| File name: | Photos.exe |
| Full analysis: | https://app.any.run/tasks/b2a308fb-66ac-49f2-ba98-42d1b88abec4 |
| Verdict: | Malicious activity |
| Analysis date: | December 10, 2024, 13:51:47 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 754545AFCA5D10149F1138221317DA2D |
| SHA1: | A59B67F5D3017230B3E71ED8DD0D12EBB117B1A4 |
| SHA256: | 38633E676FECE37028170D8736E1BC616784ECD7FCF5D503B65030688C8E4A97 |
| SSDEEP: | 24576:kUdUUUUUUHdWUUUUUU0E+WU3TAKygSXaGTwVLxDqs+Oj0J5tMHW9XQBOQrQZG4ZV:kSQ+WU3TAKygSXaGTiLxDqs+Oj0J5tMI |
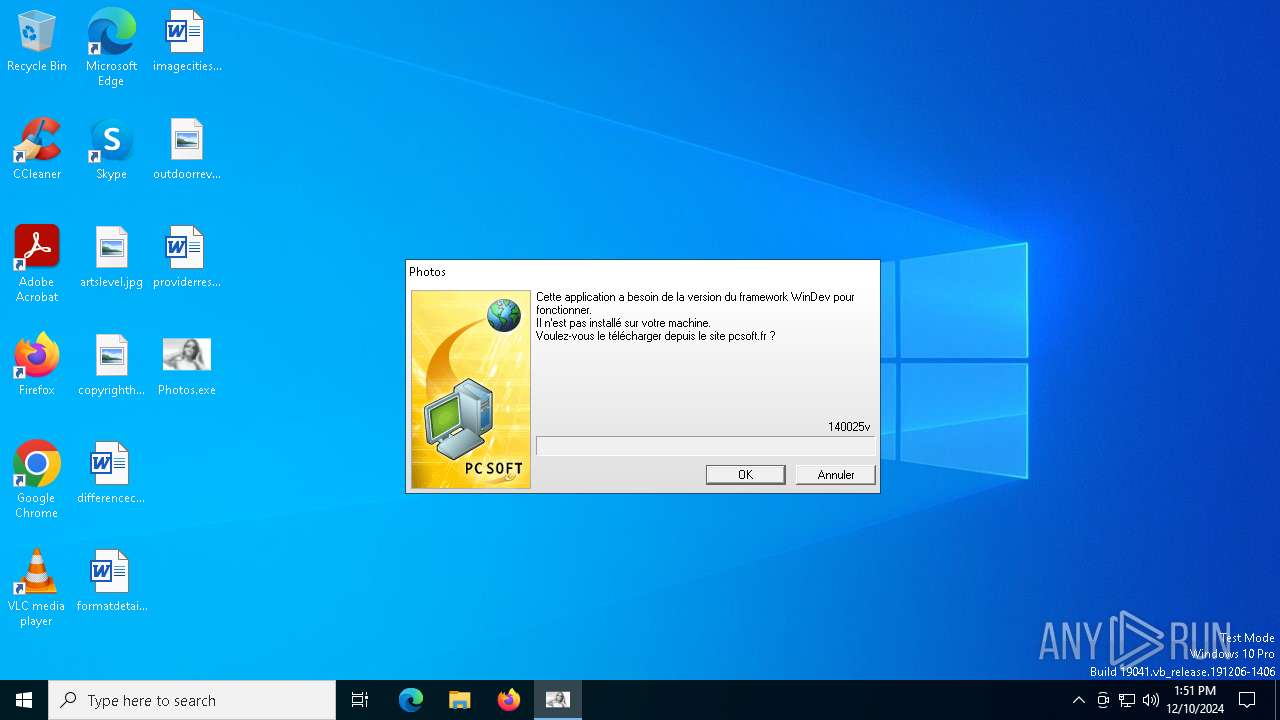
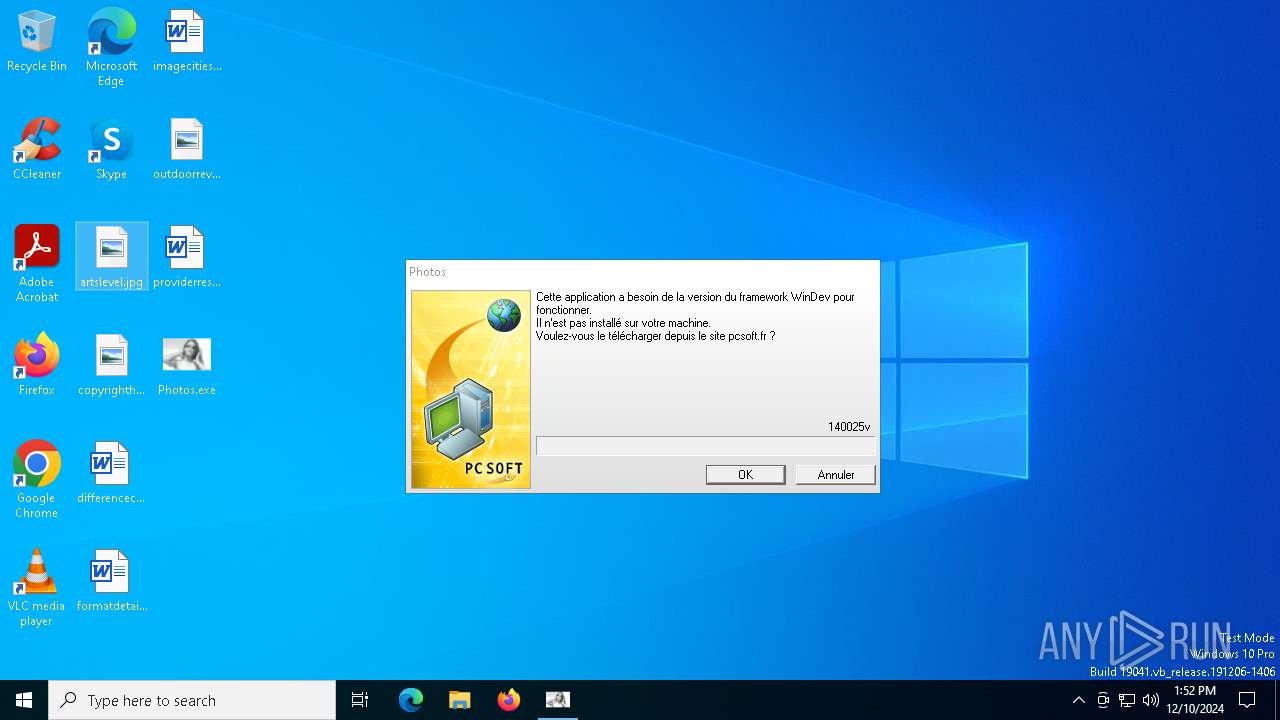
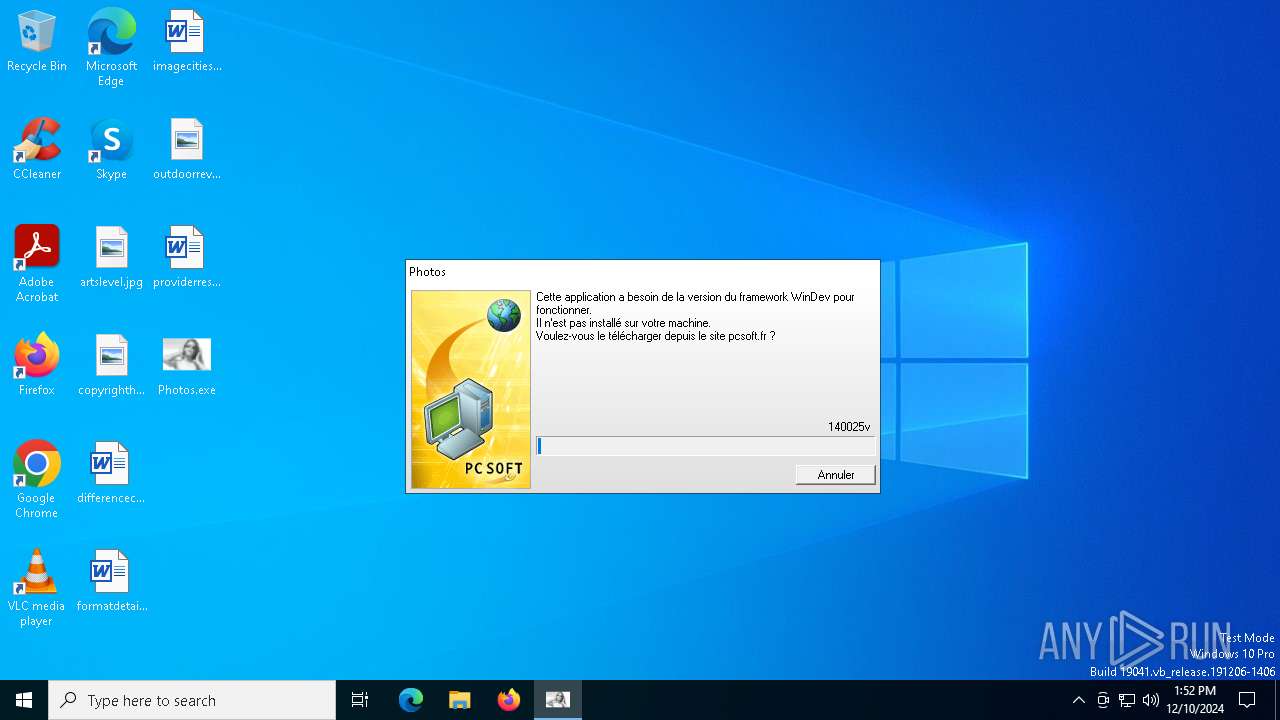
MALICIOUS
Executing a file with an untrusted certificate
- InstallFramework.exe (PID: 4652)
- InstallFramework.exe (PID: 6664)
Changes the autorun value in the registry
- Photos.exe (PID: 6616)
SUSPICIOUS
There is functionality for communication over UDP network (YARA)
- Photos.exe (PID: 6616)
- rundll32.exe (PID: 1468)
Reads security settings of Internet Explorer
- Photos.exe (PID: 6616)
- rundll32.exe (PID: 1468)
Connects to FTP
- Photos.exe (PID: 6616)
Connects to unusual port
- Photos.exe (PID: 6616)
- rundll32.exe (PID: 1468)
Executable content was dropped or overwritten
- Photos.exe (PID: 6616)
- InstallFramework.exe (PID: 6664)
Starts itself from another location
- Photos.exe (PID: 6616)
There is functionality for taking screenshot (YARA)
- rundll32.exe (PID: 1468)
There is functionality for sending ICMP (YARA)
- rundll32.exe (PID: 1468)
INFO
Reads the computer name
- Photos.exe (PID: 6616)
- rundll32.exe (PID: 1468)
Checks supported languages
- Photos.exe (PID: 6616)
- InstallFramework.exe (PID: 6664)
- rundll32.exe (PID: 1468)
Create files in a temporary directory
- Photos.exe (PID: 6616)
Creates files or folders in the user directory
- Photos.exe (PID: 6616)
Checks proxy server information
- Photos.exe (PID: 6616)
- rundll32.exe (PID: 1468)
The process uses the downloaded file
- Photos.exe (PID: 6616)
Process checks computer location settings
- Photos.exe (PID: 6616)
Creates files in the program directory
- Photos.exe (PID: 6616)
Reads the machine GUID from the registry
- rundll32.exe (PID: 1468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (46.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (41) |
| .exe | | | Win32 Executable (generic) (6.6) |
| .exe | | | Generic Win/DOS Executable (2.9) |
| .exe | | | DOS Executable Generic (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2008:12:15 17:42:27+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 7.1 |
| CodeSize: | 65536 |
| InitializedDataSize: | 110592 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xf9ce |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | French |
| CharacterSet: | Unicode |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.00Bx |
| Version: | 1.00Bx |
| LegalCopyright: | - |
| WDVersion: | 14 |
Total processes
139
Monitored processes
6
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1468 | "C:\ProgramData\Microsoft Tools\rundll32.exe" | C:\ProgramData\Microsoft Tools\rundll32.exe | Photos.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 1.00Bx Modules
| |||||||||||||||
| 3928 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 Modules
| |||||||||||||||
| 4652 | "C:\Users\admin\AppData\Local\Temp\InstallFramework.exe" /REP="C:\Users\admin\Desktop\" /SILENT | C:\Users\admin\AppData\Local\Temp\InstallFramework.exe | — | Photos.exe | |||||||||||
User: admin Company: PC SOFT Integrity Level: MEDIUM Description: PC SOFT - Executable auto-extractible Exit code: 3221226540 Version: 14.00Aa Modules
| |||||||||||||||
| 6616 | "C:\Users\admin\Desktop\Photos.exe" | C:\Users\admin\Desktop\Photos.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Version: 1.00Bx Modules
| |||||||||||||||
| 6664 | "C:\Users\admin\AppData\Local\Temp\InstallFramework.exe" /REP="C:\Users\admin\Desktop\" /SILENT | C:\Users\admin\AppData\Local\Temp\InstallFramework.exe | Photos.exe | ||||||||||||
User: admin Company: PC SOFT Integrity Level: HIGH Description: PC SOFT - Executable auto-extractible Exit code: 0 Version: 14.00Aa Modules
| |||||||||||||||
| 6684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UCPDMgr.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 213
Read events
1 208
Write events
5
Delete events
0
Modification events
| (PID) Process: | (6616) Photos.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\PC SOFT\WinDev\14.0\APPLI\Photos |
| Operation: | write | Name: | LAST_FRAMEWORK |
Value: 140025v | |||
| (PID) Process: | (6616) Photos.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6616) Photos.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6616) Photos.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6616) Photos.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Poisson18 |
Value: C:\ProgramData\Microsoft Tools\rundll32.exe | |||
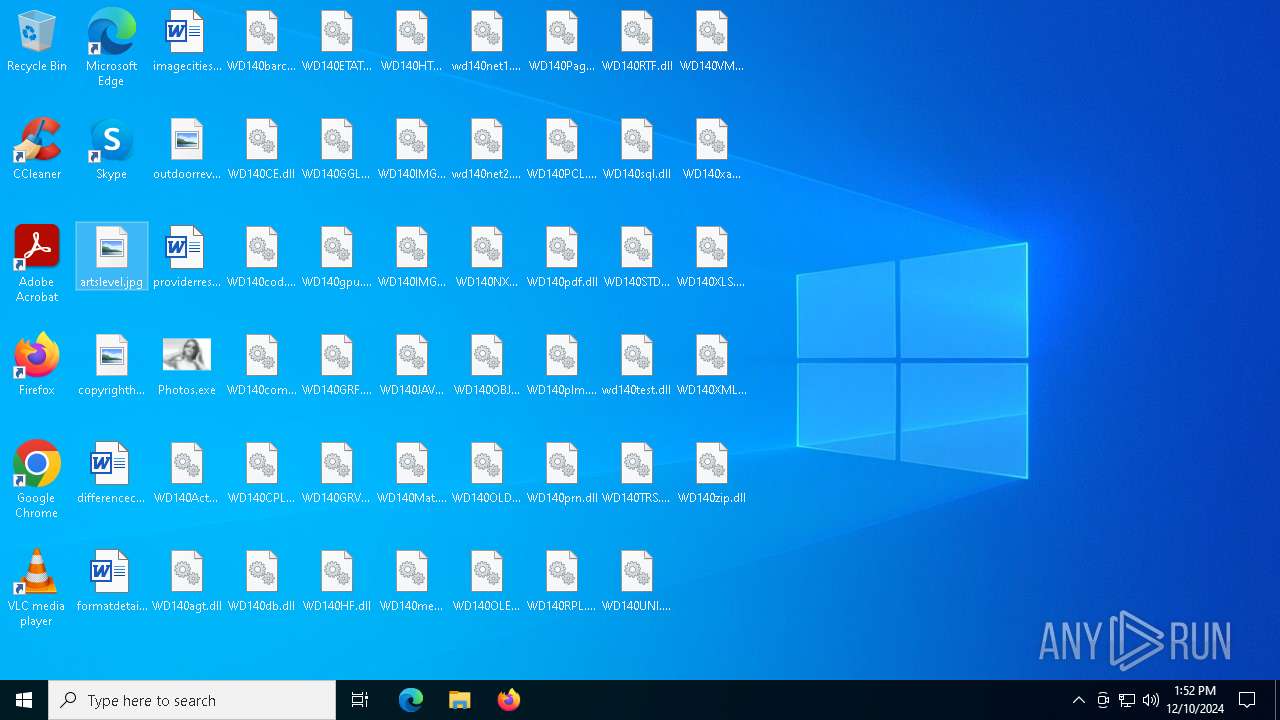
Executable files
87
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6664 | InstallFramework.exe | C:\Users\admin\Desktop\WD140barc.dll | executable | |
MD5:EB8F13AD9760EAECEF52E6F8911F42E0 | SHA256:BAA794E8010C5002CDC7AA7EA27B120D380FCC9AFACBEC825F428B512C4E9C77 | |||
| 6616 | Photos.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\InstallFramework_140025v[1].exe | executable | |
MD5:19A76EDA7B7D0BA22FA8FAB03E6CFC11 | SHA256:CDC01013292ED4766341F91FEB702EE8B4248E10EC127C3E241B1CE09CDB000E | |||
| 6664 | InstallFramework.exe | C:\Users\admin\Desktop\WD140Action.dll | executable | |
MD5:960599A741CAB2930772618EF7FE4B06 | SHA256:2F56CA86392C4C5A324D1B986C08B2A83E80D1D1FCB17633572E800FD501F772 | |||
| 6664 | InstallFramework.exe | C:\Users\admin\Desktop\WD140CE.dll | executable | |
MD5:3923452A556D7A8D8D6E7B63FA23267F | SHA256:1E210908A5D8976D7A908AEA989FA99D560A3EC90C5A5356CD597A27A51A0747 | |||
| 6664 | InstallFramework.exe | C:\Users\admin\Desktop\WD140HTML.dll | executable | |
MD5:A59102038A4A3228D95CDC2D83A4740D | SHA256:218BB09ED1653883D58831496CE5B644512C666C7726A0AB6026957FAD22852E | |||
| 6664 | InstallFramework.exe | C:\Users\admin\Desktop\WD140IMG2.DLL | executable | |
MD5:216A5855A64947C0ABEE0F7C49C965A0 | SHA256:7CB5E54E2CEB1D03A0C7934AE77E6A1B629D5909744E214E4B9EB9FC71A510B3 | |||
| 6664 | InstallFramework.exe | C:\Users\admin\Desktop\WD140JAV.DLL | executable | |
MD5:53ED360C2583A474CC4D62CA78CD9897 | SHA256:D62AE2B84F7CD38F6CC1B62CECC919A7EC047C2603D450A789F844943F37B5AD | |||
| 6664 | InstallFramework.exe | C:\Users\admin\Desktop\WD140GRV.dll | executable | |
MD5:95CFCF1D0FFF3DE8C292BFFDC517DCAB | SHA256:95A257B3607249EF146BB0F9010AE01FA6D4EA53588D6165CF1C841C8275165C | |||
| 6664 | InstallFramework.exe | C:\Users\admin\Desktop\WD140HF.dll | executable | |
MD5:82EDEB6B7F463154923864C73FDAF156 | SHA256:9730858E8CA84B1EFA828B60C2368BA814D73C89108BC2259E0B3B317E02641D | |||
| 6664 | InstallFramework.exe | C:\Users\admin\Desktop\WD140IMG.DLL | executable | |
MD5:74D31E5C88636D60BB7D64F687D7ABE0 | SHA256:7F0B1F22DC5E283F31E219FB640E9390829AA012FE9278230860BA8E04185238 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
58
DNS requests
20
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4308 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
6188 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
6516 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
6188 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
4308 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 314 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4308 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4308 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.23.209.187:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1076 | svchost.exe | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6616 | Photos.exe | Misc activity | ET INFO .exe File requested over FTP |
6616 | Photos.exe | Misc activity | ET HUNTING PE EXE Download over raw TCP |