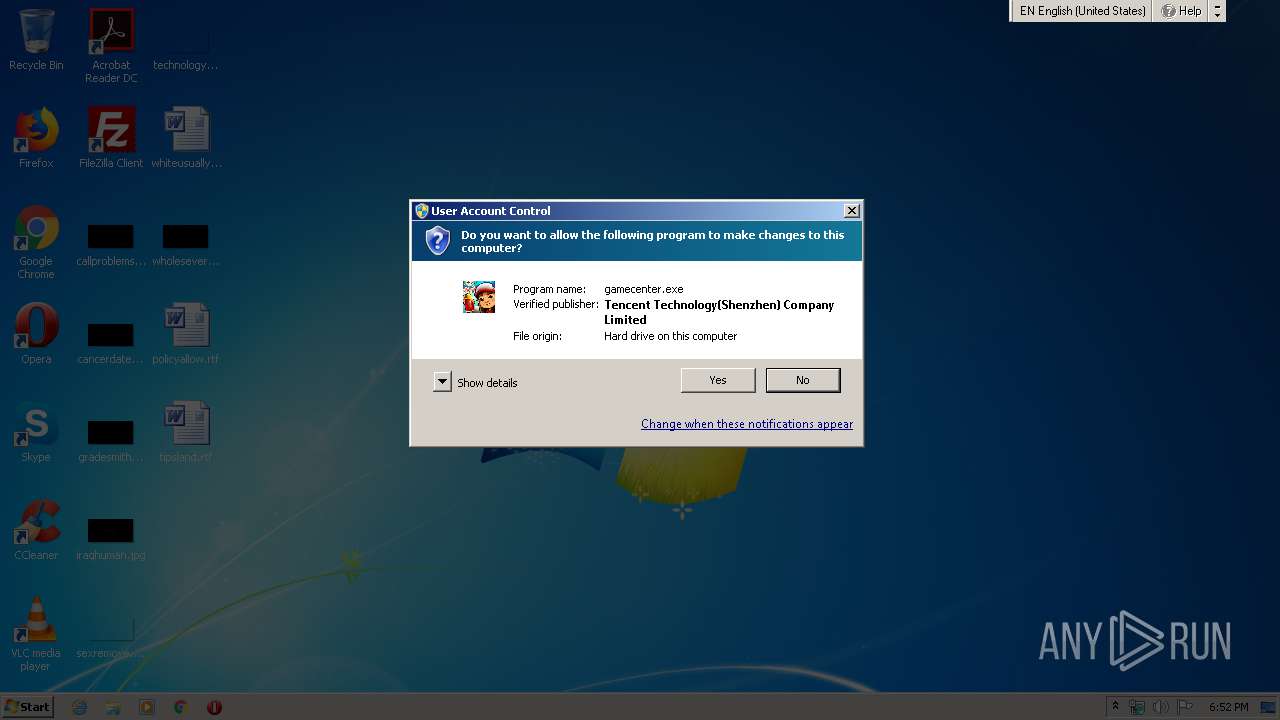
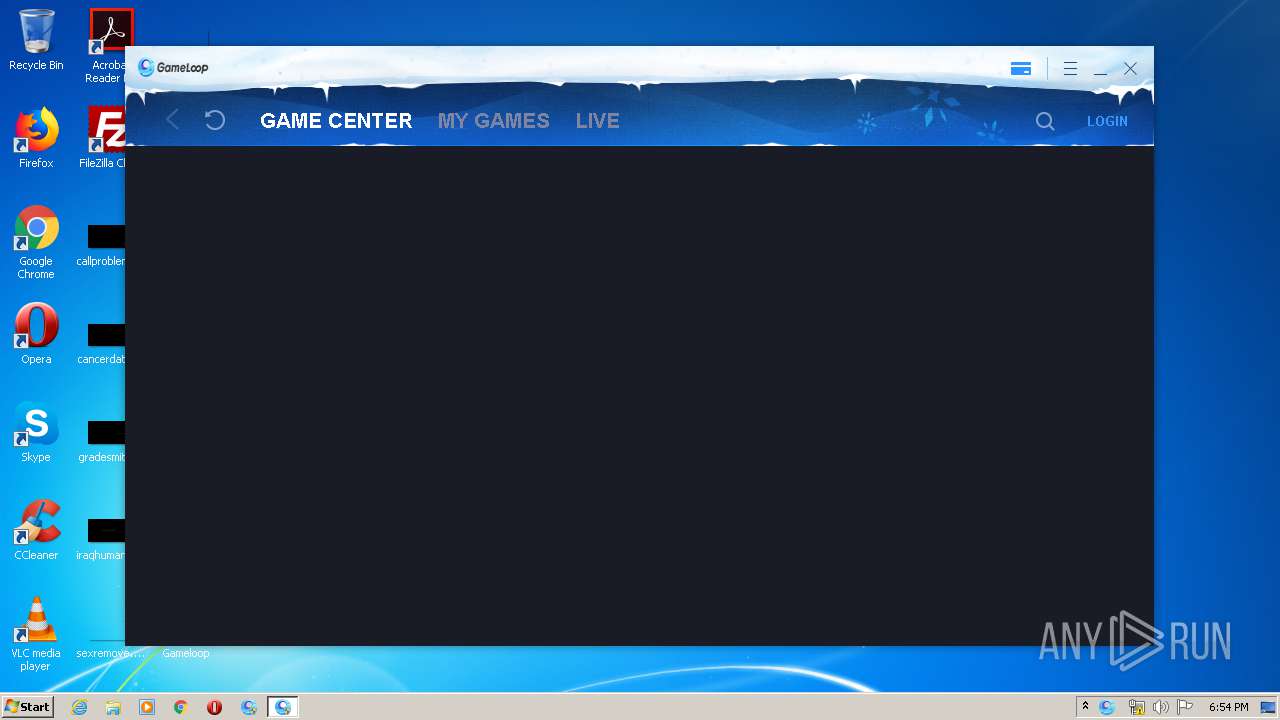
| File name: | gamecenter.exe |
| Full analysis: | https://app.any.run/tasks/7f9a0862-756e-4e6c-bc8e-590b9737d39b |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | May 12, 2020, 17:52:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5FA43DF11E9D3E548805A694B982234D |
| SHA1: | B052C14DF8775B389D905294B4FE8B80E8CD3F91 |
| SHA256: | 383B5AE69C434403D285D3BADF890A6E3B9F3D654F1AB54E29349C1948E9D9BD |
| SSDEEP: | 24576:8/KiLPCdw5c8RxEUqckhIXrnq7nJVL8ZXFzIohnpSU9fRTLI7eofAdvqvyUHajk:niLPCG5Icnq7JVQpVIoTQ70qBaY |
MALICIOUS
Loads dropped or rewritten executable
- gamecenter.exe (PID: 2064)
- QMEmulatorService.exe (PID: 3244)
- AppMarket.exe (PID: 1460)
- TBSWebRenderer.exe (PID: 3580)
- GameDownload.exe (PID: 940)
- TenioDL.exe (PID: 4008)
Application was dropped or rewritten from another process
- QMEmulatorService.exe (PID: 3244)
- Tinst.exe (PID: 1852)
- AppMarket.exe (PID: 1460)
- TBSWebRenderer.exe (PID: 3580)
- GameDownload.exe (PID: 940)
- TenioDL.exe (PID: 4008)
Adds new firewall rule via NETSH.EXE
- Tinst.exe (PID: 1852)
Downloads executable files from the Internet
- gamecenter.exe (PID: 2064)
Actions looks like stealing of personal data
- AppMarket.exe (PID: 1460)
Changes settings of System certificates
- AppMarket.exe (PID: 1460)
- gamecenter.exe (PID: 2064)
SUSPICIOUS
Executable content was dropped or overwritten
- gamecenter.exe (PID: 2064)
- Market.exe (PID: 3932)
- Tinst.exe (PID: 1852)
- GameDownload.exe (PID: 940)
Low-level read access rights to disk partition
- gamecenter.exe (PID: 2064)
- QMEmulatorService.exe (PID: 3244)
- AppMarket.exe (PID: 1460)
- GameDownload.exe (PID: 940)
Creates files in the program directory
- QMEmulatorService.exe (PID: 3244)
- gamecenter.exe (PID: 2064)
- AppMarket.exe (PID: 1460)
- Tinst.exe (PID: 1852)
Creates files in the user directory
- gamecenter.exe (PID: 2064)
- Tinst.exe (PID: 1852)
- AppMarket.exe (PID: 1460)
- GameDownload.exe (PID: 940)
- TenioDL.exe (PID: 4008)
Uses NETSH.EXE for network configuration
- Tinst.exe (PID: 1852)
Executed as Windows Service
- QMEmulatorService.exe (PID: 3244)
Creates files in the Windows directory
- QMEmulatorService.exe (PID: 3244)
Modifies the open verb of a shell class
- Tinst.exe (PID: 1852)
Creates a software uninstall entry
- Tinst.exe (PID: 1852)
Adds / modifies Windows certificates
- AppMarket.exe (PID: 1460)
- gamecenter.exe (PID: 2064)
Reads Internet Cache Settings
- GameDownload.exe (PID: 940)
Uses ICACLS.EXE to modify access control list
- TenioDL.exe (PID: 4008)
INFO
Reads settings of System Certificates
- gamecenter.exe (PID: 2064)
- AppMarket.exe (PID: 1460)
Reads the hosts file
- AppMarket.exe (PID: 1460)
- GameDownload.exe (PID: 940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:02:21 12:19:14+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 819200 |
| InitializedDataSize: | 777216 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7c0d1 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Feb-2020 11:19:14 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 21-Feb-2020 11:19:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000C7F23 | 0x000C8000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64604 |
.rdata | 0x000C9000 | 0x0003163C | 0x00031800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.14651 |
.data | 0x000FB000 | 0x00006504 | 0x00004C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.6235 |
.gfids | 0x00102000 | 0x00000CE8 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.74181 |
.tls | 0x00103000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.QMGuid | 0x00104000 | 0x00000014 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00105000 | 0x00078430 | 0x00078600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.82804 |
.reloc | 0x0017E000 | 0x0000C408 | 0x0000C600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.53711 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06216 | 651 | UNKNOWN | English - United States | RT_MANIFEST |
7 | 2.32128 | 84 | UNKNOWN | Chinese - PRC | RT_STRING |
107 | 1.51664 | 20 | UNKNOWN | Chinese - PRC | RT_GROUP_ICON |
109 | 3.24529 | 80 | UNKNOWN | Chinese - PRC | RT_MENU |
133 | 7.99643 | 354782 | UNKNOWN | Chinese - PRC | ZIPRES |
134 | 7.92411 | 30101 | UNKNOWN | Chinese - PRC | CUSTOM |
135 | 5.81636 | 76168 | UNKNOWN | Chinese - PRC | CUSTOM |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
NETAPI32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
VERSION.dll |
Total processes
68
Monitored processes
16
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 740 | "C:\Windows\system32\Netsh.exe" advfirewall firewall add rule name="AppMarket" dir=in program="c:\program files\txgameassistant\appmarket\AppMarket.exe" action=allow | C:\Windows\system32\Netsh.exe | — | Tinst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 940 | "C:\Program Files\TxGameAssistant\AppMarket\GameDownload.exe" -from appmark -component -notiywnd 524788 -noupdate -no_install_vdi -no_install_vbox -install_aow_rootfs -pkg com.kiloo.subwaysurf -downspeedlimit 0 -aeparam -engine aow -aeparamend -downspeedlimit 0 | C:\Program Files\TxGameAssistant\AppMarket\GameDownload.exe | AppMarket.exe | ||||||||||||
User: admin Company: Tencent Integrity Level: HIGH Description: Gameloop - Install Exit code: 0 Version: 3.11.377.100 Modules
| |||||||||||||||
| 1460 | "C:\Program Files\TxGameAssistant\AppMarket\AppMarket.exe" -pkg com.kiloo.subwaysurf -apksupplyid 900206145 -displayname Subway_Surfers | C:\Program Files\TxGameAssistant\AppMarket\AppMarket.exe | gamecenter.exe | ||||||||||||
User: admin Company: Tencent Integrity Level: HIGH Description: Gameloop Exit code: 0 Version: 3.11.377.100 Modules
| |||||||||||||||
| 1720 | "C:\Windows\System32\icacls.exe" C:\Users\admin\AppData\Roaming\Tencent\Config\ /t /setintegritylevel low | C:\Windows\System32\icacls.exe | — | TenioDL.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1852 | "C:\Temp\TxGameDownload\Component\AppMarket\Setup\Tinst.exe" | C:\Temp\TxGameDownload\Component\AppMarket\Setup\Tinst.exe | gamecenter.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: TMarketInst Exit code: 0 Version: 3.11.377.100 Modules
| |||||||||||||||
| 2064 | "C:\Users\admin\Desktop\gamecenter.exe" | C:\Users\admin\Desktop\gamecenter.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2132 | "C:\Windows\system32\Netsh.exe" advfirewall firewall add rule name="TInst" dir=in program="c:\program files\txgameassistant\appmarket\TInst.exe" action=allow | C:\Windows\system32\Netsh.exe | — | Tinst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2244 | "C:\Windows\system32\Netsh.exe" advfirewall firewall add rule name="bugreport" dir=in program="c:\program files\txgameassistant\appmarket\bugreport.exe" action=allow | C:\Windows\system32\Netsh.exe | — | Tinst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2460 | "C:\Windows\system32\Netsh.exe" advfirewall firewall add rule name="GameDownload" dir=in program="c:\program files\txgameassistant\appmarket\GameDownload.exe" action=allow | C:\Windows\system32\Netsh.exe | — | Tinst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2480 | "C:\Users\admin\Desktop\gamecenter.exe" | C:\Users\admin\Desktop\gamecenter.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
2 444
Read events
457
Write events
1 987
Delete events
0
Modification events
| (PID) Process: | (2064) gamecenter.exe | Key: | HKEY_CURRENT_USER\Software\Tencent\MobileGamePC |
| Operation: | write | Name: | TempPath |
Value: C:\Temp\TxGameDownload\Component\ | |||
| (PID) Process: | (2064) gamecenter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Tencent\MobileGamePC |
| Operation: | write | Name: | SupplyId |
Value: 900206145 | |||
| (PID) Process: | (2064) gamecenter.exe | Key: | HKEY_CURRENT_USER\Software\Tencent\MobileGamePC |
| Operation: | write | Name: | UserLanguage |
Value: en | |||
| (PID) Process: | (2064) gamecenter.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2064) gamecenter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\CDD4EEAE6000AC7F40C3802C171E30148030C072 |
| Operation: | write | Name: | Blob |
Value: 0F0000000100000014000000391BE92883D52509155BFEAE27B9BD340170B76B030000000100000014000000CDD4EEAE6000AC7F40C3802C171E30148030C0720B000000010000004A0000004D006900630072006F0073006F0066007400200052006F006F007400200043006500720074006900660069006300610074006500200041007500740068006F007200690074007900000069000000010000000E000000300C060A2B0601040182373C030220000000010000009D0500003082059930820381A003020102021079AD16A14AA0A5AD4C7358F407132E65300D06092A864886F70D0101050500305F31133011060A0992268993F22C6401191603636F6D31193017060A0992268993F22C64011916096D6963726F736F6674312D302B060355040313244D6963726F736F667420526F6F7420436572746966696361746520417574686F72697479301E170D3031303530393233313932325A170D3231303530393233323831335A305F31133011060A0992268993F22C6401191603636F6D31193017060A0992268993F22C64011916096D6963726F736F6674312D302B060355040313244D6963726F736F667420526F6F7420436572746966696361746520417574686F7269747930820222300D06092A864886F70D01010105000382020F003082020A0282020100F35DFA8067D45AA7A90C2C9020D035083C7584CDB707899C89DADECEC360FA91685A9E94712918767CC2E0C82576940E58FA043436E6DFAFF780BAE9580B2B93E59D05E3772291F734643C22911D5EE10990BC14FEFC755819E179B70792A3AE885908D89F07CA0358FC68296D32D7D2A8CB4BFCE10B48324FE6EBB8AD4FE45C6F139499DB95D575DBA81AB79491B4775BF5480C8F6A797D1470047D6DAF90F5DA70D847B7BF9B2F6CE705B7E11160AC7991147CC5D6A6E4E17ED5C37EE592D23C00B53682DE79E16DF3B56EF89F33C9CB527D739836DB8BA16BA295979BA3DEC24D26FF0696672506C8E7ACE4EE1233953199C835084E34CA7953D5B5BE6332594036C0A54E044D3DDB5B0733E458BFEF3F5364D842593557FD0F457C24044D9ED6387411972290CE684474926FD54B6FB086E3C73642A0D0FCC1C05AF9A361B9304771960A16B091C04295EF107F286AE32A1FB1E4CD033F777104C720FC490F1D4588A4D7CB7E88AD8E2DEC45DBC45104C92AFCEC869E9A11975BDECE5388E6E2B7FDAC95C22840DBEF0490DF813339D9B245A5238706A5558931BB062D600E41187D1F2EB597CB11EB15D524A594EF151489FD4B73FA325BFCD13300F95962700732EA2EAB402D7BCADD21671B30998F16AA23A841D1B06E119B36C4DE40749CE15865C1601E7A5B38C88FBB04267CD41640E5B66B6CAA86FD00BFCEC1350203010001A351304F300B0603551D0F0404030201C6300F0603551D130101FF040530030101FF301D0603551D0E041604140EAC826040562797E52513FC2AE10A539559E4A4301006092B06010401823715010403020100300D06092A864886F70D01010505000382020100C5114D033A60DD5D5211778FB2BB36C8B205BFB4B7A8D8209D5C1303B61C22FA061335B6C863D49A476F2657D255F104B1265FD6A95068A0BCD2B86ECCC3E9ACDF19CD78AC5974AC663436C41B3E6C384C330E30120DA326FE515300FFAF5A4E840D0F1FE46D052E4E854B8D6C336F54D264ABBF50AF7D7A39A037ED63030FFC1306CE1636D4543B951B51623AE54D17D40539929A27A85BAABDECBBBEE3208960716C56B3A513D06D0E237E9503ED683DF2D863B86B4DB6E830B5E1CA944BF7A2AA5D9930B23DA7C2516C28200124272B4B00B79D116B70BEB21082BC0C9B68D08D3B2487AA9928729D335F5990BDF5DE939E3A625A3439E288551DB906B0C1896B2DD769C319123684D0C9A0DAFF2F6978B2E57ADAEBD70CC0F7BD6317B8391338A2365B7BF285566A1D6462C138E2AABF5166A294F5129C6622106BF2B730922DF229F03D3B144368A2F19C2937CBCE3820256D7C67F37E24122403088147ECA59E97F518D7CFBBD5EF7696EFFDCEDB569D95A042F99758E1D73122D35F59E63E6E2200EA4384B625DBD9F3085668C0646B1D7CECB693A262576E2ED8E7588FC4314926DDDE293587F53071705B143C69BD89127DEB2EA3FED87F9E825A520A2BC1432BD930889FC810FB898DE6A18575337E6C9EDB7313646269A52F7DCA966D9FF8044D30923D6E211421C93DE0C3FD8A6B9D4AFDD1A19D9943773FB0DA | |||
| (PID) Process: | (2064) gamecenter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\A43489159A520F0D93D032CCAF37E7FE20A8B419 |
| Operation: | write | Name: | Blob |
Value: 0F00000001000000100000008B3C3087B7056F5EC5DDBA91A1B901F069000000010000000E000000300C060A2B0601040182373C03020B00000001000000320000004D006900630072006F0073006F0066007400200052006F006F007400200041007500740068006F0072006900740079000000030000000100000014000000A43489159A520F0D93D032CCAF37E7FE20A8B41920000000010000001604000030820412308202FAA003020102020F00C1008B3C3C8811D13EF663ECDF40300D06092A864886F70D01010405003070312B3029060355040B1322436F70797269676874202863292031393937204D6963726F736F667420436F72702E311E301C060355040B13154D6963726F736F667420436F72706F726174696F6E3121301F060355040313184D6963726F736F667420526F6F7420417574686F72697479301E170D3937303131303037303030305A170D3230313233313037303030305A3070312B3029060355040B1322436F70797269676874202863292031393937204D6963726F736F667420436F72702E311E301C060355040B13154D6963726F736F667420436F72706F726174696F6E3121301F060355040313184D6963726F736F667420526F6F7420417574686F7269747930820122300D06092A864886F70D01010105000382010F003082010A0282010100A902BDC170E63BF24E1B289F97785E30EAA2A98D255FF8FE954CA3B7FE9DA2203E7C51A29BA28F60326BD1426479EEAC76C954DAF2EB9C861C8F9F8466B3C56B7A6223D61D3CDE0F0192E896C4BF2D669A9A682699D03A2CBF0CB55826C146E70A3E38962CA92839A8EC498342E3840FBB9A6C5561AC827CA1602D774CE999B4643B9A501C310824149FA9E7912B18E63D986314605805659F1D375287F7A7EF9402C61BD3BF5545B38980BF3AEC54944EAEFDA77A6D744EAF18CC96092821005790606937BB4B12073C56FF5BFBA4660A08A6D2815657EFB63B5E16817704DAF6BEAE8095FEB0CD7FD6A71A725C3CCABCF008A32230B30685C9B320771385DF0203010001A381A83081A53081A20603551D0104819A30819780105BD070EF69729E23517E14B24D8EFFCBA1723070312B3029060355040B1322436F70797269676874202863292031393937204D6963726F736F667420436F72702E311E301C060355040B13154D6963726F736F667420436F72706F726174696F6E3121301F060355040313184D6963726F736F667420526F6F7420417574686F72697479820F00C1008B3C3C8811D13EF663ECDF40300D06092A864886F70D0101040500038201010095E80BC08DF3971835EDB80124D87711F35C60329F9E0BCB3E0591888FC93AE621F2F057932CB5A047C862EFFCD7CC3B3B5AA9365469FE246D3FC9CCAADE057CDD318D3D9F10706ABBFE124F1869C0FCD043E3115A204FEA627BAFAA19C82B37252DBE65A1128A250F63A3F7541CF921C9D615F352AC6E433207FD8217F8E5676C0D51F6BDF152C7BDE7C430FC203109881D95291A4DD51D02A5F180E003B45BF4B1DDC857EE6549C75254B6B4032812FF90D6F0088F7EB897C5AB372CE47AE4A877E376A000D06A3FC1D2368AE04112A8356A1B6ADB35E1D41C04E4A84504C85A33386E4D1C0D62B70AA28CD3D5543F46CD1C55A670DB123A8793759FA7D2A0 | |||
| (PID) Process: | (2064) gamecenter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\7F88CD7223F3C813818C994614A89C99FA3B5247 |
| Operation: | write | Name: | Blob |
Value: 0F0000000100000010000000D67576F5521D1CCAB52E9215E0F9F7430B00000001000000400000004D006900630072006F0073006F00660074002000410075007400680065006E007400690063006F0064006500280074006D002900200052006F006F0074000000090000000100000016000000301406082B0601050507030406082B060105050703030300000001000000140000007F88CD7223F3C813818C994614A89C99FA3B52472000000001000000DA030000308203D6308202BEA003020102020101300D06092A864886F70D01010405003050310B3009060355040613025553310D300B060355040A13044D53465431323030060355040313294D6963726F736F66742041757468656E7469636F646528746D2920526F6F7420417574686F72697479301E170D3935303130313038303030315A170D3939313233313233353935395A3050310B3009060355040613025553310D300B060355040A13044D53465431323030060355040313294D6963726F736F66742041757468656E7469636F646528746D2920526F6F7420417574686F7269747930820122300D06092A864886F70D01010105000382010F003082010A0282010100DF08BAE33F6E649BF589AF28964A078F1B2E8B3E1DFCB88069A3A1CEDBDFB08E6C8976294FCA603539AD7232E00BAE293D4C16D94B3C9DDAC5D3D109C92C6FA6C2605345DD4BD155CD031CD2595624F3E578D807CCD8B31F903FC01A71501D2DA712086D7CB0866CC7BA853207E1616FAF03C56DE5D6A18F36F6C10BD13E69974872C97FA4C8C24A4C7EA1D194A6D7DCEB05462EB818B4571D8649DB694A2C21F55E0F542D5A43A97A7E6A8E504D2557A1BF1B1505437B2C058DBD3D038C93227D63EA0A5705060ADB6198652D4749A8E7E656755CB8640863A9304066B2F9B6E334E86730E1430B87FFC9BE72105E23F09BA74865BF09887BCD72BC2E799B7B0203010001A381BA3081B7300D0603551D0A040630040302078030320603550403042B13294D6963726F736F66742041757468656E7469636F646528746D2920526F6F7420417574686F7269747930720603551D01046B306980101A1BE75B9FFD8C2AC339AE0C622E5332A1523050310B3009060355040613025553310D300B060355040A13044D53465431323030060355040313294D6963726F736F66742041757468656E7469636F646528746D2920526F6F7420417574686F72697479820101300D06092A864886F70D010104050003820101002DC9E2F6129E5D5667FAFA4B9A7EDC29565C80140228856E26F3CD58DA5080C5F819B3A67CE29D6B5F3B8F2274E61804FC4740D87A3F3066F012A4D1EB1DE7B6F498AB5322865158EE230976E41D455C4BFF4CE302500113CC41A45297D486D5C4FE8383657DEABEA2683BC1B12998BFA2A5FC9DD384EE701750F30BFA3CEFA9278B91B448C845A0E101424B4476041CC219A28E6B2098C4DD02ACB4D2A20E8D5DB9368E4A1B5D6C1AE2CB007F10F4B295EFE3E8FFA17358A9752CA2499585FECCDA448AC21244D244C8A5A21FA95A8E56C2C37BCF4260DC821FFBCE74067ED6F1AC196A4F745CC51566316CC16271910F595B7D2A821ADFB1B4D81D37DE0D0F | |||
| (PID) Process: | (2064) gamecenter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\3B1EFD3A66EA28B16697394703A72CA340A05BD5 |
| Operation: | write | Name: | Blob |
Value: 0F000000010000002000000008FBA831C08544208F5208686B991CA1B2CFC510E7301784DDF1EB5BF039323969000000010000000E000000300C060A2B0601040182373C03020B00000001000000540000004D006900630072006F0073006F0066007400200052006F006F007400200043006500720074006900660069006300610074006500200041007500740068006F0072006900740079002000320030003100300000000300000001000000140000003B1EFD3A66EA28B16697394703A72CA340A05BD52000000001000000F1050000308205ED308203D5A003020102021028CC3A25BFBA44AC449A9B586B4339AA300D06092A864886F70D01010B0500308188310B3009060355040613025553311330110603550408130A57617368696E67746F6E3110300E060355040713075265646D6F6E64311E301C060355040A13154D6963726F736F667420436F72706F726174696F6E31323030060355040313294D6963726F736F667420526F6F7420436572746966696361746520417574686F726974792032303130301E170D3130303632333231353732345A170D3335303632333232303430315A308188310B3009060355040613025553311330110603550408130A57617368696E67746F6E3110300E060355040713075265646D6F6E64311E301C060355040A13154D6963726F736F667420436F72706F726174696F6E31323030060355040313294D6963726F736F667420526F6F7420436572746966696361746520417574686F72697479203230313030820222300D06092A864886F70D01010105000382020F003082020A0282020100B9089E28E4E4EC064E5068B341C57BEBAEB68EAF81BA22441F6534694CBE704017F2167BE279FD86ED0D39F41BA8AD92901ECB3D768F5AD9B591102E3C058D8A6D2454E71FED56AD83B4509C15A51774885920FC08C58476D368D46F2878CE5CB8F3509044FFE3635FBEA19A2C961504D607FE1E8421E0423111C4283694CF50A4629EC9D6AB7100B25B0CE696D40A2496F5FFC6D5B71BD7CBB72162AF12DCA15D37E31AFB1A4698C09BC0E7631F2A0893027E1E6A8EF29F1889E42285A2B1845740FFF50ED86F9CEDE2453101CD17E97FB08145E3AA214026A172AAA74F3C01057EEE8358B15E06639962917882B70D930C246AB41BDB27EC5F95043F934A30F59718B3A7F919A793331D01C8DB22525CD725C946F9A2FB875943BE9B62B18D2D86441A46AC78617E3009FAAE89C4412A2266039139459CC78B0CA8CA0D2FFB52EA0CF76333239DFEB01FAD67D6A75003C6047063B52CB1865A43B7FBAEF96E296E21214126068CC9C3EEB0C28593A1B985D9E6326C4B4C3FD65DA3E5B59D77C39CC055B77400E3B838AB839750E19A42241DC6C0A330D11A5AC85234F773F1C7181F33AD7AECCB4160F3239420C24845AC5C51C62E80C2E27715BD8587ED369D9691EE00B5A370EC9FE38D80688376BAAF5D70522216E266FBBAB3C5C2F73E2F77A6CADEC1A6C6484CC3375123D327D7B84E7096F0A14476AF78CF9AE166130203010001A351304F300B0603551D0F040403020186300F0603551D130101FF040530030101FF301D0603551D0E04160414D5F656CB8FE8A25C6268D13D94905BD7CE9A18C4301006092B06010401823715010403020100300D06092A864886F70D01010B05000382020100ACA5968CBFBBAEA6F6D7718743315688FD1C32715B35B7D4F091F2AF37E214F1F30226053E16147F14BAB84FFB89B2B2E7D409CC6DB95B3B64657066B7F2B15ADF1A02F3F551B8676D79F3BF567BE484B92B1E9B409C2634F947189869D81CD7B6D1BF8F61C267C4B5EF60438E101B3649E420CAADA7C1B1276509F8CDF55B2AD08433F3EF1FF2F59C0B589337A075A0DE72DE6C752A6622F58C0630569F40B930AA40771582D78BECC0D3B2BD83C5770C1EAEAF1953A04D79719F0FAF30CE67F9D62CCC22417A07F2974218CE59791055DE6F10E4B8DA836640160968235B972E269A02BB578CC5B8BA69623280899EA1FDC0927C7B2B3319842A63C5006862FA9F478D997A453AA7E9EDEE6942B5F3819B4756107BFC7036841873EAEFF9974D9E3323DD260BBA2AB73F44DC8327FFBD61592B11B7CA4FDBC58B0C1C31AE32F8F8B942F77FDC619A76B15A04E1113D6645B71871BEC92485D6F3D4BA41345D122D25B98DA613486D4BB0077D99930961817457268AAB69E3E4D9C788CC24D8EC52245C1EBC9114E296DEEB0ADA9EDD5FB35BDBD482ECC620508725403AFBC7EECDFE33E56EC3840955032539C0E9355D6531A8F6BFA009CD29C7B336322EDC95F383C15ACF8B8DF6EAB321F8A4ED1E310EB64C11AB600BA412232217A3366482910412E0AB6F1ECB500561B440FF598671D1D533697CA9738A38D7640CF169 | |||
| (PID) Process: | (2064) gamecenter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\245C97DF7514E7CF2DF8BE72AE957B9E04741E85 |
| Operation: | write | Name: | Blob |
Value: 0F00000001000000100000009DF0D13100123AECA770130F4AD8D209030000000100000014000000245C97DF7514E7CF2DF8BE72AE957B9E04741E8509000000010000000C000000300A06082B060105050703080B00000001000000320000004D006900630072006F0073006F00660074002000540069006D0065007300740061006D007000200052006F006F00740000002000000001000000B1020000308202AD30820216020101300D06092A864886F70D010104050030819E3120301E060355040A13174D6963726F736F6674205472757374204E6574776F726B311E301C060355040B13154D6963726F736F667420436F72706F726174696F6E312D302B060355040B13244D6963726F736F66742054696D65205374616D70696E67205365727669636520526F6F74312B3029060355040B1322436F70797269676874202863292031393937204D6963726F736F667420436F72702E301E170D3937303531333136313235395A170D3939313233303233353935395A30819E3120301E060355040A13174D6963726F736F6674205472757374204E6574776F726B311E301C060355040B13154D6963726F736F667420436F72706F726174696F6E312D302B060355040B13244D6963726F736F66742054696D65205374616D70696E67205365727669636520526F6F74312B3029060355040B1322436F70797269676874202863292031393937204D6963726F736F667420436F72702E30819F300D06092A864886F70D010101050003818D0030818902818100B75A38F51F37CCA943C4DC2418BEF28552B41D5B5F18B90B8F4B6DA8FFCD40506CD3A0D35C47C2B9F786E4CD7D350569371FAF3DDD1FFD8F1534C2C479CC59748A6F8C0EC3E811EB8438479853E1F10C0DE4010CF01B1E20DA2A7A3DC215528E8AFF7B32BF581E25988326CB8AC9C4071424BC499ED77AB3871A2533BC6D08470203010001300D06092A864886F70D010104050003818100505BC56B6F8D525B0DC9BDAC347398CA0A87CAAE4C4ABA14A4EB52709521E0B5A1604EF743025101AF1E3A70CEBF18B686289967EB08E897405C1682FDB825FB366F6F763EC54C8EE2A751FACAC163BA5E8324470B9372F6449ACEA7953A8F50109E1DB15916ABCF3EDF838BC7FAC36BDC649F402B1F452404AE492FF6DF0C91 | |||
| (PID) Process: | (2064) gamecenter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\18F7C1FCC3090203FD5BAA2F861A754976C8DD25 |
| Operation: | write | Name: | Blob |
Value: 0F000000010000001000000065FC47520F66383962EC0B7B88A0821D03000000010000001400000018F7C1FCC3090203FD5BAA2F861A754976C8DD2509000000010000000C000000300A06082B060105050703080B000000010000003400000056006500720069005300690067006E002000540069006D00650020005300740061006D00700069006E00670020004300410000002000000001000000C0020000308202BC3082022502104A19D2388C82591CA55D735F155DDCA3300D06092A864886F70D010104050030819E311F301D060355040A1316566572695369676E205472757374204E6574776F726B31173015060355040B130E566572695369676E2C20496E632E312C302A060355040B1323566572695369676E2054696D65205374616D70696E67205365727669636520526F6F7431343032060355040B132B4E4F204C494142494C4954592041434345505445442C20286329393720566572695369676E2C20496E632E301E170D3937303531323030303030305A170D3034303130373233353935395A30819E311F301D060355040A1316566572695369676E205472757374204E6574776F726B31173015060355040B130E566572695369676E2C20496E632E312C302A060355040B1323566572695369676E2054696D65205374616D70696E67205365727669636520526F6F7431343032060355040B132B4E4F204C494142494C4954592041434345505445442C20286329393720566572695369676E2C20496E632E30819F300D06092A864886F70D010101050003818D0030818902818100D32E20F0687C2C2D2E811CB106B2A70BB7110D57DA53D875E3C9332AB2D4F6095B34F3E990FE090CD0DB1B5AB9CDE7F688B19DC08725EB7D5810736A78CB7115FDC658F629AB585E9604FD2D621158811CCA7194D522582FD5CC14058436BA94AAB44D4AE9EE3B22AD56997E219C6C86C04A47976AB4A636D5FC092DD3B4399B0203010001300D06092A864886F70D01010405000381810061550E3E7BC792127E11108E22CCD4B3132B5BE844E40B789EA47EF3A707721EE259EFCC84E389944CDB4E61EFB3A4FB463D50340B9F7056F68E2A7F17CEE563BF796907732EB095288AF5EDAAA9D25DCD0ACA10098FCEB3AF2896C479298492DCFFBA674248A69010E4BF61F89C53E593D1733FF8FD9D4F84AC55D1FD116363 | |||
Executable files
234
Suspicious files
116
Text files
1 589
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2064 | gamecenter.exe | C:\test.tmp | — | |
MD5:— | SHA256:— | |||
| 2064 | gamecenter.exe | C:\Temp\TxGameDownload\Component\AppMarket\Market.exe | — | |
MD5:— | SHA256:— | |||
| 3932 | Market.exe | C:\Temp\TxGameDownload\Component\AppMarket\Setup\AowGame.xml | text | |
MD5:34A4AAF787D9308C043FE022D513FF31 | SHA256:D41553986FDA3E5C64AB02C498677CB294735891A76C5CF2AC23D5267A6D0A5B | |||
| 3932 | Market.exe | C:\Temp\TxGameDownload\Component\AppMarket\Setup\AECommonDll.dll | executable | |
MD5:CE9B3E164648FAEFAE1D39890570DB95 | SHA256:0DD924ECE23DDD41CED23D43D13E87C6AF4BA8EC7DDF494290F7CE71DFFC4813 | |||
| 2064 | gamecenter.exe | C:\Users\admin\AppData\Roaming\Tencent\DeskUpdate\GlobalMgr.db | text | |
MD5:583BA5AA3F6EC3DF8E58DB6AA6AEB789 | SHA256:BF9D9B1B0AA4F9EF5D775F4BA409BF3D69556E77EADFBA20E371B980ED77C8AA | |||
| 2064 | gamecenter.exe | C:\Users\admin\AppData\Local\Temp\TGBDownload\A1FB.tmp | xml | |
MD5:CCEB2187E19C4E612E9DEFA699325F2D | SHA256:802AFD97BC967CF54296D82EF94A17F30D36D574FFCE81EDF7D69B2824586FD6 | |||
| 3932 | Market.exe | C:\Temp\TxGameDownload\Component\AppMarket\Setup\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:11E55839FCB3A53BDFED2A27FB7D5E80 | SHA256:F6BDC8FFD172B44F4D169707D9A457AEEF619872661229B8629EE4F15EEFFF0D | |||
| 3932 | Market.exe | C:\Temp\TxGameDownload\Component\AppMarket\Setup\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:D826D27C73D9F2420FB39FBE0745C7F0 | SHA256:C0E5D482BD93BF71A73C01D0C1EC0722EA3260EBA1F4C87E797BAE334B5E9870 | |||
| 3932 | Market.exe | C:\Temp\TxGameDownload\Component\AppMarket\Setup\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:EC4F2CB68DCF7E96516EB284003BE8BB | SHA256:3816BBB7DD76D8FC6A7B83A0ED2F61B23DD5FC0843D3308EE077CB725D5C9088 | |||
| 3932 | Market.exe | C:\Temp\TxGameDownload\Component\AppMarket\Setup\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:9F3CF9F22836C32D988D7C7E0A977E1B | SHA256:7D588A5A958E32875D7BD346D1371E6EBFD9D5D2EDE47755942BADFC9C74E207 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
143
DNS requests
95
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1460 | AppMarket.exe | POST | 200 | 203.205.255.80:8080 | http://wup.imtt.qq.com:8080/?encrypt=17&len=1024&v=3&iv=11db22a0352040e7&id=a690d5f54b43ca535af266c3180769c7&qbkey=7B3DFFE8B9EAD7CCB529EFDC79569235E76C357BB0BFCB54F9DC04D1137858834D92F398EEA0426BCF0617533A4361CC256FD9682743BF07CE7E199BEFA68C93977C60F153375AA544A87FF09820FE2567B69B43E0E40A2BF016F158D34767F8C70E5E6404F9A70D8B88330F957EC6E6735B16CCB83BFBF1F9D70BF2234914FA | CN | binary | 160 b | suspicious |
1460 | AppMarket.exe | POST | — | 183.62.104.184:80 | http://masterconn.qq.com/q.cgi | CN | — | — | unknown |
1460 | AppMarket.exe | POST | 200 | 203.205.255.80:8080 | http://wup.imtt.qq.com:8080/?encrypt=17&len=1024&v=3&iv=04f945cfd85b4bc1&id=a690d5f54b43ca535af266c3180769c7&qbkey=0C2B5CFAD3FA112934CCB55782F409057CDF73C38655B6C893ED53C3C2F8A832D16DC181F1A4F69915501E1628B7DFFF24D8EB8558884D2A7B4BF8CC72043DABD6B6F4EED9E40C620F31EE0DECAA823D44C8C988AB78F399905CA1F8F06B8655692C13DE184D63D8A2539225C35A86799CDB2B0A350A06D7ACEE170ED93CE189 | CN | binary | 112 b | suspicious |
2064 | gamecenter.exe | GET | 200 | 104.123.50.122:80 | http://dldir1.qq.com/syzs/oversea_component/Market_3.11.377.100.dat | US | executable | 58.4 Mb | whitelisted |
1460 | AppMarket.exe | POST | — | 183.62.104.184:80 | http://masterconn.qq.com/q.cgi | CN | — | — | unknown |
1460 | AppMarket.exe | POST | — | 183.62.104.184:80 | http://masterconn.qq.com/q.cgi | CN | — | — | unknown |
— | — | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/gsorganizationvalsha2g2/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQMnk2cPe3vhNiR6XLHz4QGvBl7BwQUlt5h8b0cFilTHMDMfTuDAEDmGnwCDHGQKtP62BOm98s81w%3D%3D | US | der | 1.54 Kb | whitelisted |
1460 | AppMarket.exe | POST | — | 183.62.104.184:80 | http://masterconn.qq.com/q.cgi | CN | — | — | unknown |
1460 | AppMarket.exe | POST | — | 123.151.71.34:80 | http://masterconn.qq.com/q.cgi | CN | — | — | unknown |
1460 | AppMarket.exe | GET | 200 | 203.205.137.182:80 | http://pm.myapp.com/invc/xfspeed/qqpcmgr/module_update/emulator/keymap//585c305d644afe27efe70b786743e963_AowGame.xml | CN | text | 11.6 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2064 | gamecenter.exe | 87.245.210.7:443 | s.syzs.qq.com | RETN Limited | GB | unknown |
2064 | gamecenter.exe | 58.251.106.185:443 | masterconn11.qq.com | China Unicom Guangdong IP network | CN | malicious |
2064 | gamecenter.exe | 113.105.95.120:443 | — | China Telecom (Group) | CN | malicious |
2064 | gamecenter.exe | 104.123.50.122:80 | dldir1.qq.com | Akamai Technologies, Inc. | US | suspicious |
1852 | Tinst.exe | 87.245.210.7:443 | s.syzs.qq.com | RETN Limited | GB | unknown |
2064 | gamecenter.exe | 125.39.120.82:443 | — | CHINA UNICOM China169 Backbone | CN | malicious |
1460 | AppMarket.exe | 58.251.106.185:443 | masterconn11.qq.com | China Unicom Guangdong IP network | CN | malicious |
3244 | QMEmulatorService.exe | 58.251.106.185:443 | masterconn11.qq.com | China Unicom Guangdong IP network | CN | malicious |
1460 | AppMarket.exe | 203.205.255.80:8080 | master.etl.desktop.qq.com | — | CN | suspicious |
1460 | AppMarket.exe | 183.62.104.184:8000 | — | China Telecom (Group) | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
master.etl.desktop.qq.com |
| whitelisted |
s.syzs.qq.com |
| suspicious |
dldir1.qq.com |
| whitelisted |
masterconn11.qq.com |
| whitelisted |
wup.imtt.qq.com |
| suspicious |
sy.guanjia.qq.com |
| whitelisted |
masterconn.qq.com |
| whitelisted |
syzs.qq.com |
| unknown |
s.gameloop.fun |
| suspicious |
pingjs.qq.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1460 | AppMarket.exe | Unknown Traffic | ET INFO Suspicious User-Agent (1 space) |
1460 | AppMarket.exe | Unknown Traffic | ET INFO Suspicious User-Agent (1 space) |
4008 | TenioDL.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag false) |
4008 | TenioDL.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag true change port flag false) |
4008 | TenioDL.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag true) |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
AppMarket.exe | [0512/185436:INFO:exception_record.cc(518)] [QB]Process ID: 1460 Type: 1
|
AppMarket.exe | [Downloader] DriverType C: = 3 |
AppMarket.exe | [Downloader] GetLogicalDrives 4 |
TBSWebRenderer.exe | [0512/185438:INFO:exception_record.cc(518)] [QB]Process ID: 3580 Type: 2
|
AppMarket.exe | [0512/185441:INFO:http_cache_transaction.cc(72)] IgnoreZeroCacheError: 0
|
GameDownload.exe | [Downloader] GetLogicalDrives 4
|
GameDownload.exe | [Downloader] DriverType C: = 3
|
GameDownload.exe | [Downloader] DriverType C: = 3
|
GameDownload.exe | [Downloader] GetLogicalDrives 4
|
TenioDL.exe | Open AppMarket Register Path Failed. ErrorCode[2] |