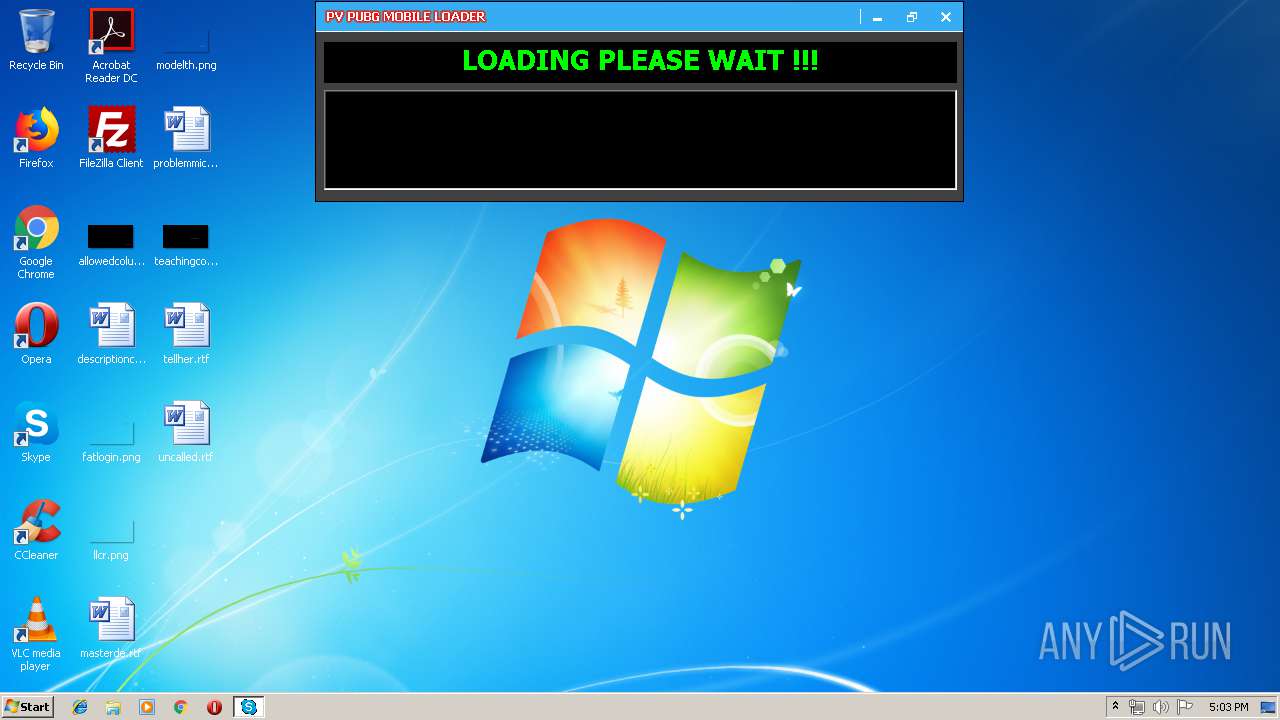
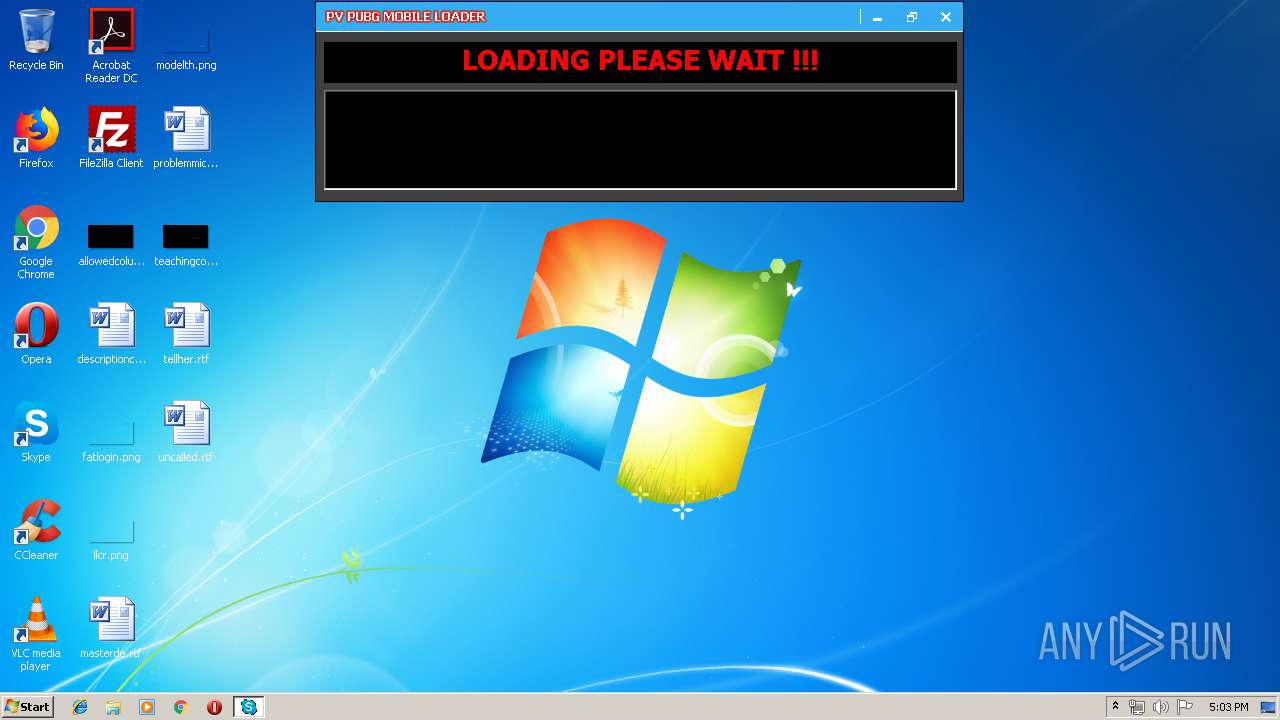
| File name: | PVPubgVIP8.2 (di' cu~).EXE |
| Full analysis: | https://app.any.run/tasks/5b8f1650-2252-4c2d-80fc-e669eaaac6e2 |
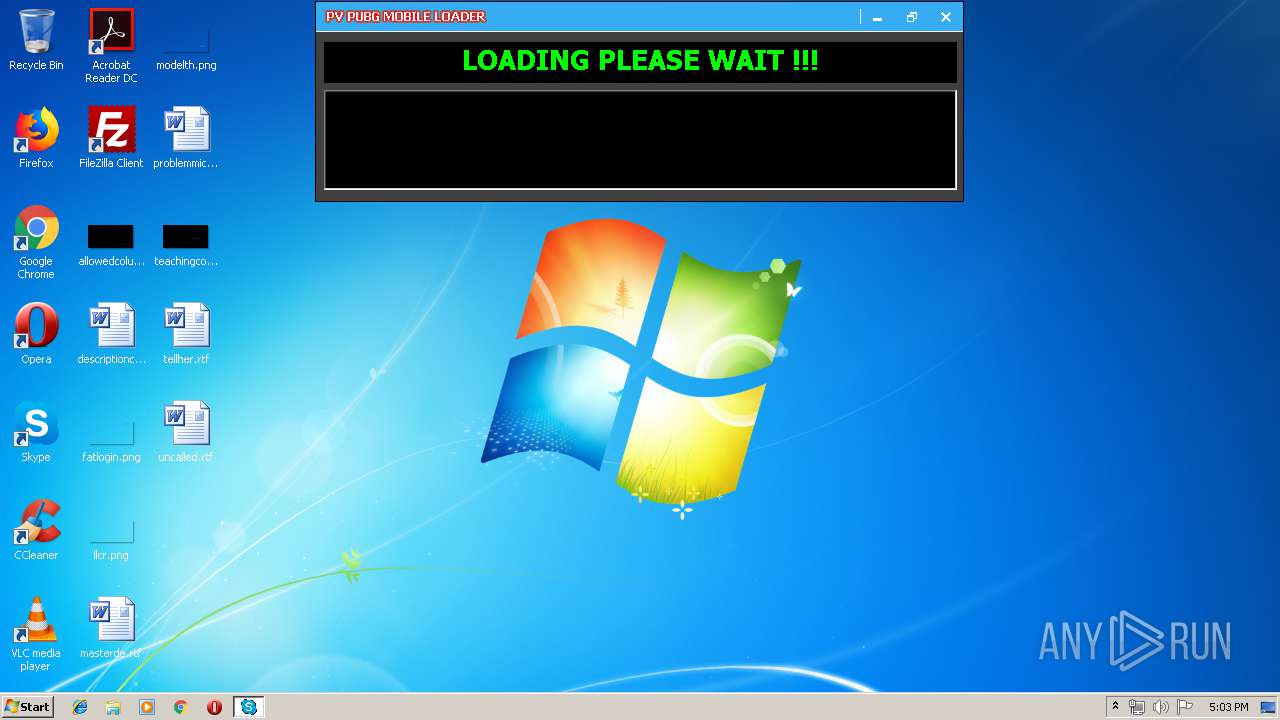
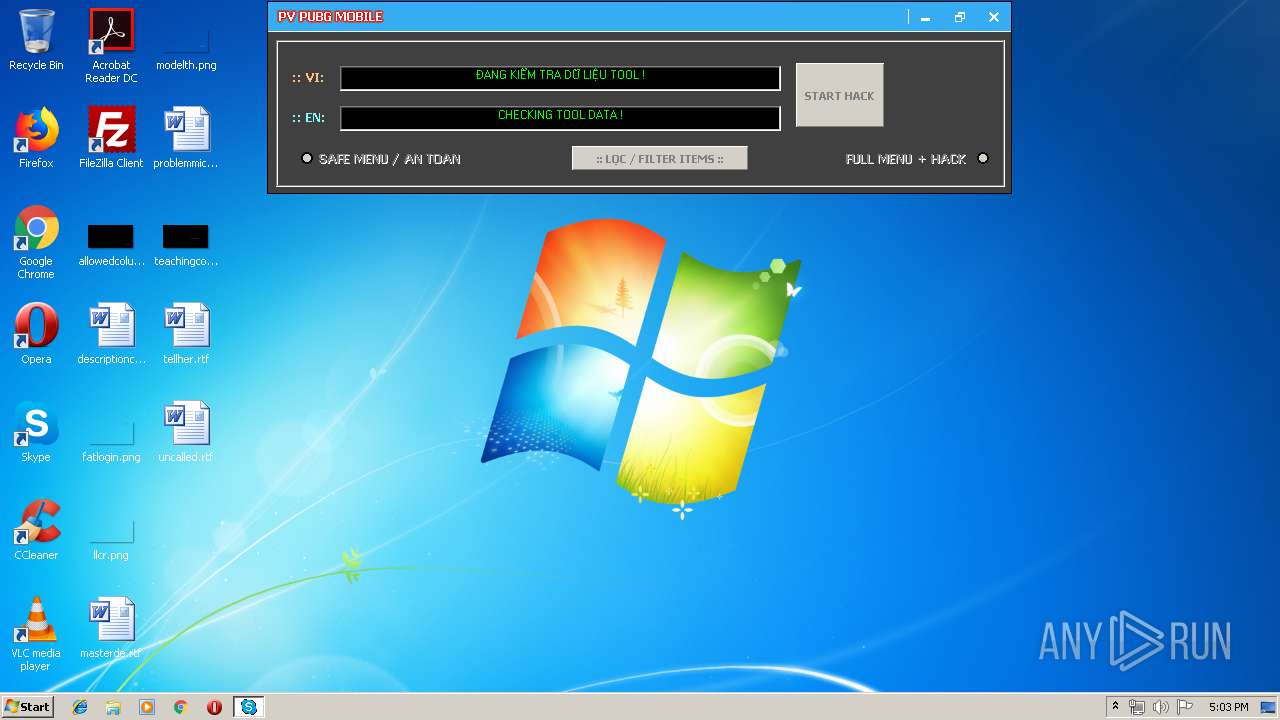
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 16:02:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E065D23E2D11BA7AEBF58EBDB5A14931 |
| SHA1: | 2A1D0FCC1E16DCA61653B9D32D6866DA8D3DD004 |
| SHA256: | 3847F998DC005F1F2E6608E4AAA694A334E9D935EE2927FB5C6BD29F3C6C8CD2 |
| SSDEEP: | 98304:8ElmoNGP6aNPFFja43VcbIeJn+ZBd+PUbwrDsuT7pHNvK3zAHIytB0:Nlmo4P6aNjja43YIxBd+PNjxNvK3di |
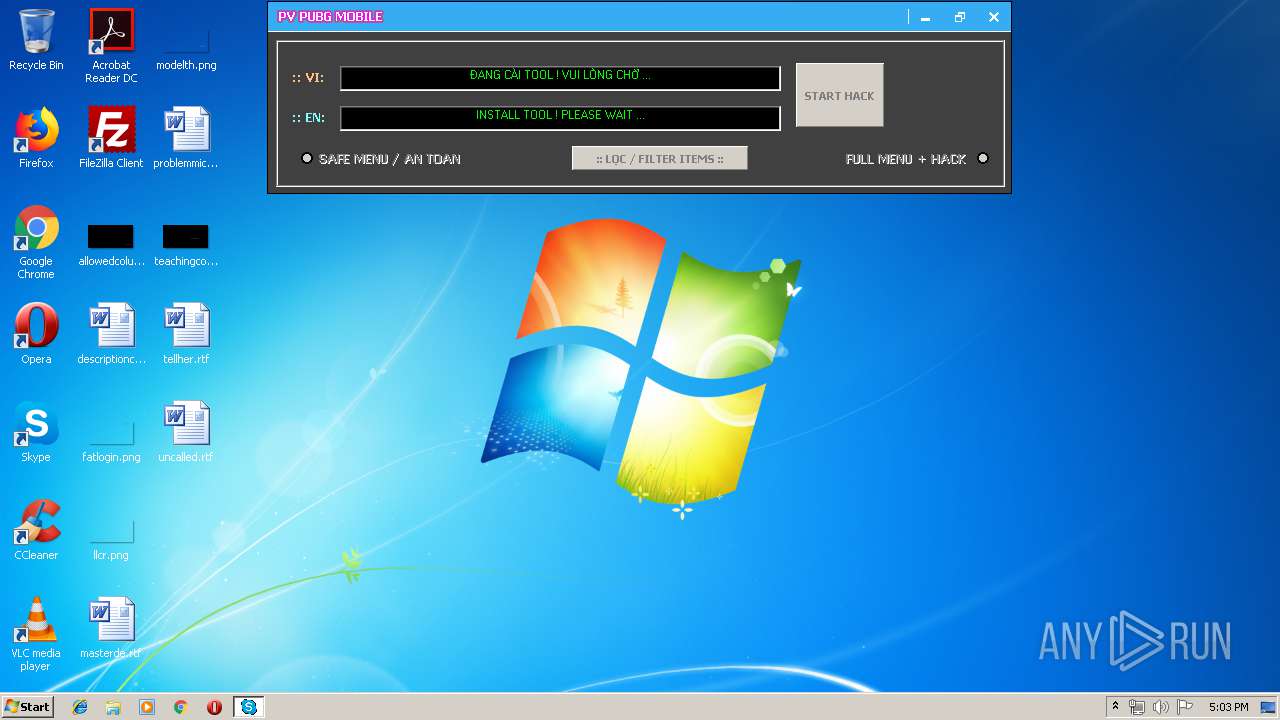
MALICIOUS
Application was dropped or rewritten from another process
- install.exe (PID: 3368)
- 453BE91F.EXE (PID: 1480)
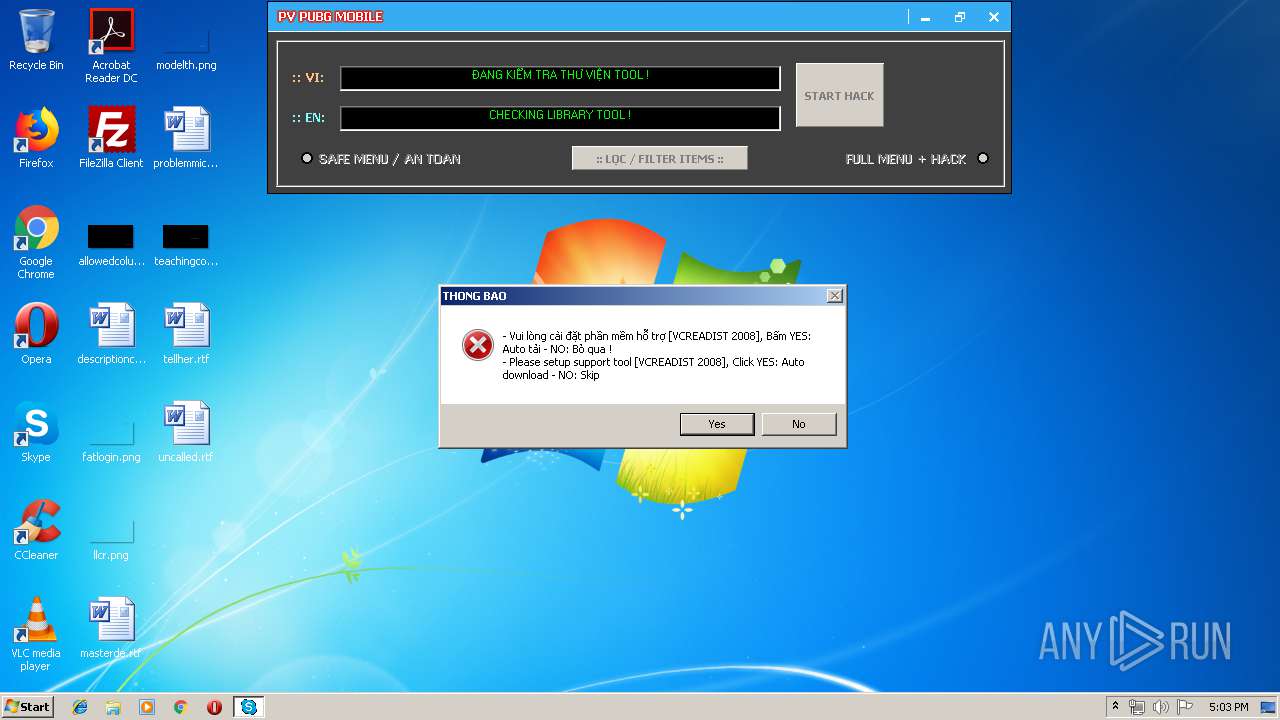
- VC2008.EXE (PID: 360)
Changes settings of System certificates
- 453BE91F.EXE (PID: 1480)
Loads dropped or rewritten executable
- install.exe (PID: 3368)
SUSPICIOUS
Starts itself from another location
- PVPubgVIP8.2 (di' cu~).EXE (PID: 2944)
Executable content was dropped or overwritten
- PVPubgVIP8.2 (di' cu~).EXE (PID: 2944)
- 453BE91F.EXE (PID: 1480)
- VC2008.EXE (PID: 360)
- 4E8EDF95.EXE (PID: 2580)
- msiexec.exe (PID: 3420)
Adds / modifies Windows certificates
- 453BE91F.EXE (PID: 1480)
Creates files in the Windows directory
- msiexec.exe (PID: 3420)
Removes files from Windows directory
- msiexec.exe (PID: 3420)
INFO
Creates a software uninstall entry
- msiexec.exe (PID: 3420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:29 09:58:45+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 348160 |
| InitializedDataSize: | 2703360 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x739000 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | Microsoft Coporation |
| CompanyName: | Microsoft Coporation |
| FileDescription: | Microsoft Coporation |
| ProductName: | Microsoft Coporation |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | PV LOADER |
| OriginalFileName: | PV LOADER.EXE |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Jul-2019 07:58:45 |
| Detected languages: |
|
| Comments: | Microsoft Coporation |
| CompanyName: | Microsoft Coporation |
| FileDescription: | Microsoft Coporation |
| ProductName: | Microsoft Coporation |
| FileVersion: | 1.00 |
| ProductVersion: | 1.00 |
| InternalName: | PV LOADER |
| OriginalFilename: | PV LOADER.EXE |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 29-Jul-2019 07:58:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00001000 | 0x00058000 | 0x00010000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.88235 | |
.rsrc | 0x00059000 | 0x0029296C | 0x00286000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.9821 |
.idata | 0x002EC000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.175446 |
0x002ED000 | 0x00296000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0407044 | |
govzcxjp | 0x00583000 | 0x001B5000 | 0x001B5000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.84915 |
daalxhbn | 0x00738000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.73639 |
.taggant | 0x00739000 | 0x00003000 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.553943 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.79352 | 523 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
101 | 7.98182 | 2551808 | Latin 1 / Western European | English - United States | CUSTOM |
30001 | 4.26154 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
30002 | 4.71623 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
30003 | 4.78523 | 1736 | Latin 1 / Western European | UNKNOWN | RT_ICON |
30004 | 4.71556 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
30005 | 7.93375 | 9456 | Latin 1 / Western European | UNKNOWN | RT_ICON |
30006 | 3.47641 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
30007 | 3.54405 | 38056 | Latin 1 / Western European | UNKNOWN | RT_ICON |
30008 | 3.74047 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
kernel32.dll |
Total processes
44
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | C:\Users\admin\AppData\Local\Temp\LIB\VC2008.EXE /Q | C:\Users\admin\AppData\Local\Temp\LIB\VC2008.EXE | 453BE91F.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2008 Redistributable Setup Exit code: 0 Version: 9.0.30729.17 Modules
| |||||||||||||||
| 1480 | "C:\Users\admin\AppData\Local\Temp\453BE91F.EXE" | C:\Users\admin\AppData\Local\Temp\453BE91F.EXE | 4E8EDF95.EXE | ||||||||||||
User: admin Company: Microsoft Coporation Integrity Level: HIGH Description: Microsoft Coporation Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2252 | "C:\Users\admin\AppData\Local\Temp\PVPubgVIP8.2 (di' cu~).EXE" | C:\Users\admin\AppData\Local\Temp\PVPubgVIP8.2 (di' cu~).EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Coporation Integrity Level: MEDIUM Description: Microsoft Coporation Exit code: 3221226540 Version: 1.00 Modules
| |||||||||||||||
| 2580 | "C:\Users\admin\AppData\Local\Temp\4E8EDF95.EXE" C:\Users\admin\AppData\Local\Temp\PVPubgVIP8.2 (di' cu~).EXE | C:\Users\admin\AppData\Local\Temp\4E8EDF95.EXE | PVPubgVIP8.2 (di' cu~).EXE | ||||||||||||
User: admin Company: Microsoft Coporation Integrity Level: HIGH Description: Microsoft Coporation Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2944 | "C:\Users\admin\AppData\Local\Temp\PVPubgVIP8.2 (di' cu~).EXE" | C:\Users\admin\AppData\Local\Temp\PVPubgVIP8.2 (di' cu~).EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Coporation Integrity Level: HIGH Description: Microsoft Coporation Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3368 | c:\a64949a19f6d1a42e24d09b2a3d844\.\install.exe /Q | c:\a64949a19f6d1a42e24d09b2a3d844\install.exe | — | VC2008.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: External Installer Exit code: 0 Version: 9.0.30729.1 built by: SP Modules
| |||||||||||||||
| 3420 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 182
Read events
940
Write events
230
Delete events
12
Modification events
| (PID) Process: | (2944) PVPubgVIP8.2 (di' cu~).EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2944) PVPubgVIP8.2 (di' cu~).EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2580) 4E8EDF95.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2580) 4E8EDF95.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1480) 453BE91F.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: 453BE91F.EXE | |||
| (PID) Process: | (1480) 453BE91F.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\453BE91F_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1480) 453BE91F.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\453BE91F_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1480) 453BE91F.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\453BE91F_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1480) 453BE91F.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\453BE91F_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1480) 453BE91F.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\453BE91F_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
29
Suspicious files
3
Text files
27
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2944 | PVPubgVIP8.2 (di' cu~).EXE | C:\Users\admin\AppData\Local\Temp\~DF13AD4598A10EF06B.TMP | — | |
MD5:— | SHA256:— | |||
| 2580 | 4E8EDF95.EXE | C:\Users\admin\AppData\Local\Temp\~DF4E295C566A12F73A.TMP | — | |
MD5:— | SHA256:— | |||
| 1480 | 453BE91F.EXE | C:\Users\admin\AppData\Local\Temp\3E31.tmp | — | |
MD5:— | SHA256:— | |||
| 2580 | 4E8EDF95.EXE | C:\Users\admin\AppData\Local\Temp\453BE91F.EXE | executable | |
MD5:— | SHA256:— | |||
| 2944 | PVPubgVIP8.2 (di' cu~).EXE | C:\Users\admin\AppData\Local\Temp\4E8EDF95.EXE | executable | |
MD5:— | SHA256:— | |||
| 360 | VC2008.EXE | C:\a64949a19f6d1a42e24d09b2a3d844\vc_red.cab | compressed | |
MD5:ECCA3C1ACB74CB73C600EABDD3F9C9D9 | SHA256:43B7648183347374236296F2176C7C7DA920DA9C1A08ADDA761E12614EFB299E | |||
| 360 | VC2008.EXE | C:\a64949a19f6d1a42e24d09b2a3d844\install.res.1049.dll | executable | |
MD5:2E57AE4186F17BE4148077FFE8212A27 | SHA256:AC9EF02D54EB87A5BC2BC8C77A6497853072FF37E7E82495EF8D79F6A5AF07E3 | |||
| 360 | VC2008.EXE | C:\a64949a19f6d1a42e24d09b2a3d844\install.res.1040.dll | executable | |
MD5:DCCA7196203D338B41EAD5E1418C6A92 | SHA256:C2A81077DA2201D180BD5496129EA6BCFC5930D8A6D256BABDB9A552B1A597D2 | |||
| 360 | VC2008.EXE | C:\a64949a19f6d1a42e24d09b2a3d844\install.res.1041.dll | executable | |
MD5:0FCC2F2BF7C18392514413A3C2A5EC5A | SHA256:11C111B3F24BA7D197007FB572B9F77E7D6F58C290DE239A08F287C2AEB3B89D | |||
| 360 | VC2008.EXE | C:\a64949a19f6d1a42e24d09b2a3d844\install.res.3082.dll | executable | |
MD5:55A9B25FA0D768FB902842439D041B1F | SHA256:8F826DBA565FC464395ED24219DA946F55692705DE9F61F501DCFEBF338970A3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
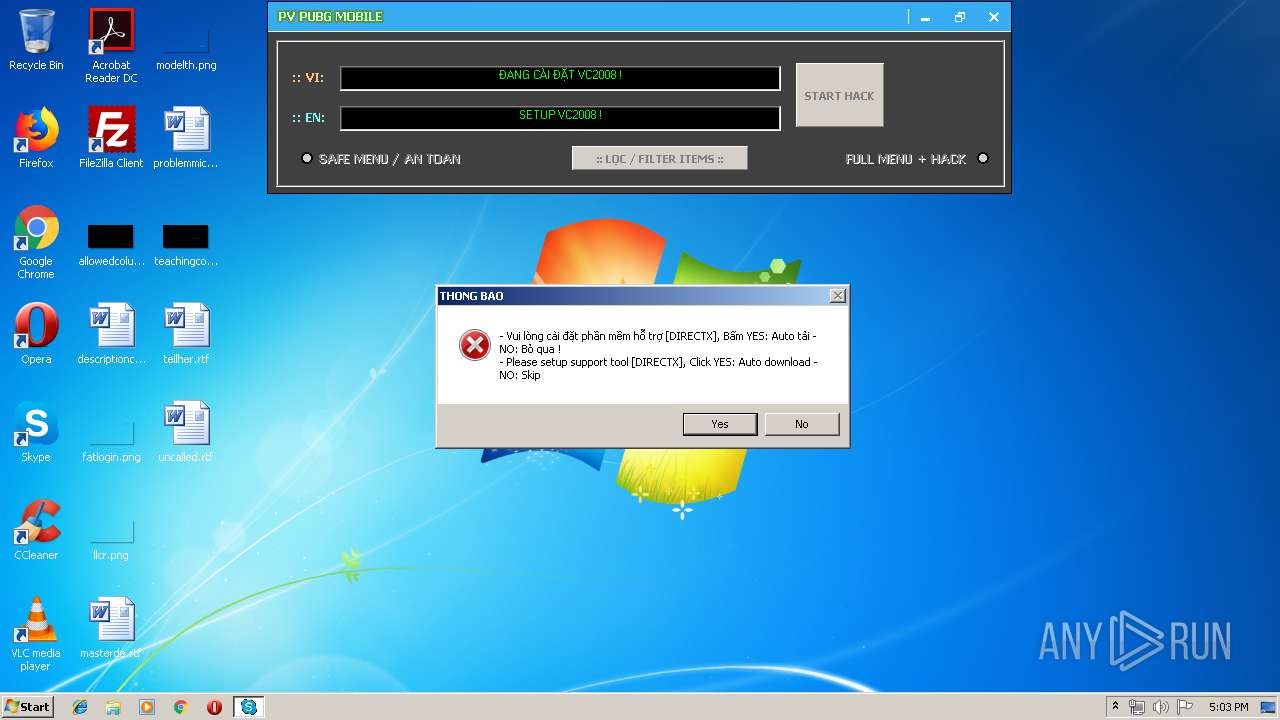
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1480 | 453BE91F.EXE | GET | — | 2.18.233.19:80 | http://download.microsoft.com/download/8/4/A/84A35BF1-DAFE-4AE8-82AF-AD2AE20B6B14/directx_Jun2010_redist.exe | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1480 | 453BE91F.EXE | 2.18.233.19:443 | download.microsoft.com | Akamai International B.V. | — | whitelisted |
1480 | 453BE91F.EXE | 2.18.233.19:80 | download.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1480 | 453BE91F.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
PVPubgVIP8.2 (di' cu~).EXE |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
4E8EDF95.EXE |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
453BE91F.EXE |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|