| download: | pfsetup.exe |
| Full analysis: | https://app.any.run/tasks/7f30f4bb-392c-4a08-9c4e-71d843c5d27a |
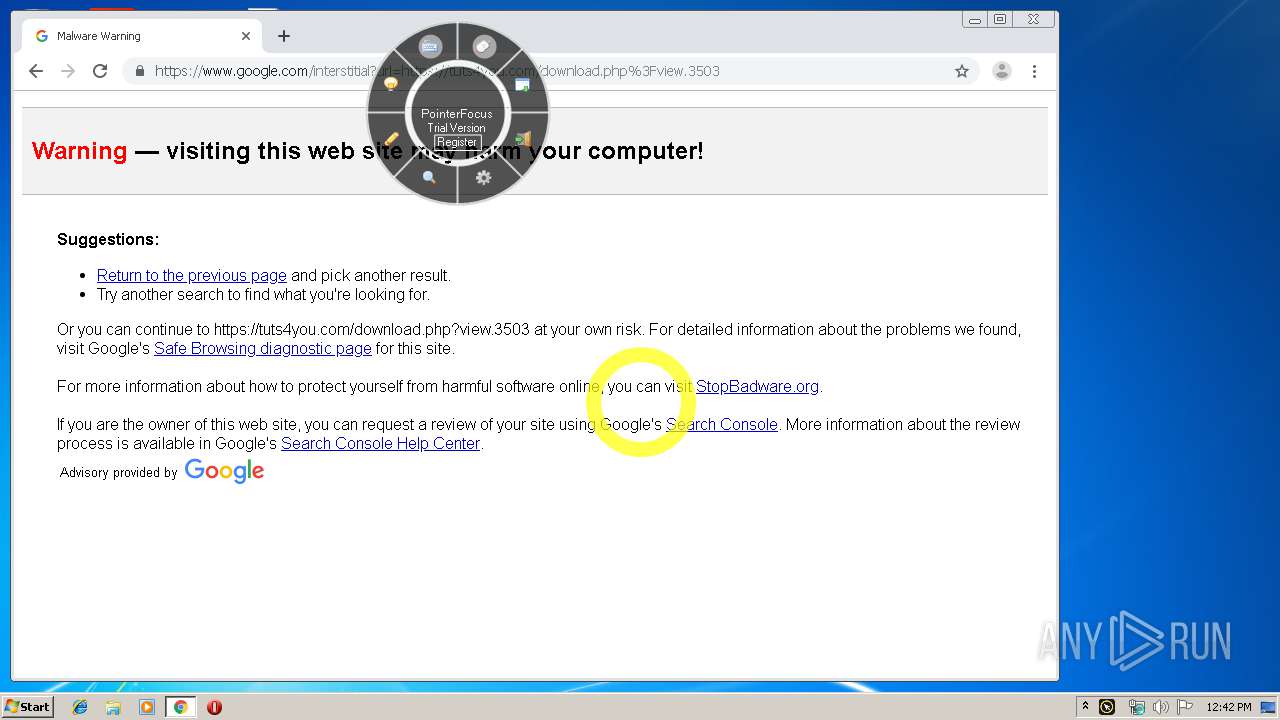
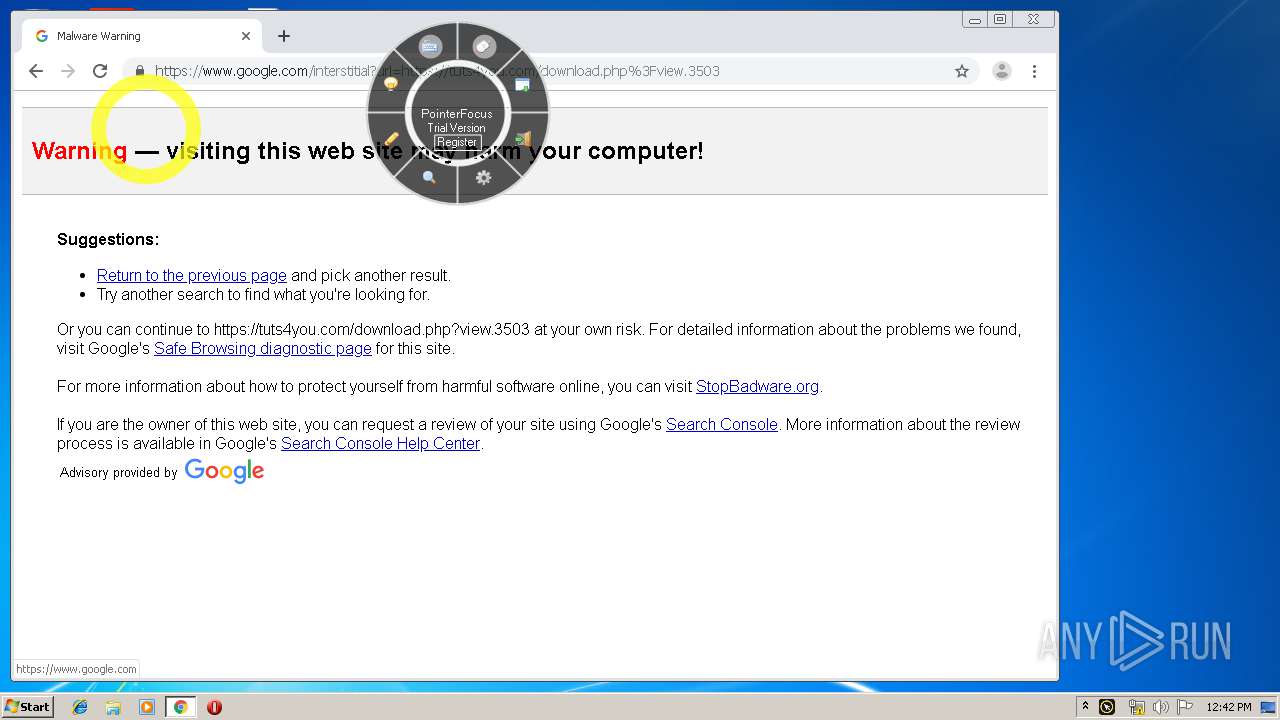
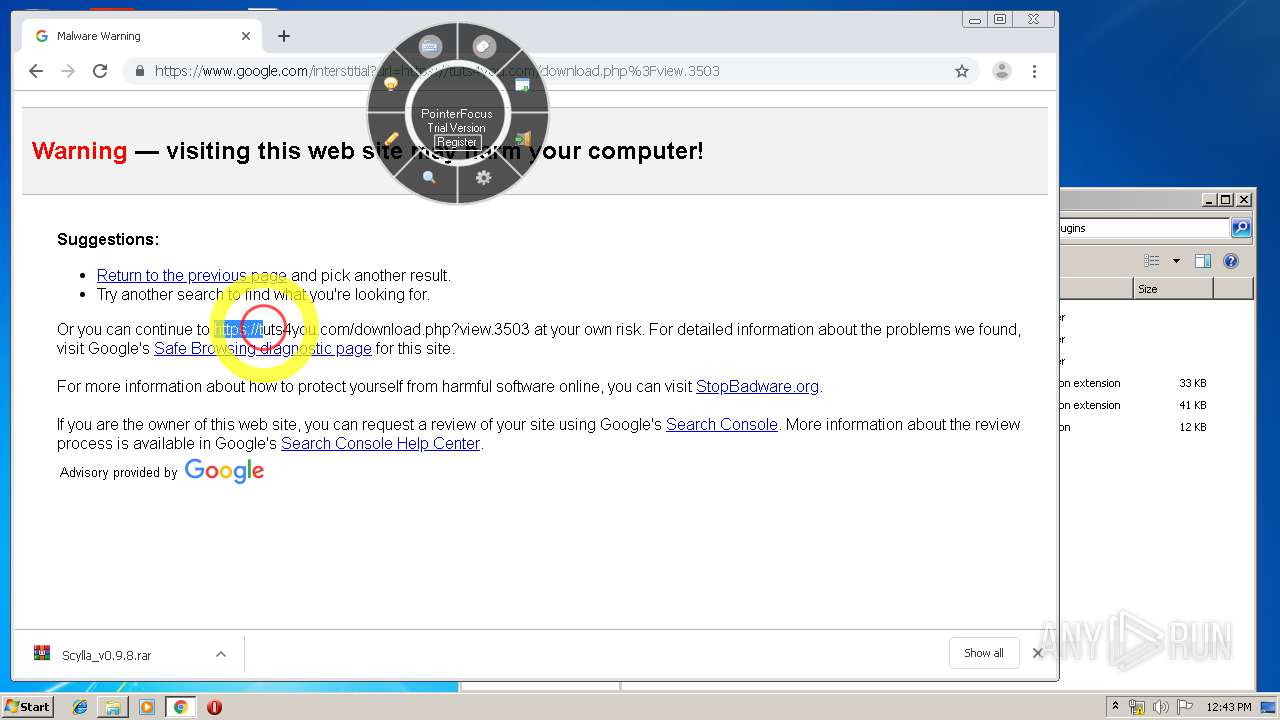
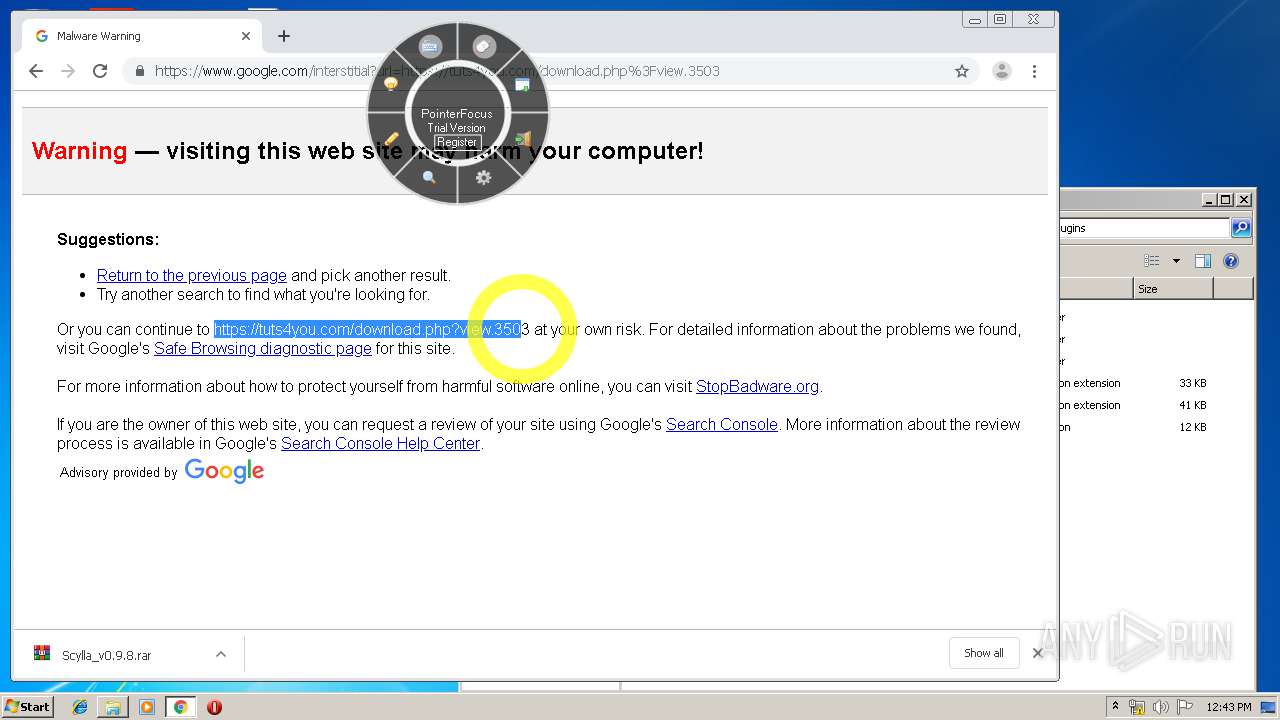
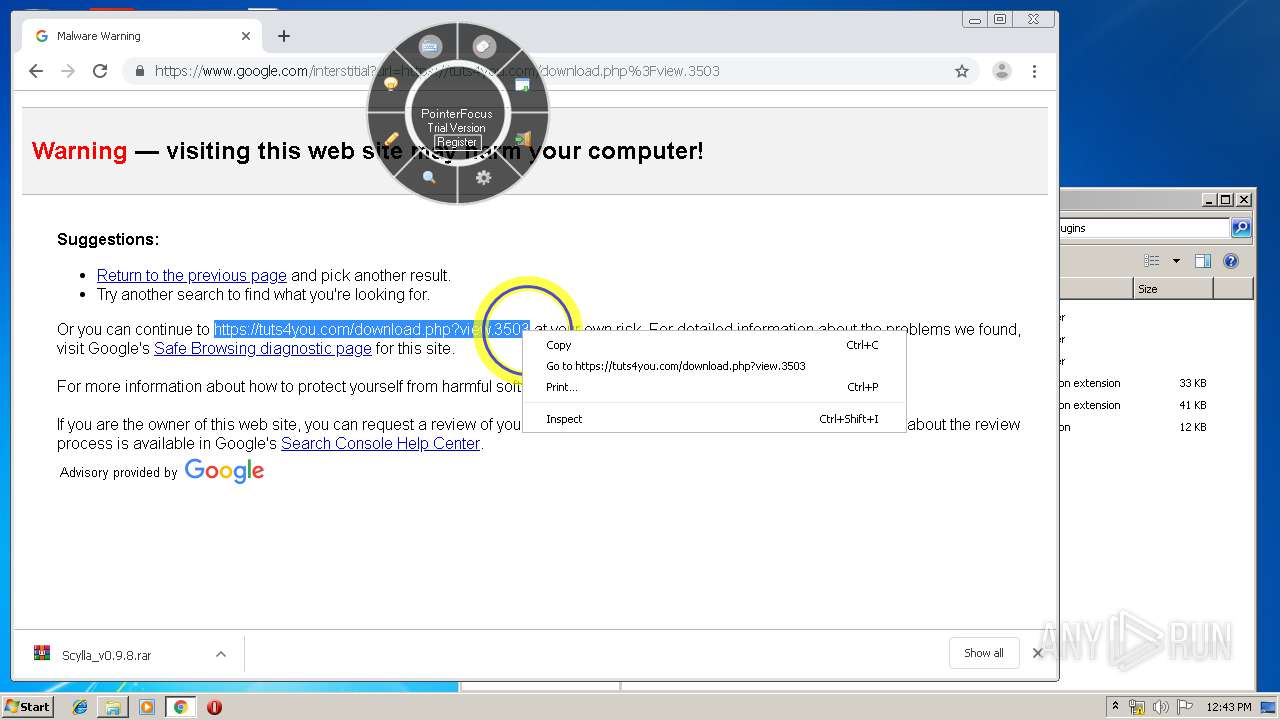
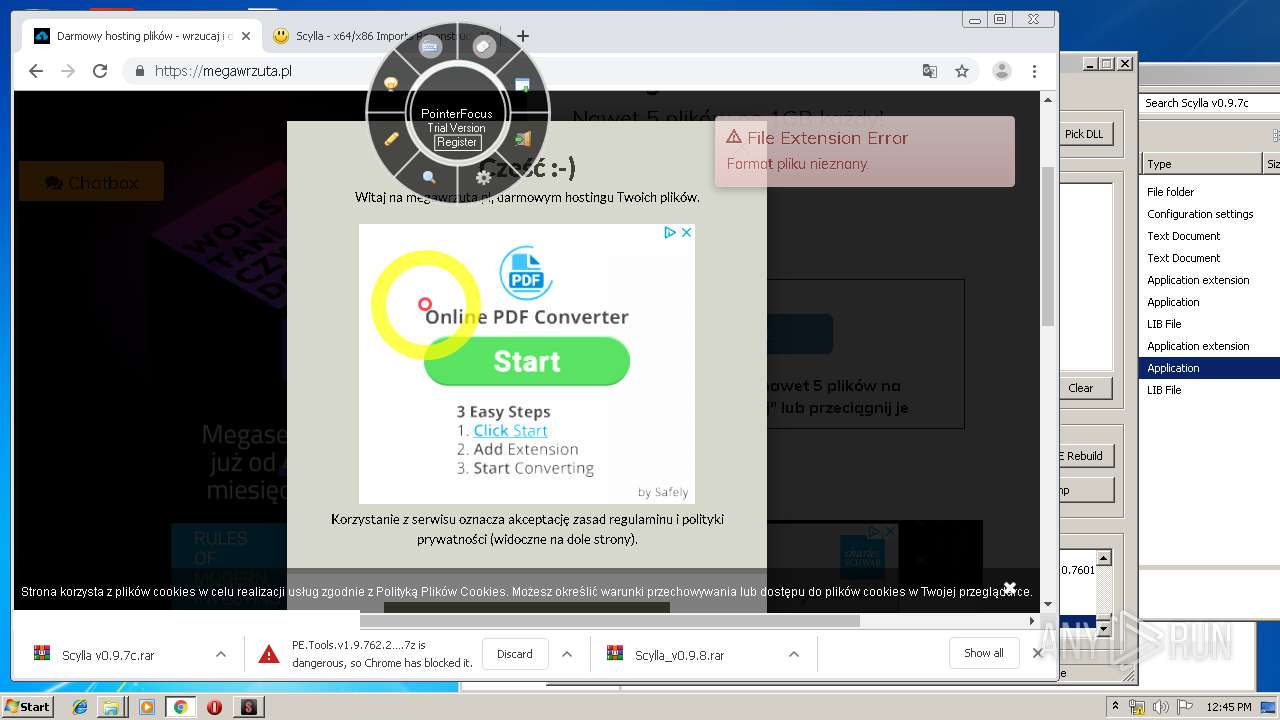
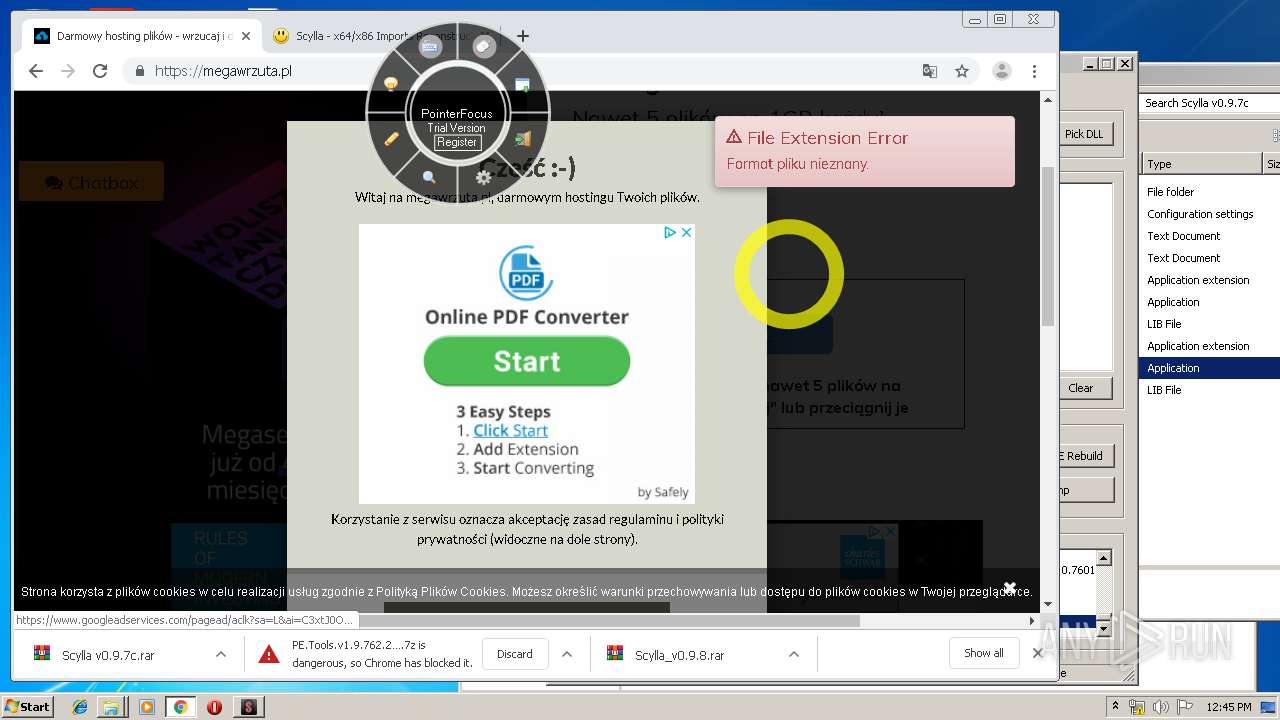
| Verdict: | Malicious activity |
| Analysis date: | July 04, 2019, 11:41:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | ED1C84573853CA34DA7D0C5E754D6A0A |
| SHA1: | 039DFEED52A703FCCD54BD67B68491903A4FEB4C |
| SHA256: | 3829EA252A6C4905CE0154EC51967E403ABB19EFA29BD227EB8028241C27650A |
| SSDEEP: | 12288:c37h6c4888888888888W88888888888UVSAHt+zqPUY0W/UFMC61T03m3y5M63yW:i7htVSazUF7W5j6CeJkkEOQy5 |
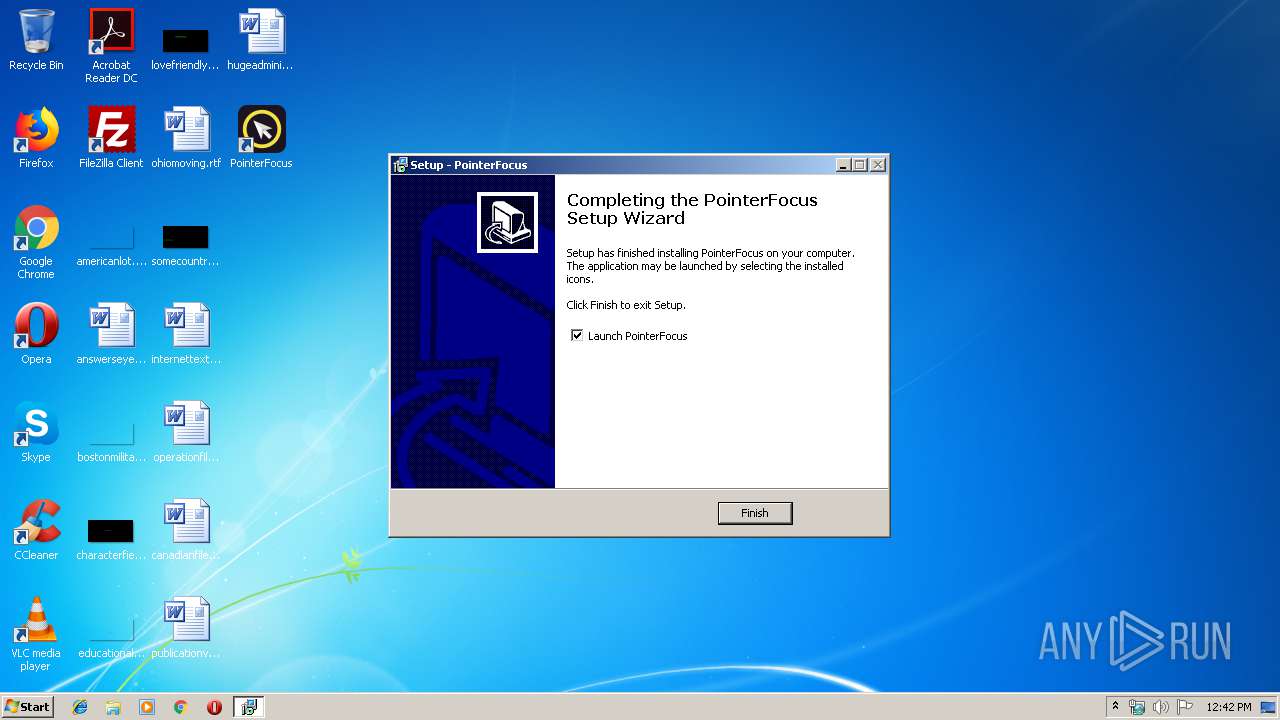
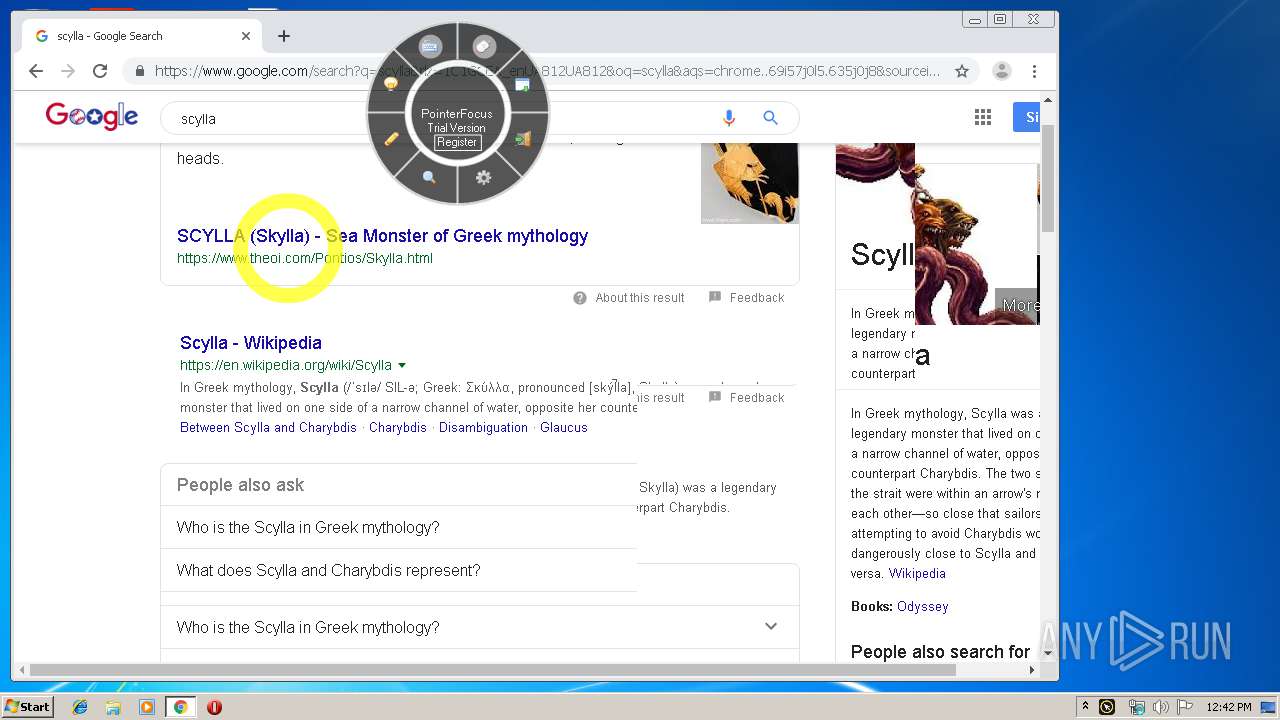
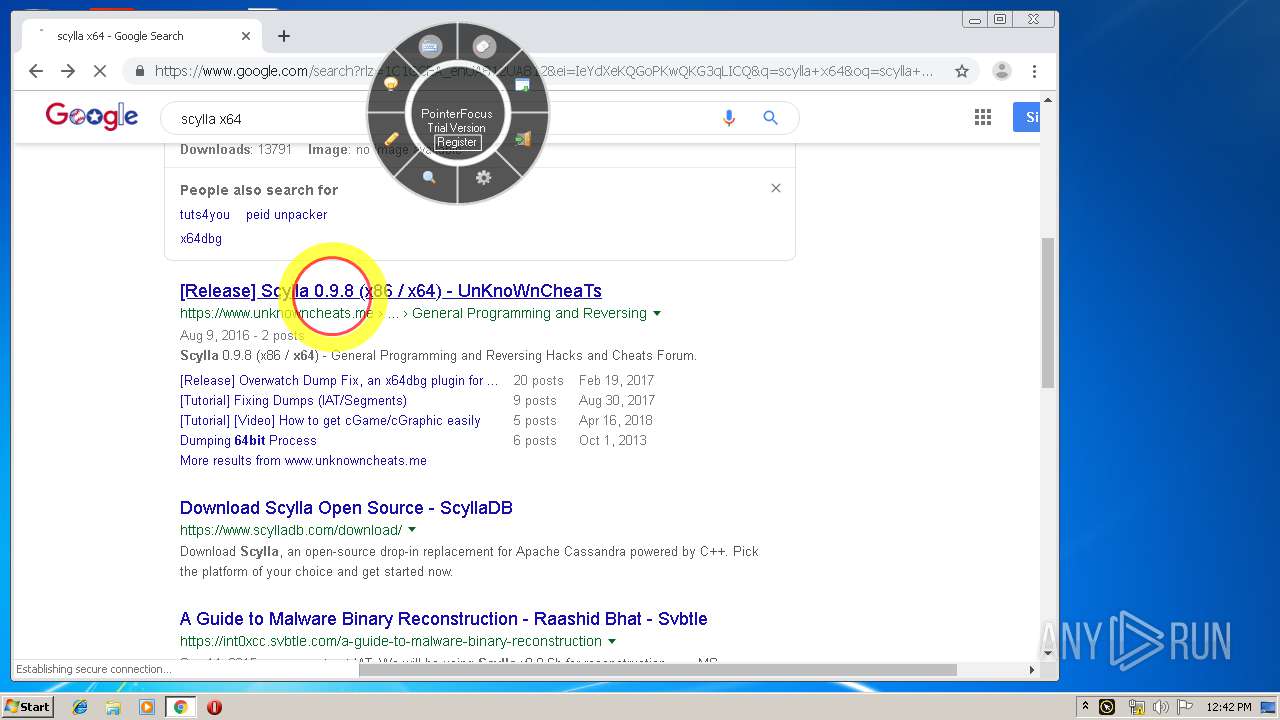
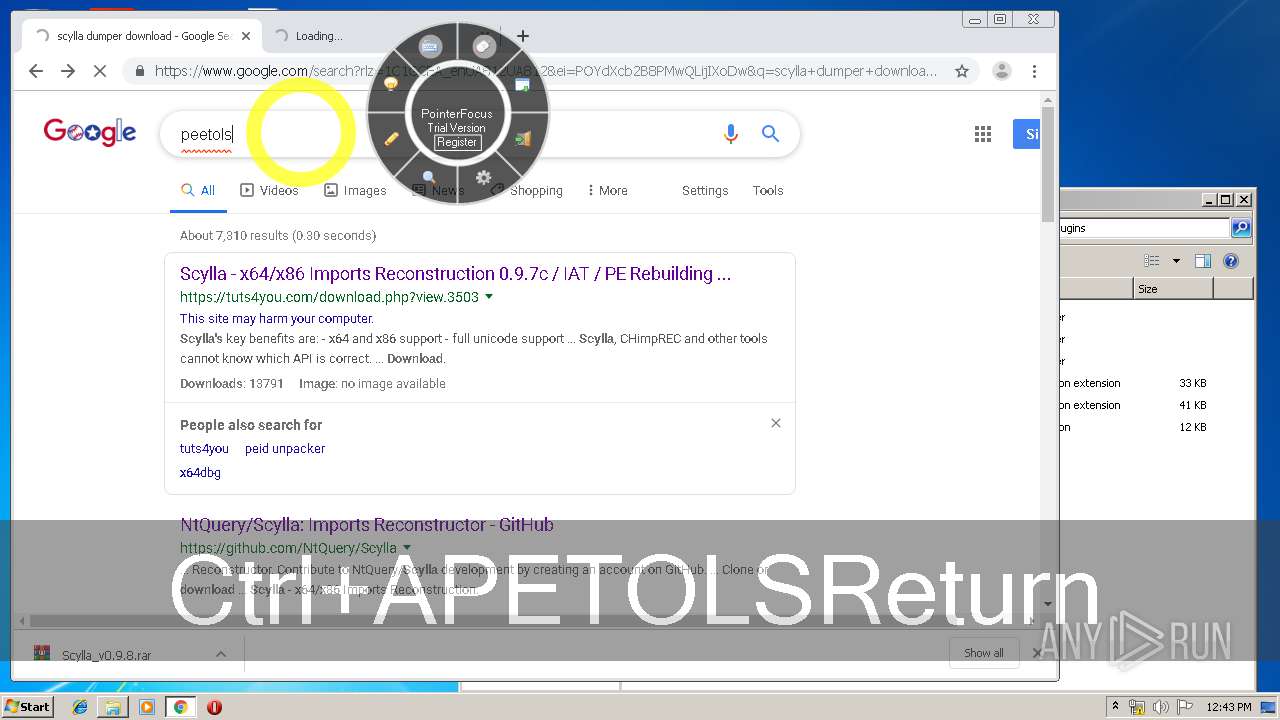
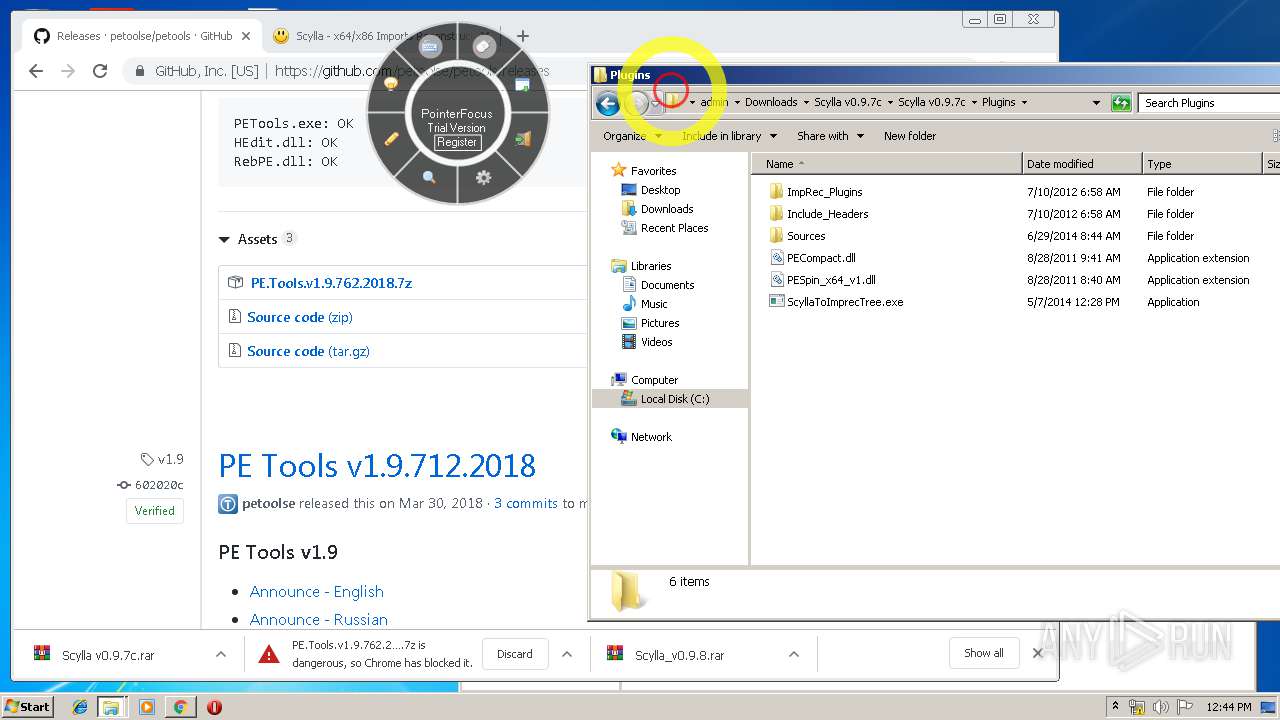
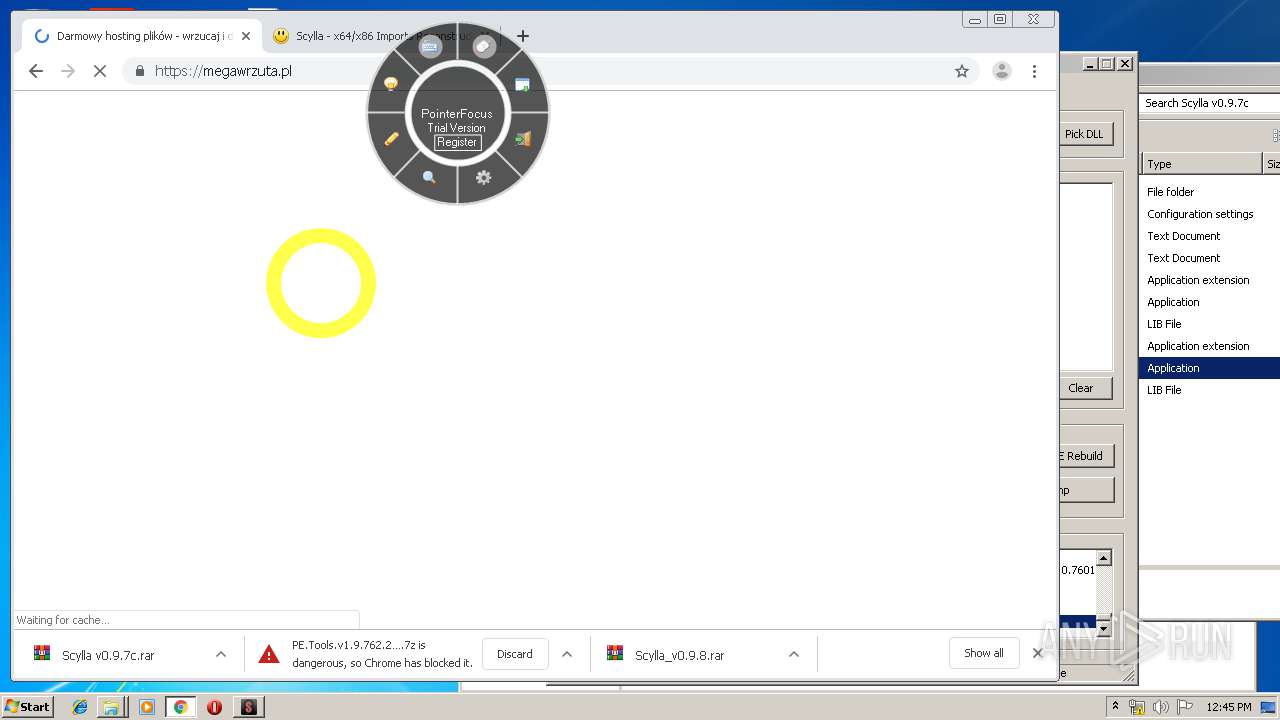
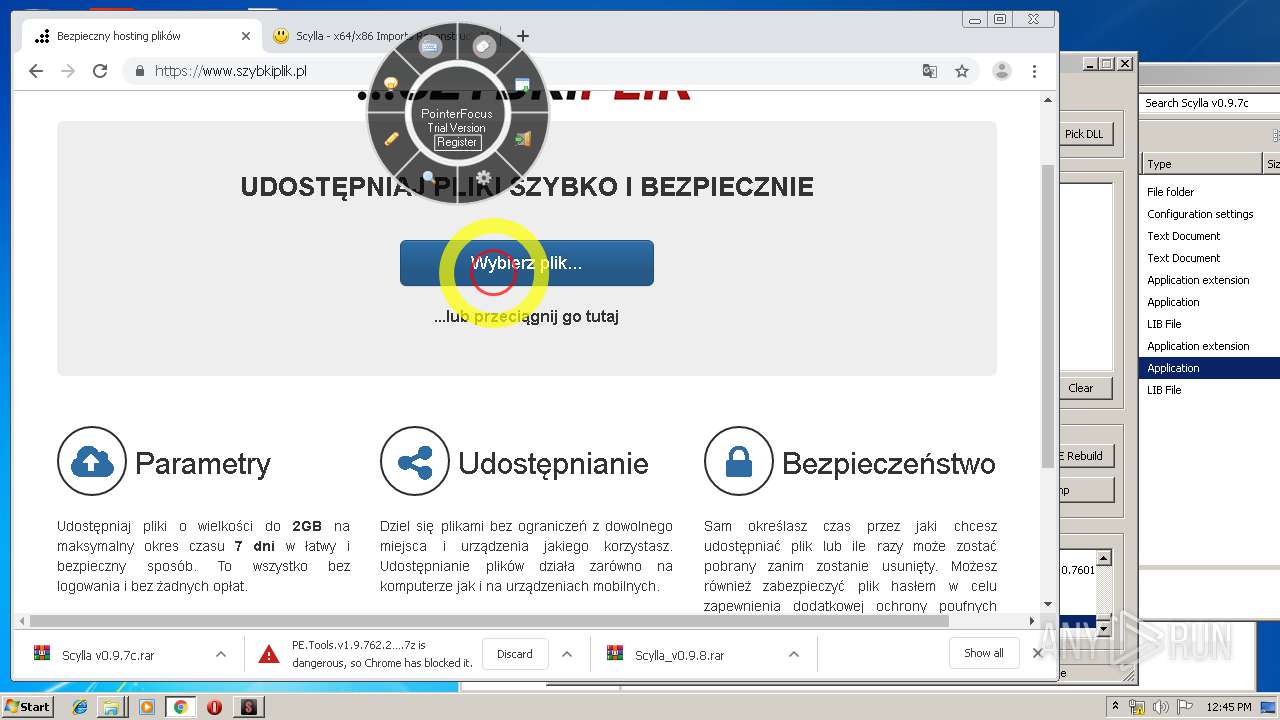
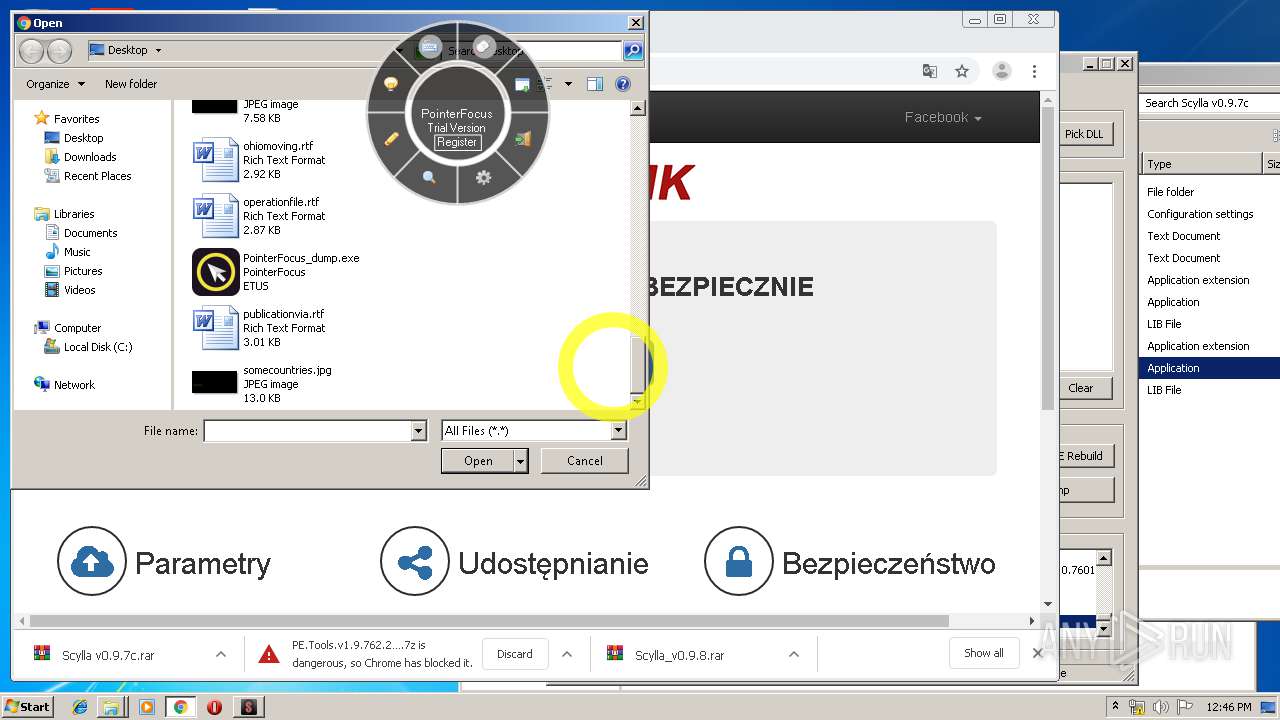
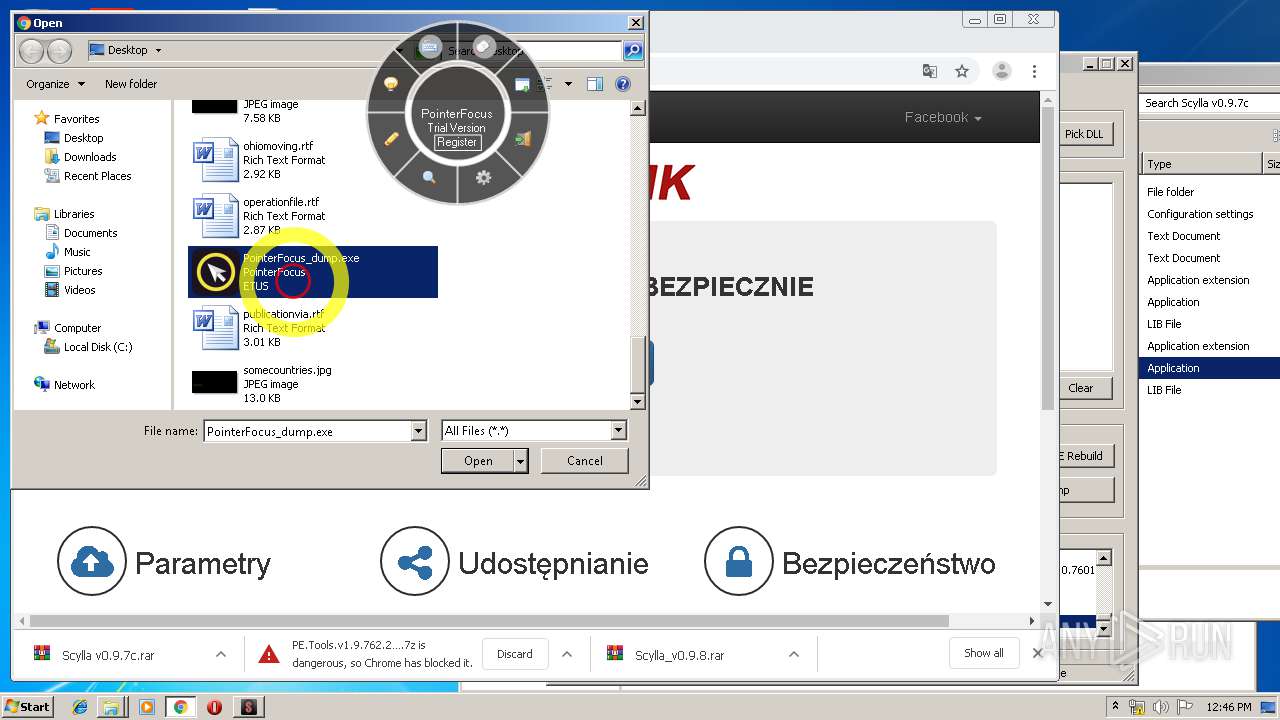
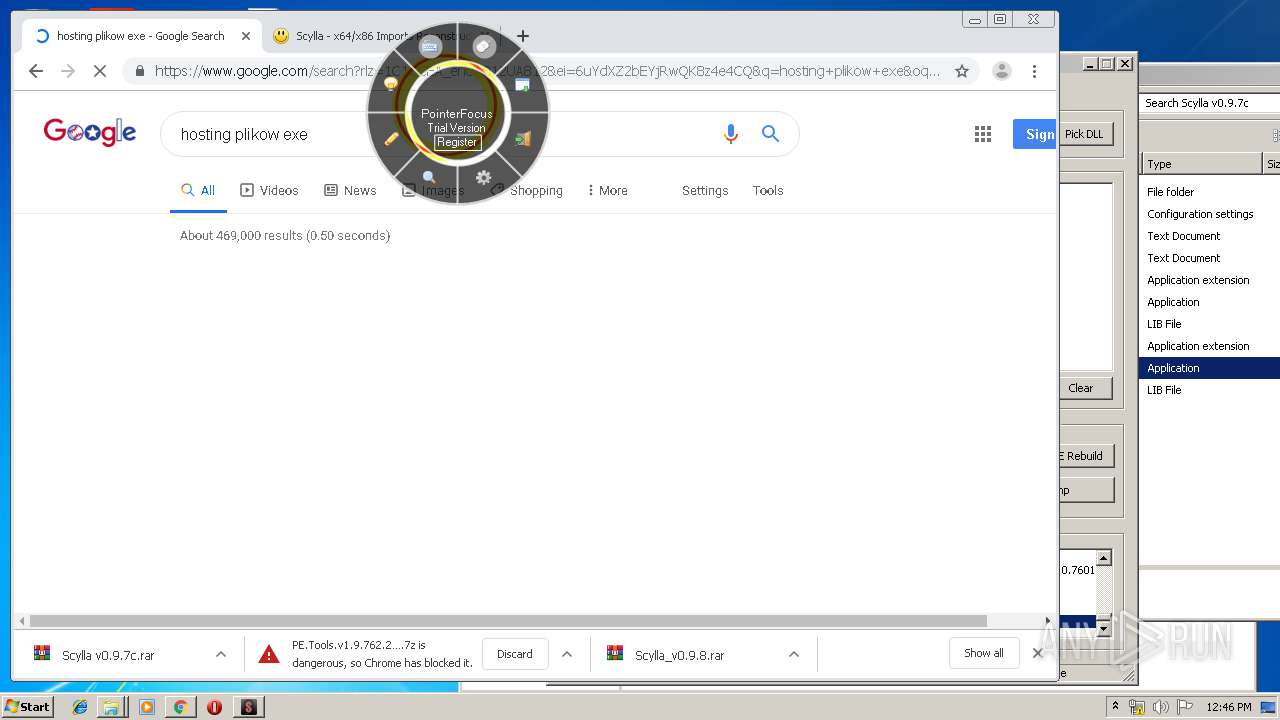
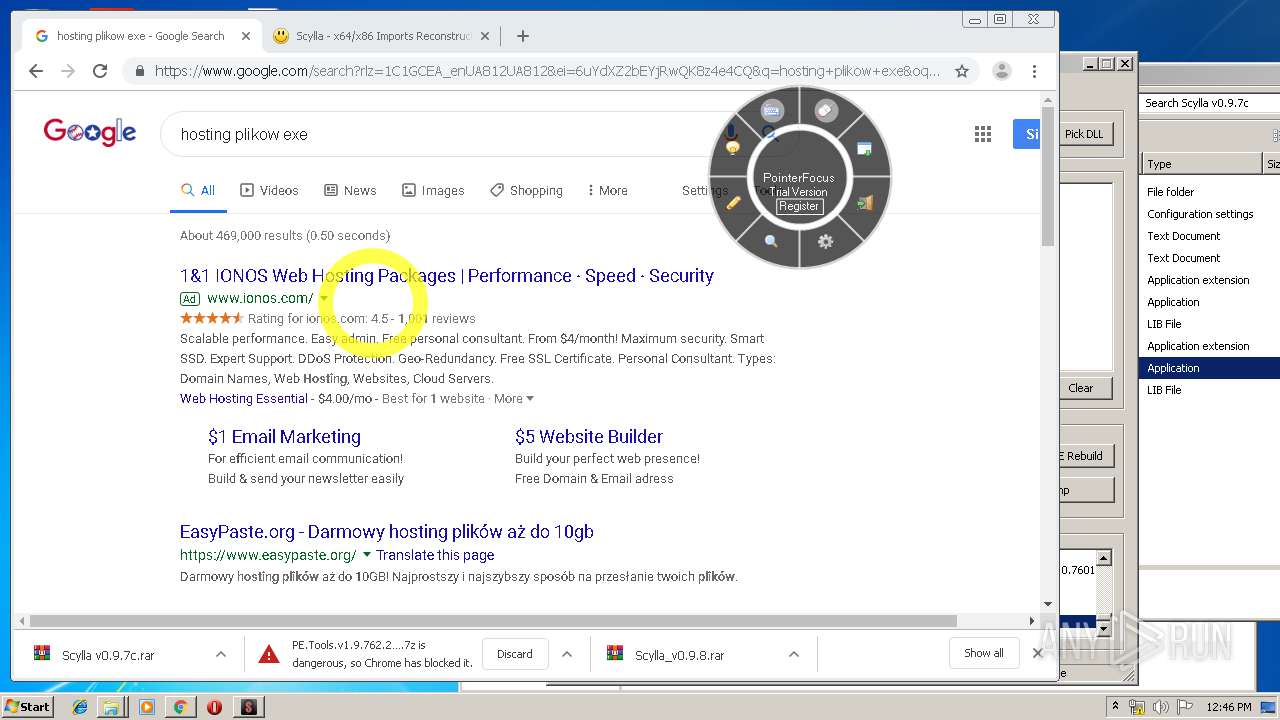
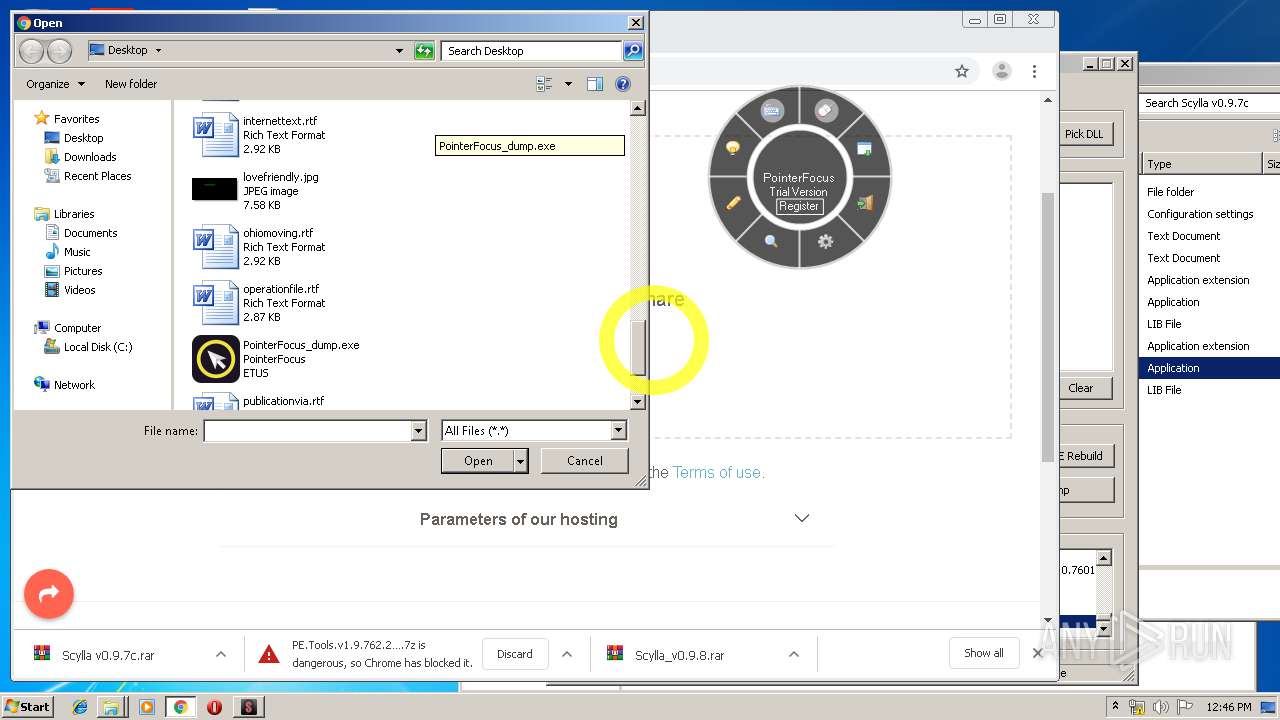
MALICIOUS
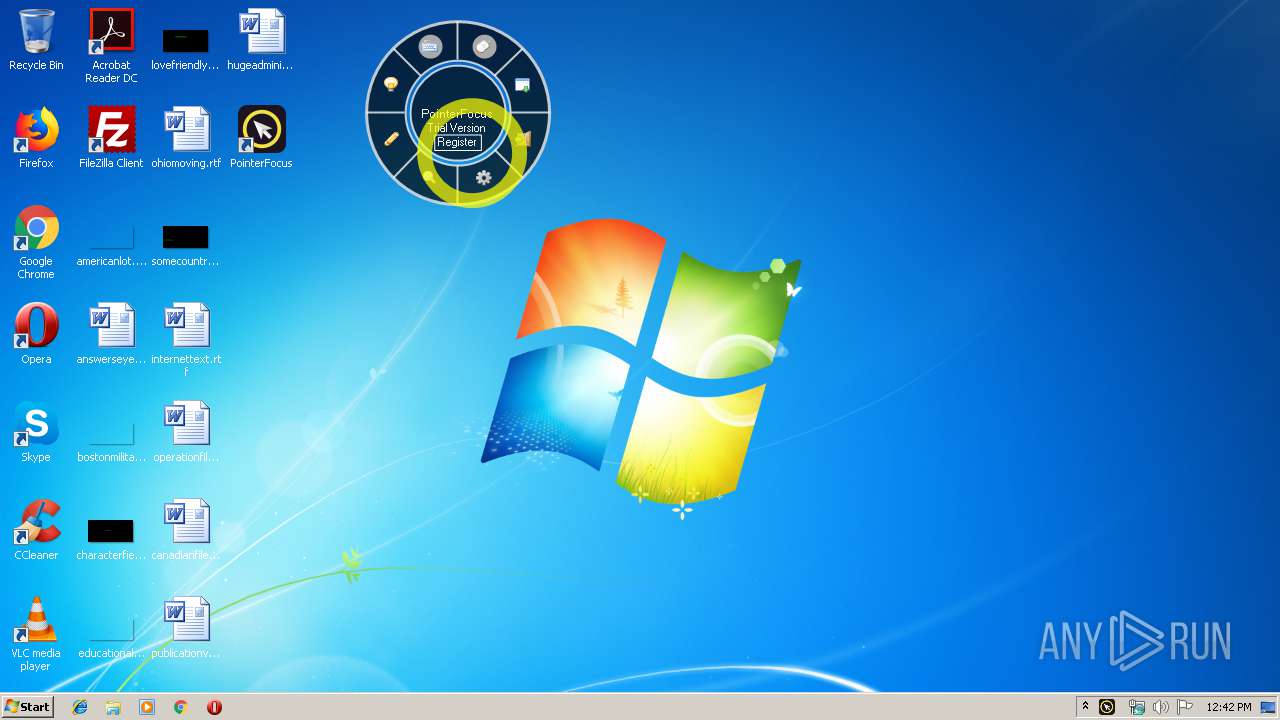
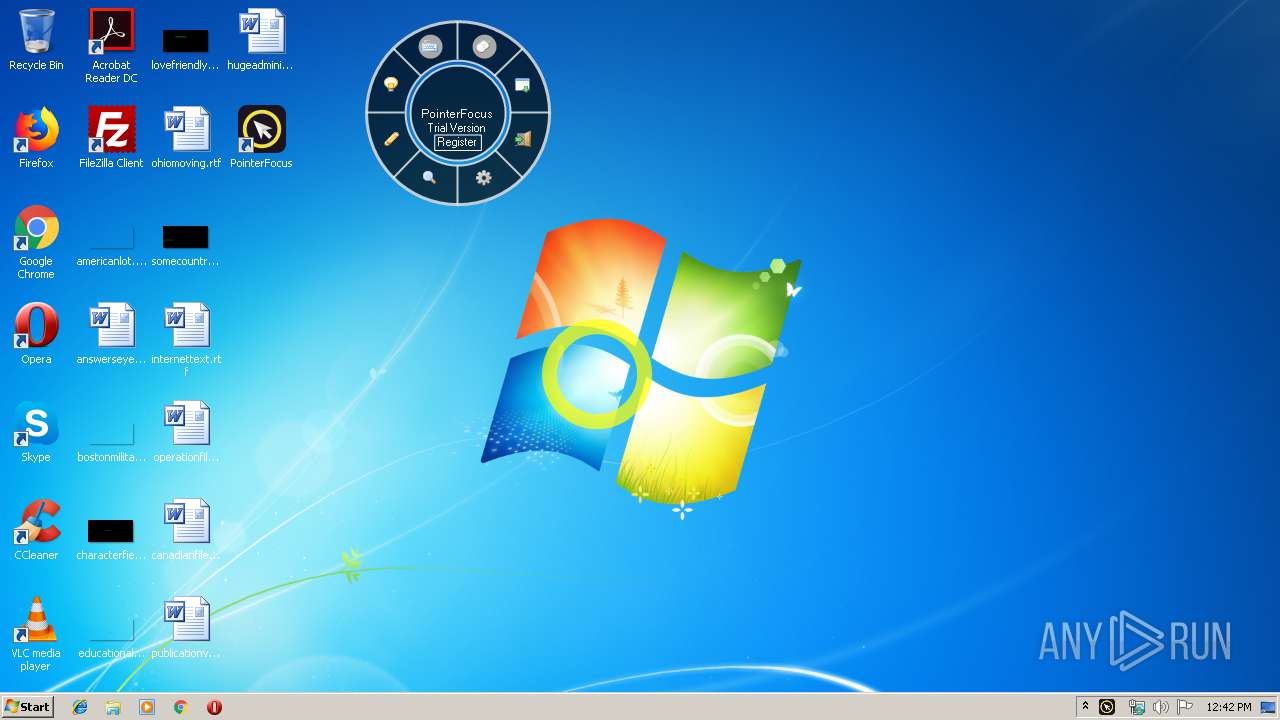
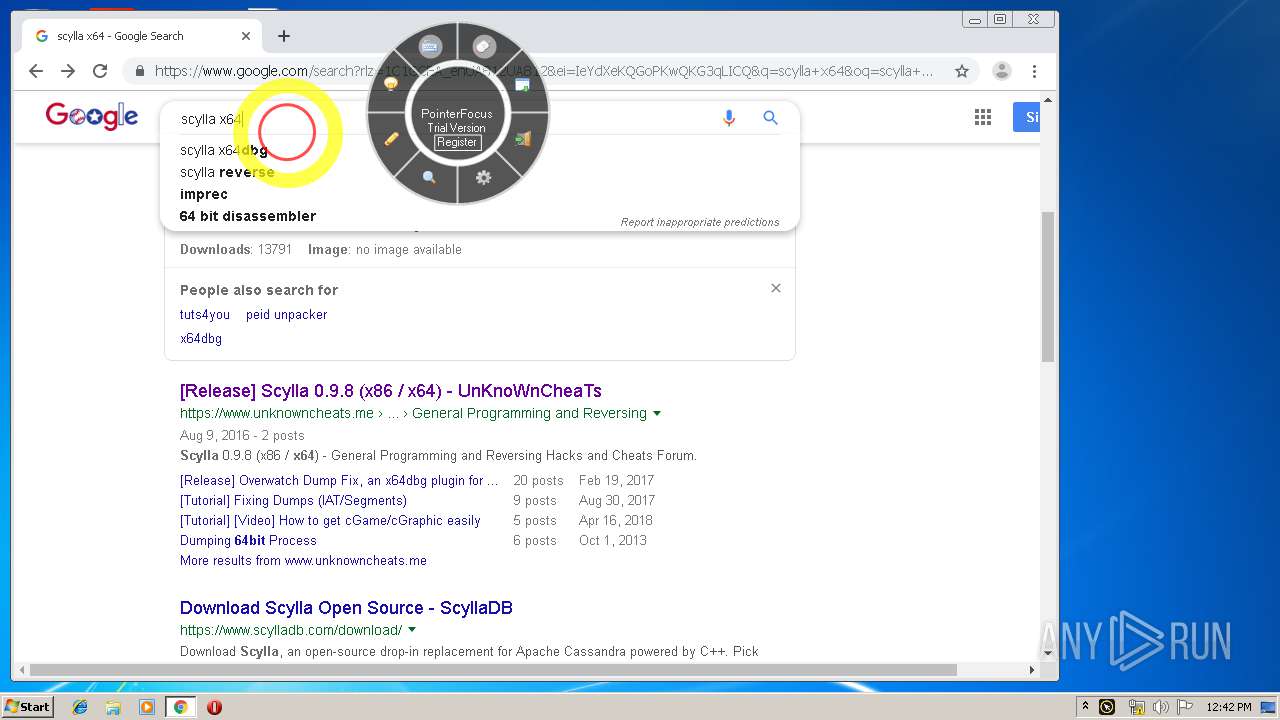
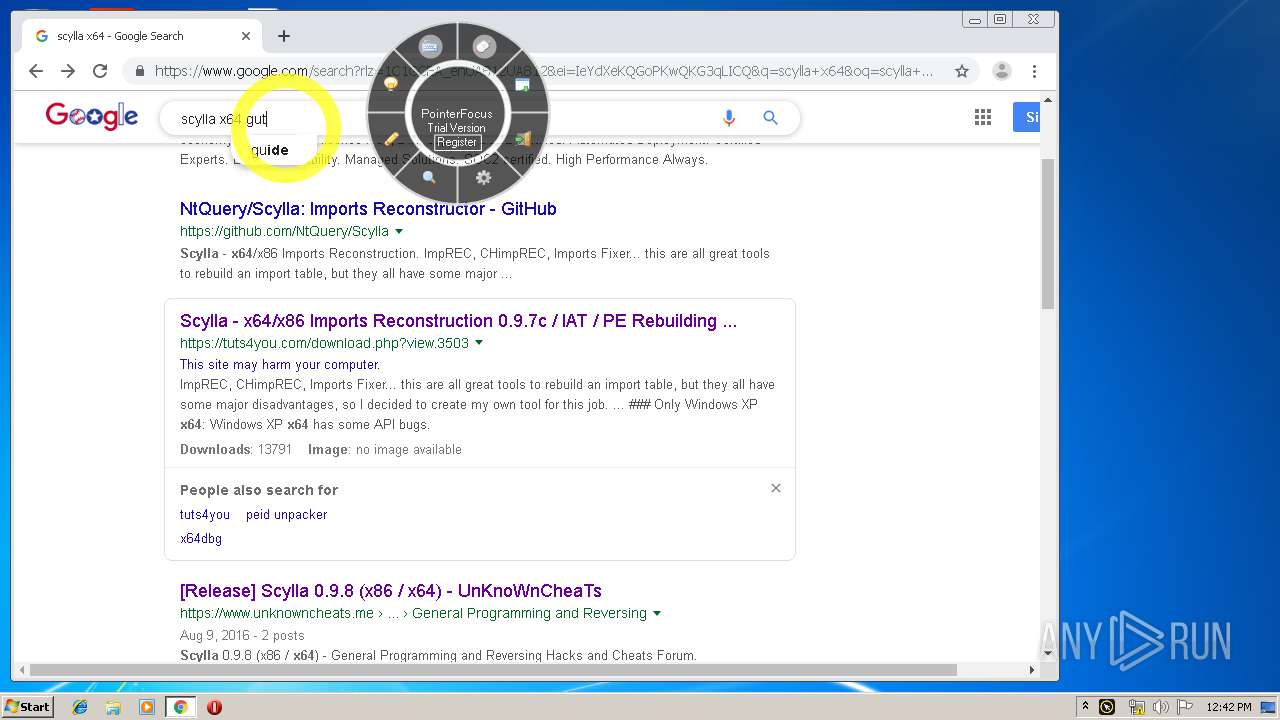
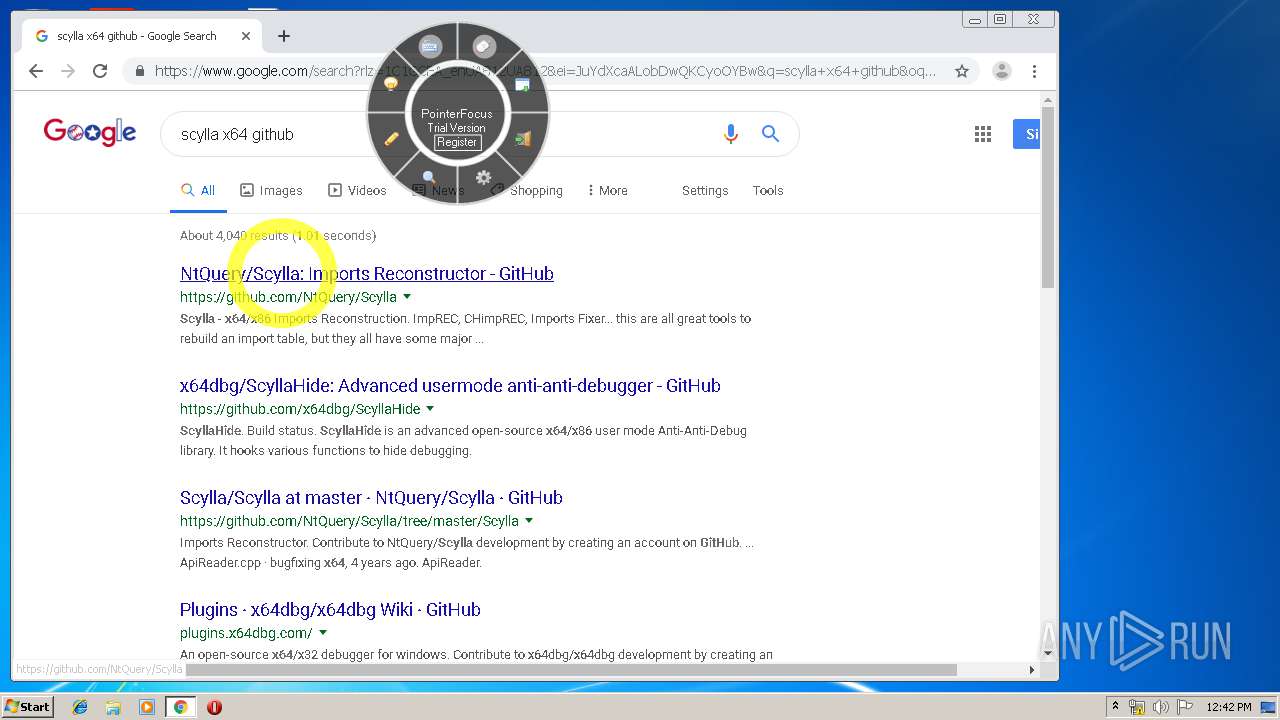
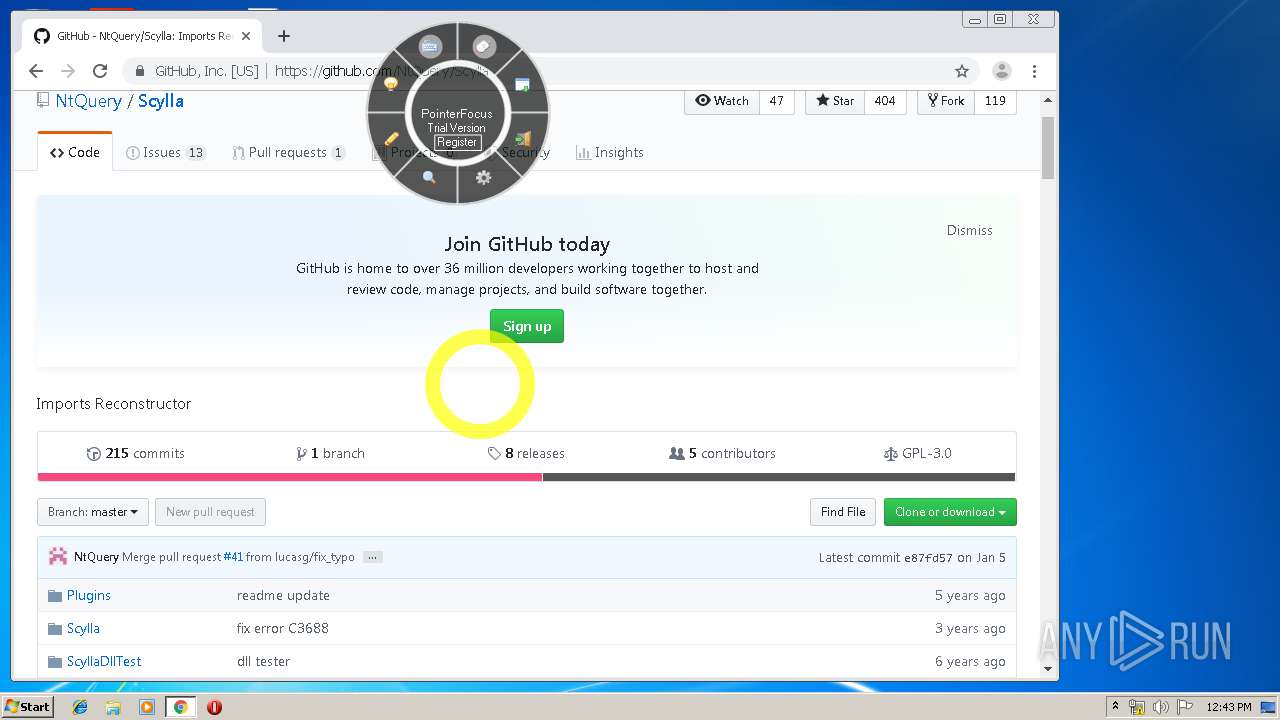
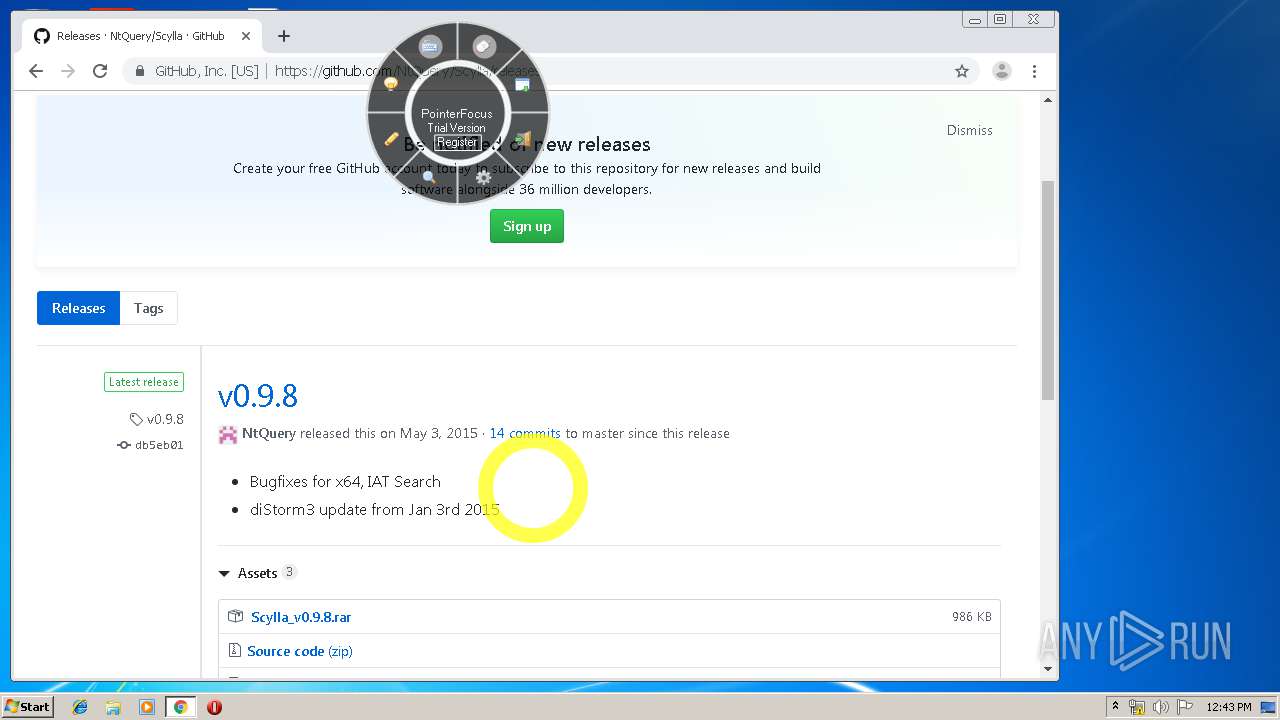
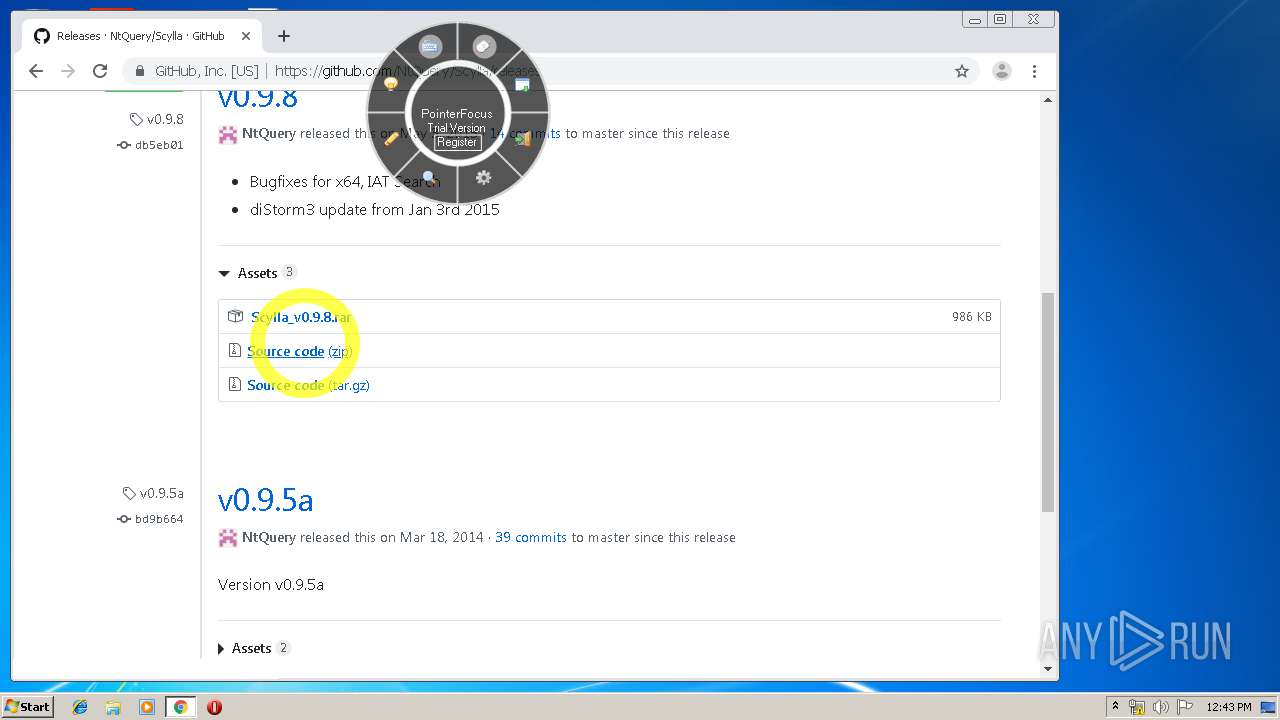
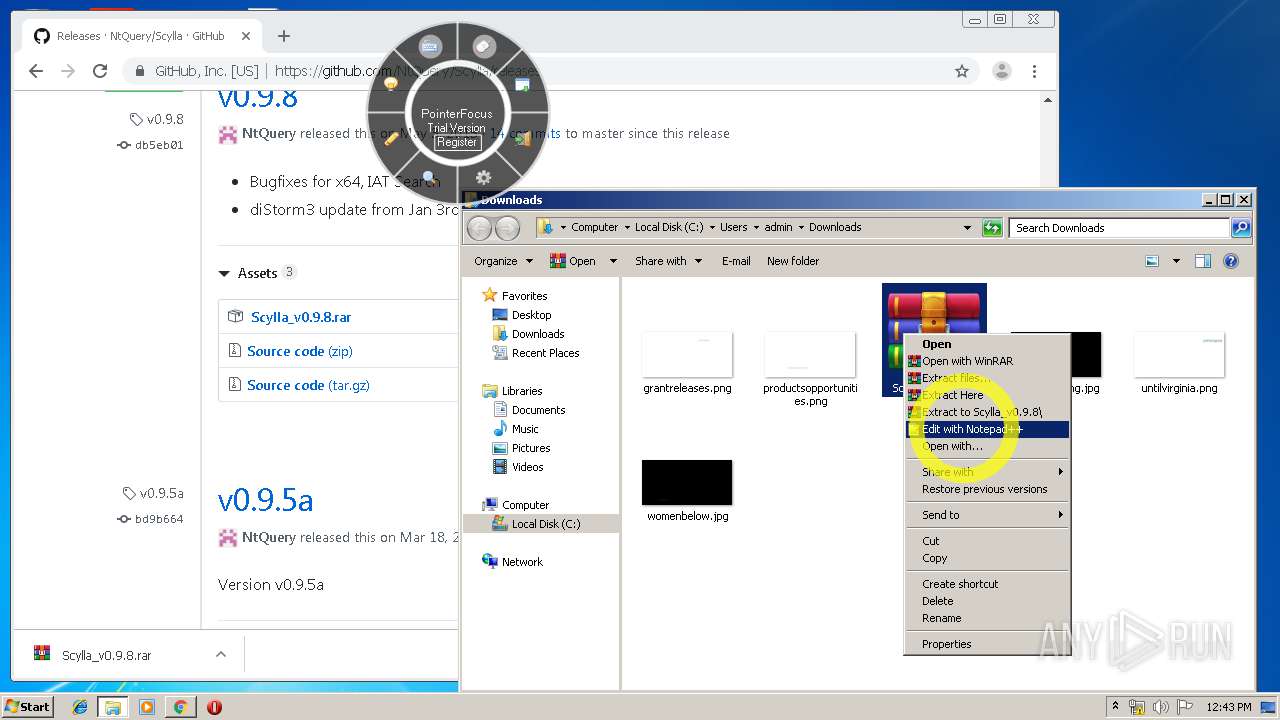
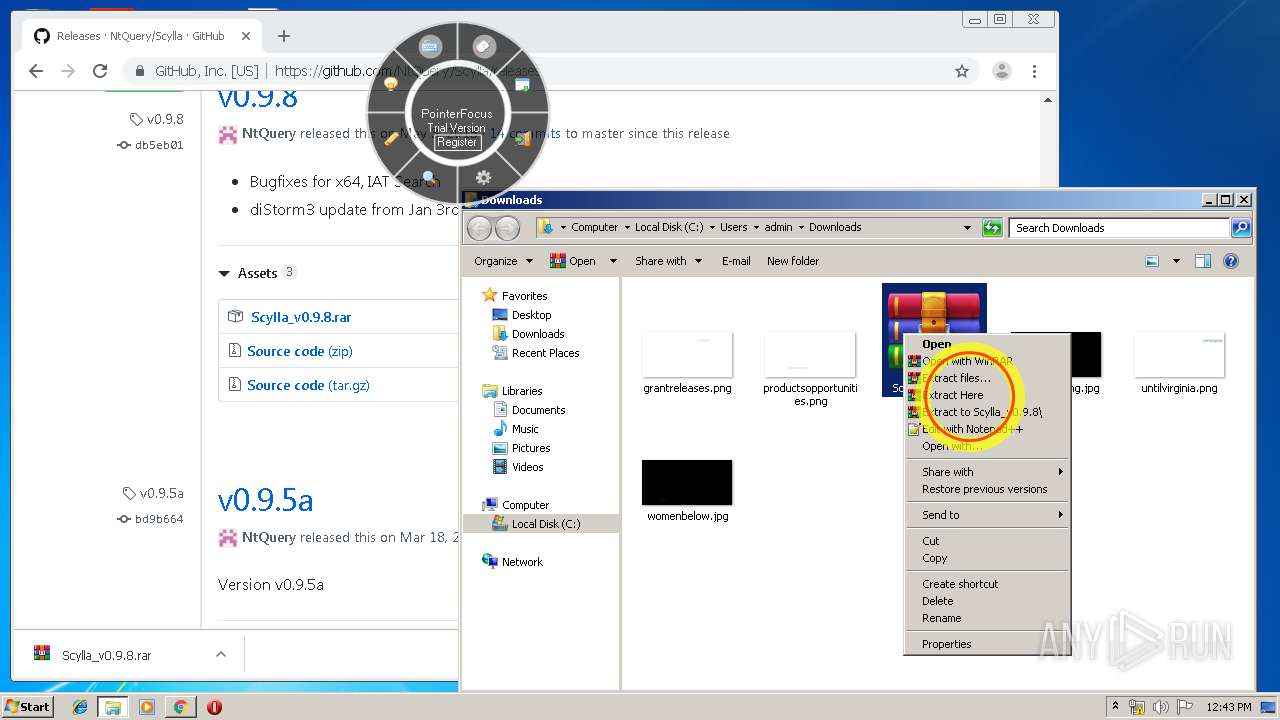
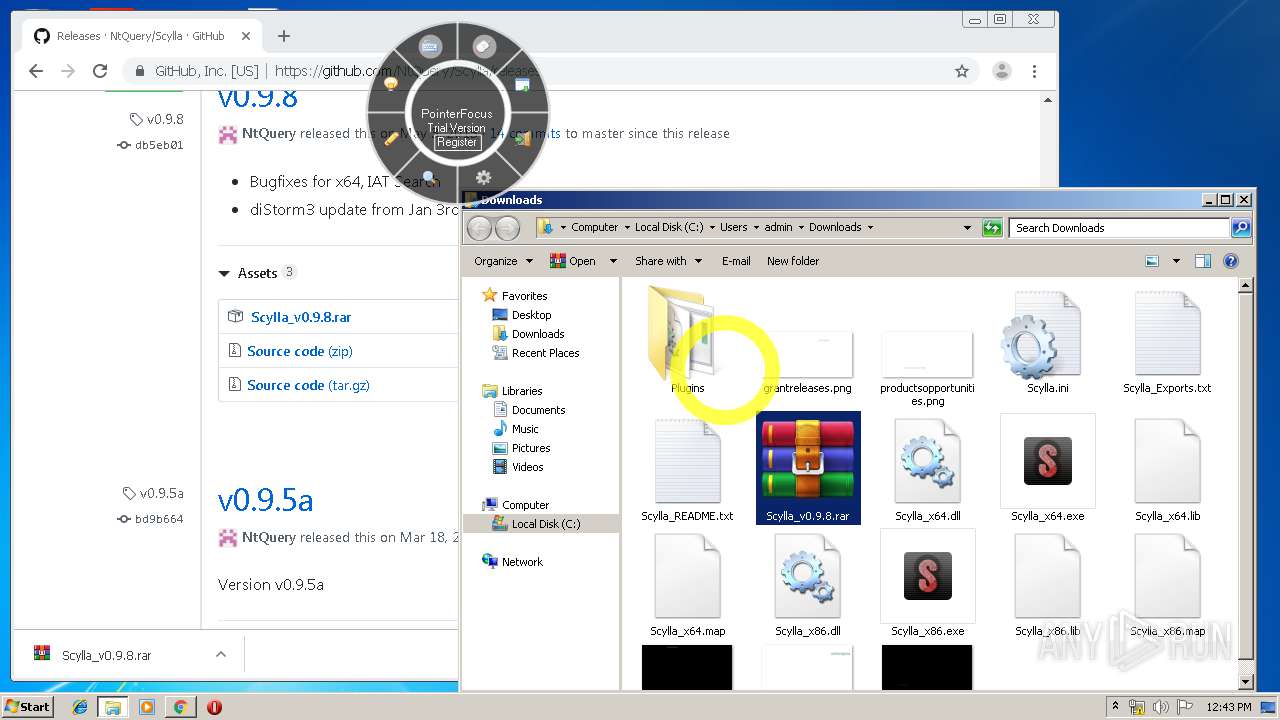
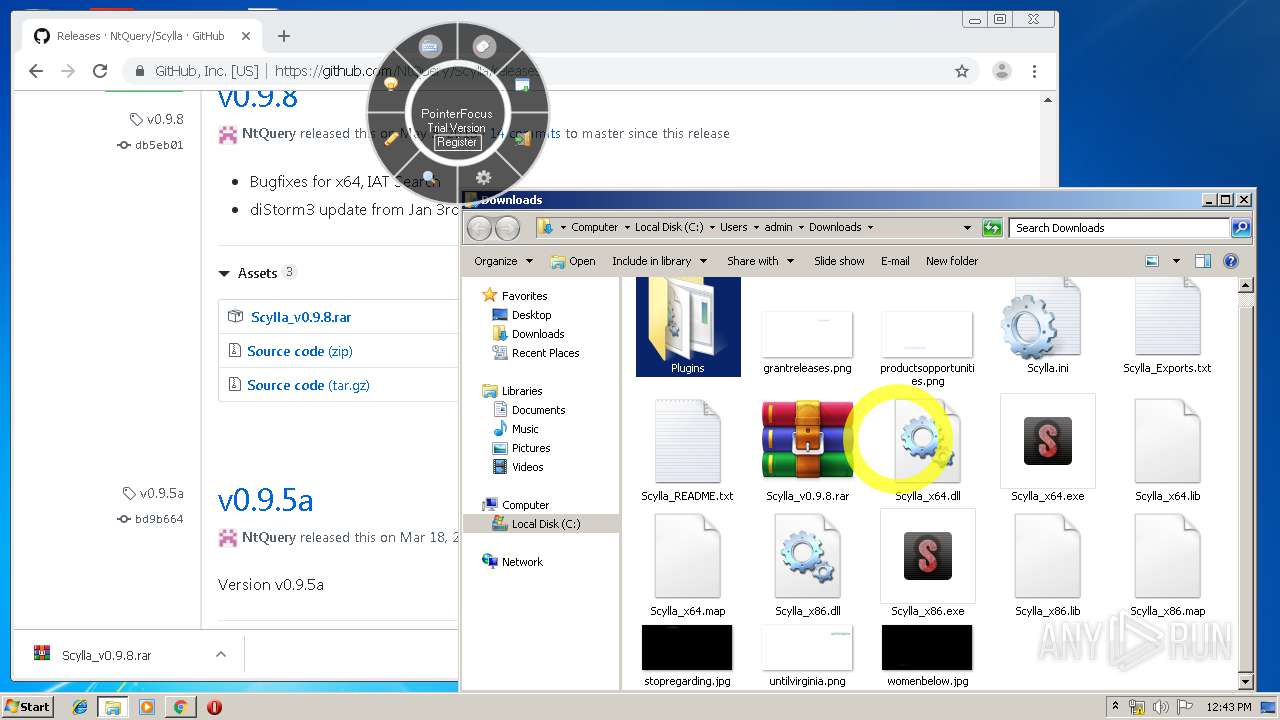
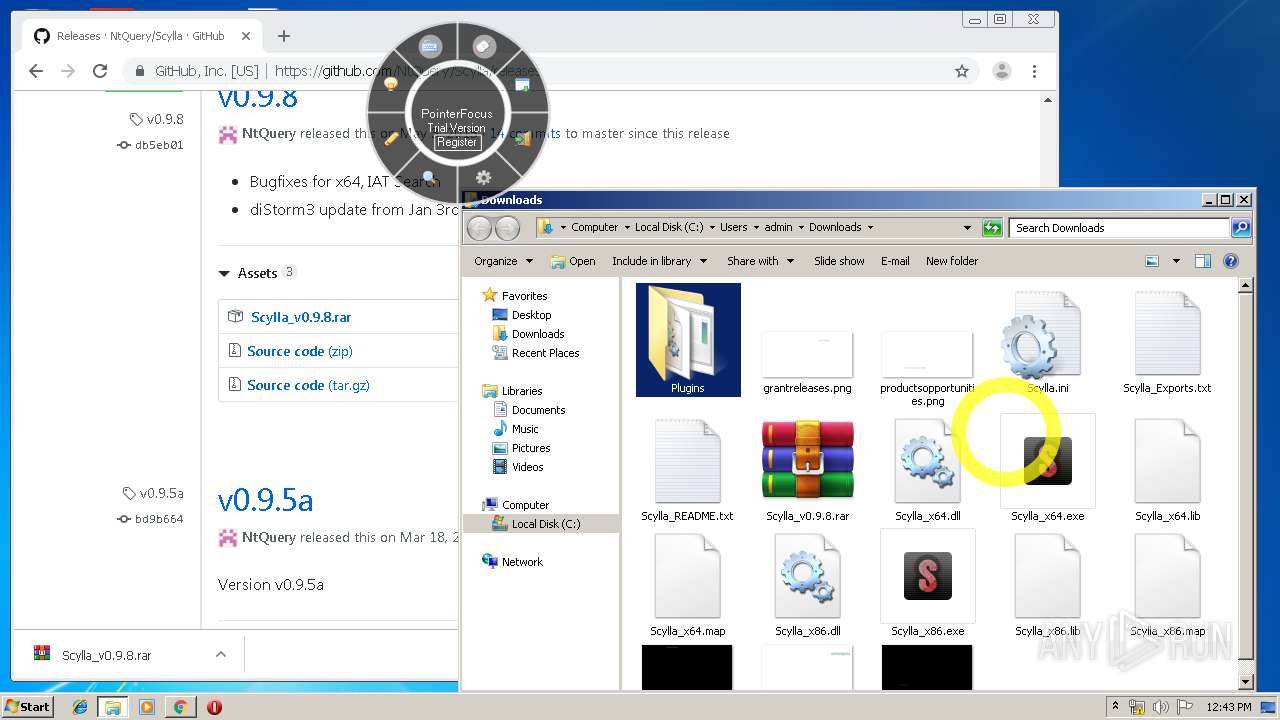
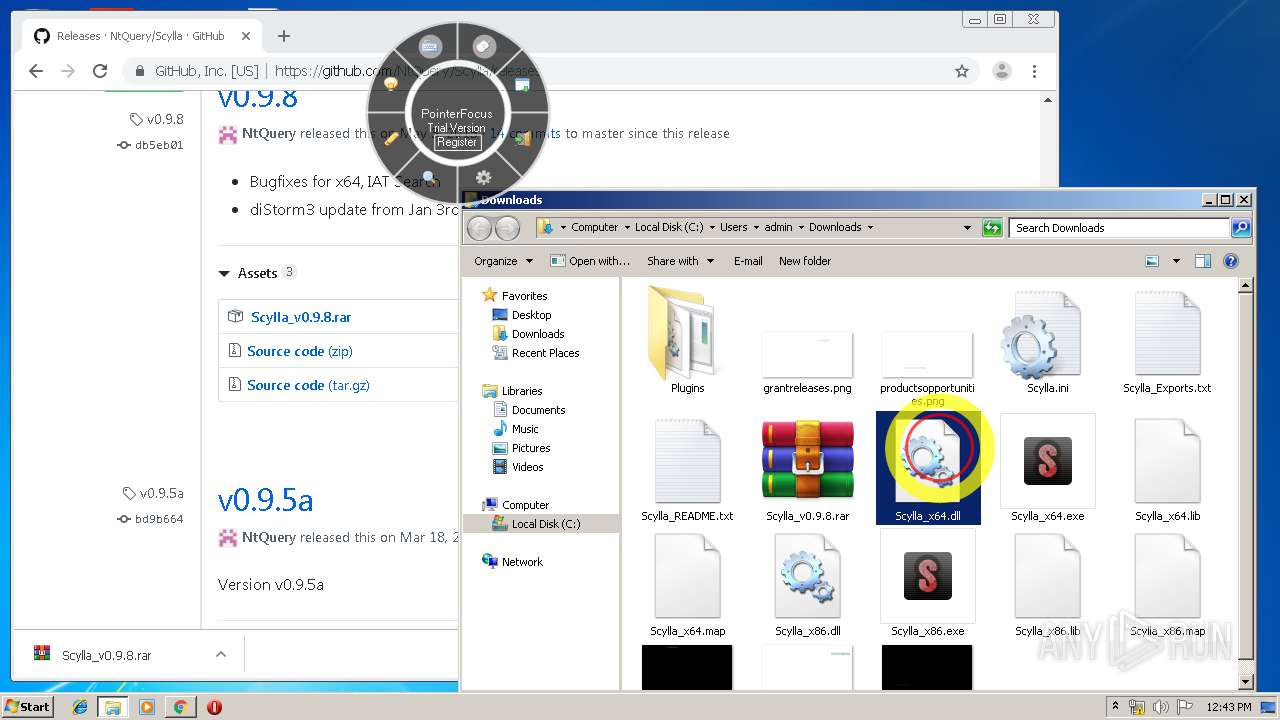
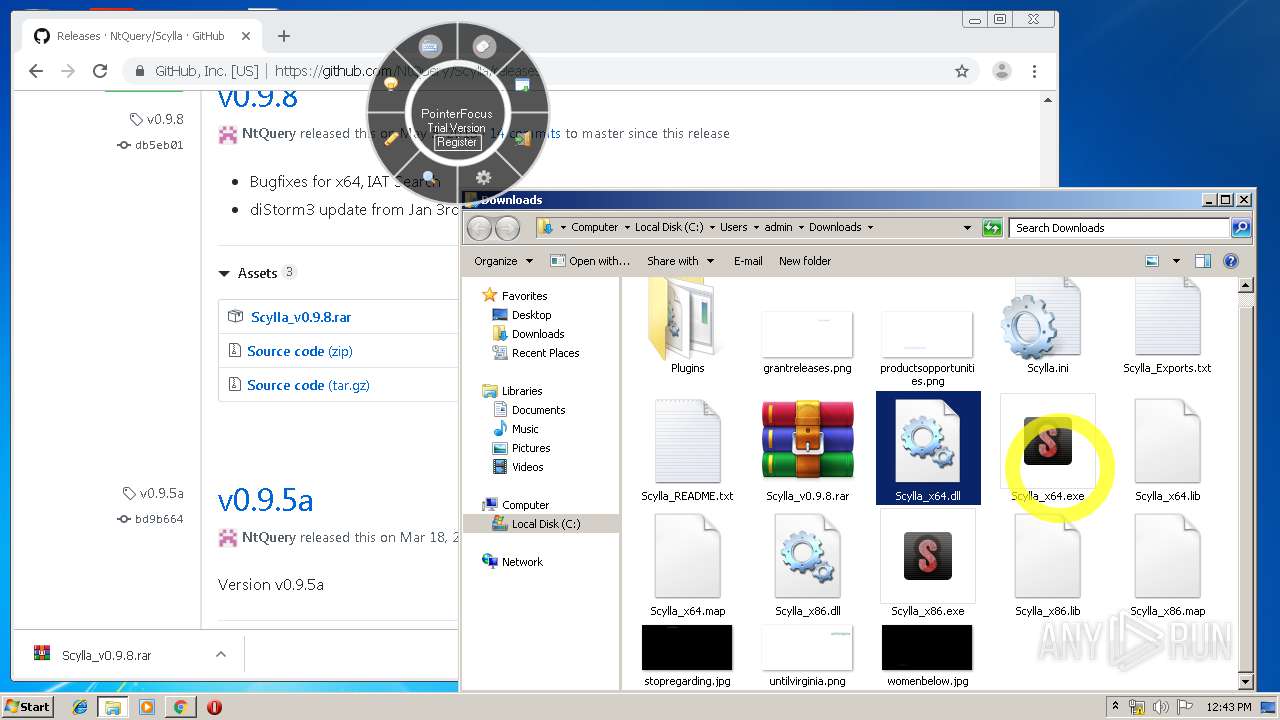
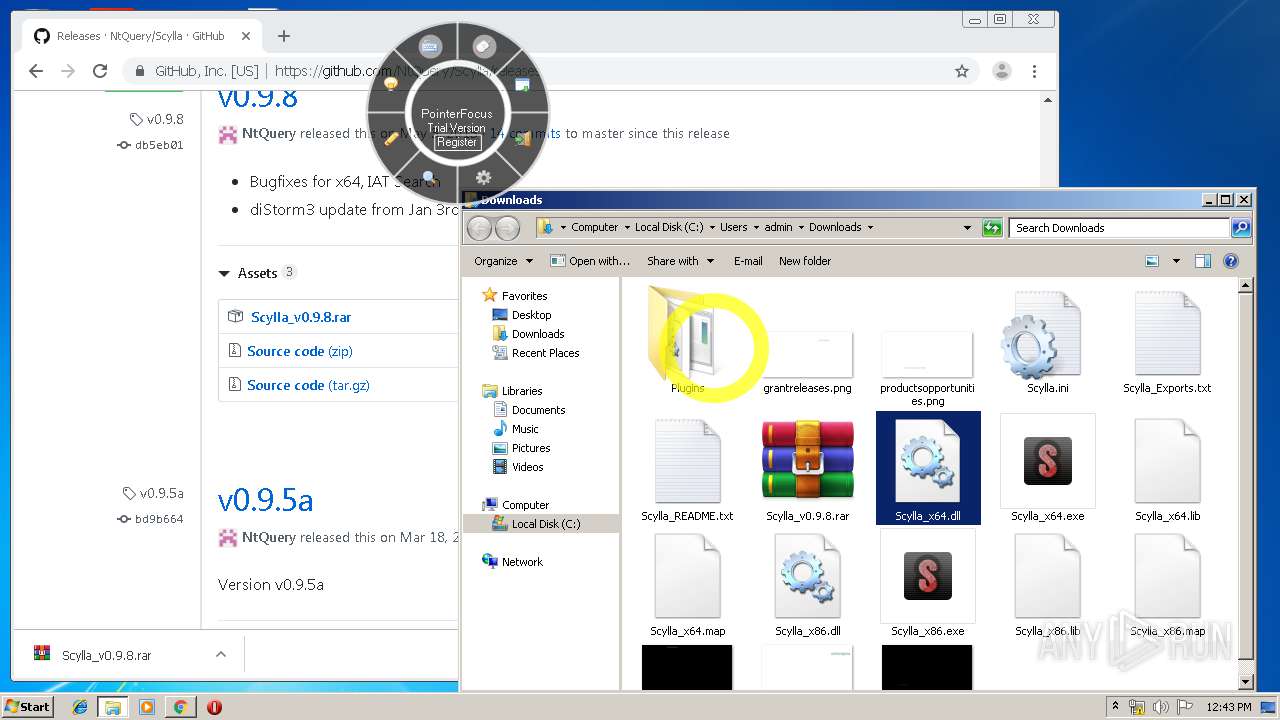
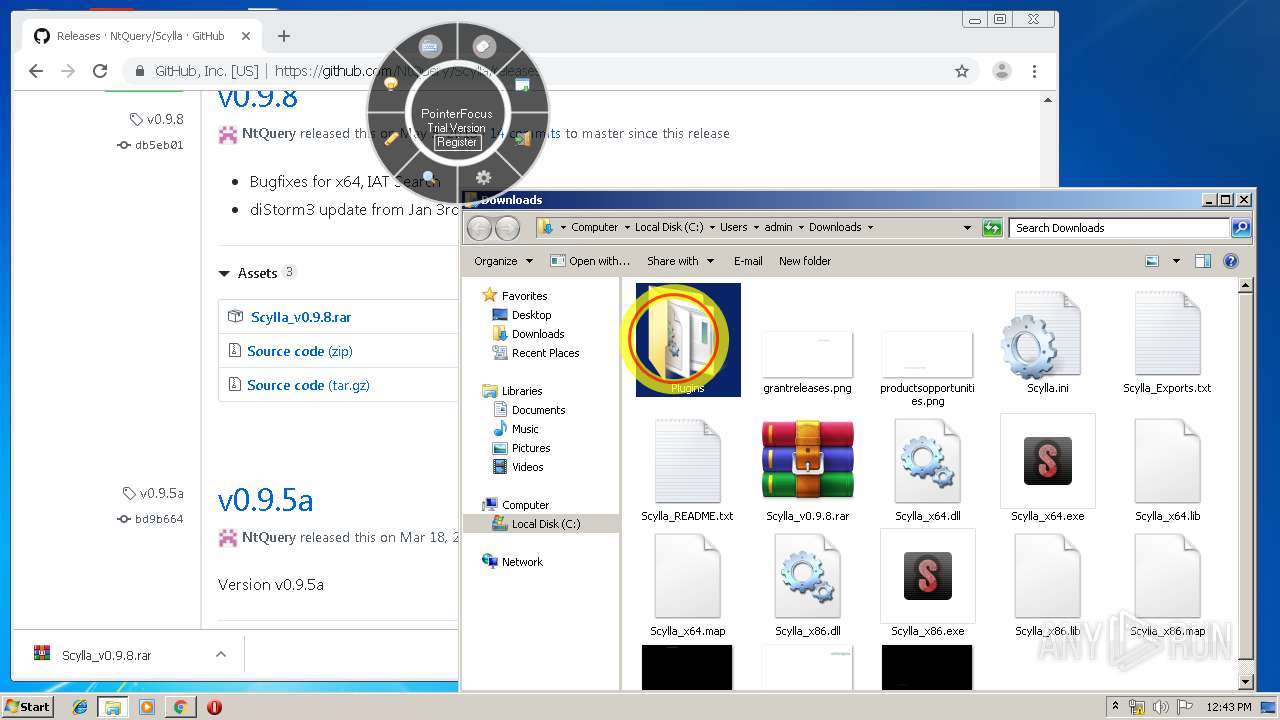
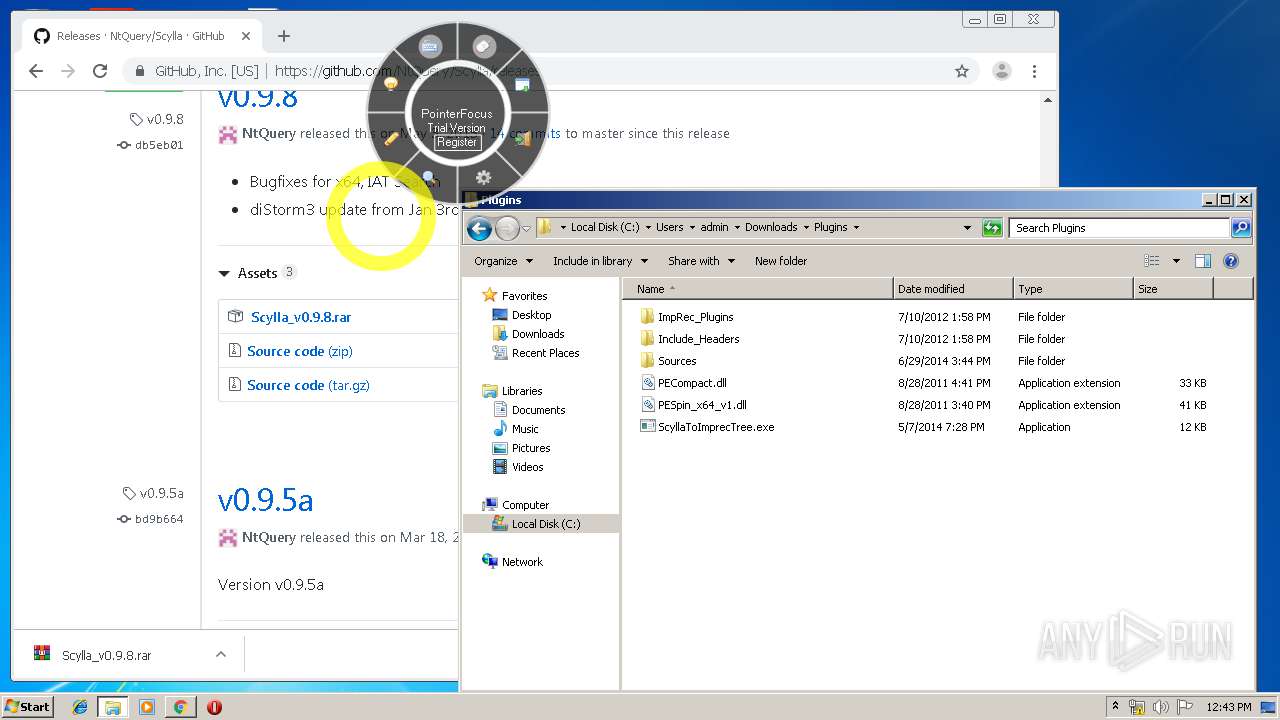
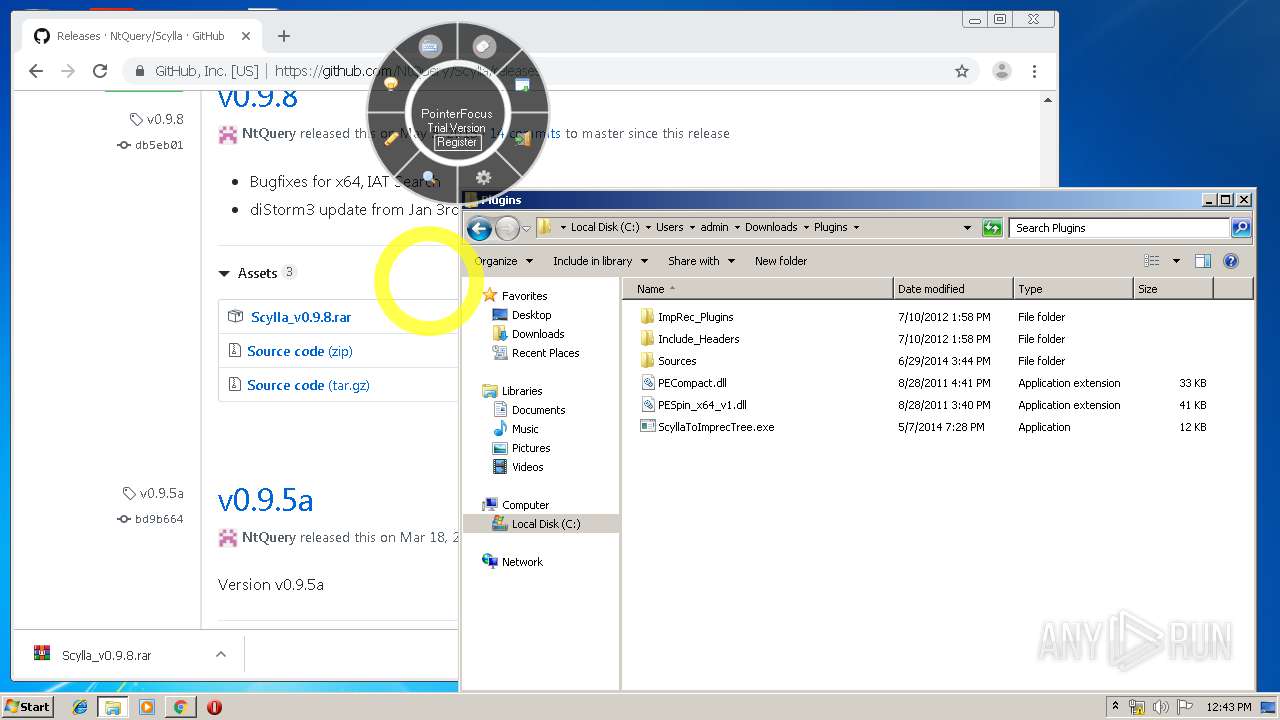
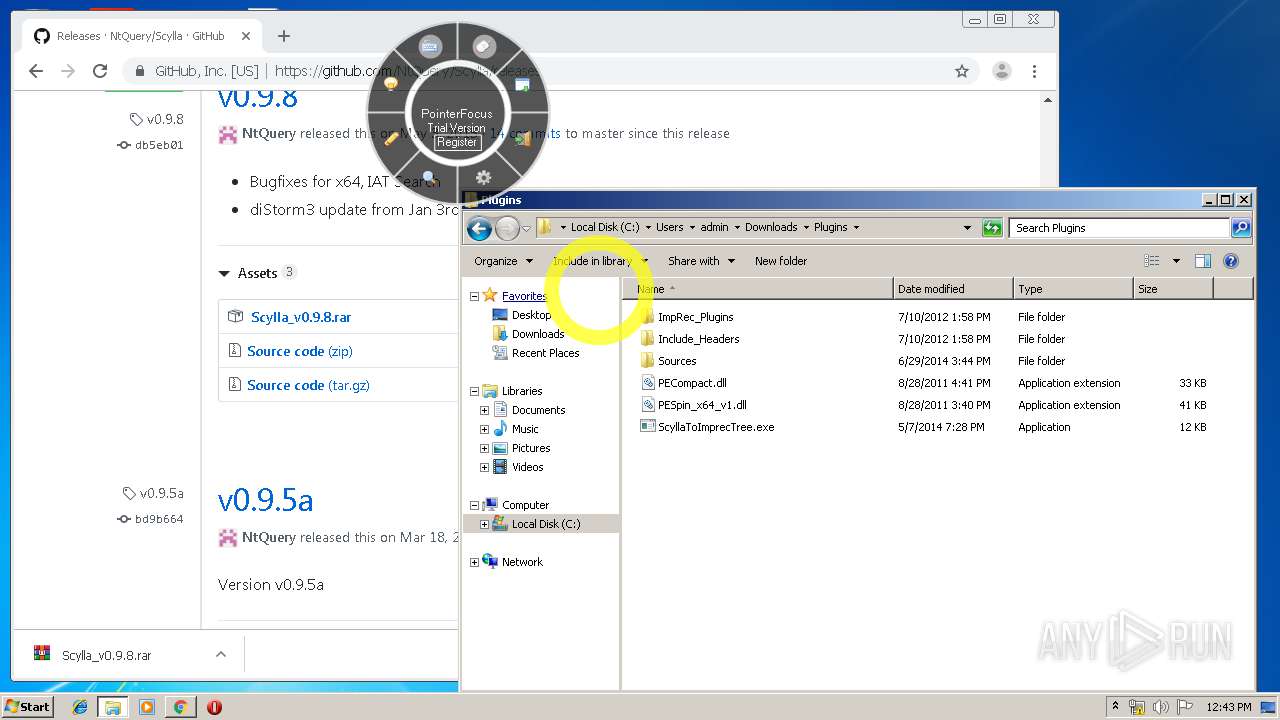
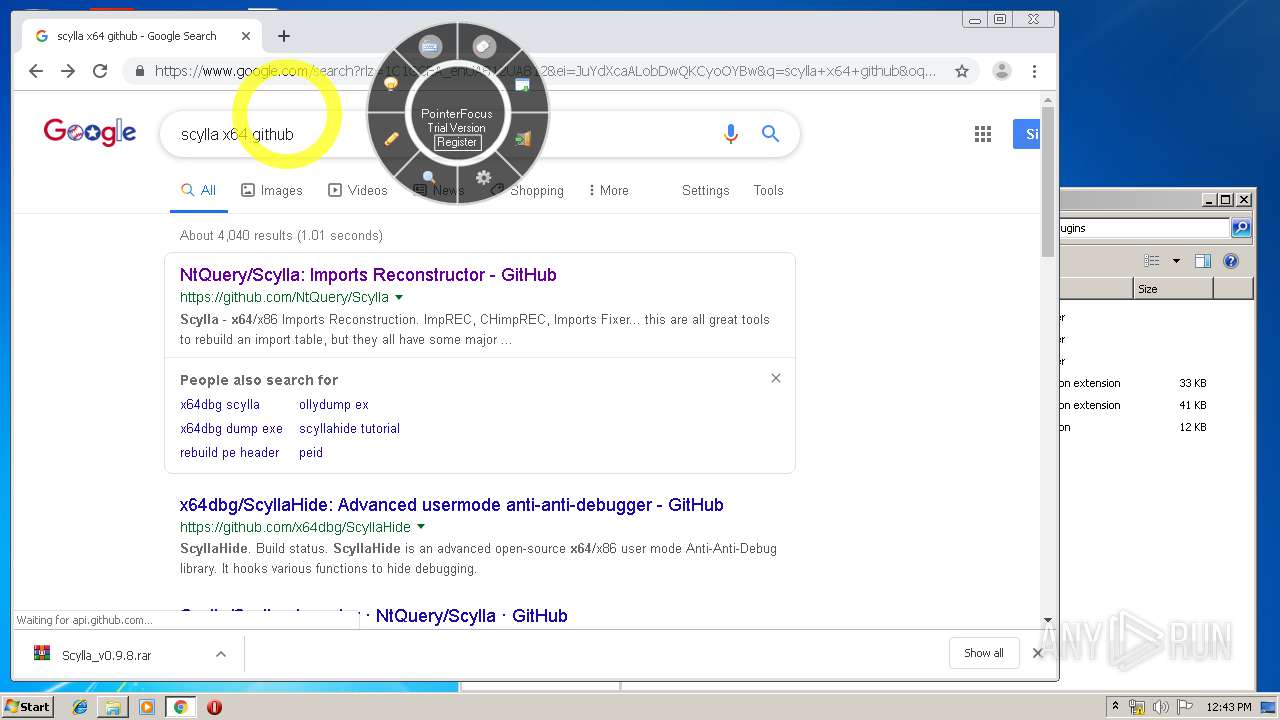
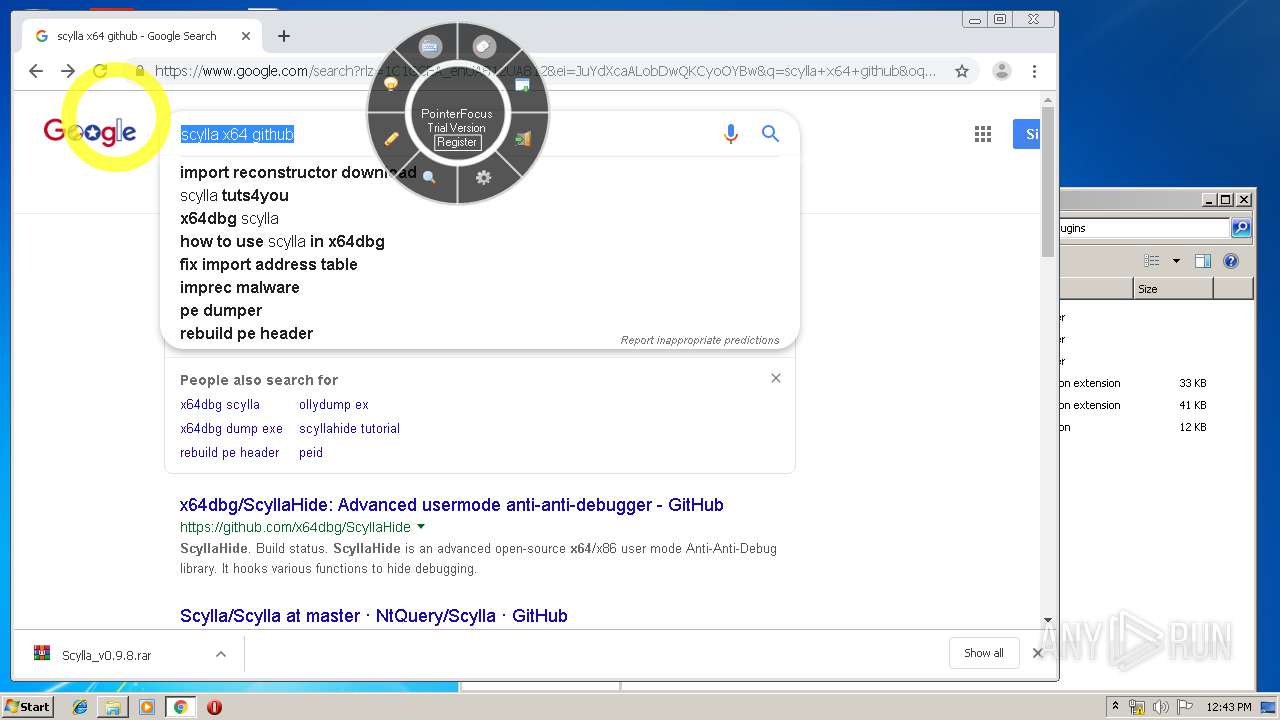
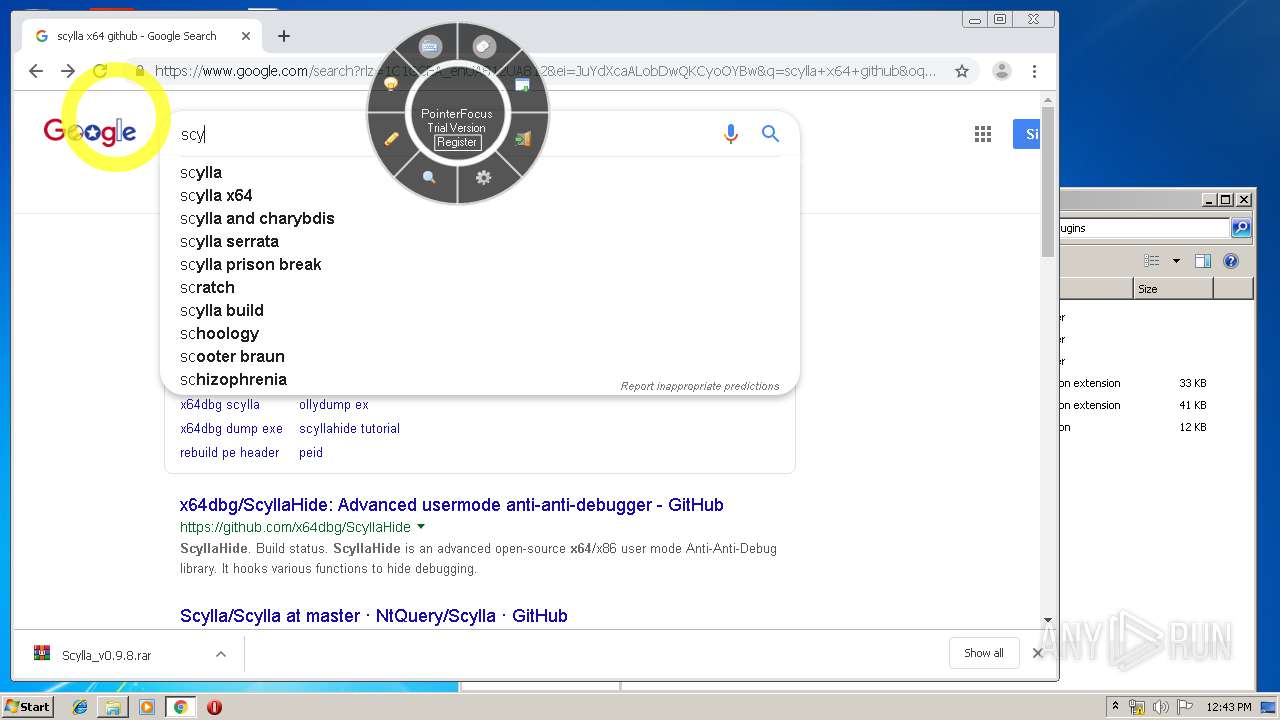
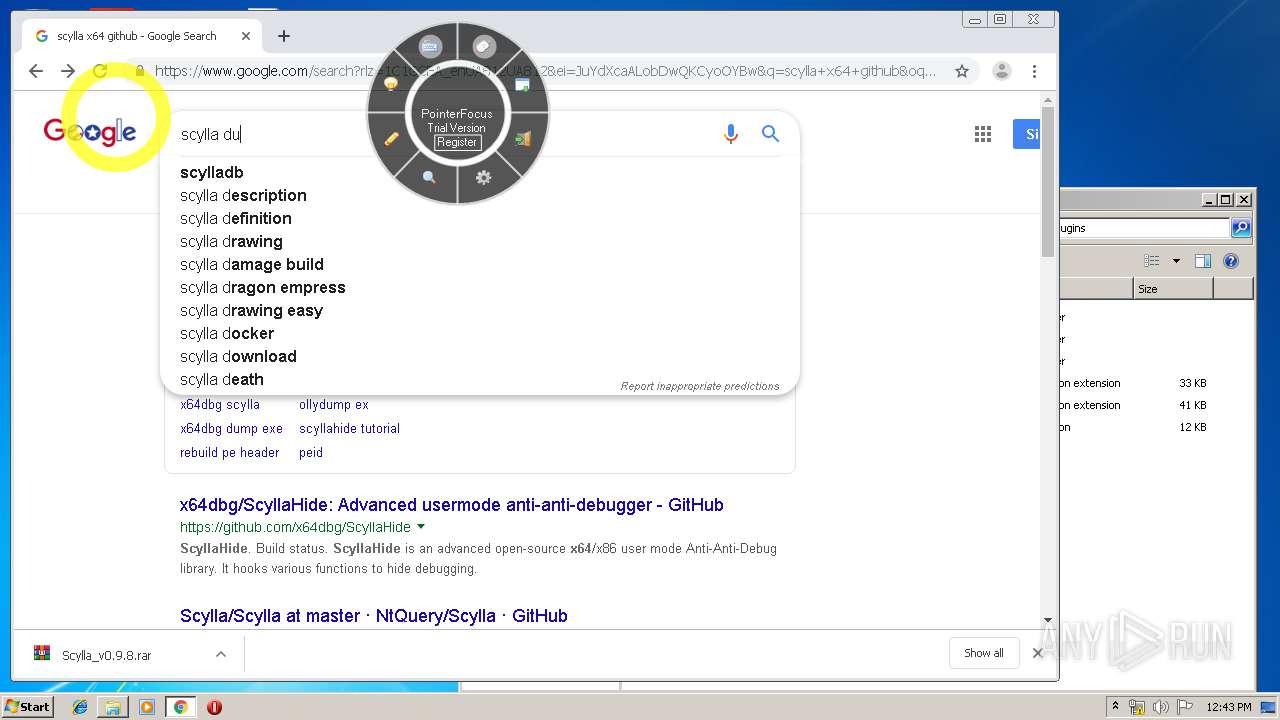
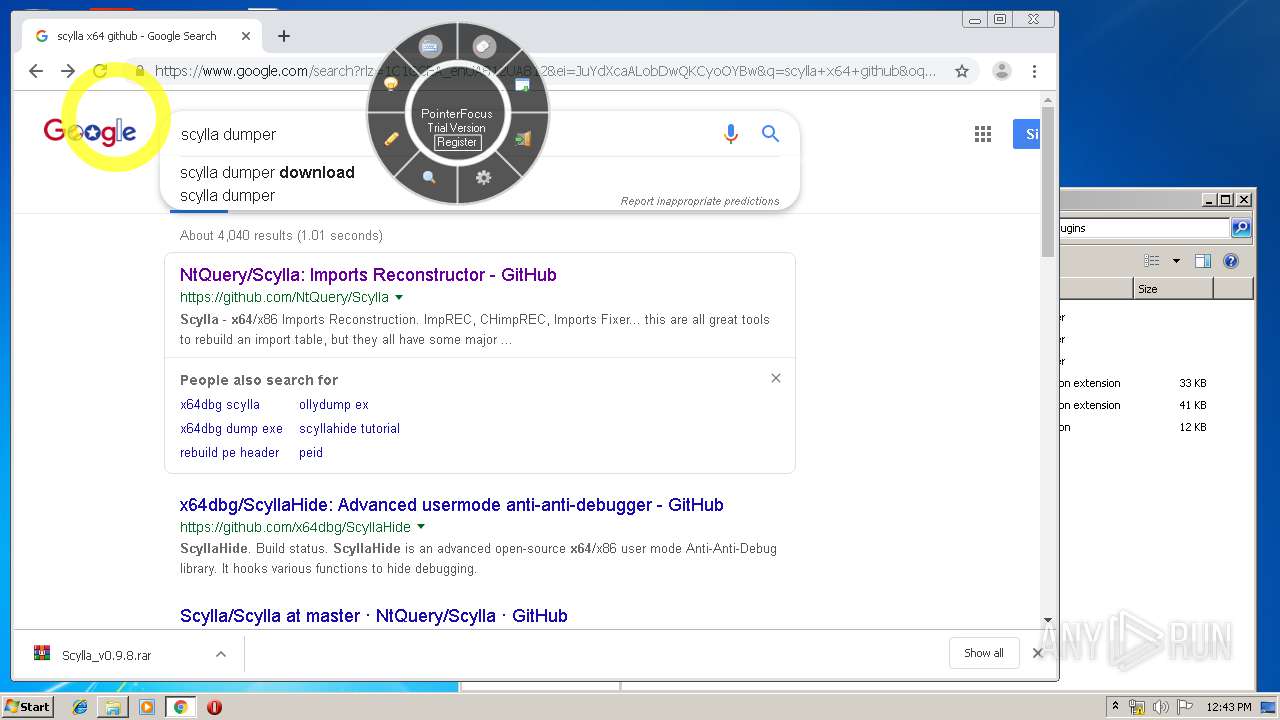
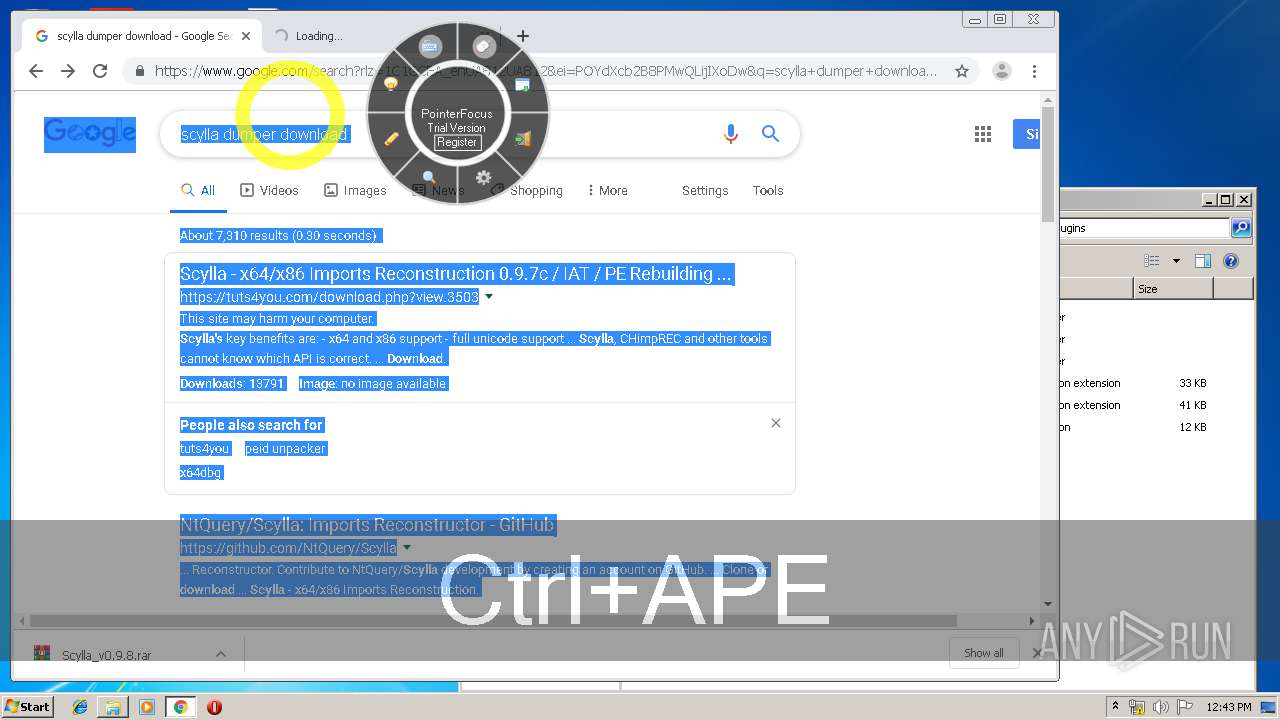
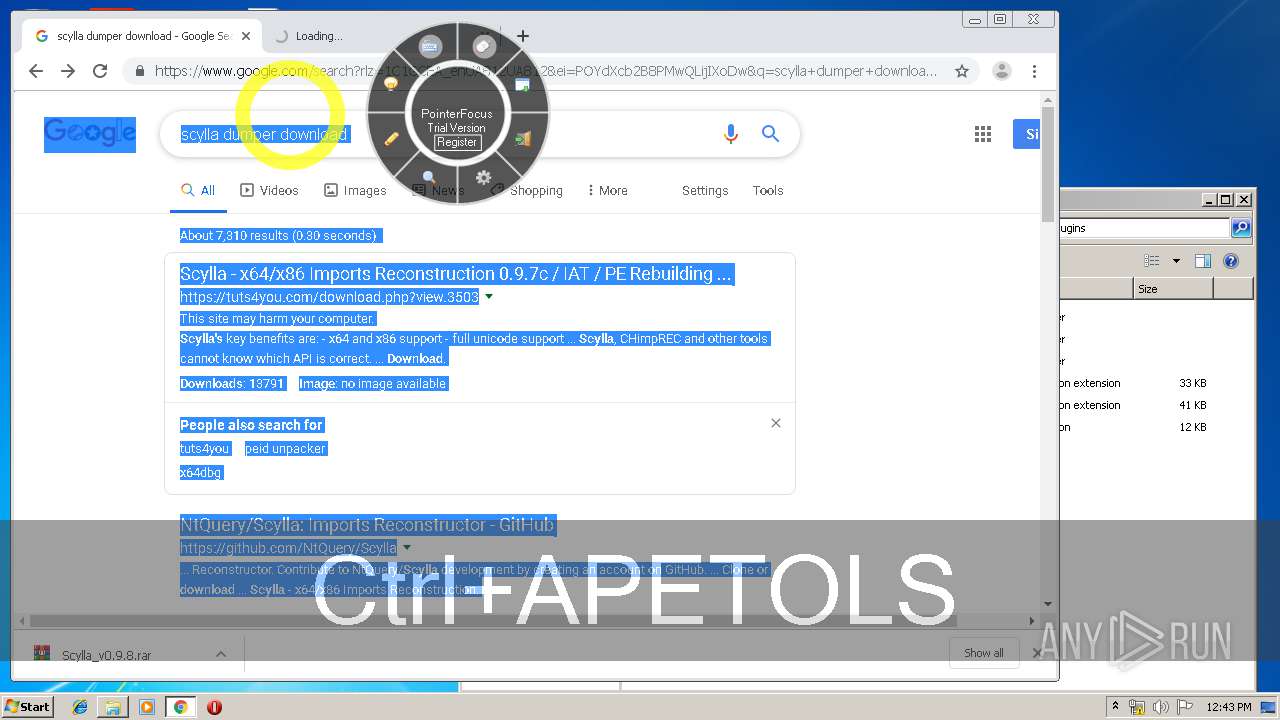
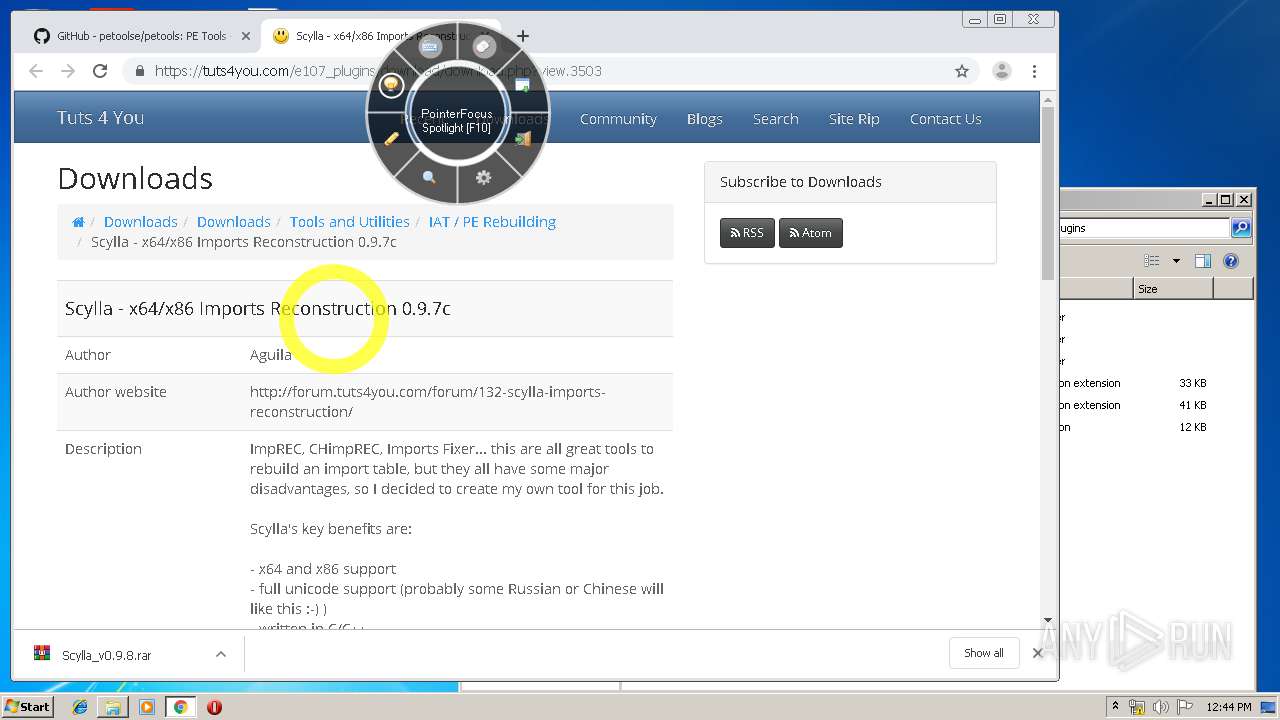
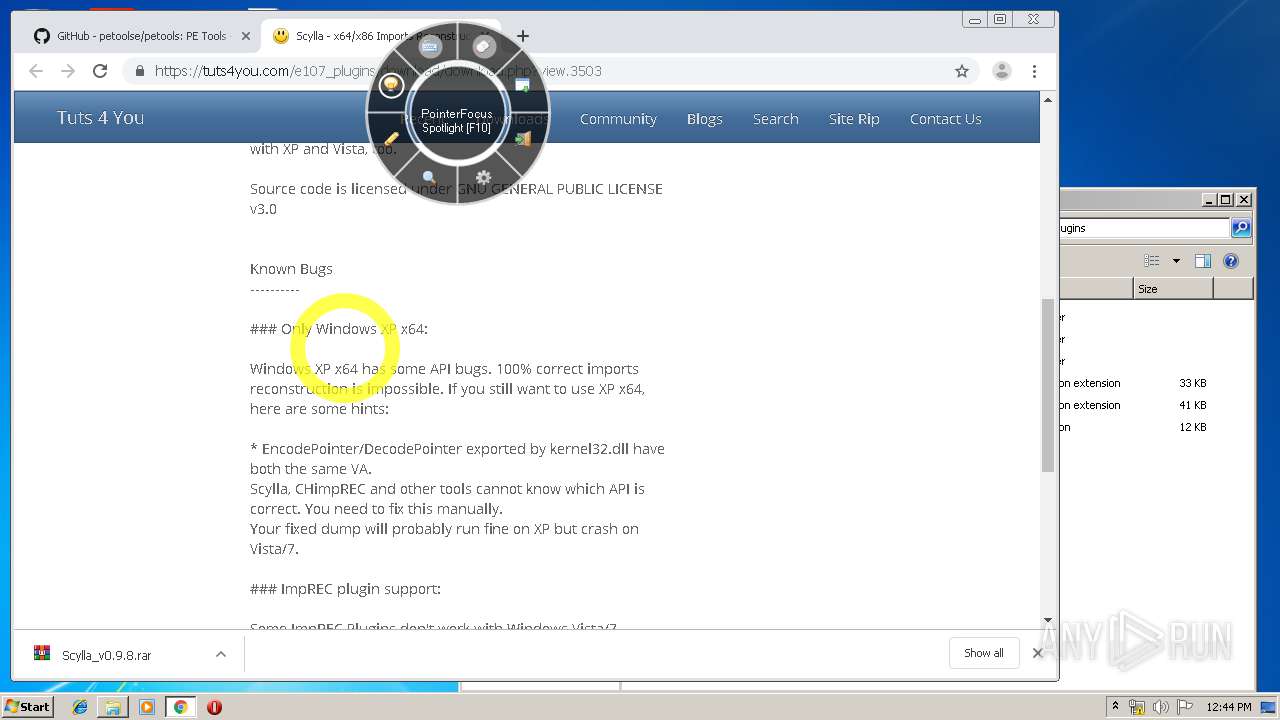
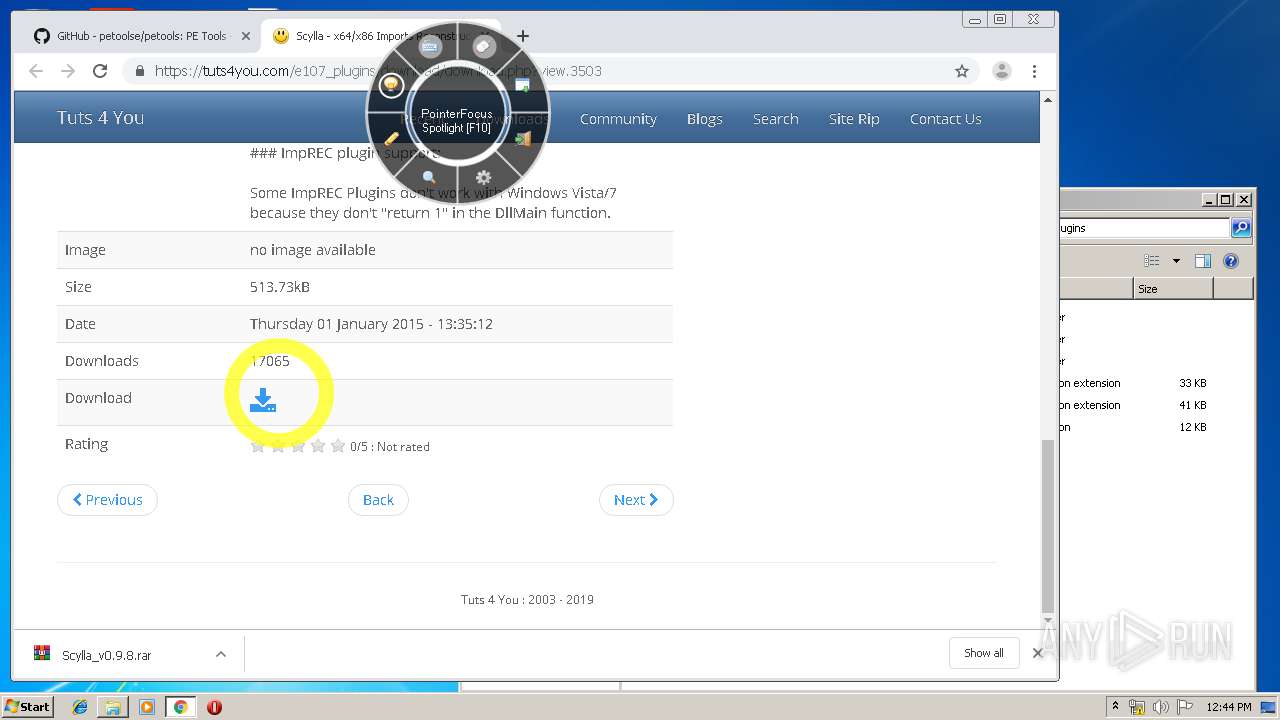
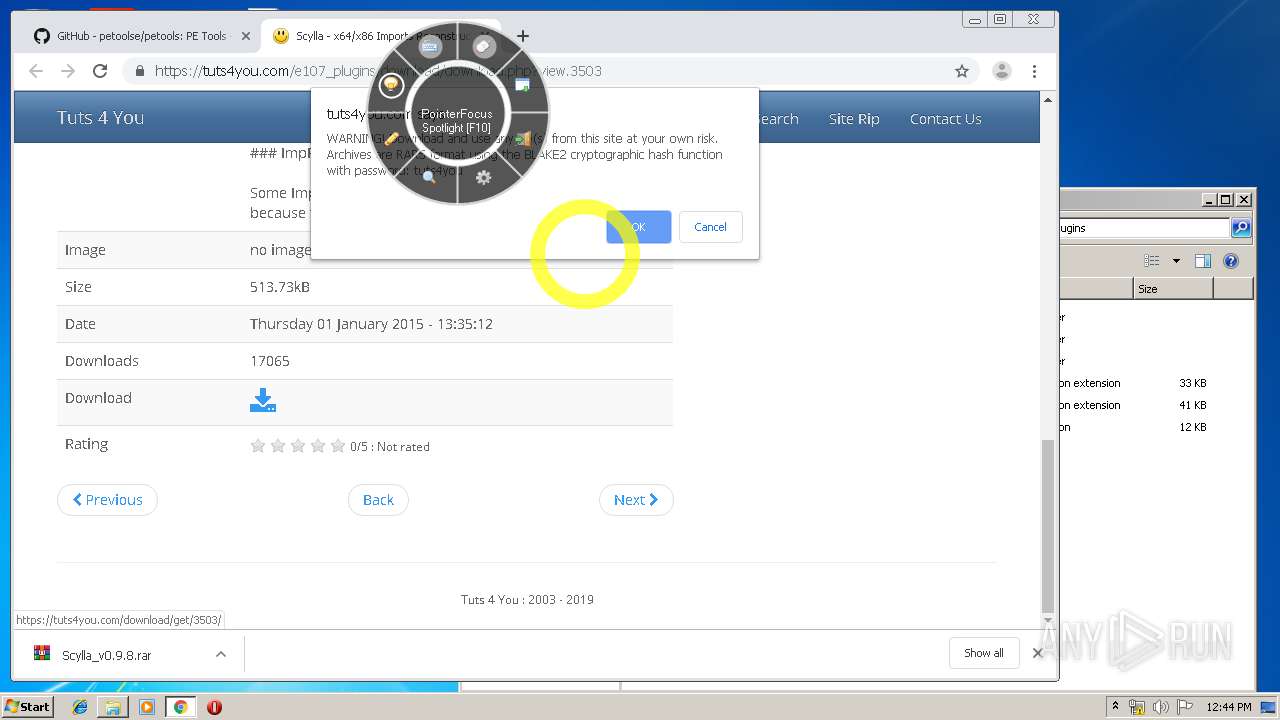
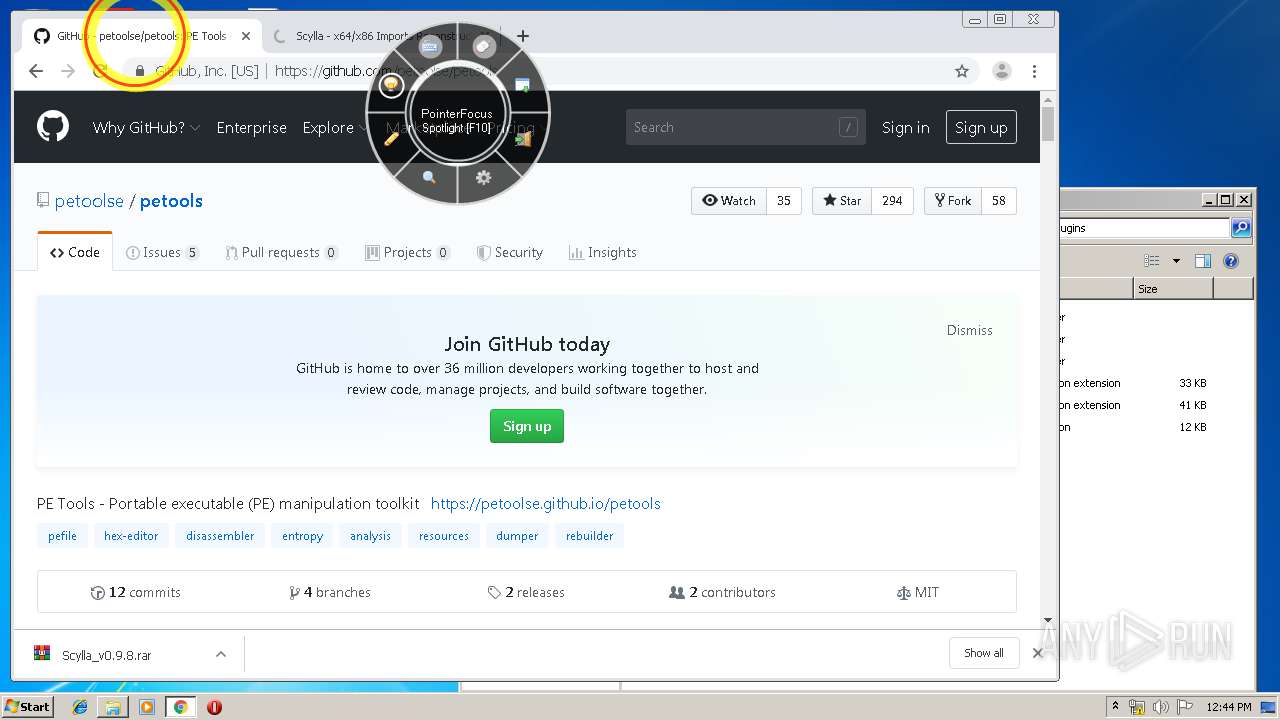
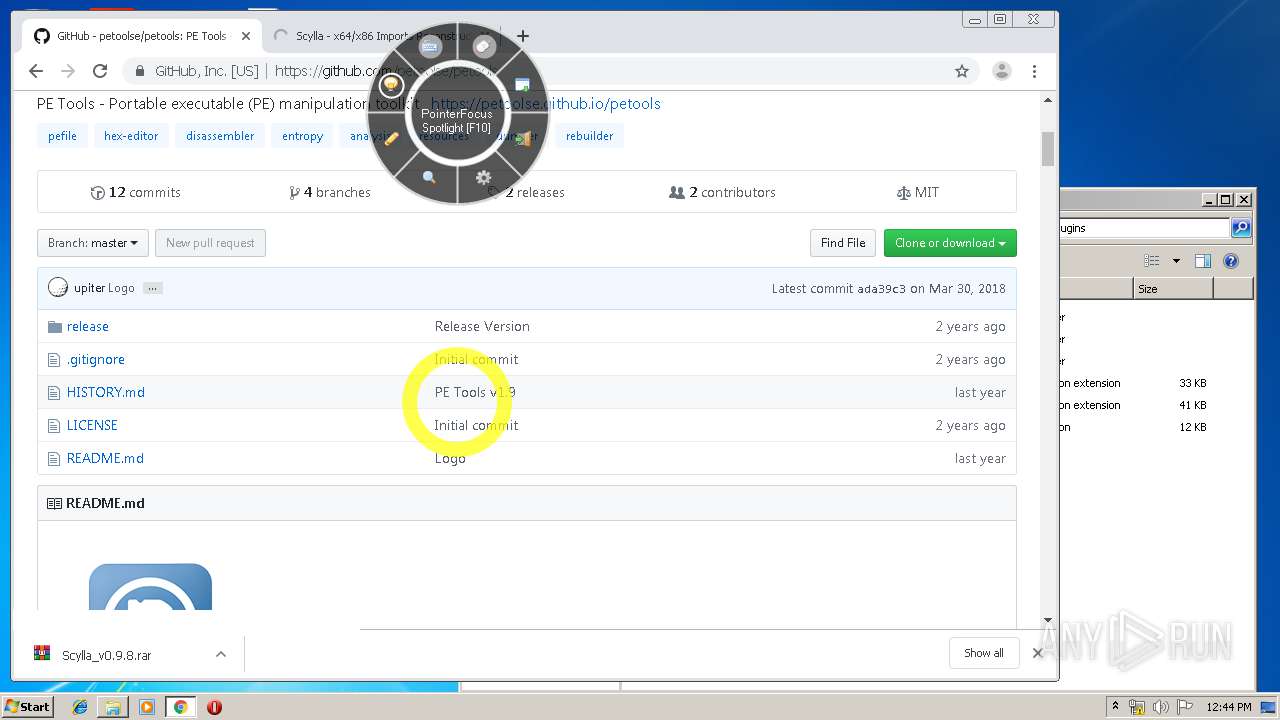
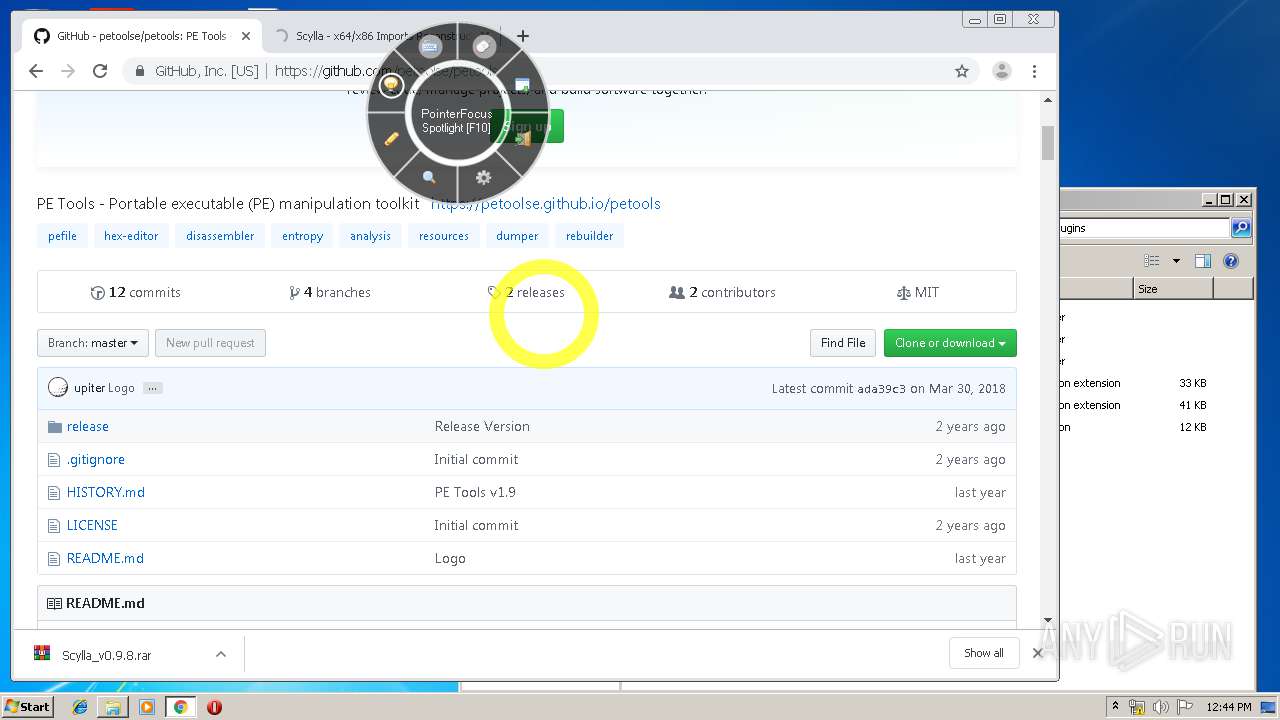
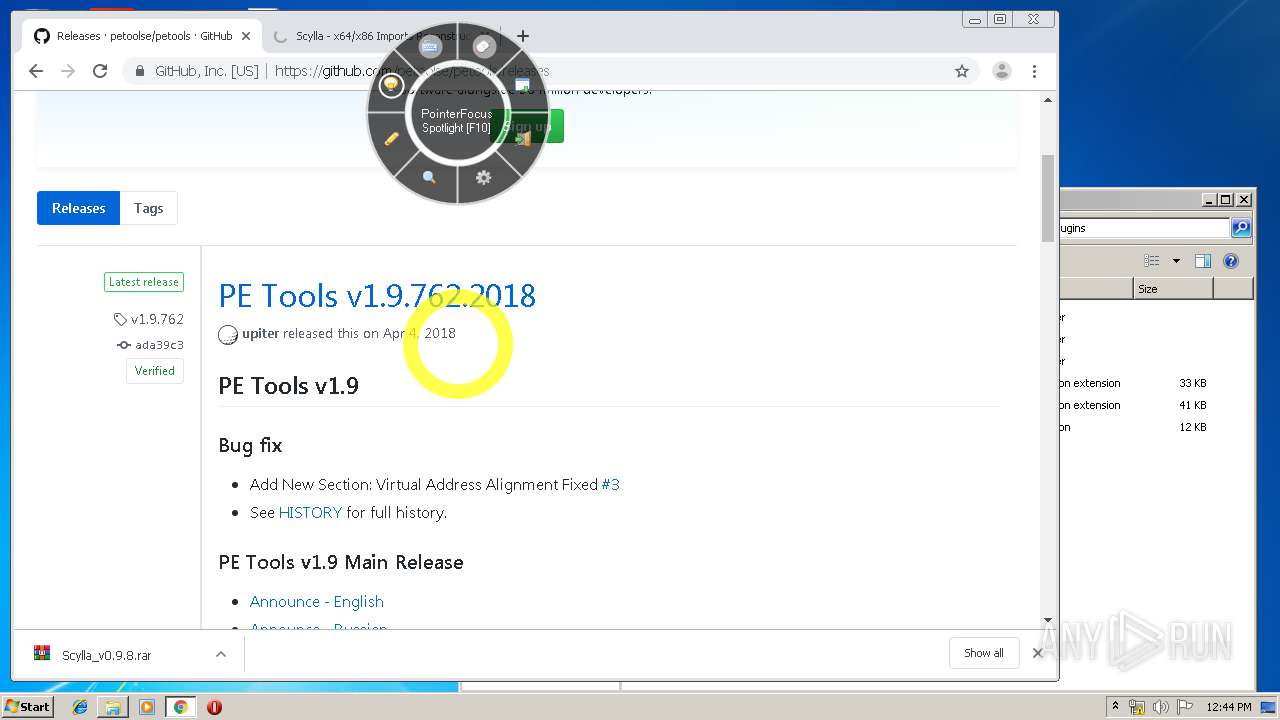
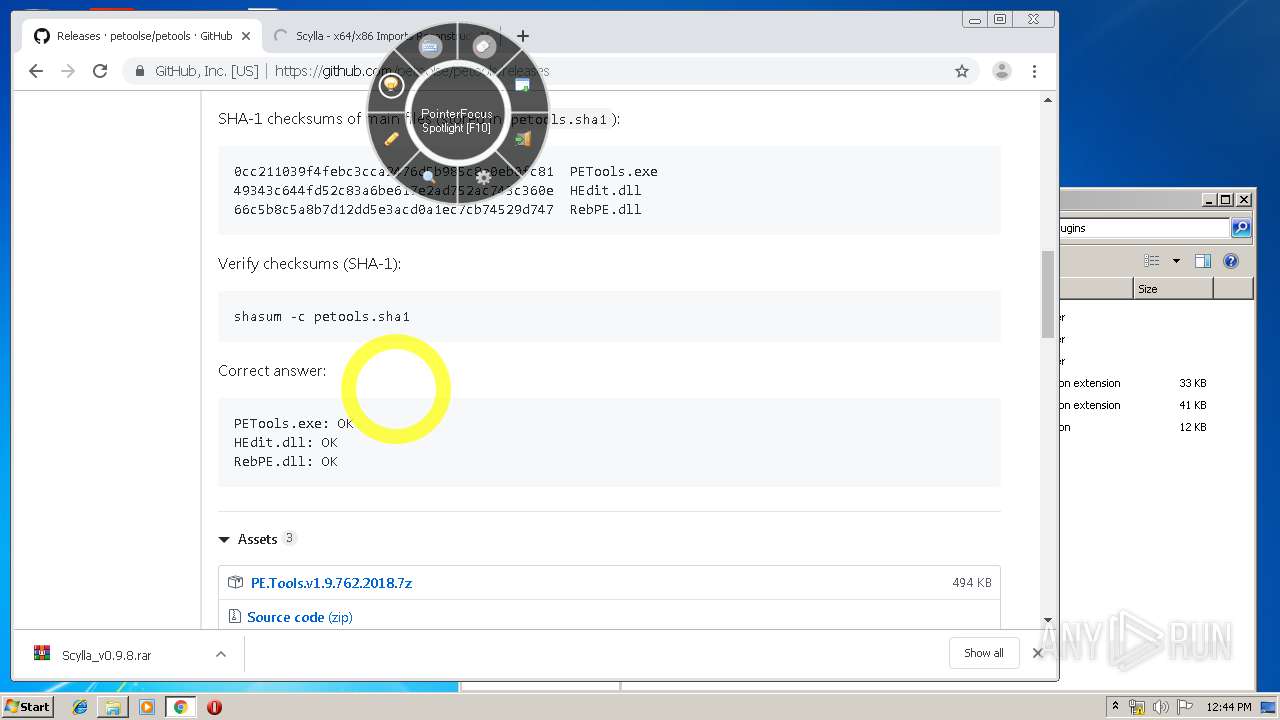
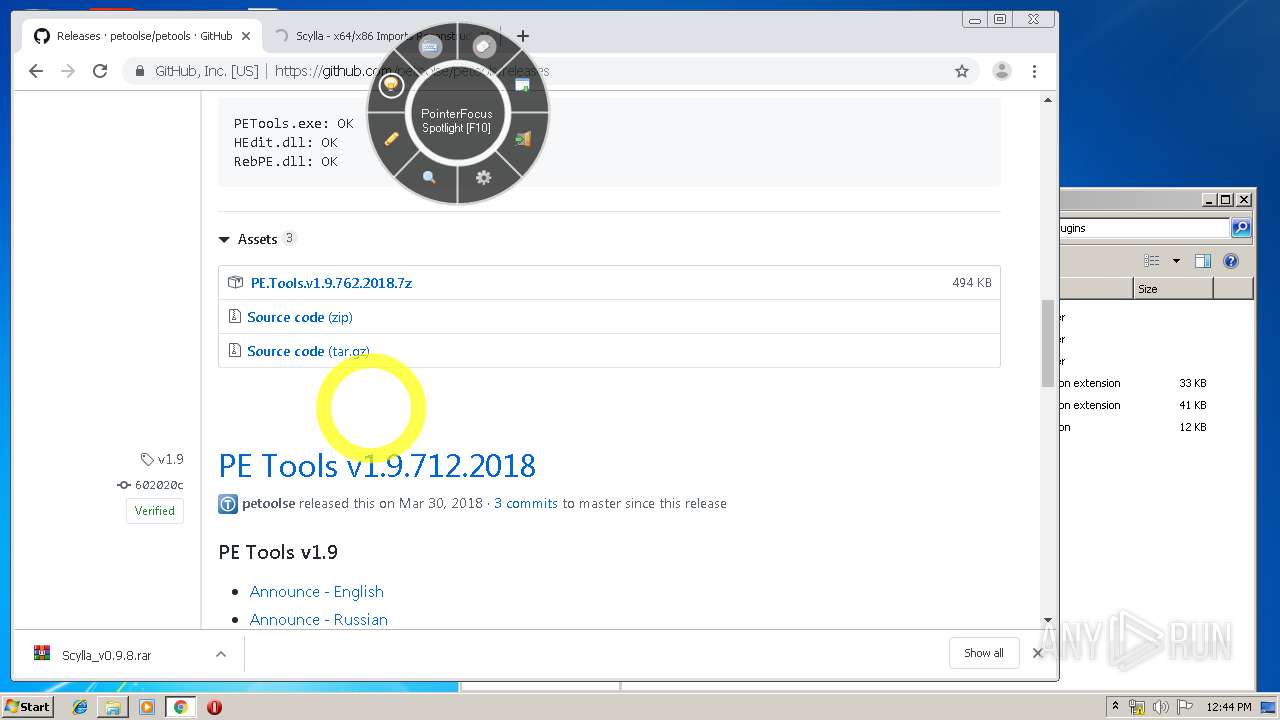
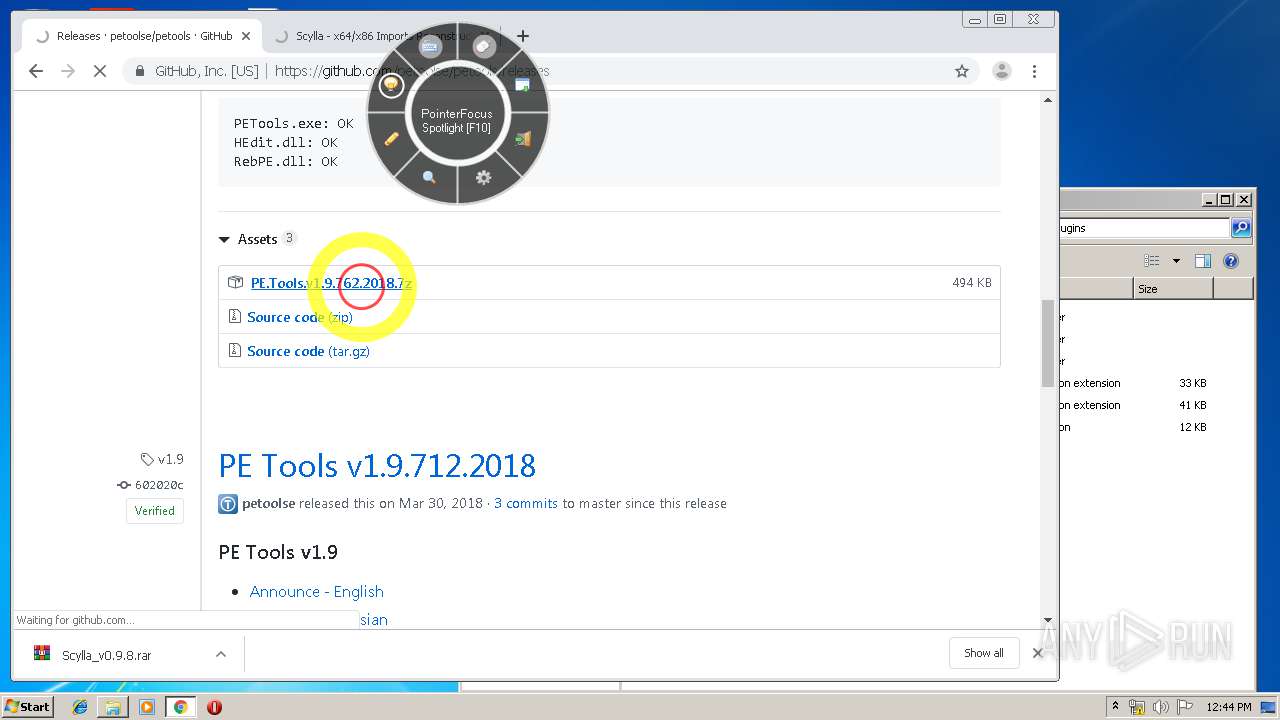
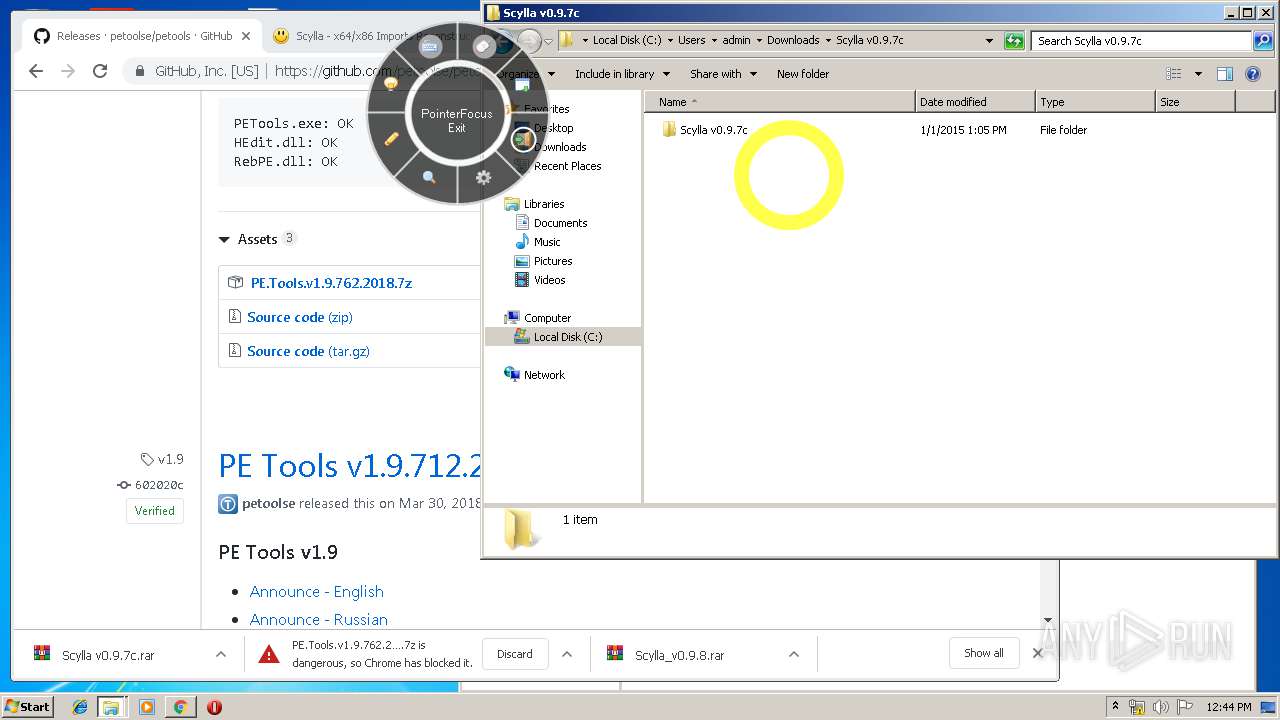
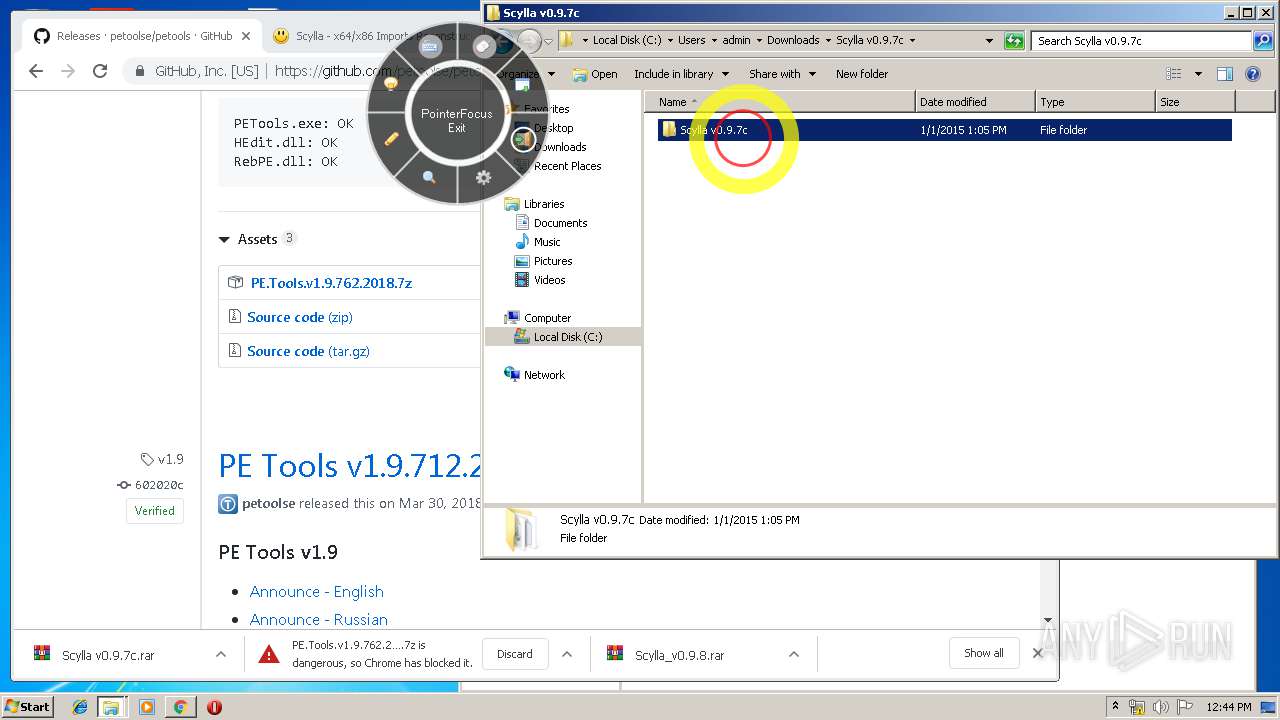
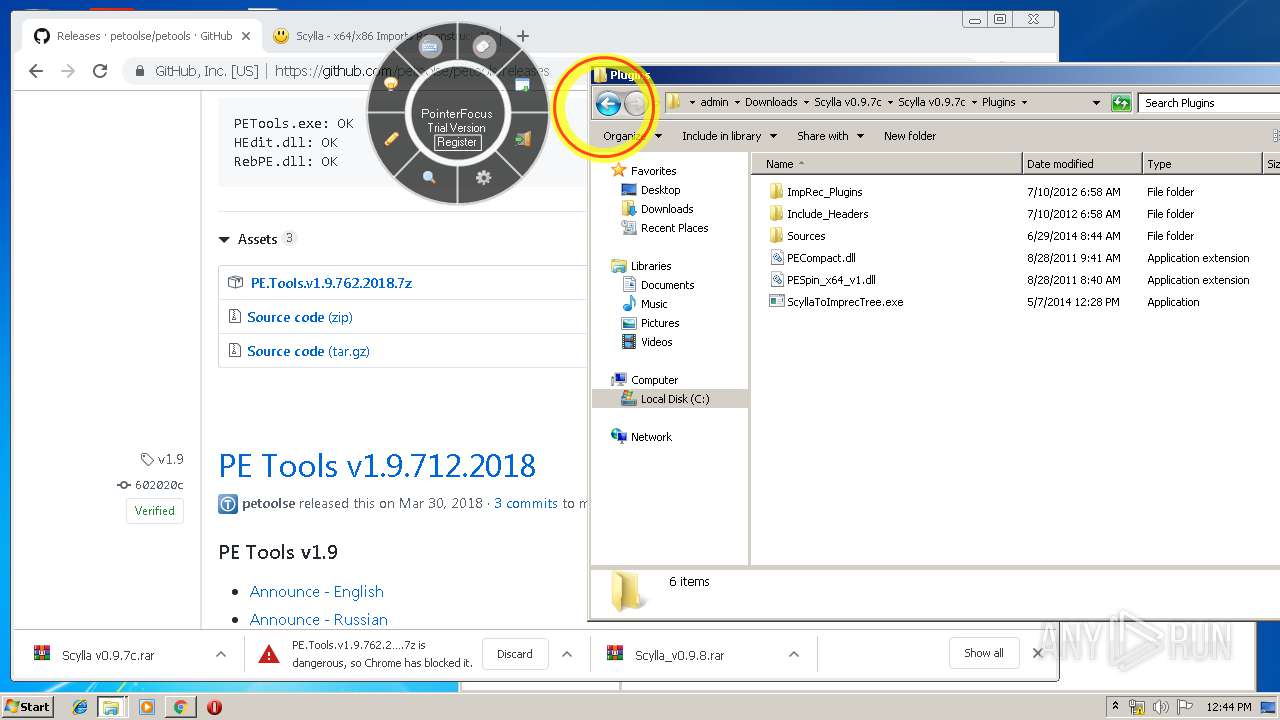
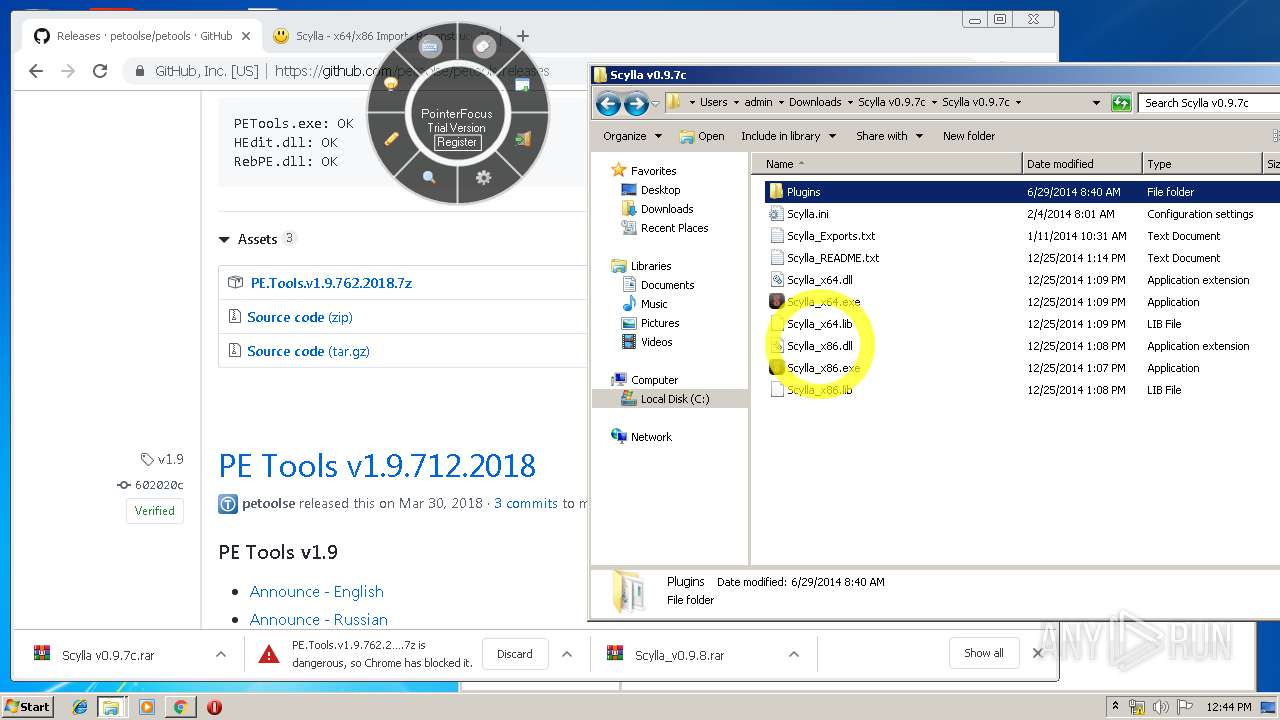
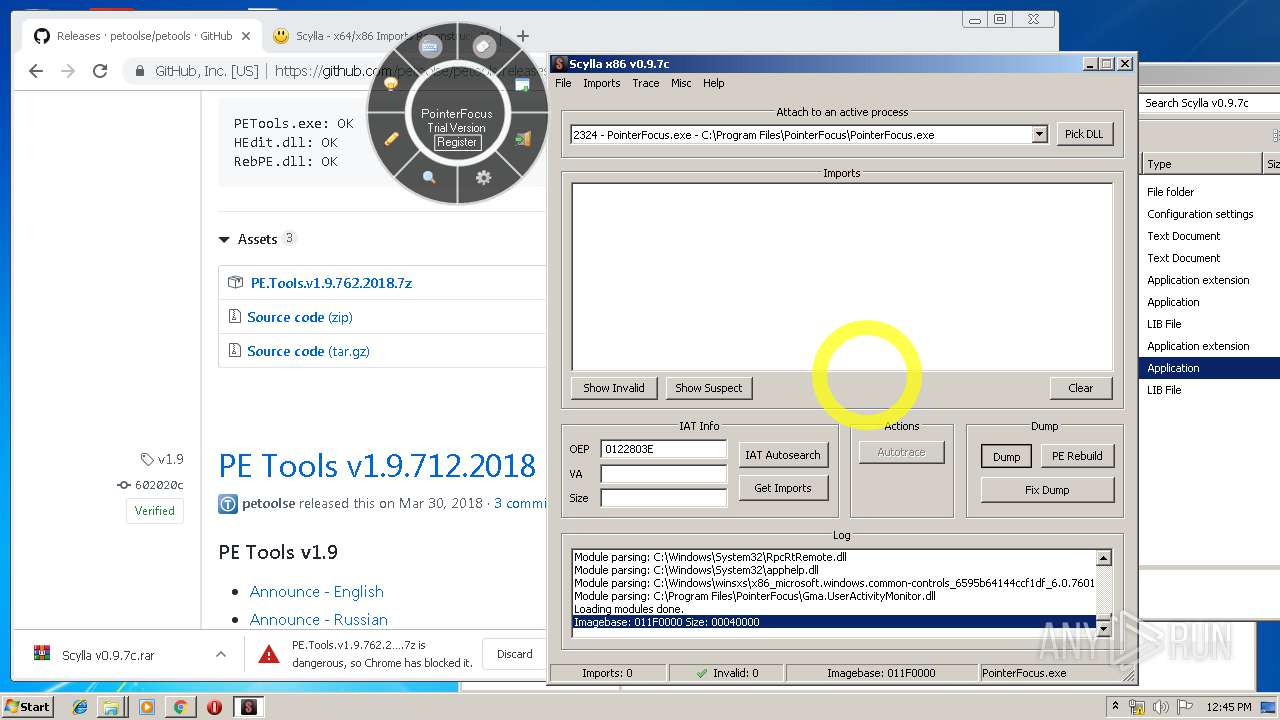
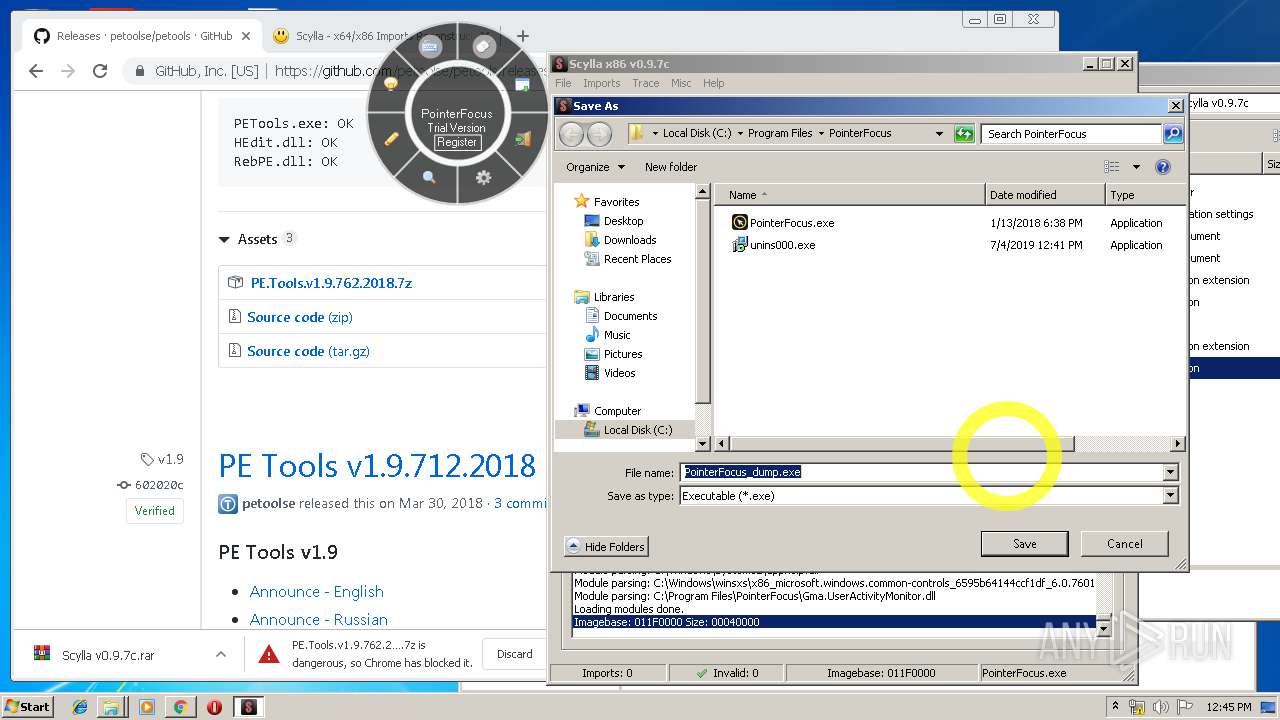
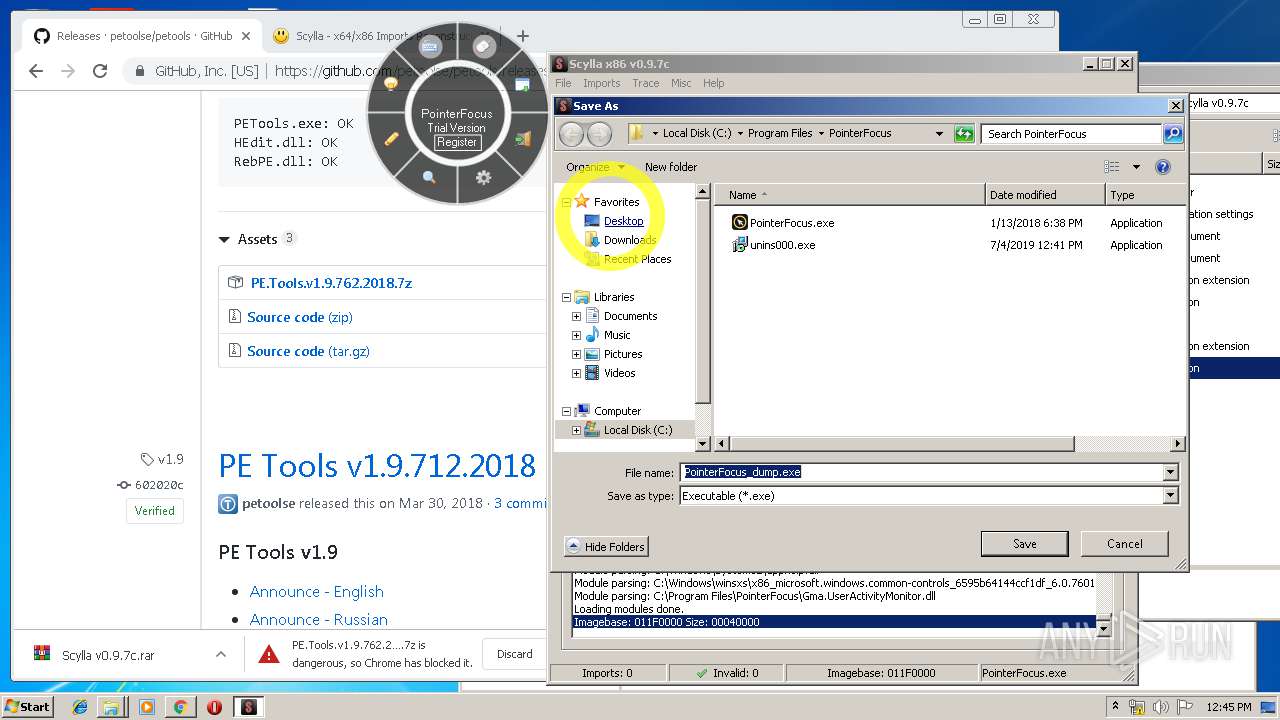
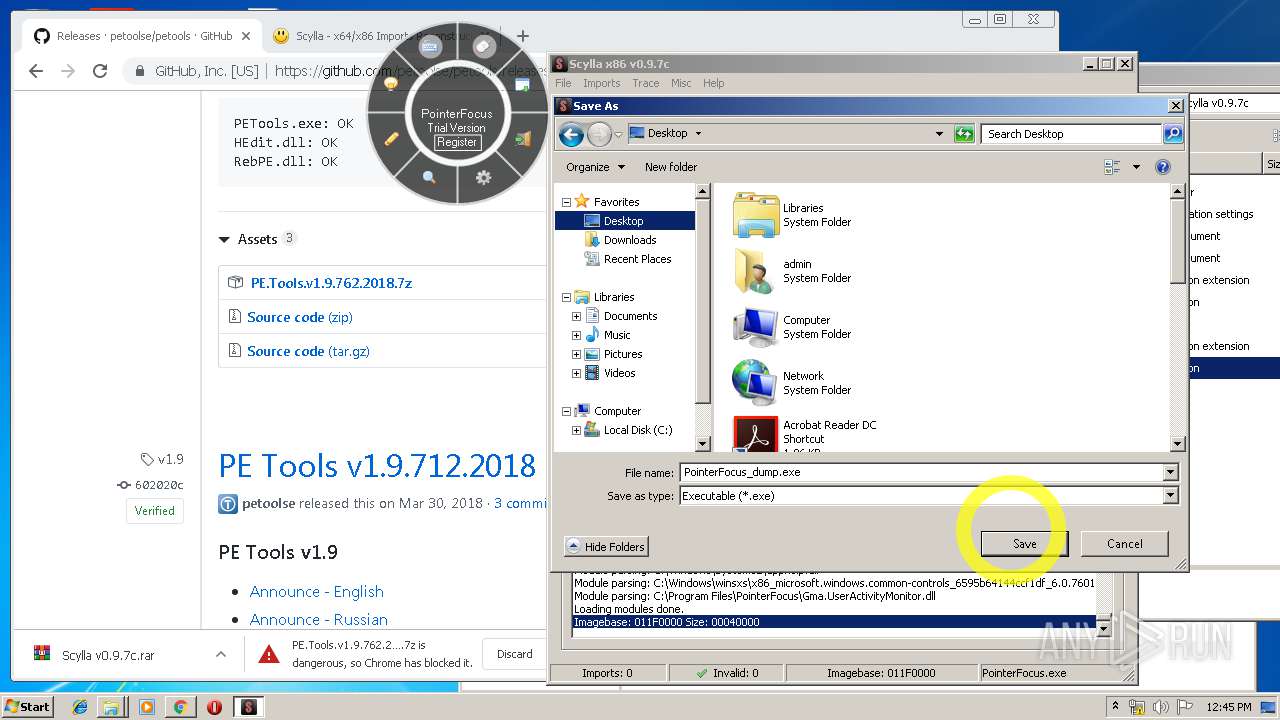
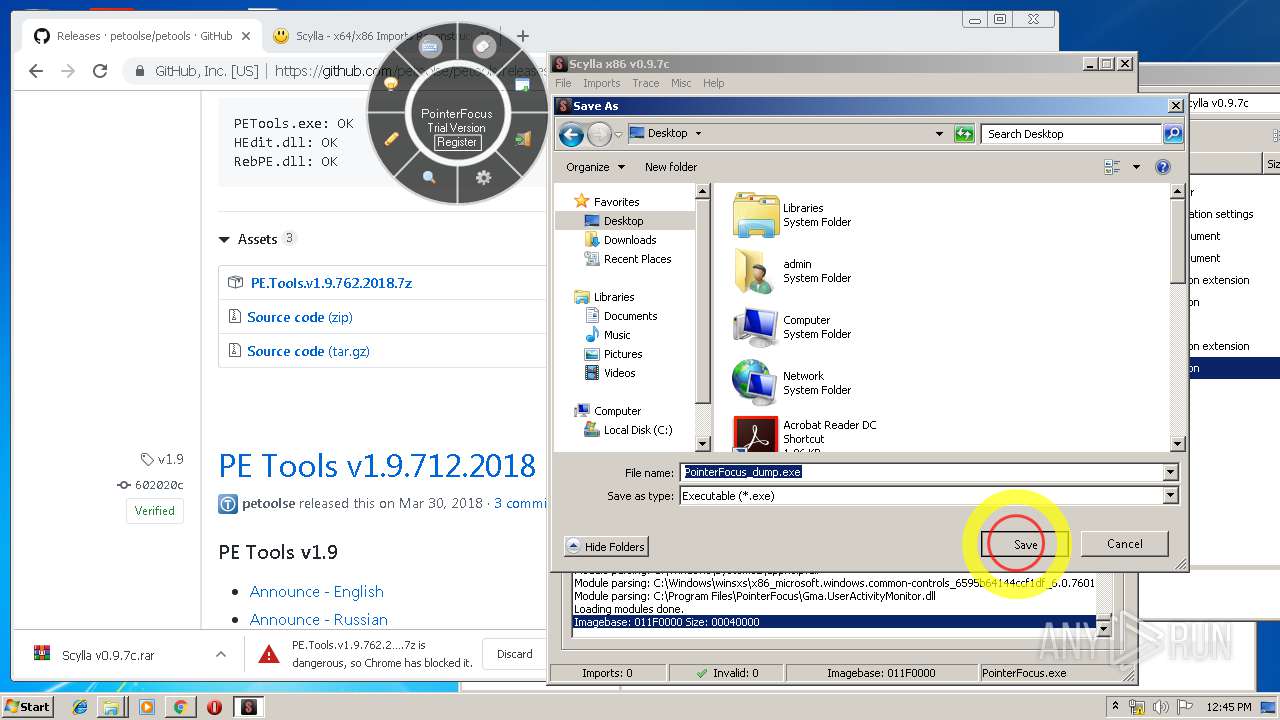
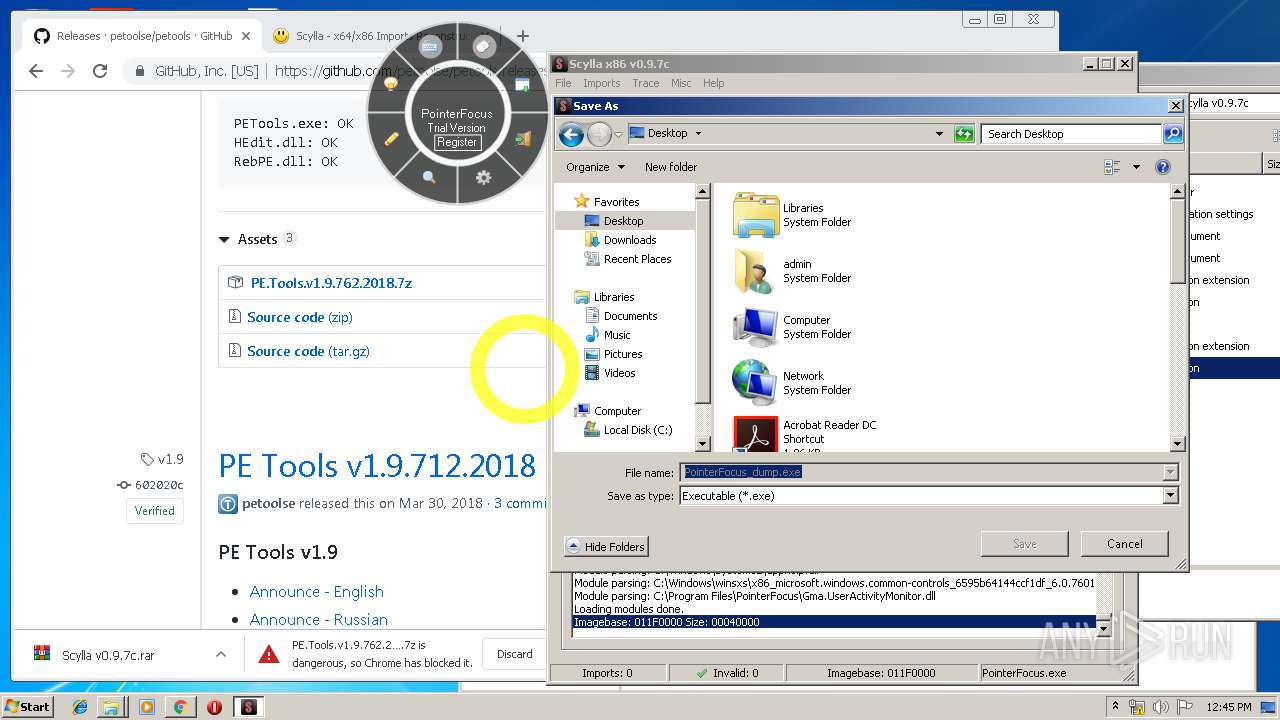
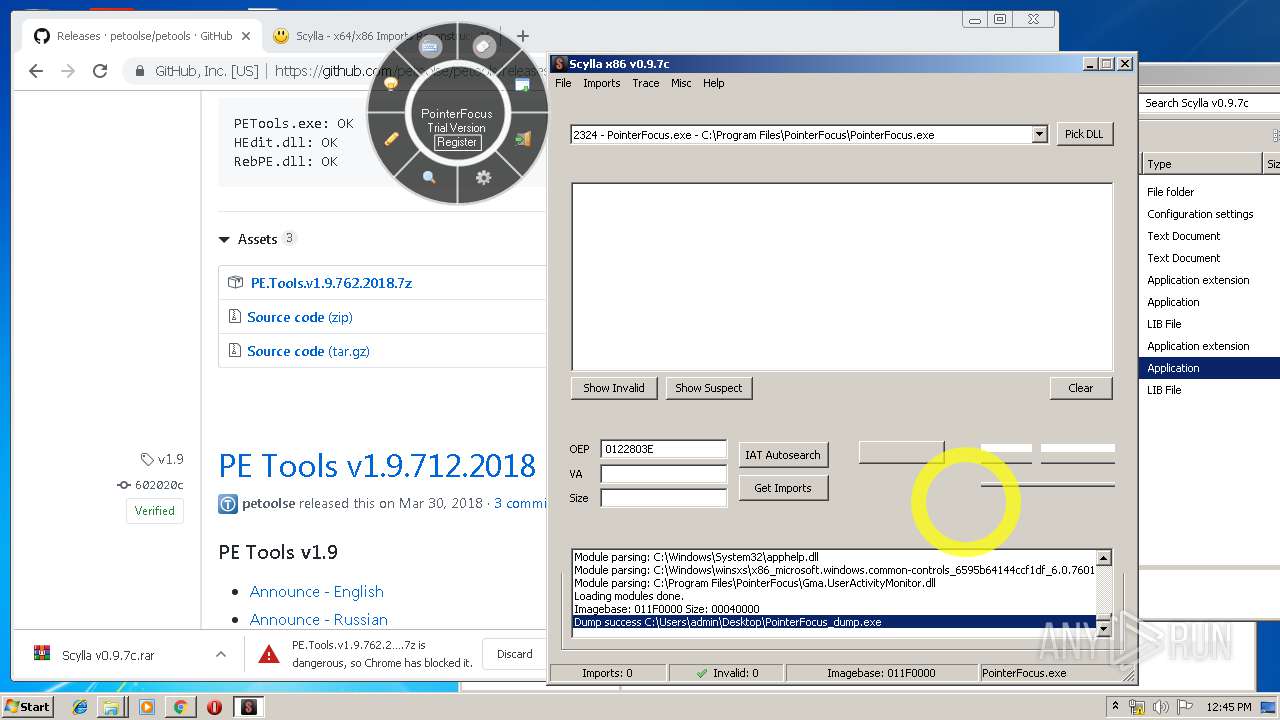
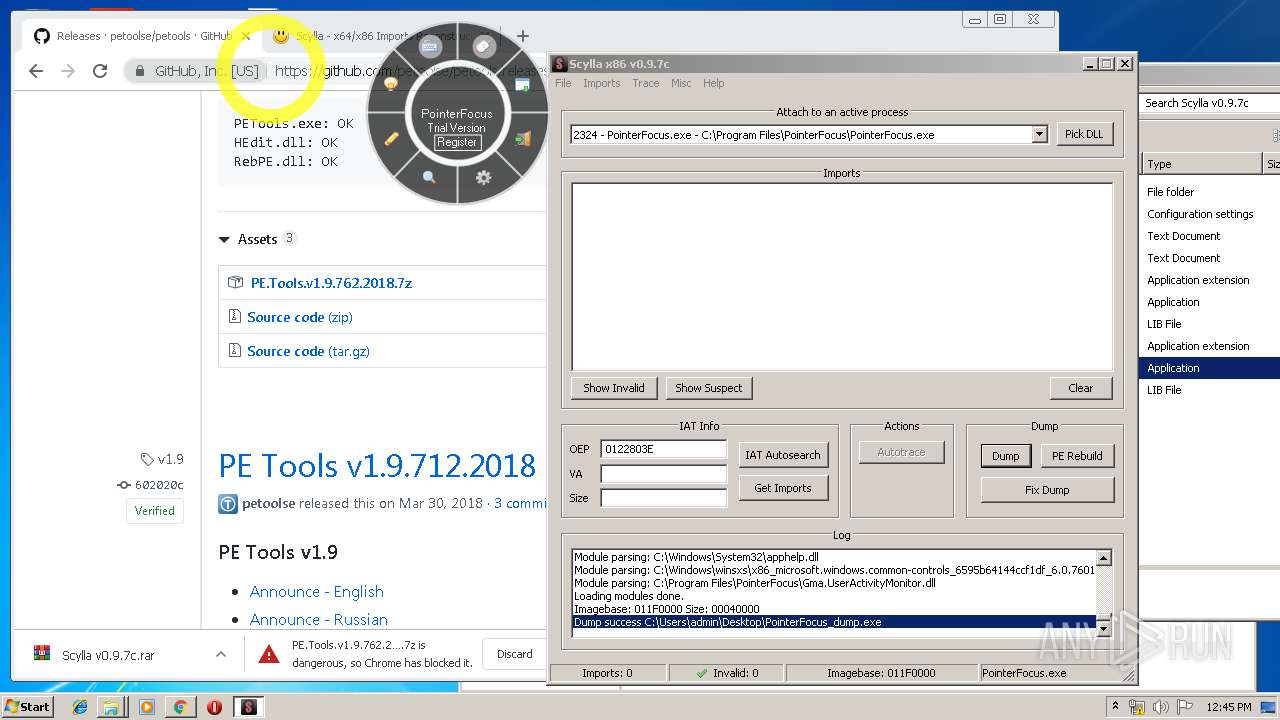
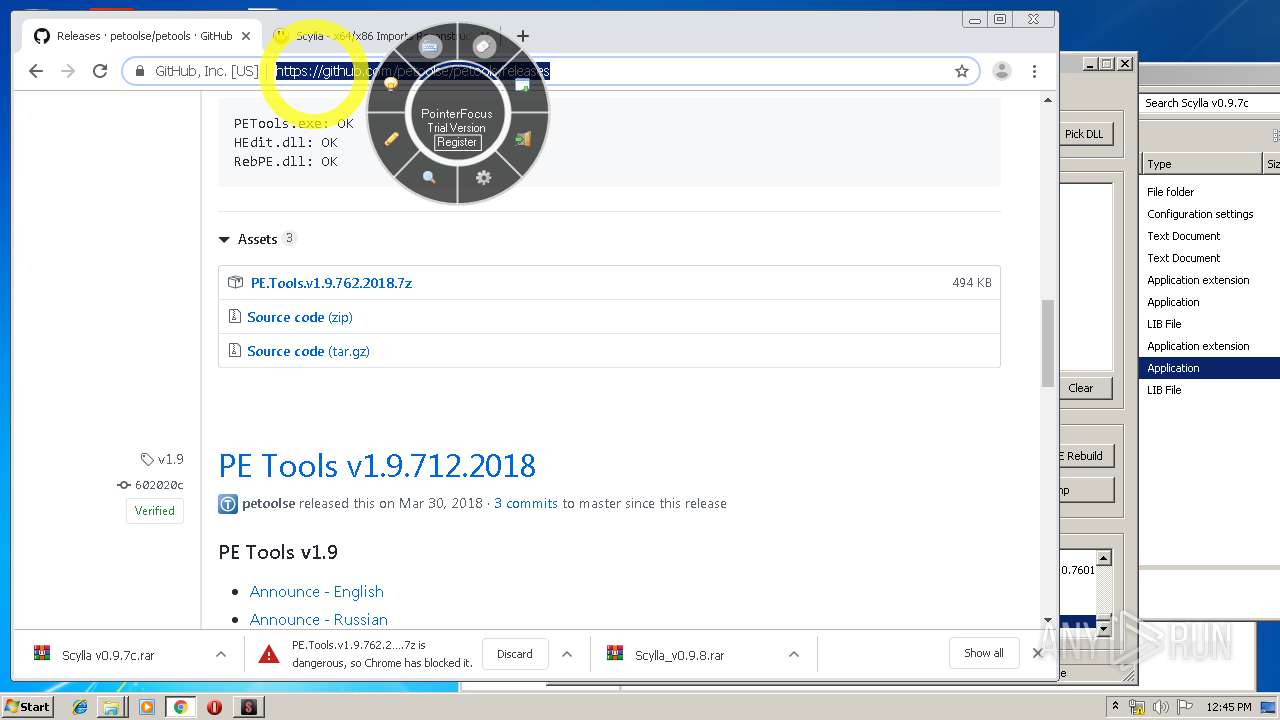
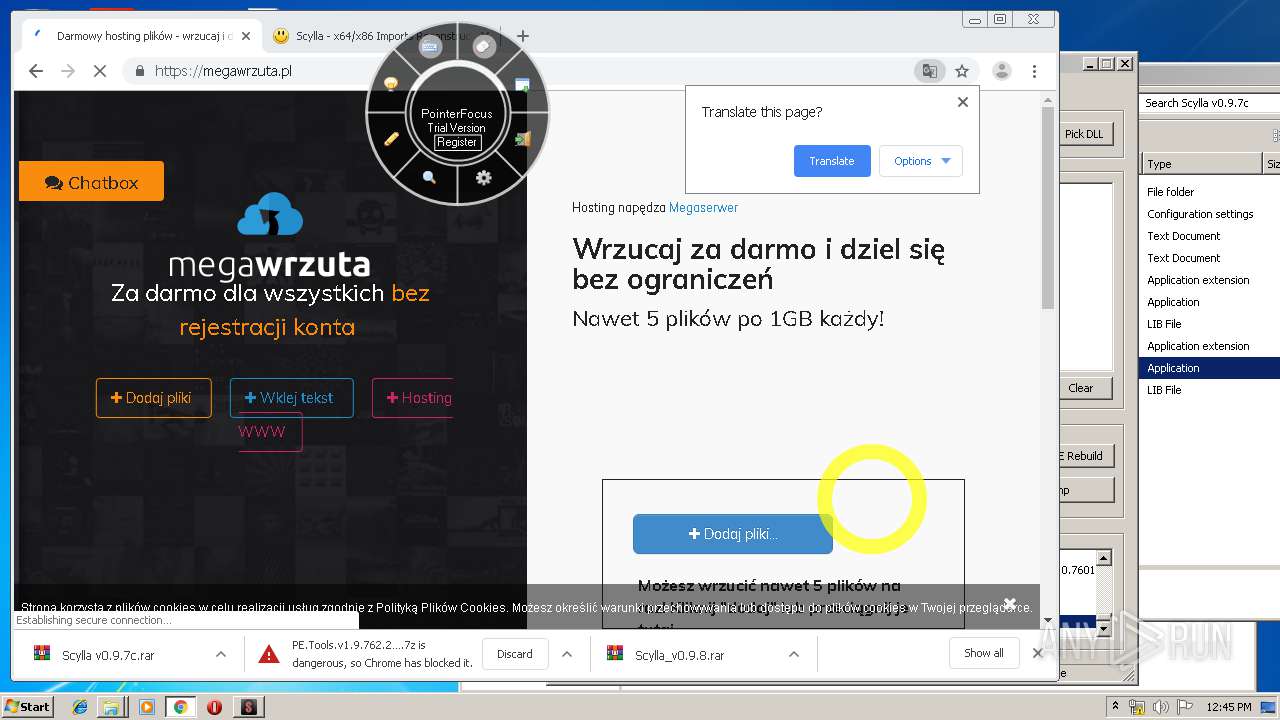
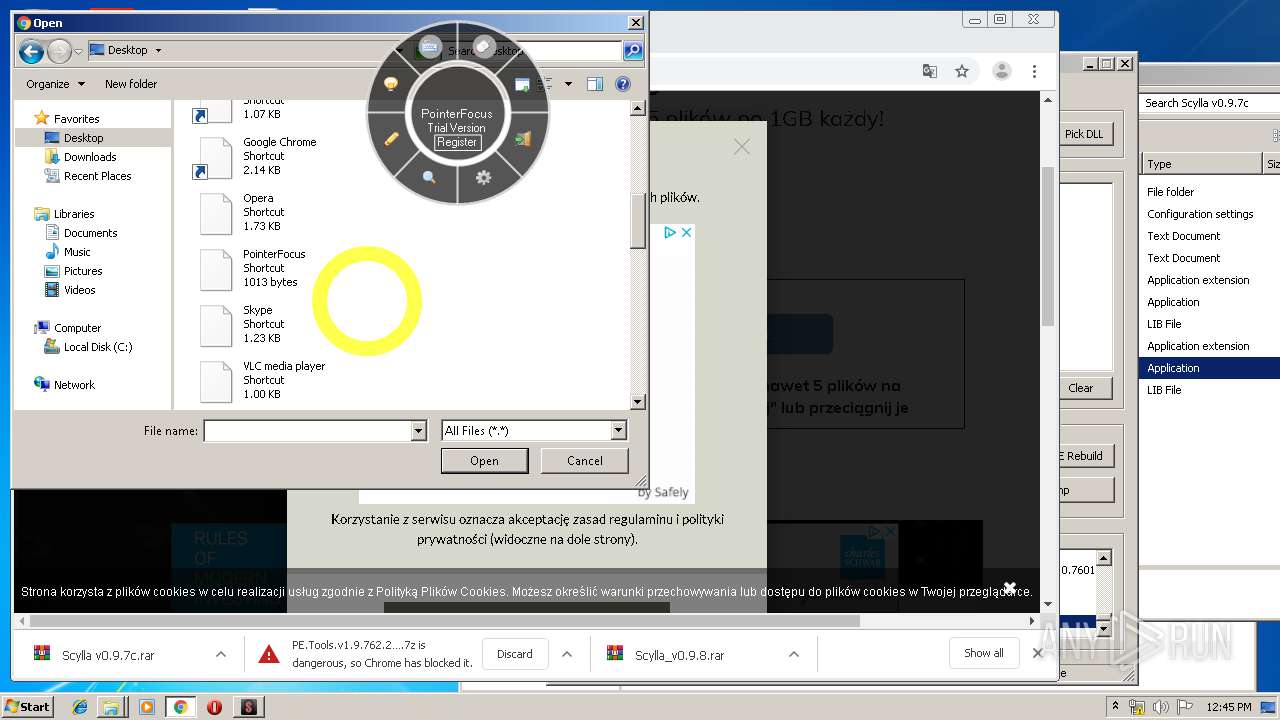
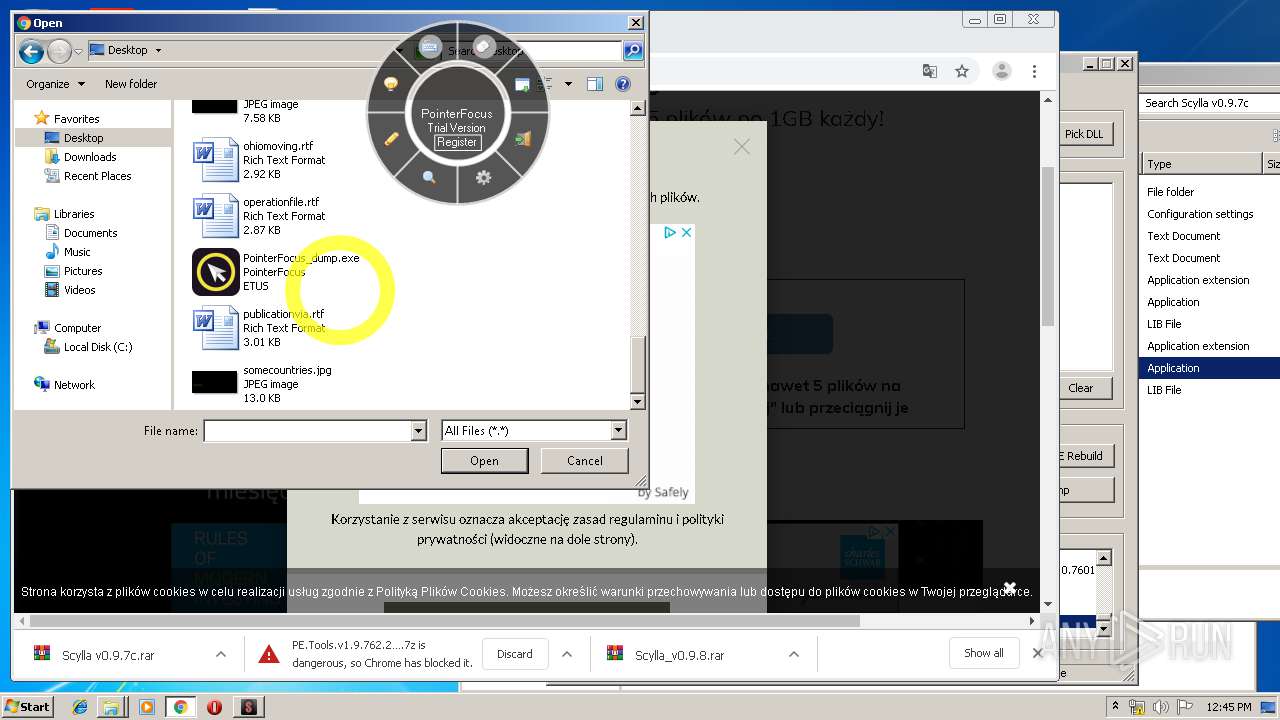
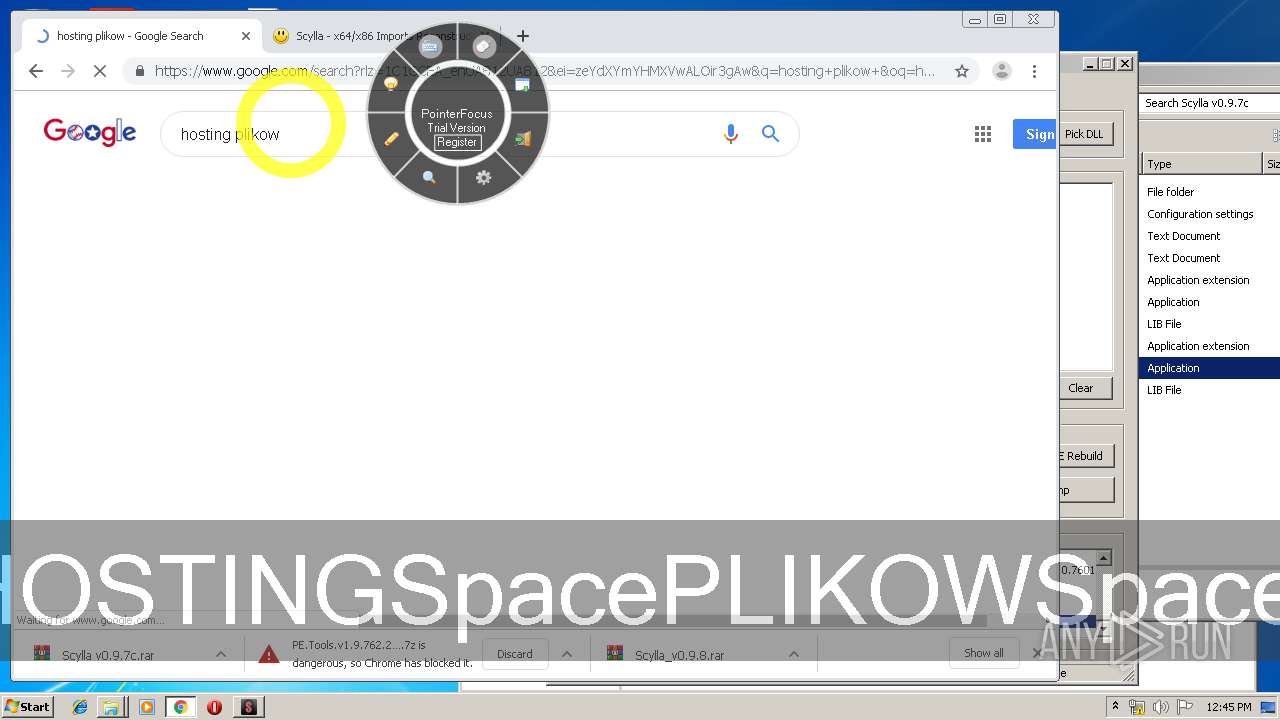
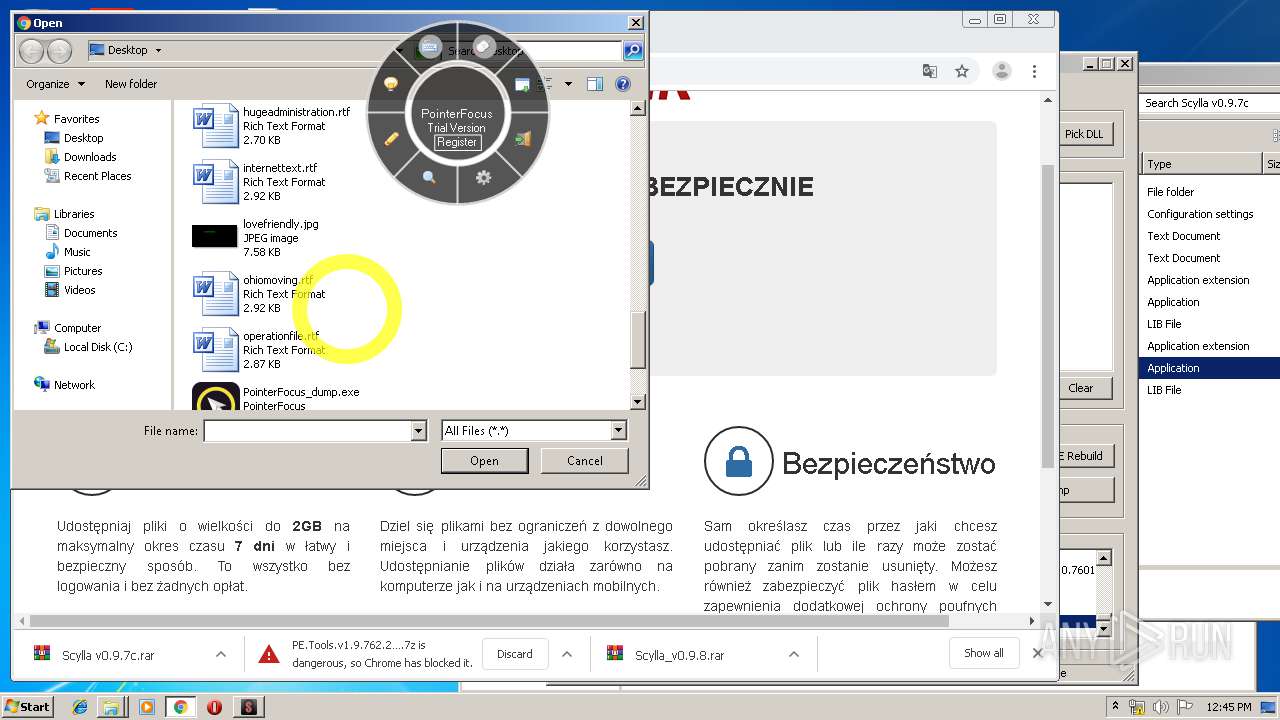
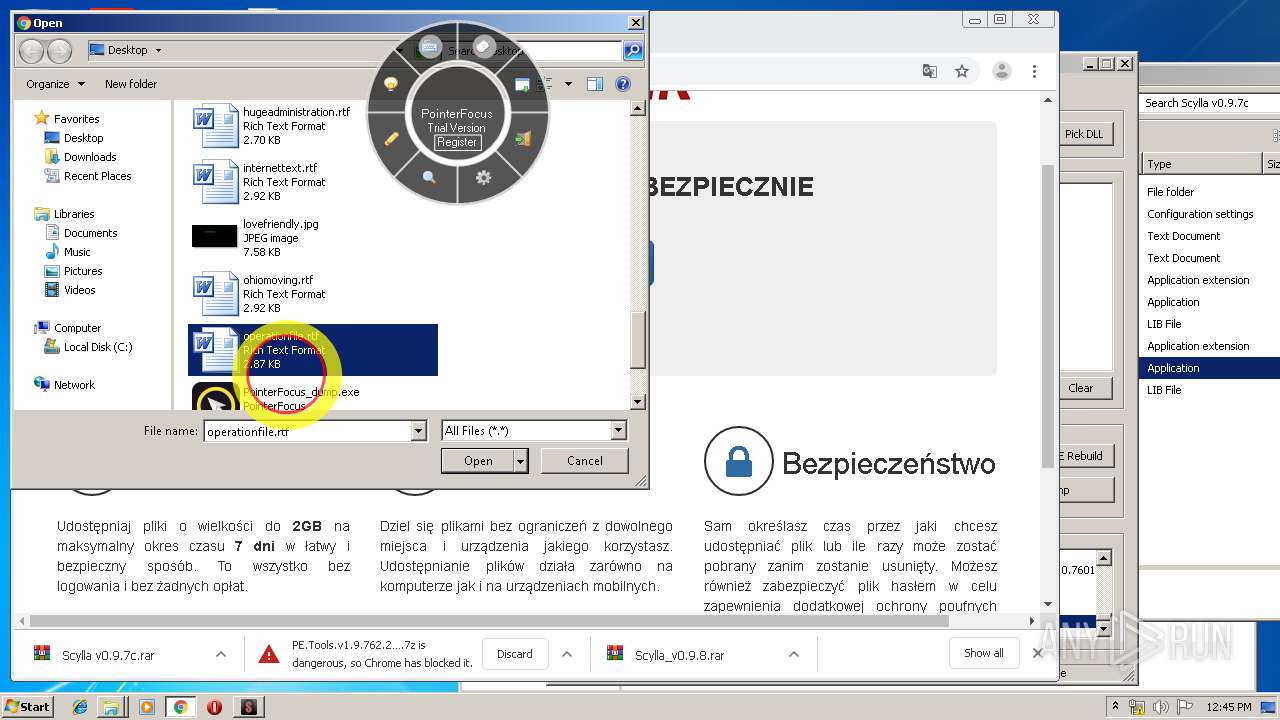
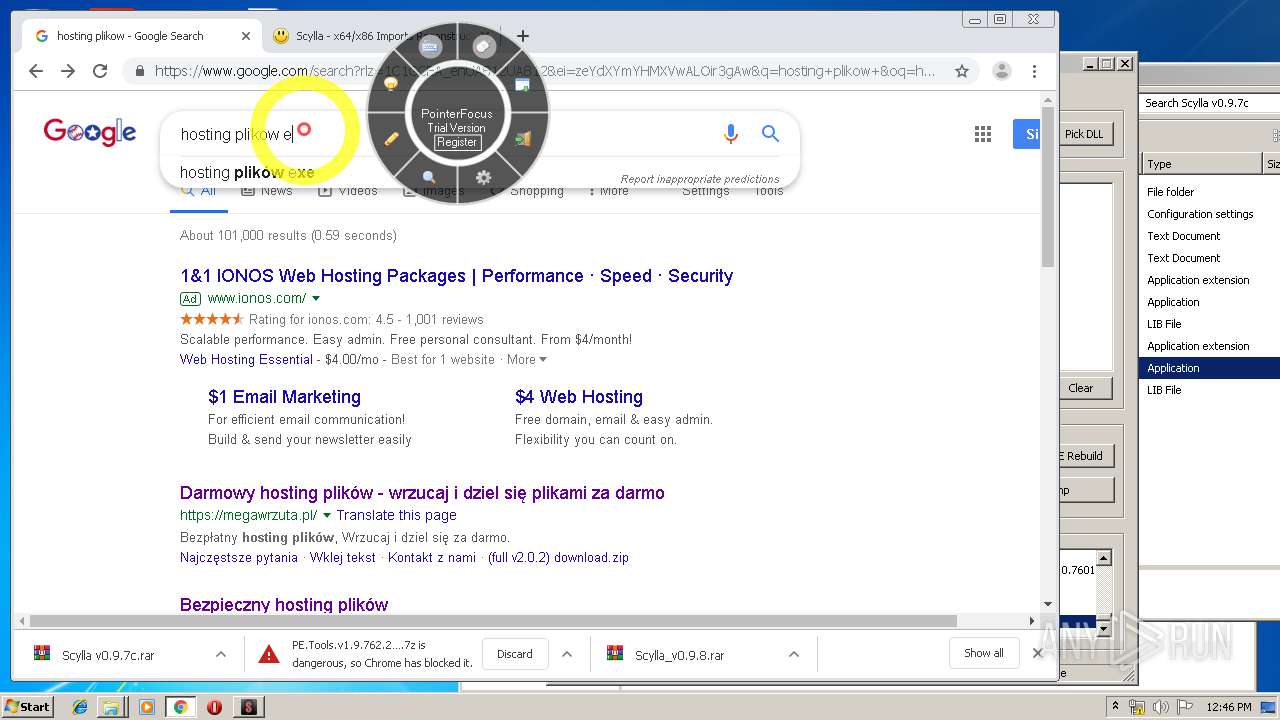
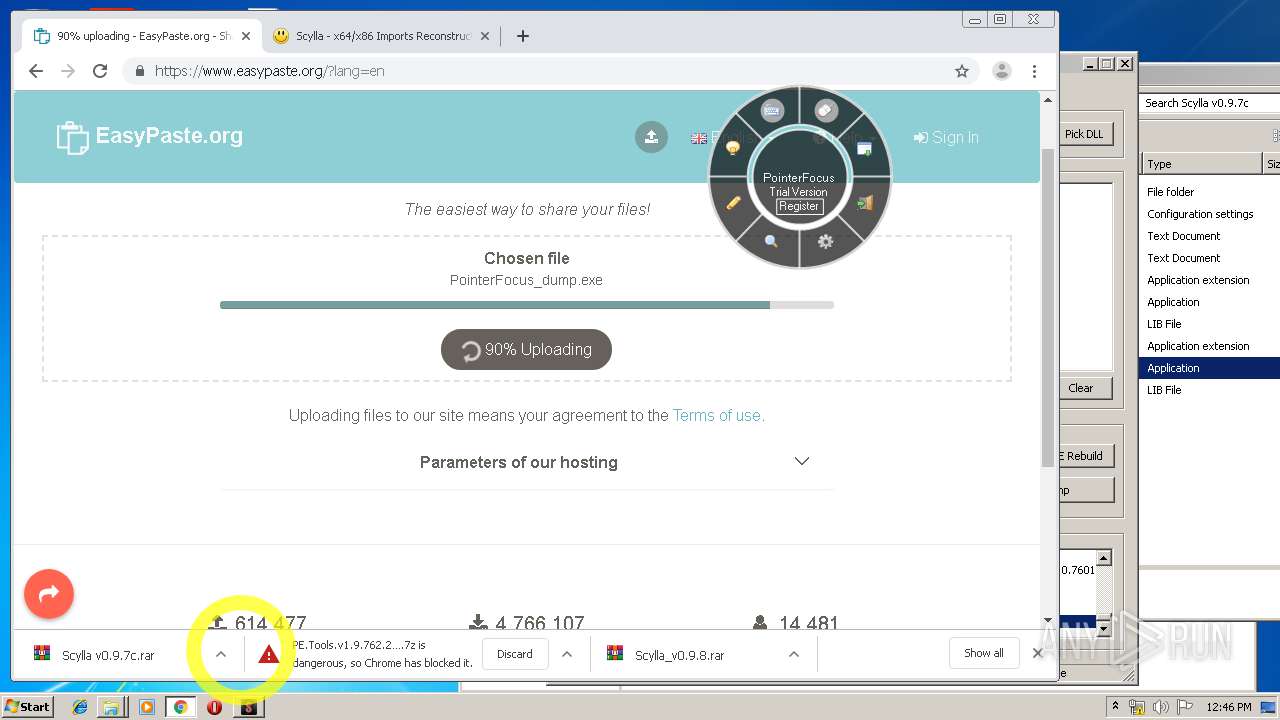
Application was dropped or rewritten from another process
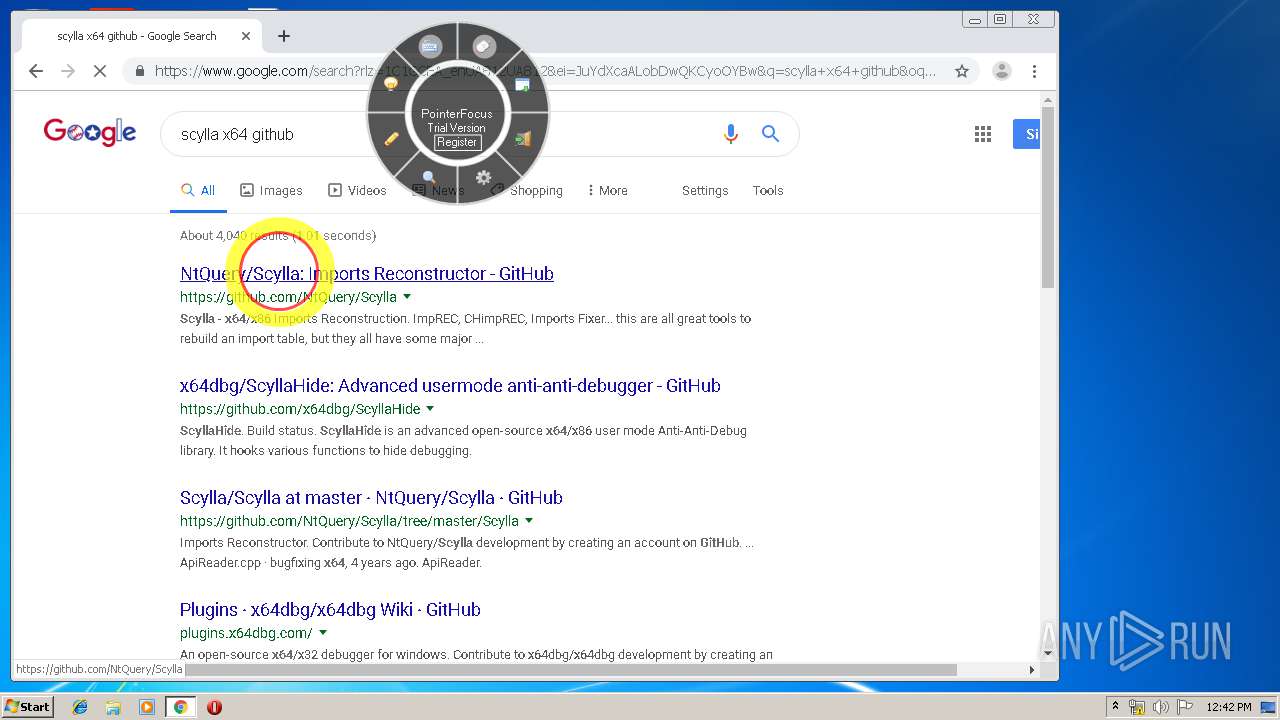
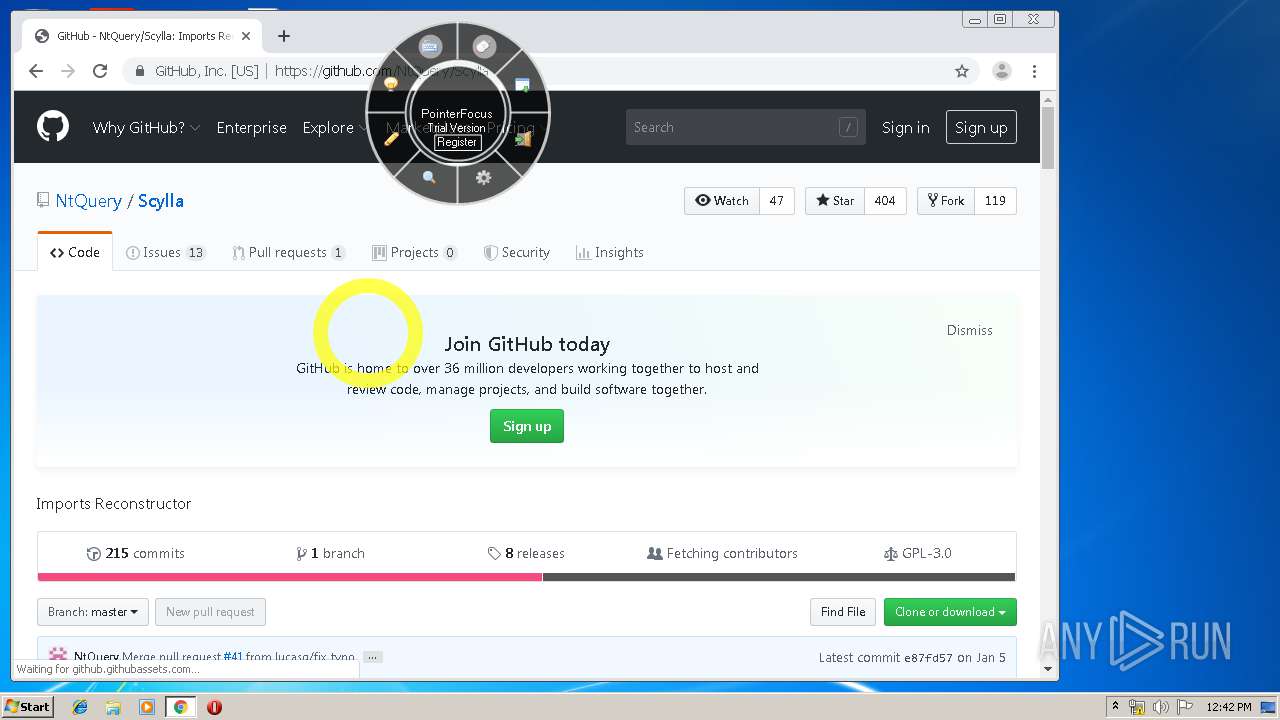
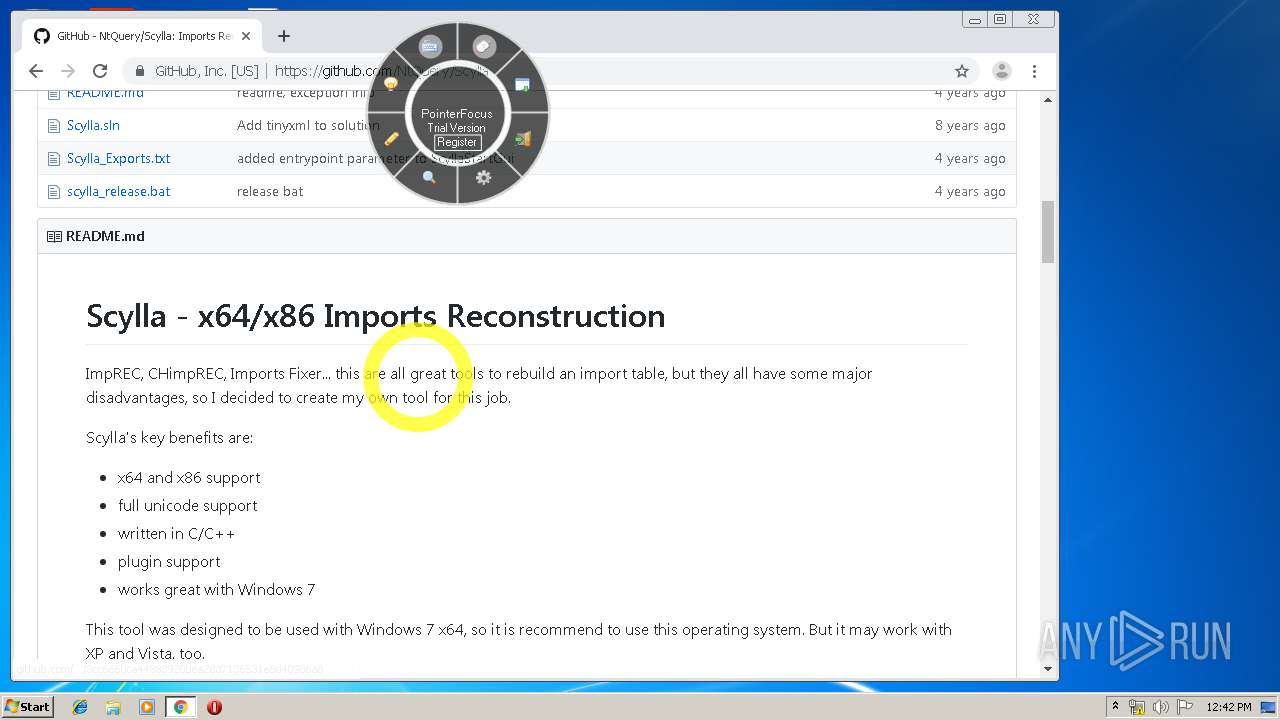
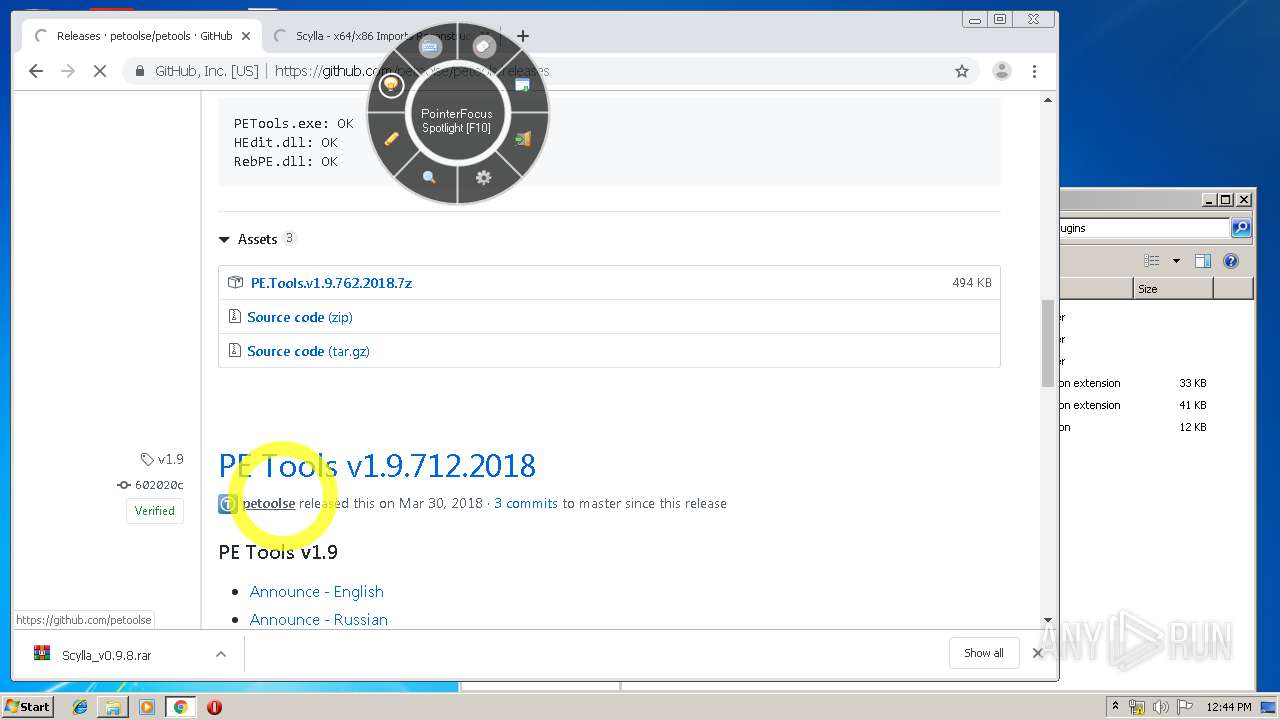
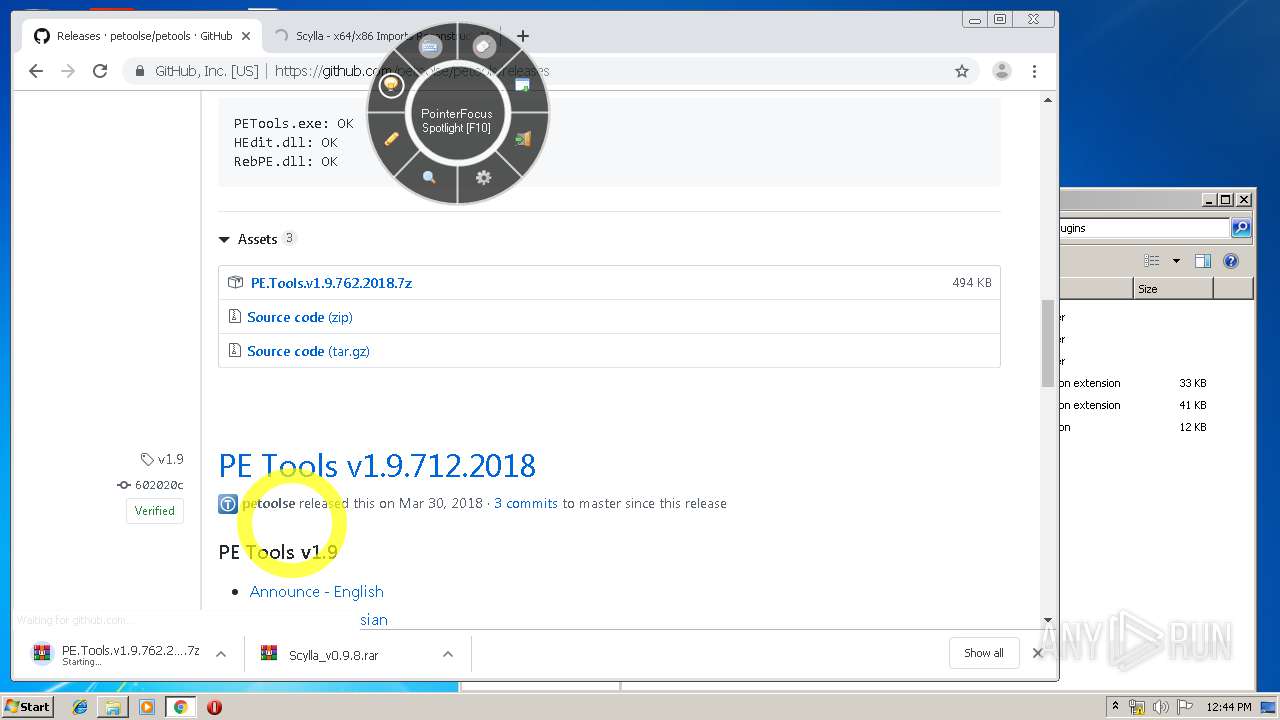
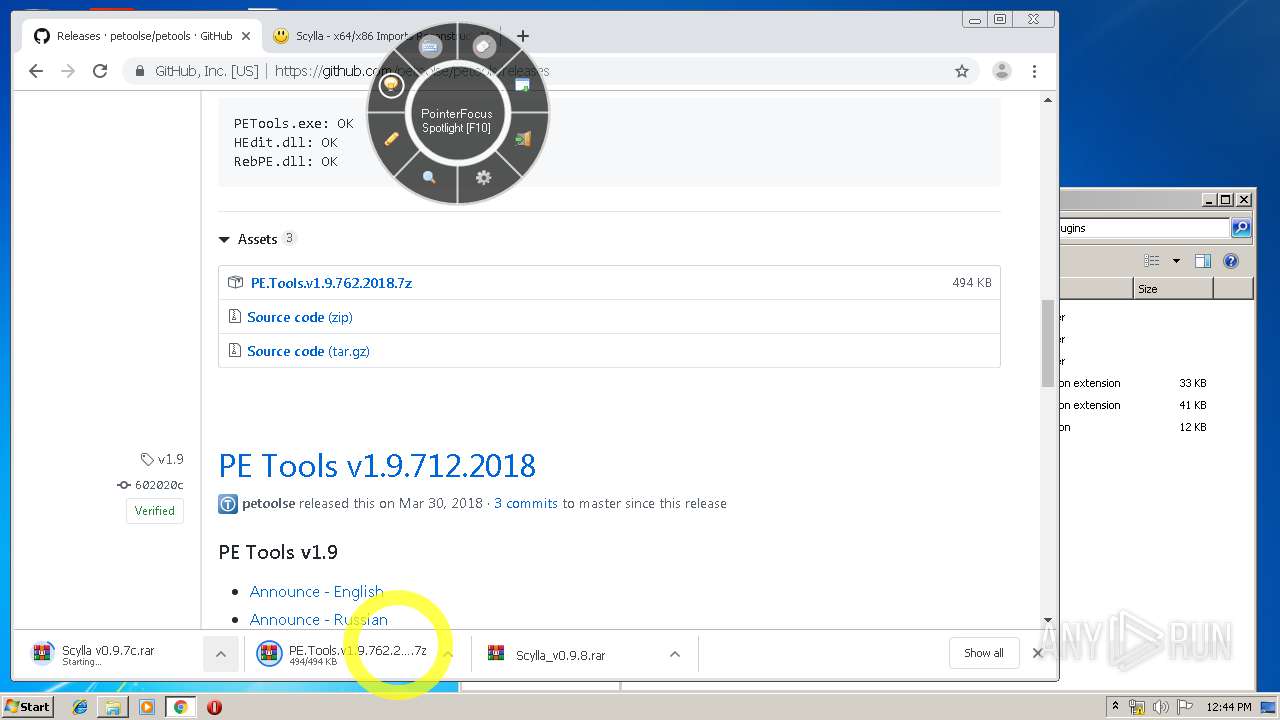
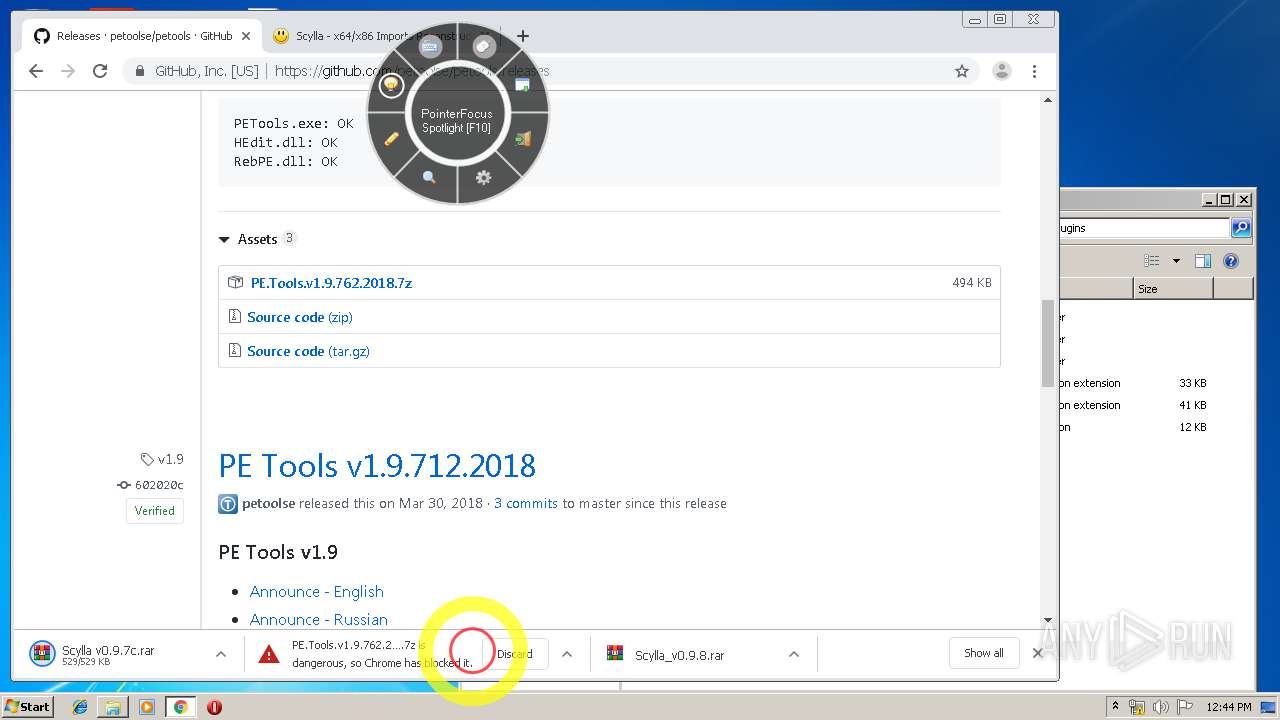
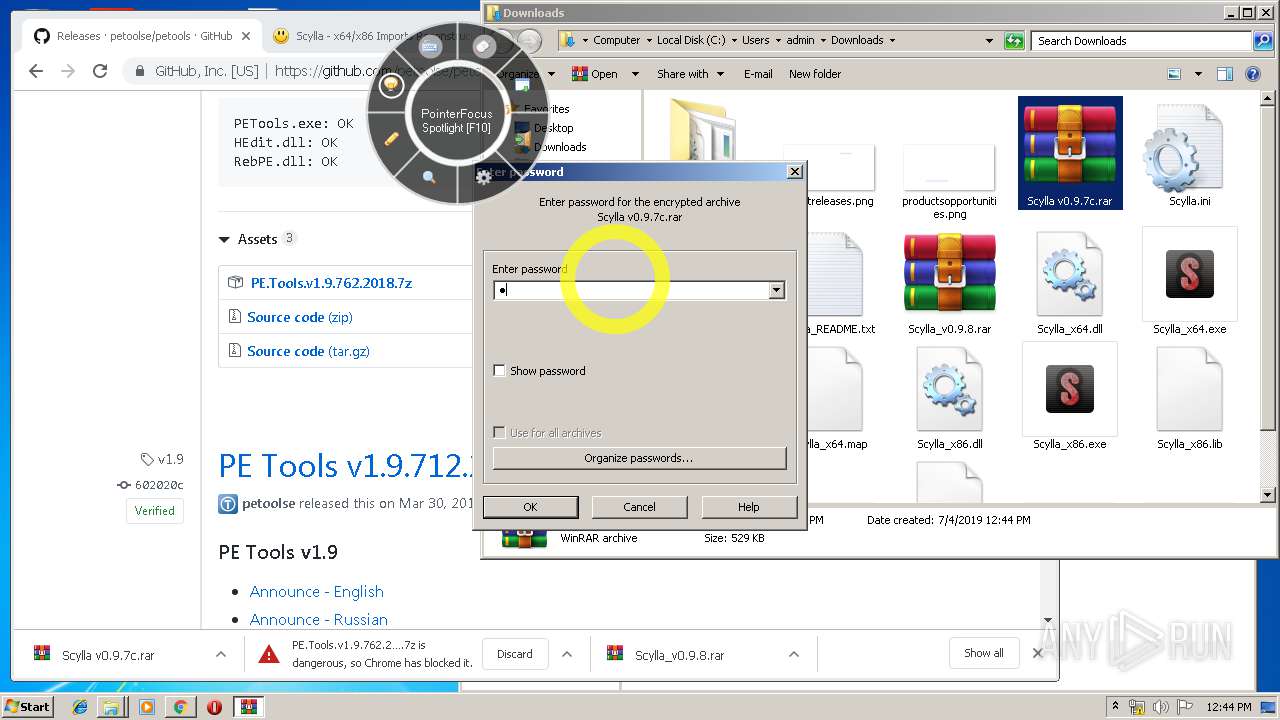
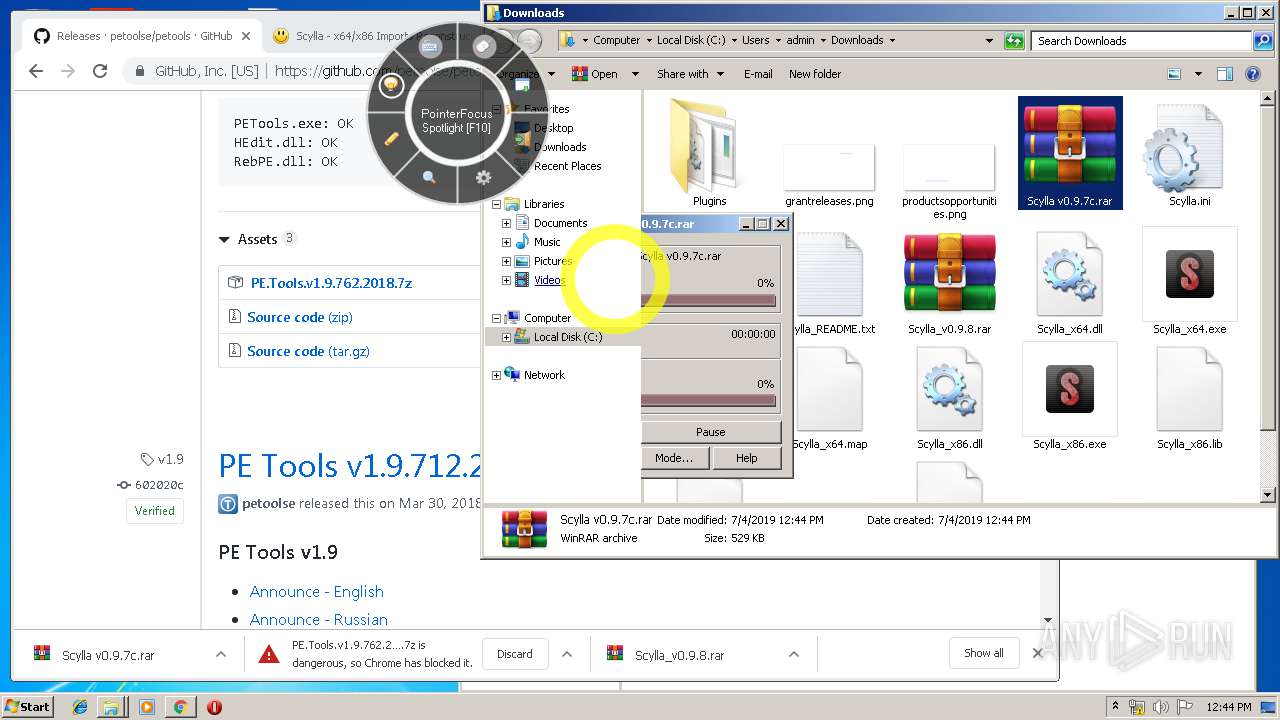
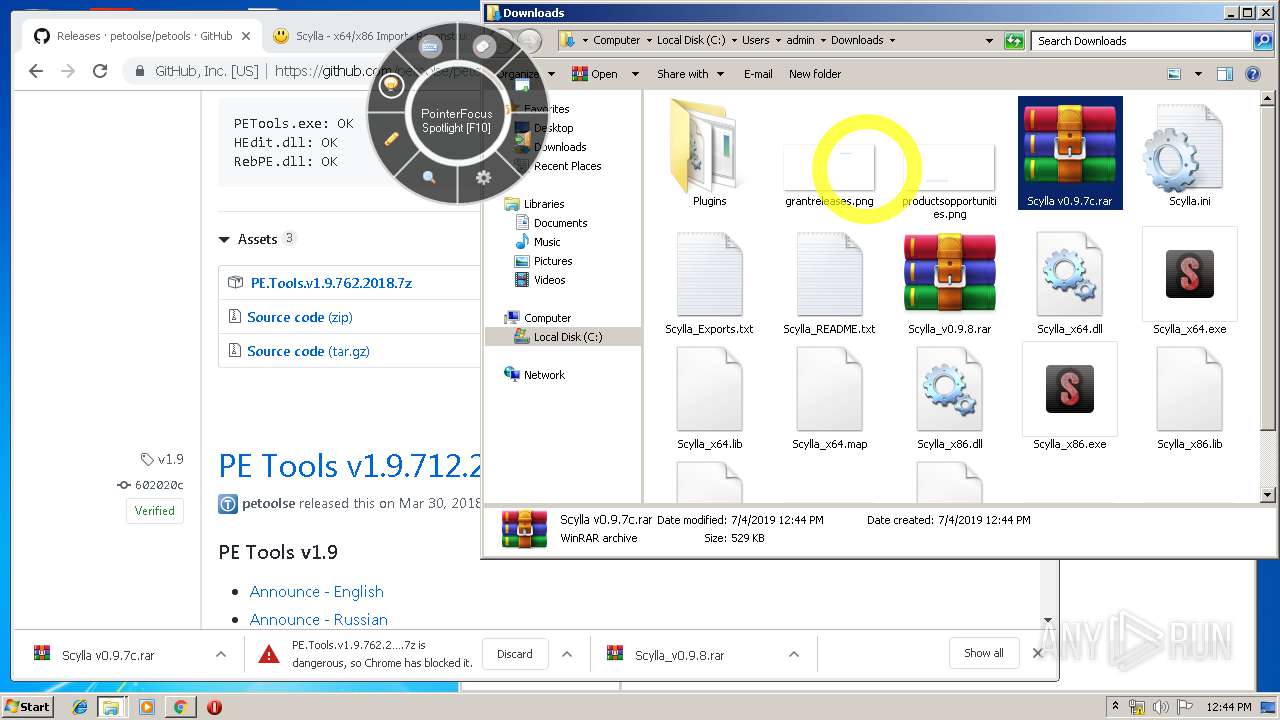
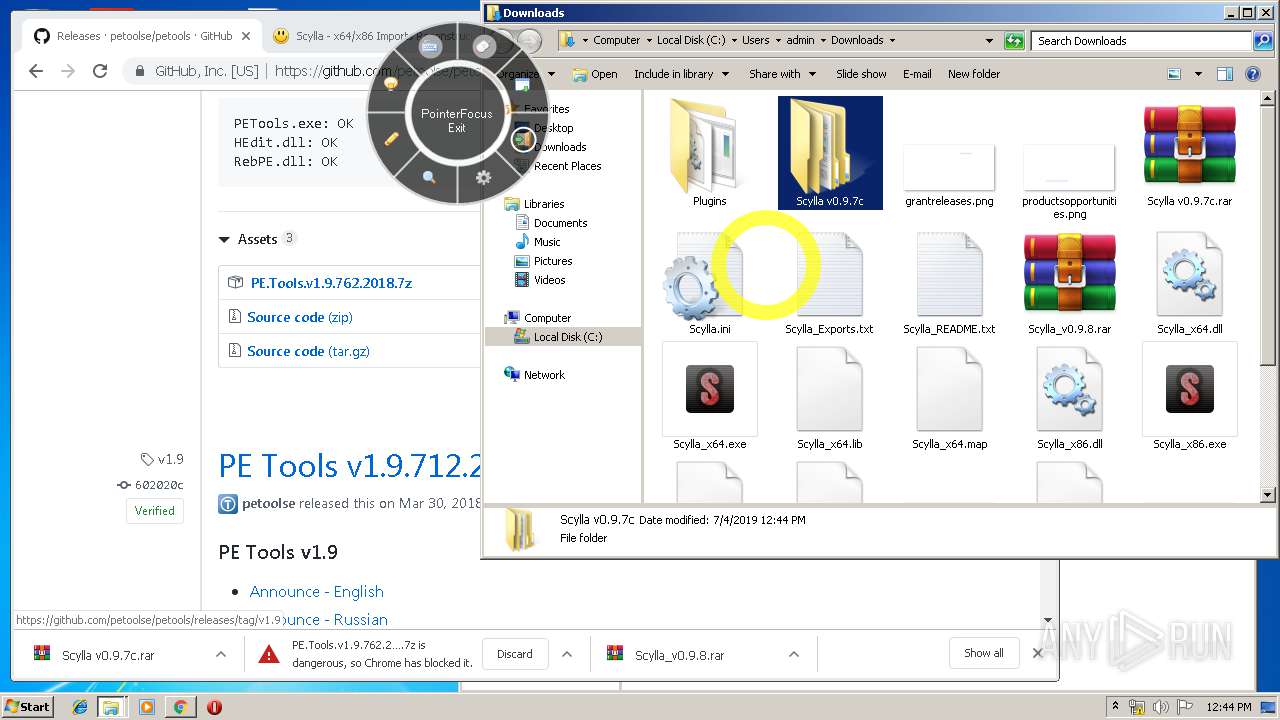
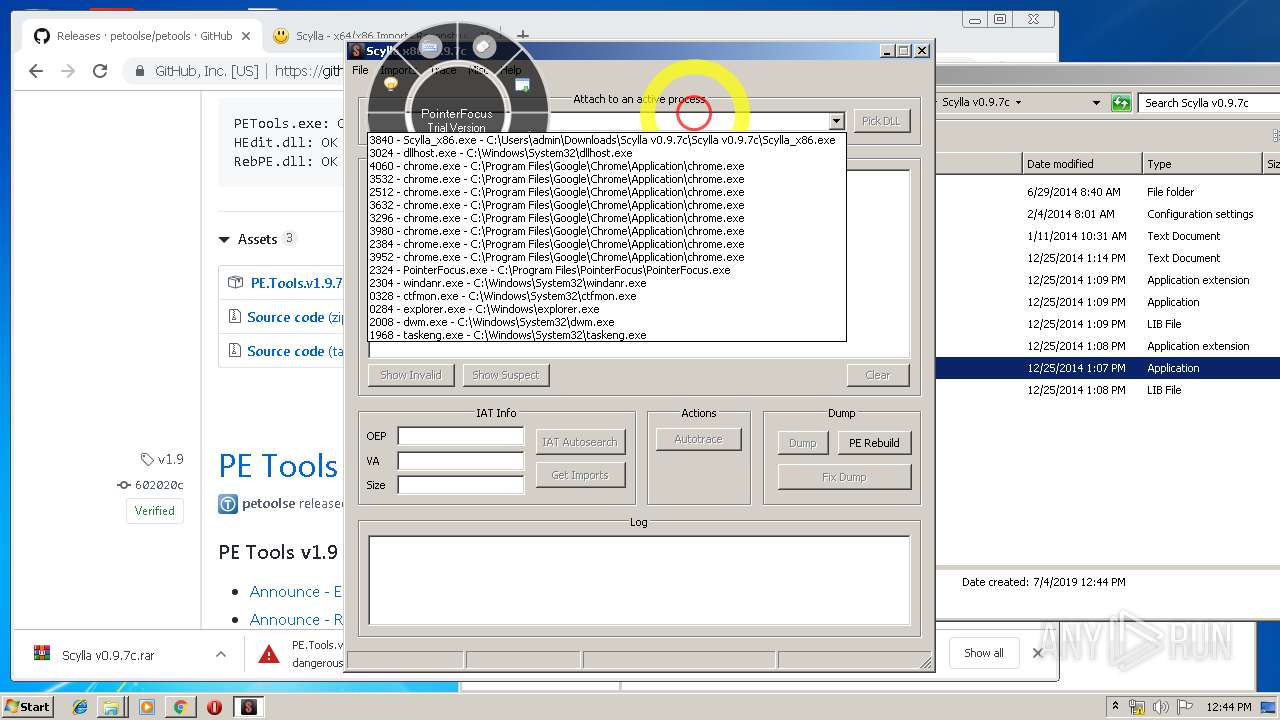
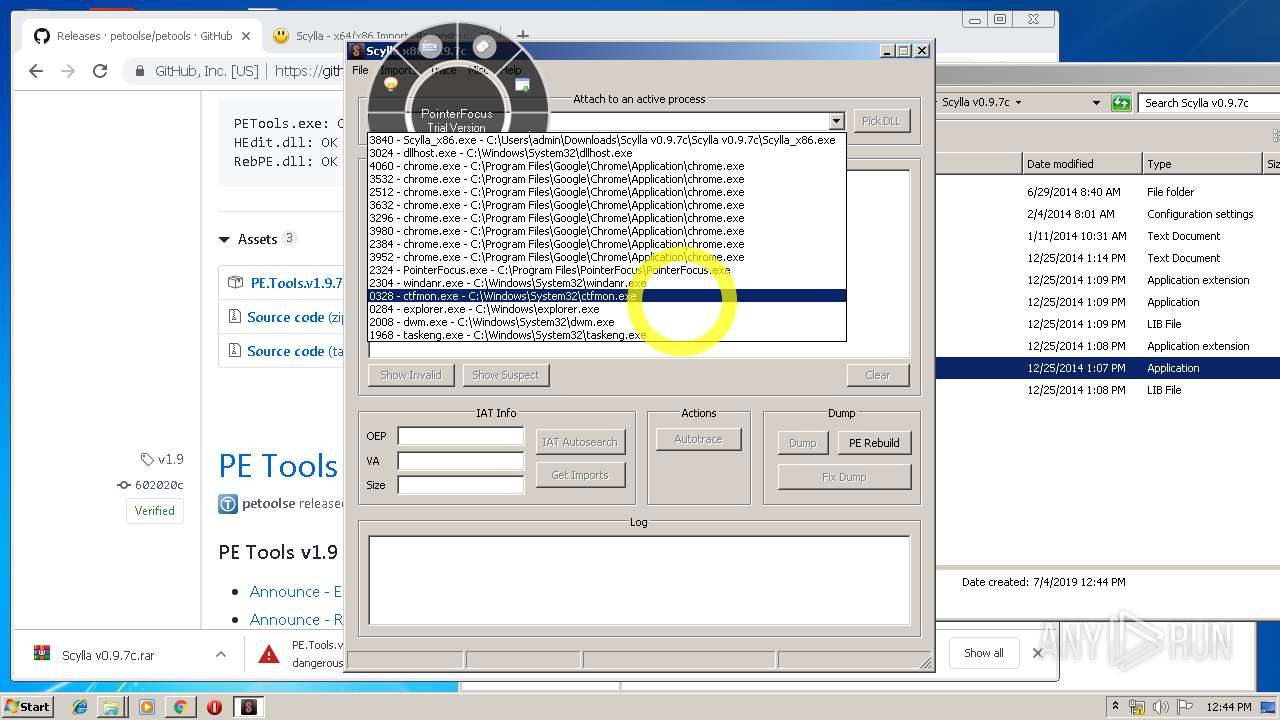
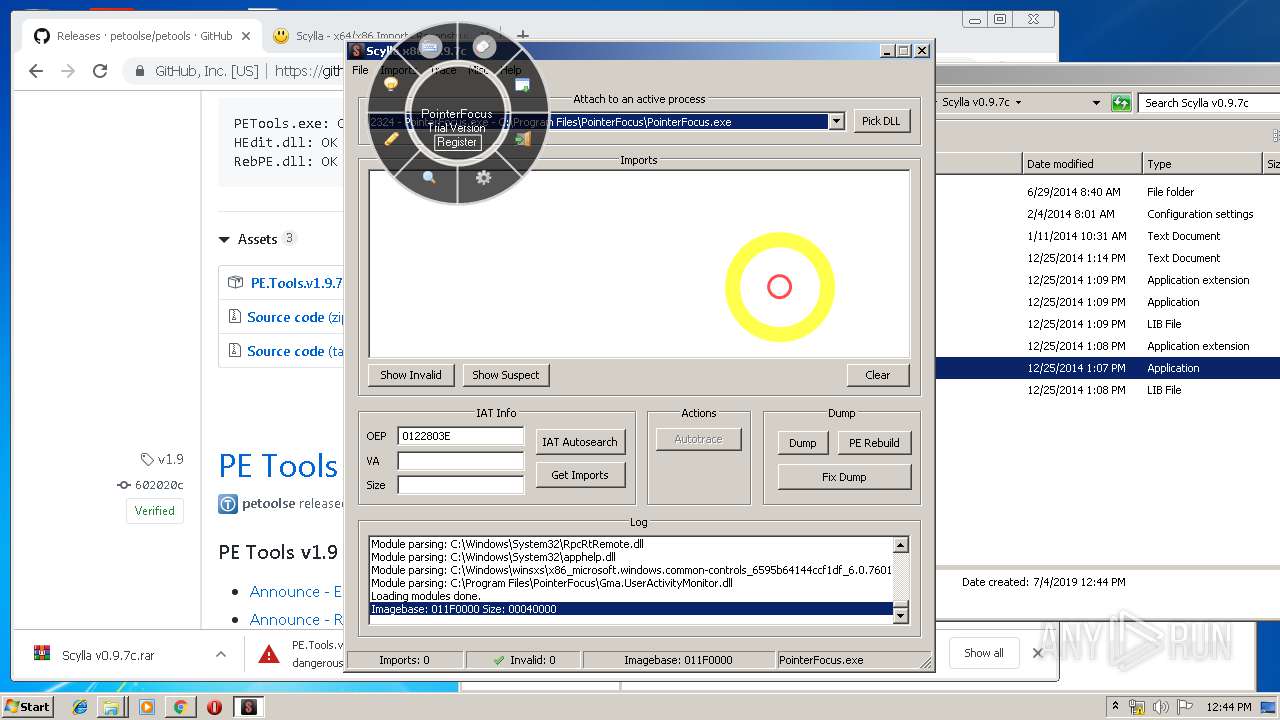
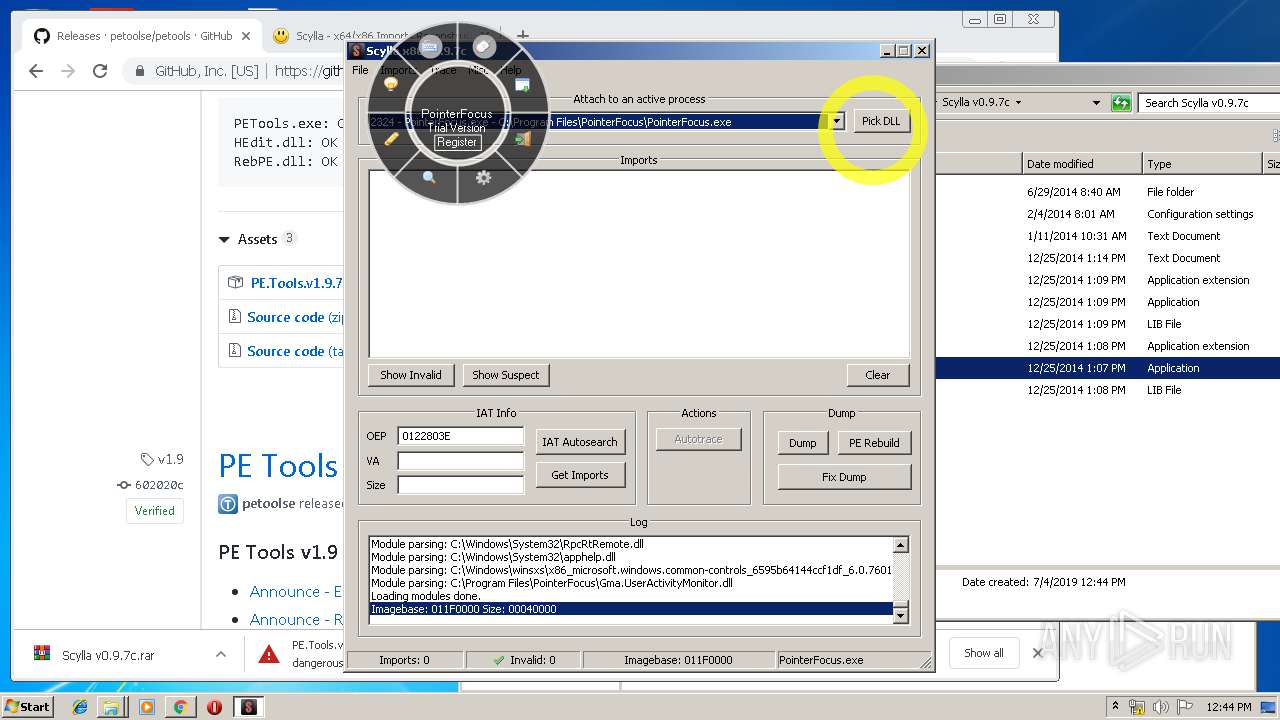
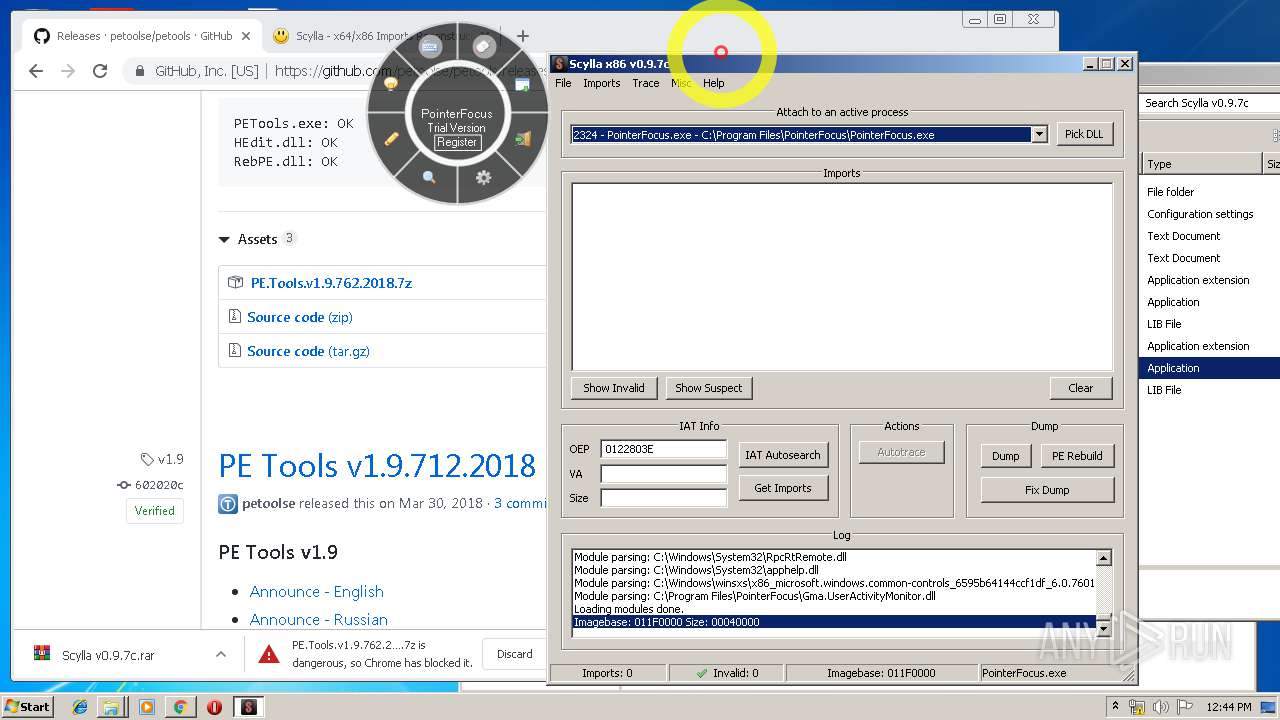
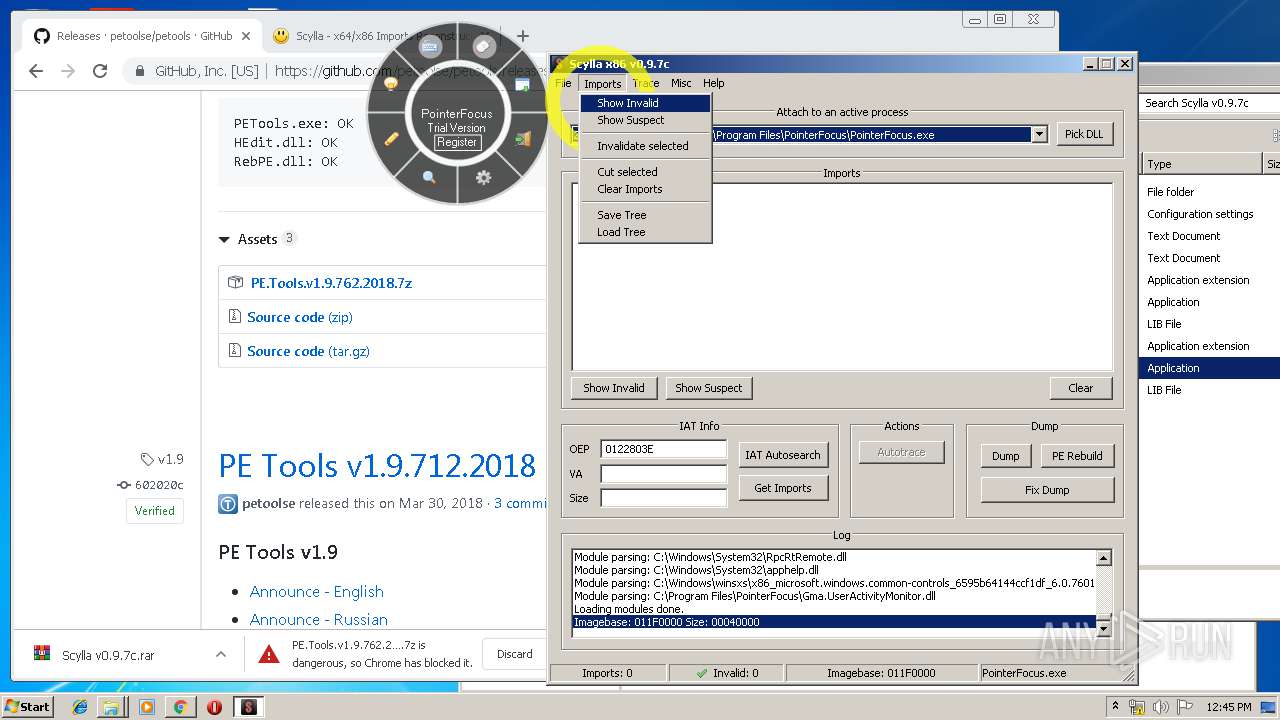
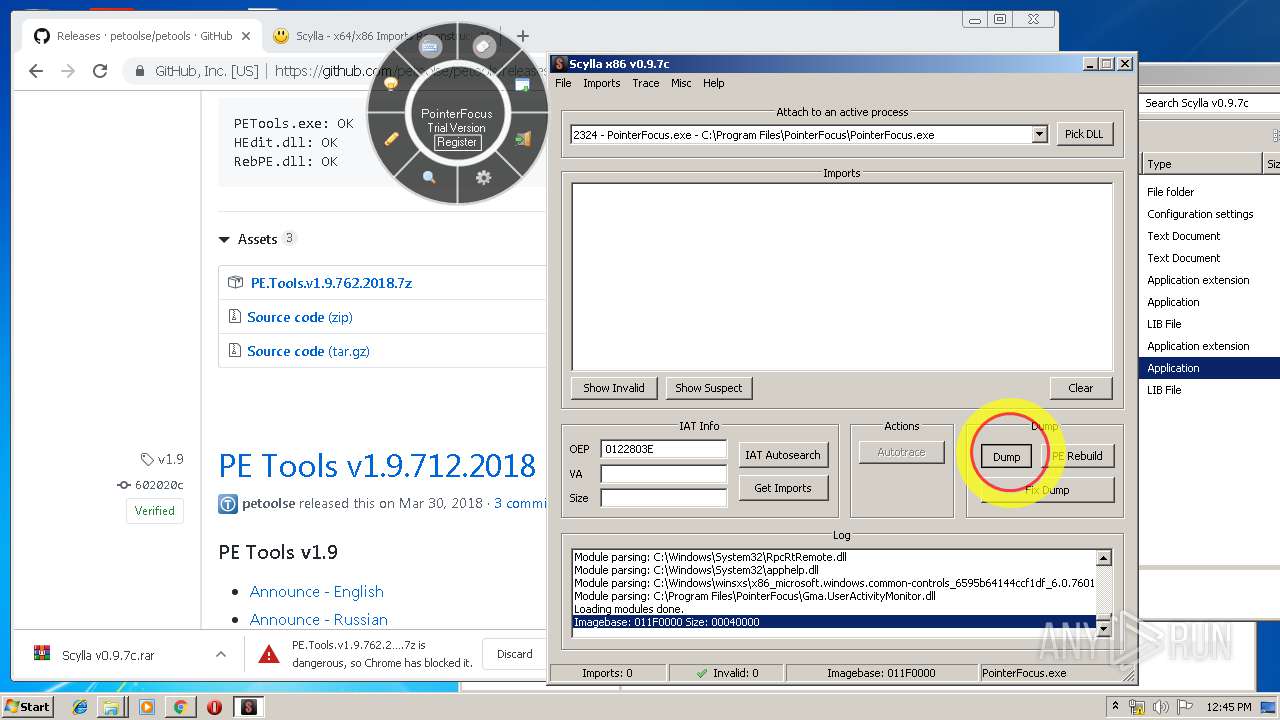
- PointerFocus.exe (PID: 2324)
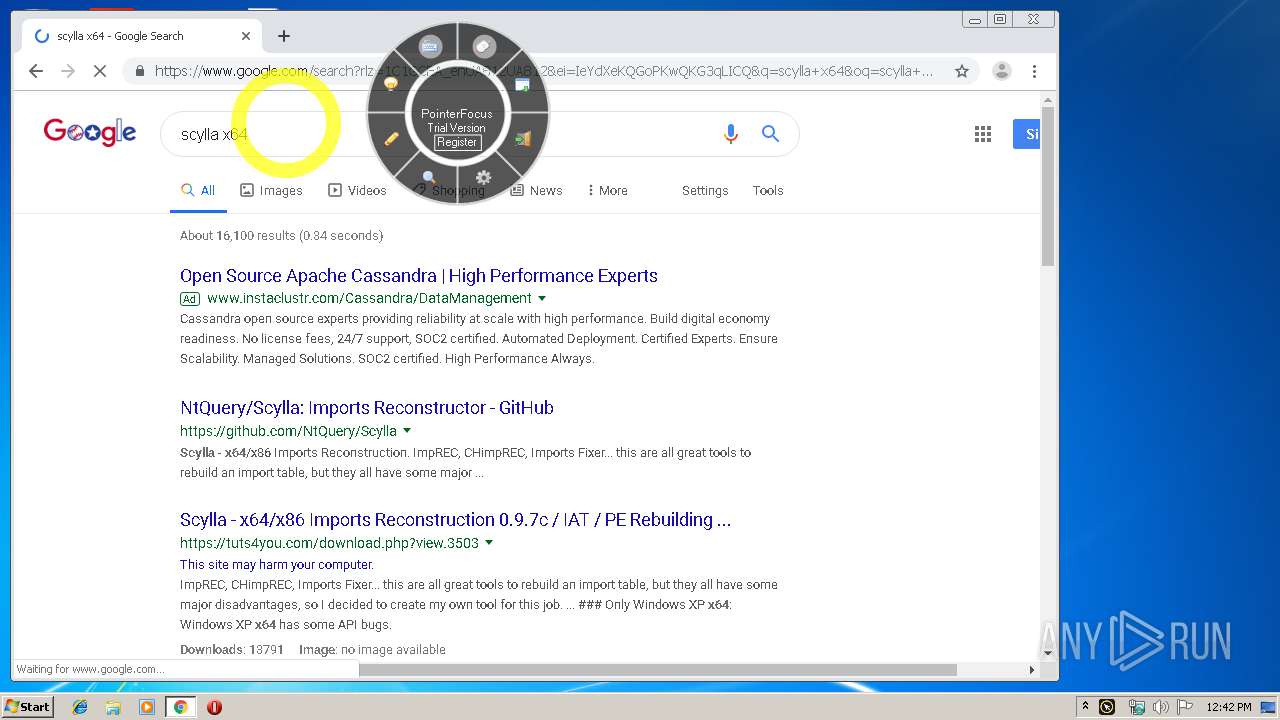
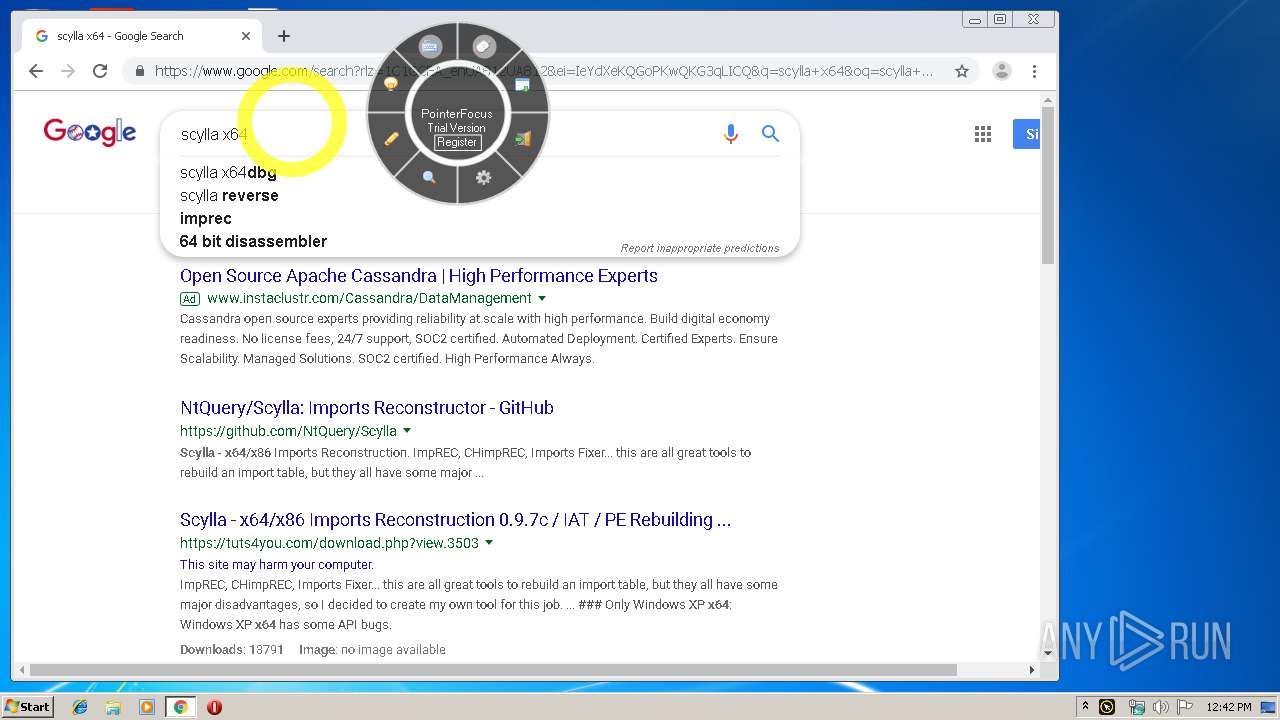
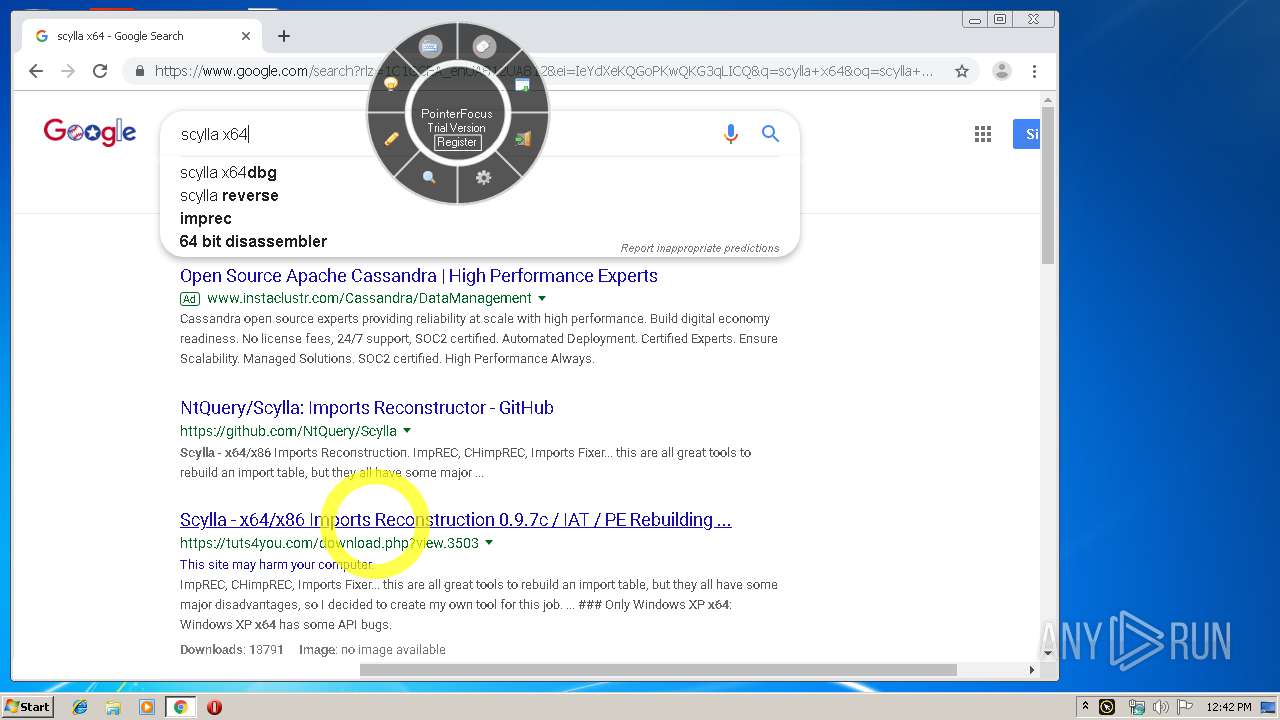
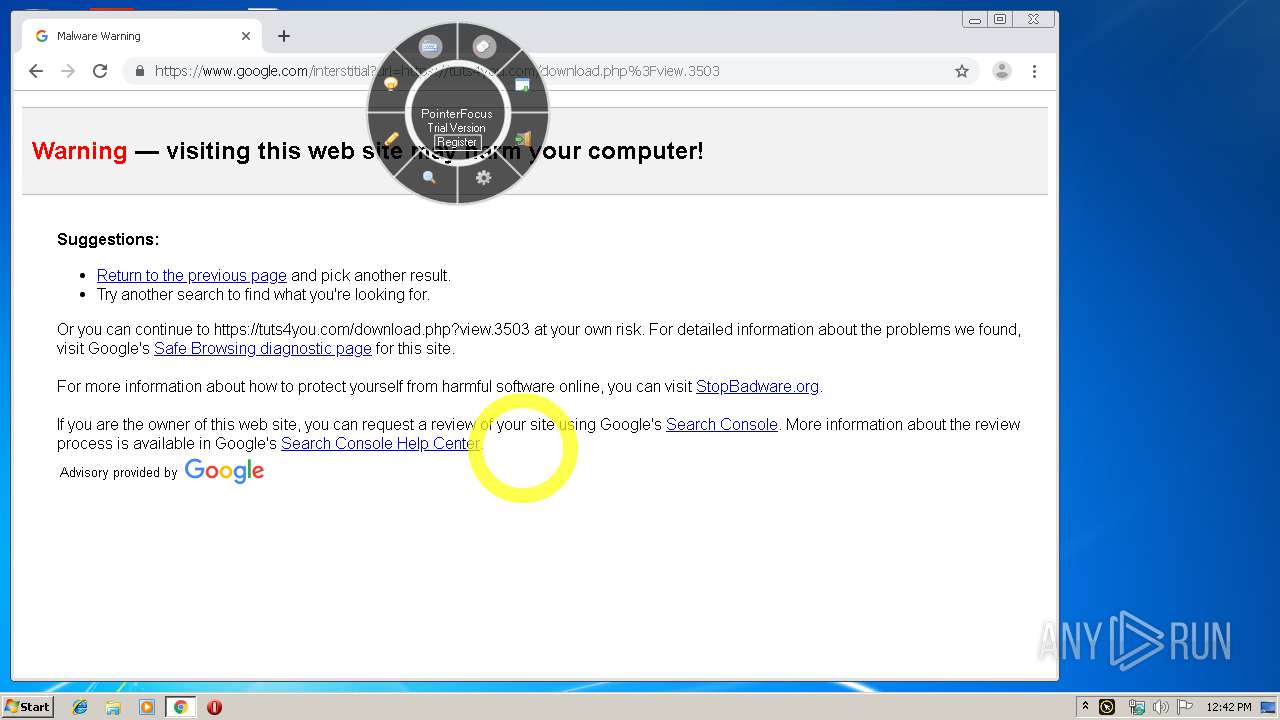
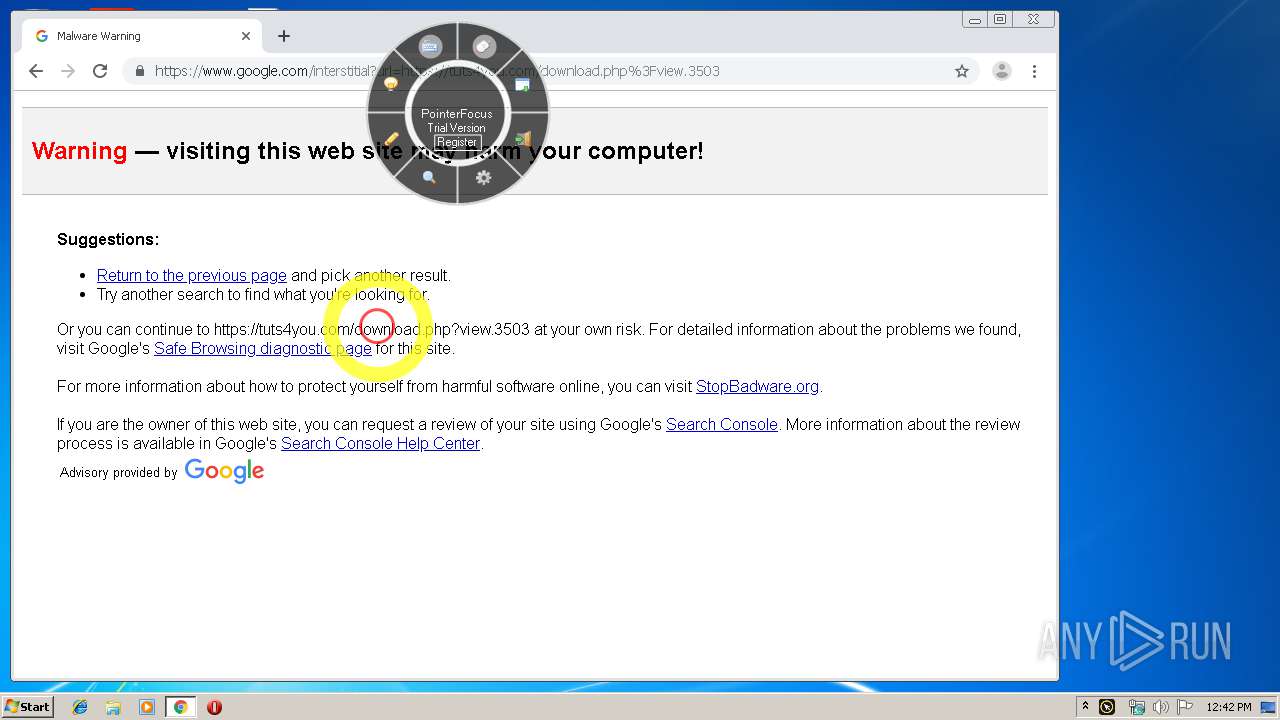
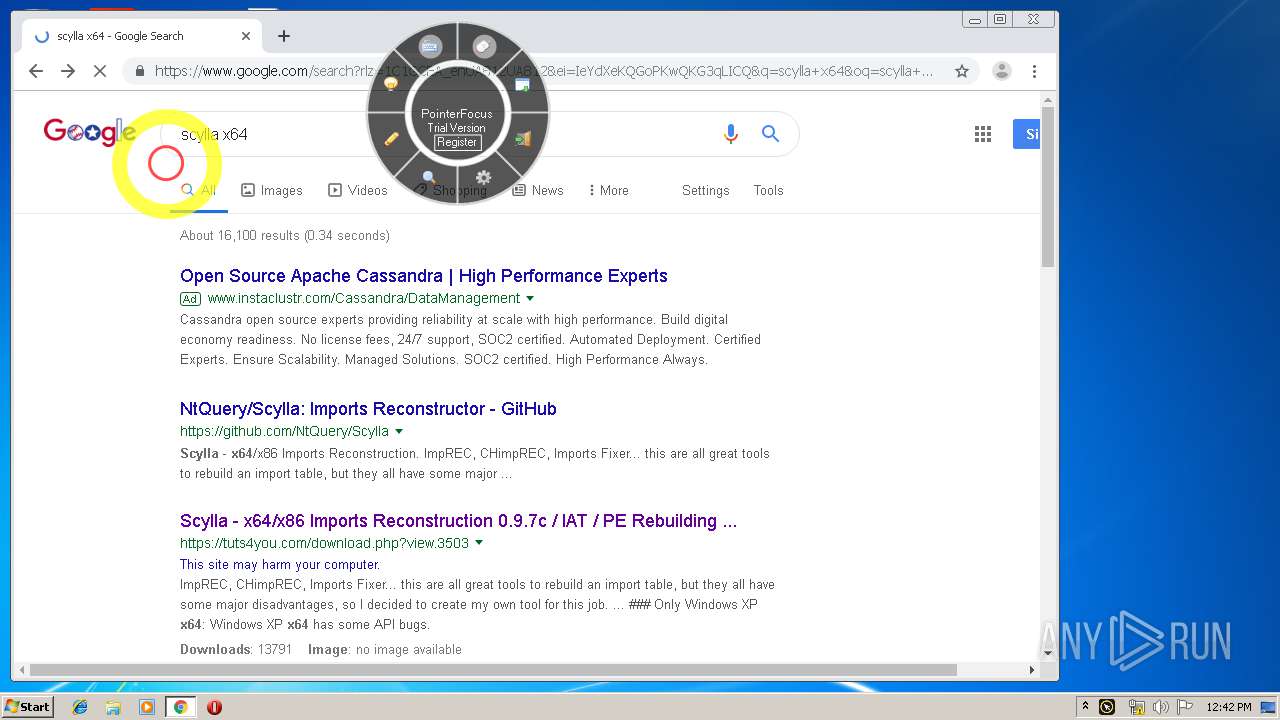
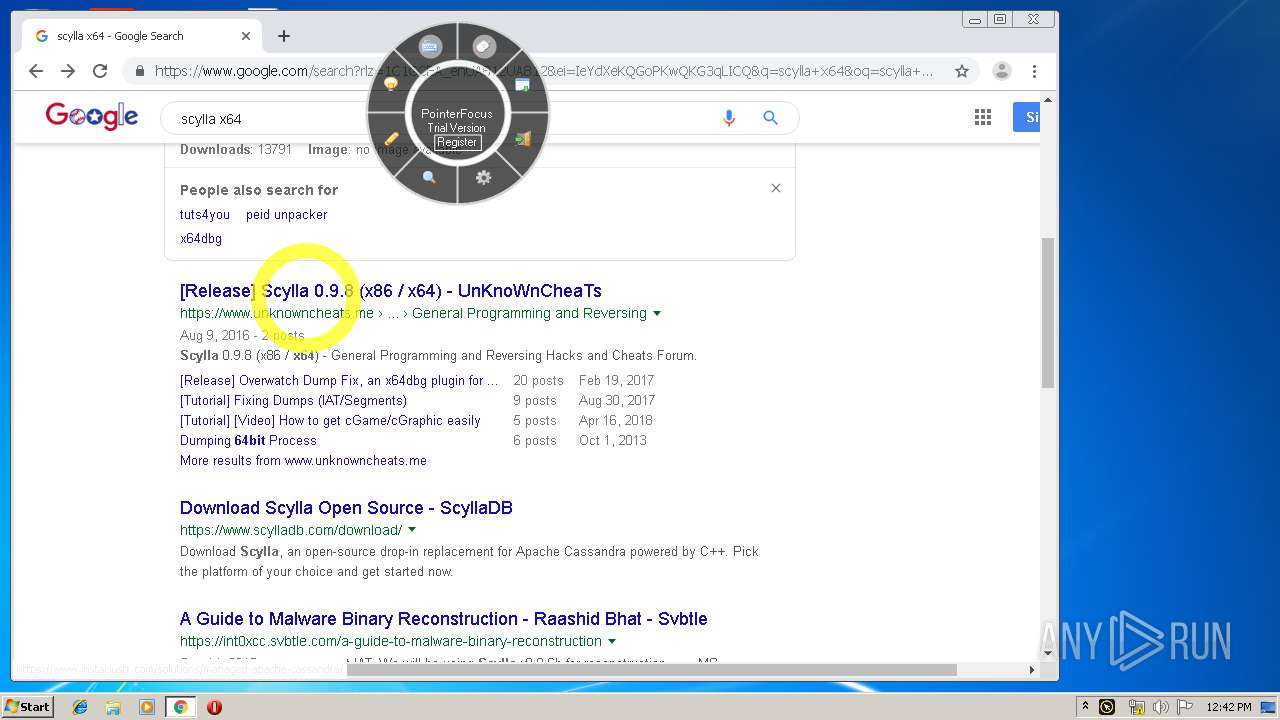
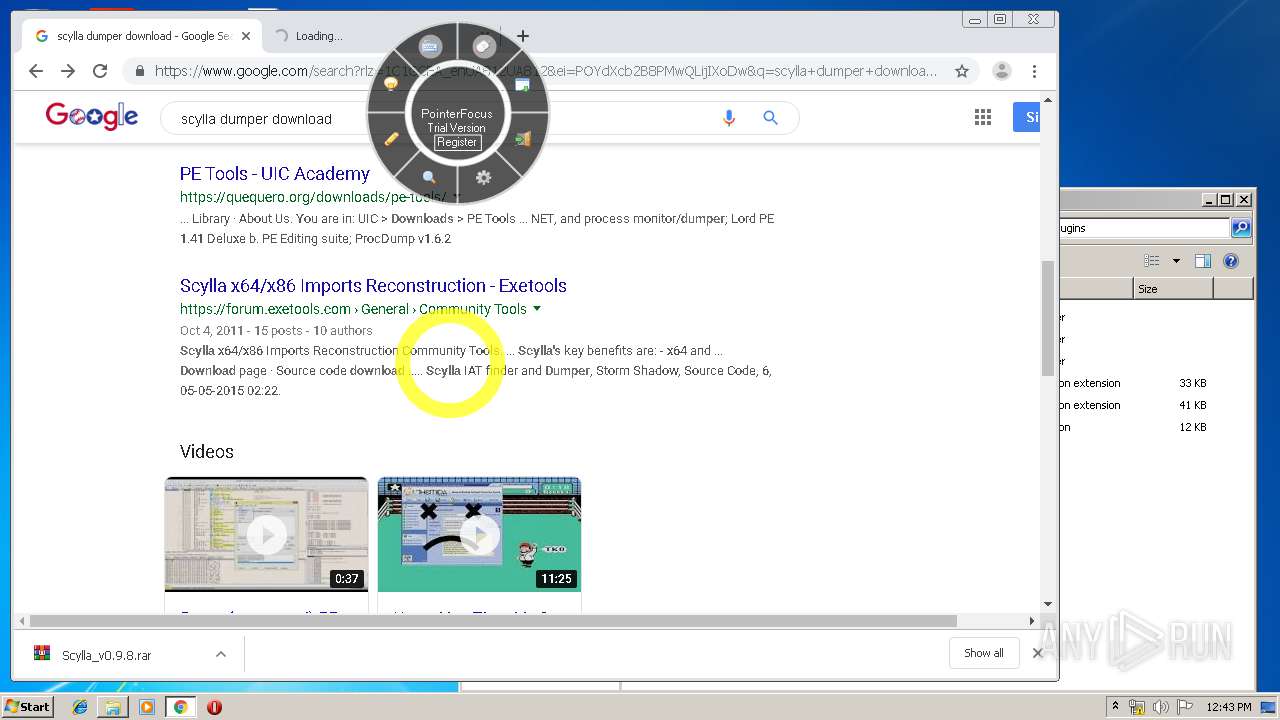
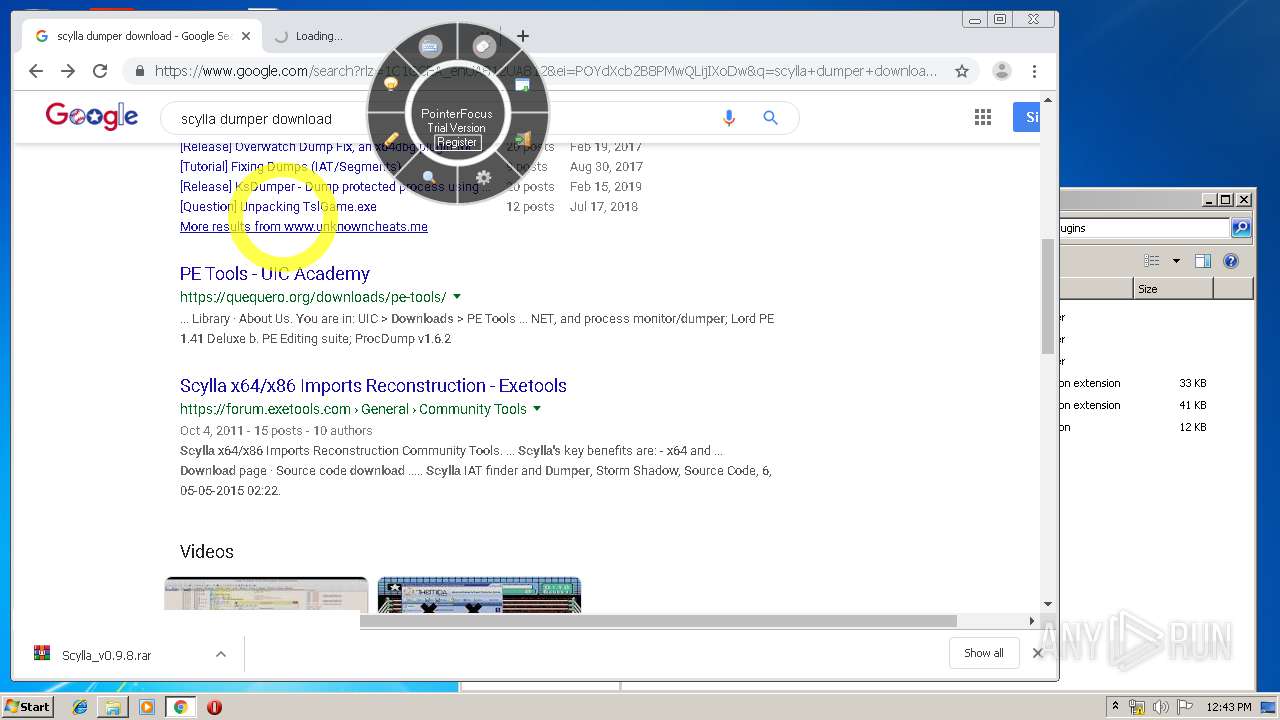
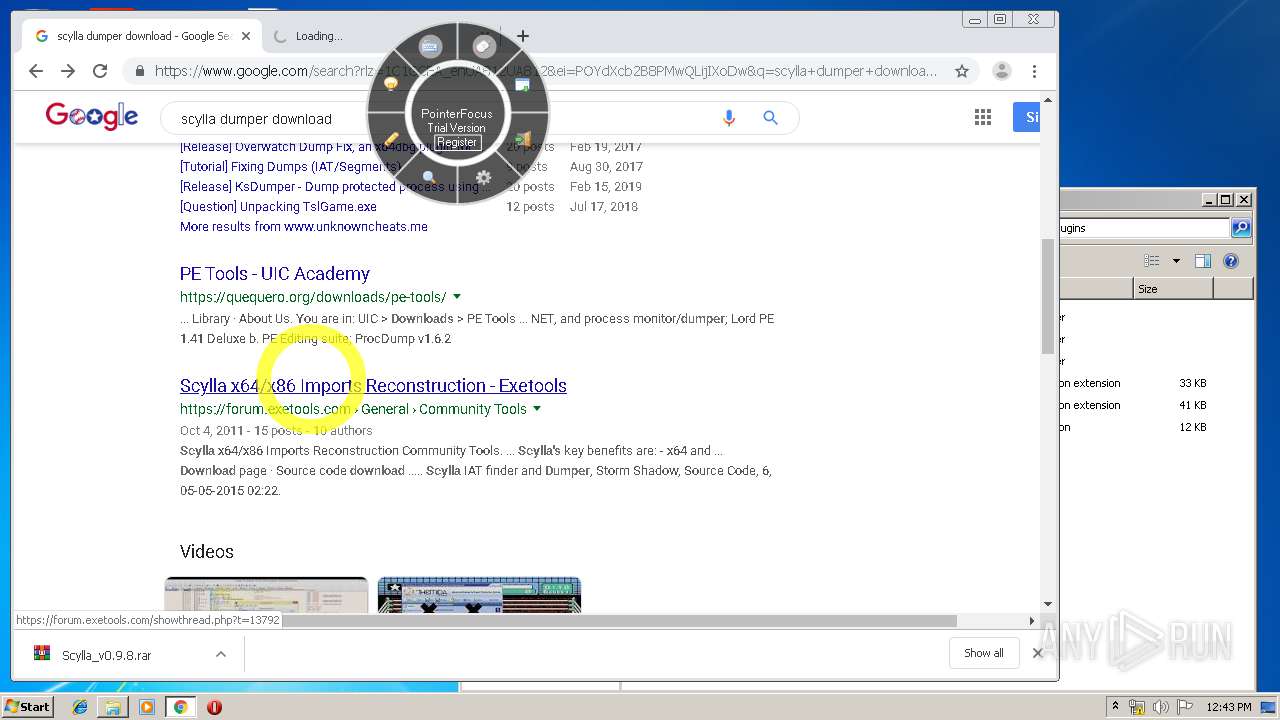
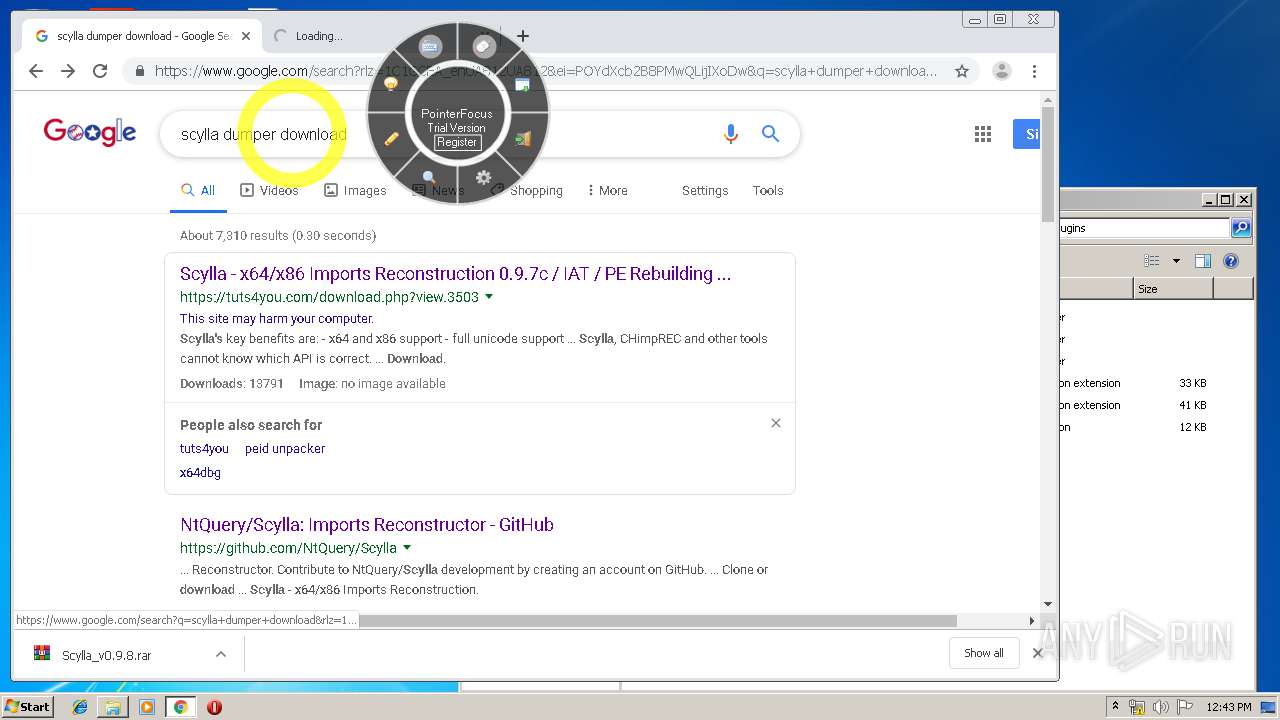
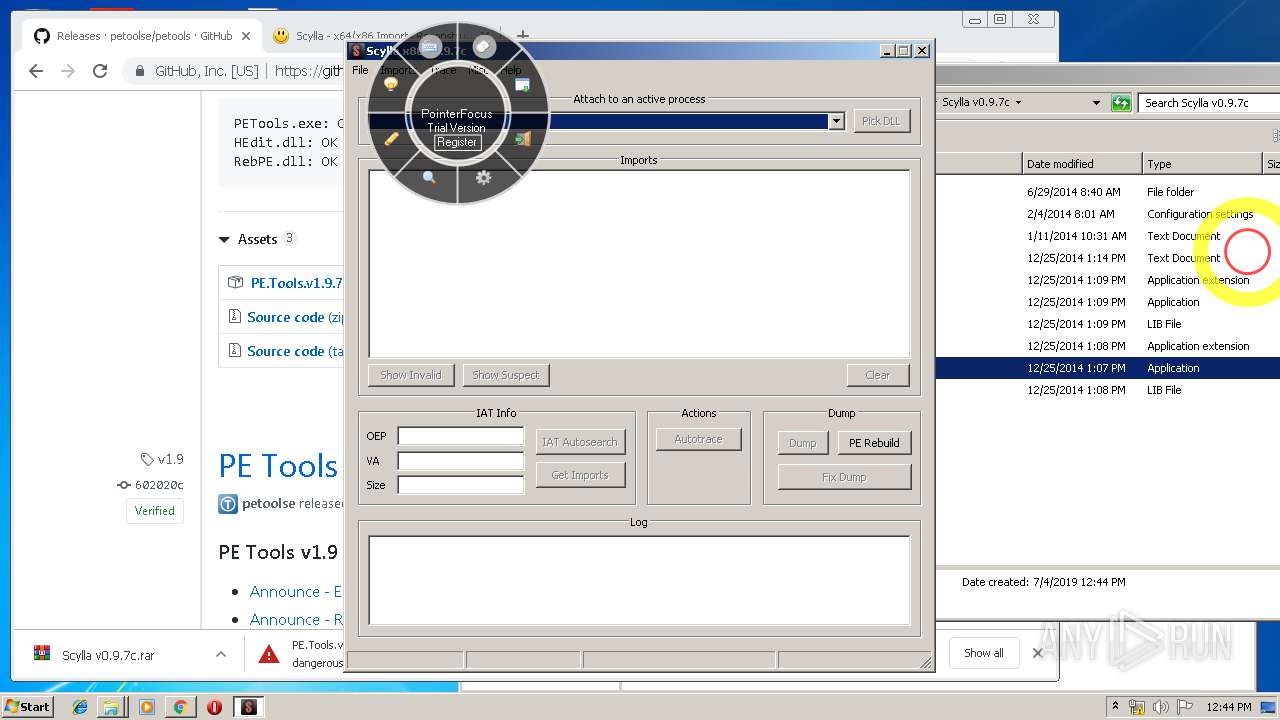
- Scylla_x86.exe (PID: 3840)
Loads dropped or rewritten executable
- PointerFocus.exe (PID: 2324)
- SearchProtocolHost.exe (PID: 2000)
- Scylla_x86.exe (PID: 3840)
Changes settings of System certificates
- PointerFocus.exe (PID: 2324)
Starts Visual C# compiler
- PointerFocus.exe (PID: 2324)
SUSPICIOUS
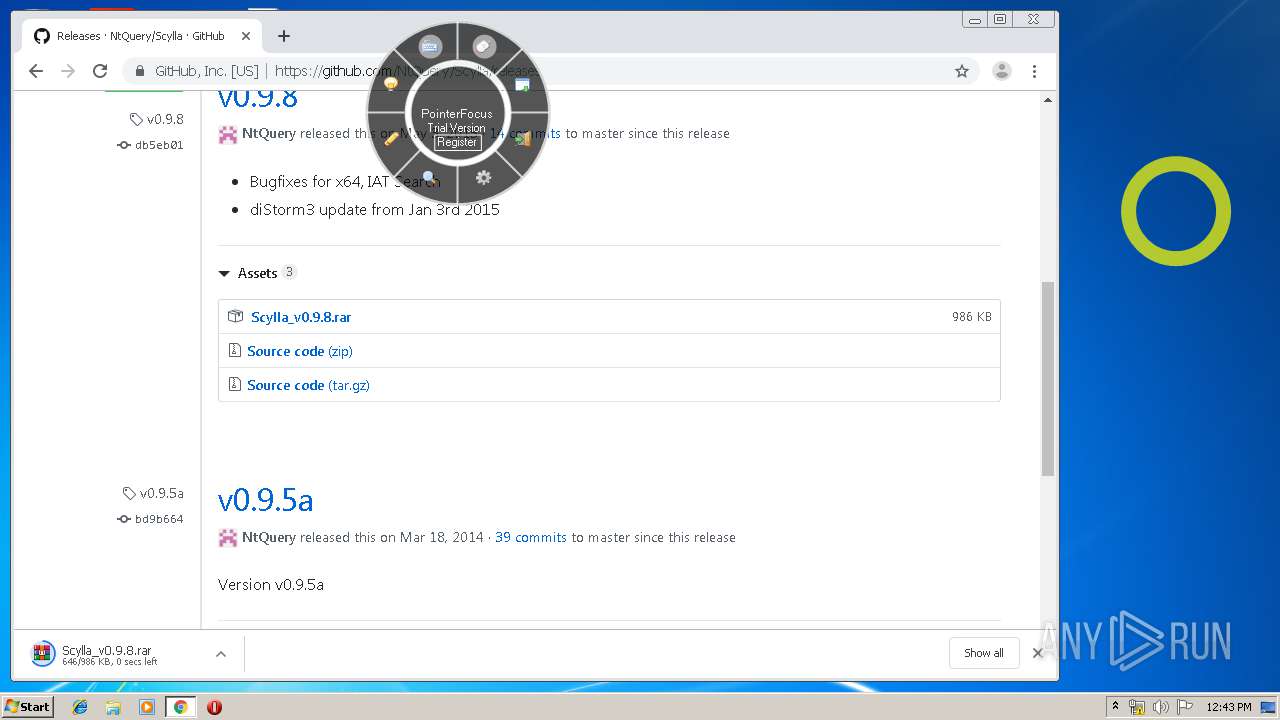
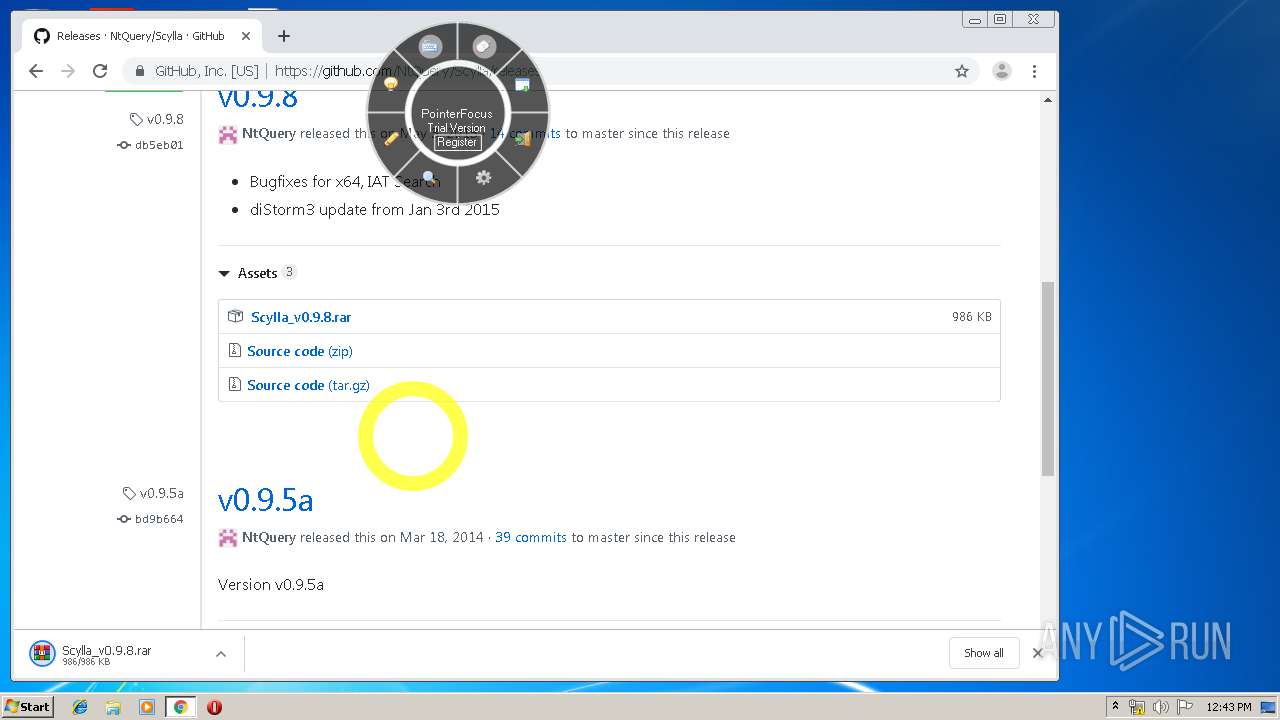
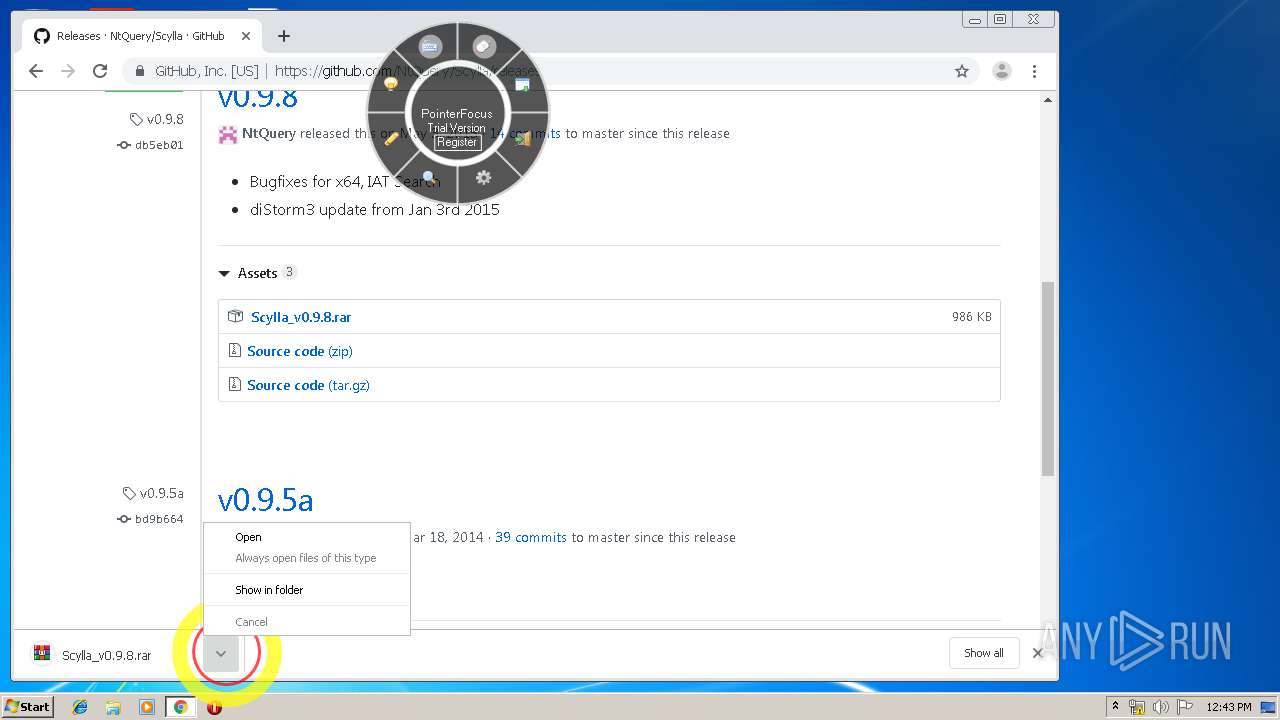
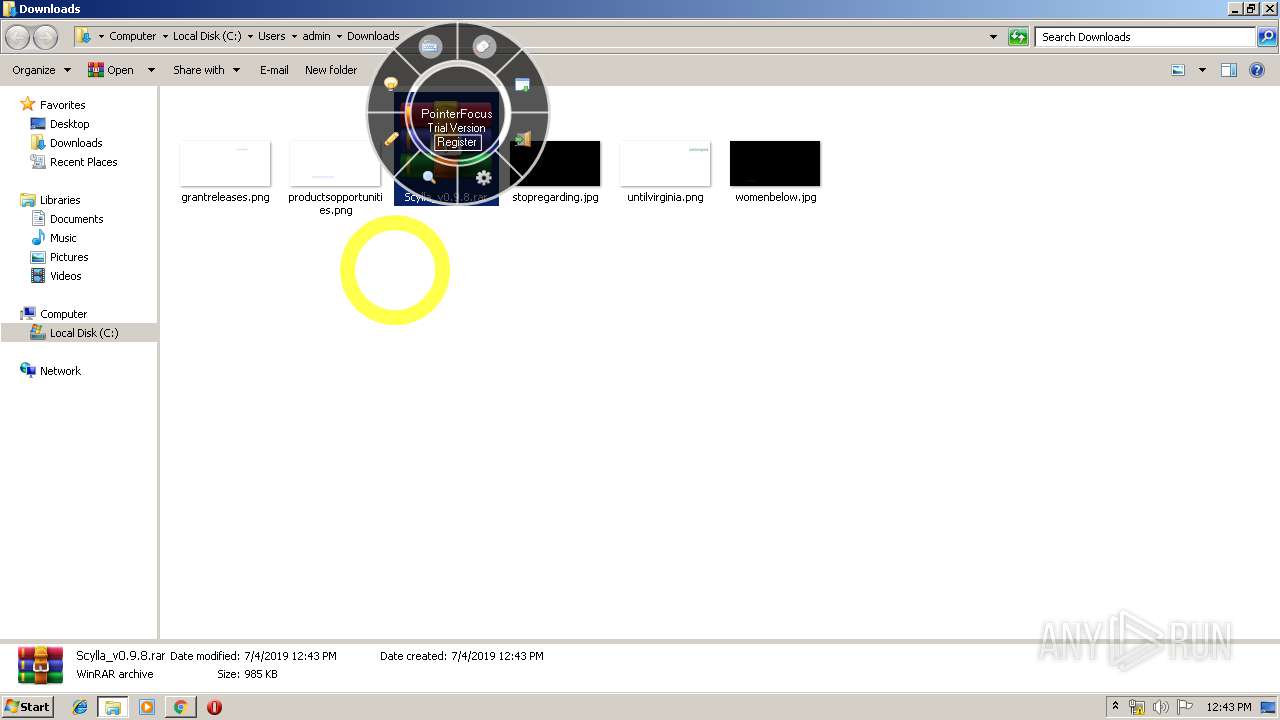
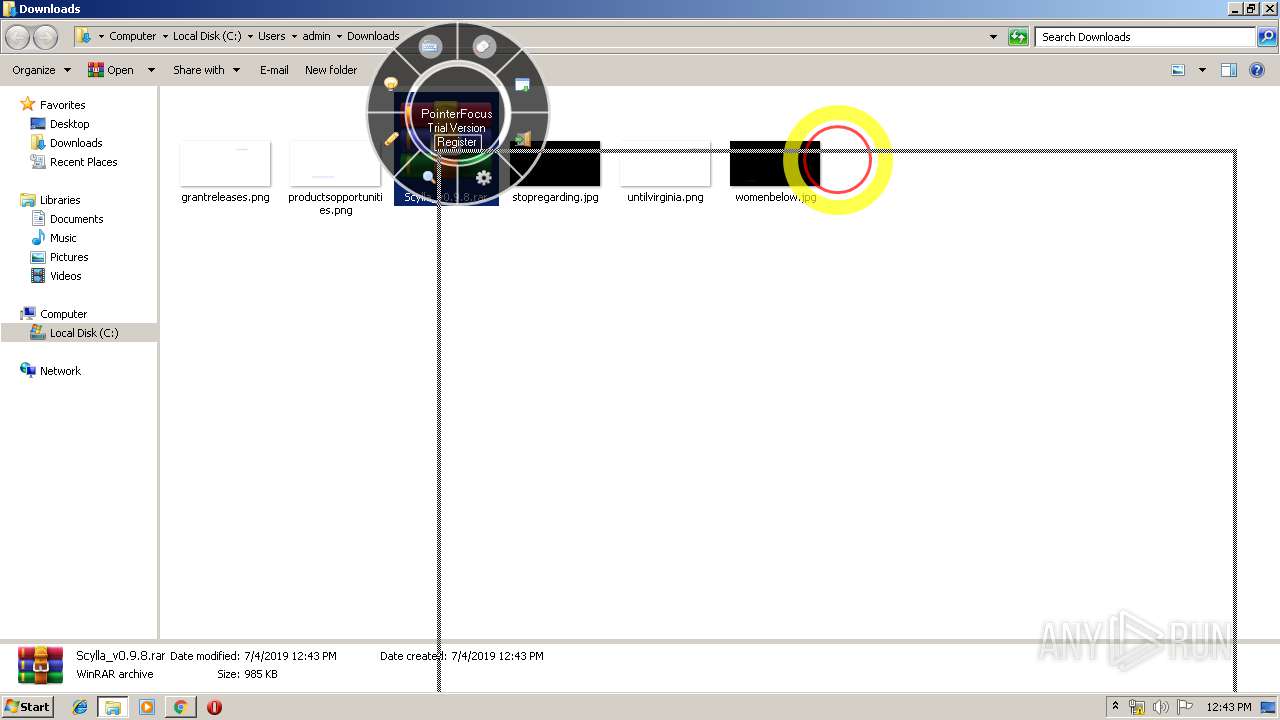
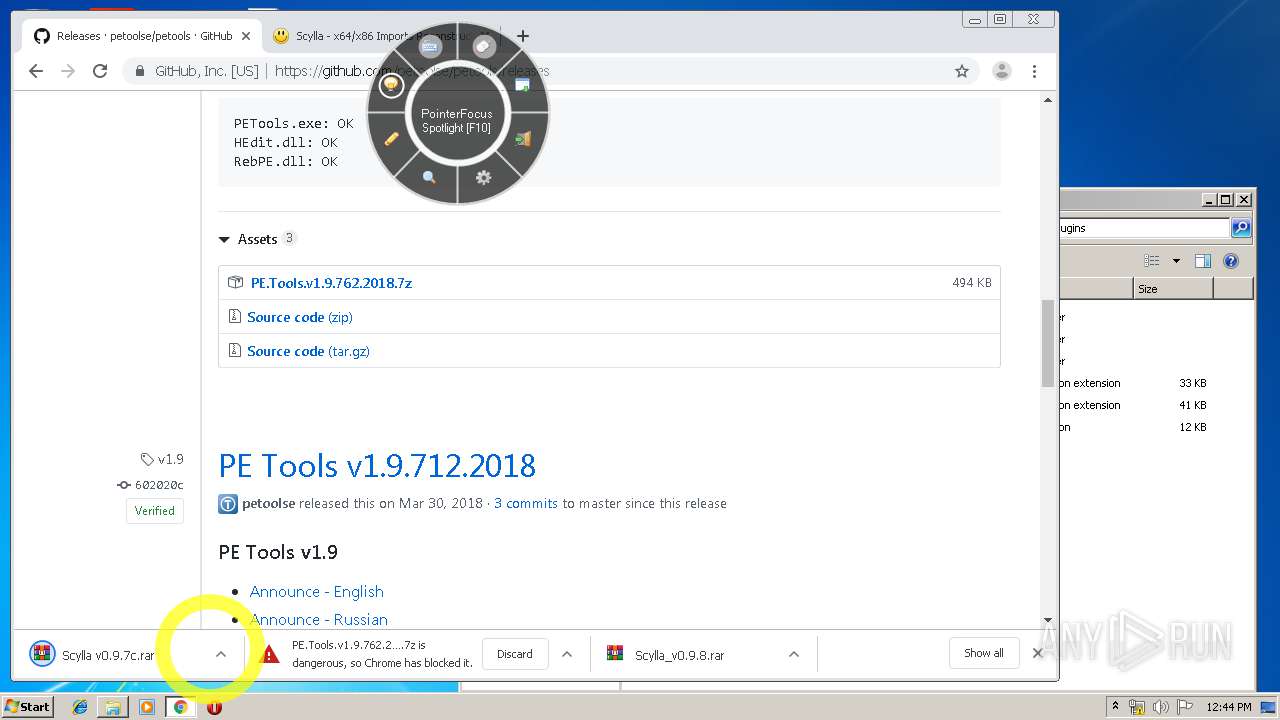
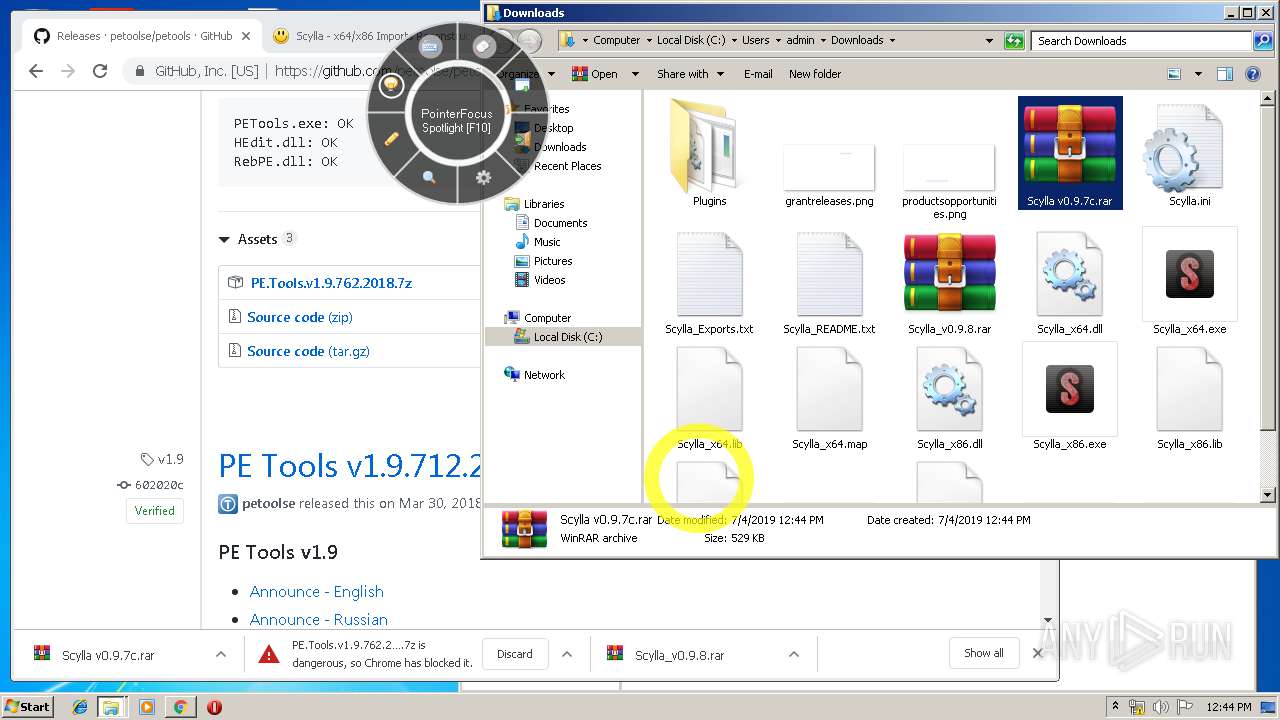
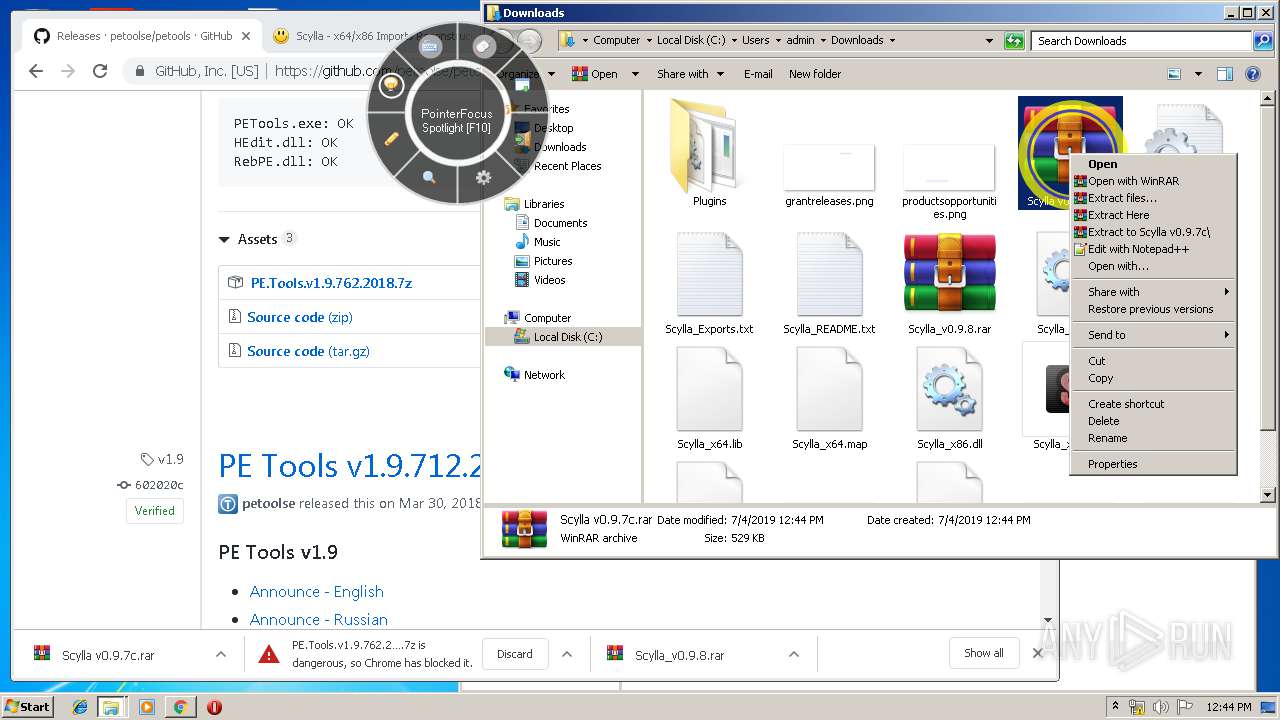
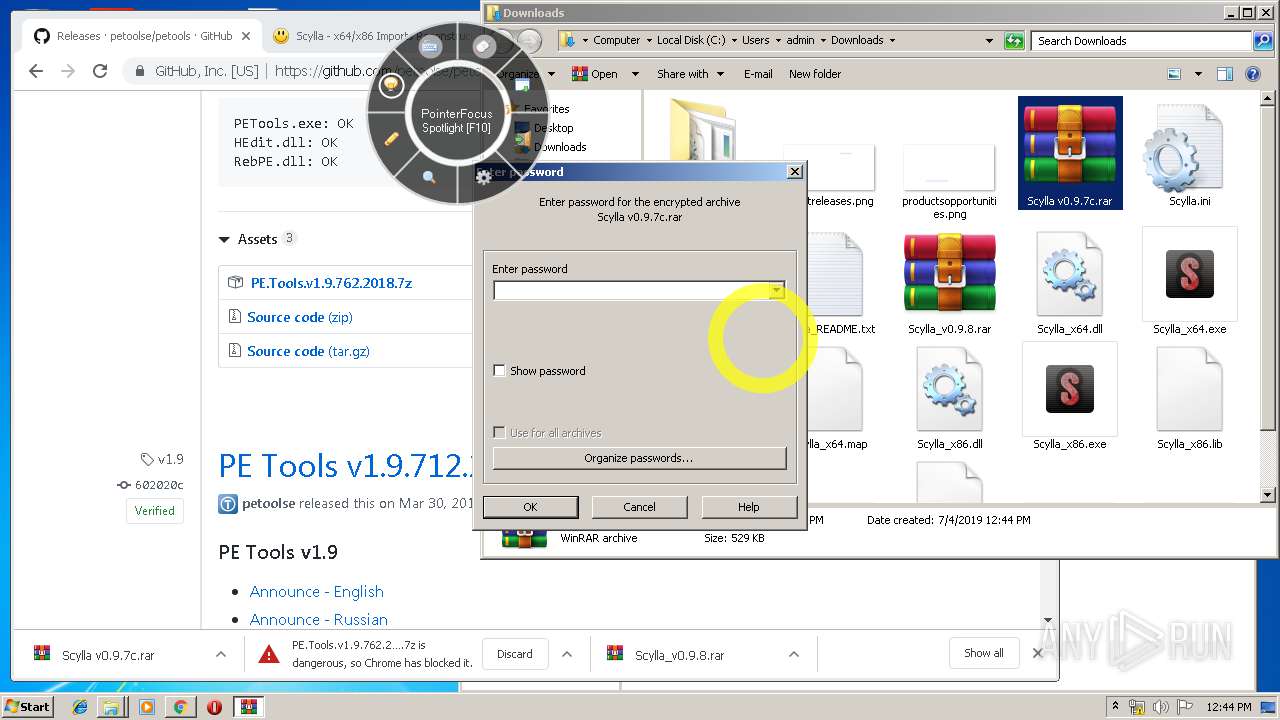
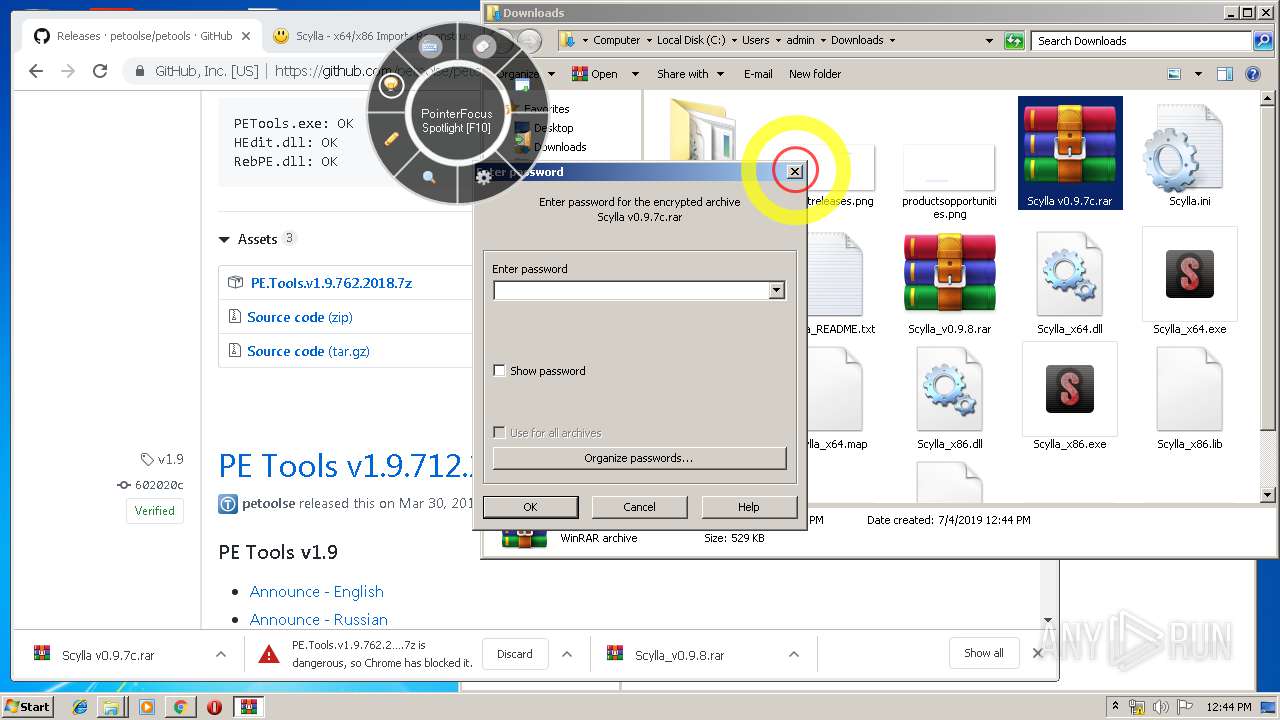
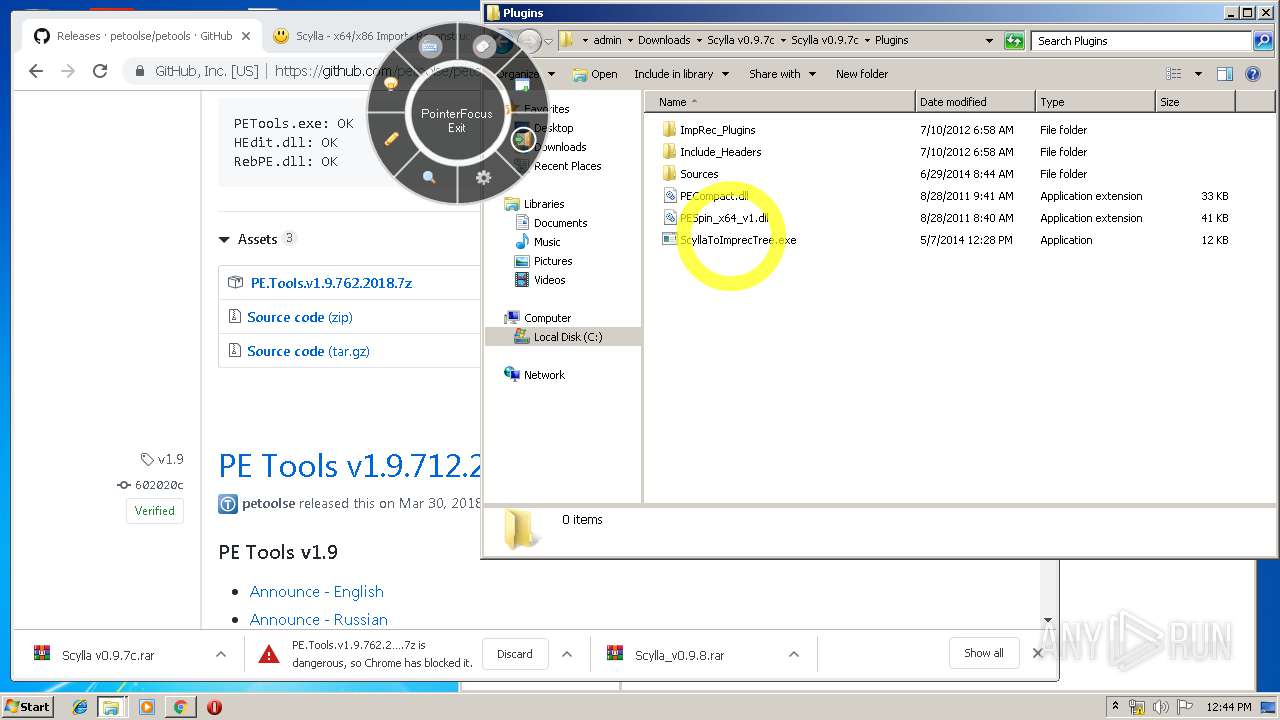
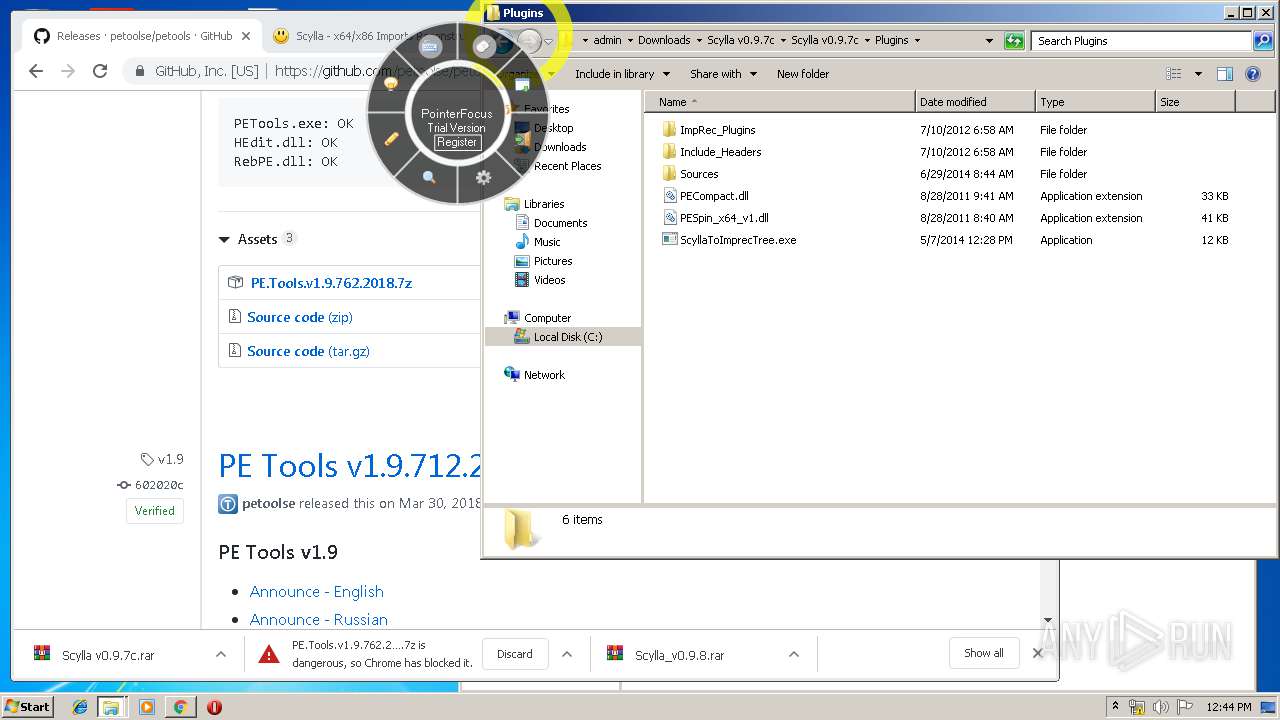
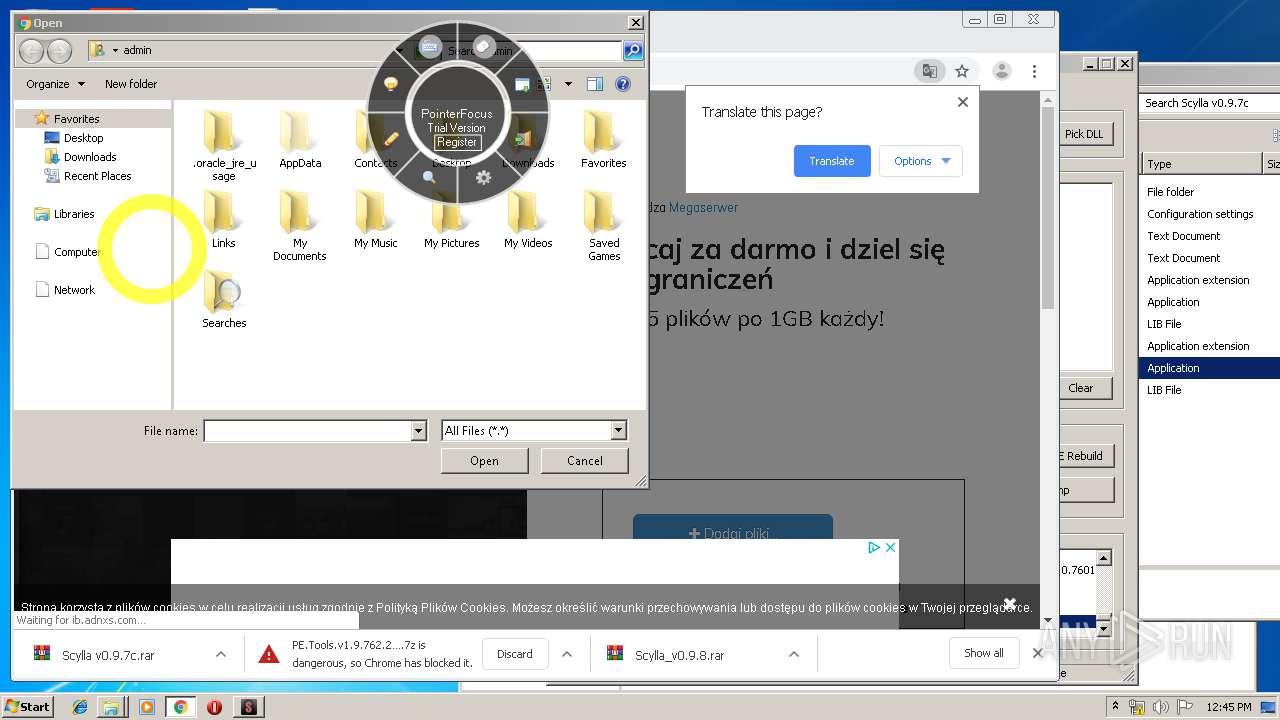
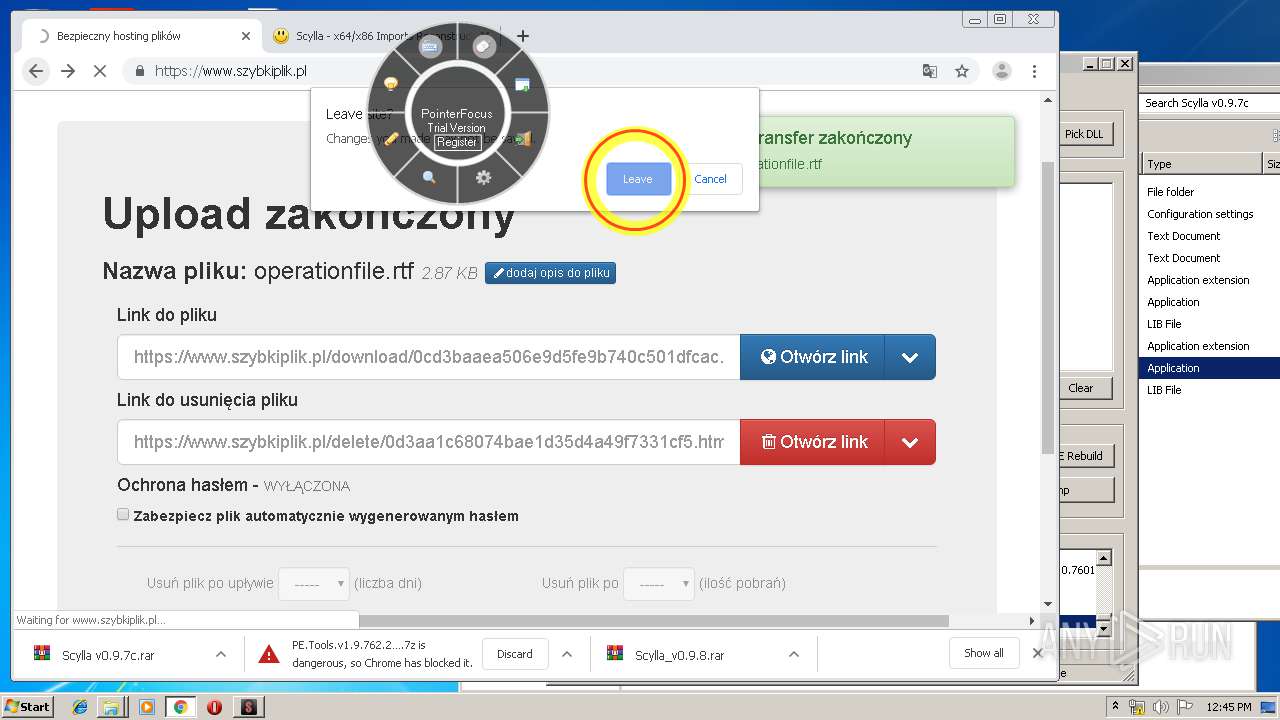
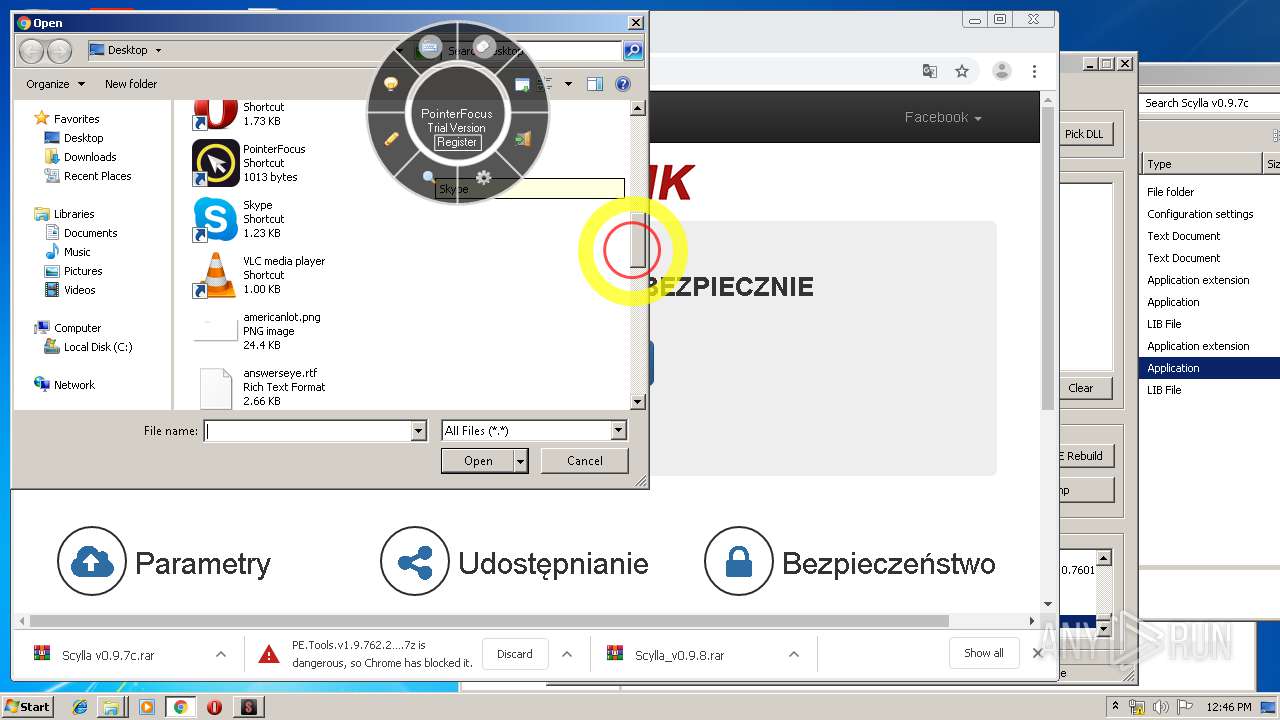
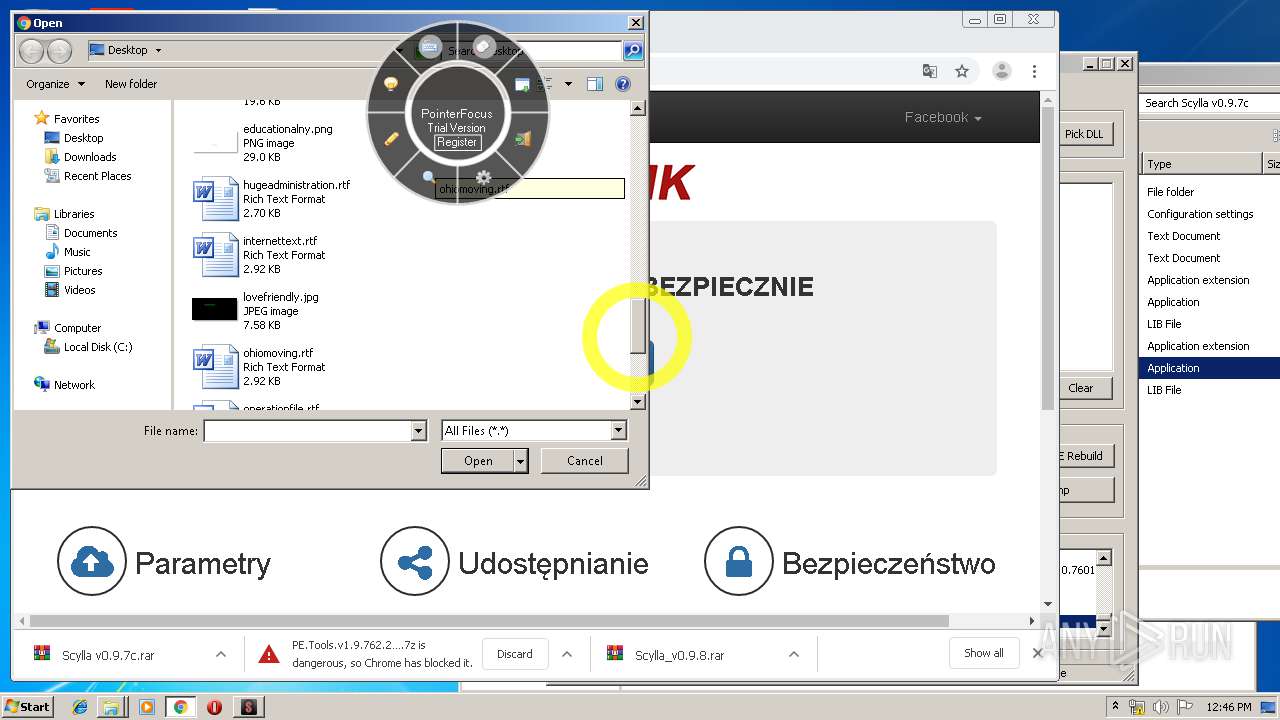
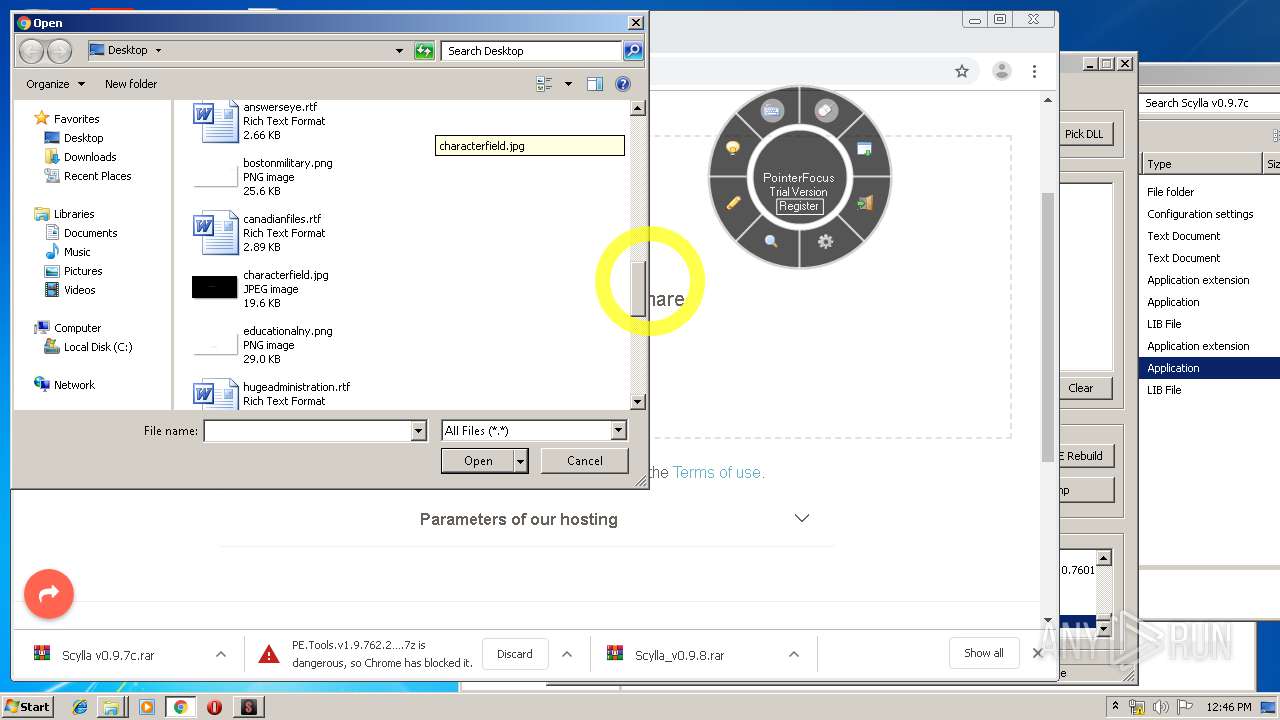
Executable content was dropped or overwritten
- pfsetup.exe (PID: 3048)
- pfsetup.exe (PID: 2572)
- pfsetup.tmp (PID: 2988)
- WinRAR.exe (PID: 2916)
- WinRAR.exe (PID: 3648)
- Scylla_x86.exe (PID: 3840)
Reads Windows owner or organization settings
- pfsetup.tmp (PID: 2988)
Reads the Windows organization settings
- pfsetup.tmp (PID: 2988)
Adds / modifies Windows certificates
- PointerFocus.exe (PID: 2324)
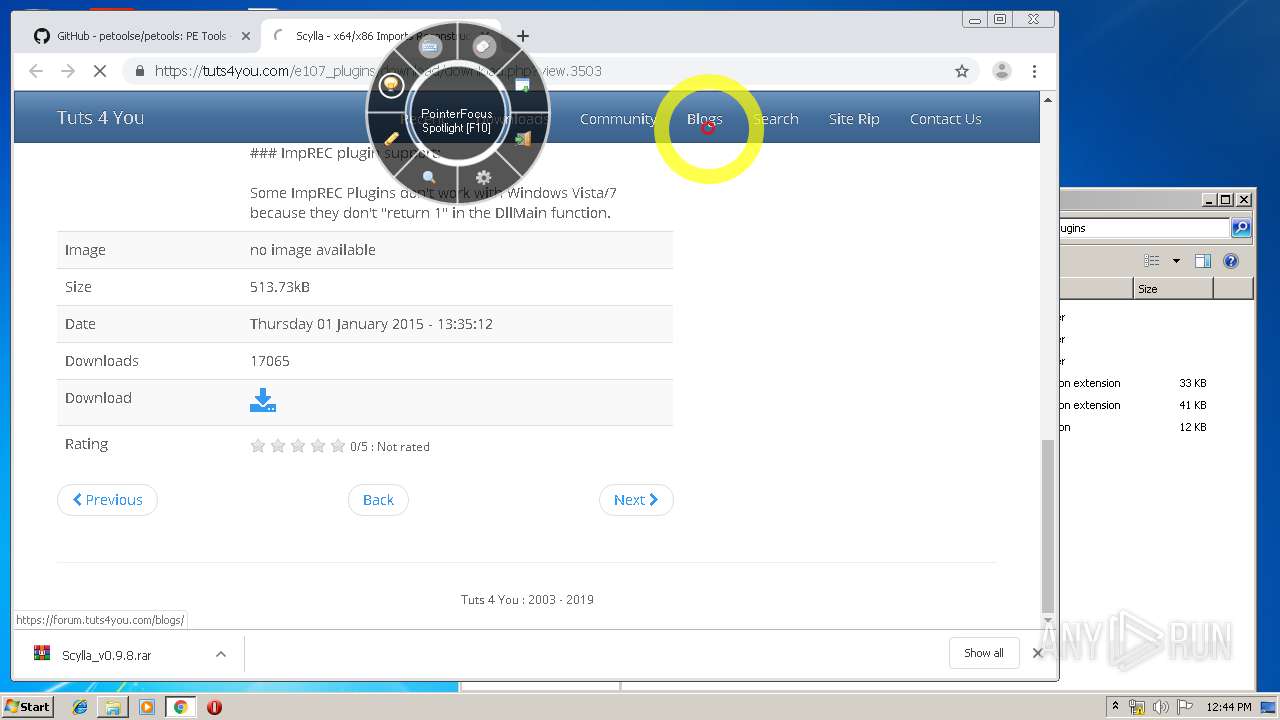
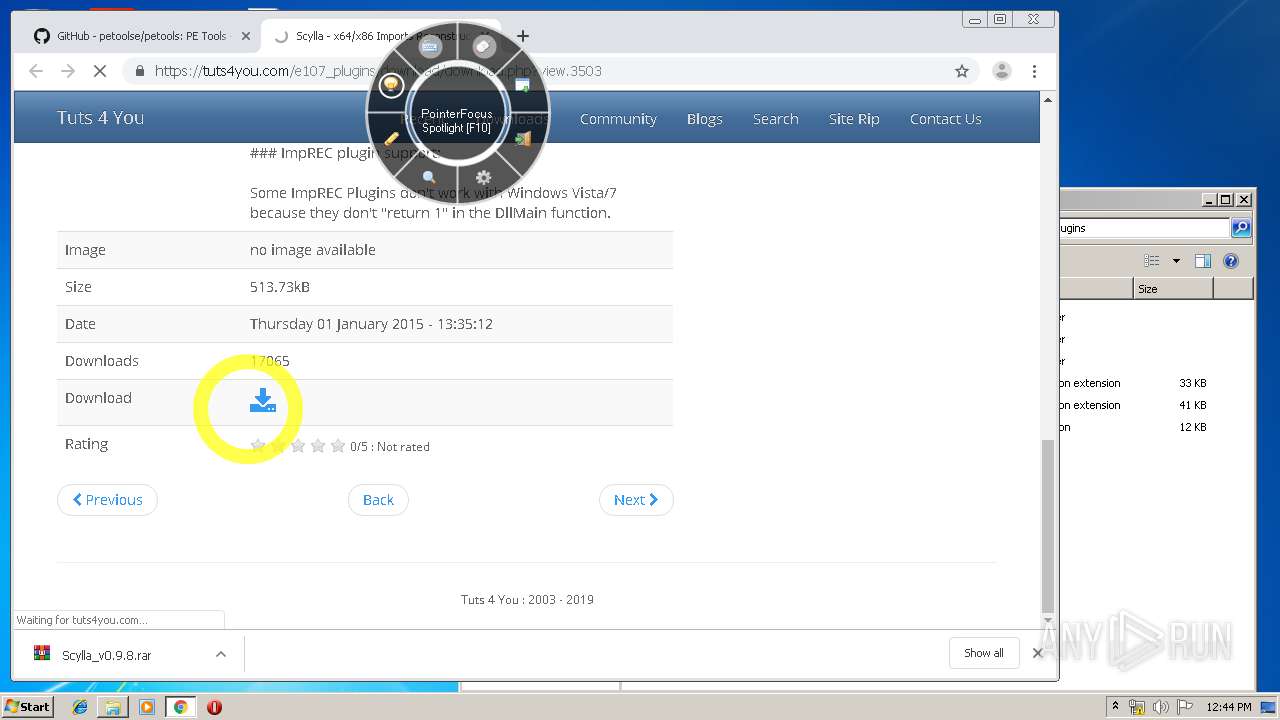
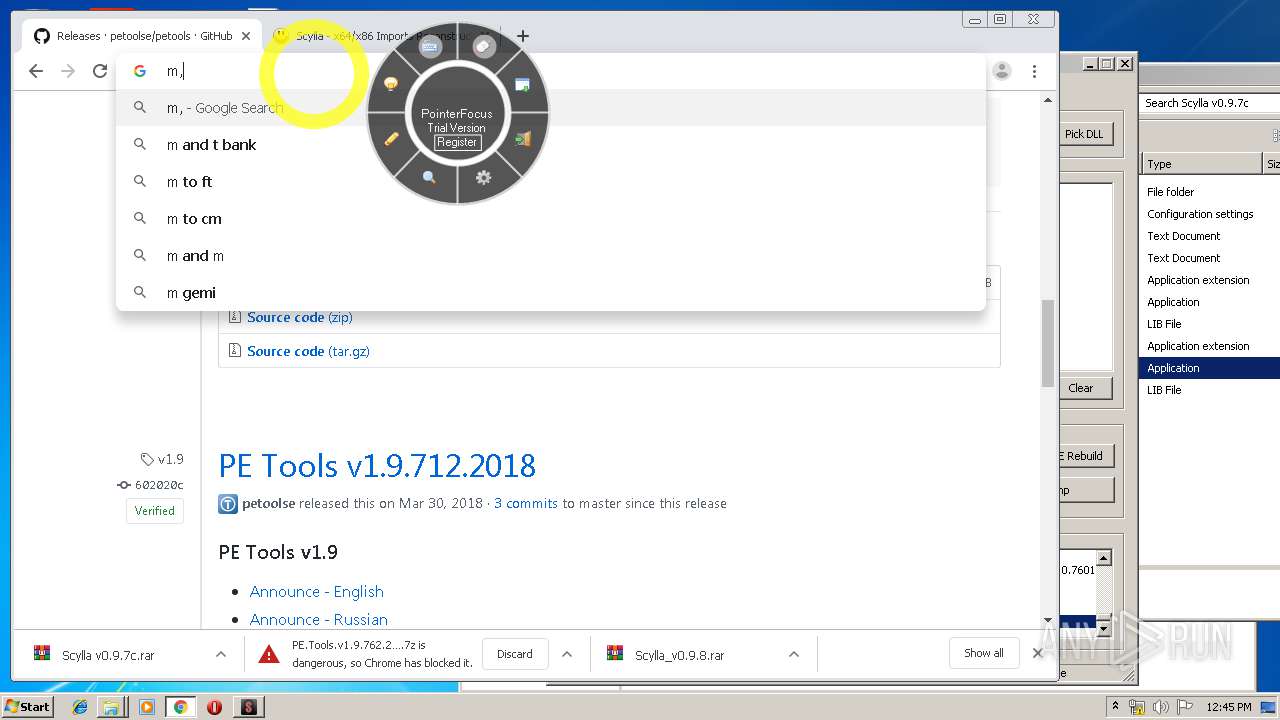
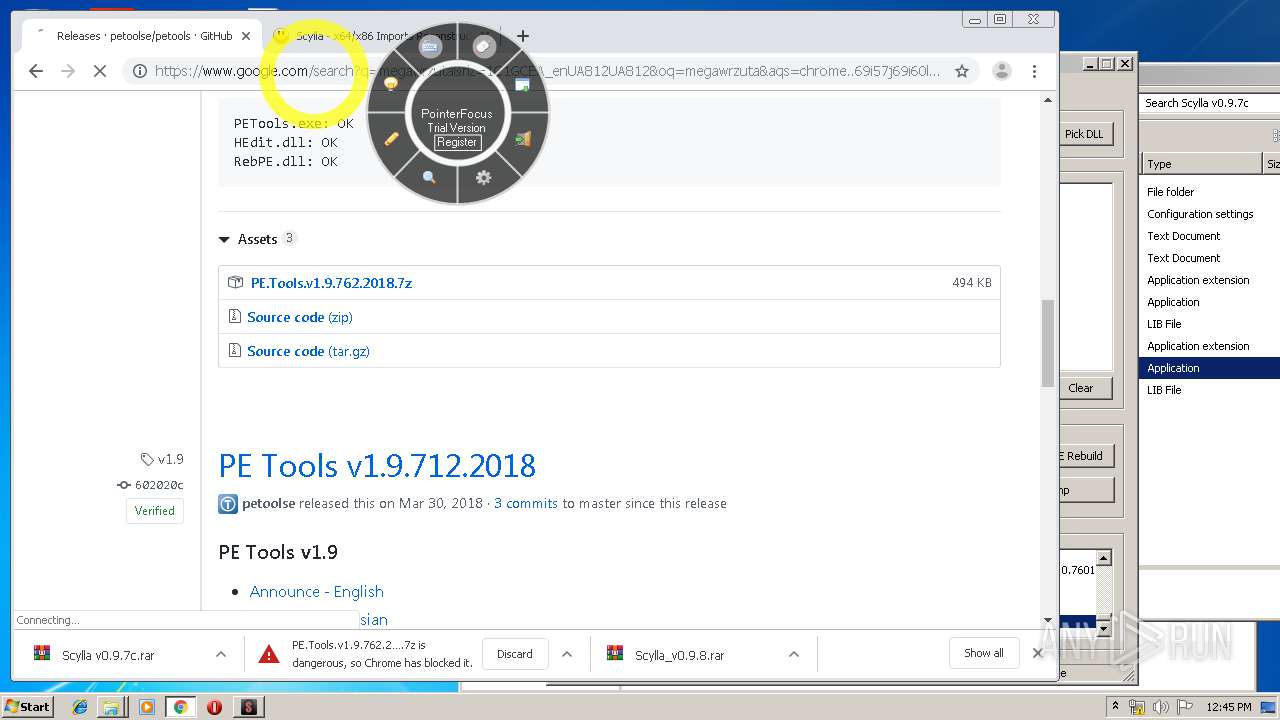
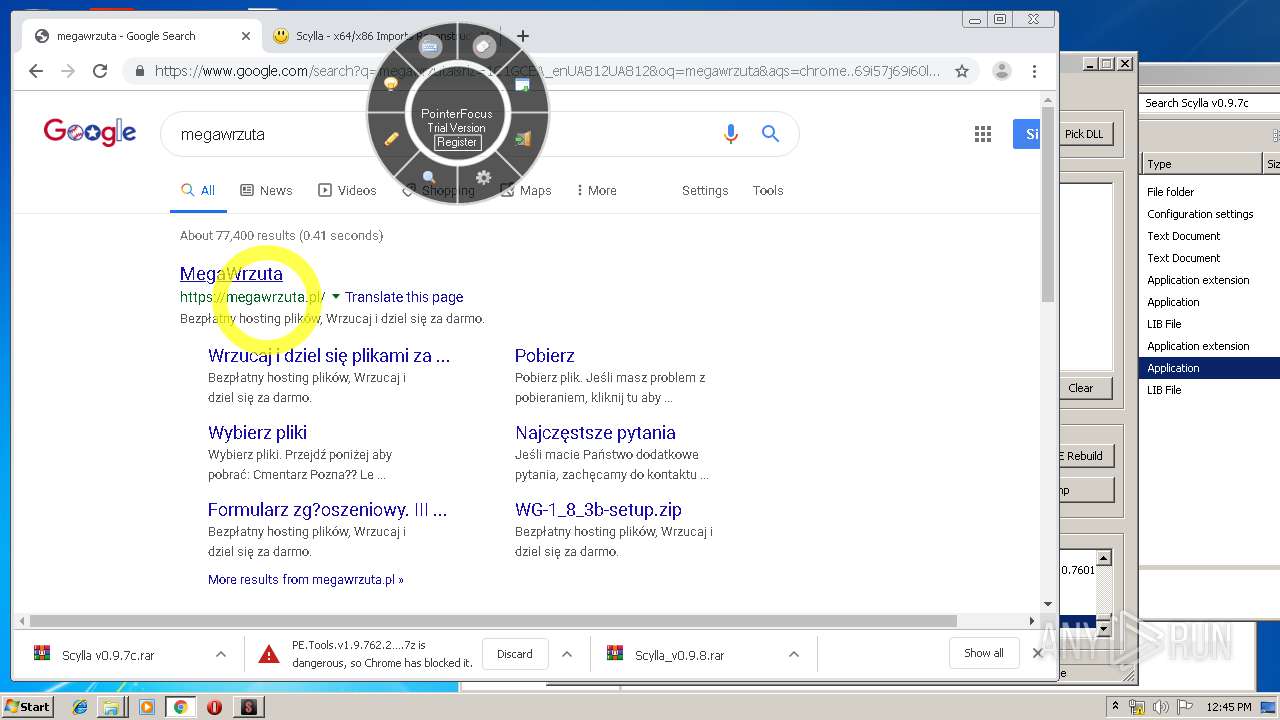
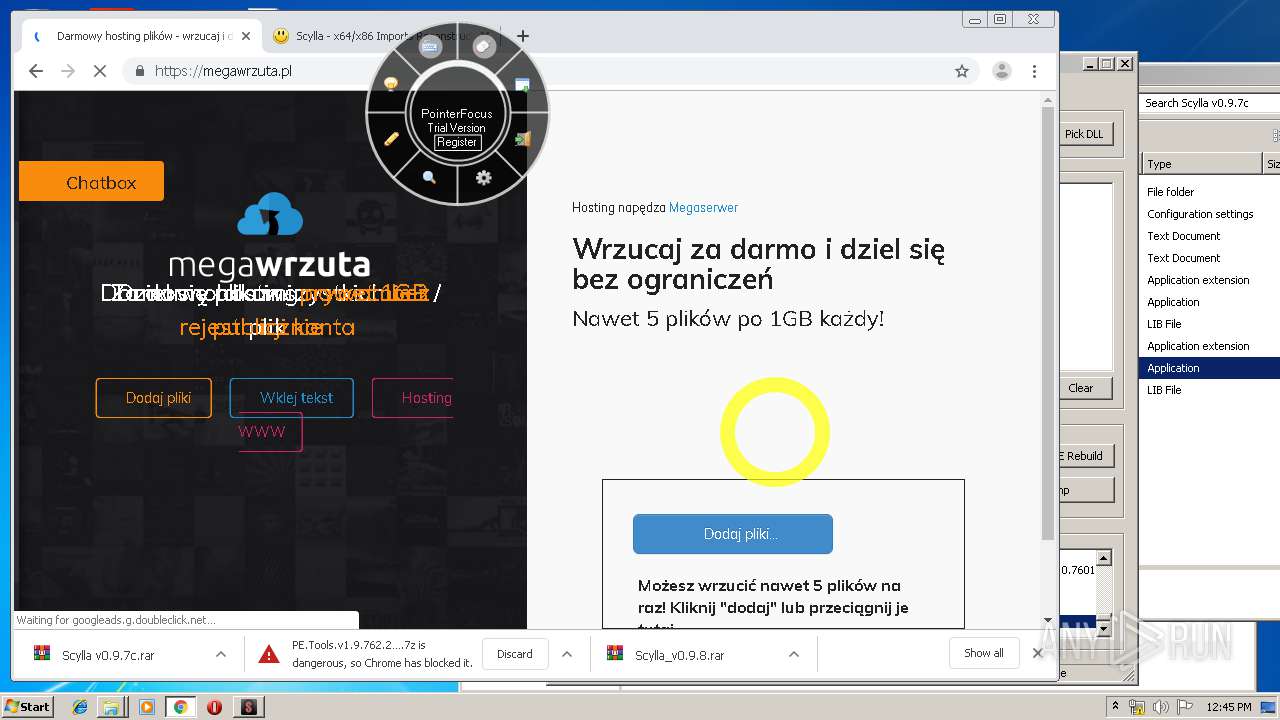
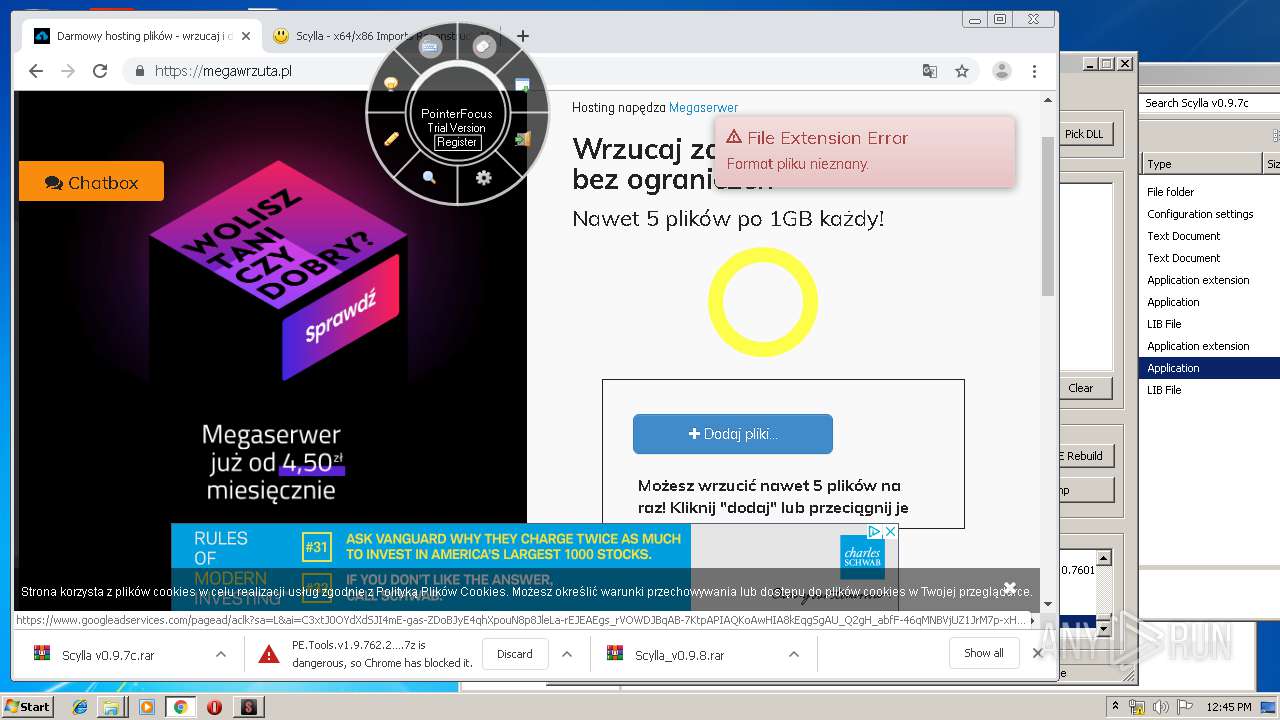
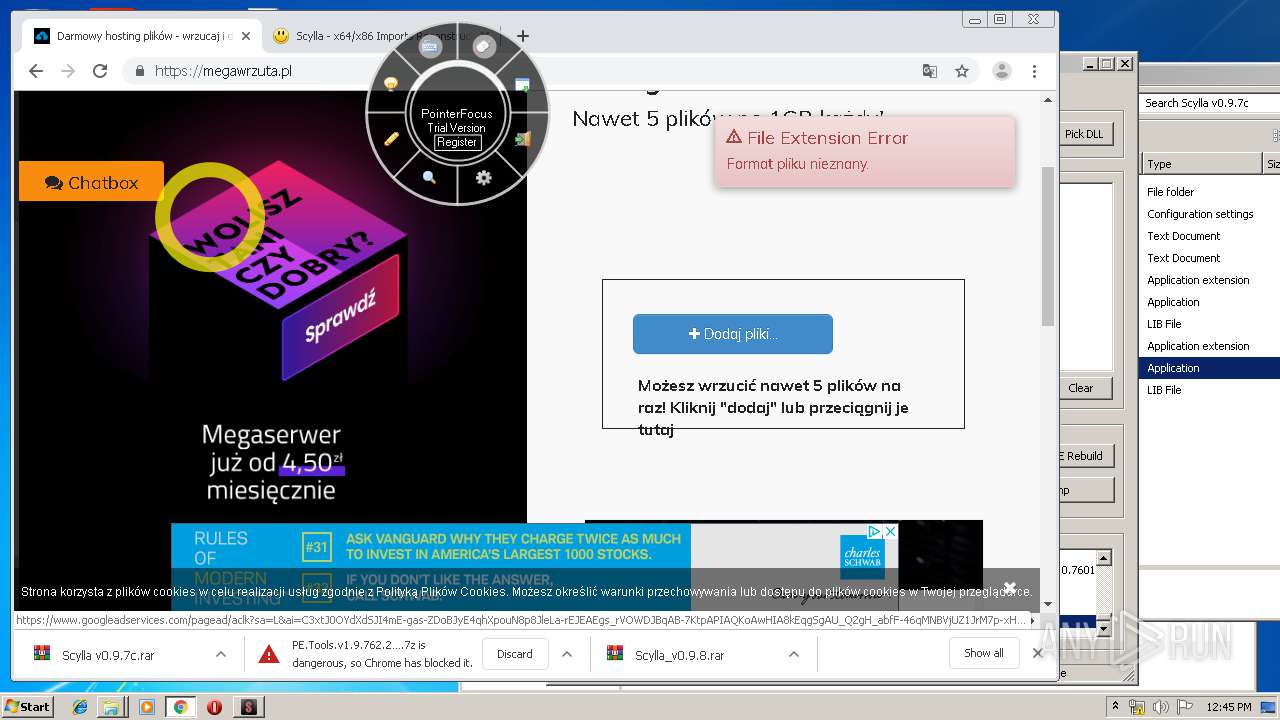
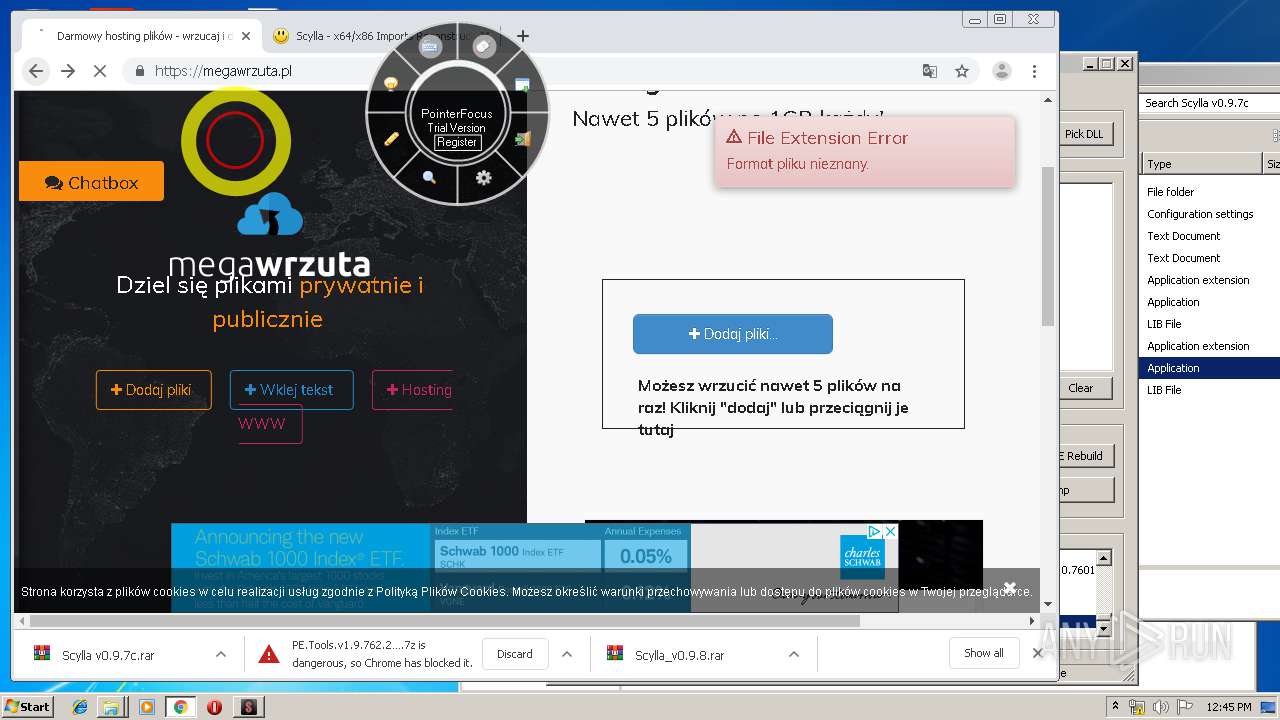
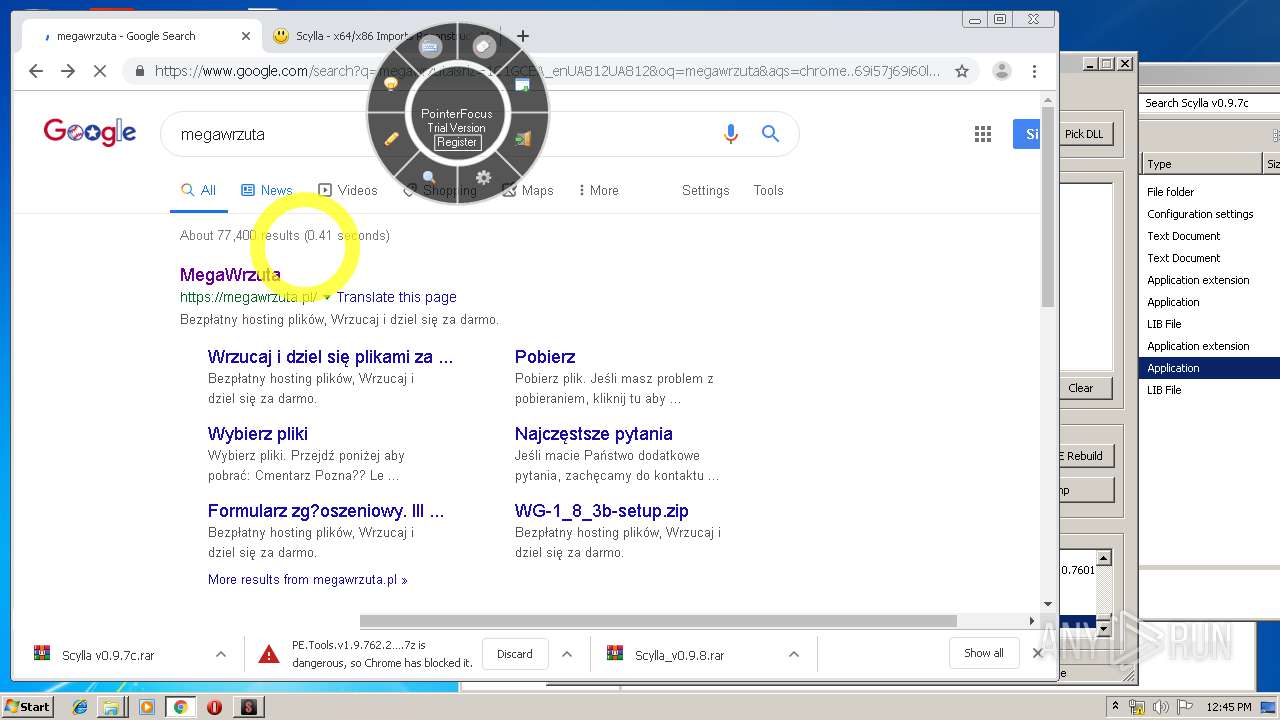
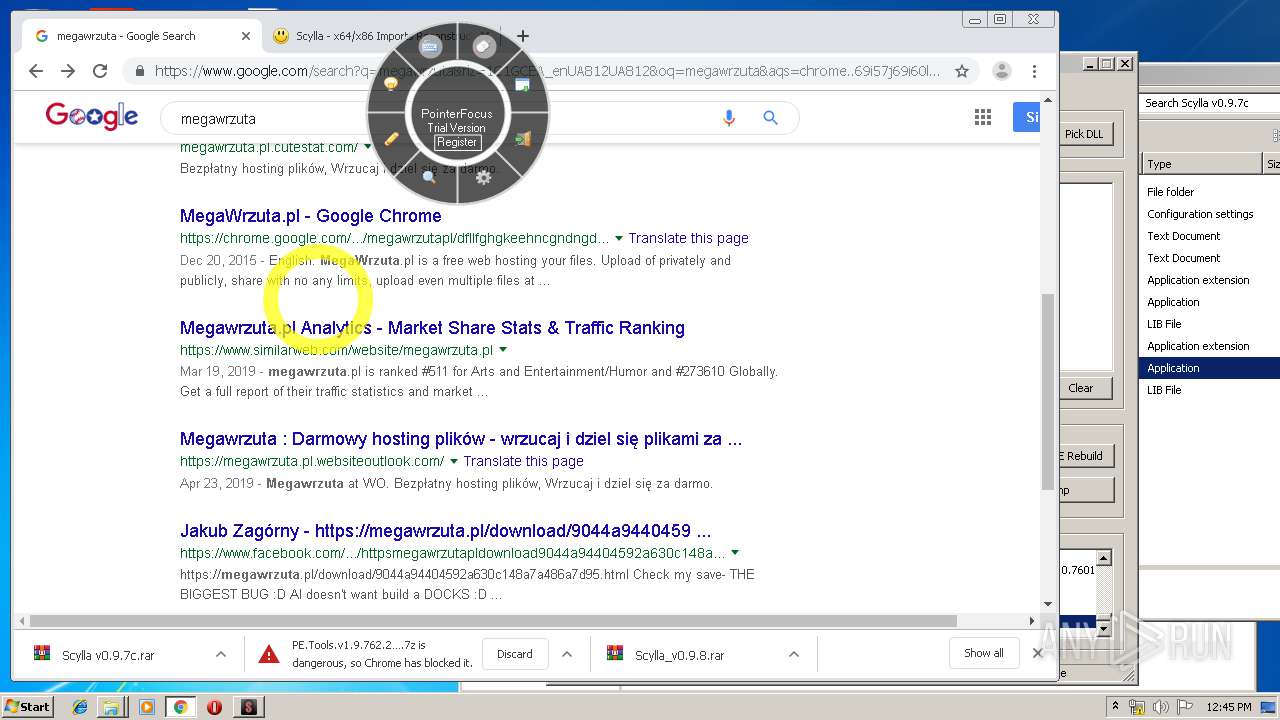
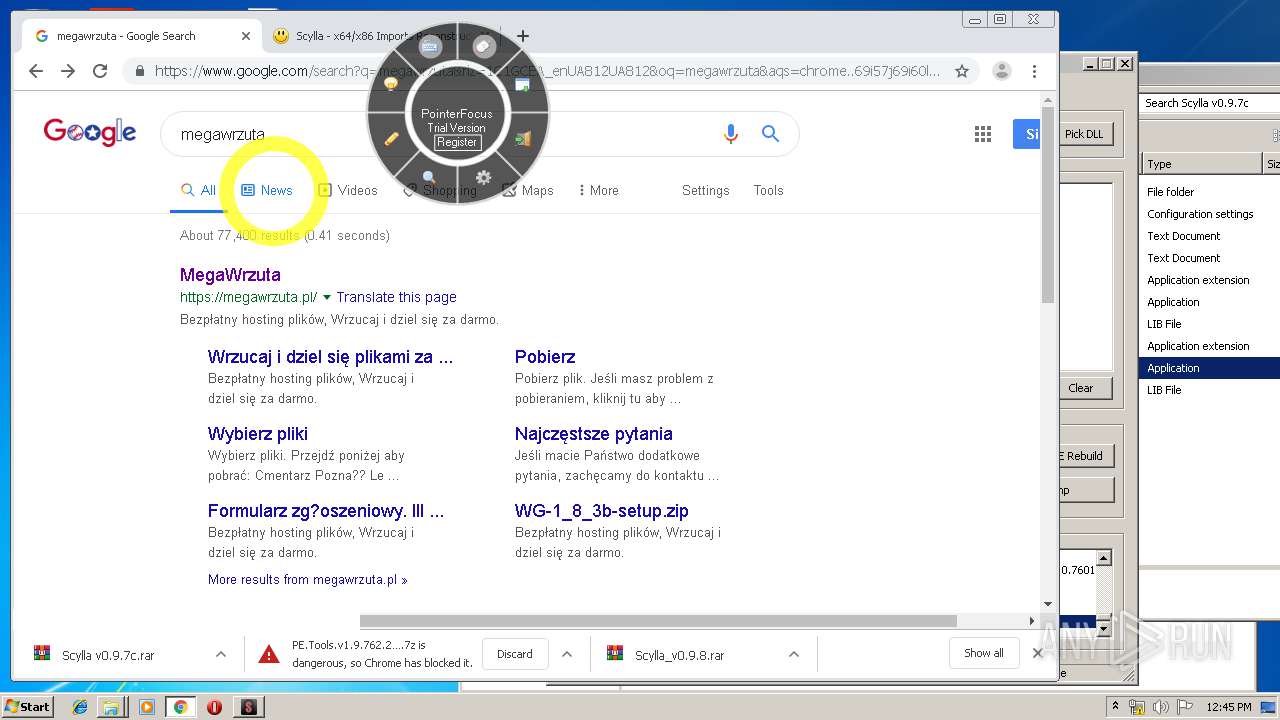
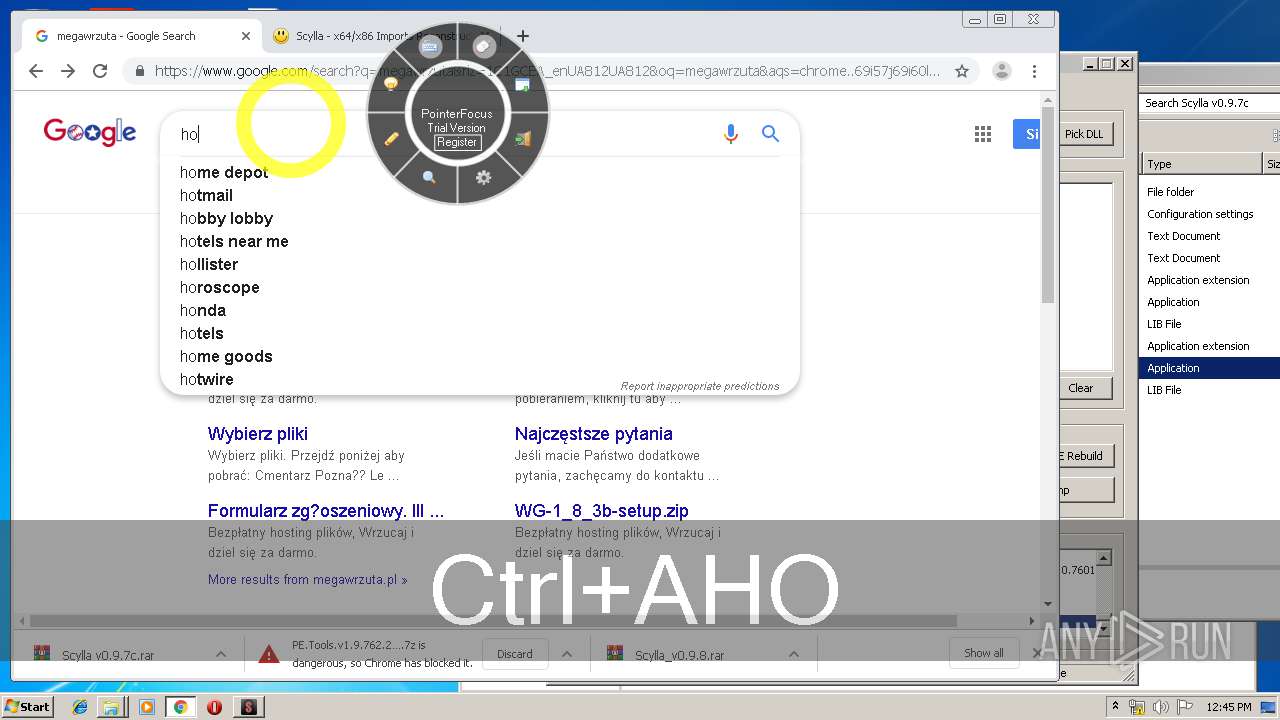
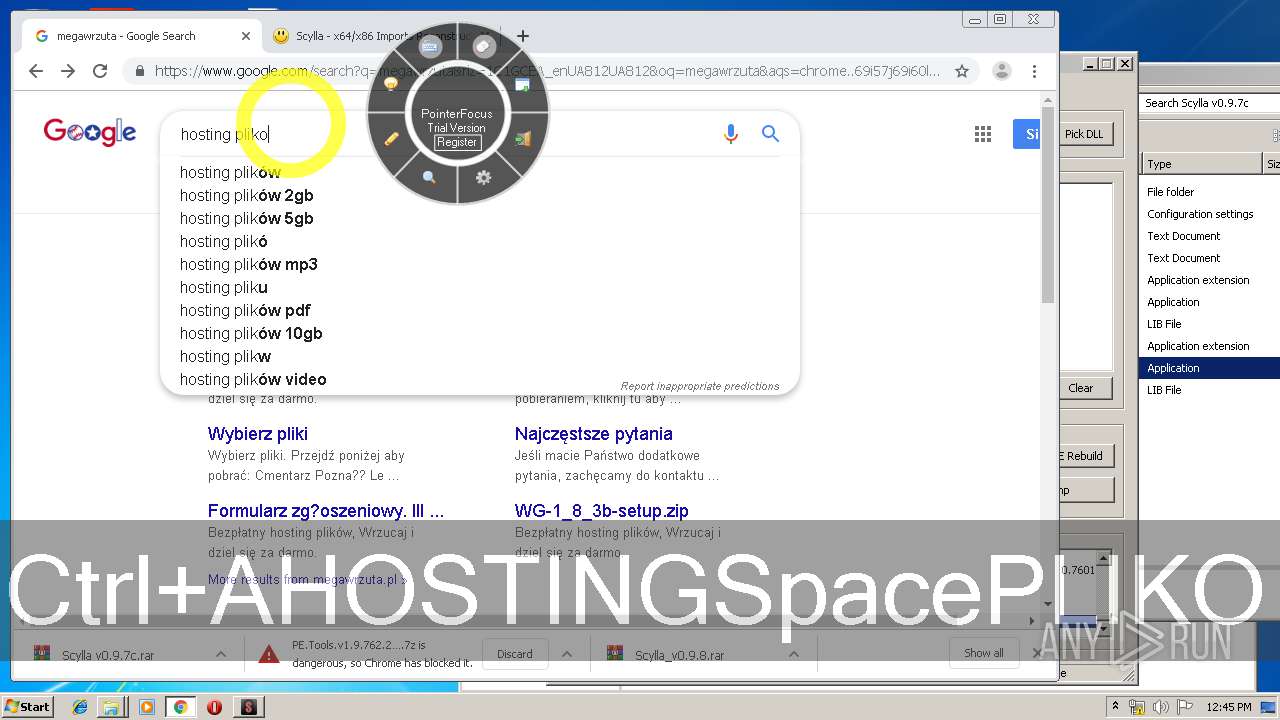
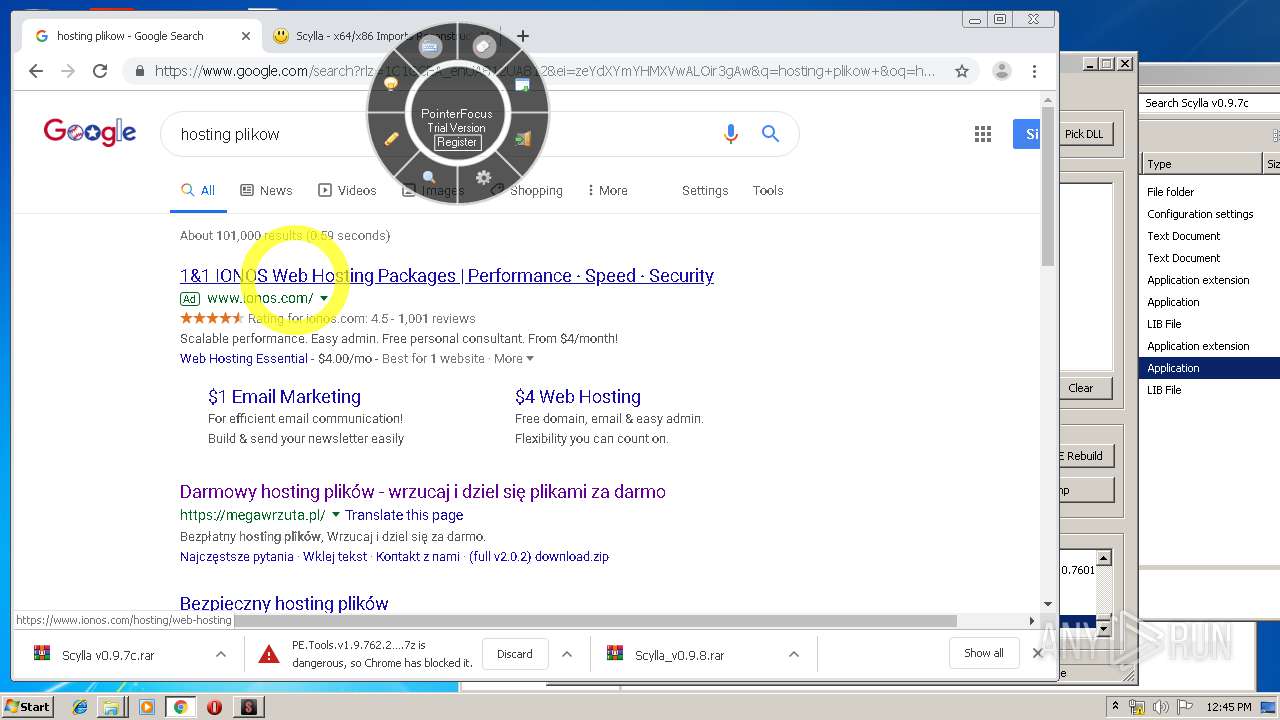
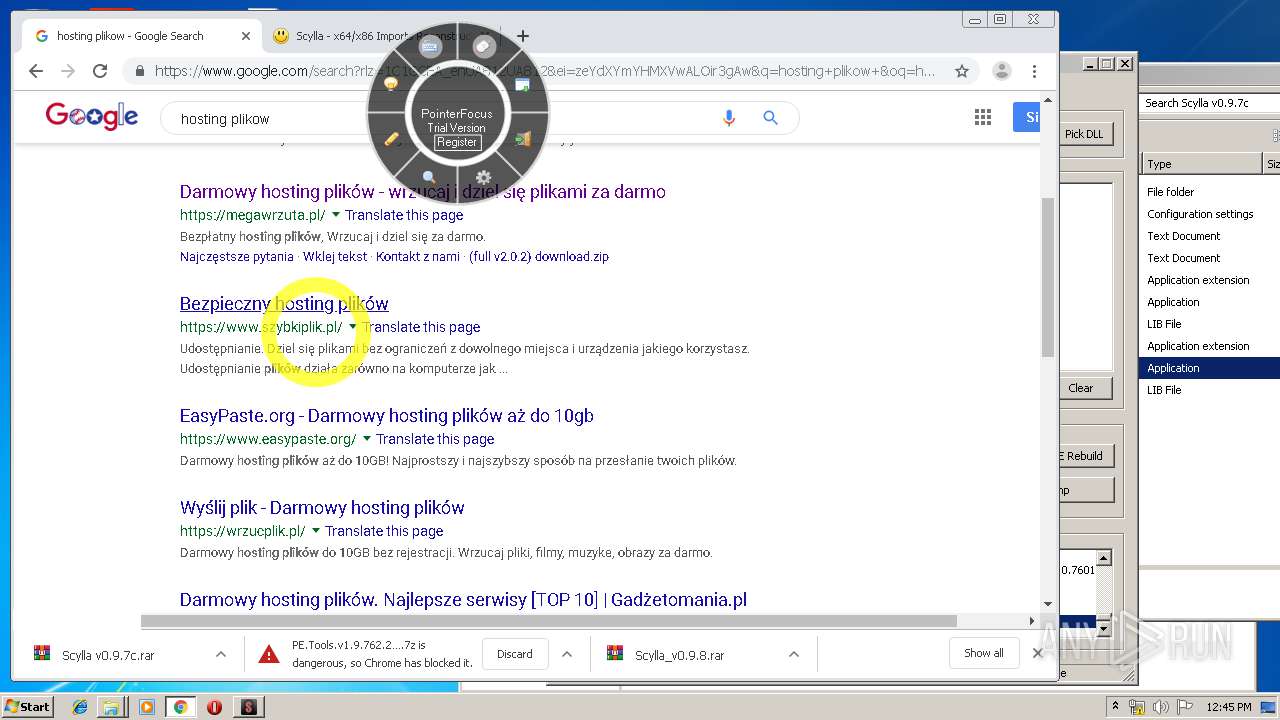
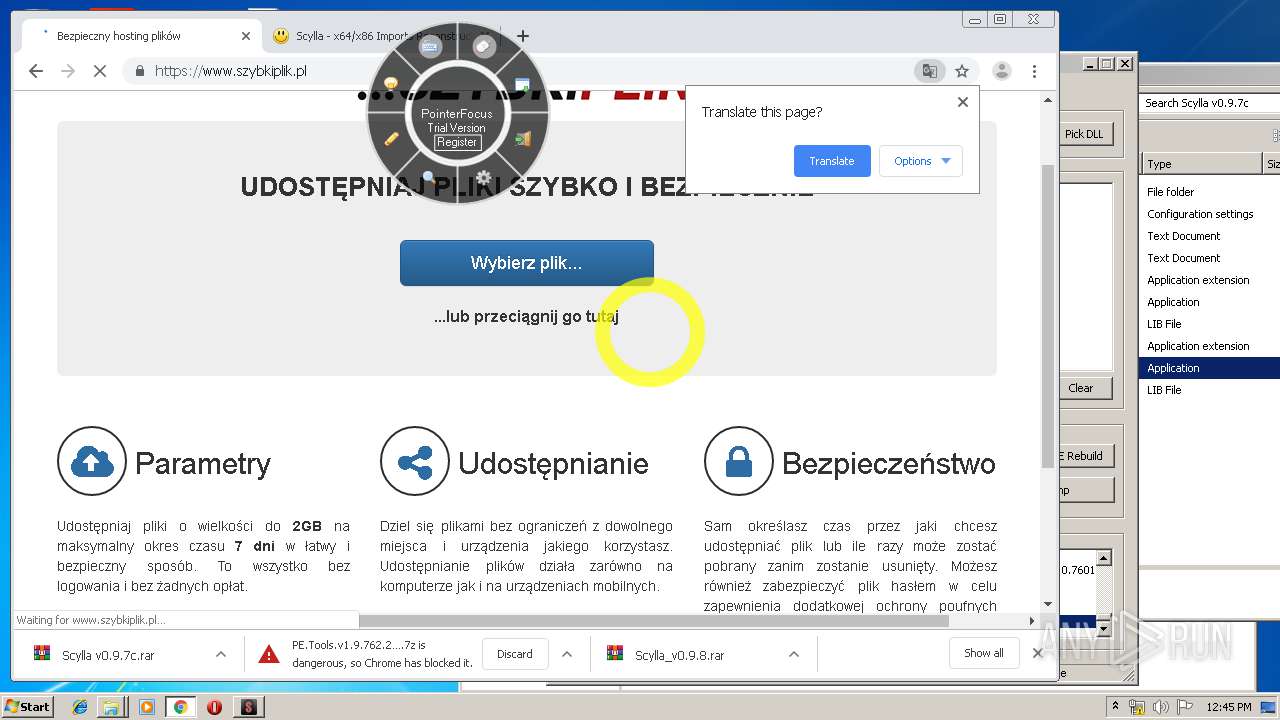
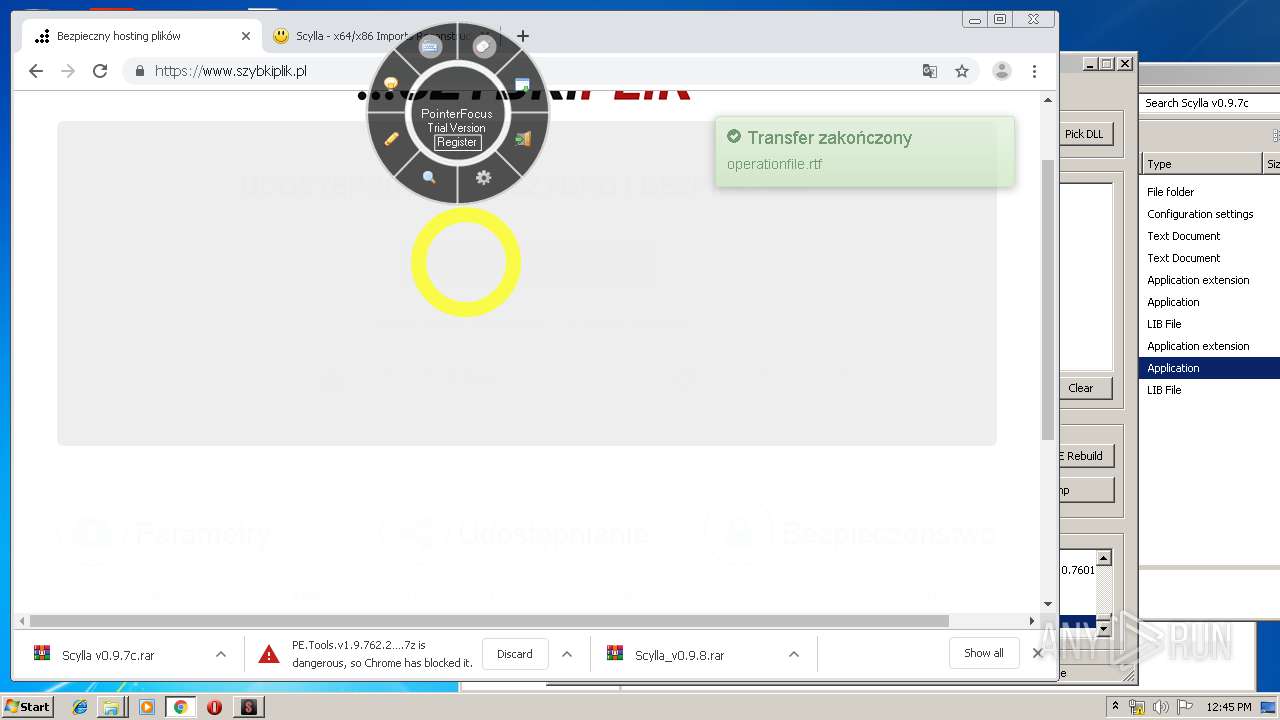
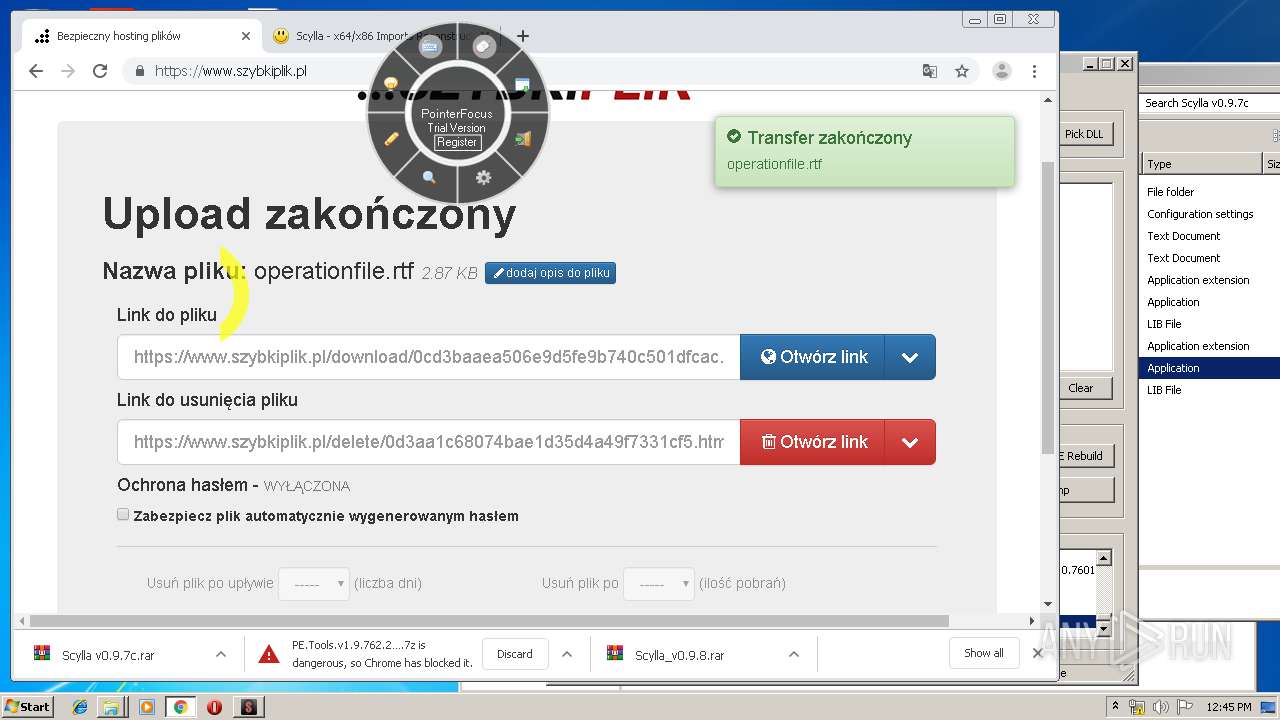
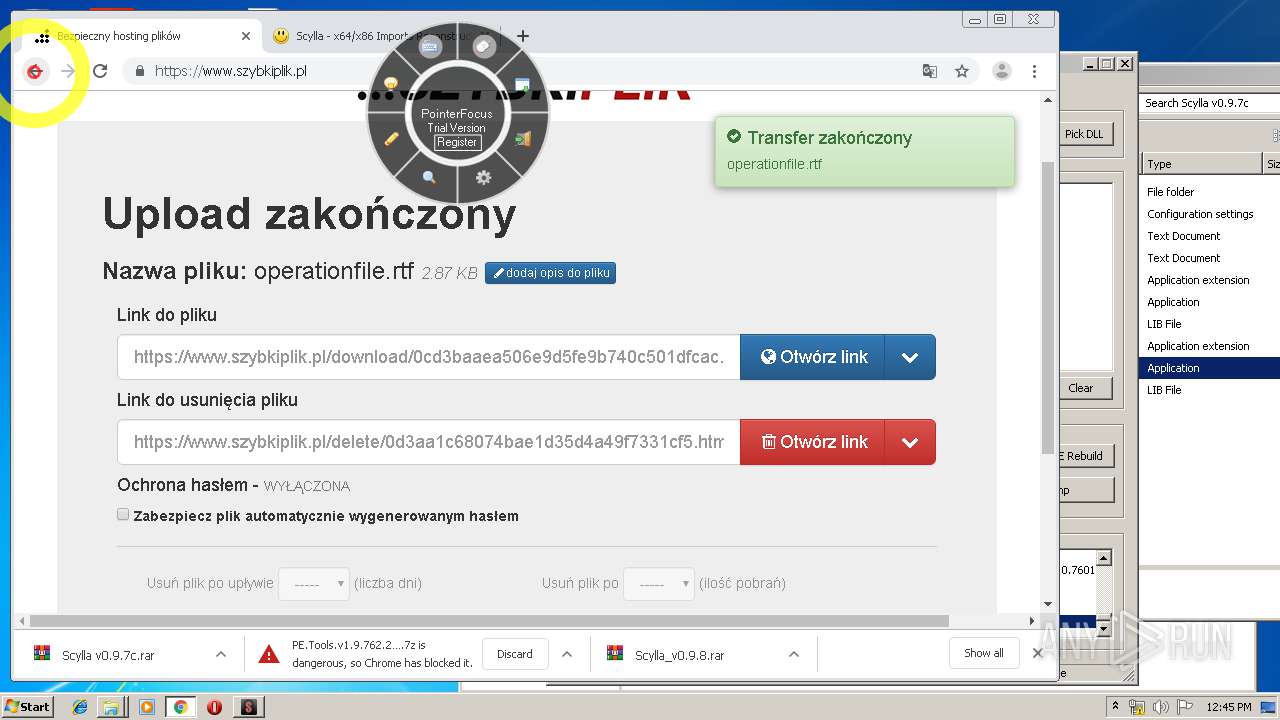
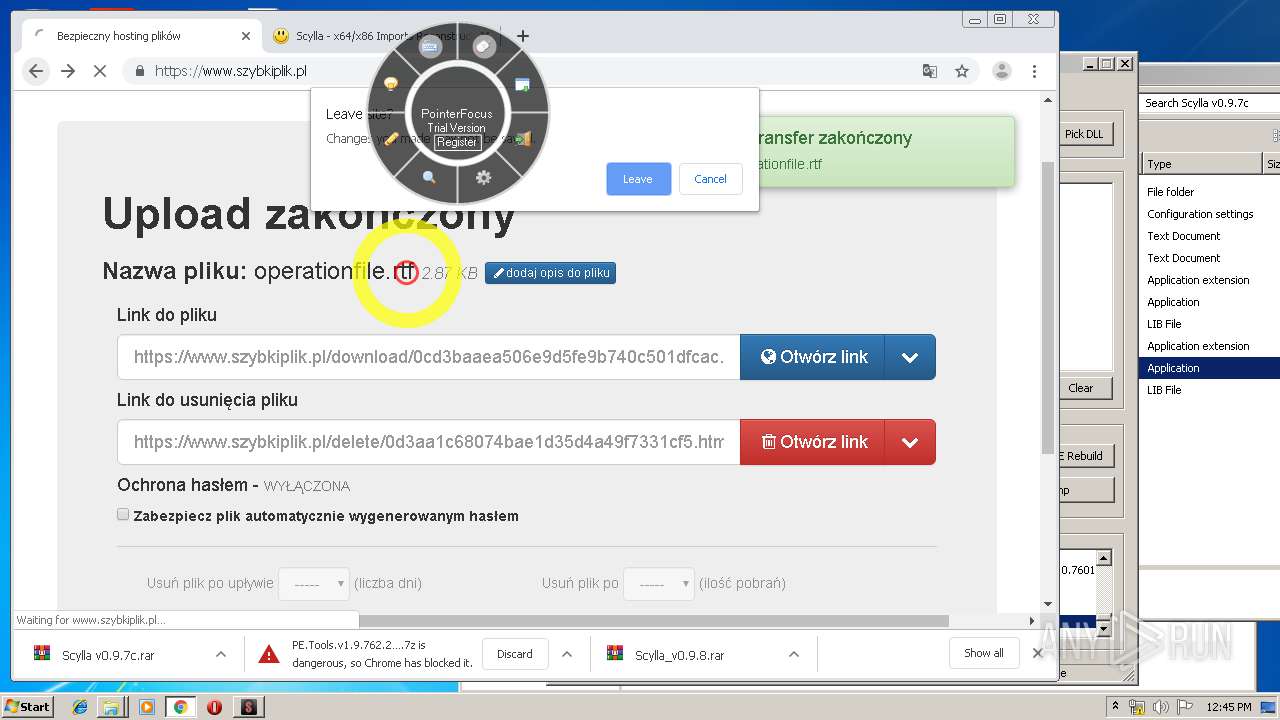
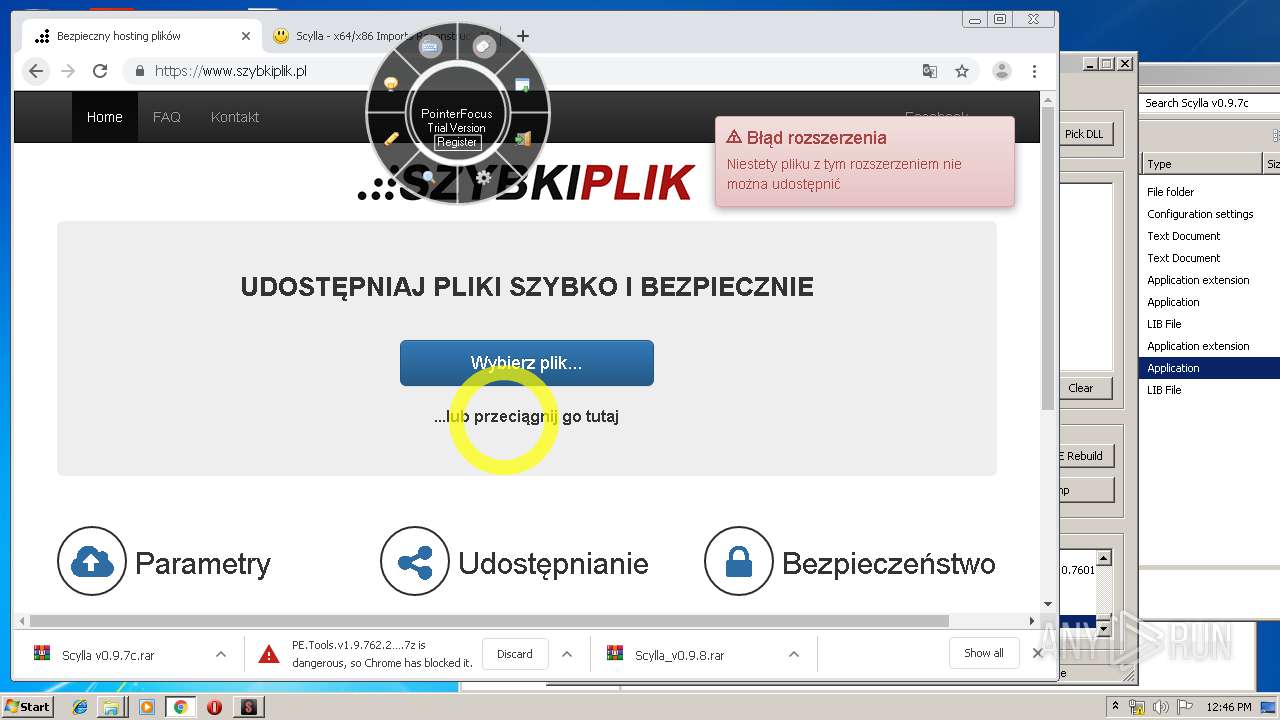
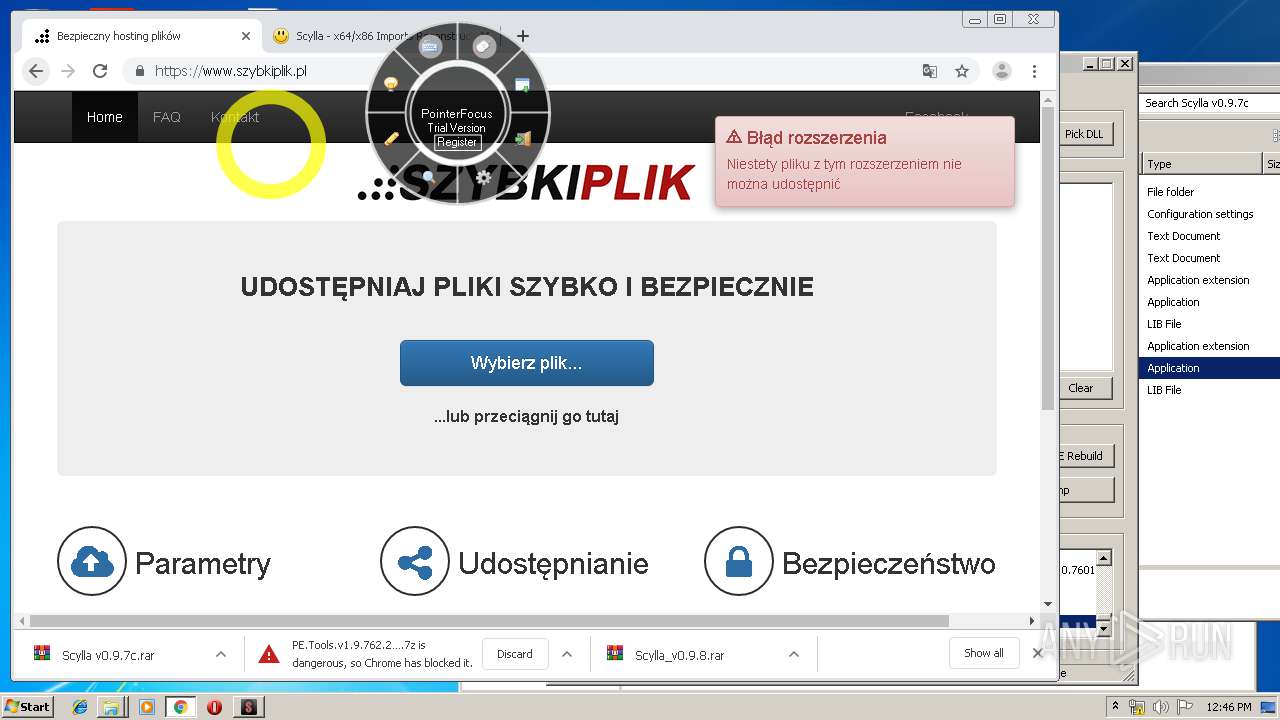
Modifies files in Chrome extension folder
- chrome.exe (PID: 3952)
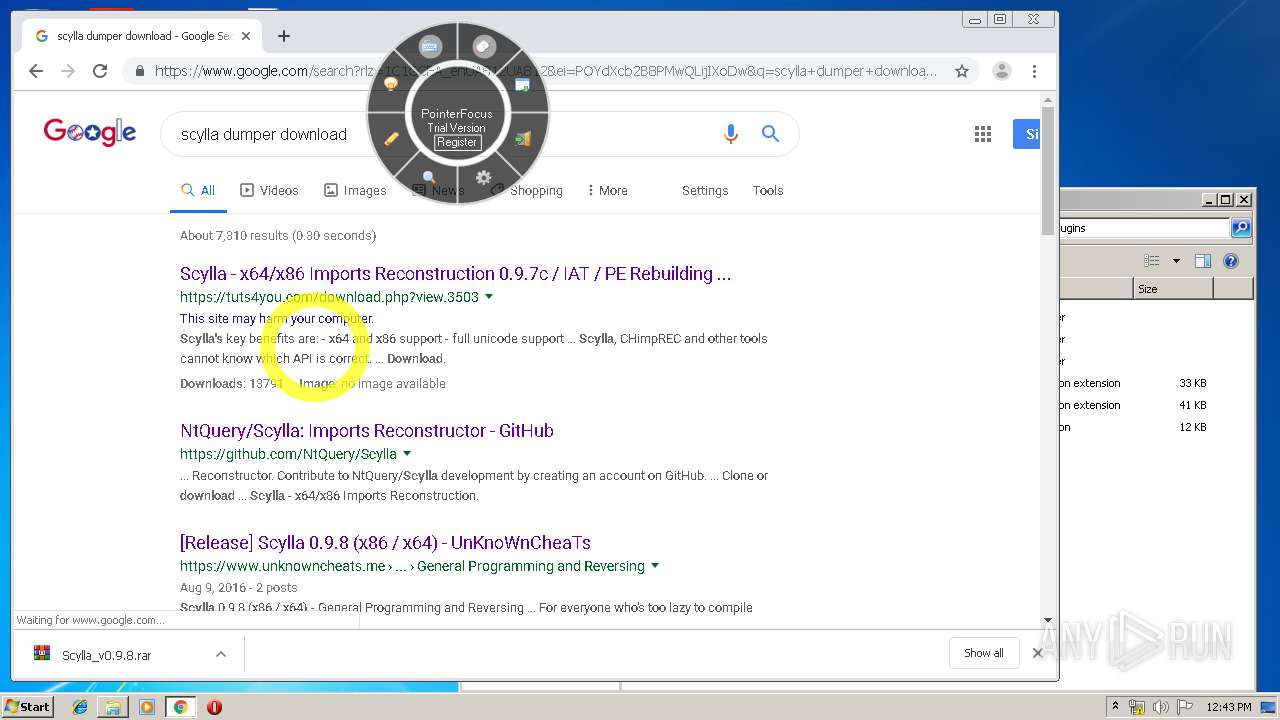
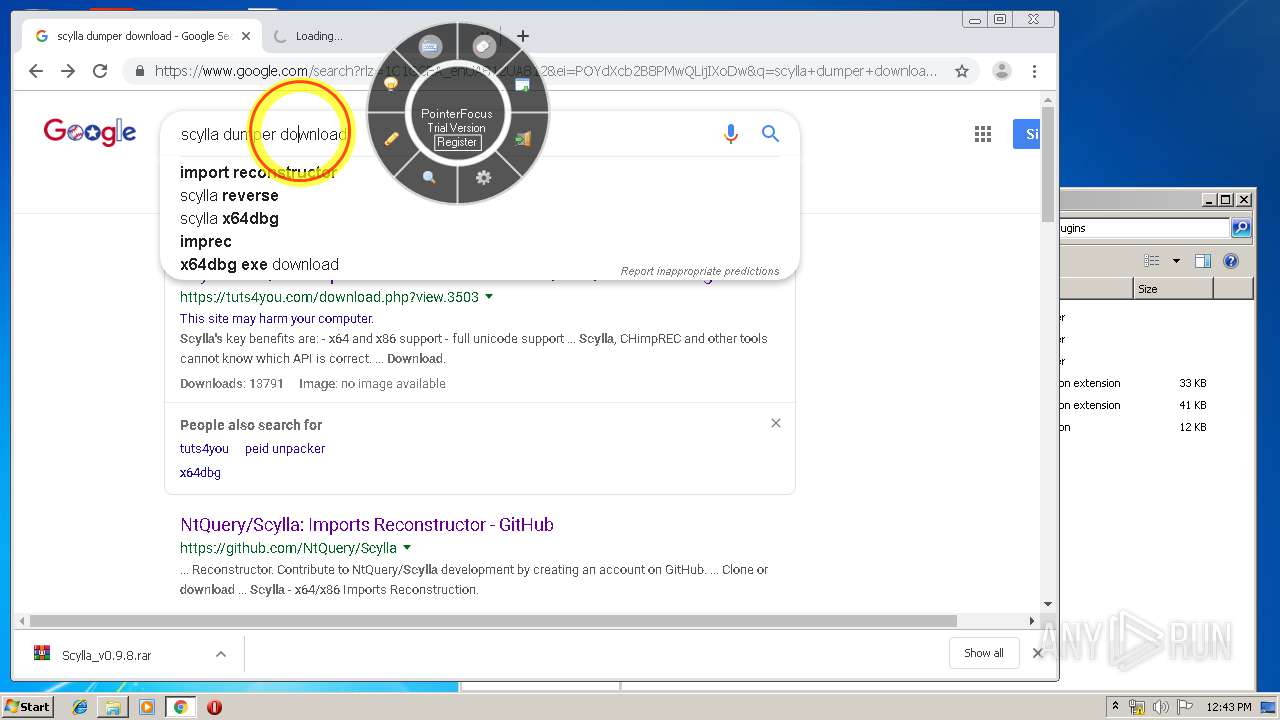
Reads Internet Cache Settings
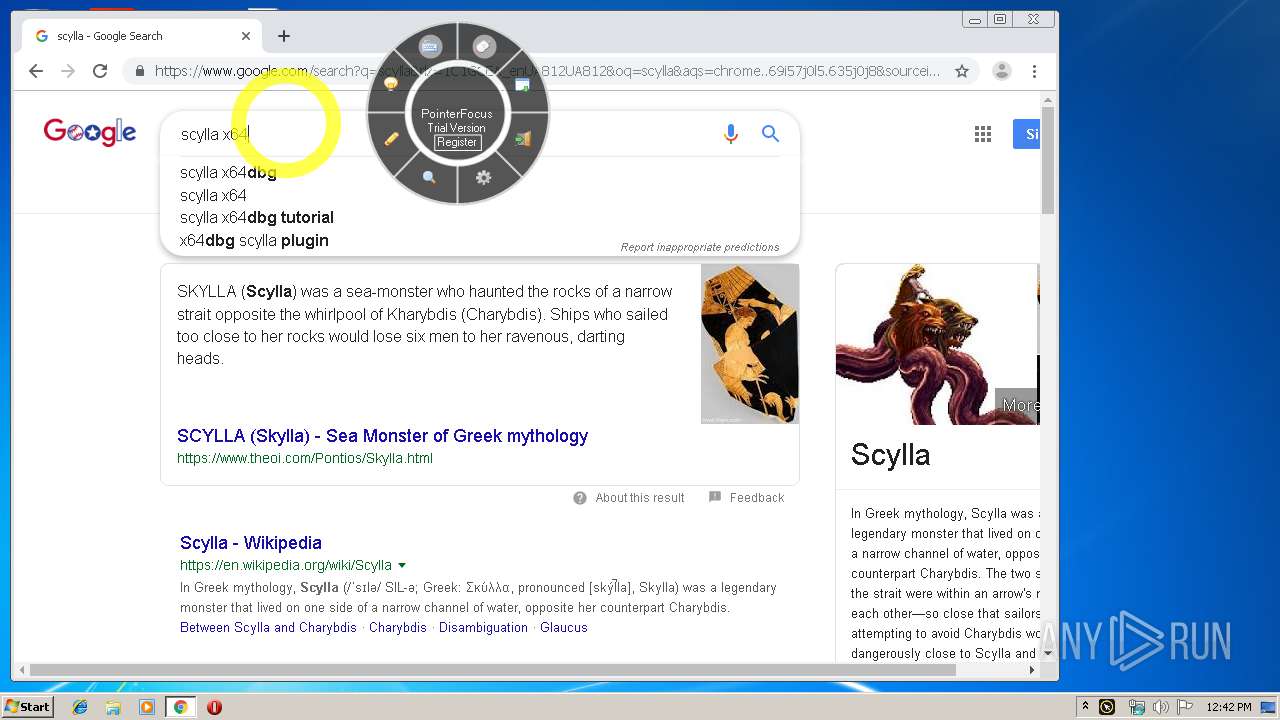
- Scylla_x86.exe (PID: 3840)
INFO
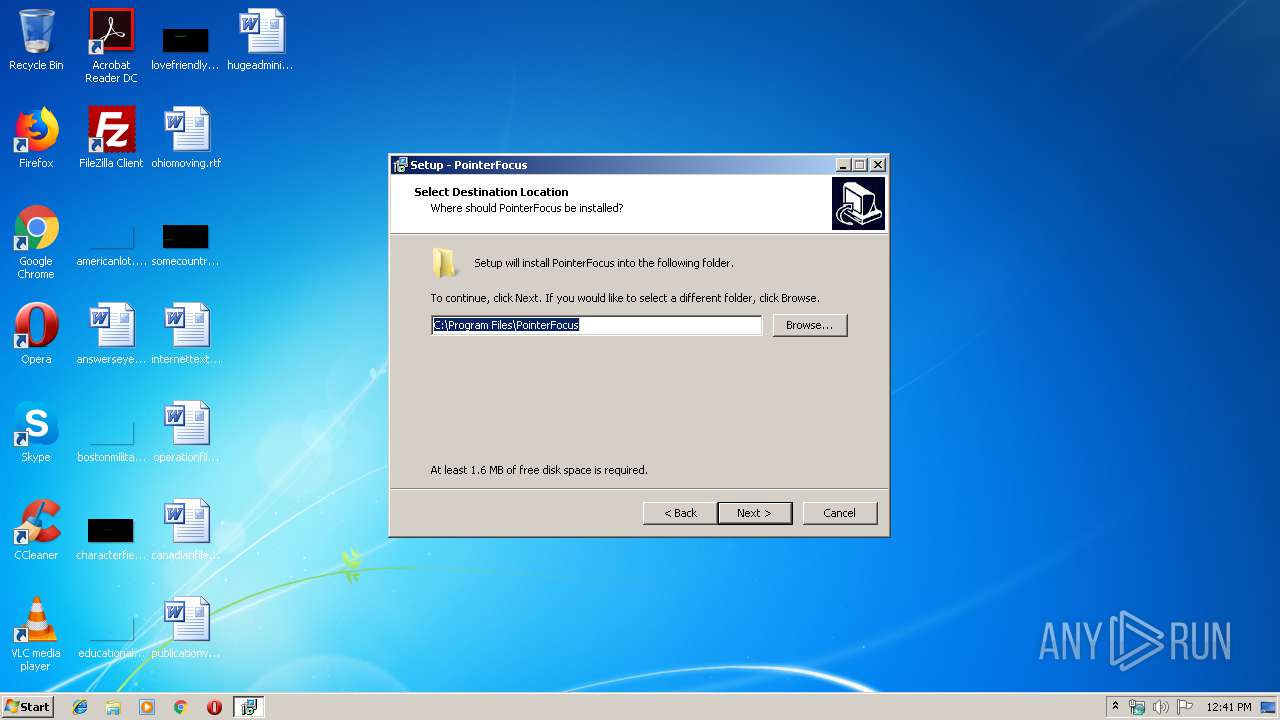
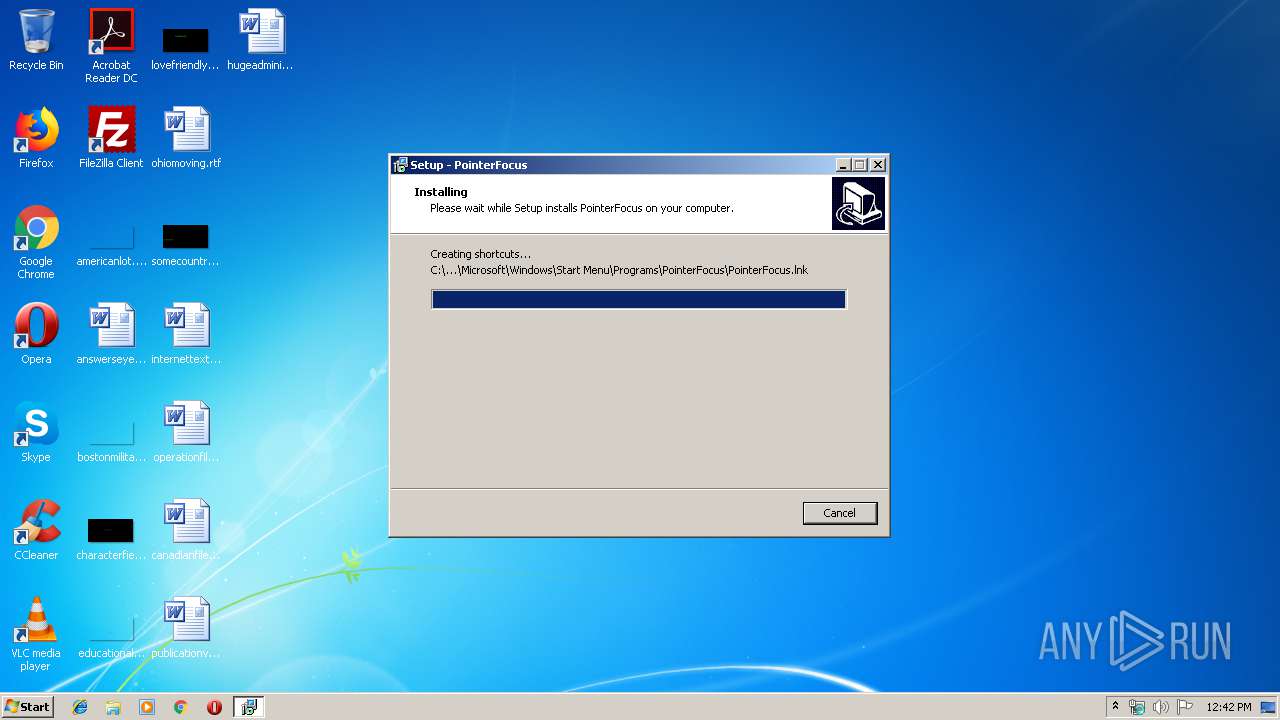
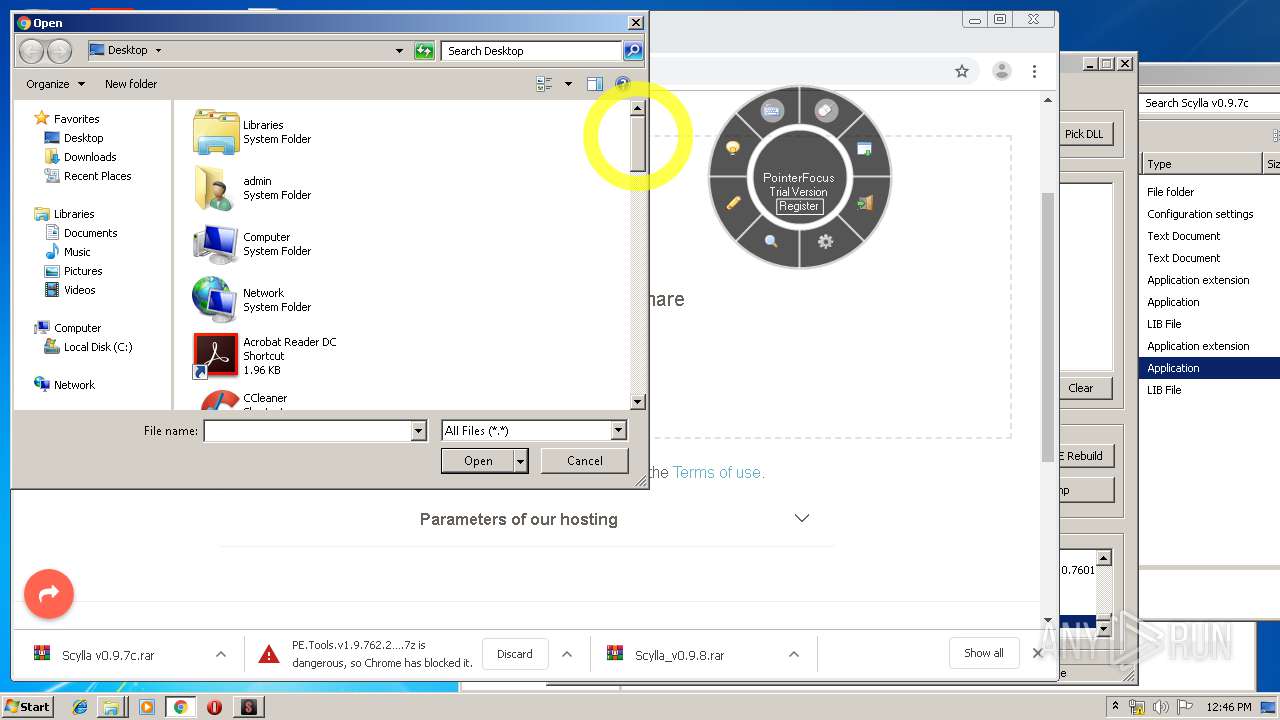
Application was dropped or rewritten from another process
- pfsetup.tmp (PID: 2988)
- pfsetup.tmp (PID: 3768)
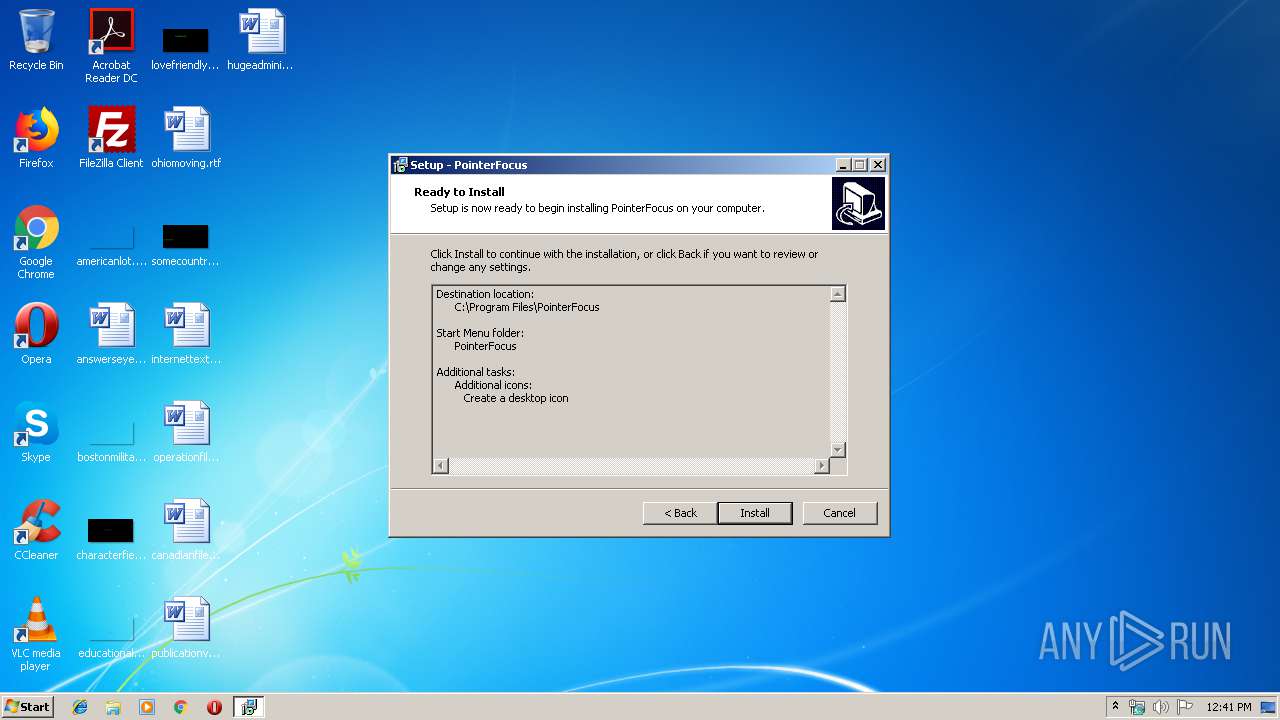
Creates a software uninstall entry
- pfsetup.tmp (PID: 2988)
Loads dropped or rewritten executable
- pfsetup.tmp (PID: 2988)
Creates files in the program directory
- pfsetup.tmp (PID: 2988)
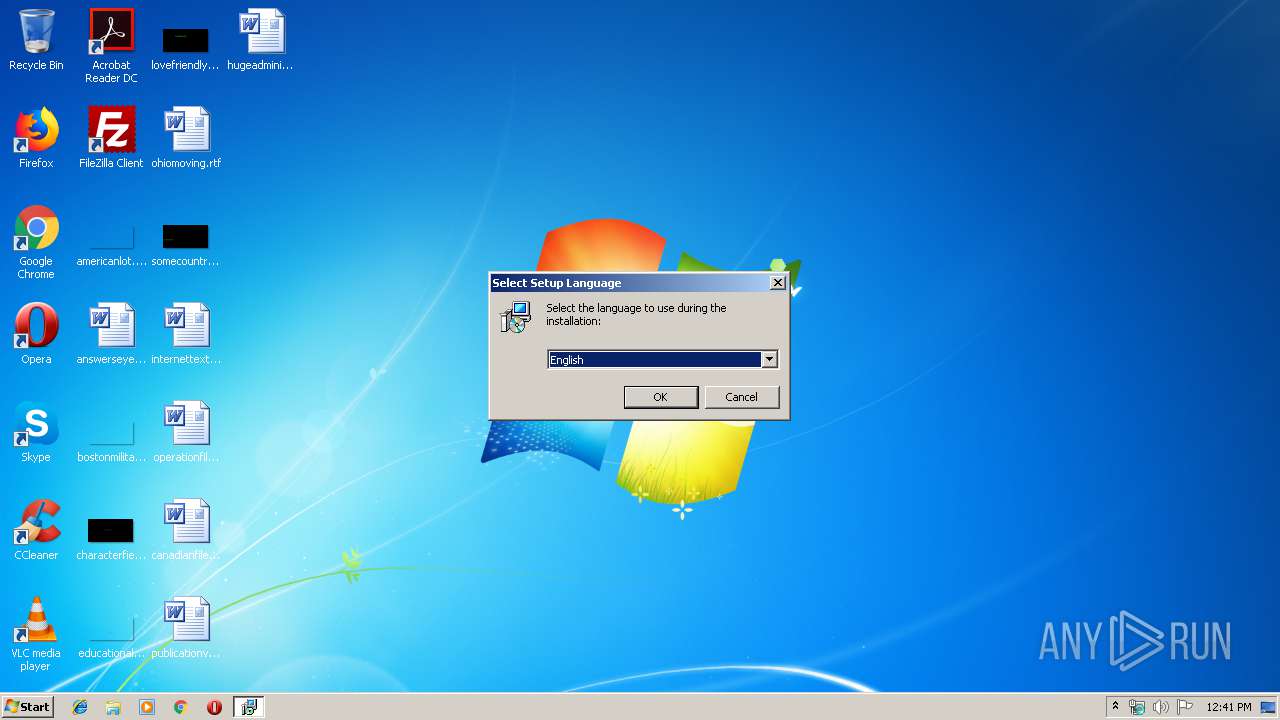
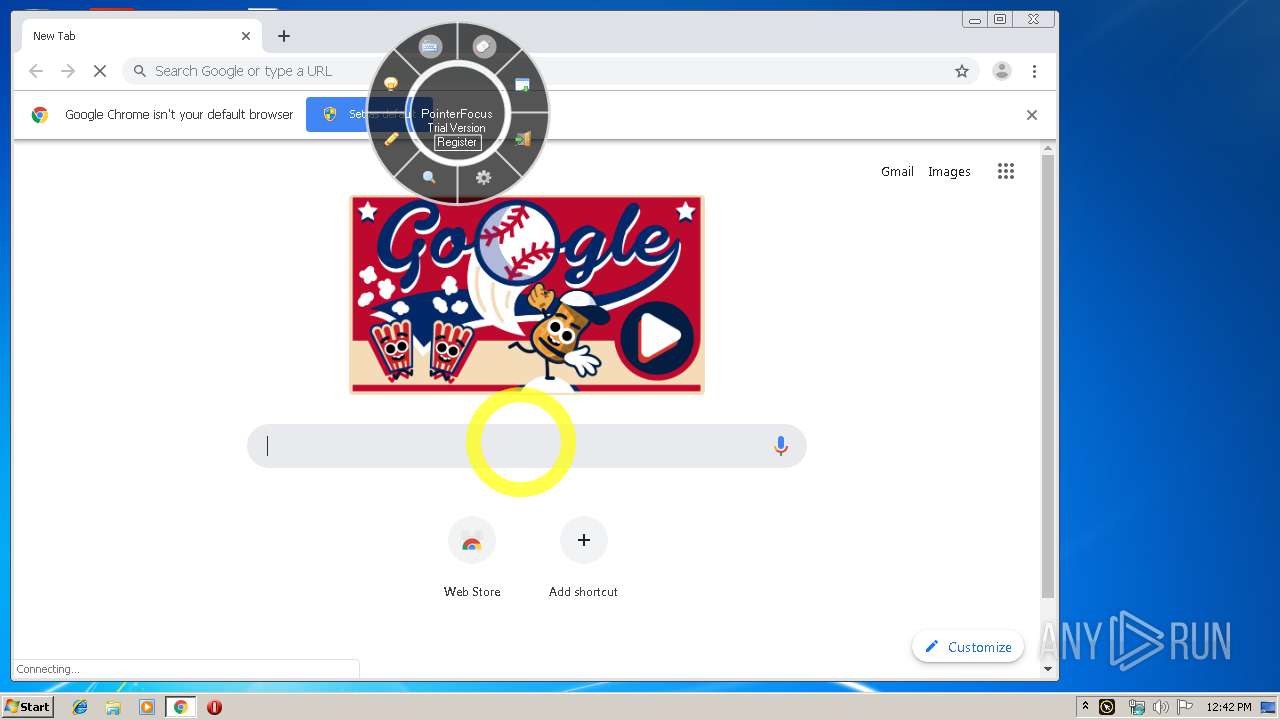
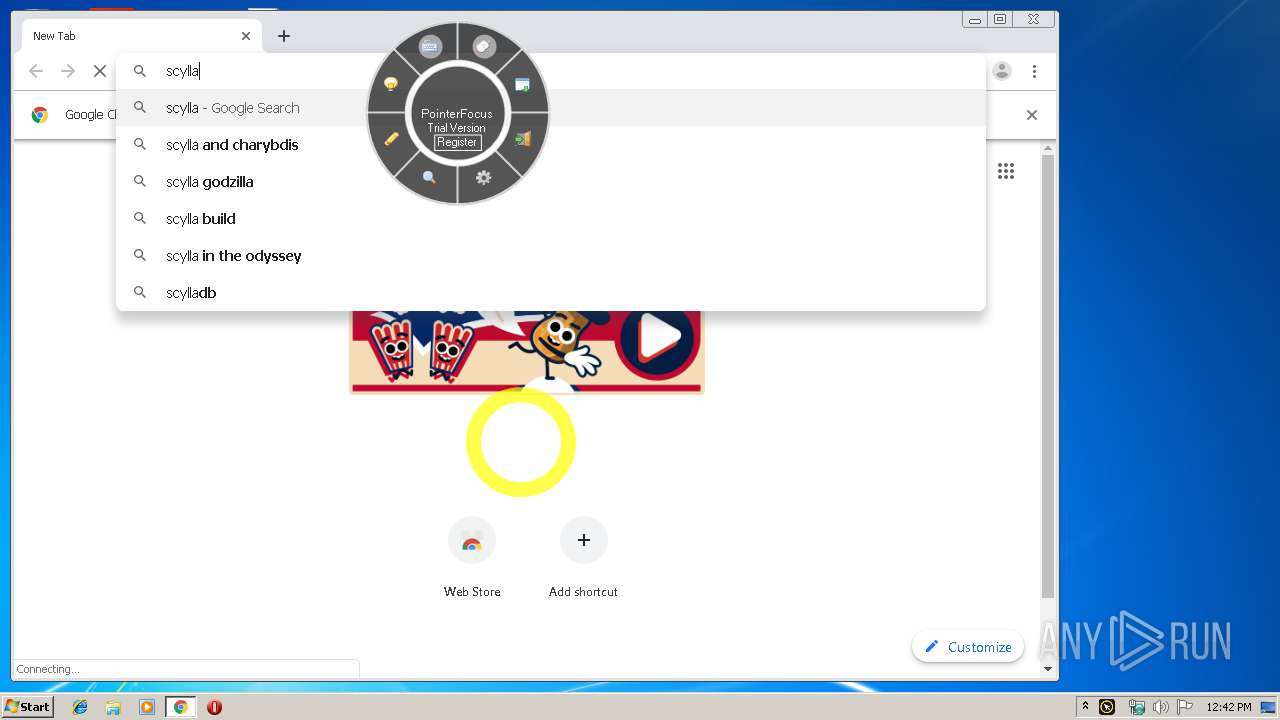
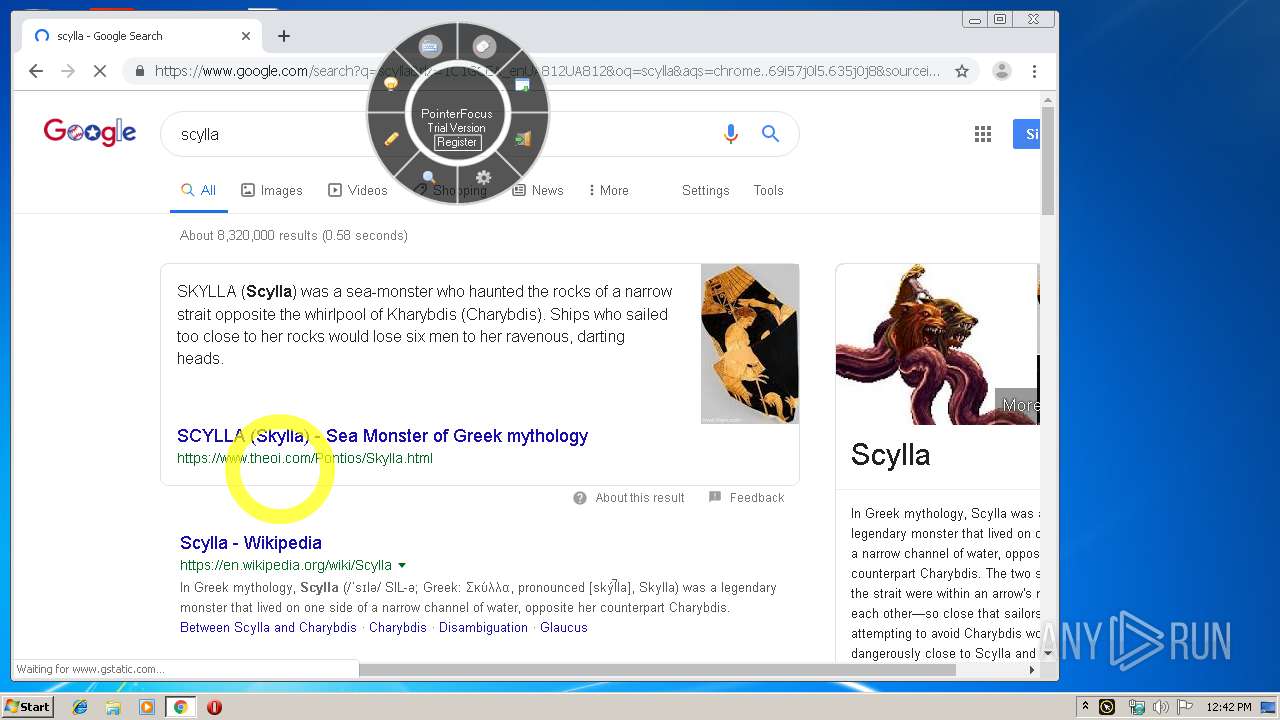
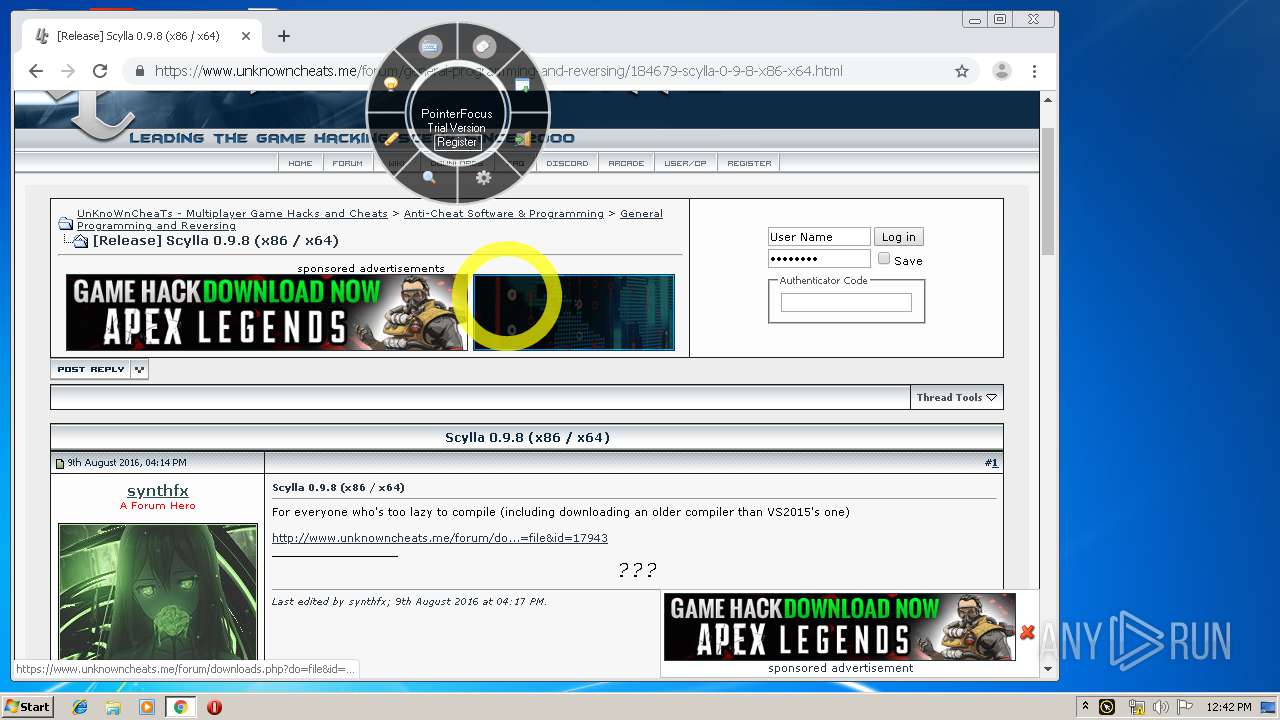
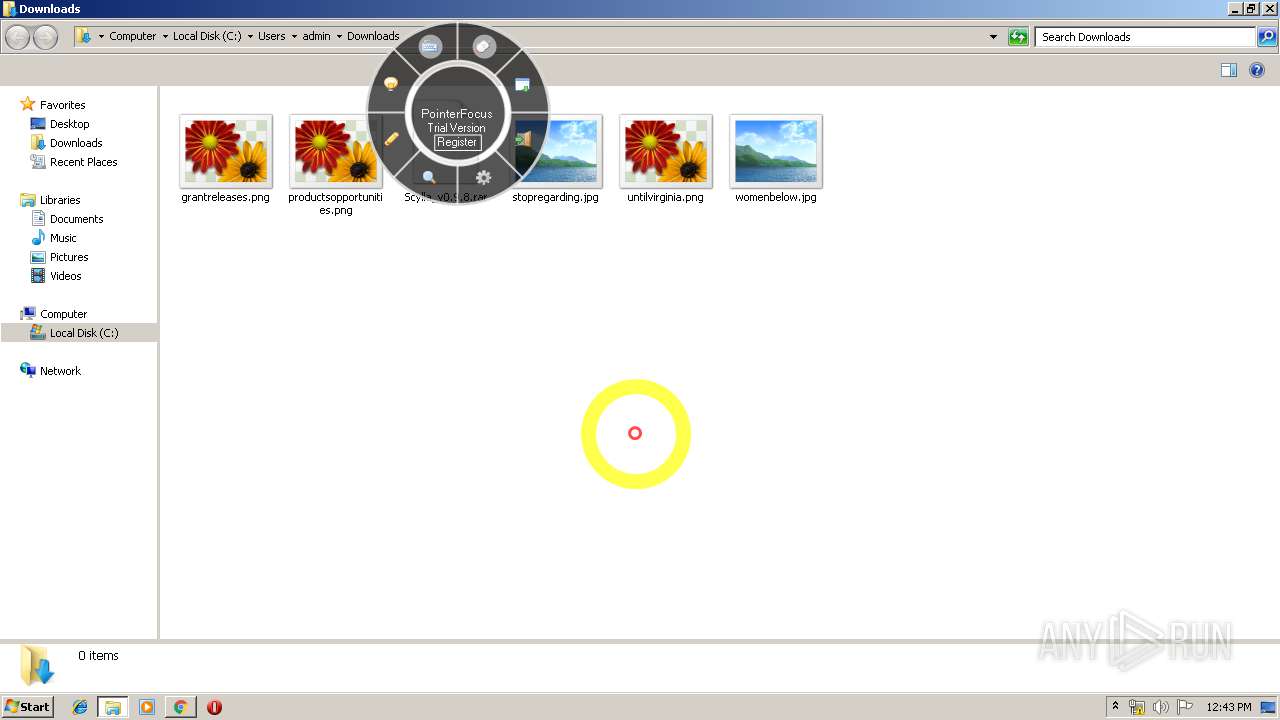
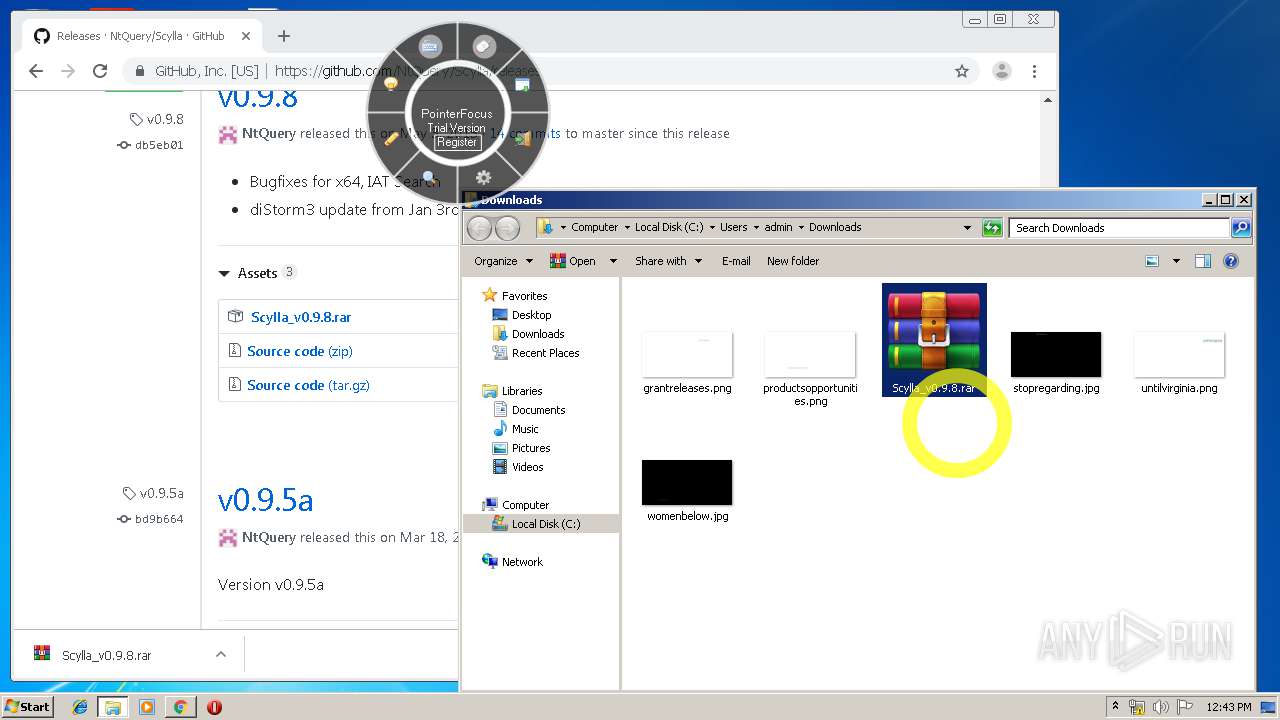
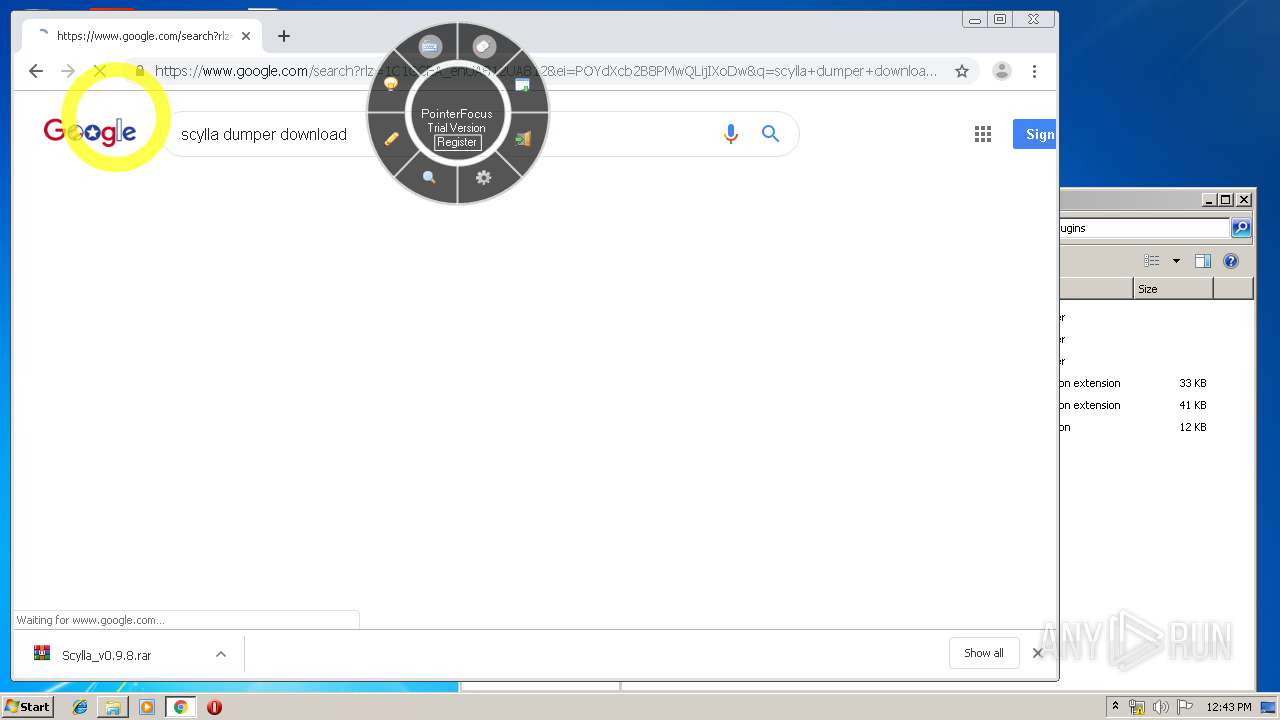
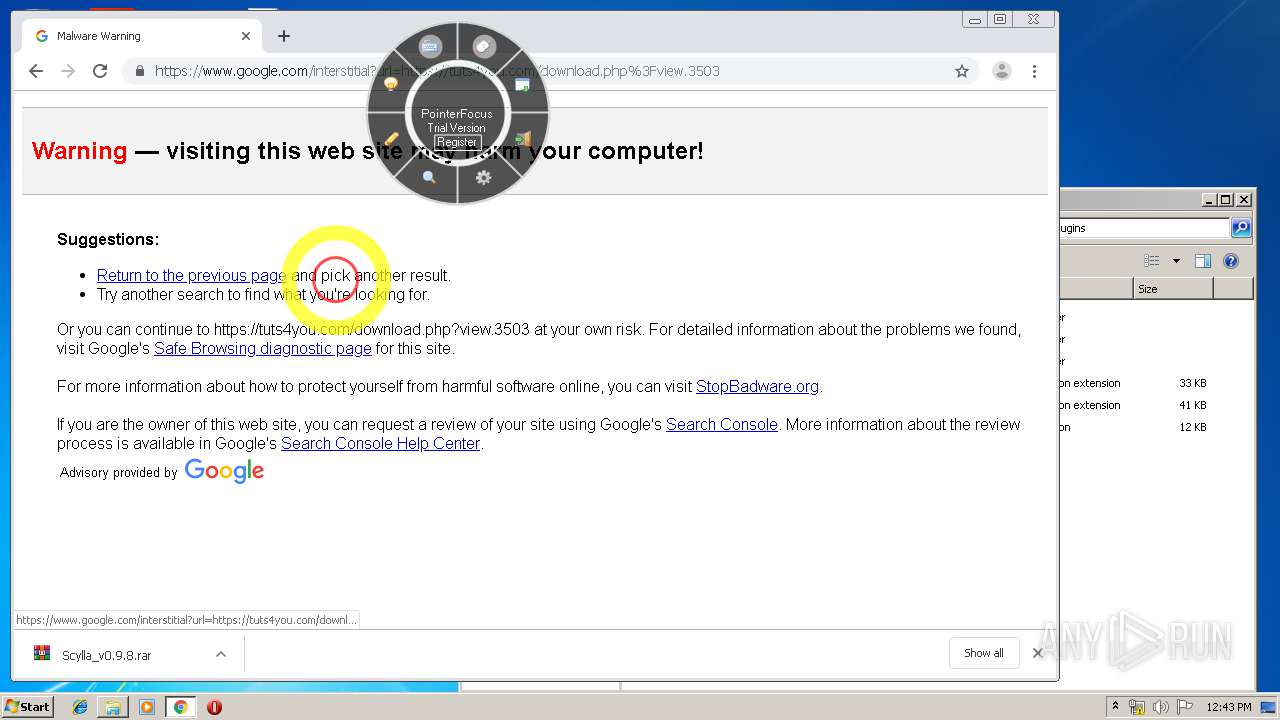
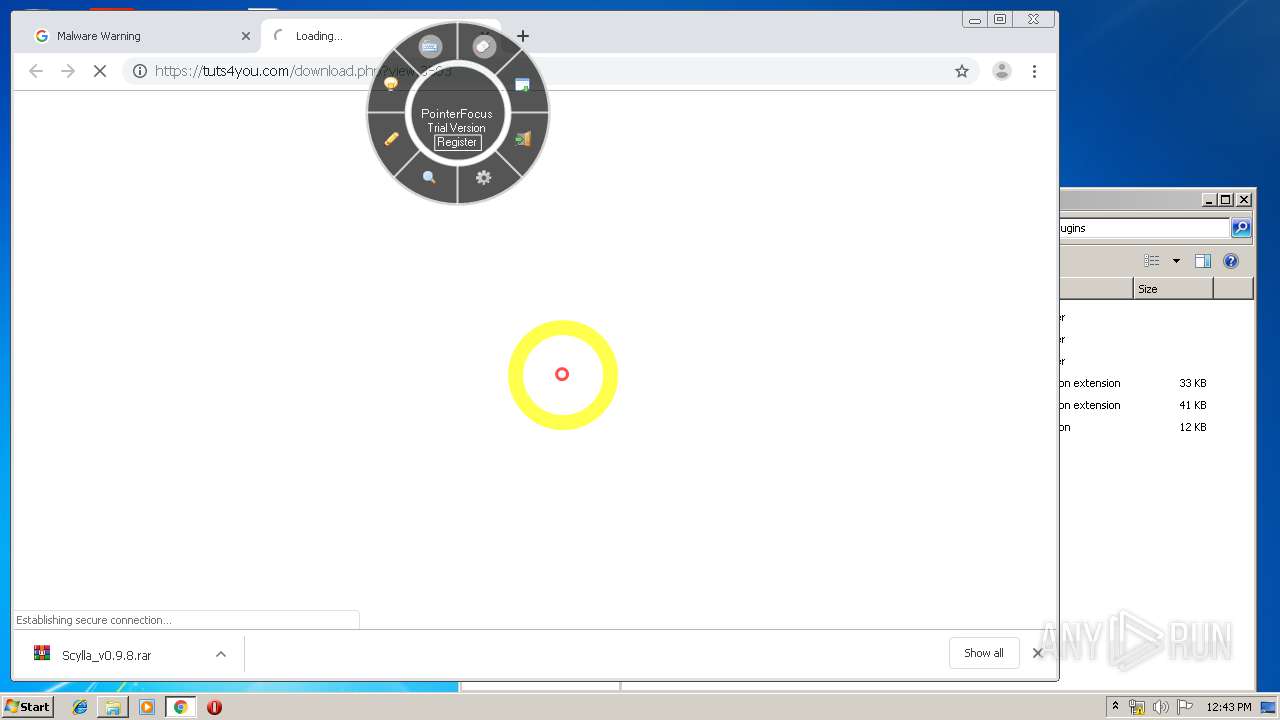
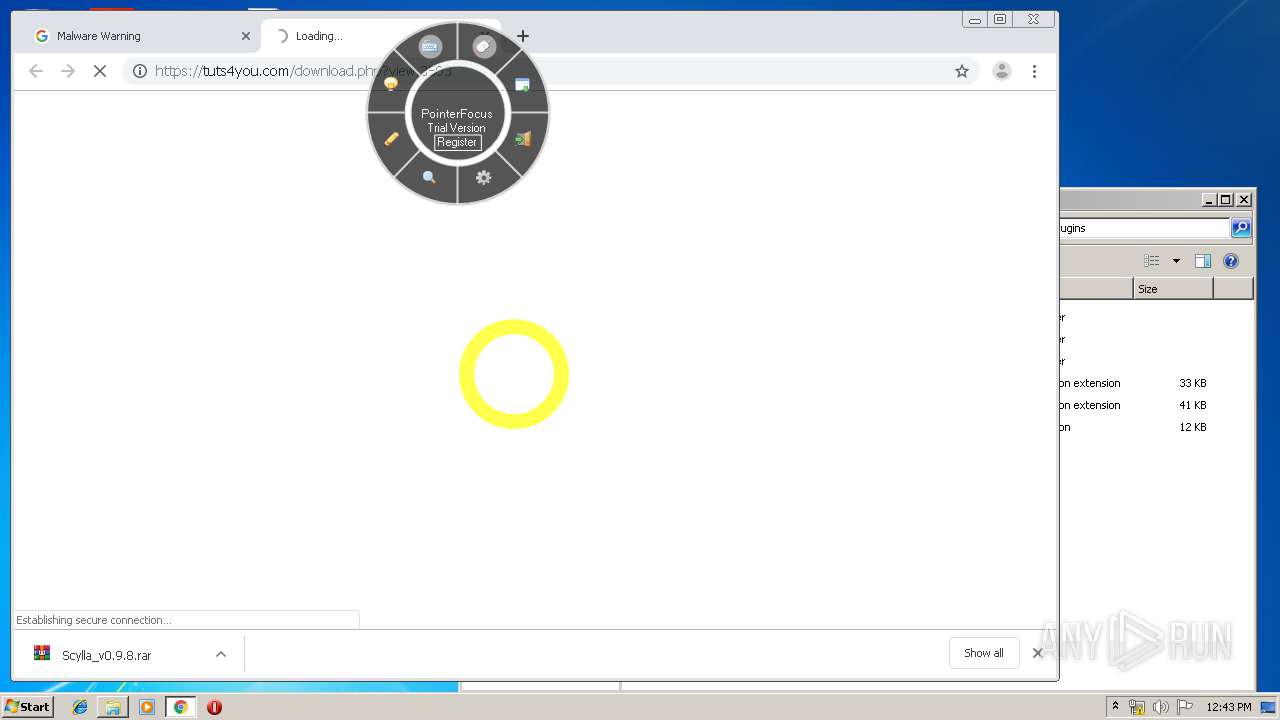
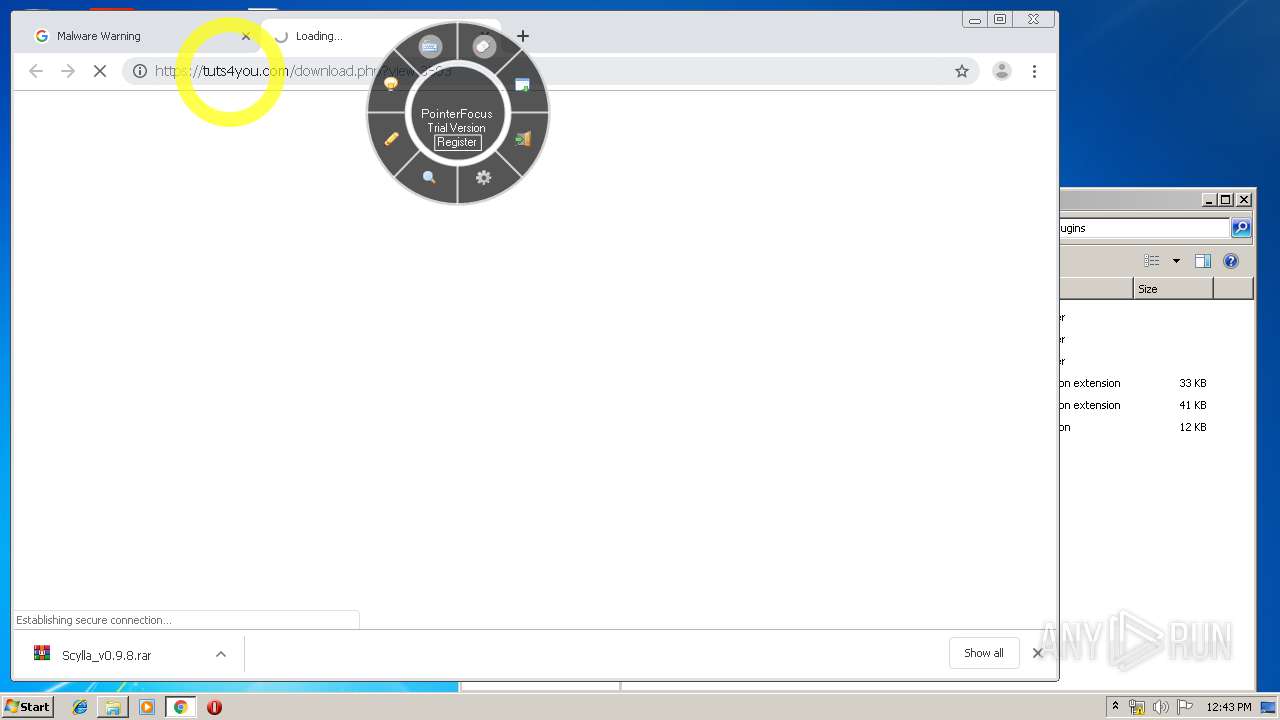
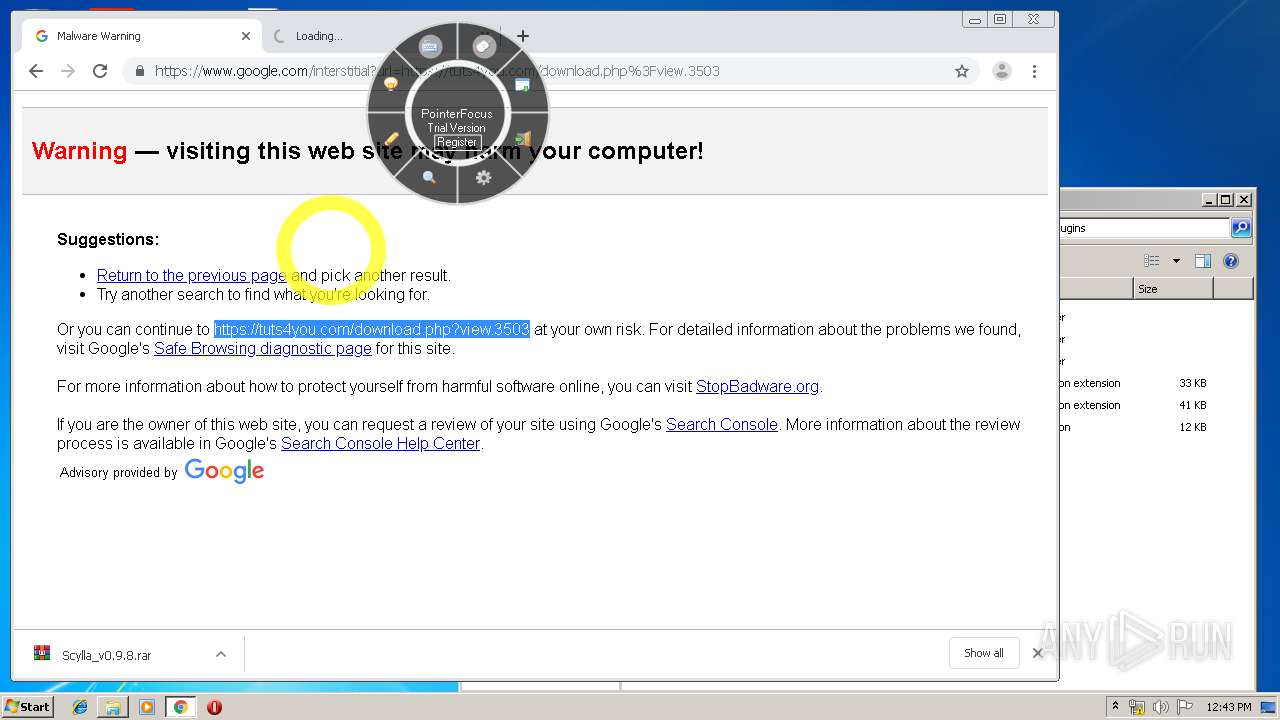
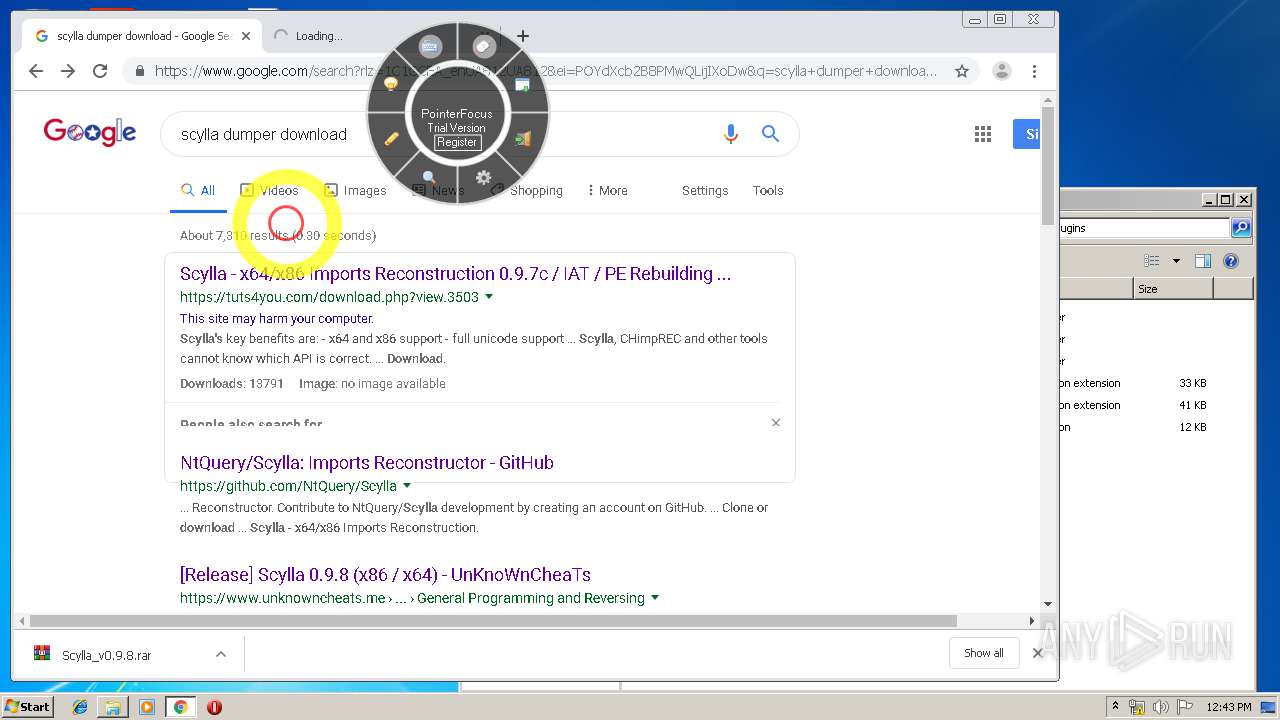
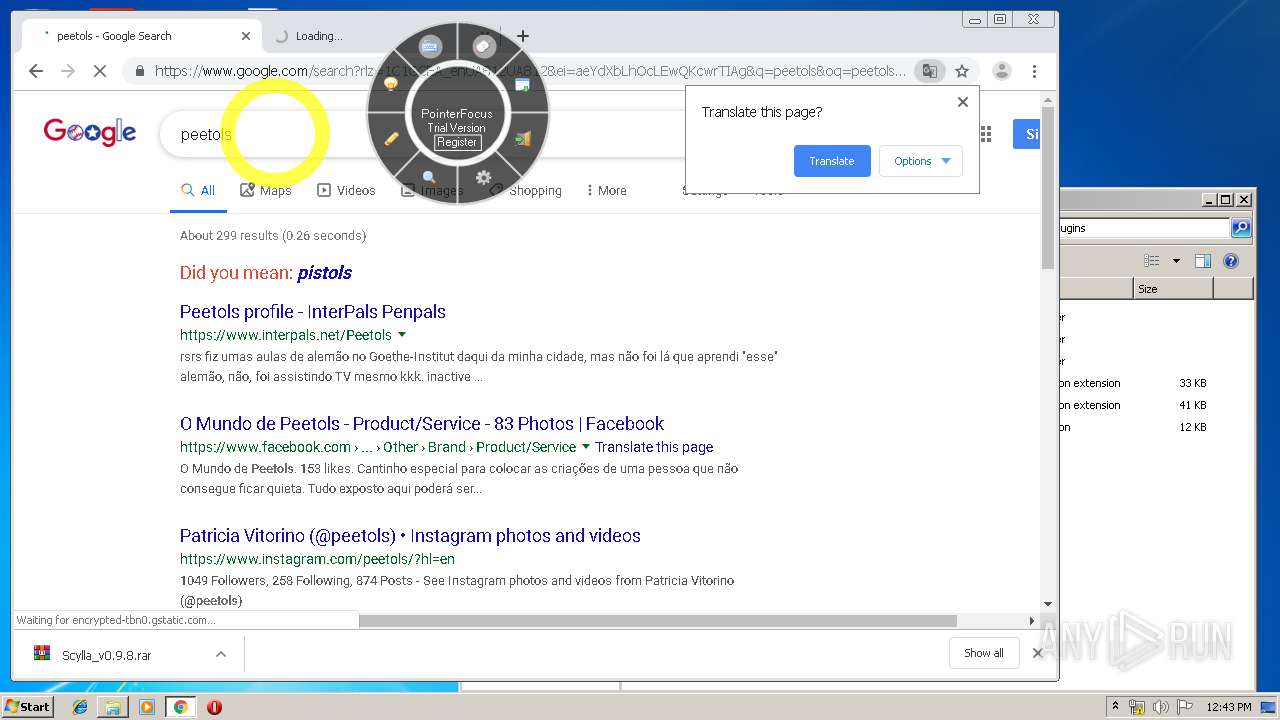
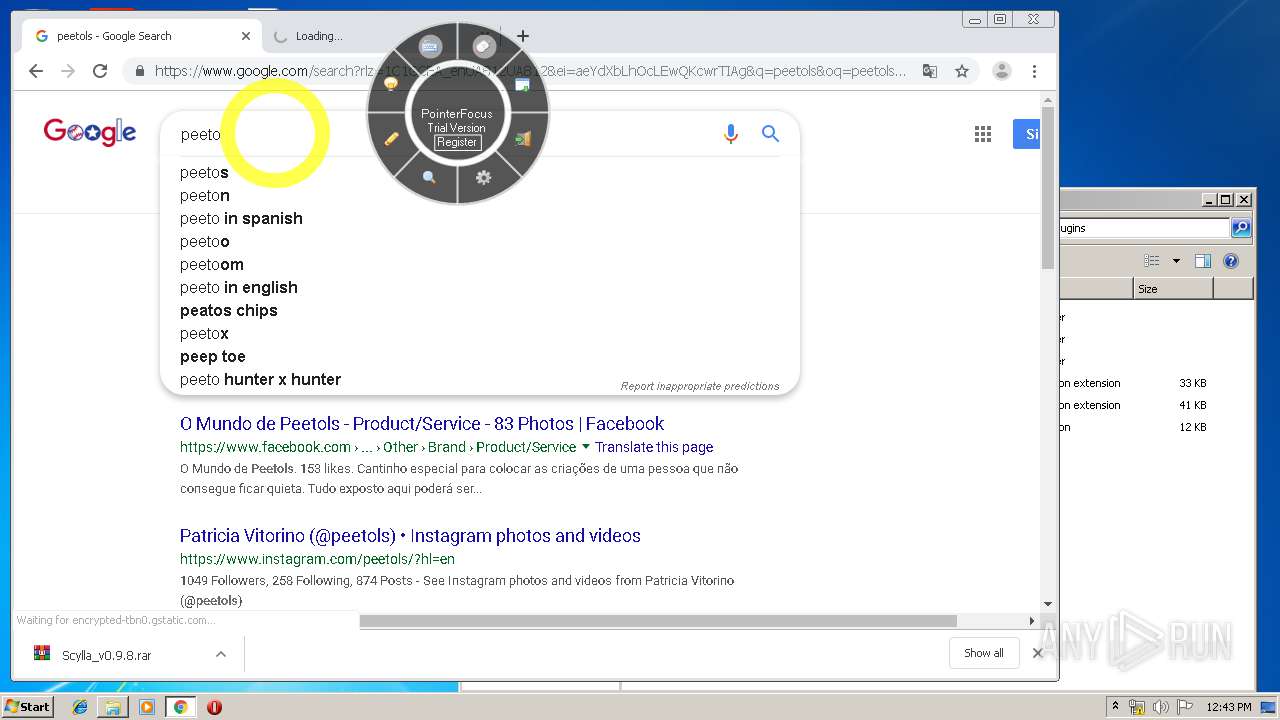
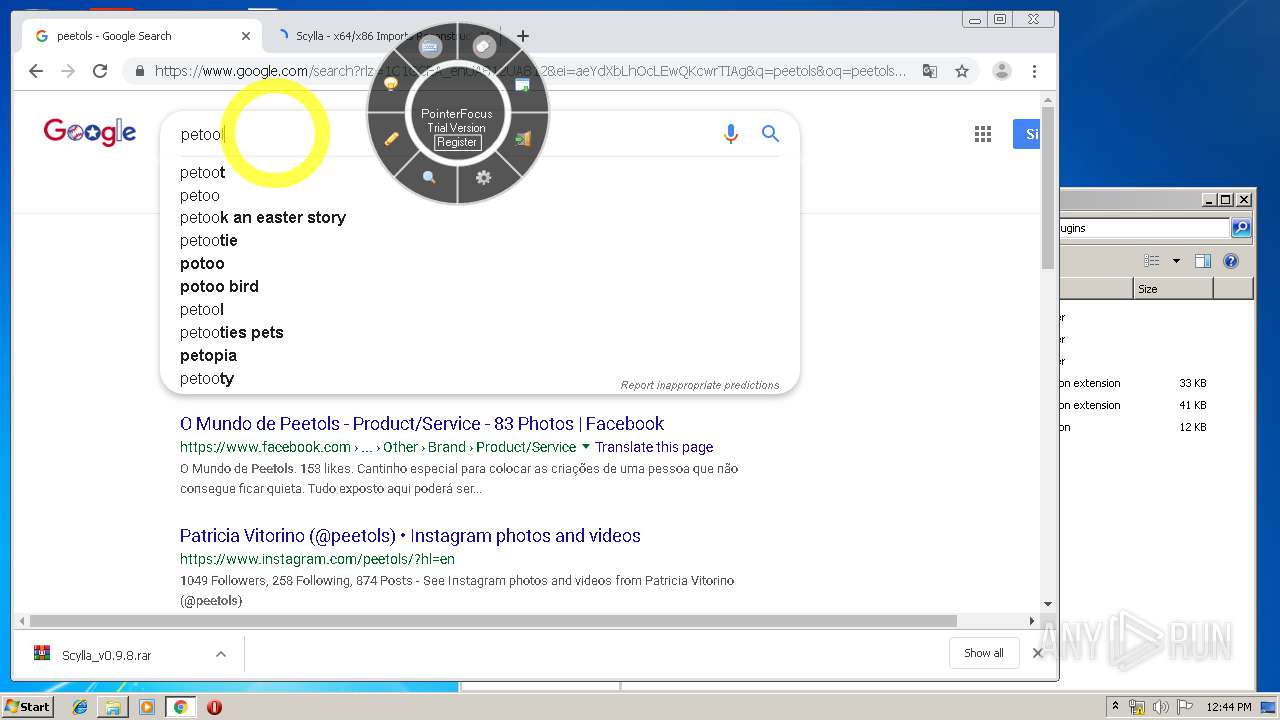
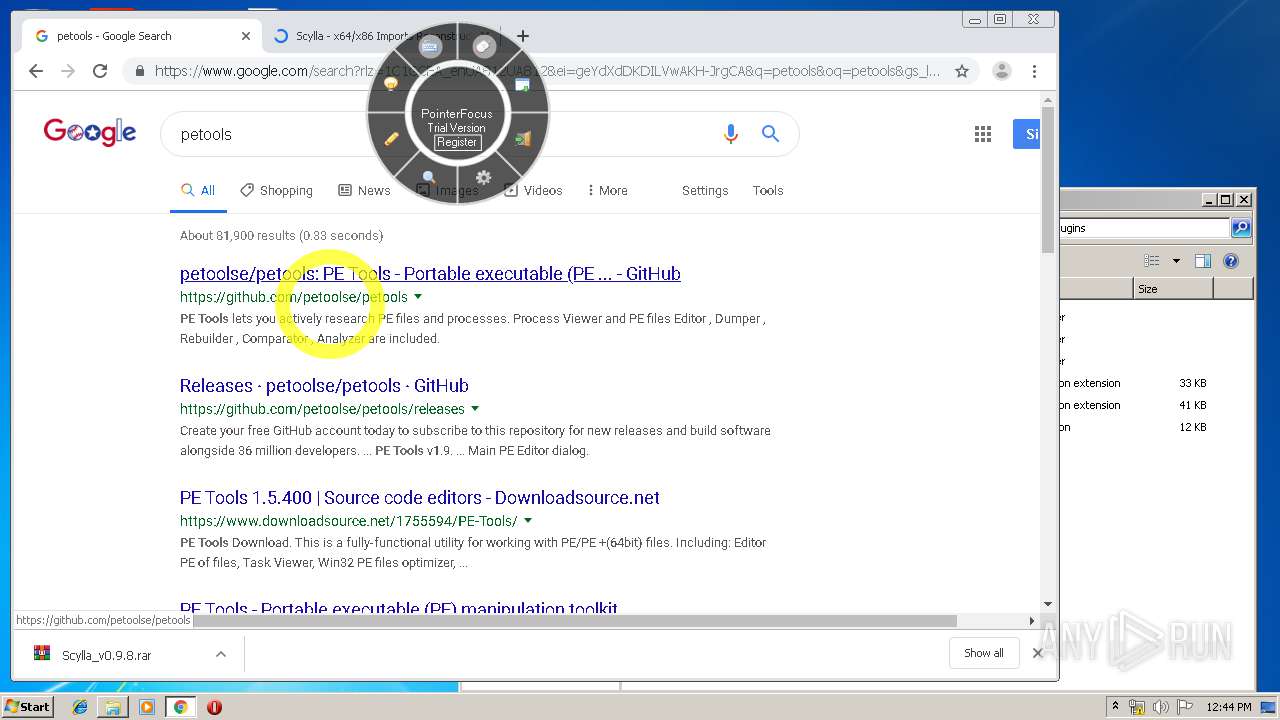
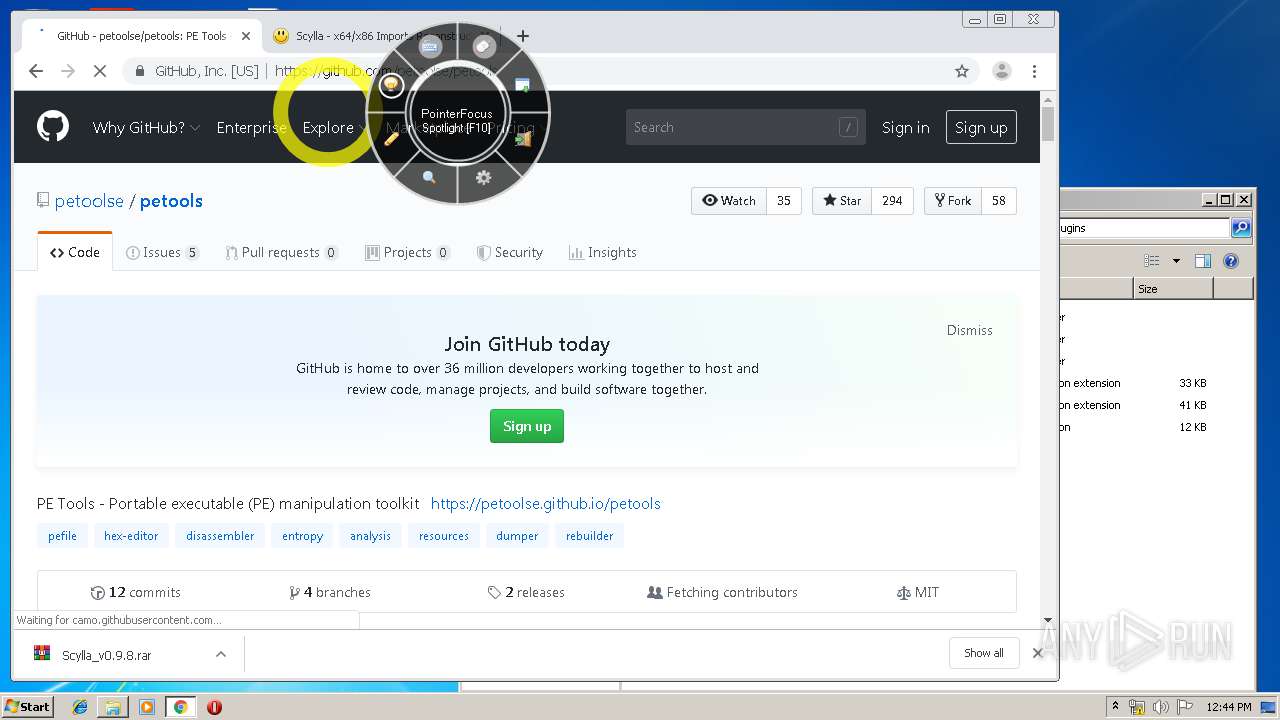
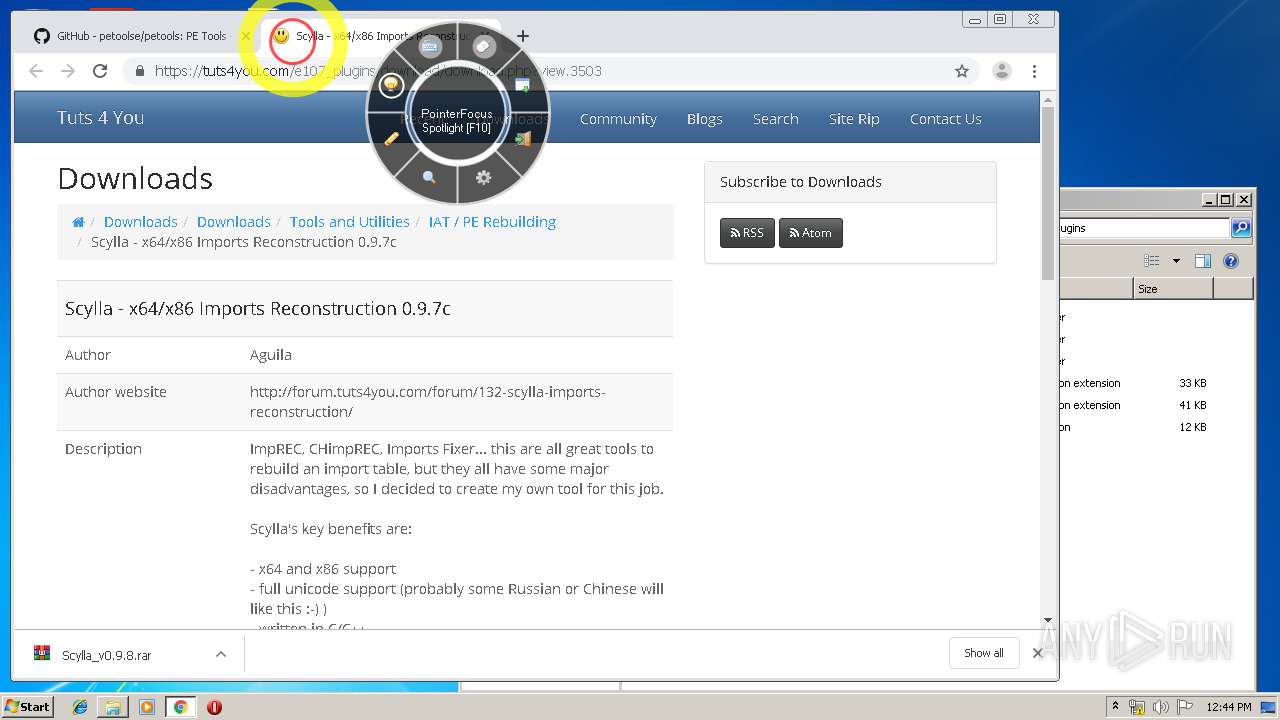
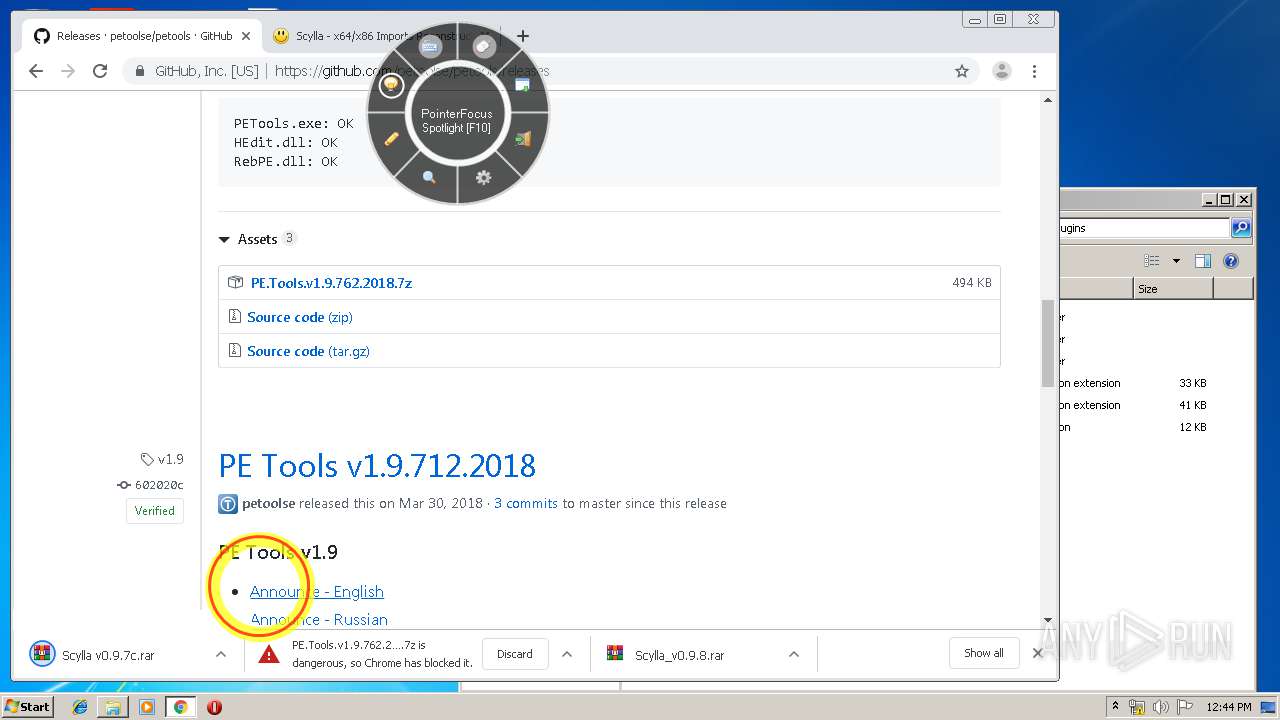
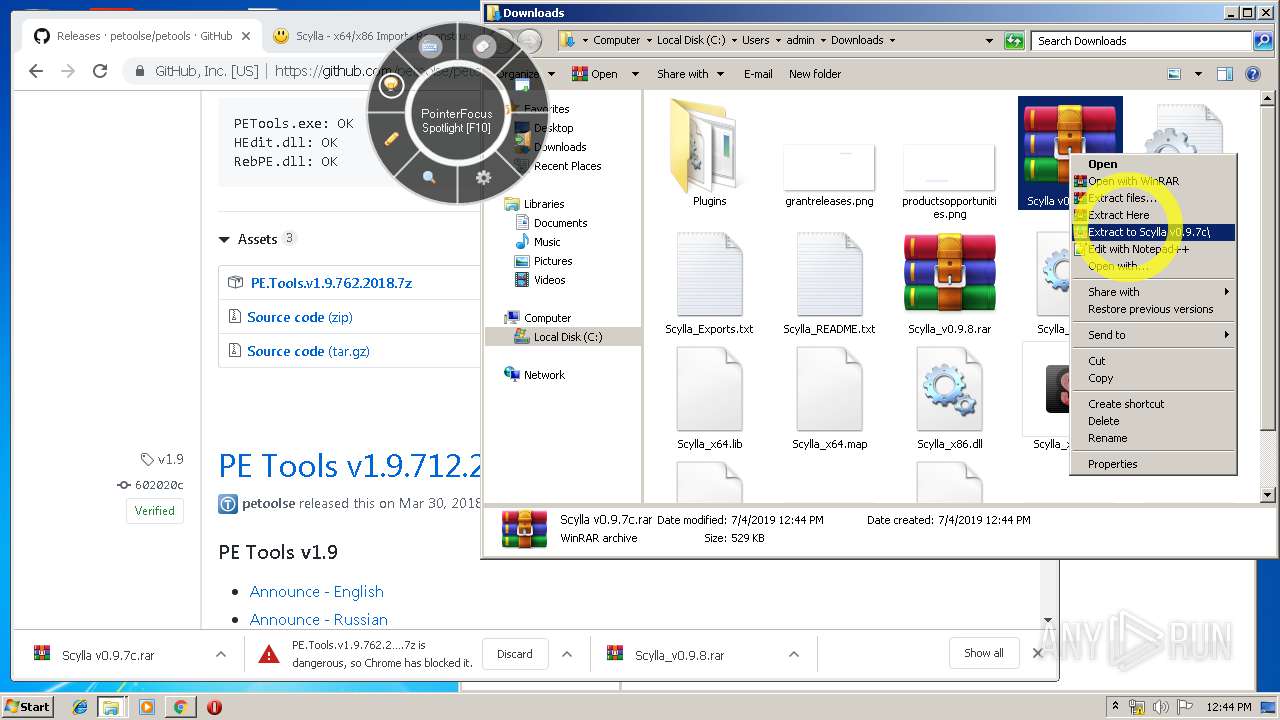
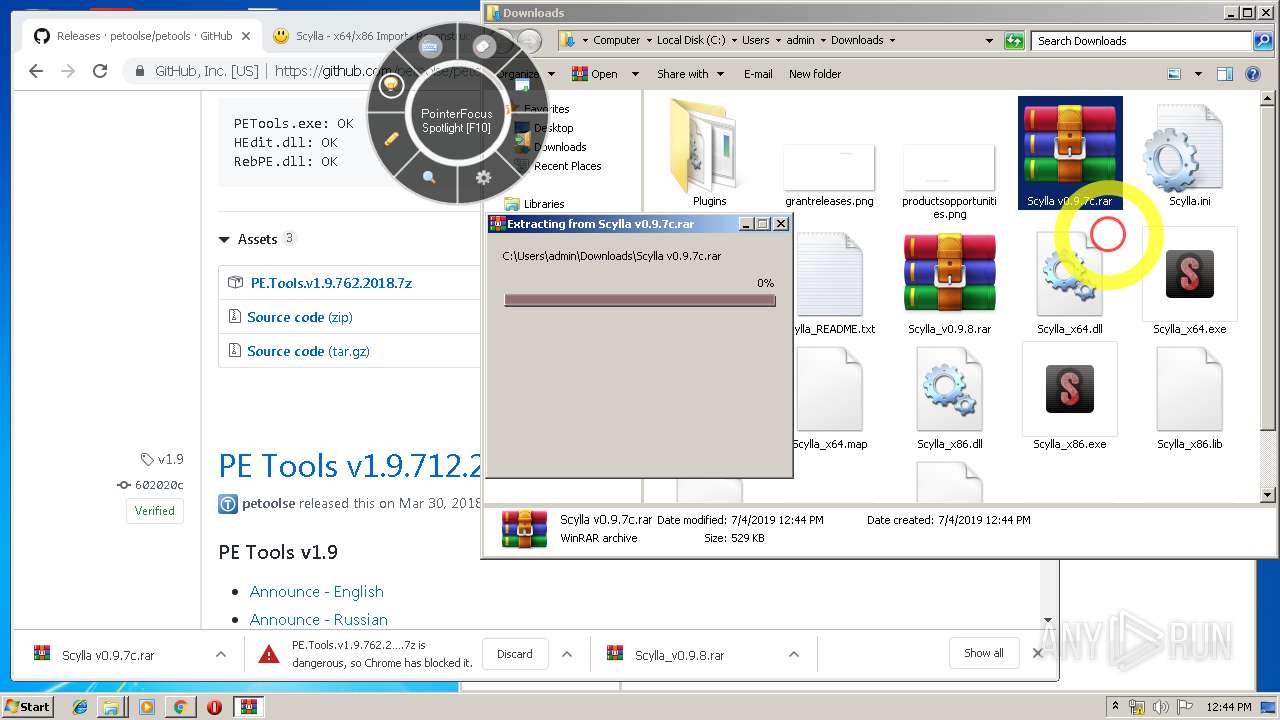
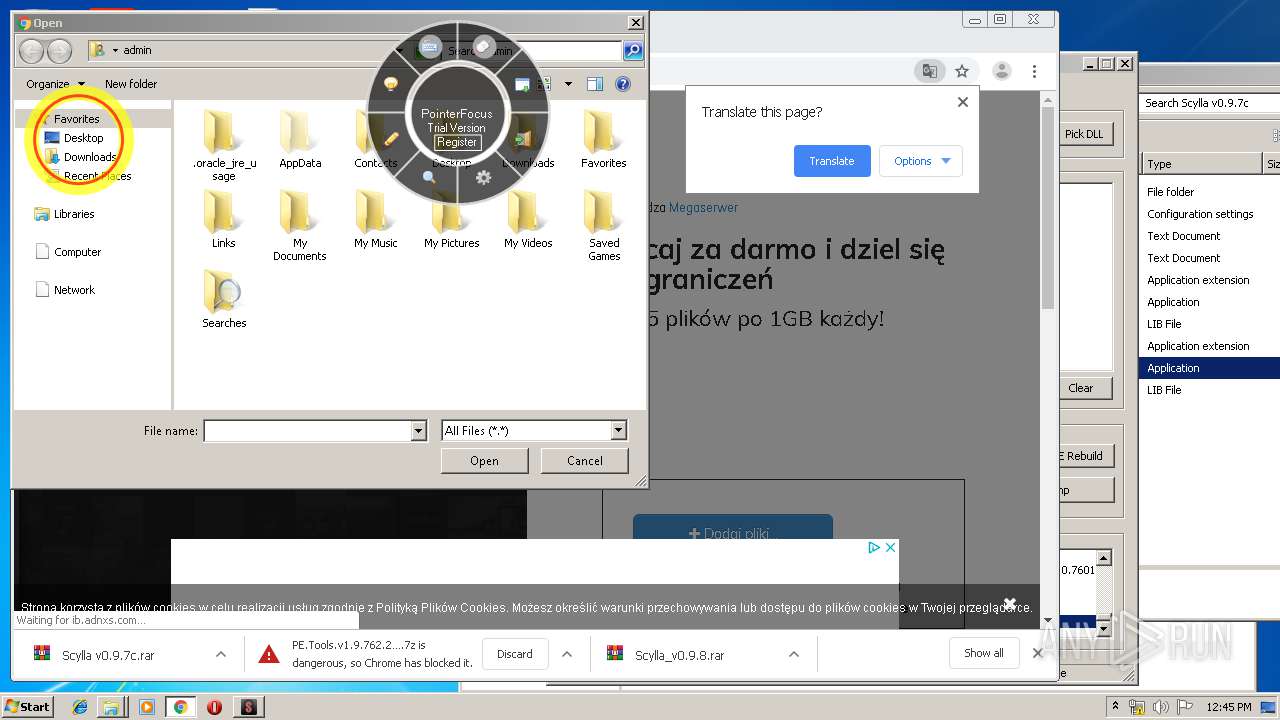
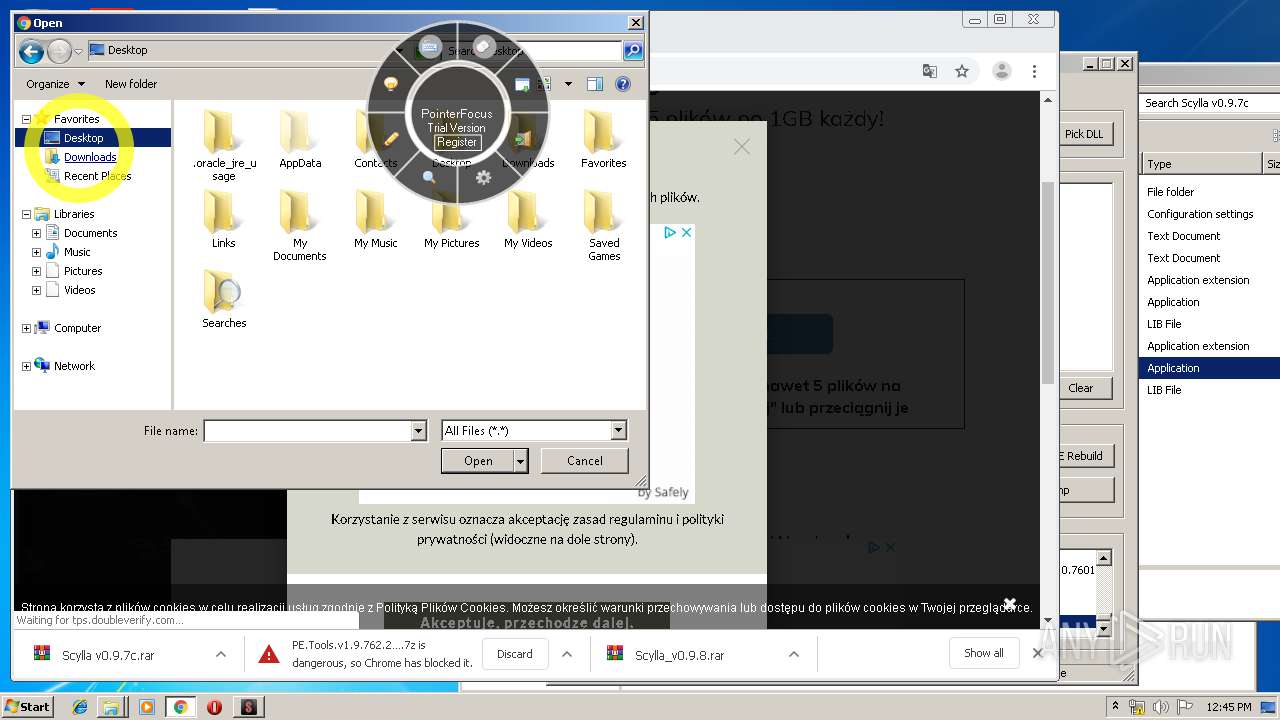
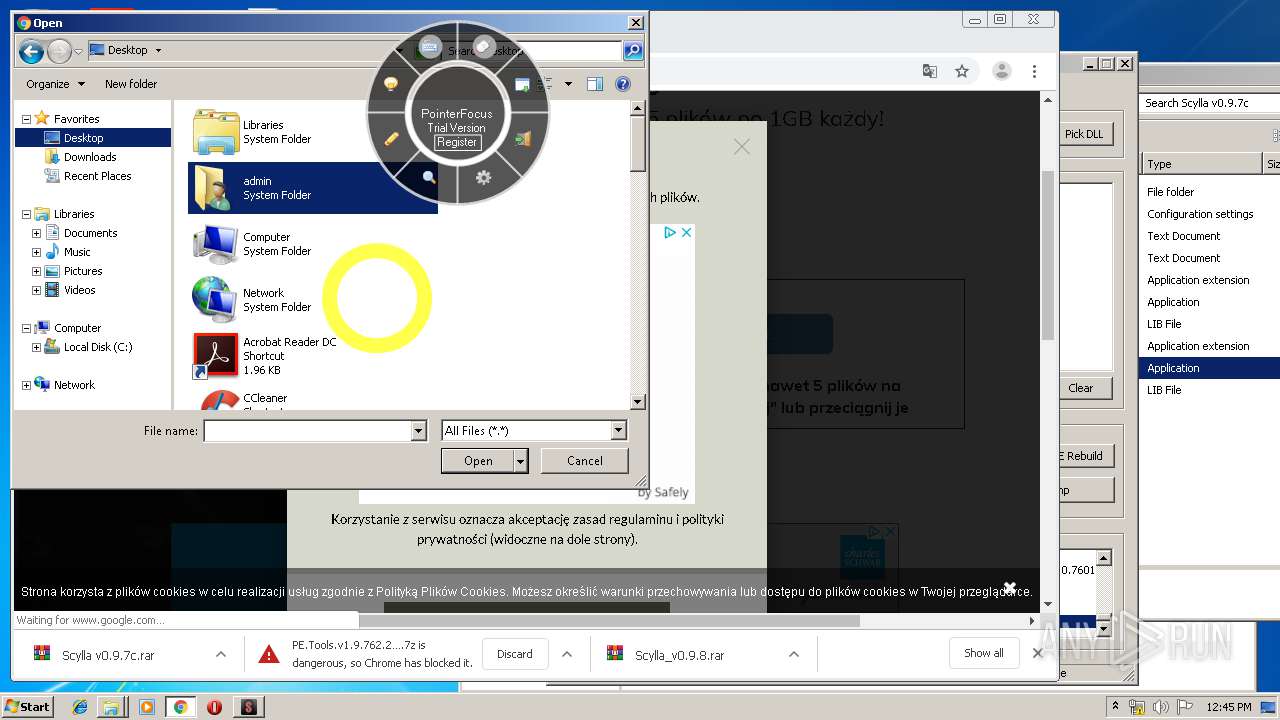
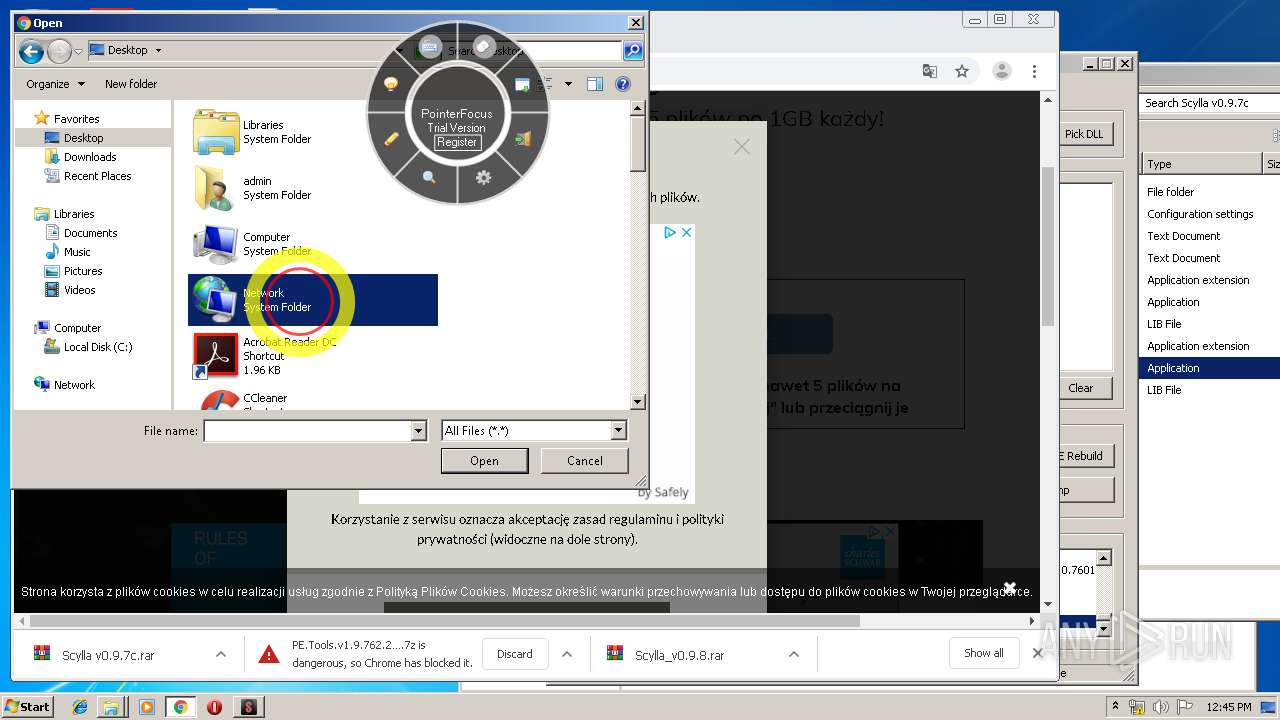
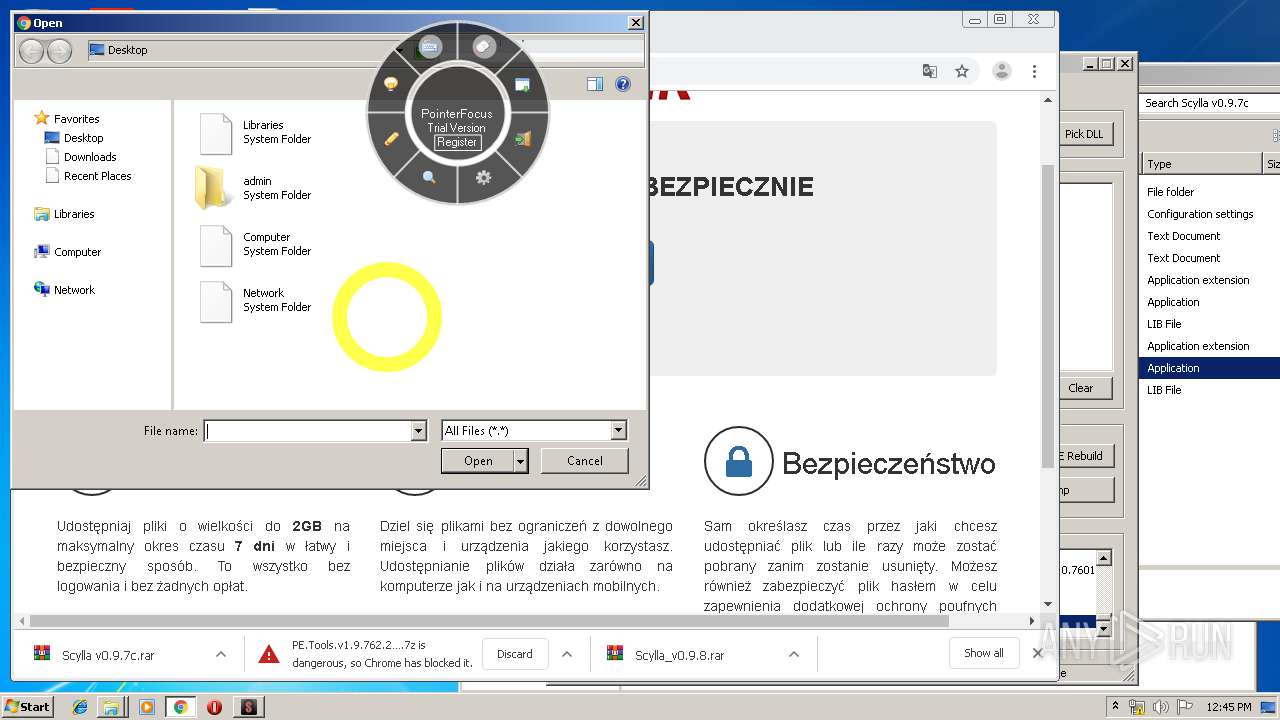
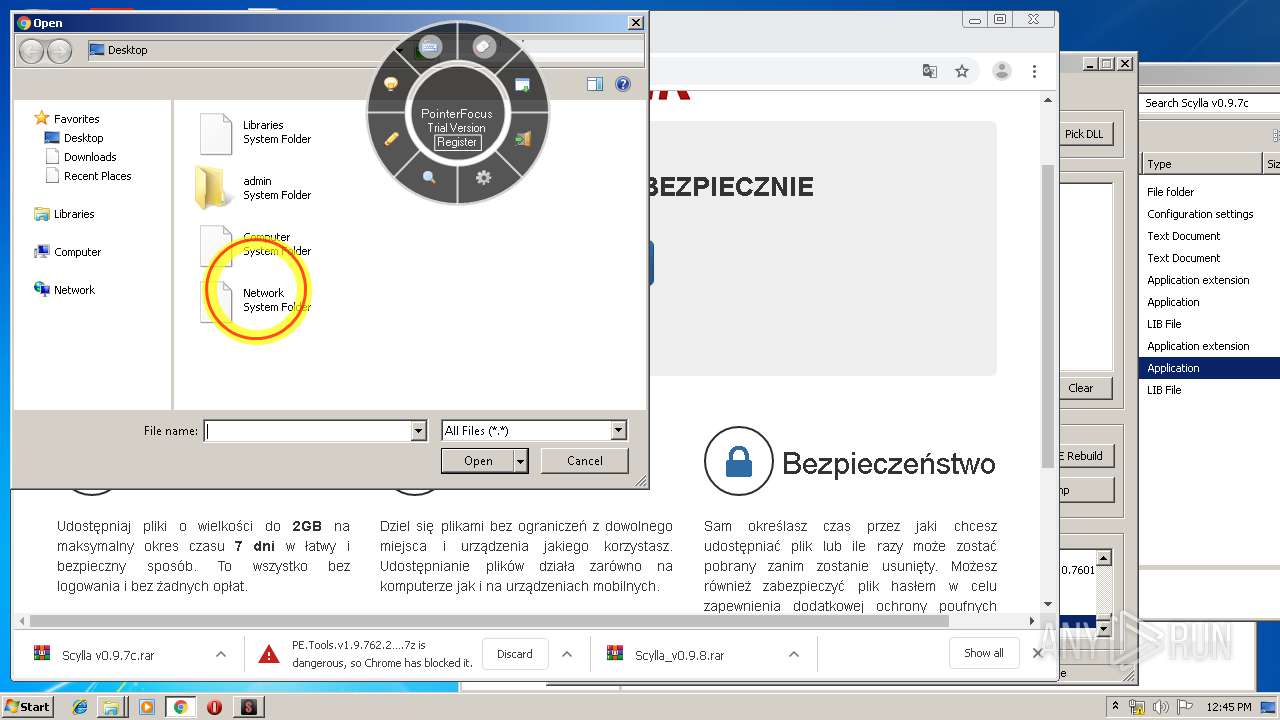
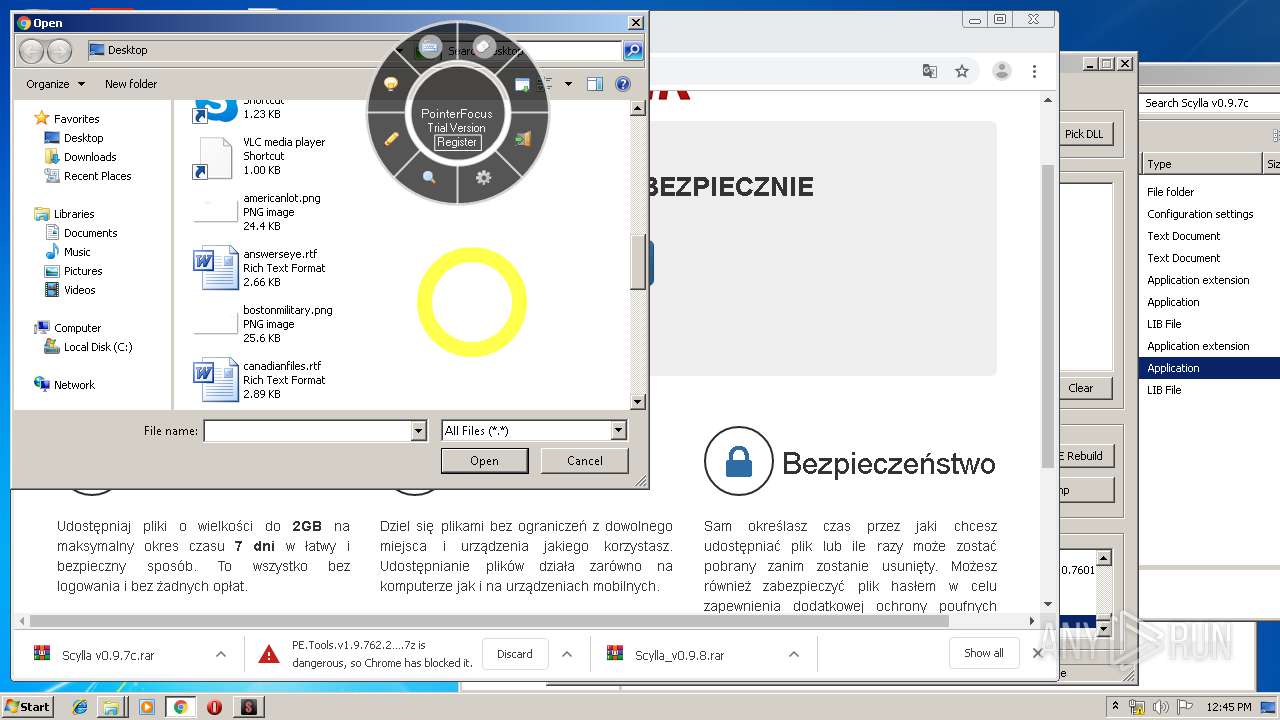
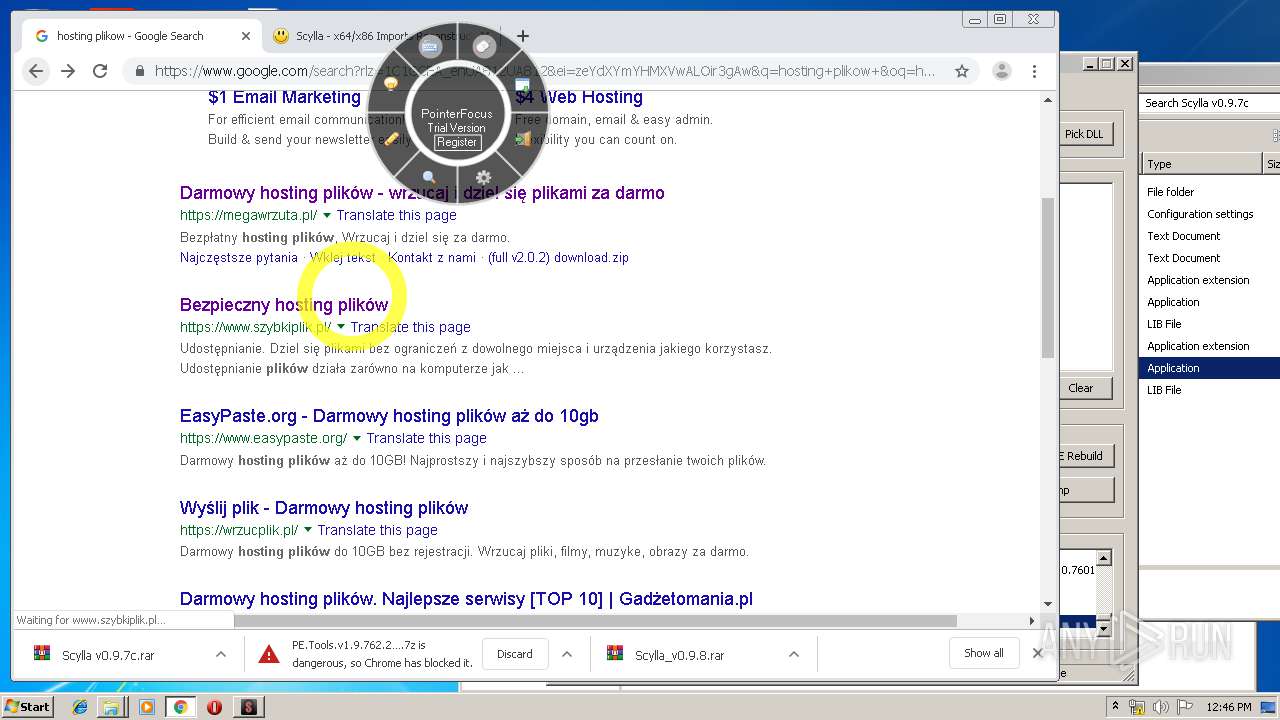
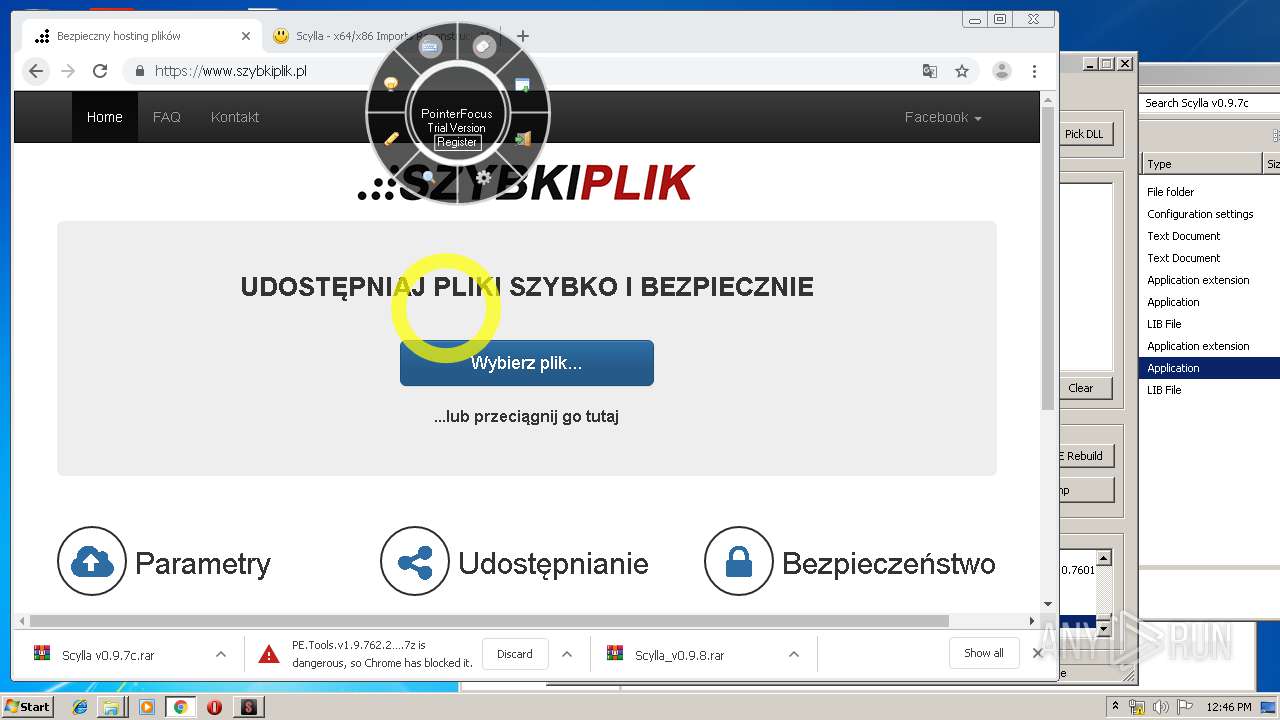
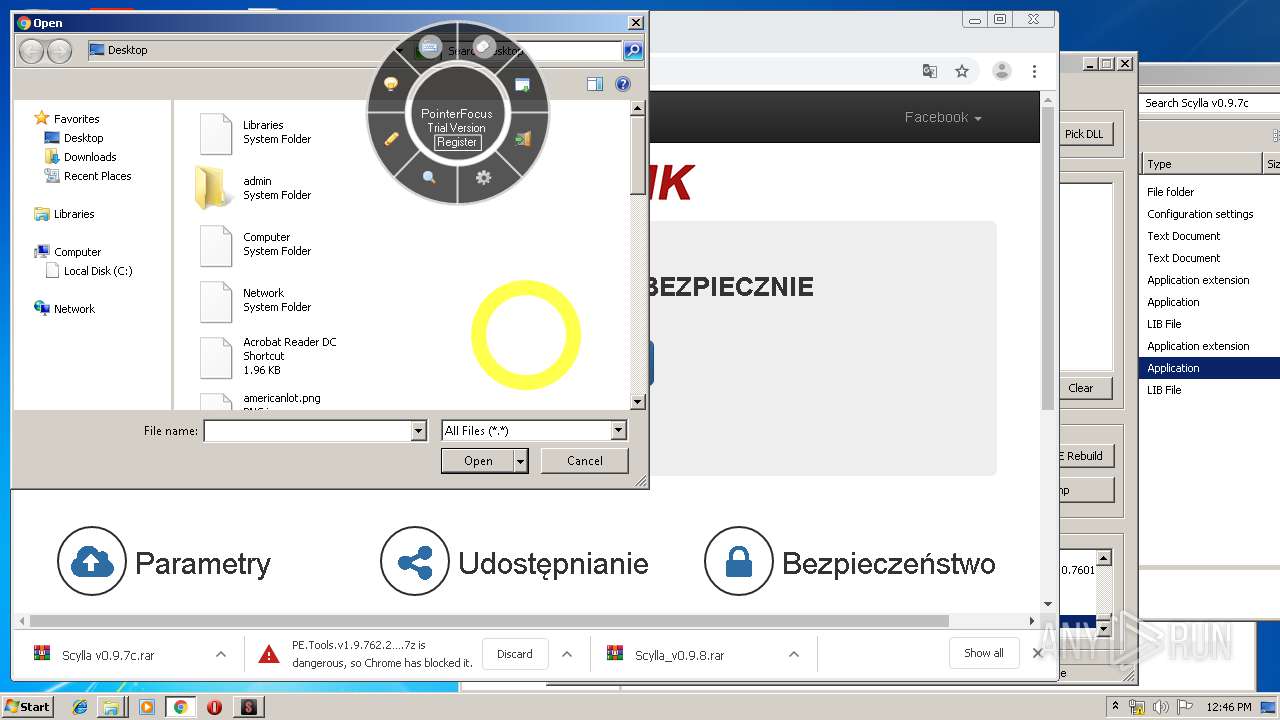
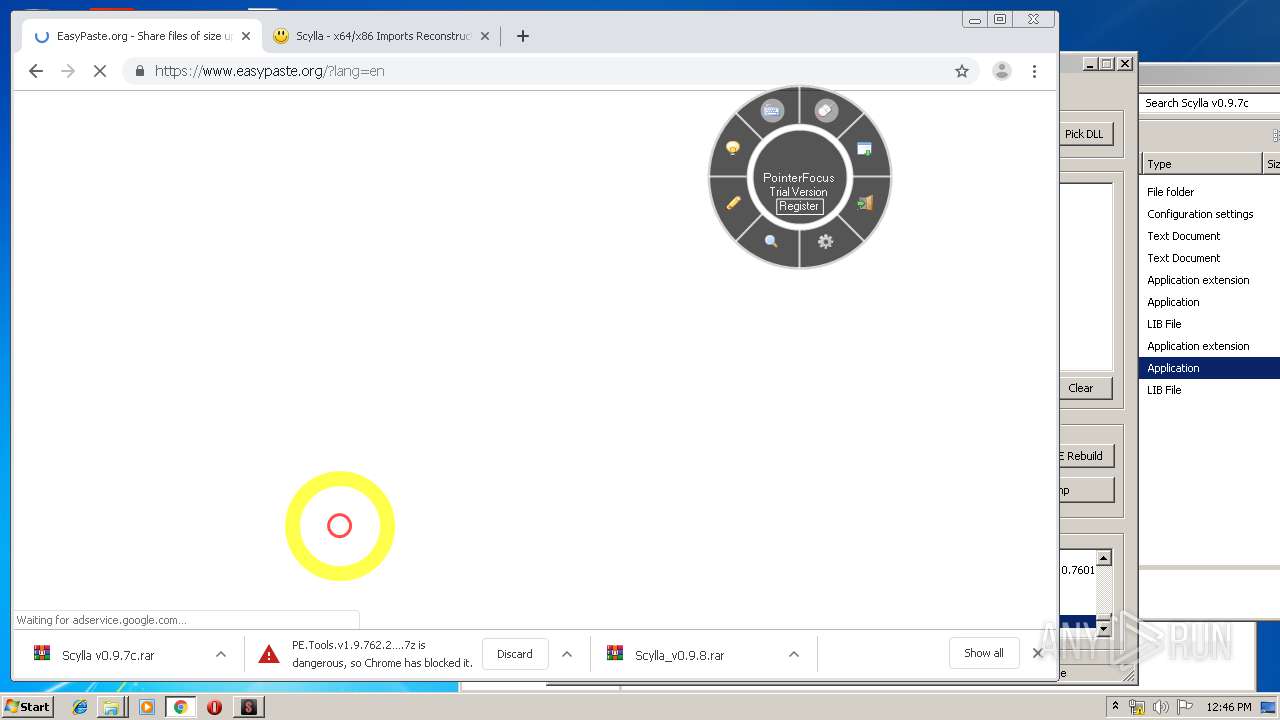
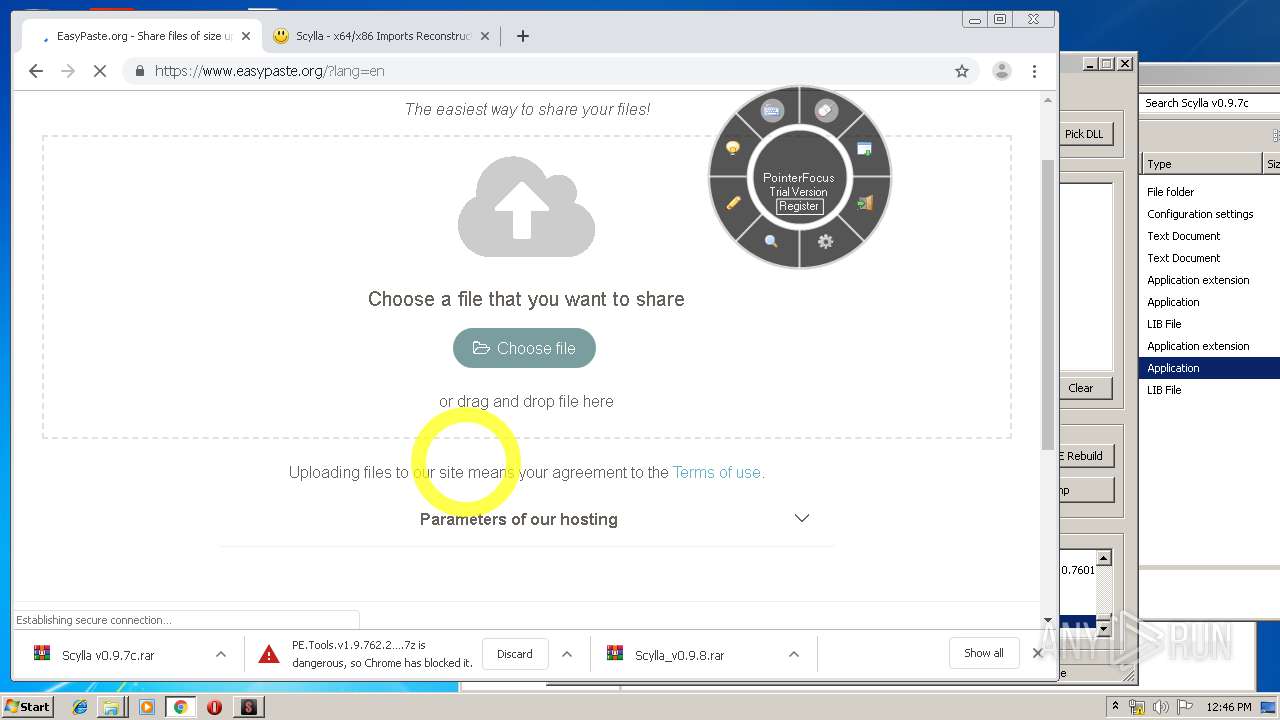
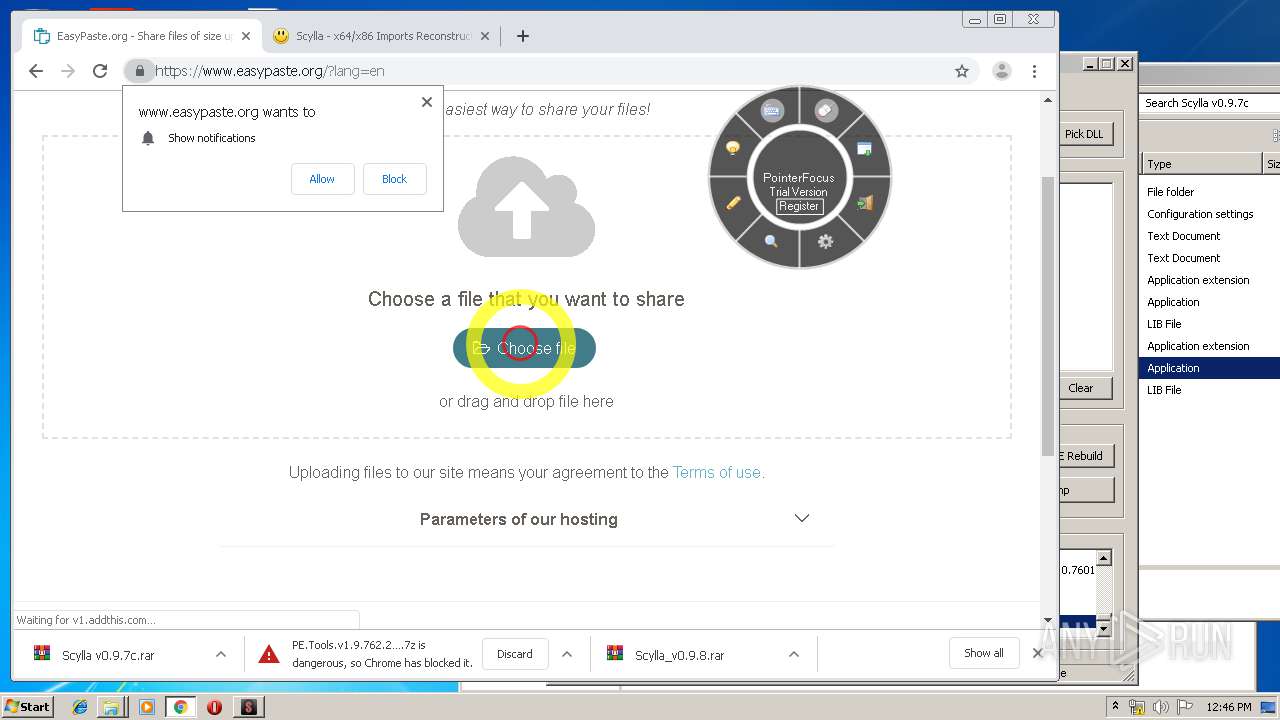
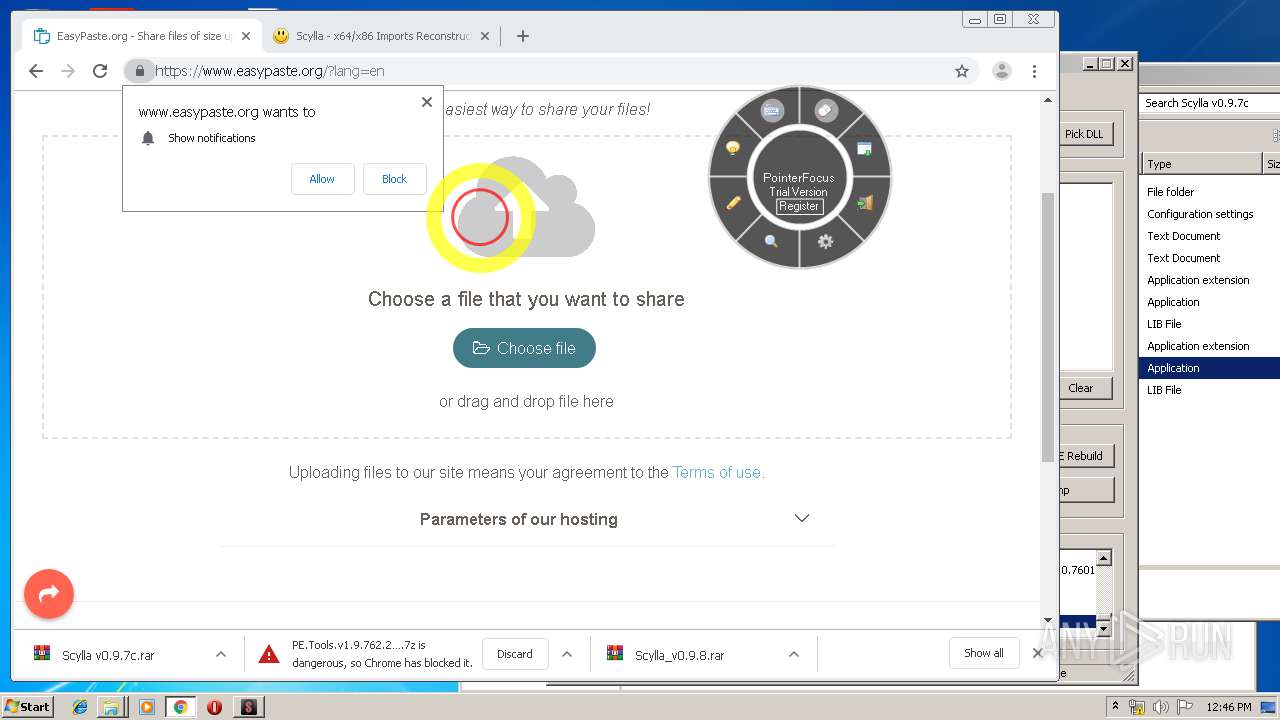
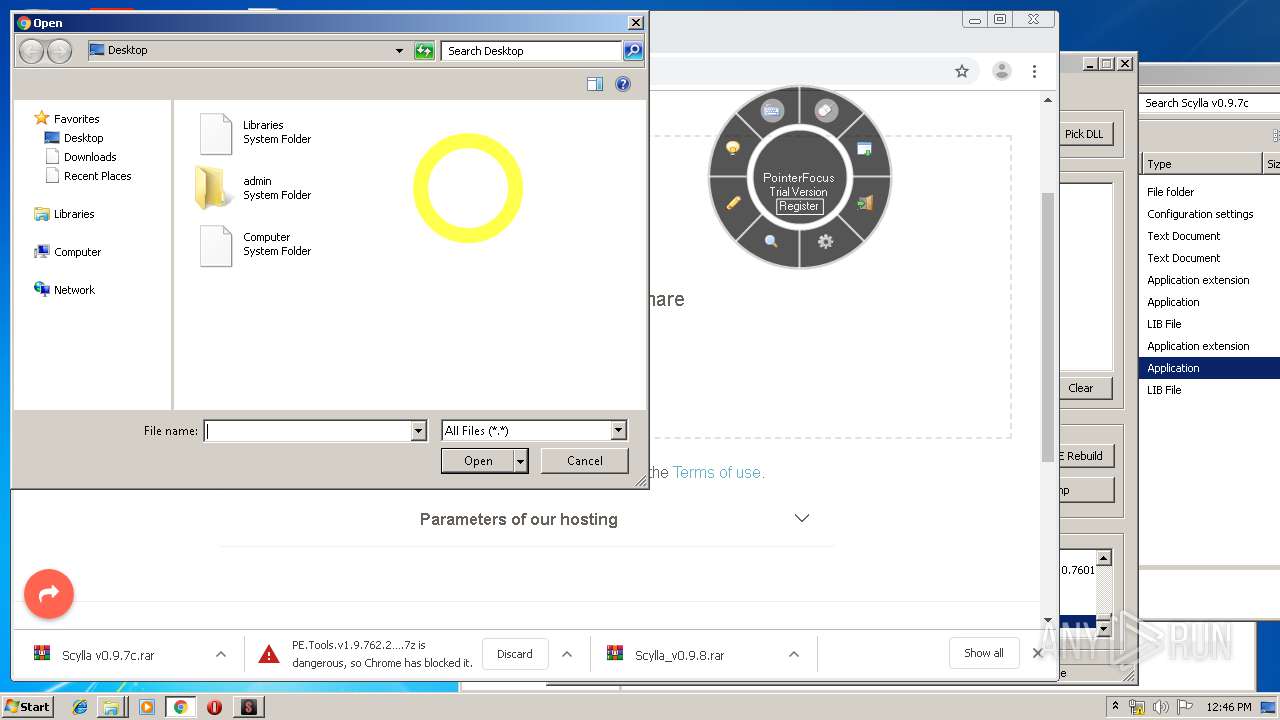
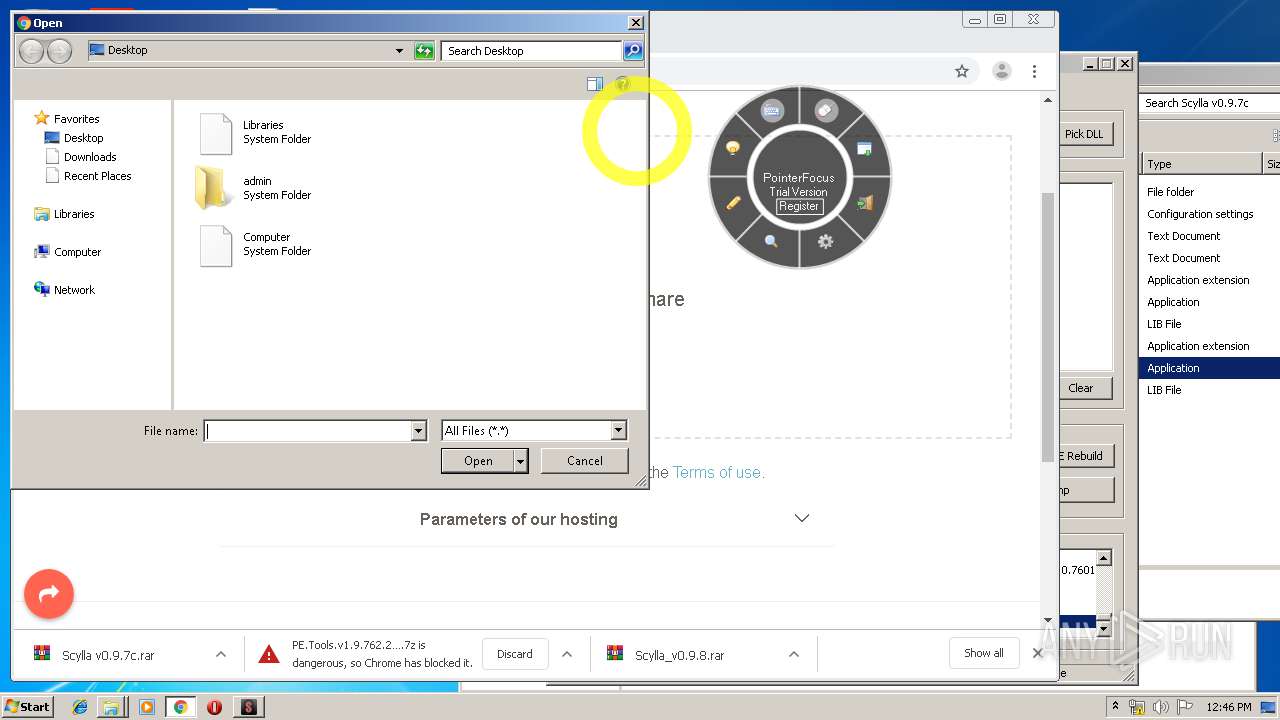
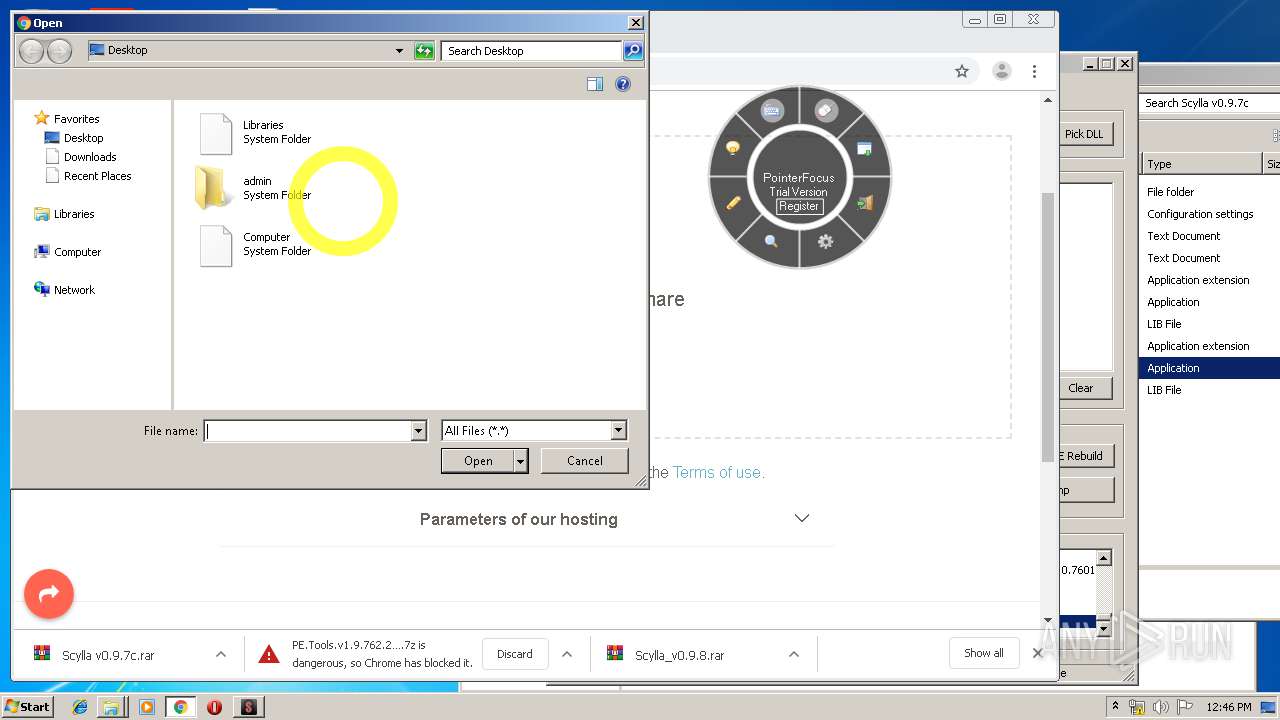
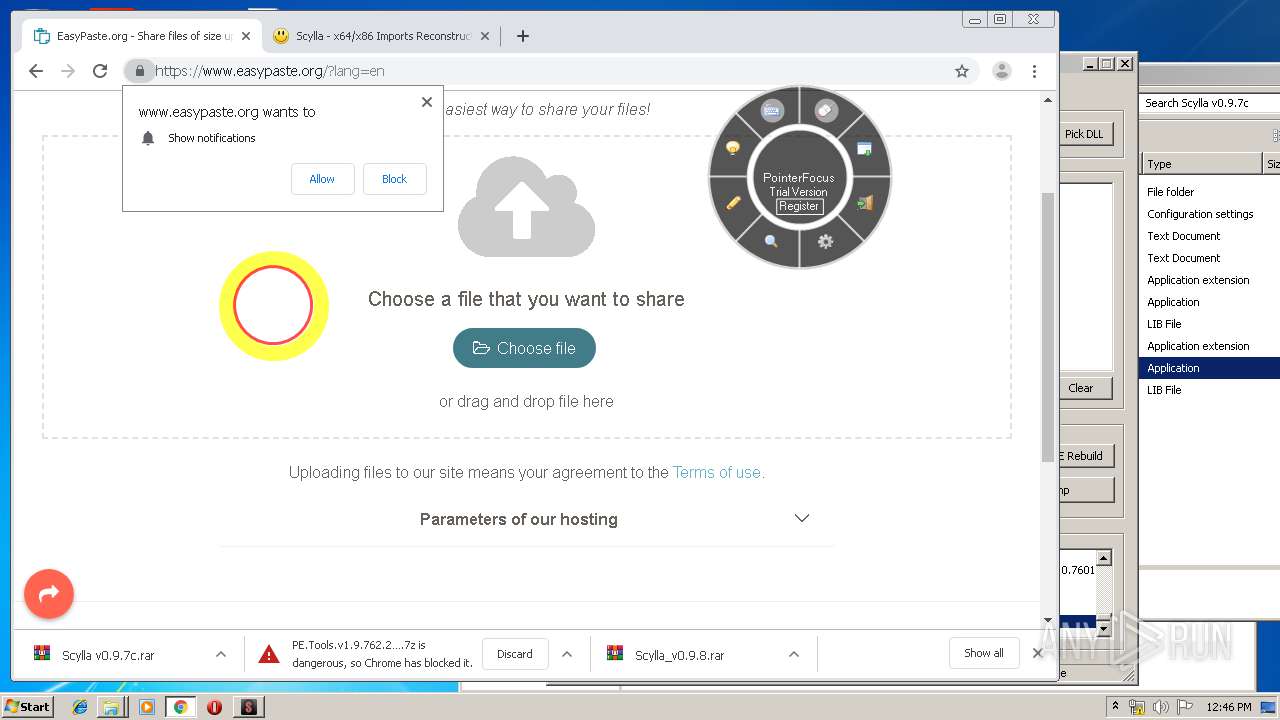
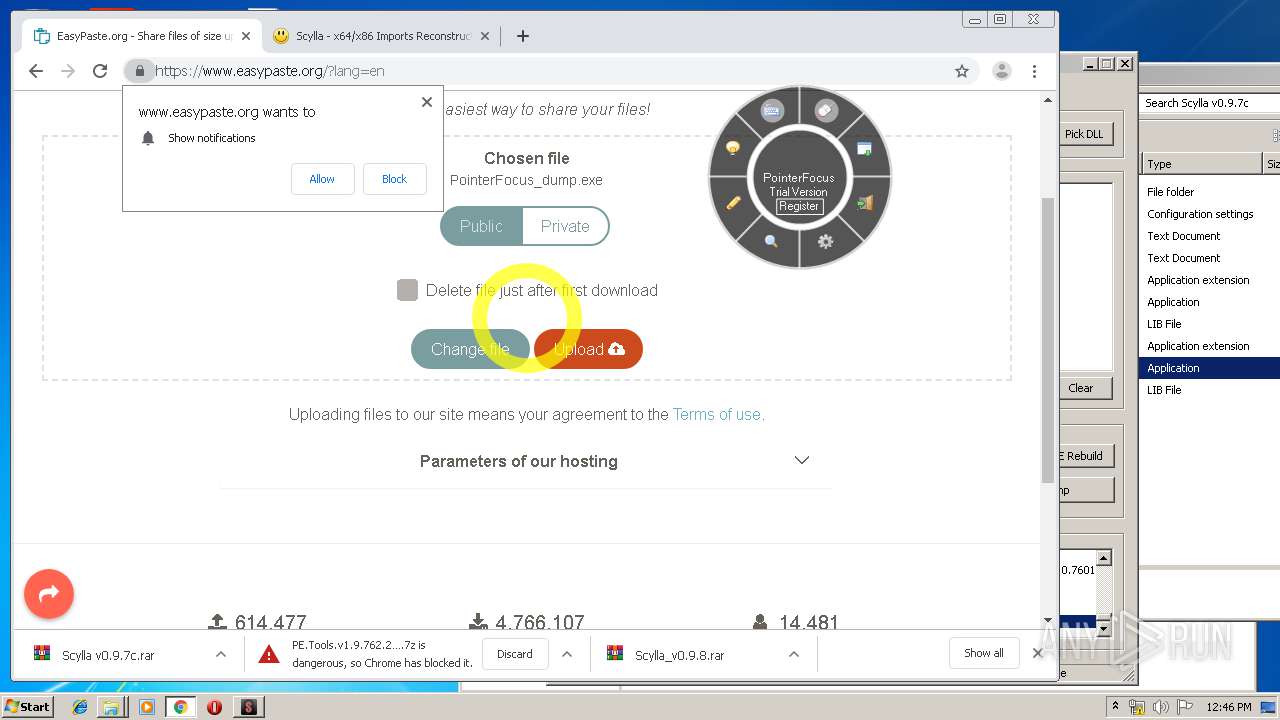
Manual execution by user
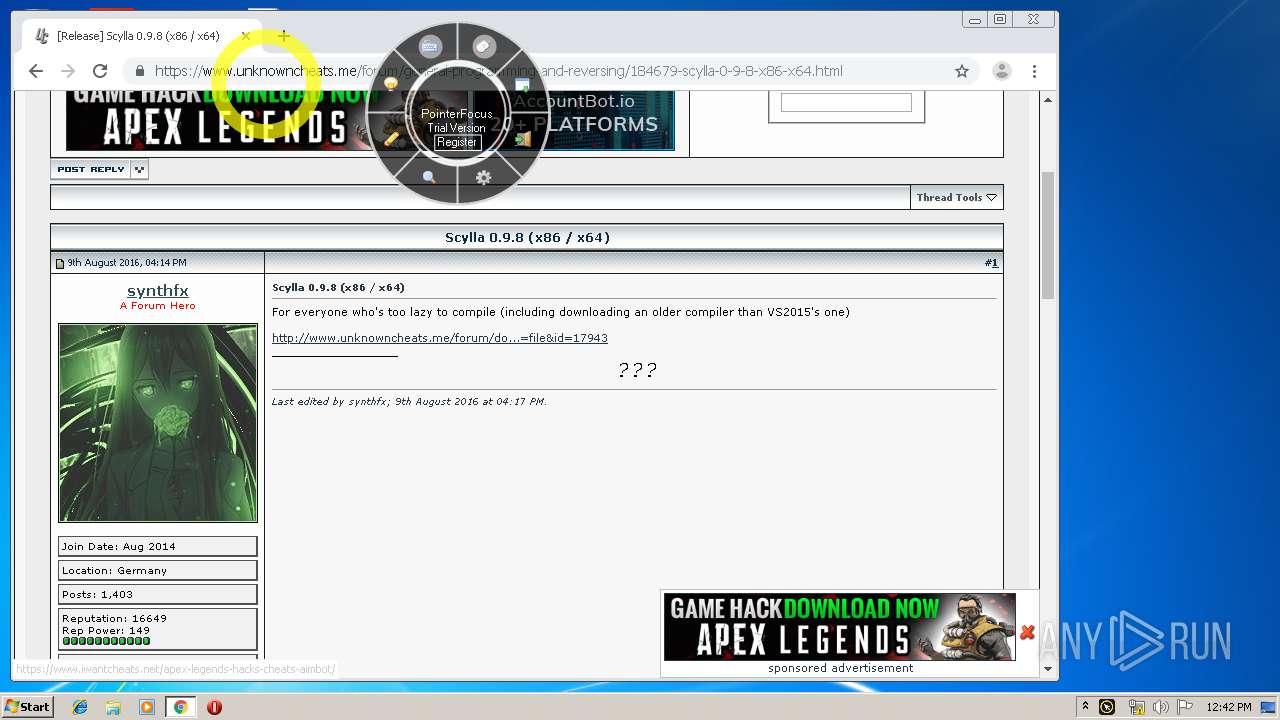
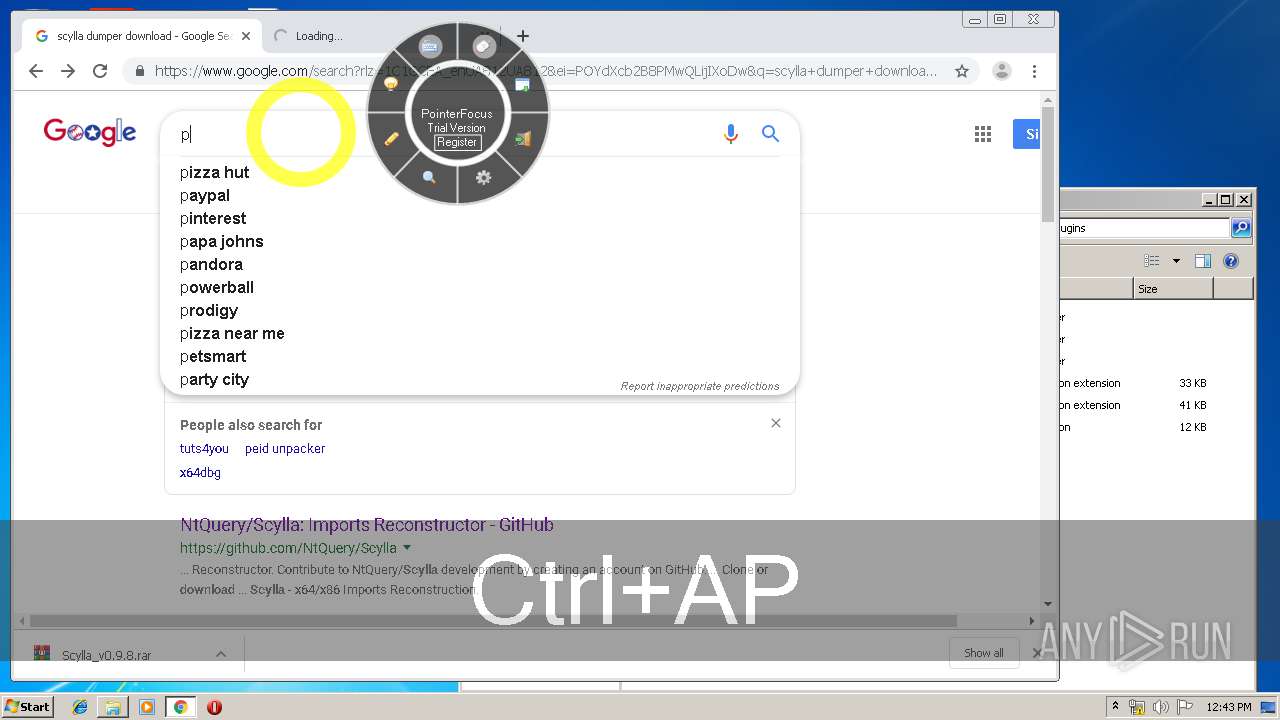
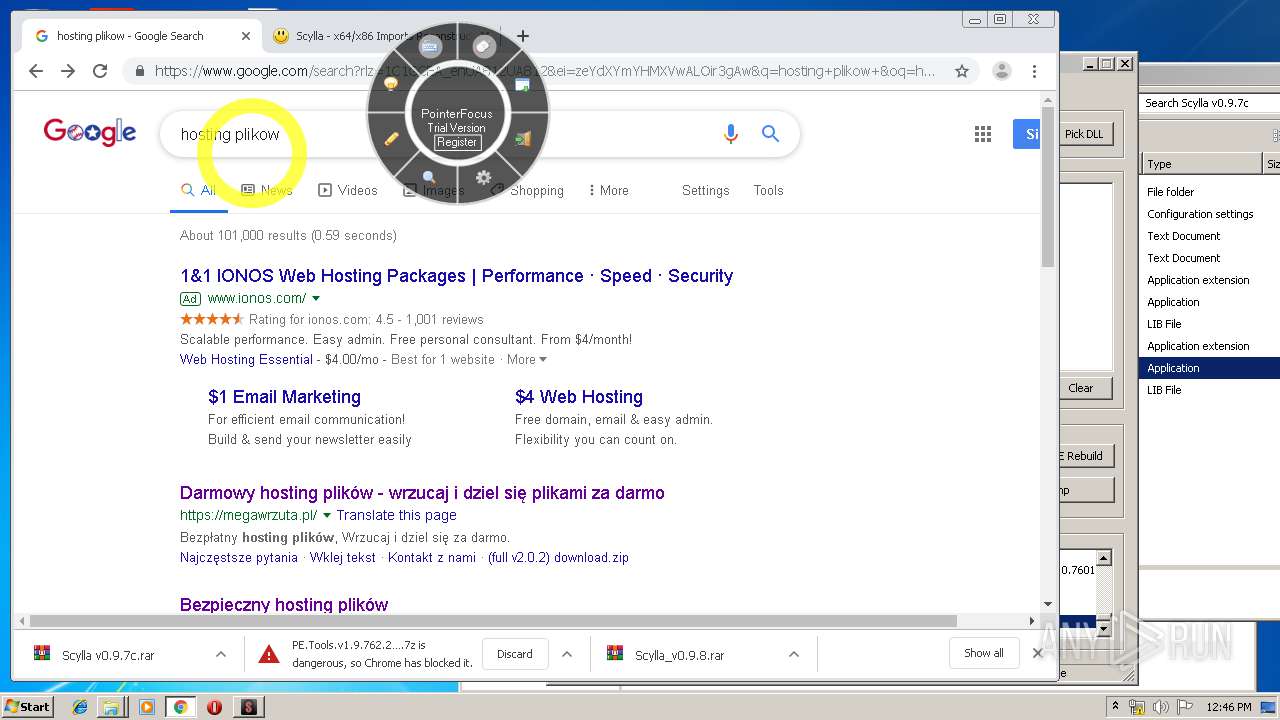
- chrome.exe (PID: 3952)
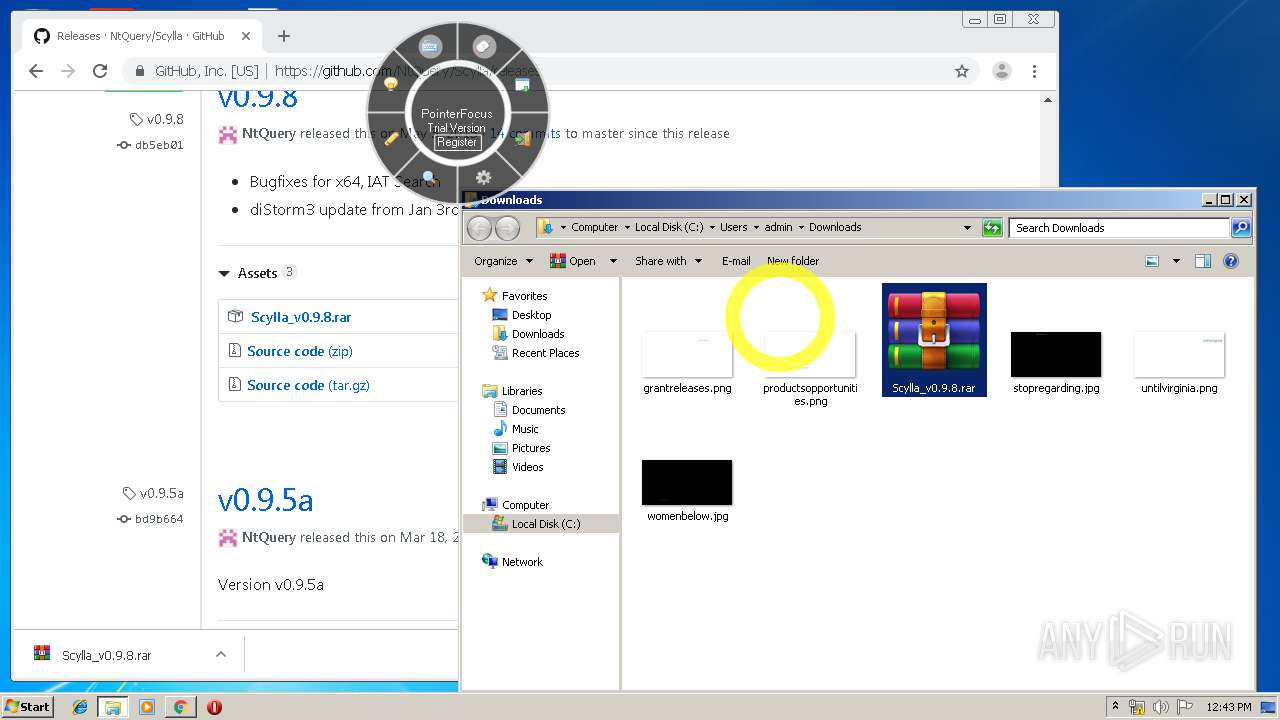
- WinRAR.exe (PID: 3648)
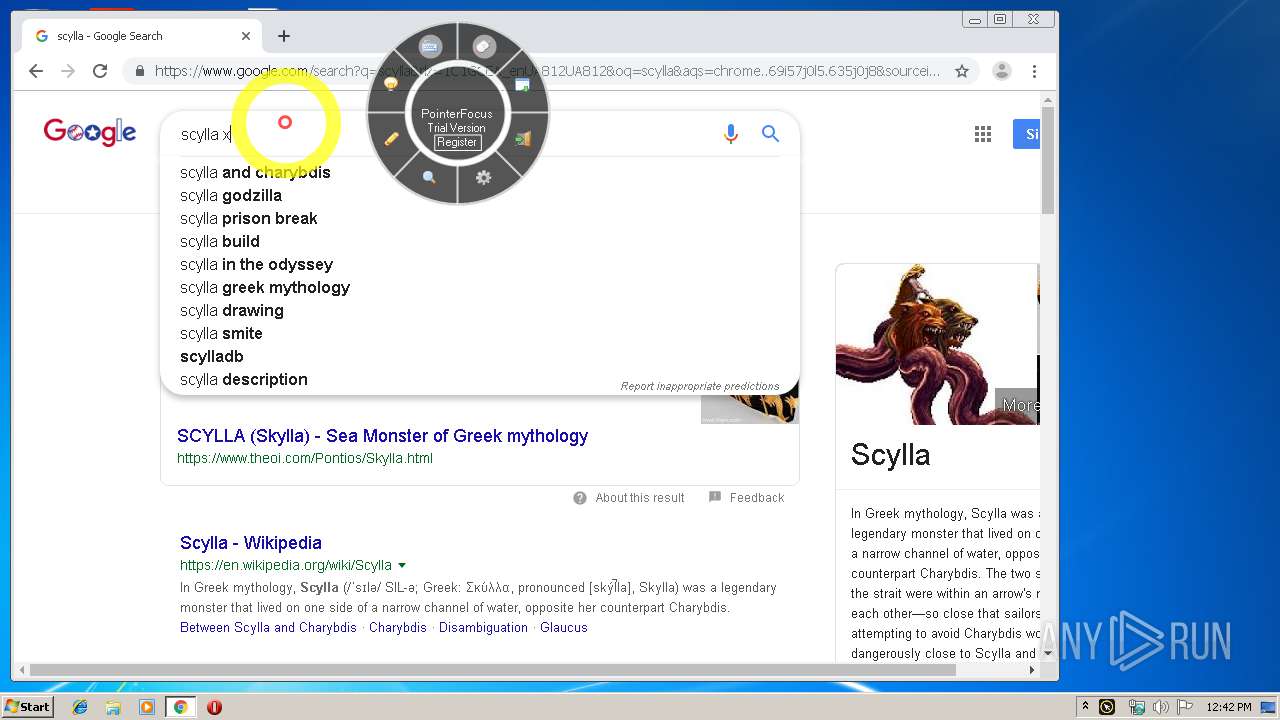
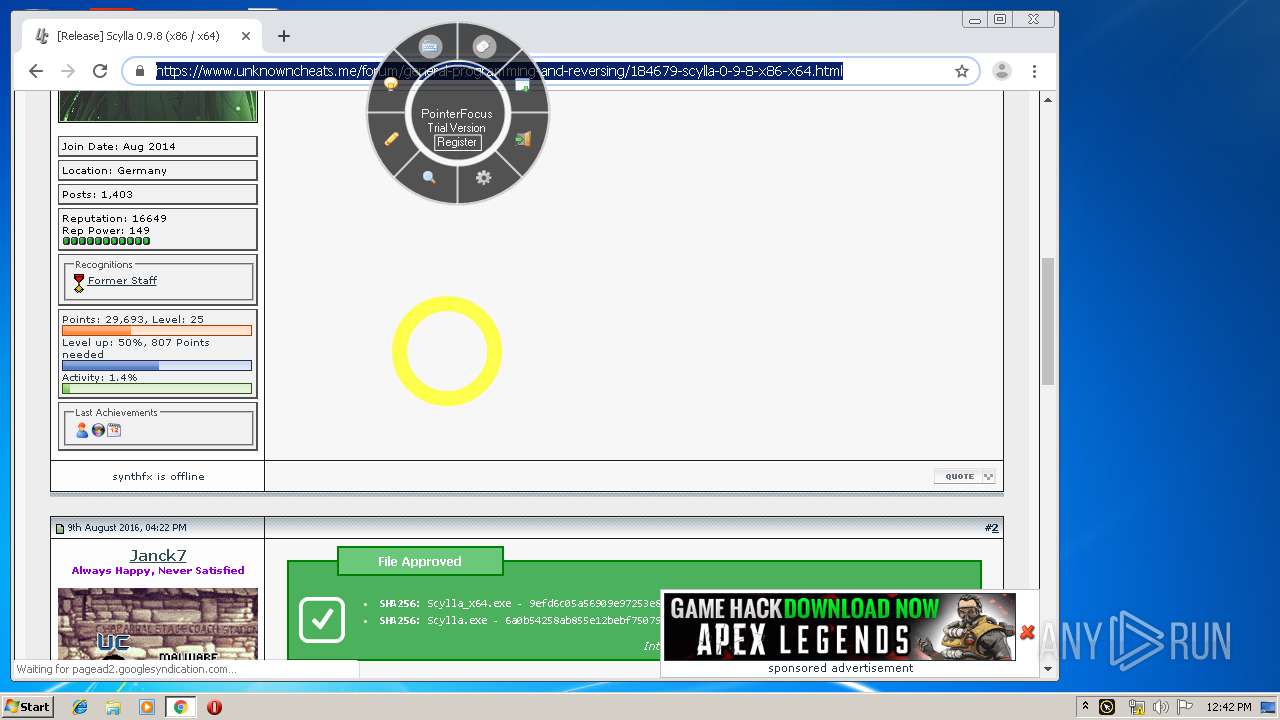
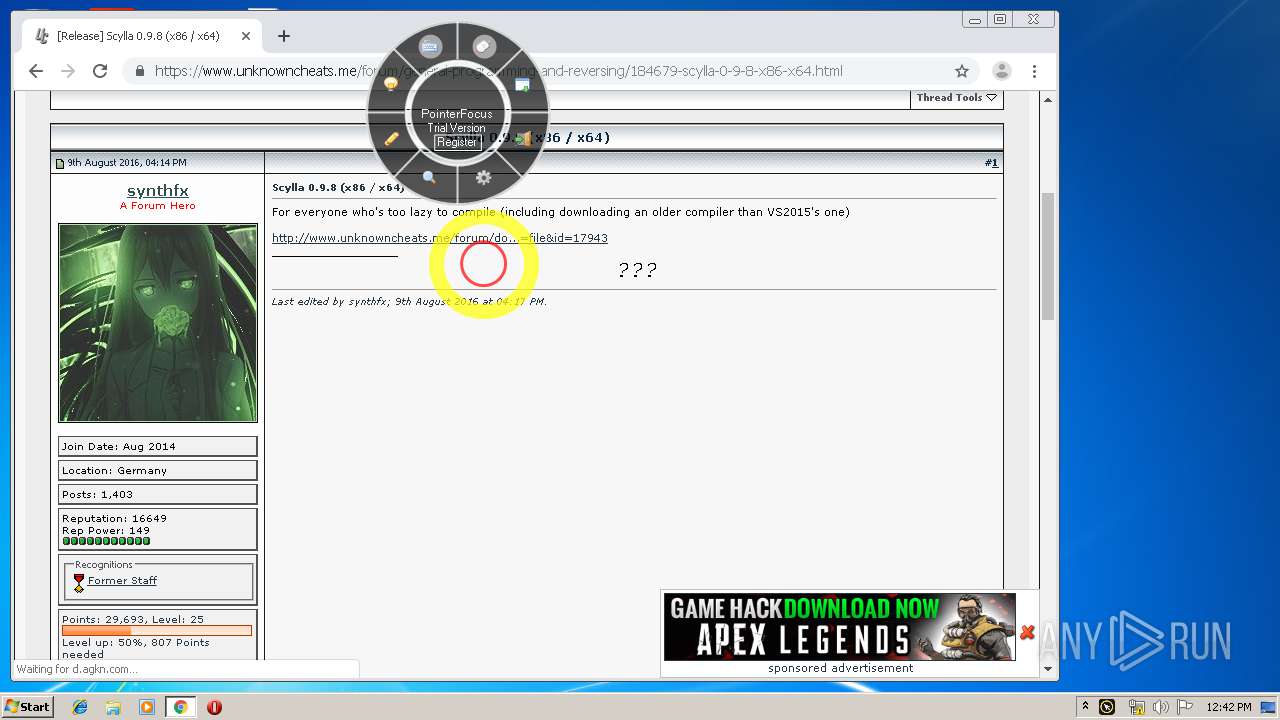
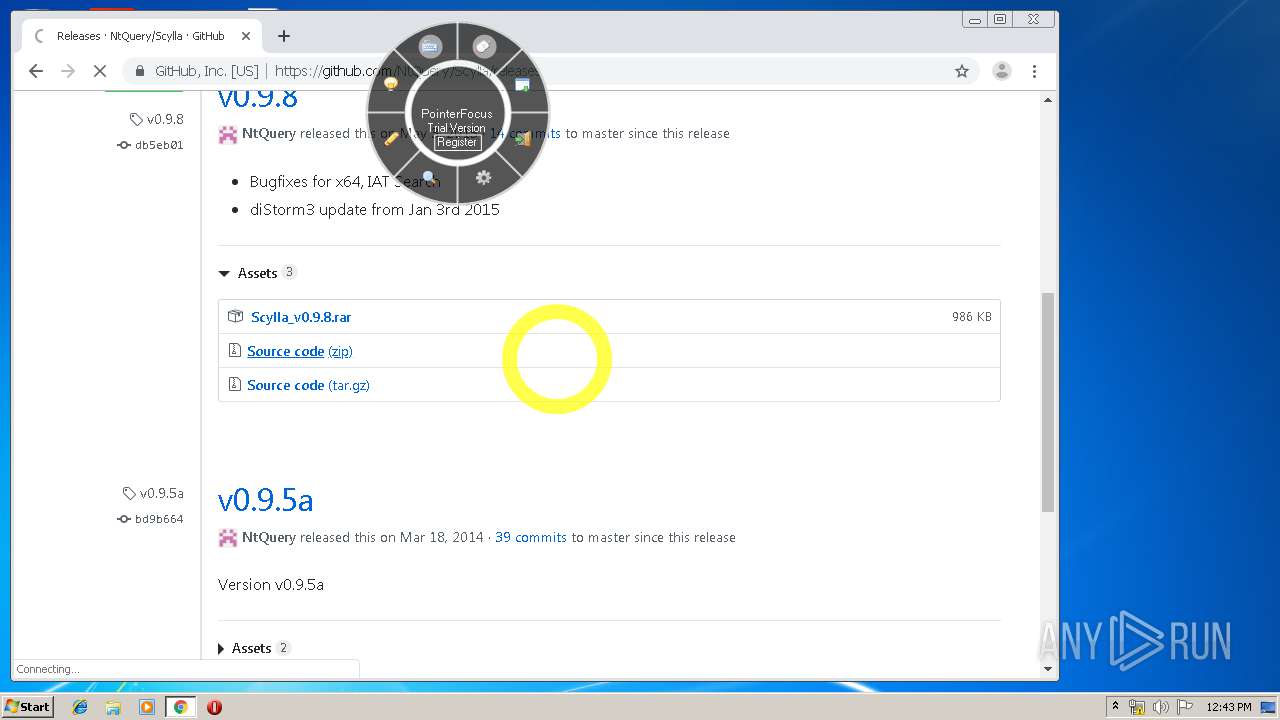
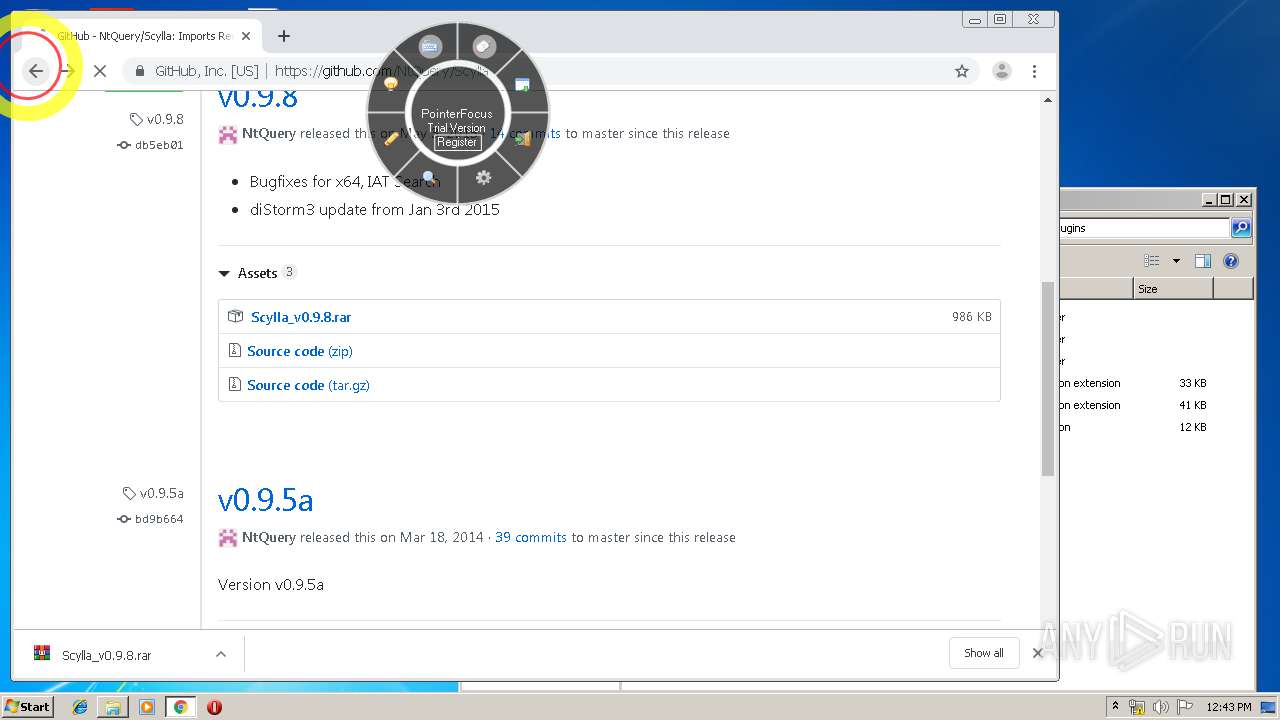
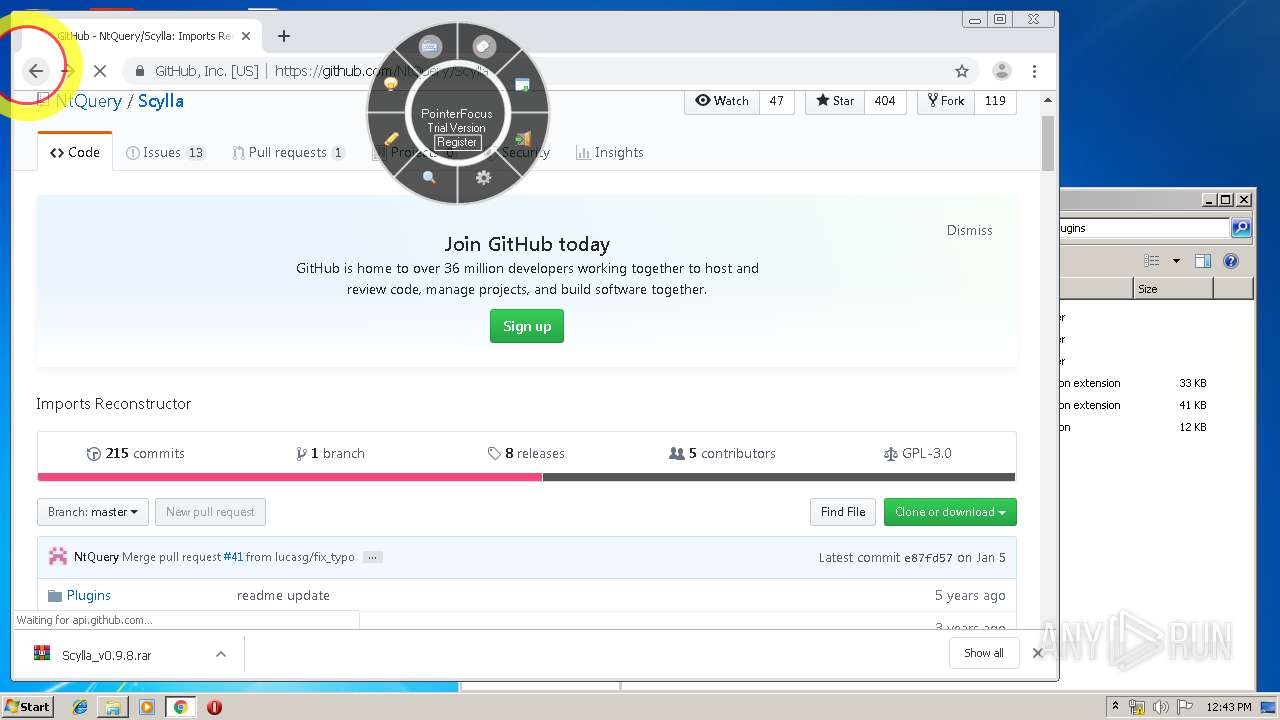
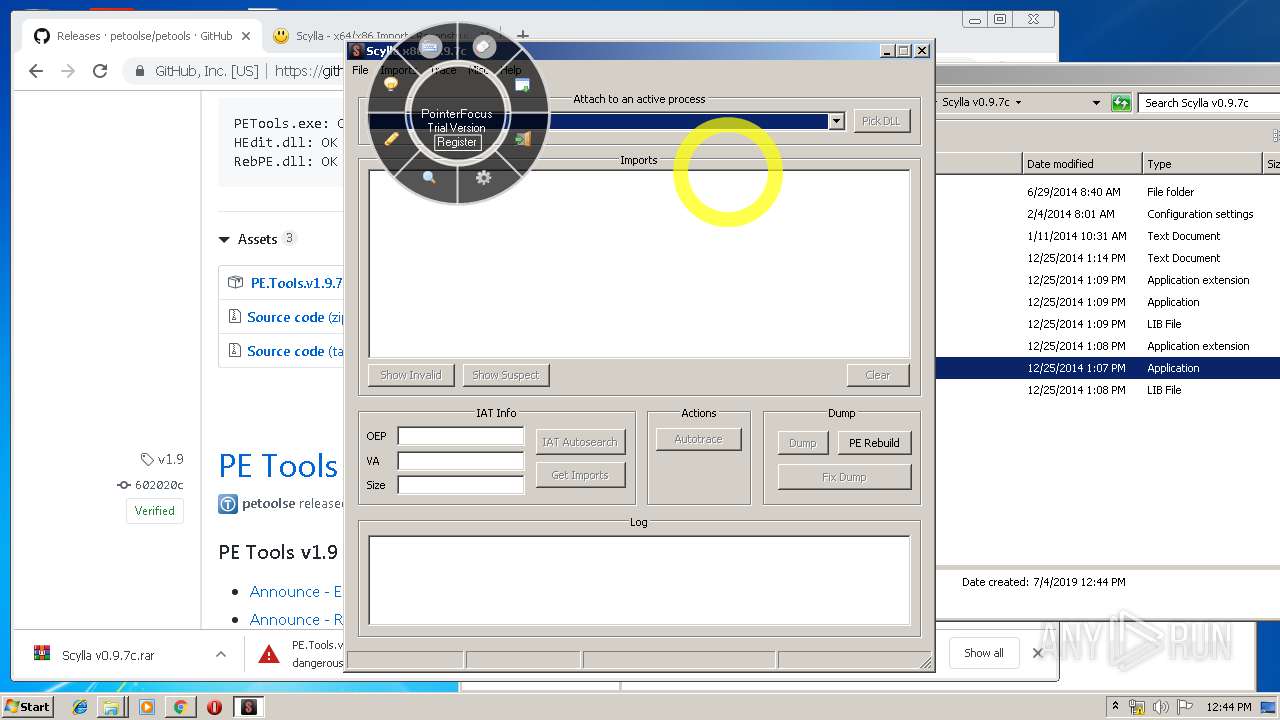
- Scylla_x86.exe (PID: 3840)
- WinRAR.exe (PID: 2916)
Reads Internet Cache Settings
- chrome.exe (PID: 3952)
Application launched itself
- chrome.exe (PID: 3952)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3648)
- WinRAR.exe (PID: 2916)
Dropped object may contain TOR URL's
- chrome.exe (PID: 3952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:06:10 16:33:52+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 87040 |
| InitializedDataSize: | 60416 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x163c4 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.4.0.0 |
| ProductVersionNumber: | 2.4.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
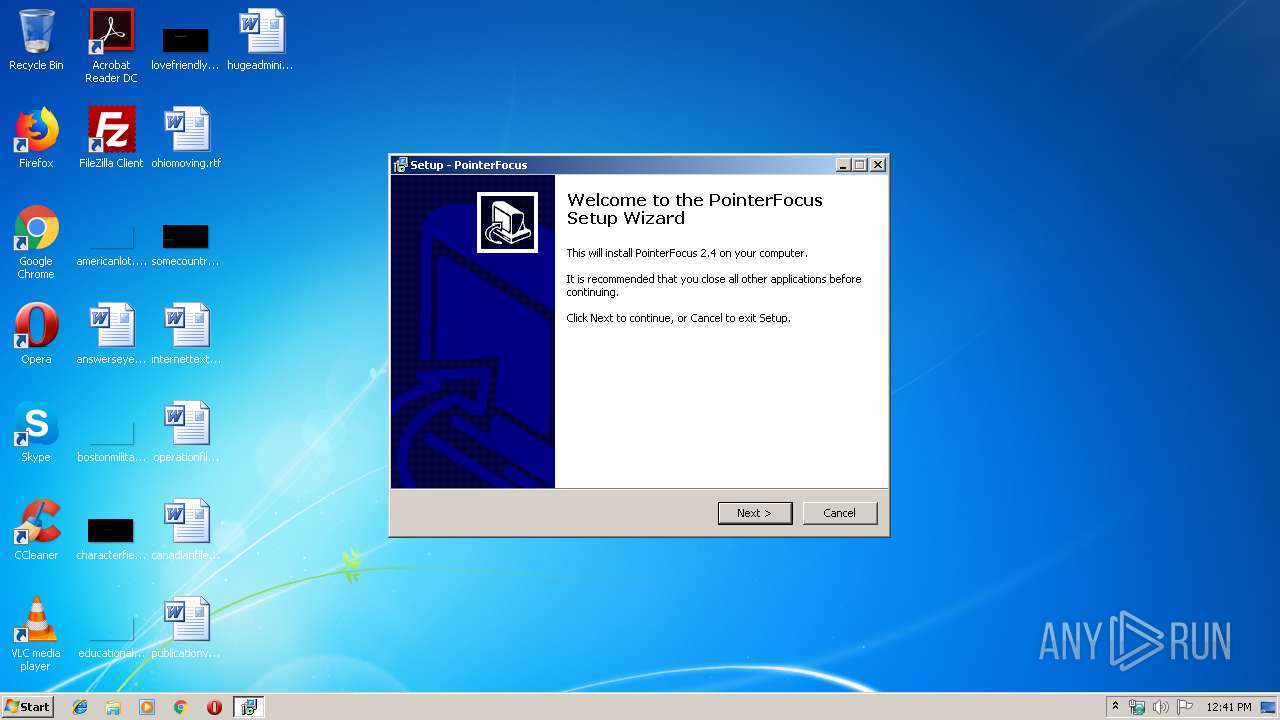
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | ETUS |
| FileDescription: | PointerFocus Setup |
| FileVersion: | 2.4 |
| LegalCopyright: | Copyright ETUS 2018 |
| ProductName: | PointerFocus |
| ProductVersion: | 2.4 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jun-2010 14:33:52 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | ETUS |
| FileDescription: | PointerFocus Setup |
| FileVersion: | 2.4 |
| LegalCopyright: | Copyright ETUS 2018 |
| ProductName: | PointerFocus |
| ProductVersion: | 2.4 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 10-Jun-2010 14:33:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001468C | 0x00014800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.46623 |
.itext | 0x00016000 | 0x00000B34 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.79924 |
.data | 0x00017000 | 0x00000D9C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.67891 |
.bss | 0x00018000 | 0x0000570C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001E000 | 0x00000F9E | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.96778 |
.tls | 0x0001F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00020000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.190489 |
.reloc | 0x00021000 | 0x00001944 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0 |
.rsrc | 0x00023000 | 0x0000B200 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.15594 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05007 | 1376 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4091 | 3.13038 | 196 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.36196 | 204 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.34841 | 372 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.29351 | 924 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
124
Monitored processes
78
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,7673994514092820430,13270976932127447770,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10279212909837028535 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3040 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,7673994514092820430,13270976932127447770,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7503795344023134842 --renderer-client-id=46 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2812 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,7673994514092820430,13270976932127447770,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7572268620654741521 --renderer-client-id=63 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4756 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,7673994514092820430,13270976932127447770,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17163463253962522250 --renderer-client-id=58 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4816 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,7673994514092820430,13270976932127447770,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7915819824779200314 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,7673994514092820430,13270976932127447770,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=513929134869782057 --renderer-client-id=51 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4428 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,7673994514092820430,13270976932127447770,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3222290621769278923 --renderer-client-id=57 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,7673994514092820430,13270976932127447770,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4636367937587013717 --renderer-client-id=61 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4024 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,7673994514092820430,13270976932127447770,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10272145563518571747 --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2836 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,7673994514092820430,13270976932127447770,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=1706633357697603376 --mojo-platform-channel-handle=1952 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 809
Read events
4 357
Write events
431
Delete events
21
Modification events
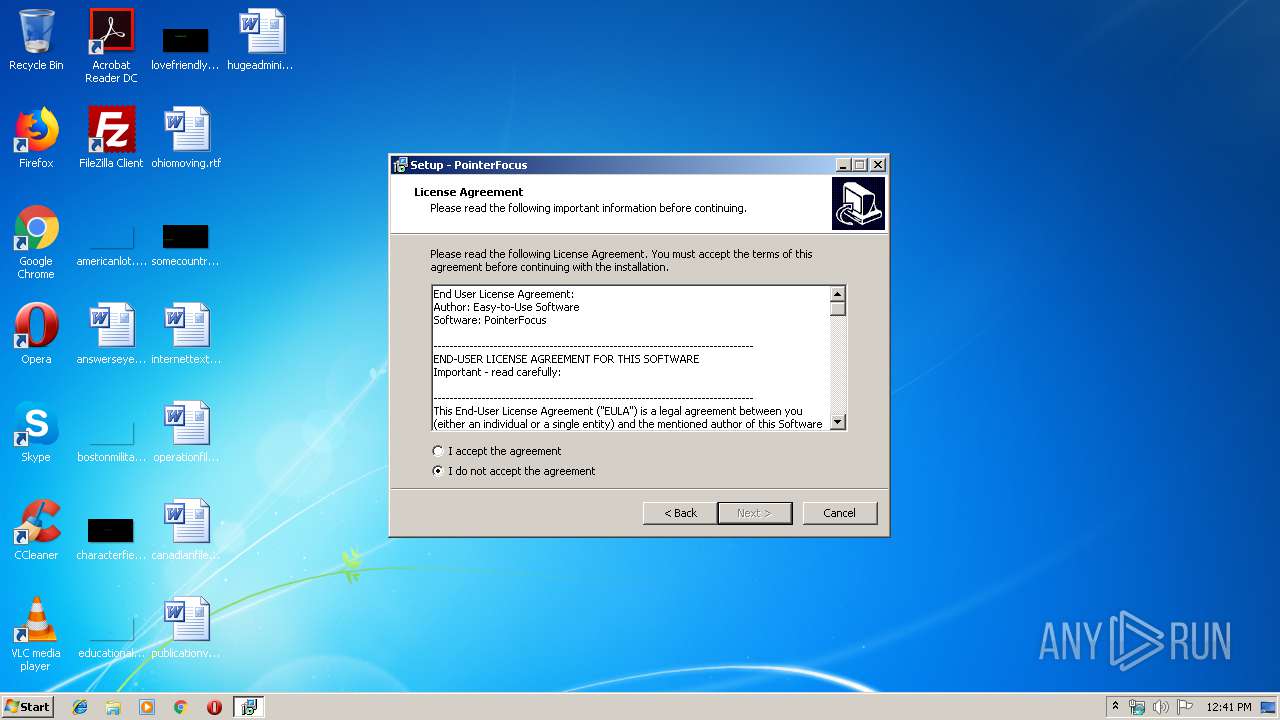
| (PID) Process: | (2988) pfsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PointerFocus_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.3.10 (u) | |||
| (PID) Process: | (2988) pfsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PointerFocus_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\PointerFocus | |||
| (PID) Process: | (2988) pfsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PointerFocus_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\PointerFocus\ | |||
| (PID) Process: | (2988) pfsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PointerFocus_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: PointerFocus | |||
| (PID) Process: | (2988) pfsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PointerFocus_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (2988) pfsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PointerFocus_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: desktopicon | |||
| (PID) Process: | (2988) pfsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PointerFocus_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: quicklaunchicon | |||
| (PID) Process: | (2988) pfsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PointerFocus_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: en | |||
| (PID) Process: | (2988) pfsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PointerFocus_is1 |
| Operation: | write | Name: | DisplayName |
Value: PointerFocus | |||
| (PID) Process: | (2988) pfsetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PointerFocus_is1 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\PointerFocus\PointerFocus.exe | |||
Executable files
26
Suspicious files
330
Text files
383
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2988 | pfsetup.tmp | C:\Program Files\PointerFocus\is-96PVP.tmp | — | |
MD5:— | SHA256:— | |||
| 2988 | pfsetup.tmp | C:\Program Files\PointerFocus\is-AV00I.tmp | — | |
MD5:— | SHA256:— | |||
| 2988 | pfsetup.tmp | C:\Program Files\PointerFocus\is-45IJO.tmp | — | |
MD5:— | SHA256:— | |||
| 2988 | pfsetup.tmp | C:\Program Files\PointerFocus\is-C1TVV.tmp | — | |
MD5:— | SHA256:— | |||
| 2988 | pfsetup.tmp | C:\Program Files\PointerFocus\is-3D6Q8.tmp | — | |
MD5:— | SHA256:— | |||
| 2988 | pfsetup.tmp | C:\Program Files\PointerFocus\is-8UAFV.tmp | — | |
MD5:— | SHA256:— | |||
| 2324 | PointerFocus.exe | C:\Users\admin\AppData\Local\Temp\Cab85E3.tmp | — | |
MD5:— | SHA256:— | |||
| 2324 | PointerFocus.exe | C:\Users\admin\AppData\Local\Temp\Tar85E4.tmp | — | |
MD5:— | SHA256:— | |||
| 2324 | PointerFocus.exe | C:\Users\admin\AppData\Local\Temp\Cab8633.tmp | — | |
MD5:— | SHA256:— | |||
| 2324 | PointerFocus.exe | C:\Users\admin\AppData\Local\Temp\Tar8634.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
194
DNS requests
139
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2324 | PointerFocus.exe | GET | 200 | 8.248.131.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.2 Kb | whitelisted |
3632 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 512 b | whitelisted |
3632 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
3632 | chrome.exe | GET | 200 | 173.194.7.89:80 | http://r3---sn-p5qs7n7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.20.5&mm=28&mn=sn-p5qs7n7e&ms=nvh&mt=1562240481&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3632 | chrome.exe | GET | 200 | 54.230.129.58:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3632 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAoGMEJ%2FW7ztaVc5ZZO2RR8%3D | US | der | 471 b | whitelisted |
3632 | chrome.exe | GET | 200 | 204.13.202.71:80 | http://ssl.trustwave.com/issuers/STCA.crt | US | der | 956 b | whitelisted |
3632 | chrome.exe | GET | 200 | 8.248.131.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/DF3C24F9BFD666761B268073FE06D1CC8D4F82A4.crt | US | der | 914 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3632 | chrome.exe | 216.58.206.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3632 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3632 | chrome.exe | 216.58.205.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
3632 | chrome.exe | 172.217.18.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3632 | chrome.exe | 173.194.7.89:80 | r3---sn-p5qs7n7e.gvt1.com | Google Inc. | US | whitelisted |
3632 | chrome.exe | 172.217.21.238:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3632 | chrome.exe | 216.58.207.67:443 | id.google.com | Google Inc. | US | whitelisted |
3632 | chrome.exe | 172.217.16.142:443 | encrypted-tbn2.gstatic.com | Google Inc. | US | whitelisted |
3632 | chrome.exe | 172.217.18.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
3632 | chrome.exe | 172.217.21.238:443 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
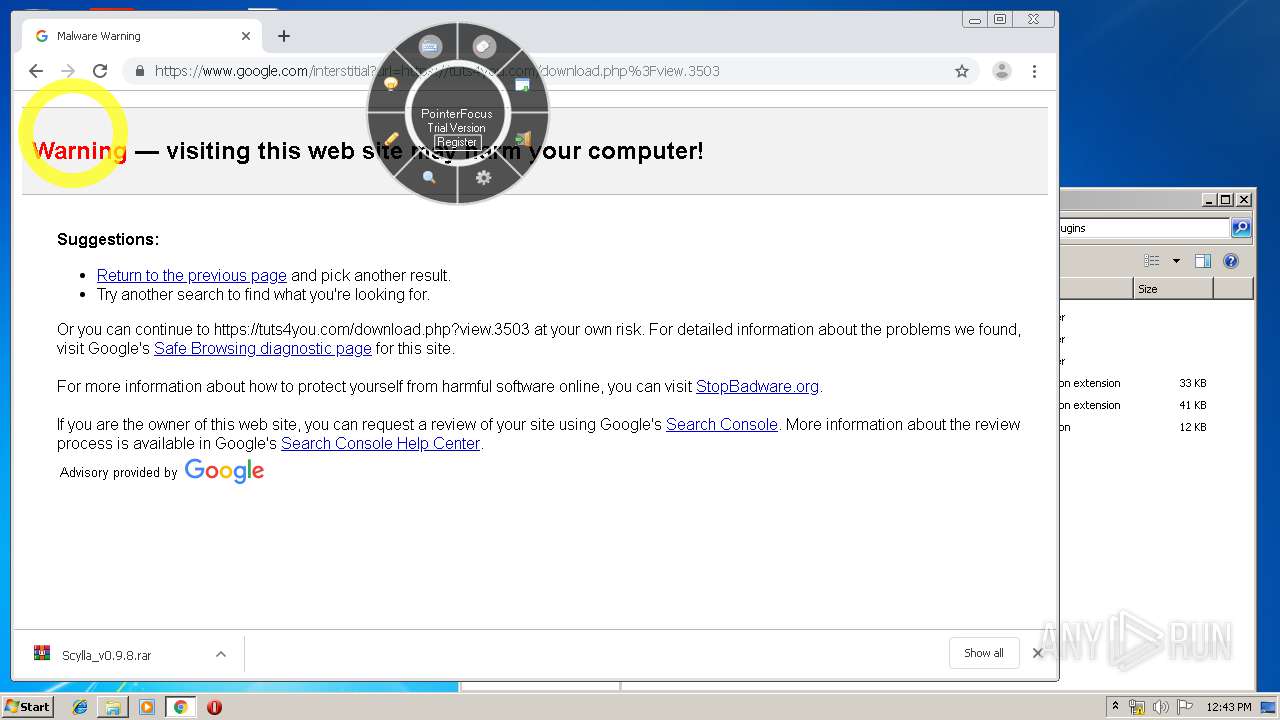
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3632 | chrome.exe | A Network Trojan was detected | MALWARE [PTsecurity] Ransom.HiddenTear!8.DC9E Malicious SSL certificate |
3632 | chrome.exe | A Network Trojan was detected | MALWARE [PTsecurity] Ransom.HiddenTear!8.DC9E Malicious SSL certificate |
3632 | chrome.exe | A Network Trojan was detected | MALWARE [PTsecurity] Ransom.HiddenTear!8.DC9E Malicious SSL certificate |
3632 | chrome.exe | A Network Trojan was detected | MALWARE [PTsecurity] Ransom.HiddenTear!8.DC9E Malicious SSL certificate |
2 ETPRO signatures available at the full report