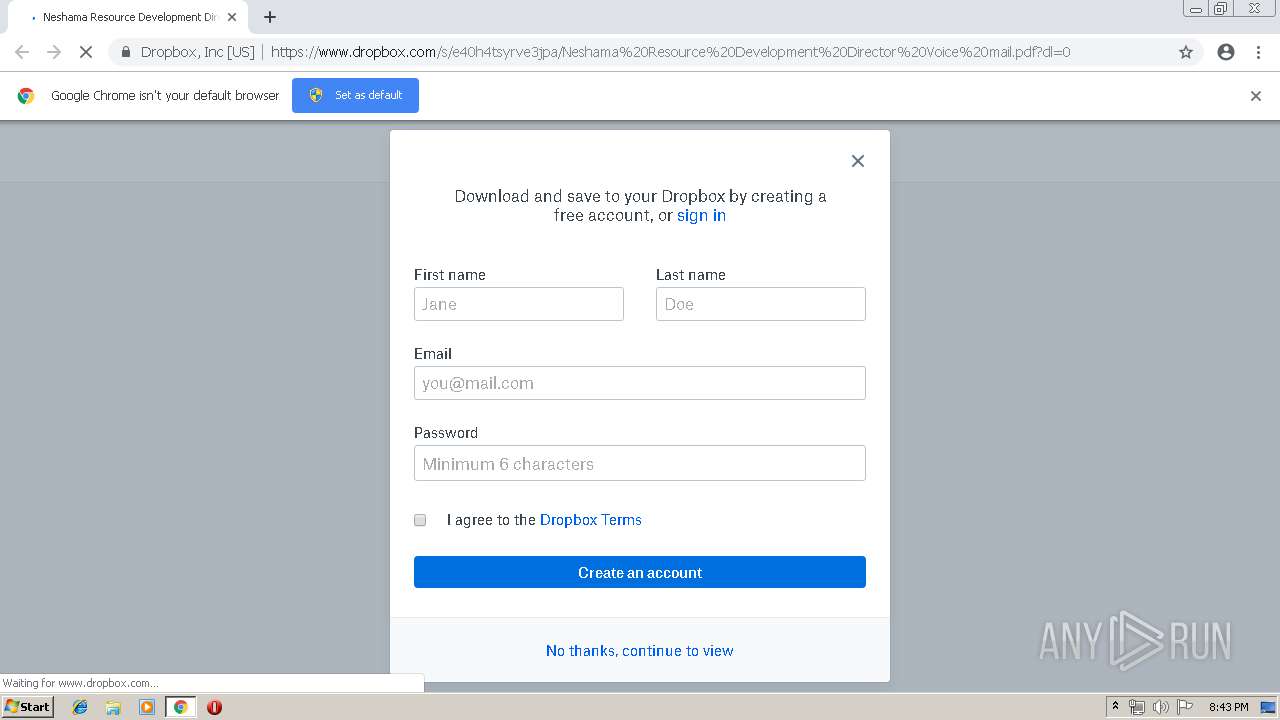
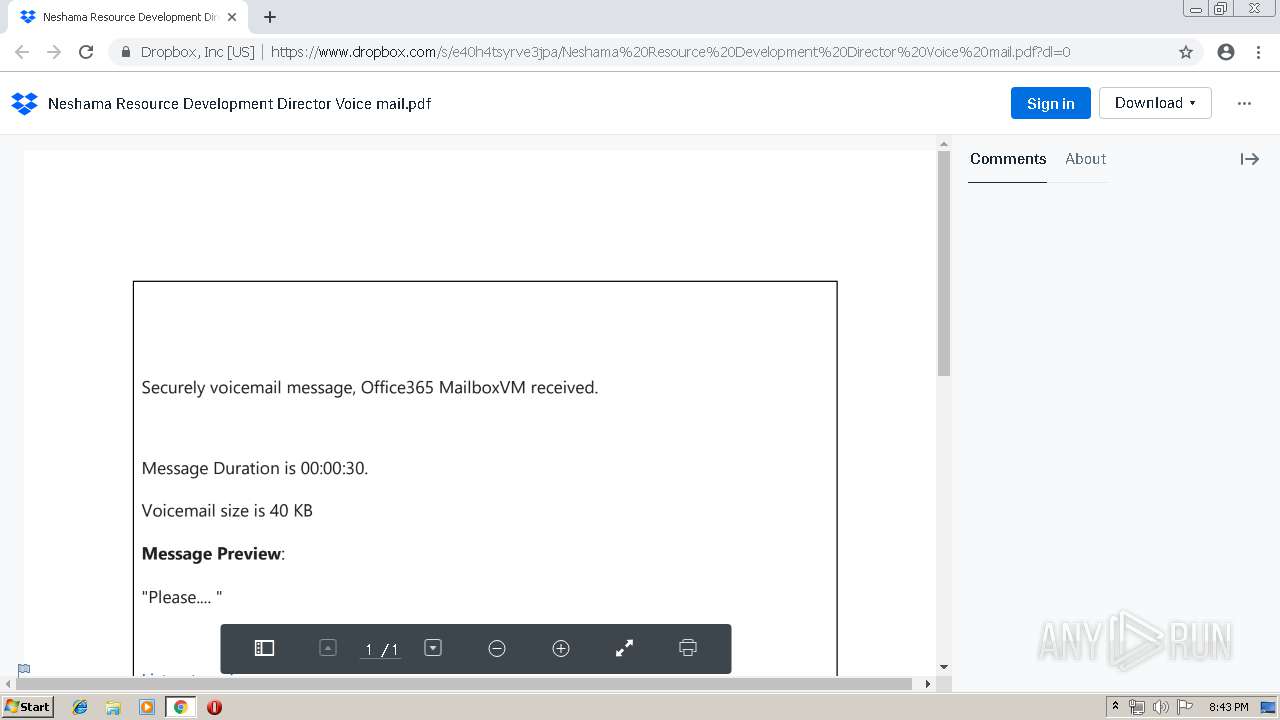
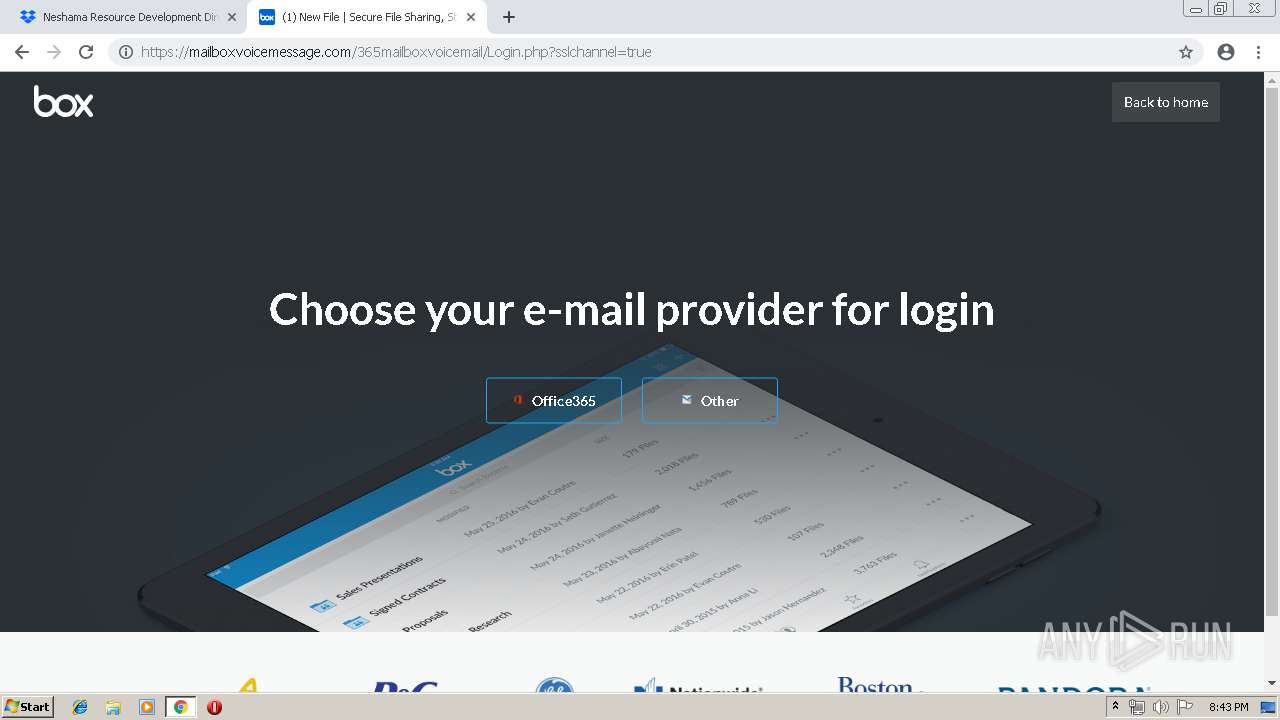
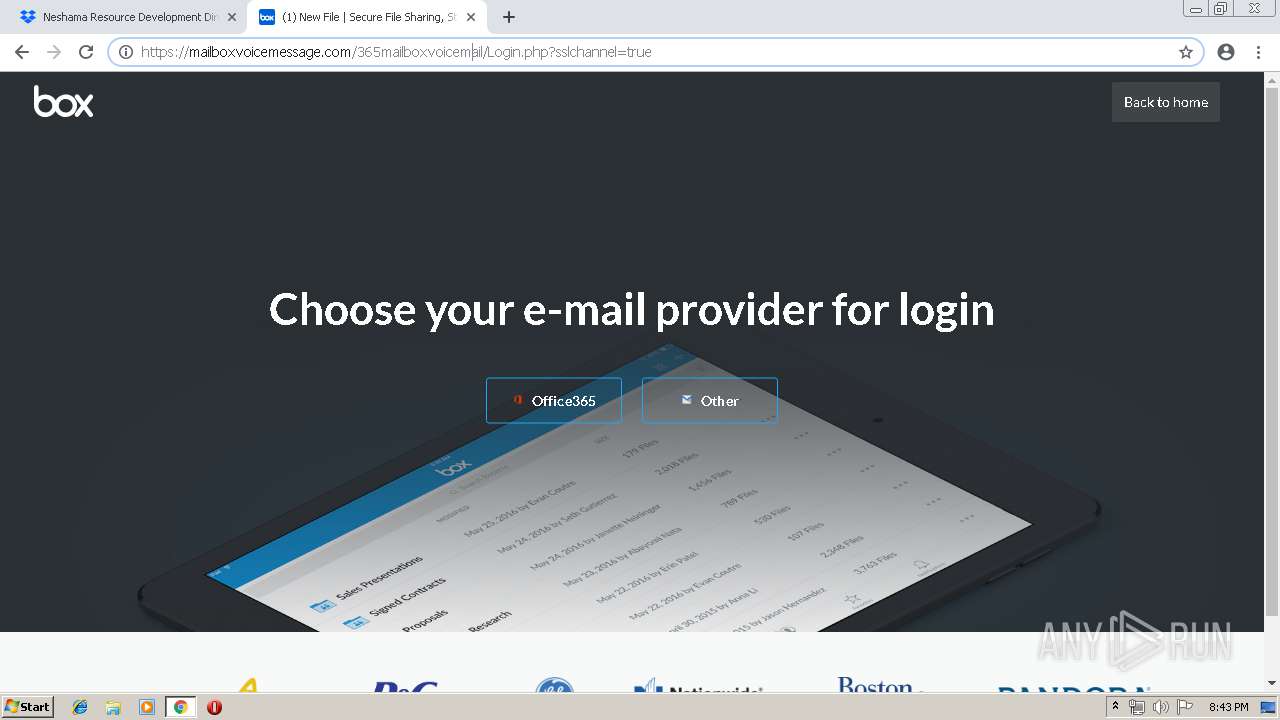
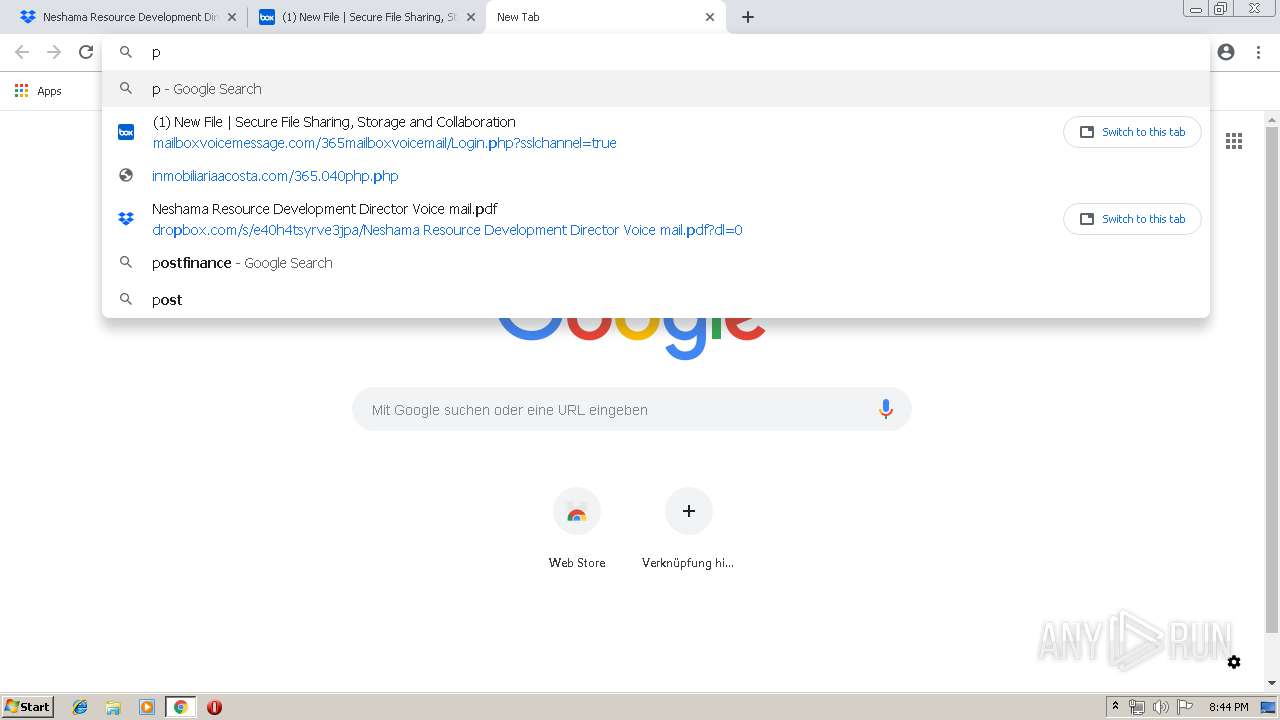
| URL: | https://www.dropbox.com/s/e40h4tsyrve3jpa/Neshama%20Resource%20Development%20Director%20Voice%20mail.pdf?dl=0 |
| Full analysis: | https://app.any.run/tasks/47dca1d6-dbe7-4991-86b1-c072736d541d |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 19:42:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E4574CC96A4462B93ACD97F096913399 |
| SHA1: | 38EA6FBFED5C3A43621AD0440A52C7E0FE1CF3C5 |
| SHA256: | 38031CDB6BA154F0377B62D8C46B630CEDE30CAA529FE39E822F6AC2824A1D23 |
| SSDEEP: | 3:N8DSLcVHGkl3WmTAojr7cWjmAMEiuQhMhCVRQVn:2OLHklWmTpjnnwEiuQhMhCvAn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2148)
INFO
Application launched itself
- chrome.exe (PID: 2148)
Reads settings of System Certificates
- chrome.exe (PID: 2148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
28
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,8588022377051013553,4511424626081502629,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3222455213829651026 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3222455213829651026 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2756 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,8588022377051013553,4511424626081502629,131072 --enable-features=PasswordImport --service-pipe-token=18102402086842906221 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18102402086842906221 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,8588022377051013553,4511424626081502629,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1788754391341334820 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1788754391341334820 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3992 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,8588022377051013553,4511424626081502629,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7755003344932284298 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7755003344932284298 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=916 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,8588022377051013553,4511424626081502629,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11462026236251187667 --mojo-platform-channel-handle=4540 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,8588022377051013553,4511424626081502629,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6999808574982129835 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6999808574982129835 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2784 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,8588022377051013553,4511424626081502629,131072 --enable-features=PasswordImport --service-pipe-token=7378554231128739446 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7378554231128739446 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1964 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f390f18,0x6f390f28,0x6f390f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,8588022377051013553,4511424626081502629,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6523419857996547492 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6523419857996547492 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4192 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
593
Read events
491
Write events
97
Delete events
5
Modification events
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2148-13200522185955750 |
Value: 259 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2148-13200522185955750 |
Value: 259 | |||
Executable files
0
Suspicious files
431
Text files
205
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cbb458d7-31e1-4faf-a36a-83f0fd110de9.tmp | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
197
DNS requests
110
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
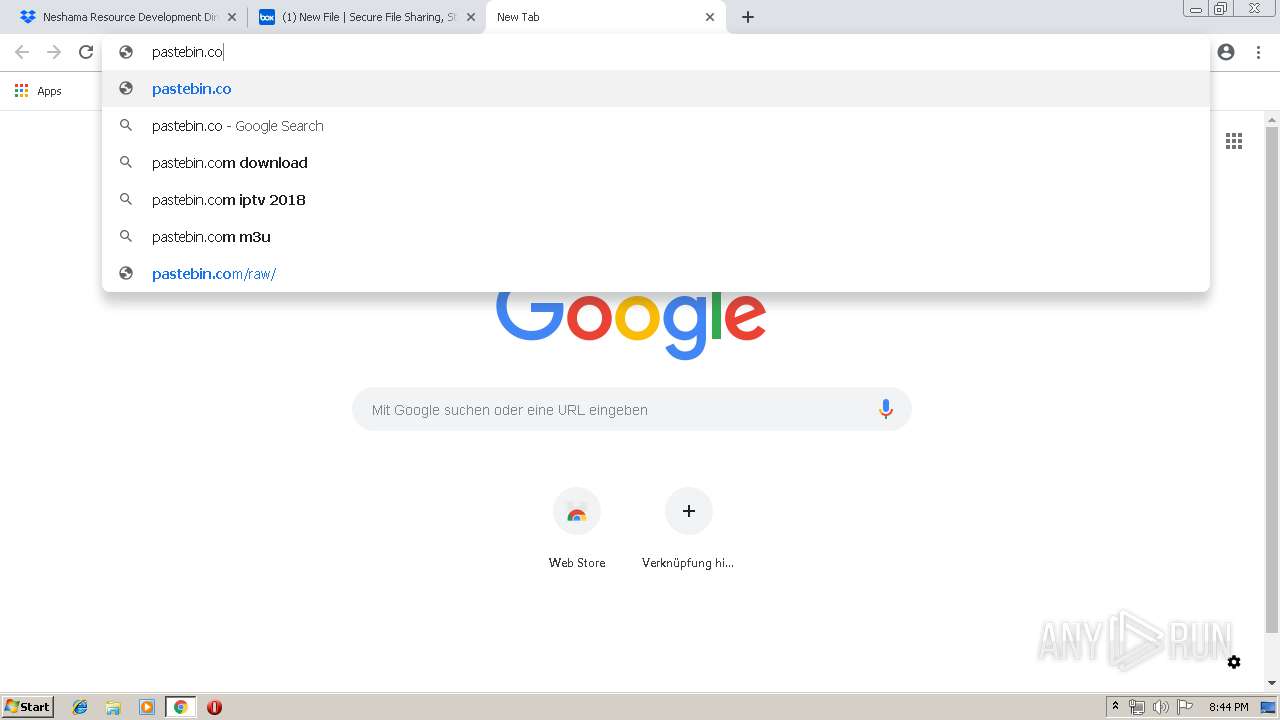
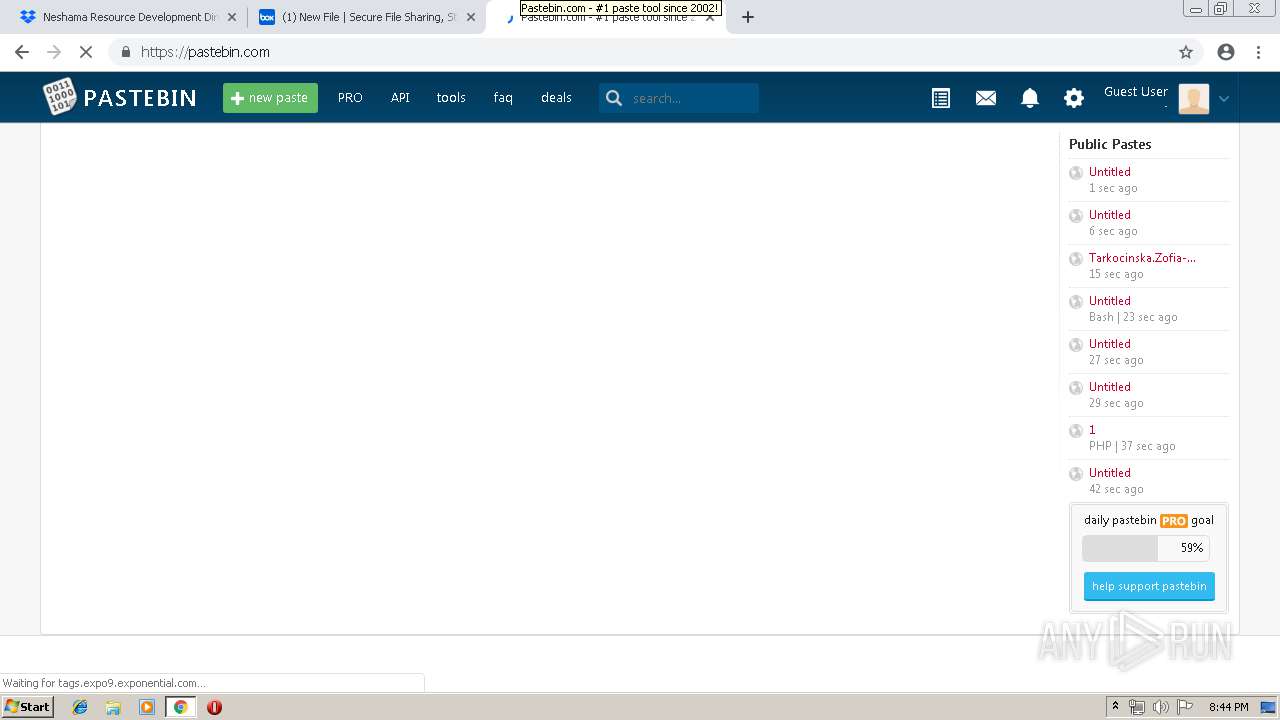
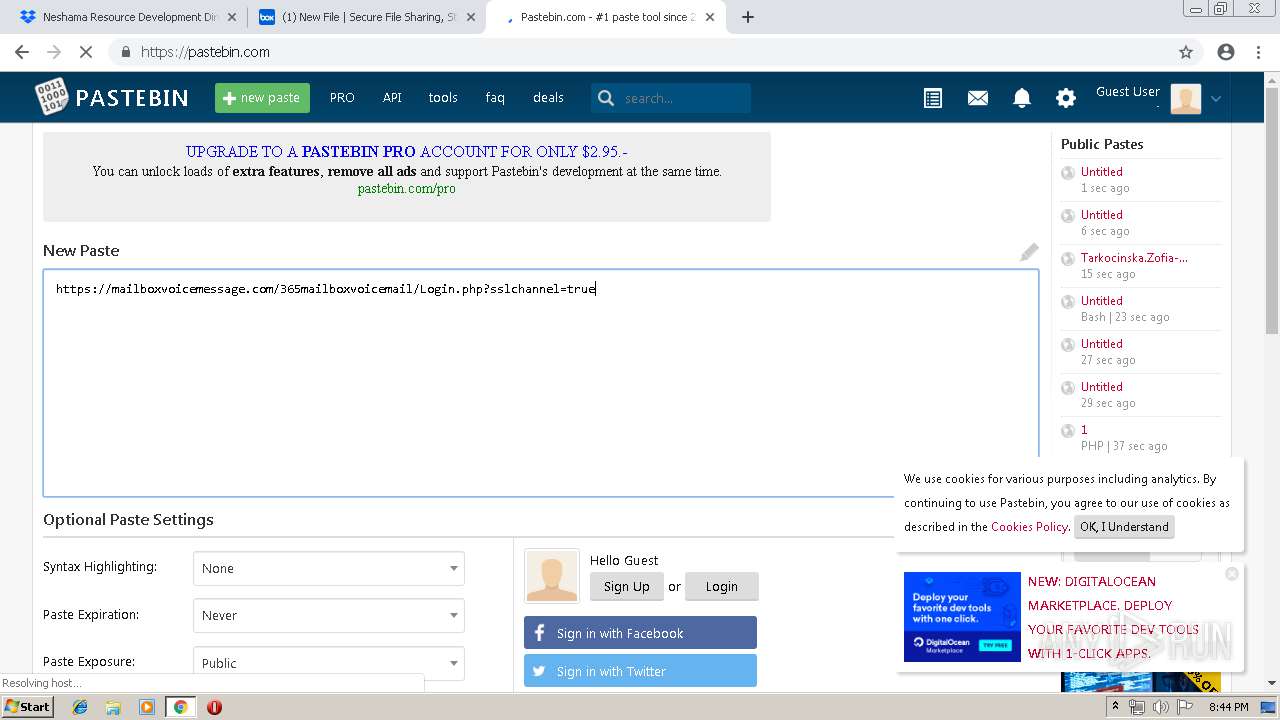
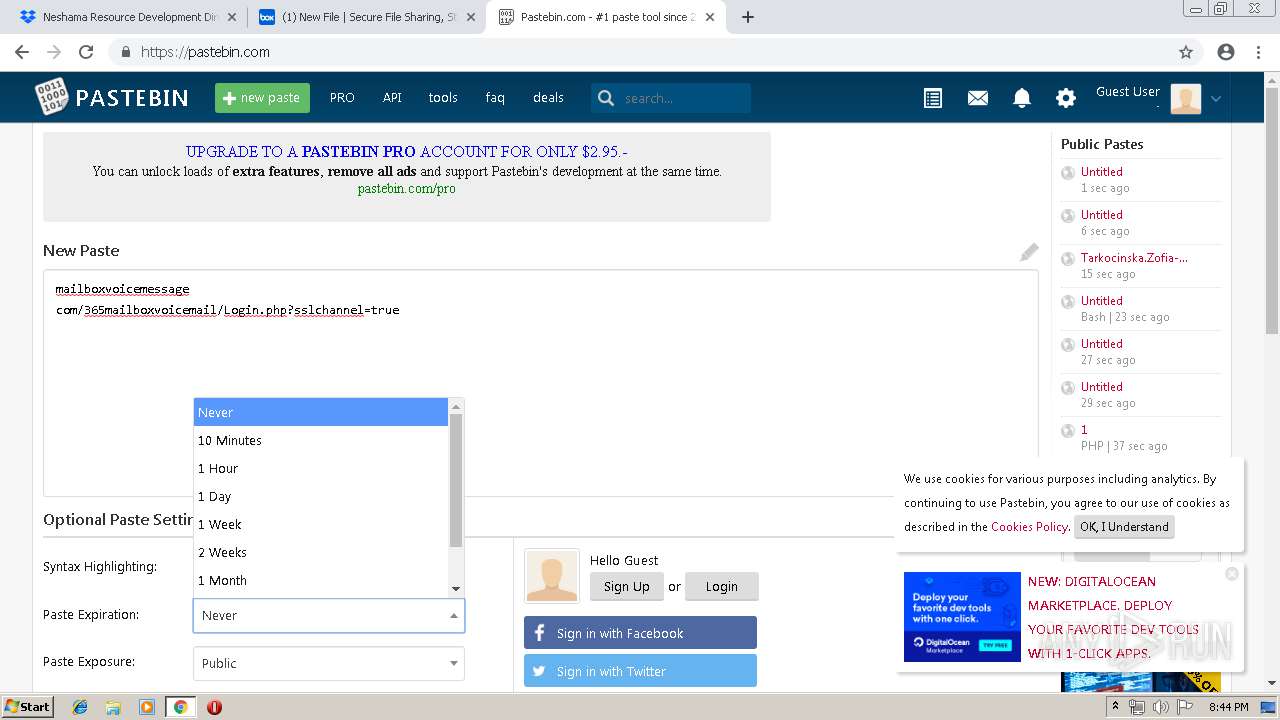
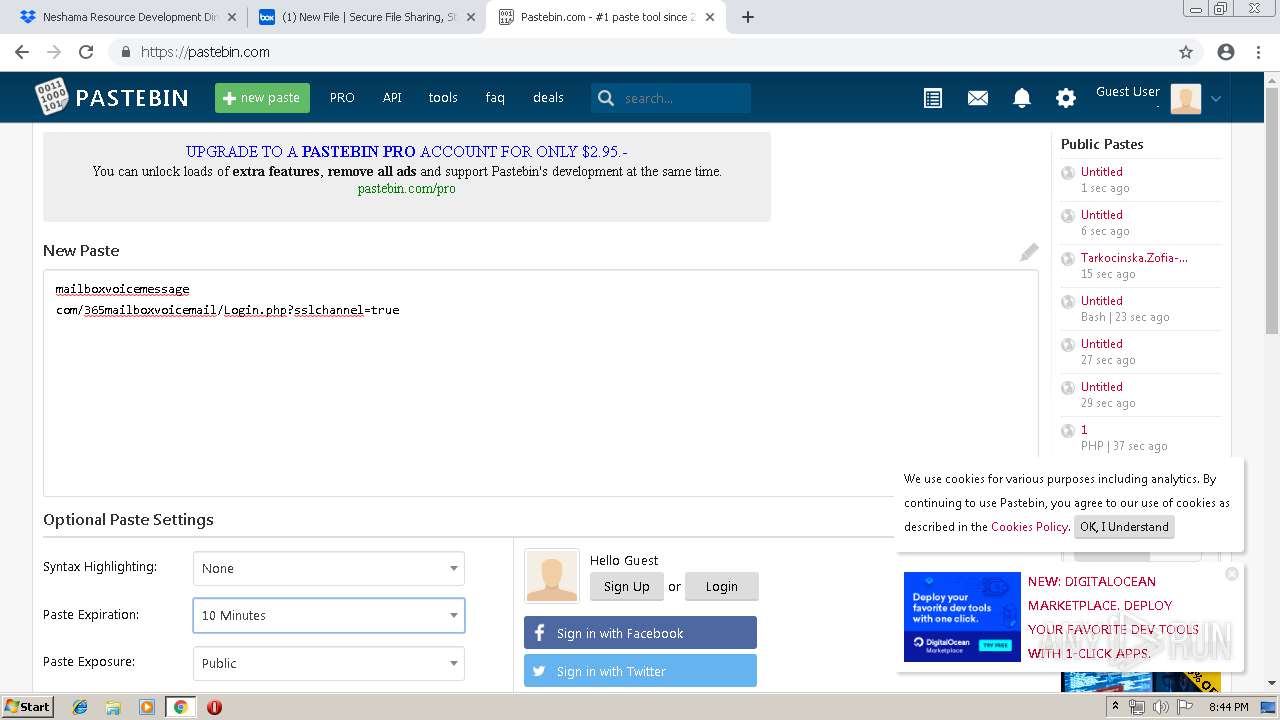
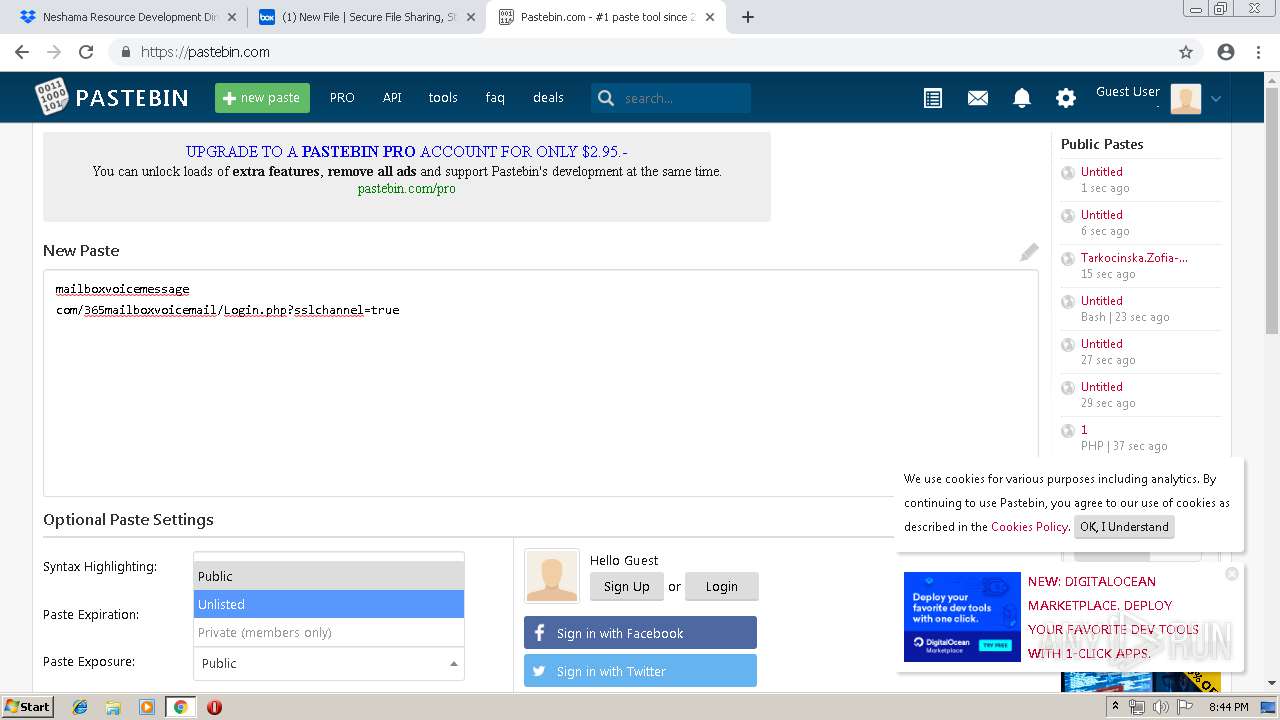
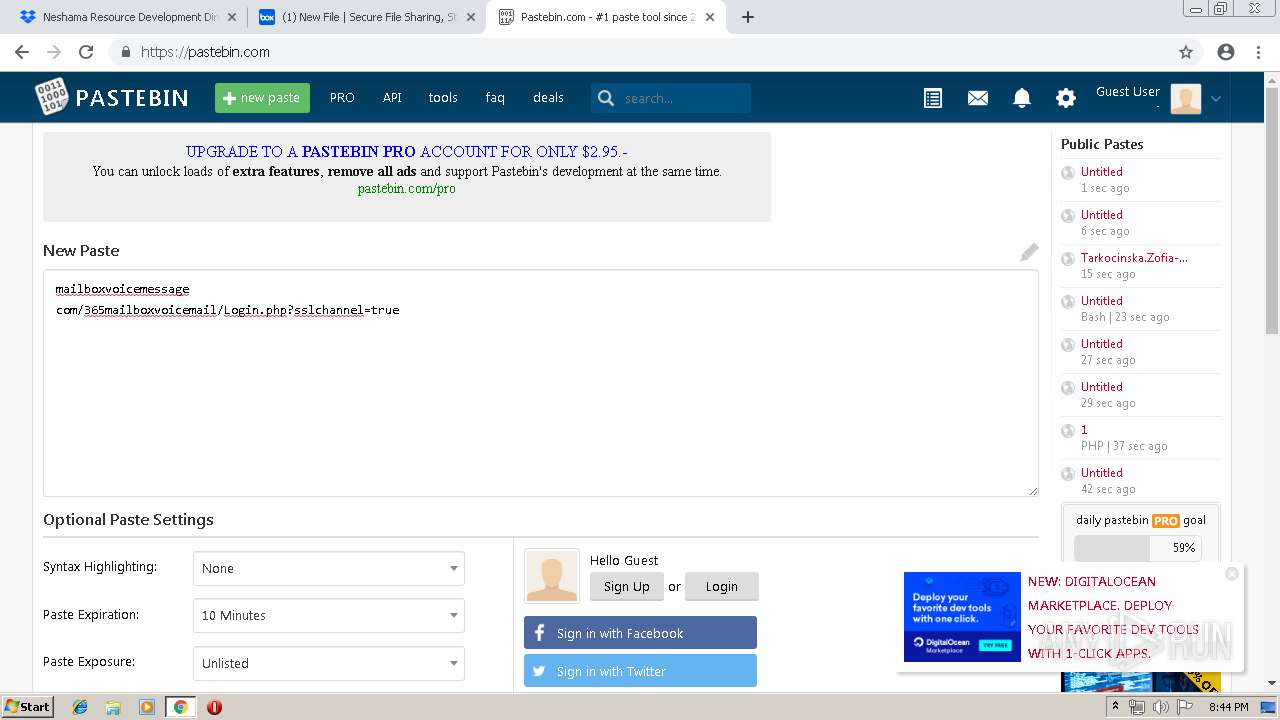
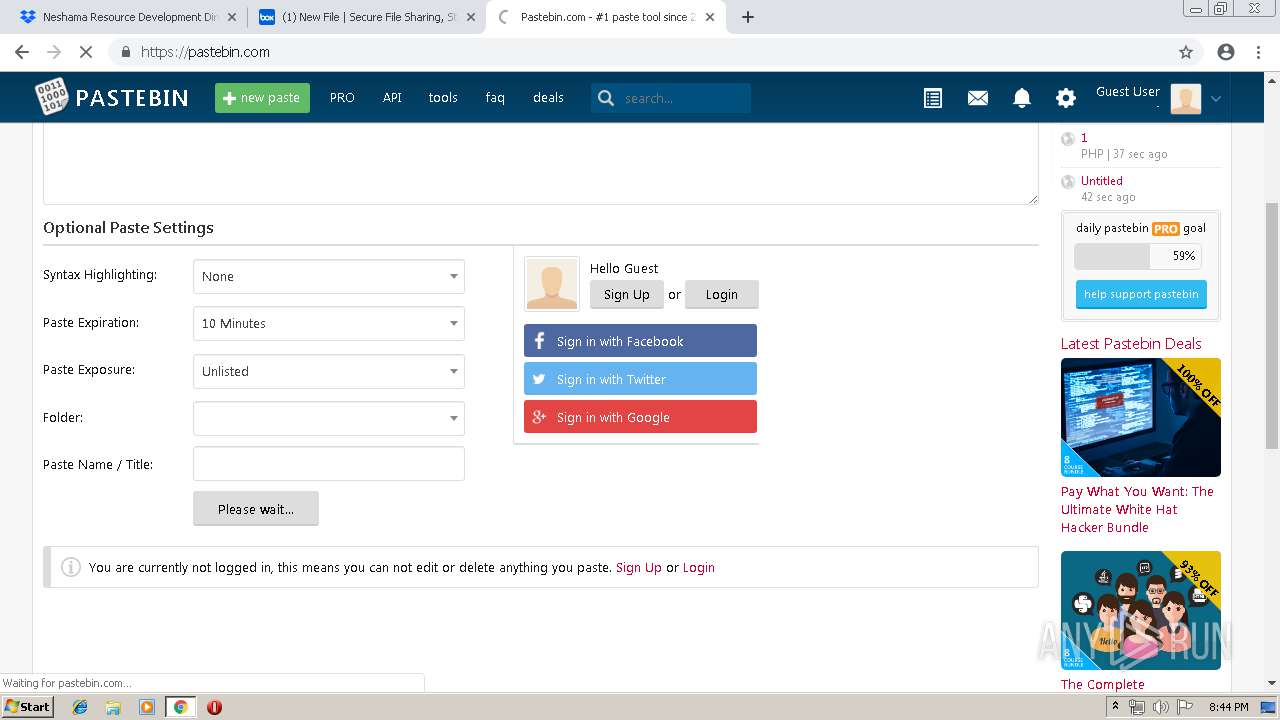
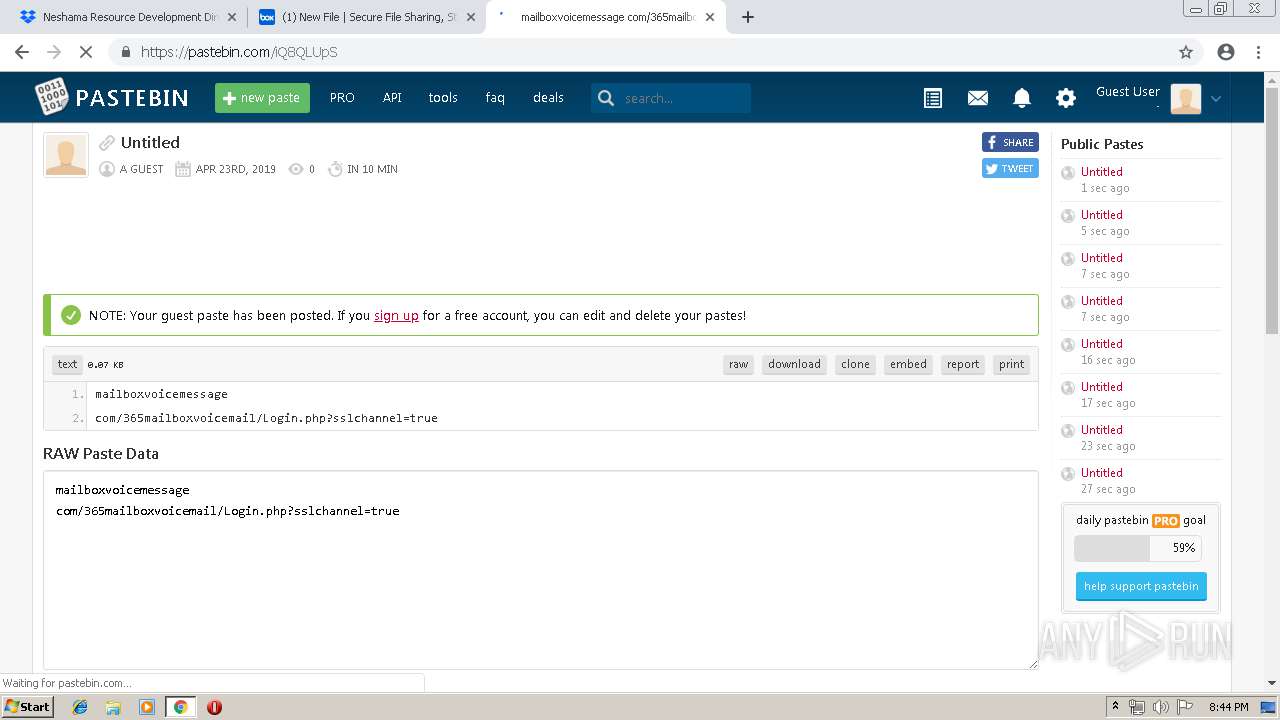
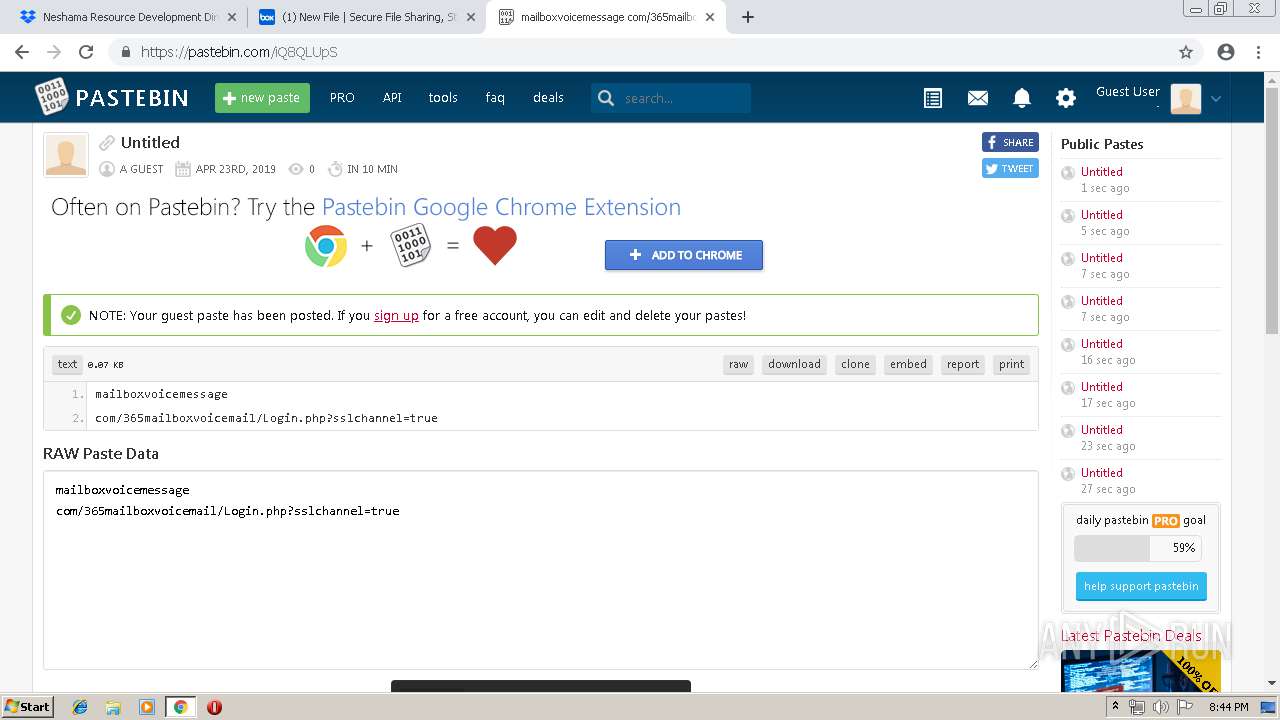
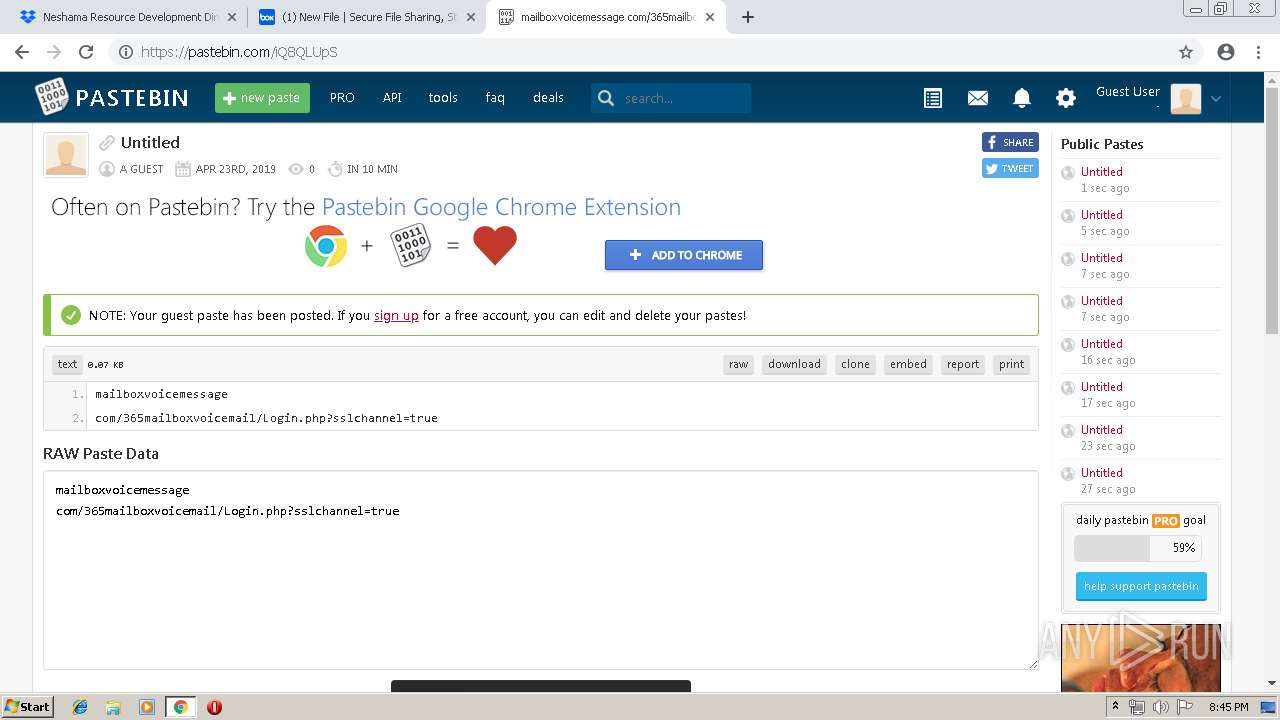
2148 | chrome.exe | GET | 301 | 104.20.209.21:80 | http://pastebin.com/ | US | — | — | malicious |
2148 | chrome.exe | GET | — | 85.194.240.137:80 | http://pixel.onaudience.com/?mapped=PtzN39jEs2h3zfNyBdr2SrQB&partner=2&redirect=grey.erne.co%2Ftags%3Fid%3Dcm_ct_%25s%26img%3D1%26red%3Dhttp%253A%252F%252Fbh.contextweb.com%252Fbh%252Frtset%253Fdo%253Dadd%2526pid%253D560956%2526ev%253DPtzN39jEs2h3zfNyBdr2SrQB | PL | — | — | whitelisted |
2148 | chrome.exe | GET | — | 85.194.240.137:80 | http://pixel.onaudience.com/?partner=104&icm&mapped=4d6f5dde7b01b5d74c7d250c20588836&redirect=http%3A%2F%2Fgrey.erne.co%2Ftags%3Fid%3Dcm_ct_c85a426df66363b5%26img%3D1%26red%3Dhttp%253A%252F%252Fbh.contextweb.com%252Fbh%252Frtset%253Fdo%253Dadd%2526pid%253D560956%2526ev%253DPtzN39jEs2h3zfNyBdr2SrQB | PL | — | — | whitelisted |
2148 | chrome.exe | GET | 302 | 52.48.148.204:80 | http://sync.crwdcntrl.net/map/ct=y/c=8587/tp=CLOD?http%3A%2F%2Fpixel.onaudience.com%2F%3Fpartner%3D104%26icm%26mapped%3D%24%7Bprofile_id%7D%26redirect%3Dhttp%253A%252F%252Fgrey.erne.co%252Ftags%253Fid%253Dcm_ct_c85a426df66363b5%2526img%253D1%2526red%253Dhttp%25253A%25252F%25252Fbh.contextweb.com%25252Fbh%25252Frtset%25253Fdo%25253Dadd%252526pid%25253D560956%252526ev%25253DPtzN39jEs2h3zfNyBdr2SrQB | IE | — | — | whitelisted |
2148 | chrome.exe | GET | 302 | 188.165.27.173:80 | http://grey.erne.co/tags?id=cm_ct_c85a426df66363b5&img=1&red=http%3A%2F%2Fbh.contextweb.com%2Fbh%2Frtset%3Fdo%3Dadd%26pid%3D560956%26ev%3DPtzN39jEs2h3zfNyBdr2SrQB | LT | — | — | whitelisted |
2148 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 506 b | whitelisted |
2148 | chrome.exe | GET | 200 | 2.16.186.72:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 55.6 Kb | whitelisted |
2148 | chrome.exe | GET | 200 | 173.194.139.6:80 | http://r1---sn-aigzrn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.230.125.140&mm=28&mn=sn-aigzrn7k&ms=nvh&mt=1556048490&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2148 | chrome.exe | GET | 302 | 52.48.148.204:80 | http://sync.crwdcntrl.net/map/c=8587/tp=CLOD?http%3A%2F%2Fpixel.onaudience.com%2F%3Fpartner%3D104%26icm%26mapped%3D%24%7Bprofile_id%7D%26redirect%3Dhttp%253A%252F%252Fgrey.erne.co%252Ftags%253Fid%253Dcm_ct_c85a426df66363b5%2526img%253D1%2526red%253Dhttp%25253A%25252F%25252Fbh.contextweb.com%25252Fbh%25252Frtset%25253Fdo%25253Dadd%252526pid%25253D560956%252526ev%25253DPtzN39jEs2h3zfNyBdr2SrQB | IE | — | — | whitelisted |
2148 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2148 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2148 | chrome.exe | 162.125.66.1:443 | www.dropbox.com | Dropbox, Inc. | DE | shared |
2148 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2148 | chrome.exe | 104.16.99.29:443 | cfl.dropboxstatic.com | Cloudflare Inc | US | shared |
2148 | chrome.exe | 172.217.21.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2148 | chrome.exe | 162.125.248.1:443 | dropbox.com | Dropbox, Inc. | US | shared |
2148 | chrome.exe | 162.125.66.5:443 | uc964cd99cdd21d5e37c1dc1e3ca.previews.dropboxusercontent.com | Dropbox, Inc. | DE | shared |
2148 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2148 | chrome.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
2148 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.dropbox.com |
| shared |
accounts.google.com |
| shared |
ocsp.digicert.com |
| whitelisted |
cfl.dropboxstatic.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
uc964cd99cdd21d5e37c1dc1e3ca.previews.dropboxusercontent.com |
| unknown |
dropbox.com |
| shared |
ucd16f058e9ebf6ce44f07dc24a1.previews.dropboxusercontent.com |
| unknown |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2148 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
2148 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
2148 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2148 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2148 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
2148 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
2148 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
2148 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
2148 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
2148 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |