| URL: | https://vaticancitystamps.org |
| Full analysis: | https://app.any.run/tasks/71b58293-6473-4fd4-9503-457bdfd28023 |
| Verdict: | Malicious activity |
| Analysis date: | August 19, 2020, 22:32:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 44E134153373BC9B9308BEC057DF0D14 |
| SHA1: | B9A9343826E47EF90F54E6062D5C8BFF9DE4E0F5 |
| SHA256: | 3825391C818ACE514B715C044AC2BF48C9F2EDCFA4B4623A497CFC181A938BC6 |
| SSDEEP: | 3:N8mHbUU:2iUU |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2820)
- chrome.exe (PID: 700)
Application launched itself
- chrome.exe (PID: 2820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
11
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,10186928147484412941,13622963100079746844,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=332967356505114155 --mojo-platform-channel-handle=1592 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,10186928147484412941,13622963100079746844,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12701613548515995166 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,10186928147484412941,13622963100079746844,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=8329551268200400538 --mojo-platform-channel-handle=2596 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,10186928147484412941,13622963100079746844,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8790268162063317609 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2508 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,10186928147484412941,13622963100079746844,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16190299184733083965 --mojo-platform-channel-handle=1052 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,10186928147484412941,13622963100079746844,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=18238619223163892124 --mojo-platform-channel-handle=3624 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2772 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://vaticancitystamps.org" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,10186928147484412941,13622963100079746844,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13856928731671575860 --mojo-platform-channel-handle=2856 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,10186928147484412941,13622963100079746844,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14058544874098075619 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
598
Read events
525
Write events
69
Delete events
4
Modification events
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2820-13242349979780625 |
Value: 259 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2820) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
38
Text files
150
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ff75da08-a1fc-4f8a-baa4-79ef06b062b6.tmp | — | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1911d8.TMP | text | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1911c9.TMP | text | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF191217.TMP | text | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1913bd.TMP | — | |
MD5:— | SHA256:— | |||
| 2820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
115
DNS requests
54
Threats
0
HTTP requests
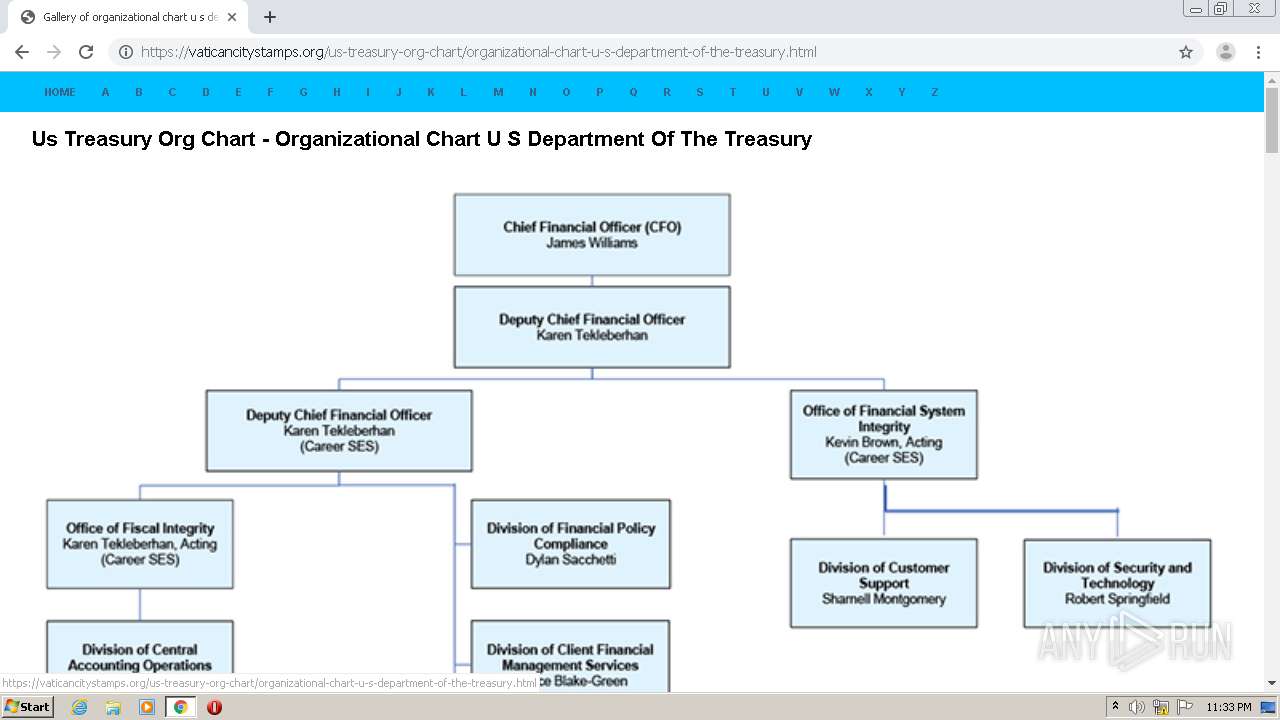
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
700 | chrome.exe | GET | — | 5.152.246.164:80 | http://www.mef.gov.it/en/ministero/struttura/img/en_organigramma_main_2x.png | IT | — | — | unknown |
700 | chrome.exe | GET | 301 | 184.31.84.172:80 | http://www.treasury.gov/about/organizational-structure/PublishingImages/organizational-chart.jpg | NL | — | — | suspicious |
700 | chrome.exe | GET | — | 172.217.22.33:80 | http://1.bp.blogspot.com/-iFsJ9eCUTu0/TaMAqpDbOKI/AAAAAAAAAK8/L_FHUpTxauQ/s1600/Treasury.jpg | US | — | — | whitelisted |
700 | chrome.exe | GET | — | 50.97.132.231:80 | http://www.orgcharting.com/wp-content/uploads/cia-org-chart.png | US | — | — | unknown |
700 | chrome.exe | GET | 200 | 172.67.73.71:80 | http://www.khilafah.com/wp-content/uploads/2016/02/KCOM_orgchart_treasury_revenues.gif | US | image | 20.0 Kb | suspicious |
700 | chrome.exe | GET | 200 | 50.97.132.231:80 | http://www.orgcharting.com/wp-content/uploads/us-treasury-department.png | US | image | 162 Kb | unknown |
700 | chrome.exe | GET | 200 | 69.167.179.178:80 | http://rmi-mof.com/wp-content/uploads/2017/04/mof-org-chart.jpg | US | image | 105 Kb | unknown |
700 | chrome.exe | GET | 200 | 50.97.132.231:80 | http://www.orgcharting.com/wp-content/uploads/american-state-department-org-chart-diagram.png | US | image | 143 Kb | unknown |
700 | chrome.exe | GET | 200 | 64.29.145.73:80 | http://www.netage.com/economics/gov/images-org/USTorgchart.jpg | US | image | 66.2 Kb | unknown |
700 | chrome.exe | GET | 200 | 172.67.73.71:80 | http://www.khilafah.com/wp-content/uploads/2016/02/KCOM_orgchart_treasury.gif | US | image | 18.8 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
700 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
700 | chrome.exe | 213.202.241.219:443 | vaticancitystamps.org | myLoc managed IT AG | DE | unknown |
— | — | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
700 | chrome.exe | 172.217.23.100:443 | www.google.com | Google Inc. | US | whitelisted |
700 | chrome.exe | 172.67.38.97:443 | secure.statcounter.com | — | US | suspicious |
700 | chrome.exe | 172.217.18.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
700 | chrome.exe | 104.111.229.214:443 | home.treasury.gov | Akamai International B.V. | NL | unknown |
700 | chrome.exe | 216.58.205.238:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
700 | chrome.exe | 91.198.174.208:443 | upload.wikimedia.org | Wikimedia Foundation, Inc. | NL | suspicious |
700 | chrome.exe | 64.29.145.73:80 | www.netage.com | InternetNamesForBusiness.com | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
vaticancitystamps.org |
| unknown |
accounts.google.com |
| shared |
secure.statcounter.com |
| whitelisted |
www.google.com |
| malicious |
c.statcounter.com |
| whitelisted |
clients2.google.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
home.treasury.gov |
| suspicious |