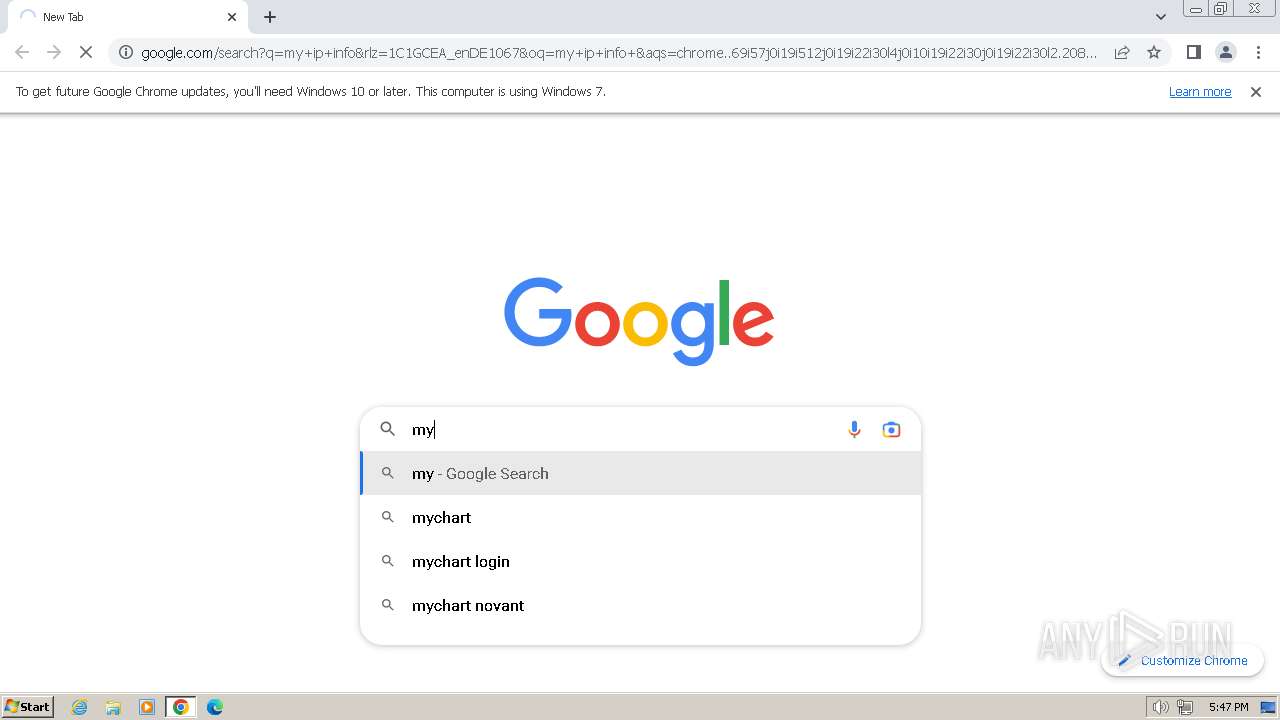
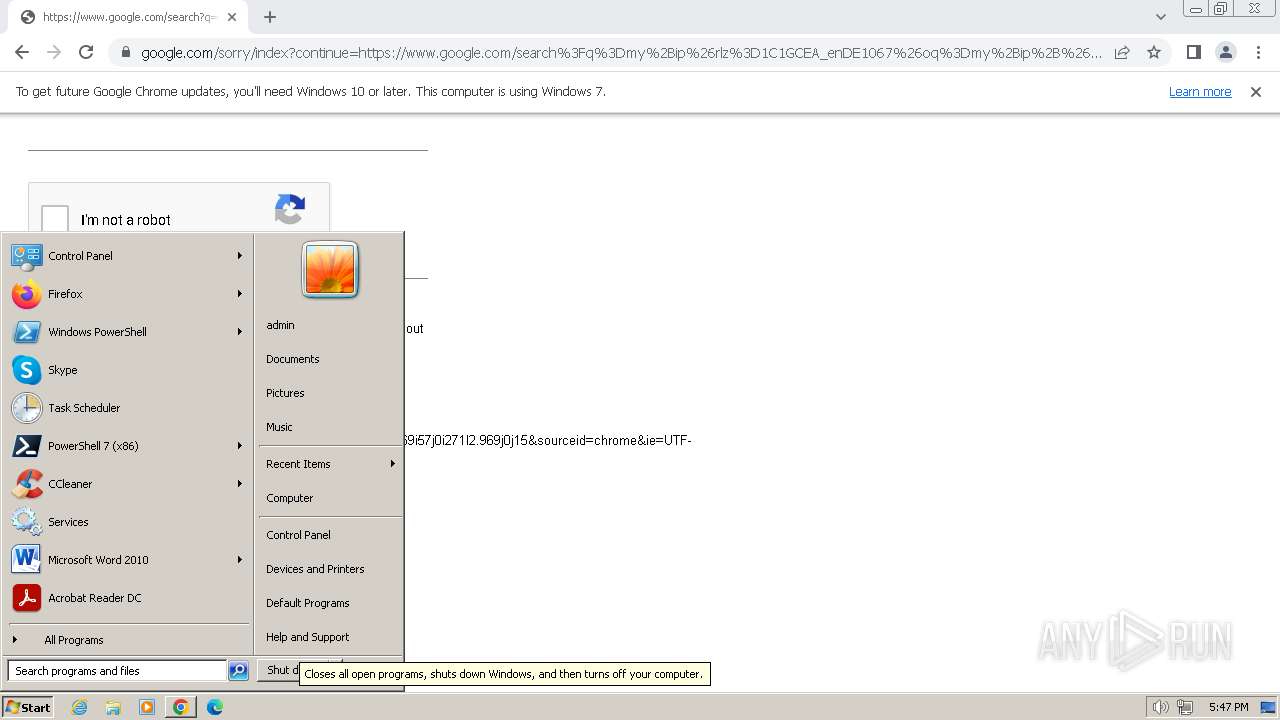
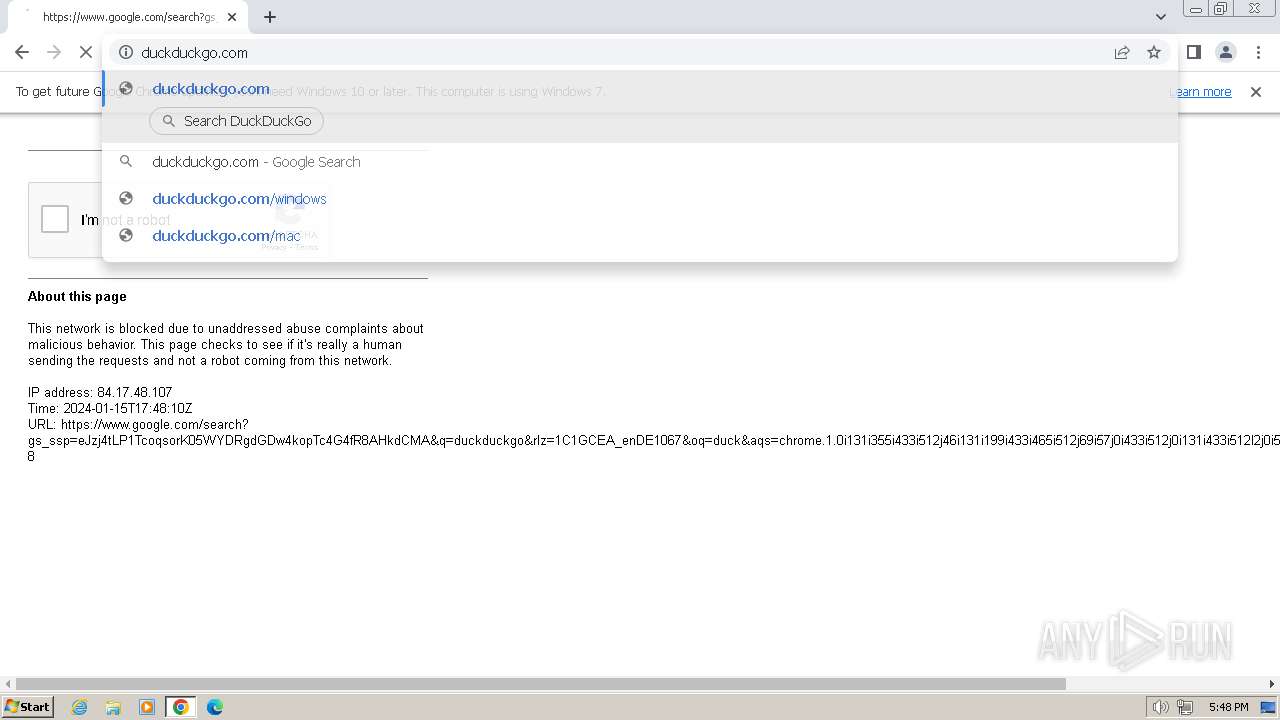
Reads the Internet Settings
- sipnotify.exe (PID: 604)
- runonce.exe (PID: 308)
- MEMZ.exe (PID: 2124)
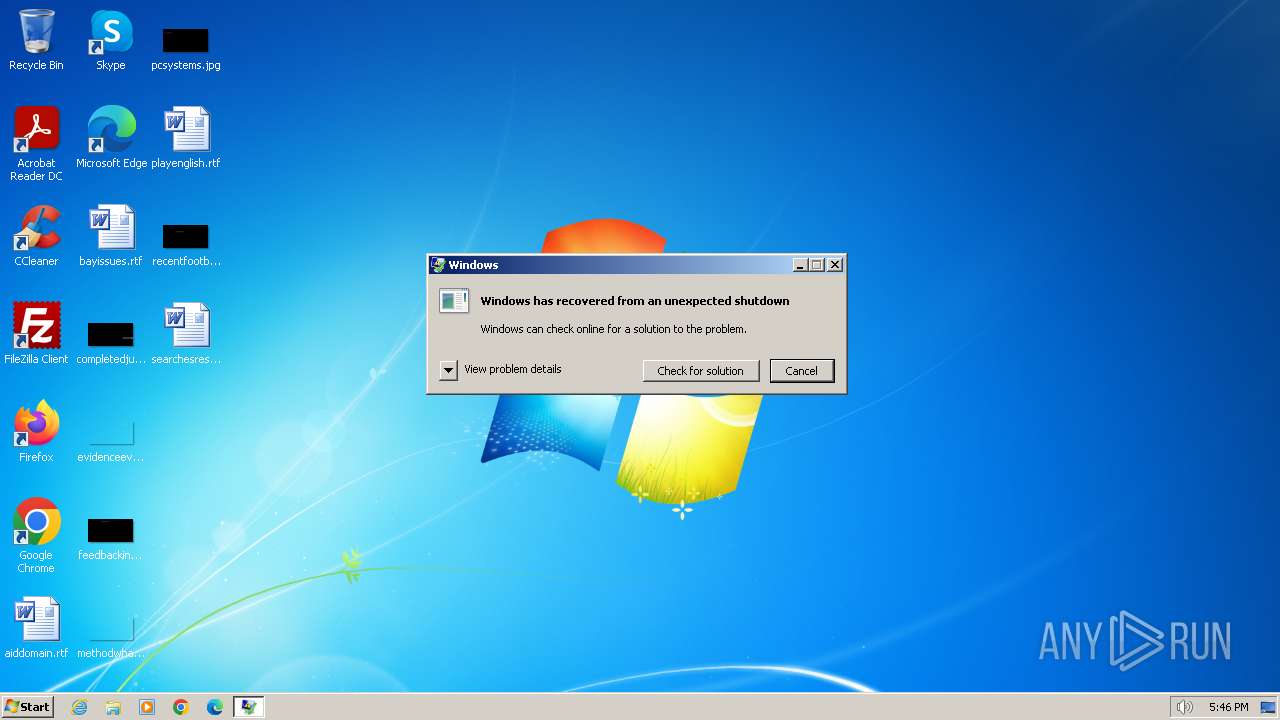
Application launched itself
- WerFault.exe (PID: 1556)
- MEMZ.exe (PID: 2124)
Reads settings of System Certificates
- sipnotify.exe (PID: 604)
INFO
Checks supported languages
- MEMZ.exe (PID: 2124)
- MEMZ.exe (PID: 1356)
- MEMZ.exe (PID: 124)
- MEMZ.exe (PID: 296)
- MEMZ.exe (PID: 392)
- MEMZ.exe (PID: 2204)
- IMEKLMG.EXE (PID: 148)
- IMEKLMG.EXE (PID: 2052)
- wmpnscfg.exe (PID: 2408)
- wmpnscfg.exe (PID: 2460)
- MEMZ.exe (PID: 1072)
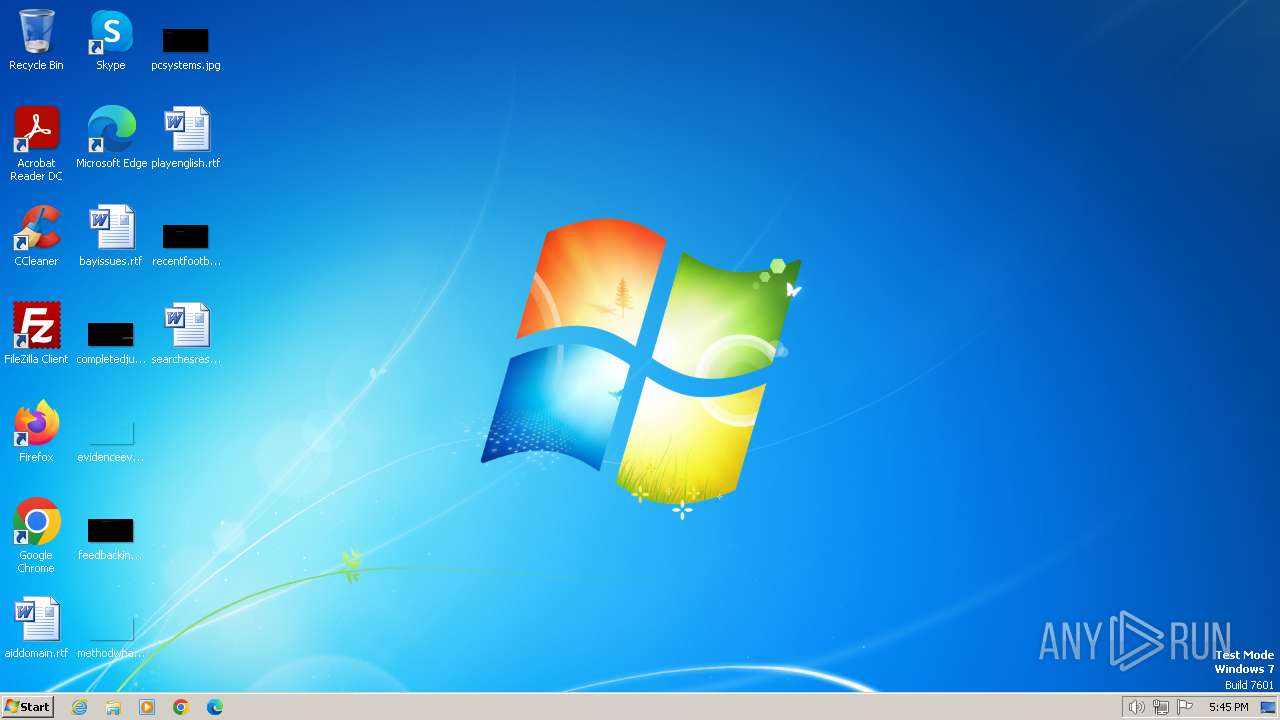
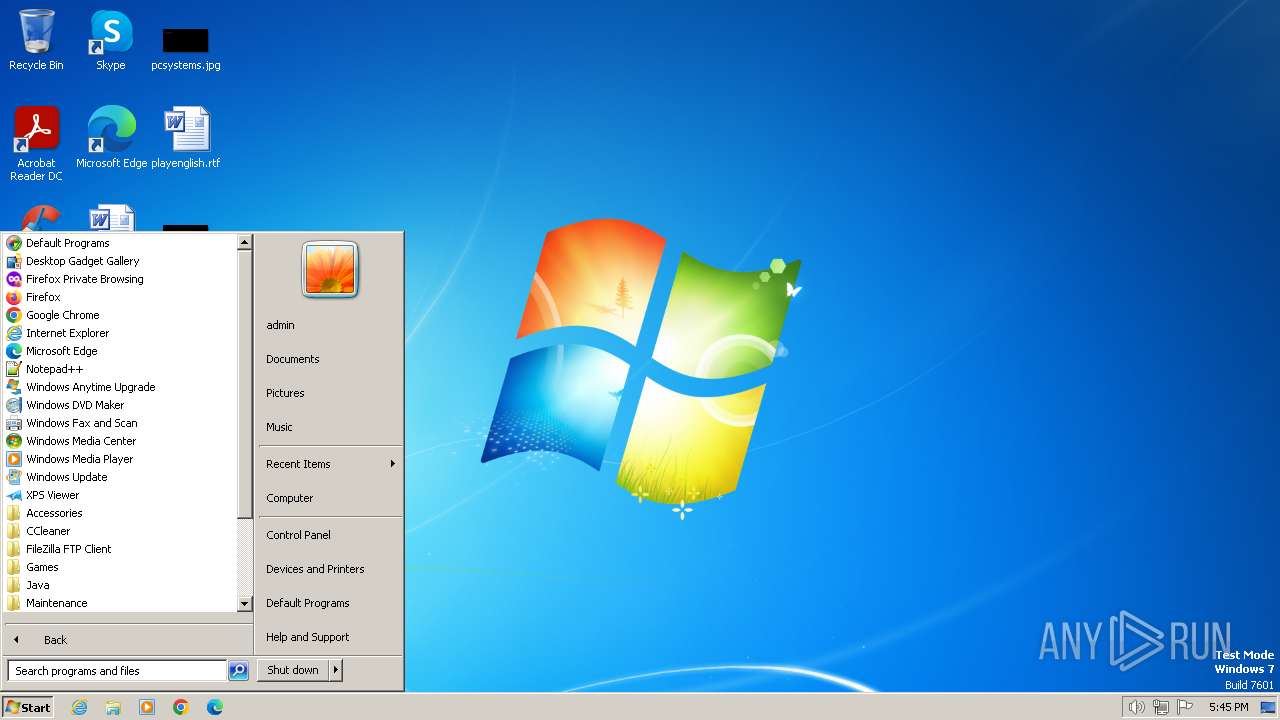
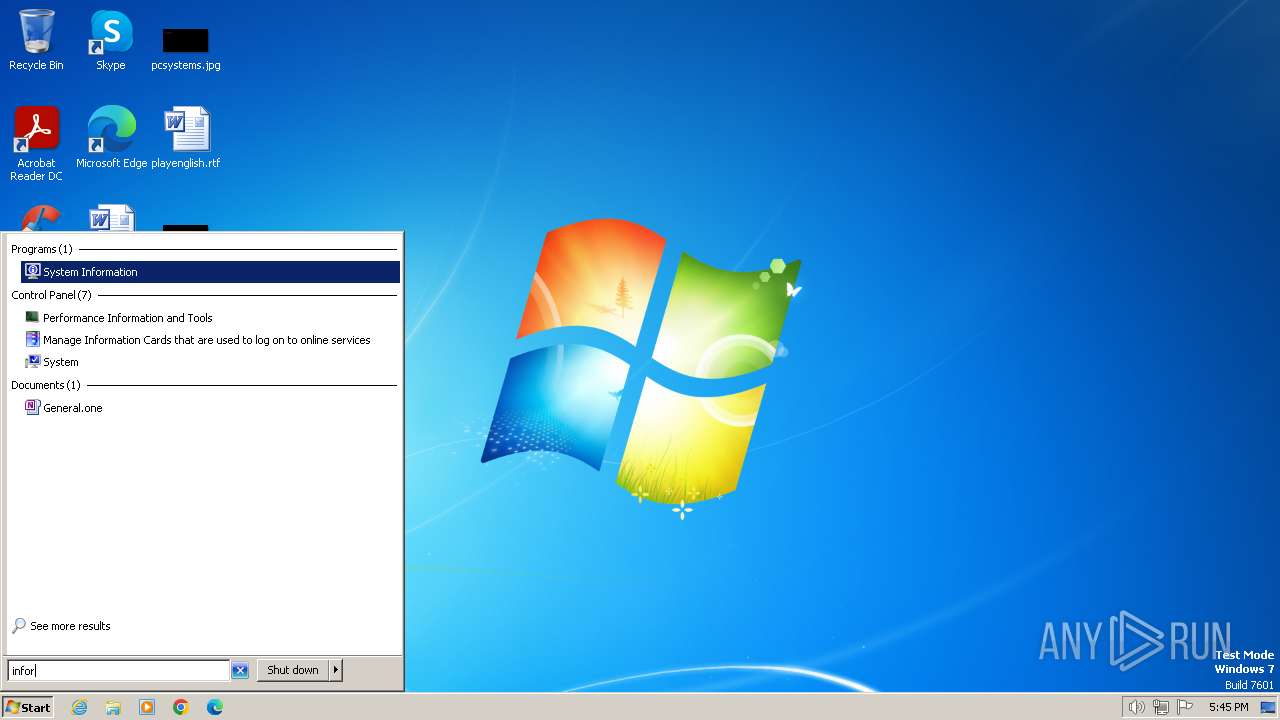
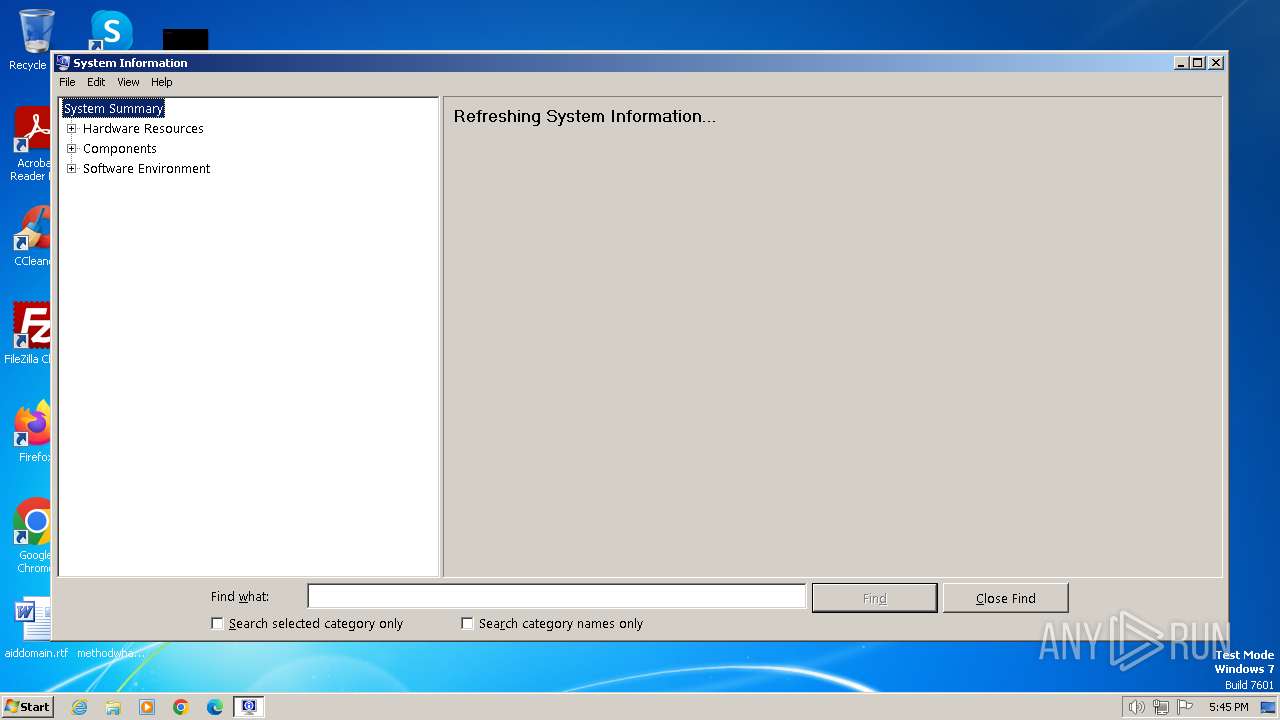
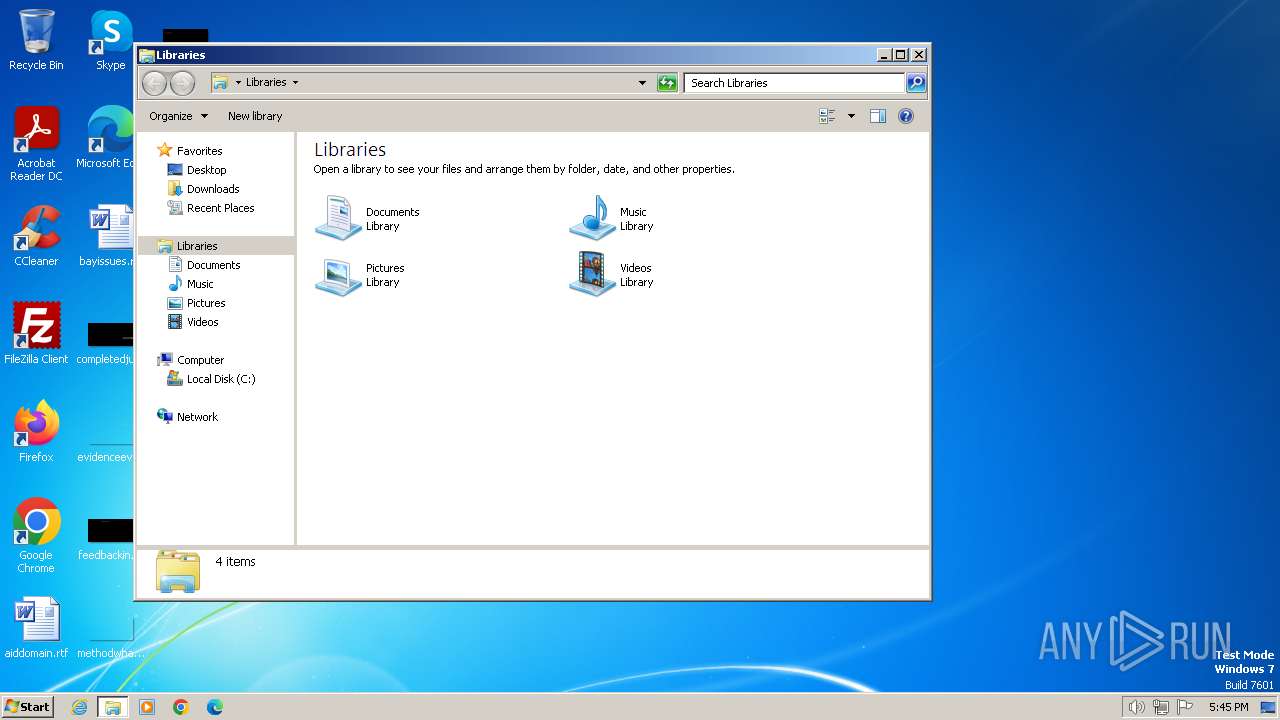
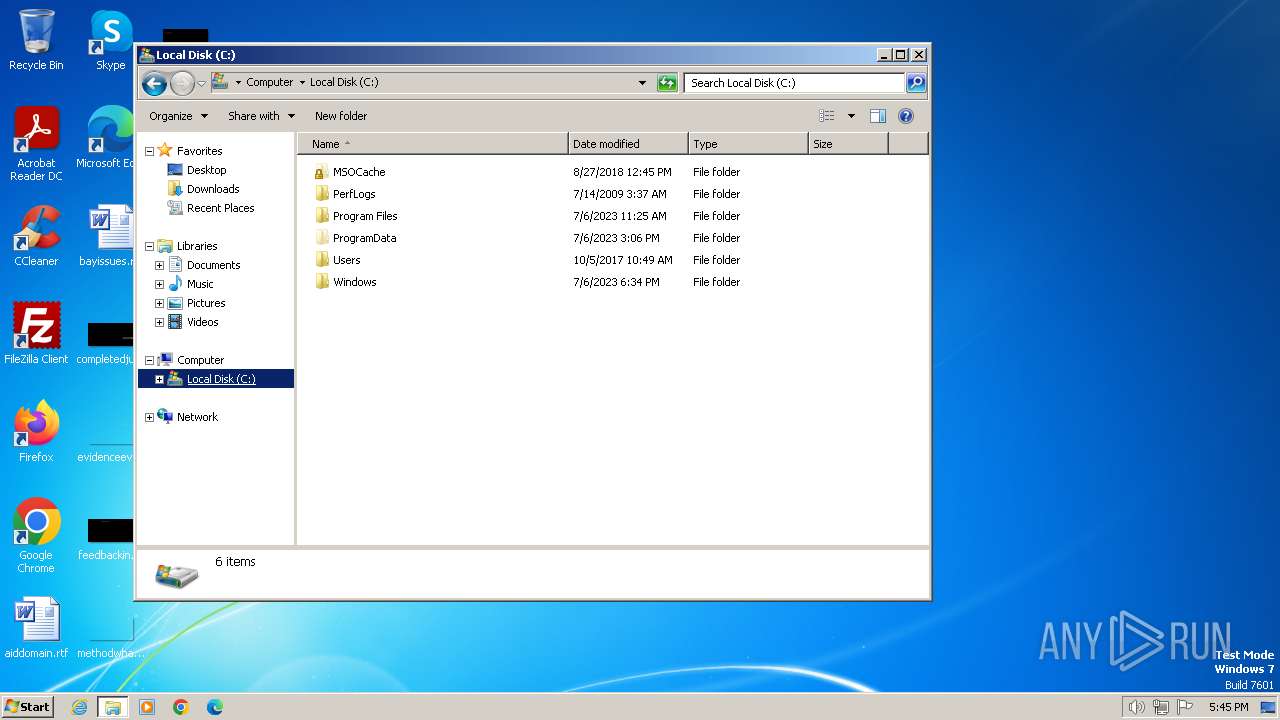
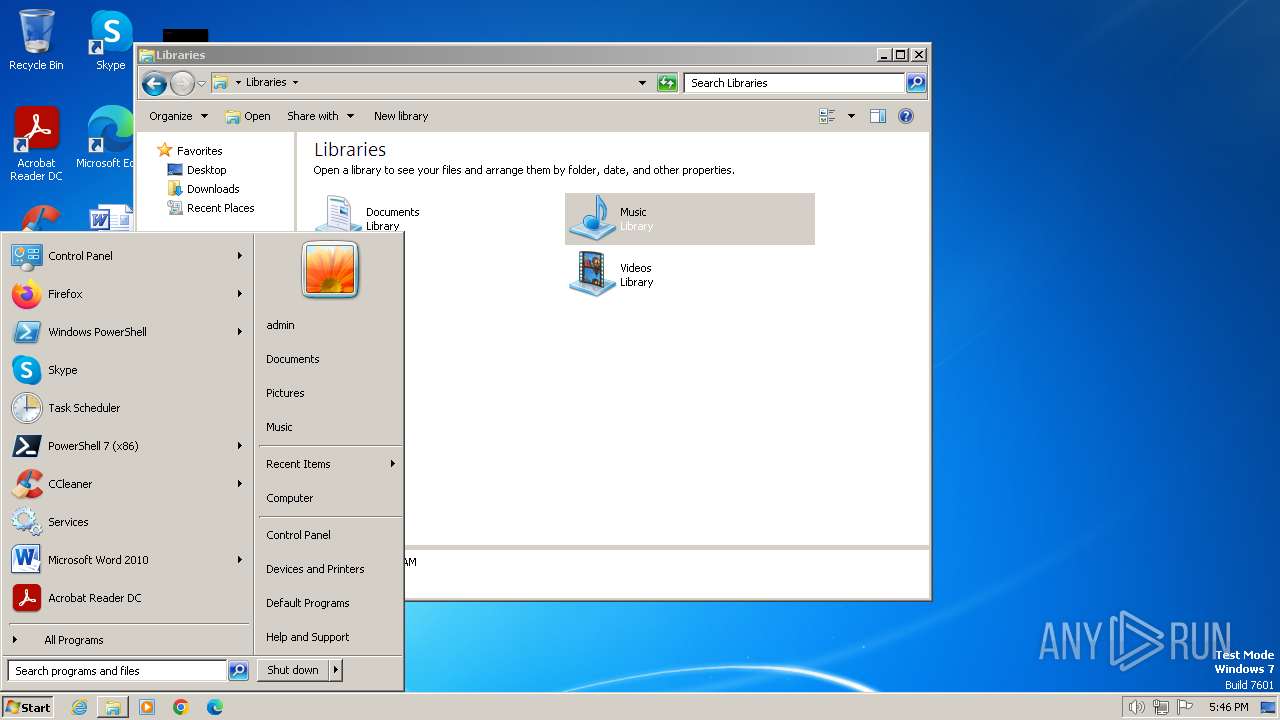
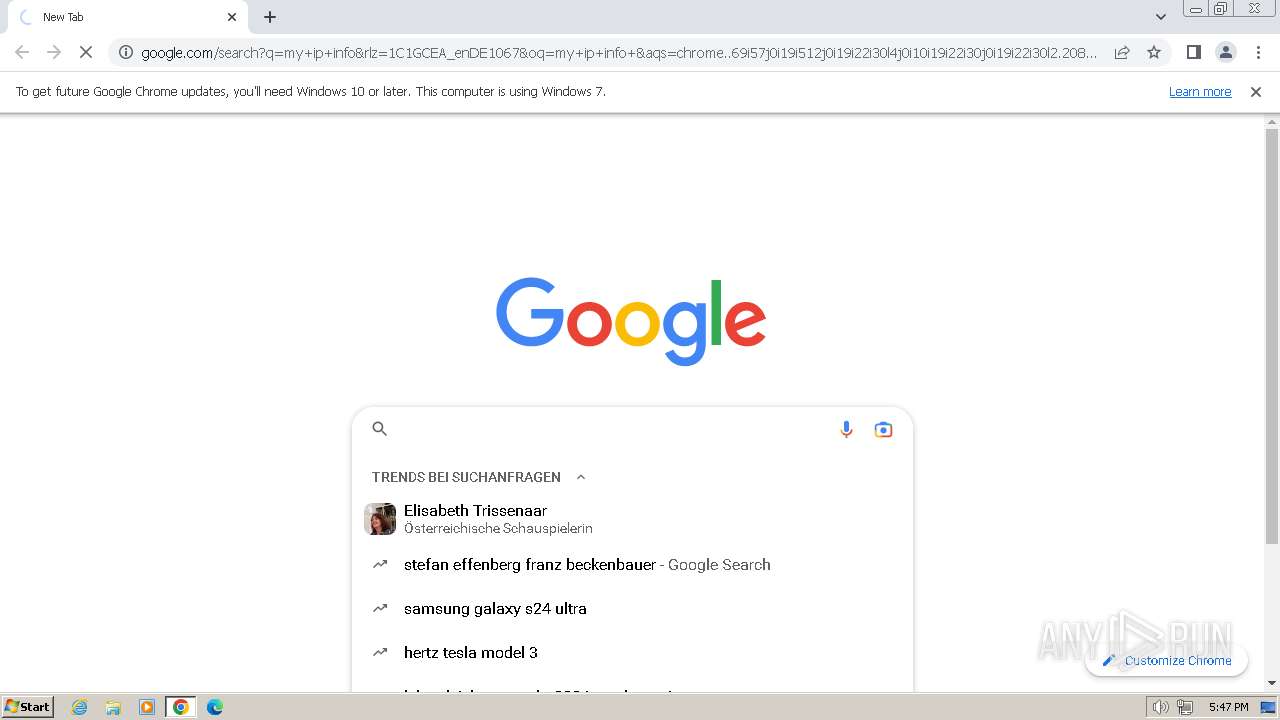
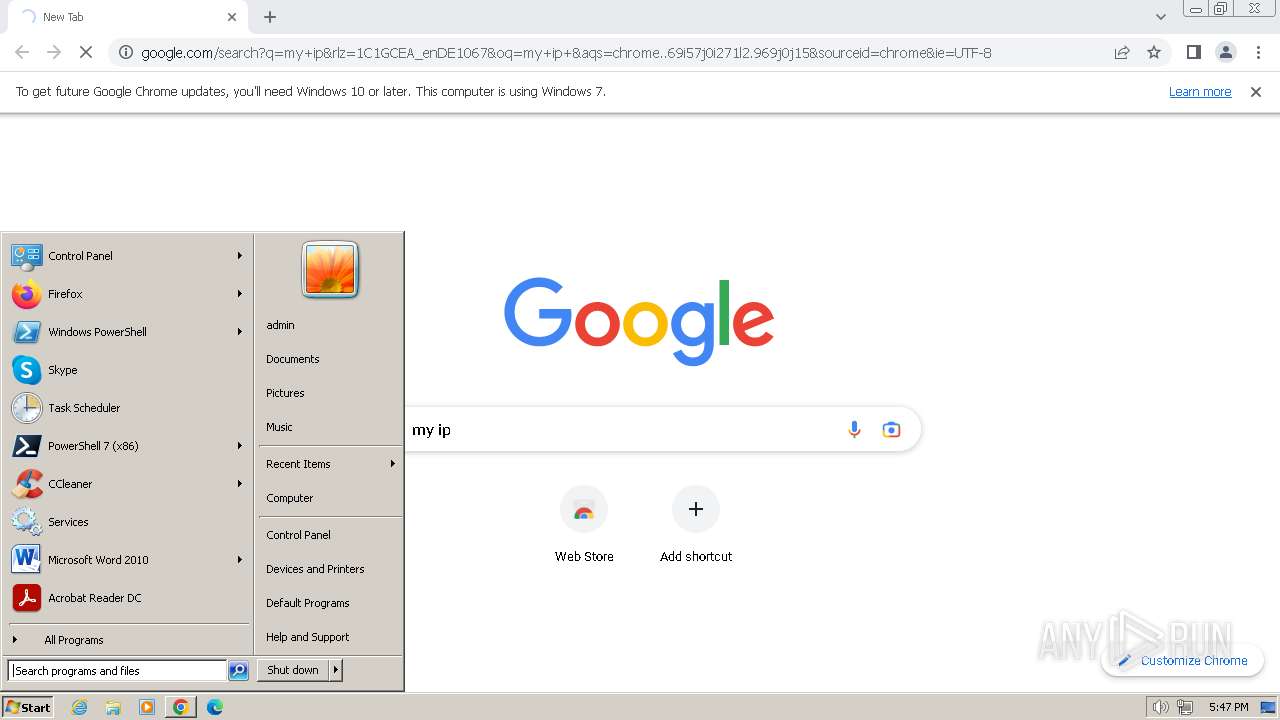
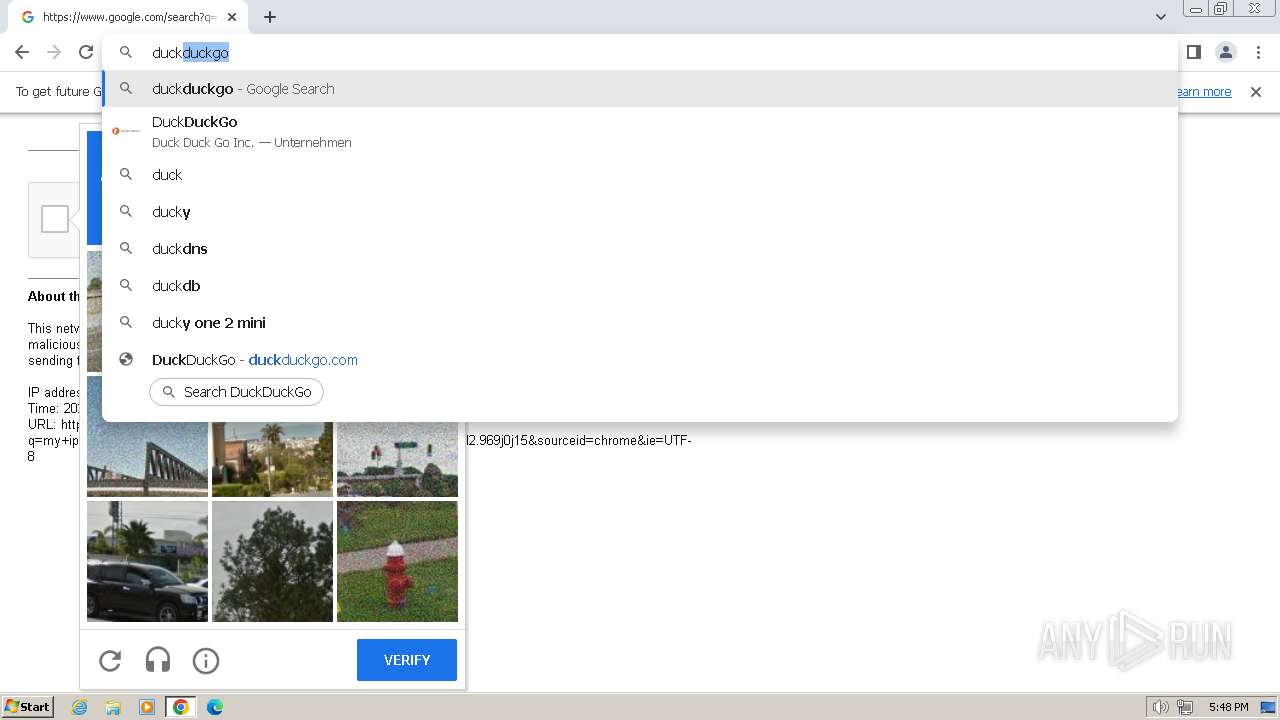
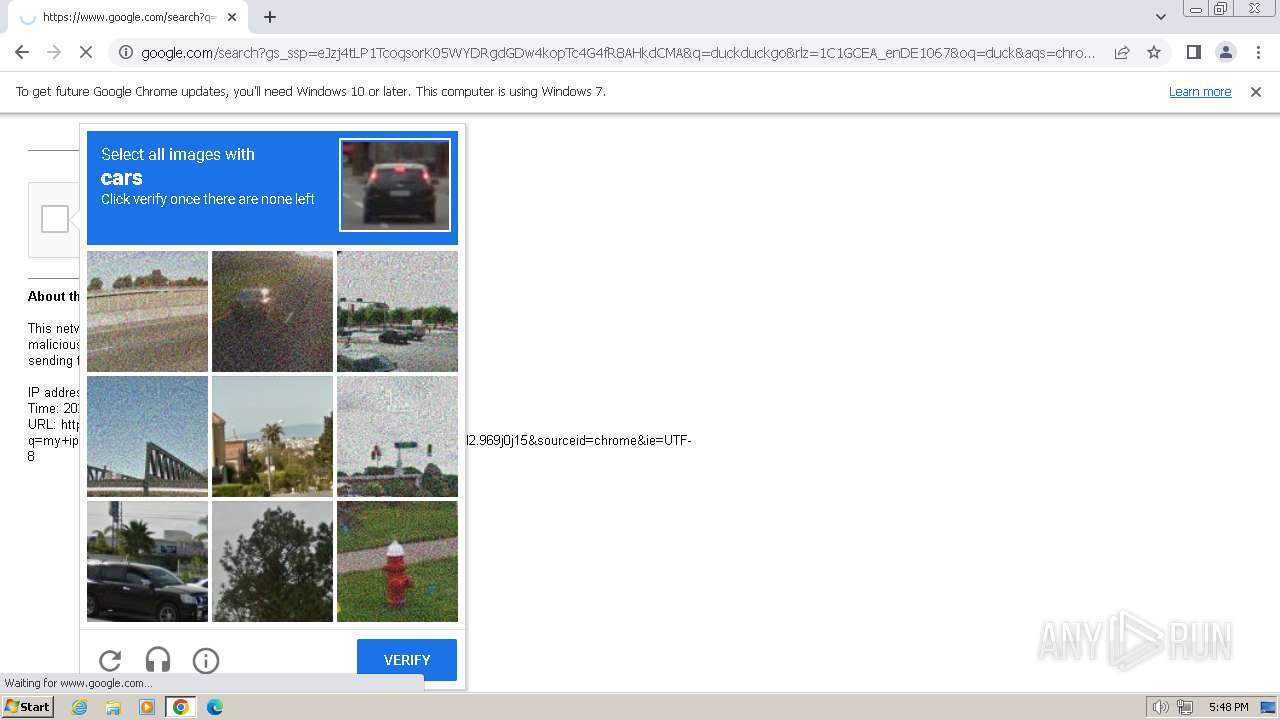
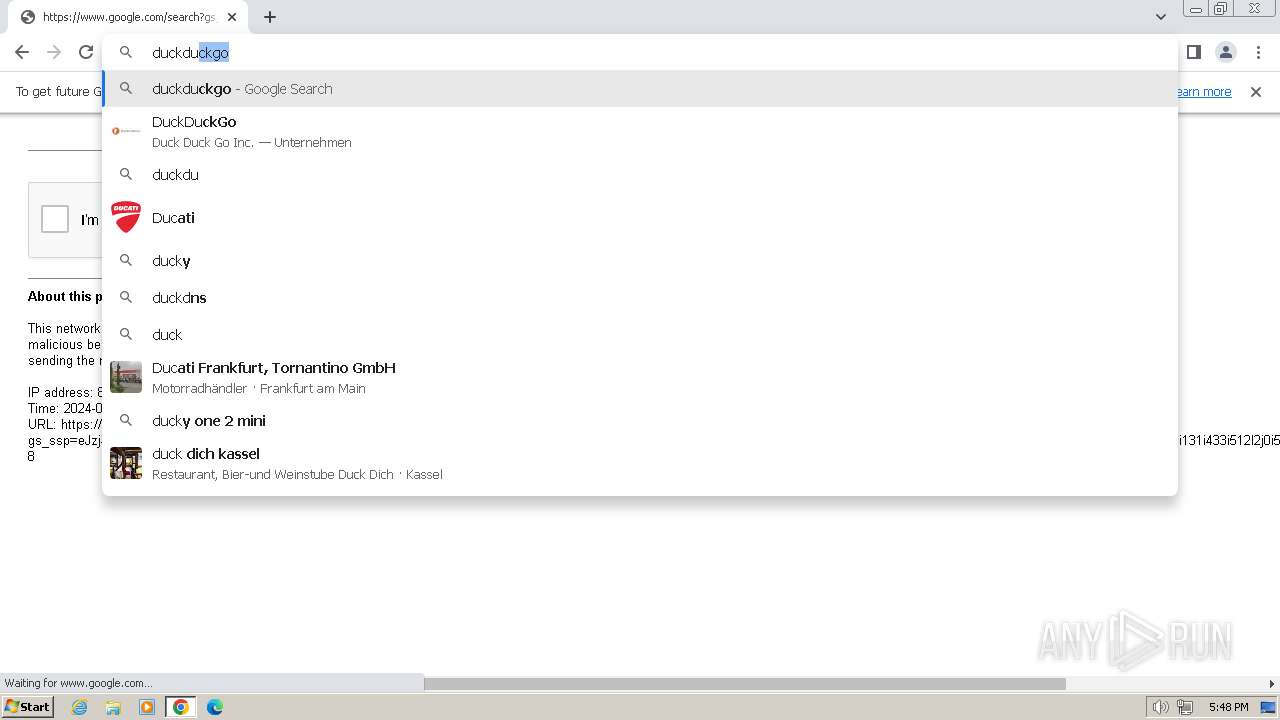
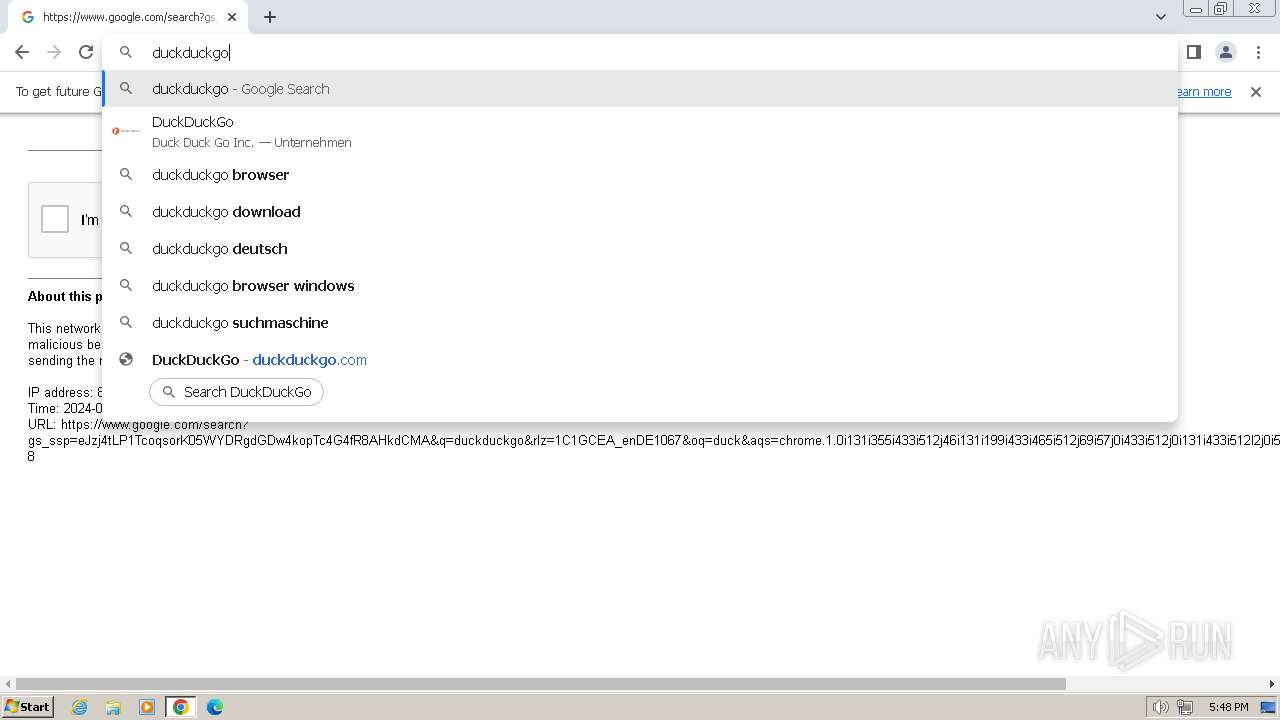
Manual execution by a user
- explorer.exe (PID: 1656)
- msinfo32.exe (PID: 1596)
- runonce.exe (PID: 308)
- IMEKLMG.EXE (PID: 148)
- wmpnscfg.exe (PID: 2408)
- wmpnscfg.exe (PID: 2460)
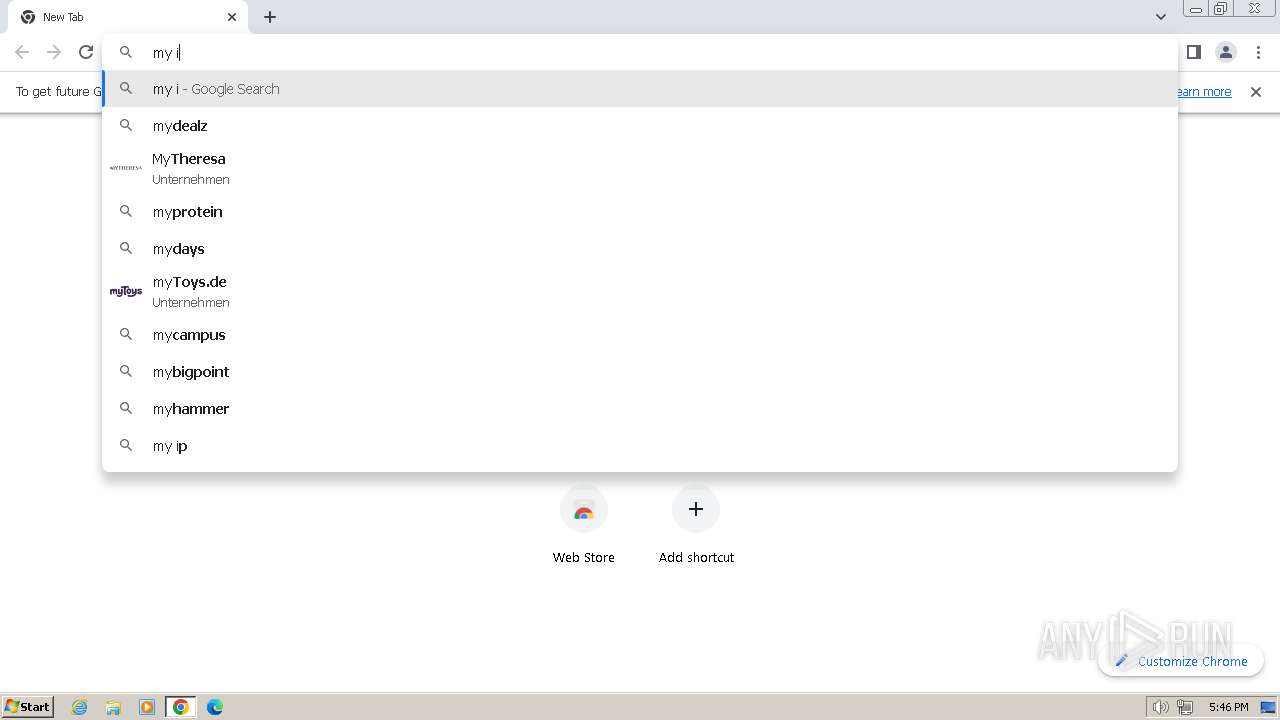
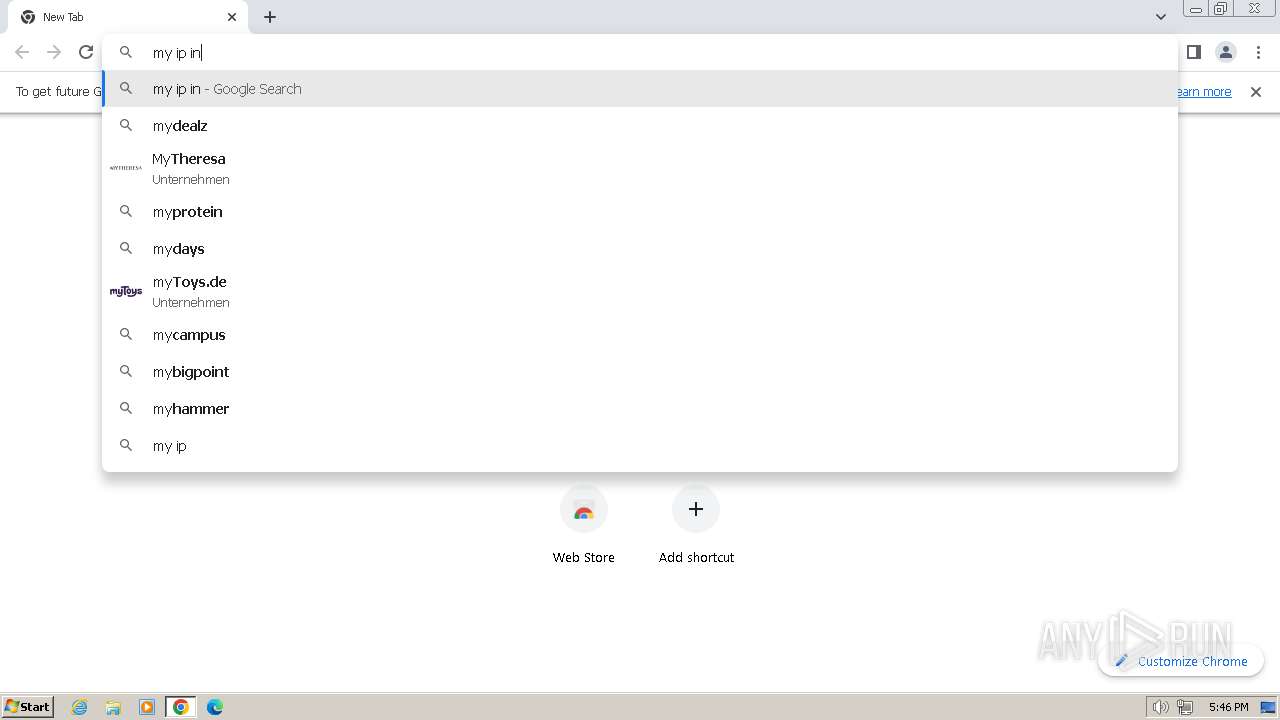
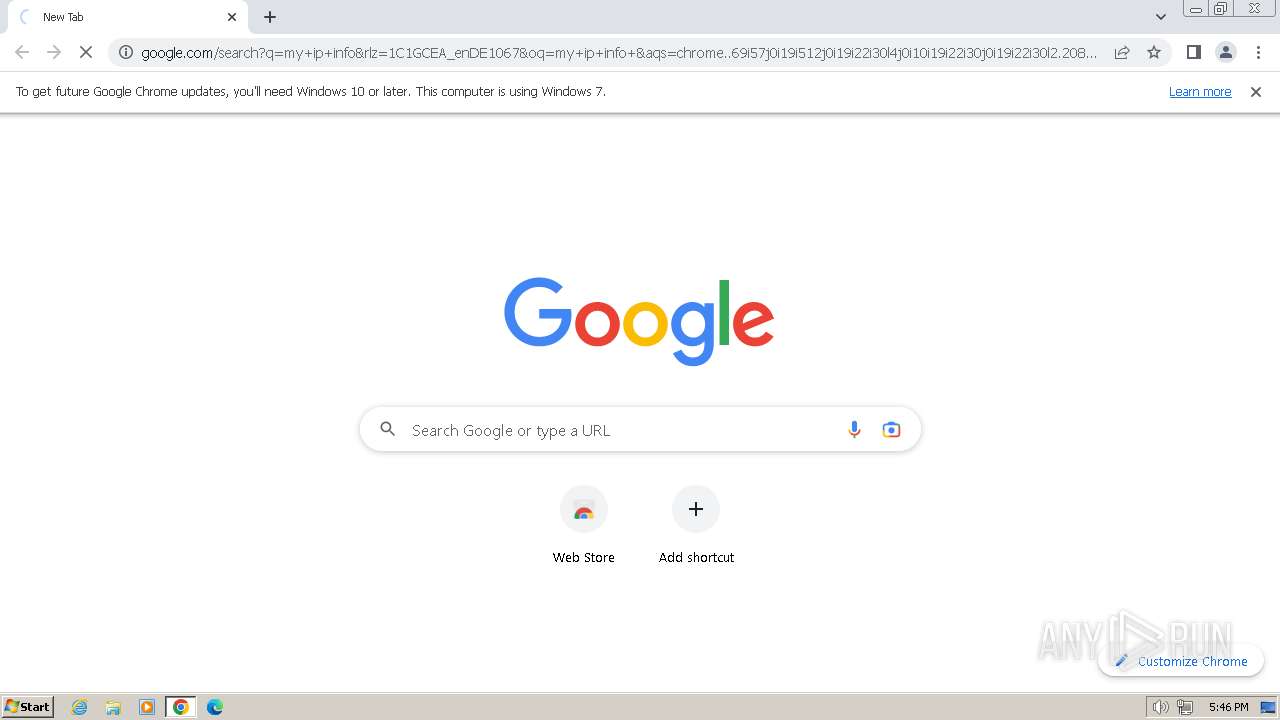
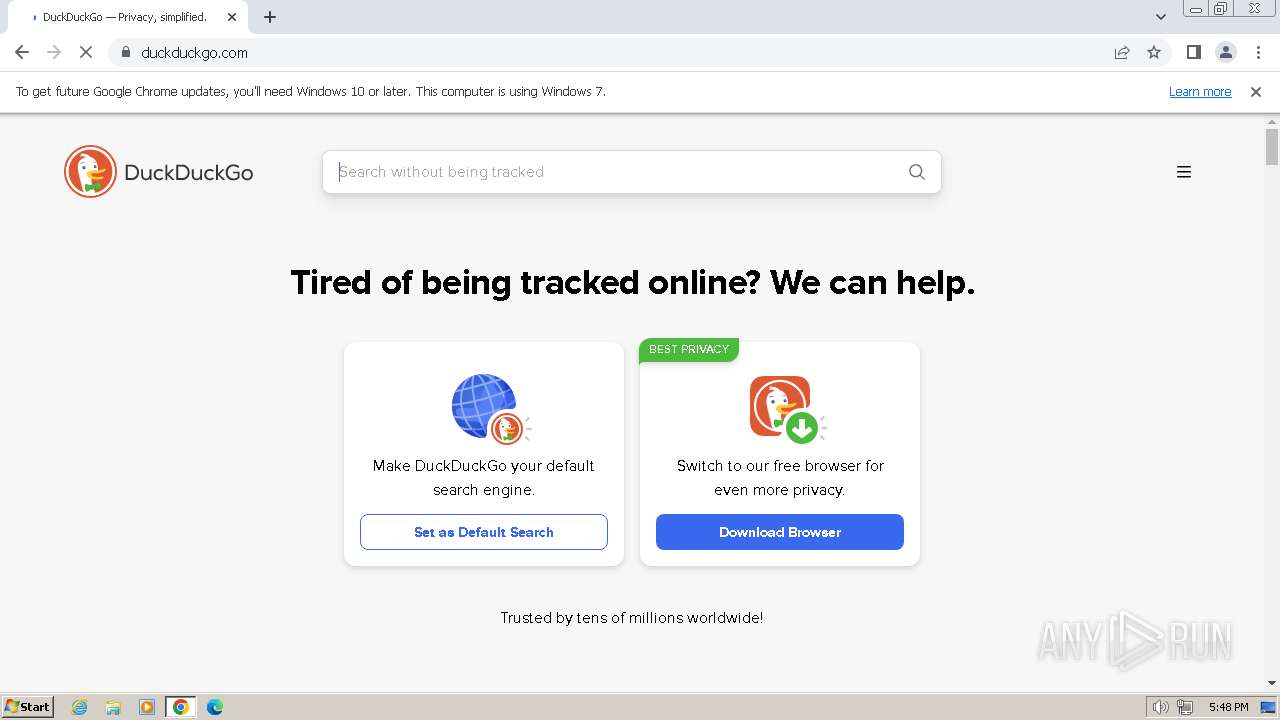
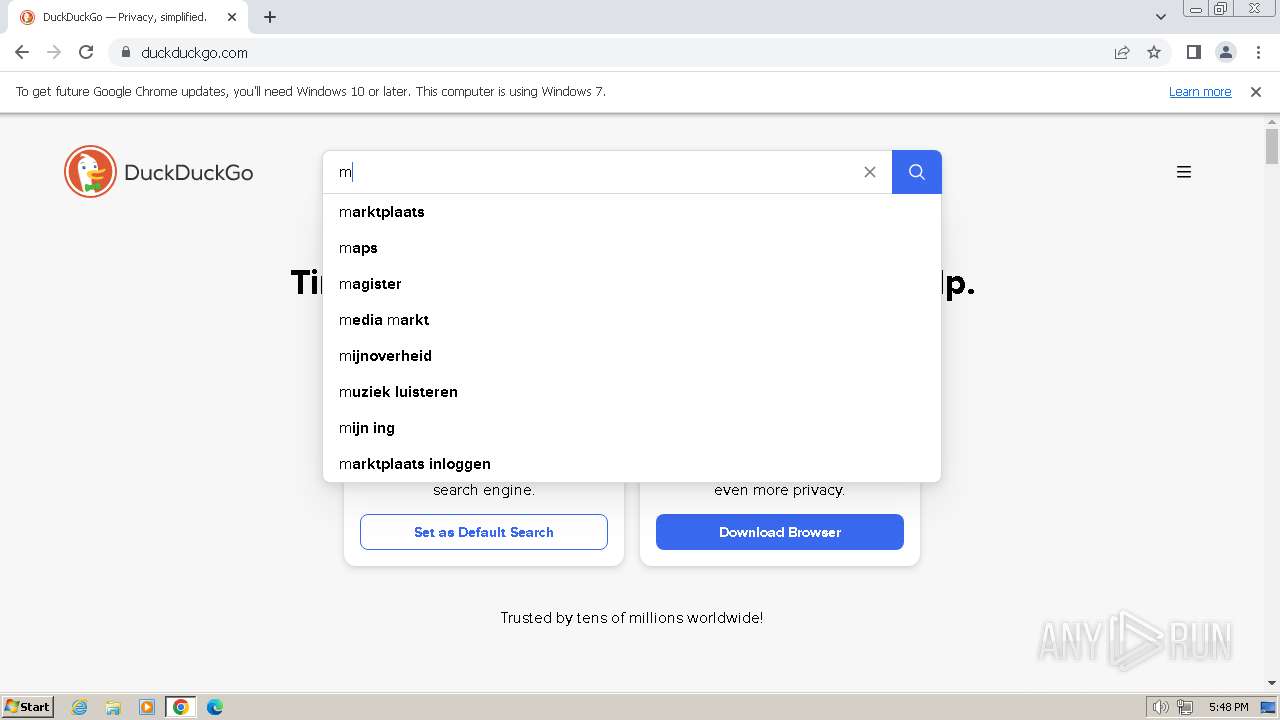
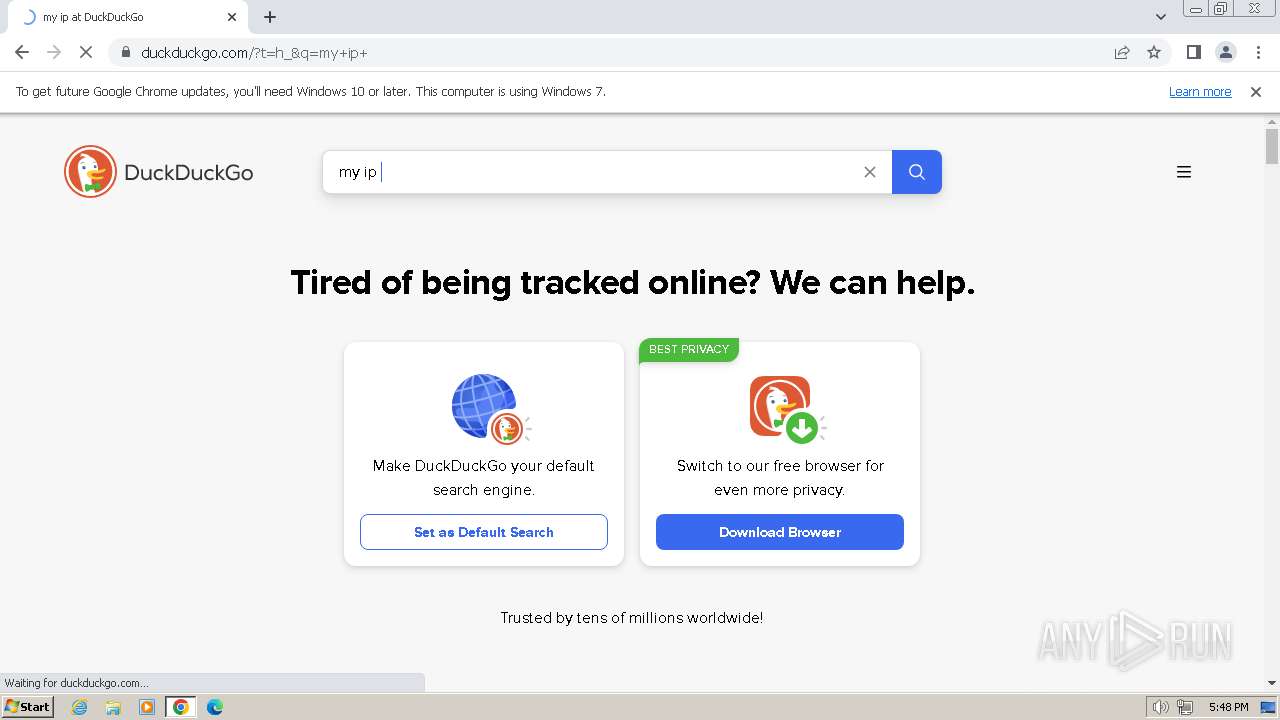
- chrome.exe (PID: 2588)
- IMEKLMG.EXE (PID: 2052)
Reads the machine GUID from the registry
- MEMZ.exe (PID: 296)
Reads the time zone
- runonce.exe (PID: 308)
Create files in a temporary directory
- WerFault.exe (PID: 1704)
Reads the computer name
- IMEKLMG.EXE (PID: 2052)
- IMEKLMG.EXE (PID: 148)
- wmpnscfg.exe (PID: 2408)
- wmpnscfg.exe (PID: 2460)
- MEMZ.exe (PID: 2124)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 148)
- IMEKLMG.EXE (PID: 2052)
Reads security settings of Internet Explorer
- sipnotify.exe (PID: 604)
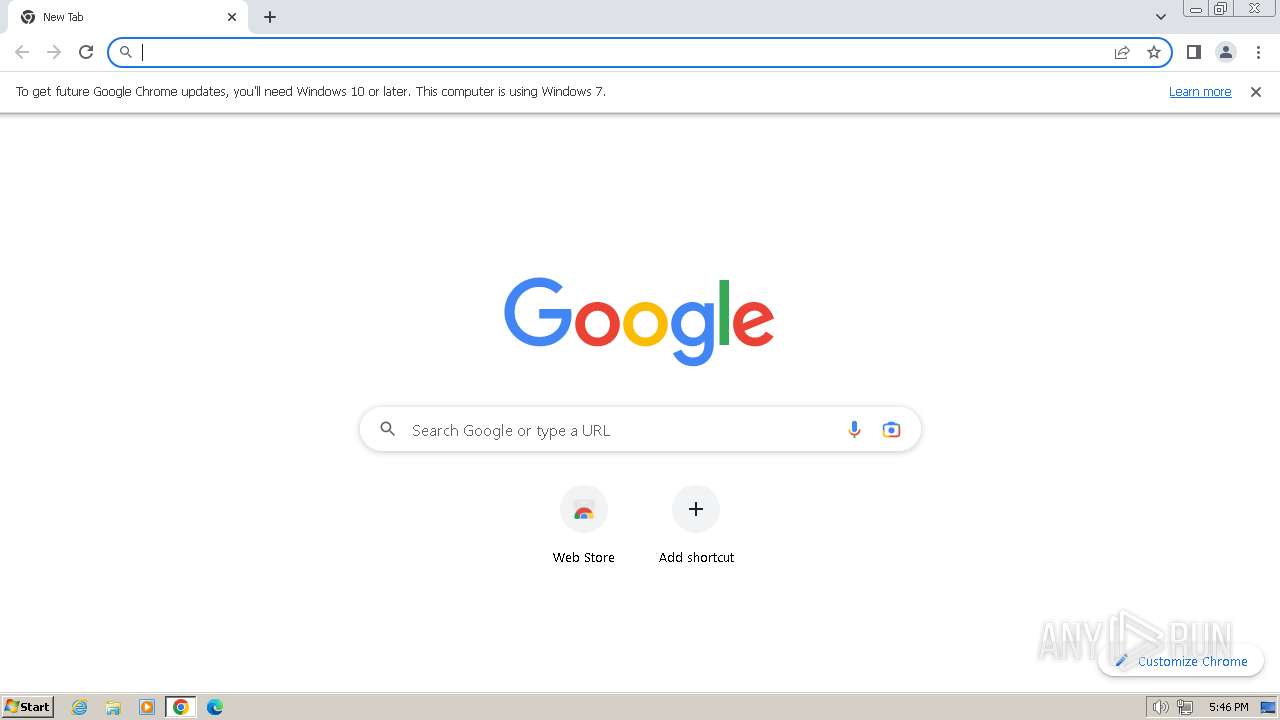
Application launched itself
- chrome.exe (PID: 2588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:03:19 04:33:10+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 3584 |
| InitializedDataSize: | 11776 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x122d |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
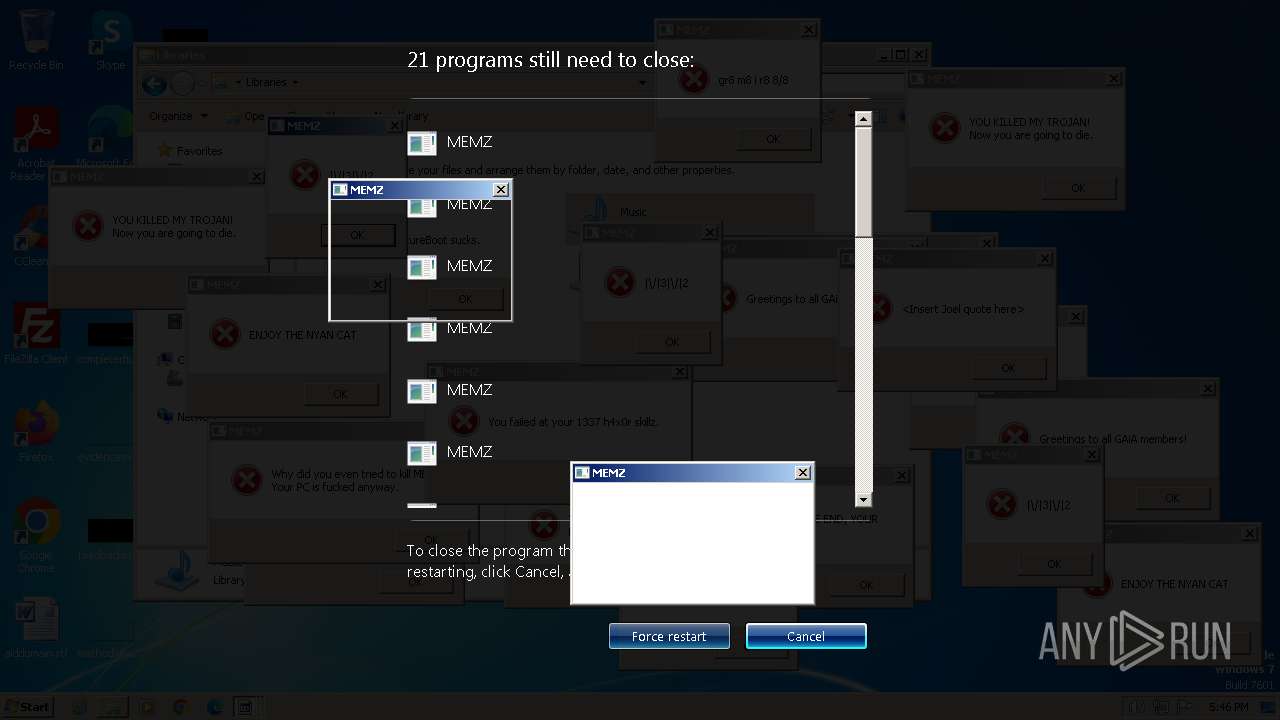
Total processes
126
Monitored processes
43
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Users\admin\AppData\Local\Temp\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 148 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /JPN /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --mojo-platform-channel-handle=4284 --field-trial-handle=1140,i,16634413325886377579,15285355115924396671,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 296 | "C:\Users\admin\AppData\Local\Temp\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 308 | runonce.exe /Explorer | C:\Windows\System32\runonce.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | "C:\Users\admin\AppData\Local\Temp\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --mojo-platform-channel-handle=4276 --field-trial-handle=1140,i,16634413325886377579,15285355115924396671,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 604 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --mojo-platform-channel-handle=4424 --field-trial-handle=1140,i,16634413325886377579,15285355115924396671,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1072 | "C:\Users\admin\AppData\Local\Temp\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Local\Temp\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
7 927
Read events
7 774
Write events
149
Delete events
4
Modification events
| (PID) Process: | (2124) MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2124) MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2124) MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2124) MEMZ.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (308) runonce.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | delete value | Name: | *WerKernelReporting |
Value: %SYSTEMROOT%\SYSTEM32\WerFault.exe -k -rq | |||
| (PID) Process: | (308) runonce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (308) runonce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (308) runonce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (308) runonce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1704) WerFault.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Windows Error Reporting\KernelFaults\Queue |
| Operation: | delete value | Name: | C:\Windows\Minidump\011524-6750-01.dmp |
Value: C24A61C5DA47DA01 | |||
Executable files
5
Suspicious files
196
Text files
50
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1704 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\Kernel_0_0_cab_06a84536\Report.wer | — | |
MD5:— | SHA256:— | |||
| 2588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF782d.TMP | — | |
MD5:— | SHA256:— | |||
| 2588 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 308 | runonce.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Explorer\ExplorerStartupLog_RunOnce.etl | binary | |
MD5:90B74629685E7218CF5693611BC7B19A | SHA256:187B8C2BAB4C47B83313136D72A669F8DD0C7128225ABB0326BA5E88BB5D2ED6 | |||
| 604 | sipnotify.exe | C:\Users\admin\AppData\Local\microsoft\windows\SipNotify\eoscontent\en-us.html | html | |
MD5:9752942B57692148B9F614CF4C119A36 | SHA256:E31B834DD53FA6815F396FC09C726636ABF98F3367F0CF1590EF5EB3801C75D1 | |||
| 604 | sipnotify.exe | C:\Users\admin\AppData\Local\microsoft\windows\SipNotify\eoscontent\metadata.json | binary | |
MD5:E8A970BA6CE386EED9A5E724F26212A6 | SHA256:7E06107D585D8FC7870998F3856DCC3E35800AA97E4406AAB83BC8444B6CBDE3 | |||
| 604 | sipnotify.exe | C:\Users\admin\AppData\Local\microsoft\windows\SipNotify\eoscontent\main.jpg | image | |
MD5:B342ACE63F77961249A084C61EABC884 | SHA256:E5067BBA2095B5DA7C3171EC116E9A92337E24E471339B0860A160076EFE49B9 | |||
| 1704 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER449B.tmp.cab.tmp | binary | |
MD5:B5CAB680118B268E2F65D2F2621C02E9 | SHA256:D1E2B80195B177DDFEBE69F0D2AA38CFA95C47A2B4D309440D0A7BFA7E24F1E5 | |||
| 1704 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER449F.tmp.cab.tmp | binary | |
MD5:8BA028678E2B812B0A124ADC1BAB3ECE | SHA256:9C43C0DF390C39D64F1E5E8E9E032029A634F0B5CE12B24DE2D20A38BF8A0CEC | |||
| 604 | sipnotify.exe | C:\Users\admin\AppData\Local\microsoft\windows\SipNotify\eoscontent\microsoft-logo.png | image | |
MD5:B7C73A0CFBA68CC70C35EF9C63703CE4 | SHA256:1D8B27A0266FF526CF95447F3701592A908848467D37C09A00A2516C1F29A013 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
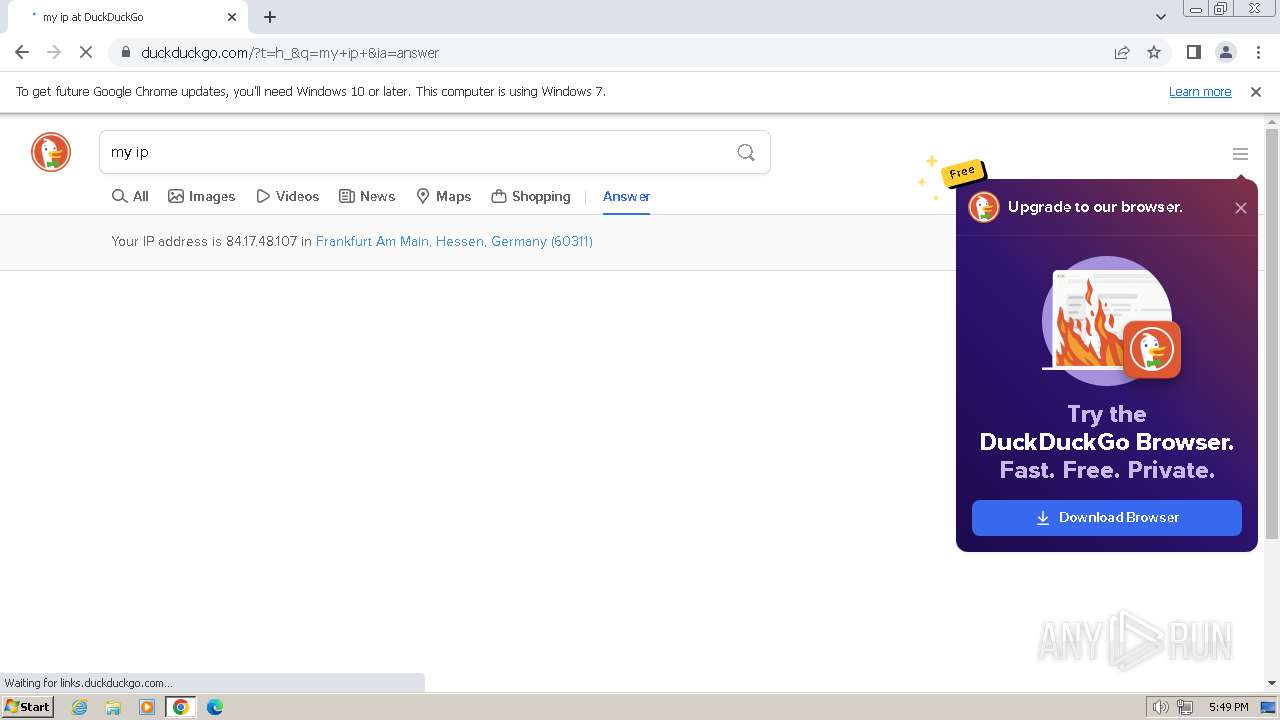
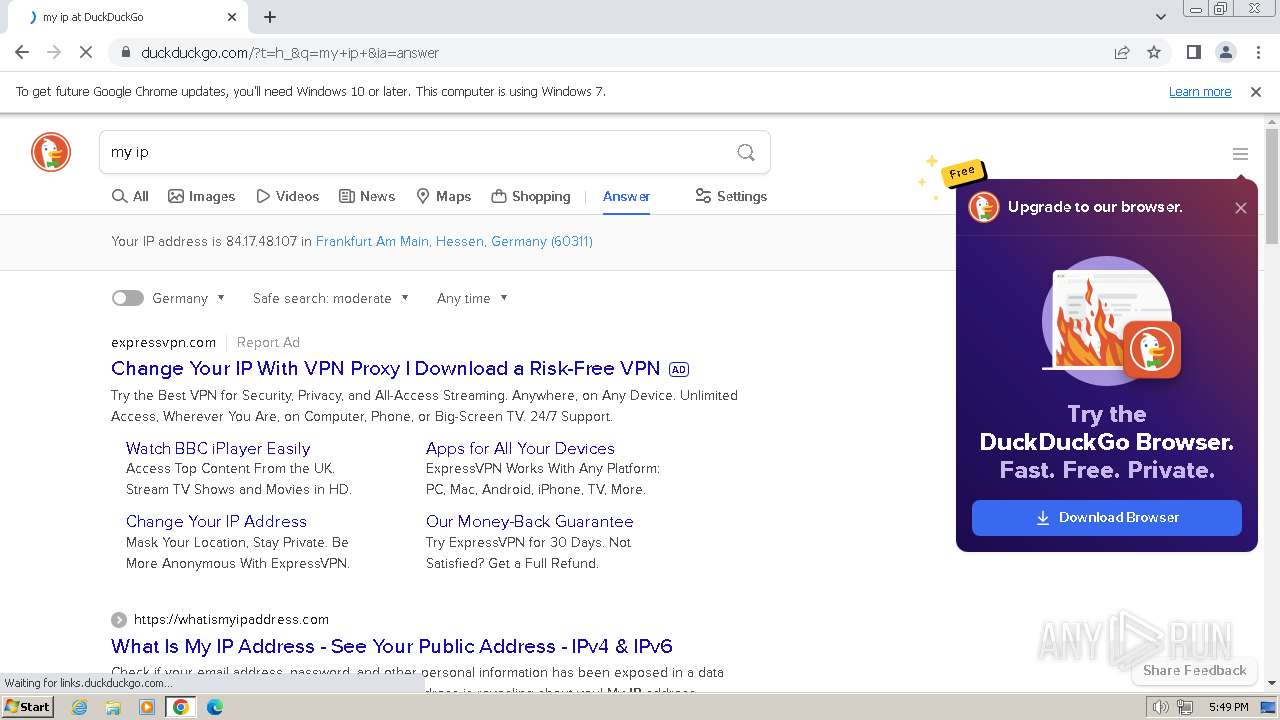
HTTP(S) requests
6
TCP/UDP connections
128
DNS requests
164
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
604 | sipnotify.exe | HEAD | 200 | 23.197.138.118:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133498143906400000 | unknown | — | — | unknown |
2756 | chrome.exe | GET | 204 | 142.250.186.35:80 | http://www.gstatic.com/generate_204 | unknown | — | — | unknown |
880 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/py5dqeczg3bmfxj4vm3bvsxb6y_3013/jflookgnkcckhobaglndicnbbgbonegd_3013_all_adgpehxzxriaky3auope65o5vw7q.crx3 | unknown | — | — | unknown |
880 | svchost.exe | GET | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/py5dqeczg3bmfxj4vm3bvsxb6y_3013/jflookgnkcckhobaglndicnbbgbonegd_3013_all_adgpehxzxriaky3auope65o5vw7q.crx3 | unknown | — | — | unknown |
880 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/py5dqeczg3bmfxj4vm3bvsxb6y_3013/jflookgnkcckhobaglndicnbbgbonegd_3013_all_adgpehxzxriaky3auope65o5vw7q.crx3 | unknown | binary | 10.3 Kb | unknown |
880 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/py5dqeczg3bmfxj4vm3bvsxb6y_3013/jflookgnkcckhobaglndicnbbgbonegd_3013_all_adgpehxzxriaky3auope65o5vw7q.crx3 | unknown | binary | 5.63 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1120 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
604 | sipnotify.exe | 23.197.138.118:80 | query.prod.cms.rt.microsoft.com | Akamai International B.V. | US | unknown |
2588 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2756 | chrome.exe | 142.250.185.67:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2756 | chrome.exe | 142.251.31.84:443 | accounts.google.com | GOOGLE | US | unknown |
2756 | chrome.exe | 142.250.186.132:443 | www.google.com | GOOGLE | US | whitelisted |
2756 | chrome.exe | 216.58.206.35:443 | update.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
query.prod.cms.rt.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
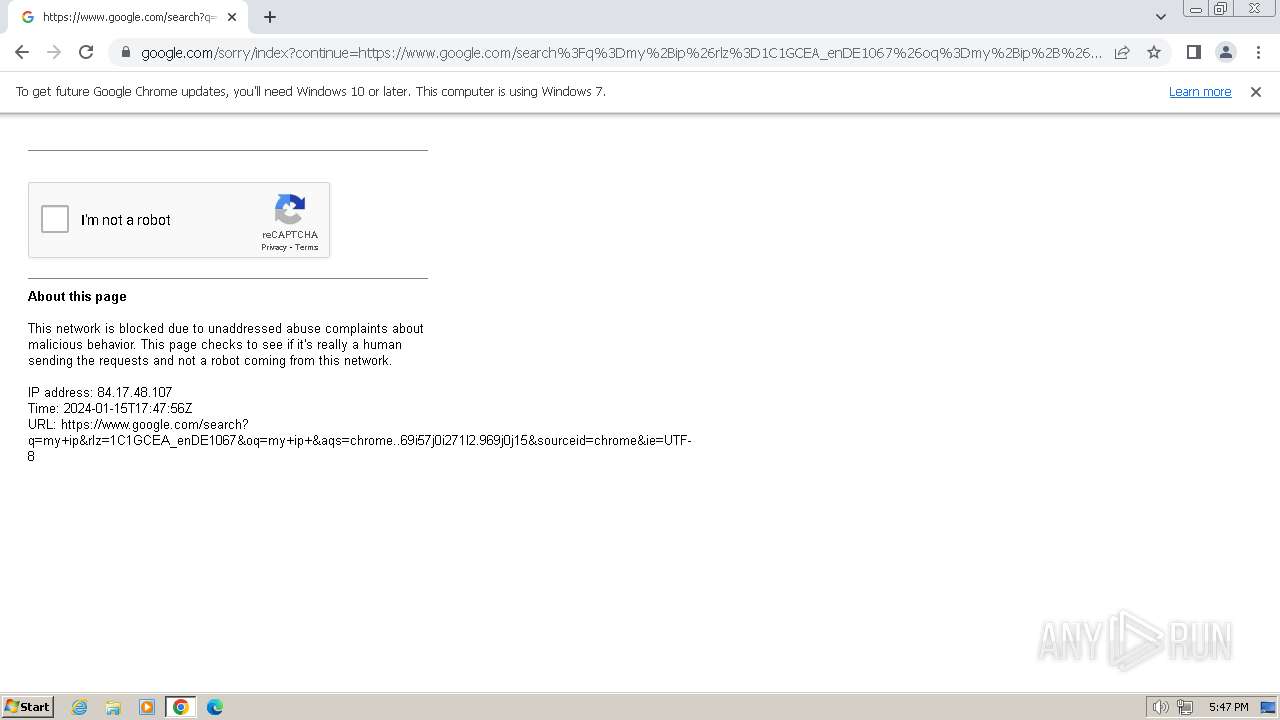
www.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |