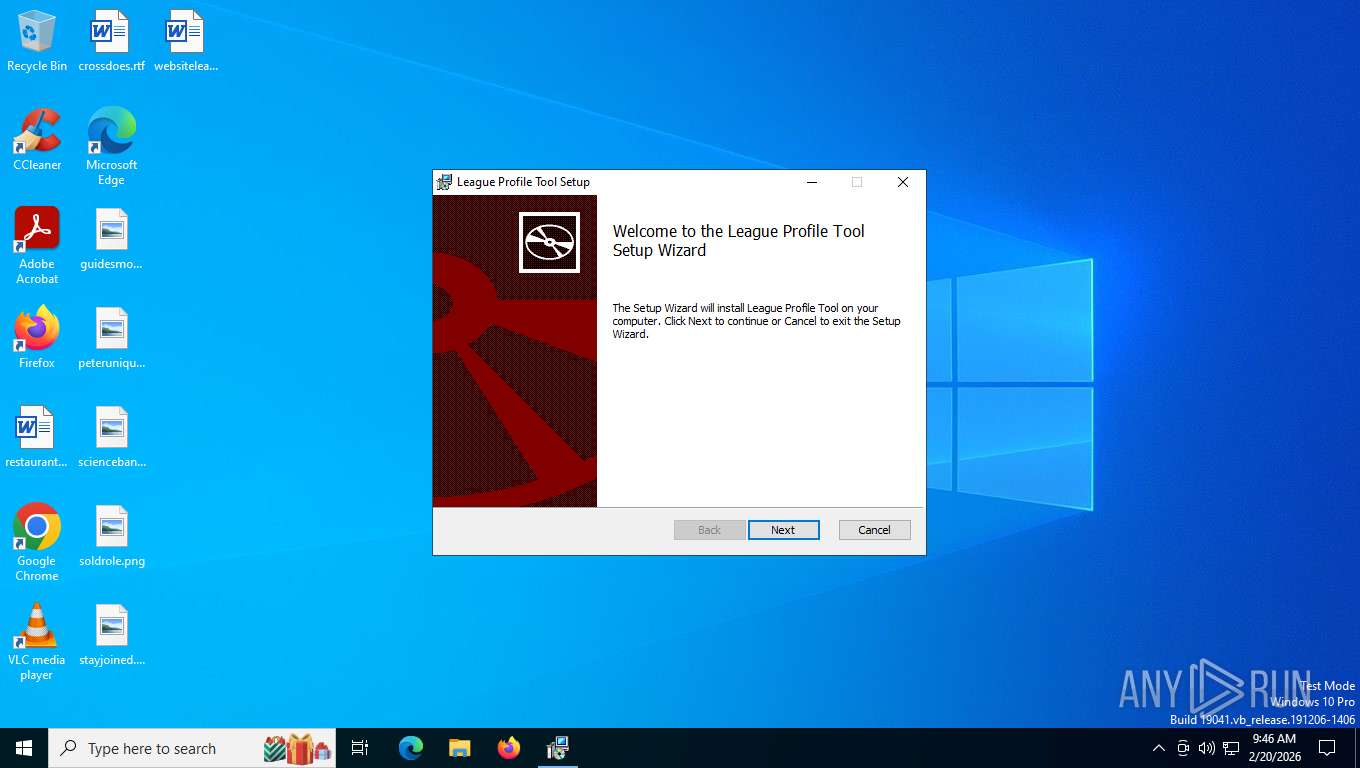
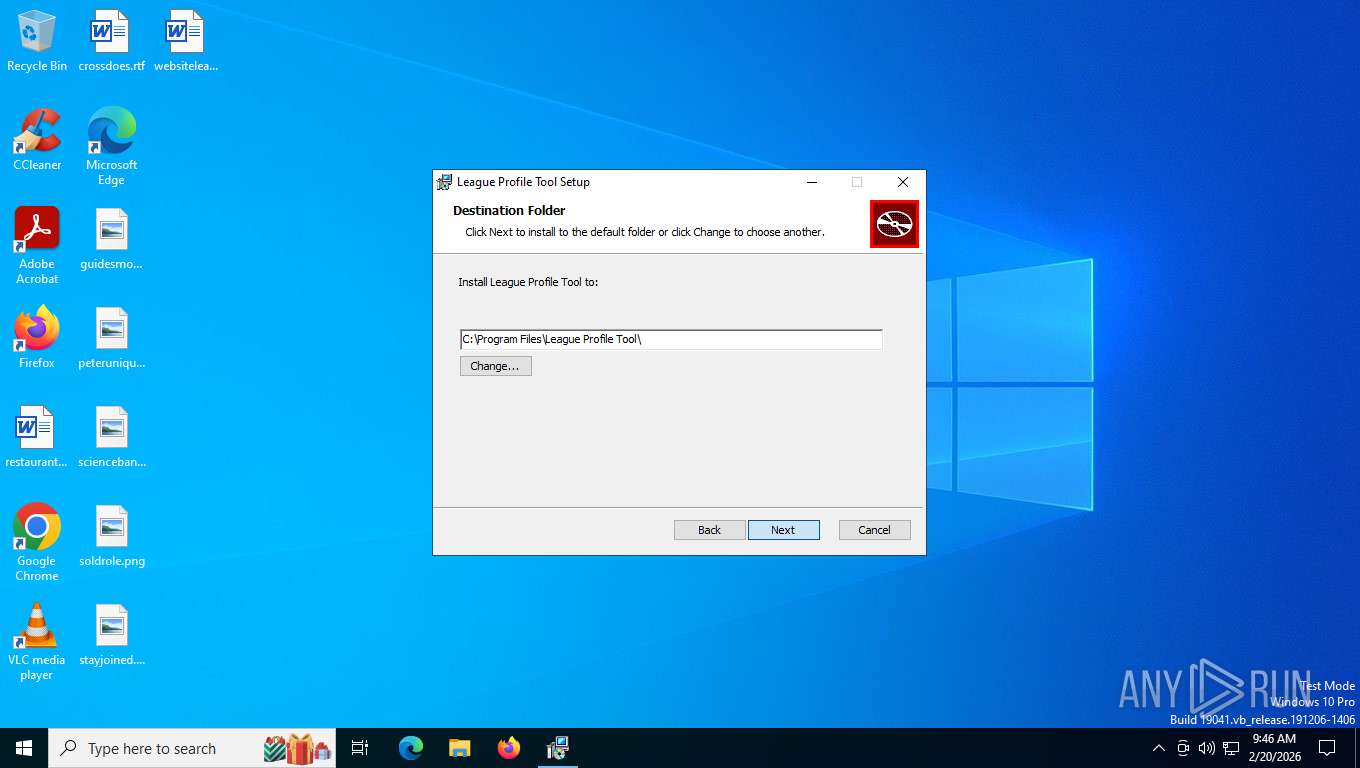
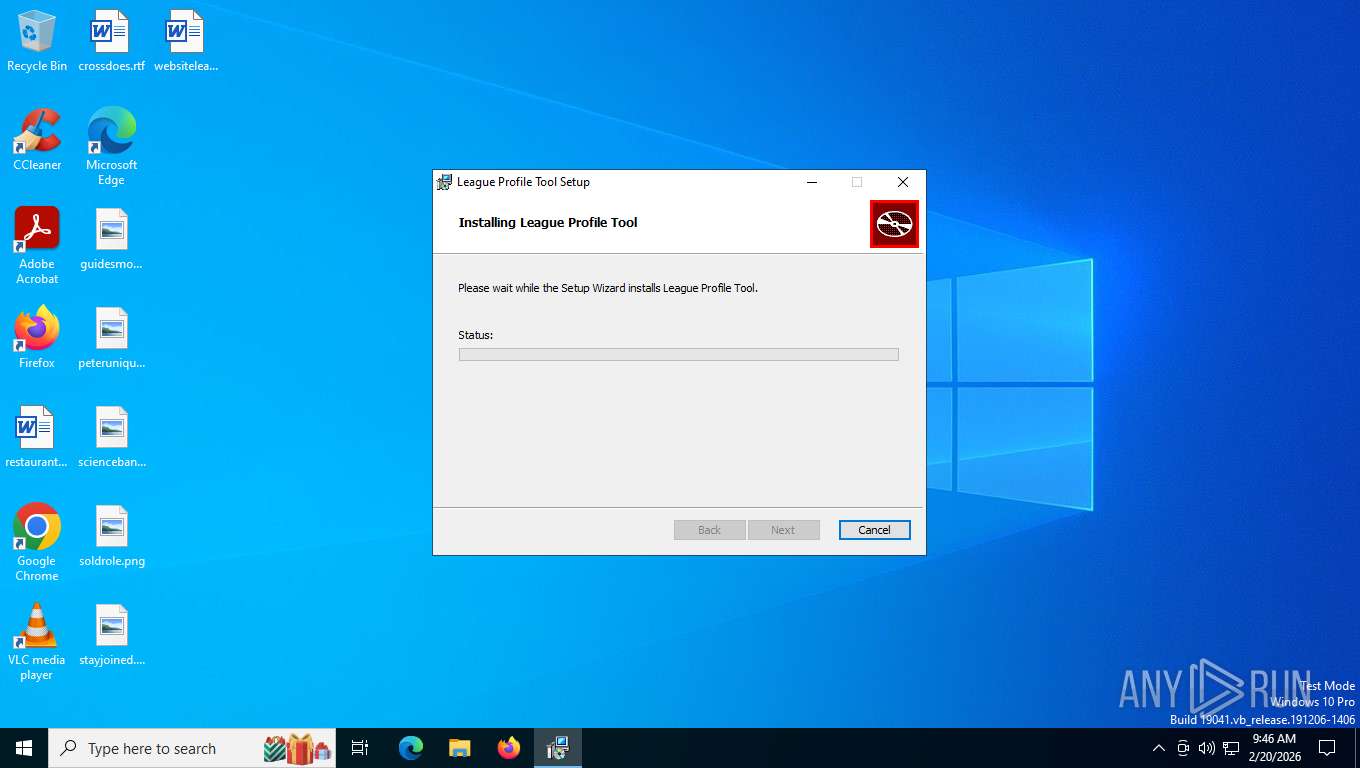
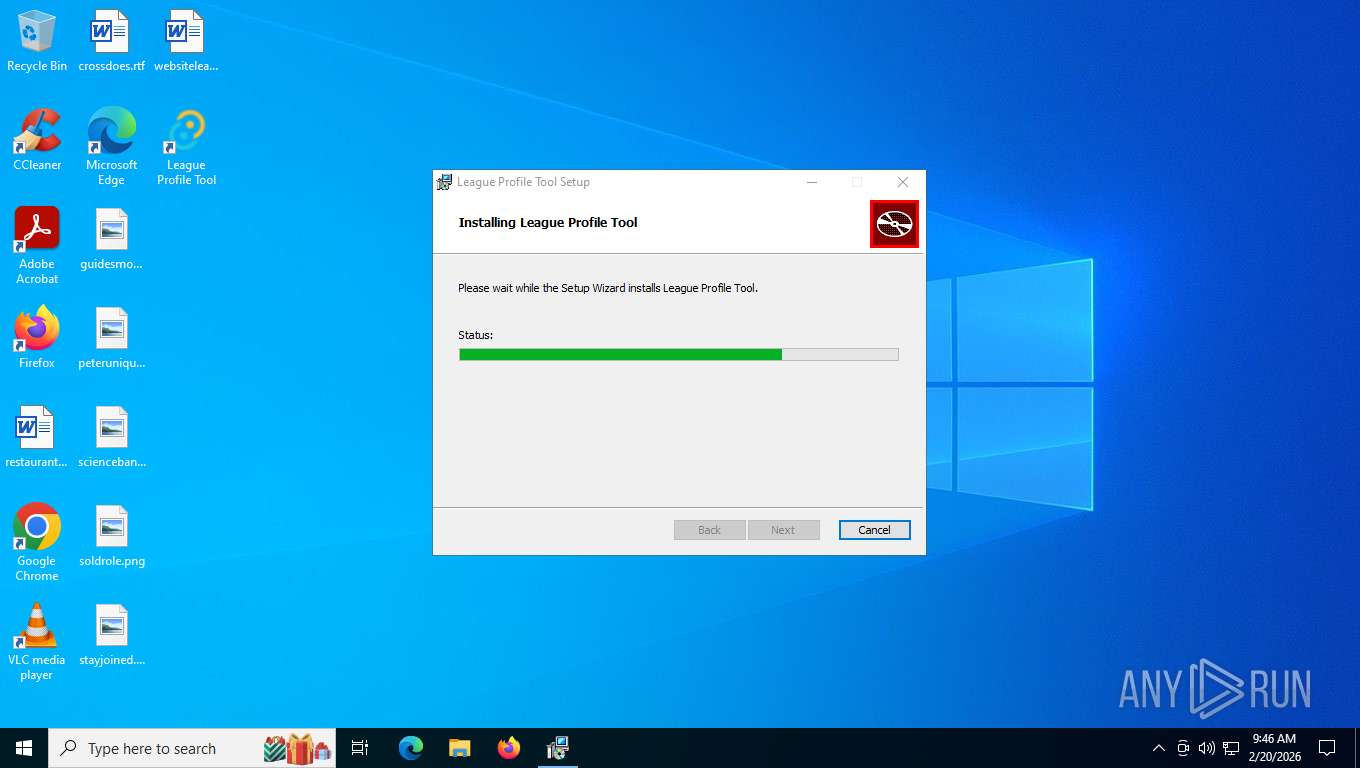
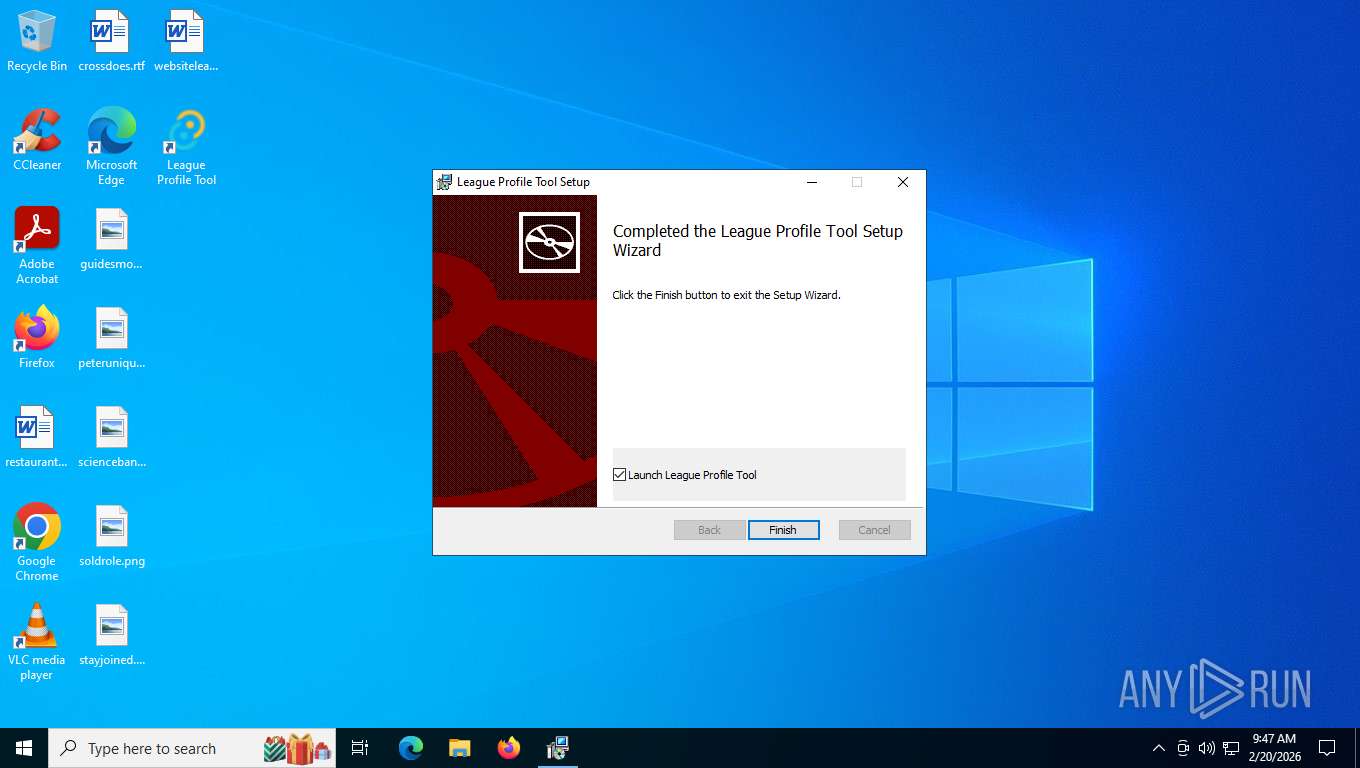
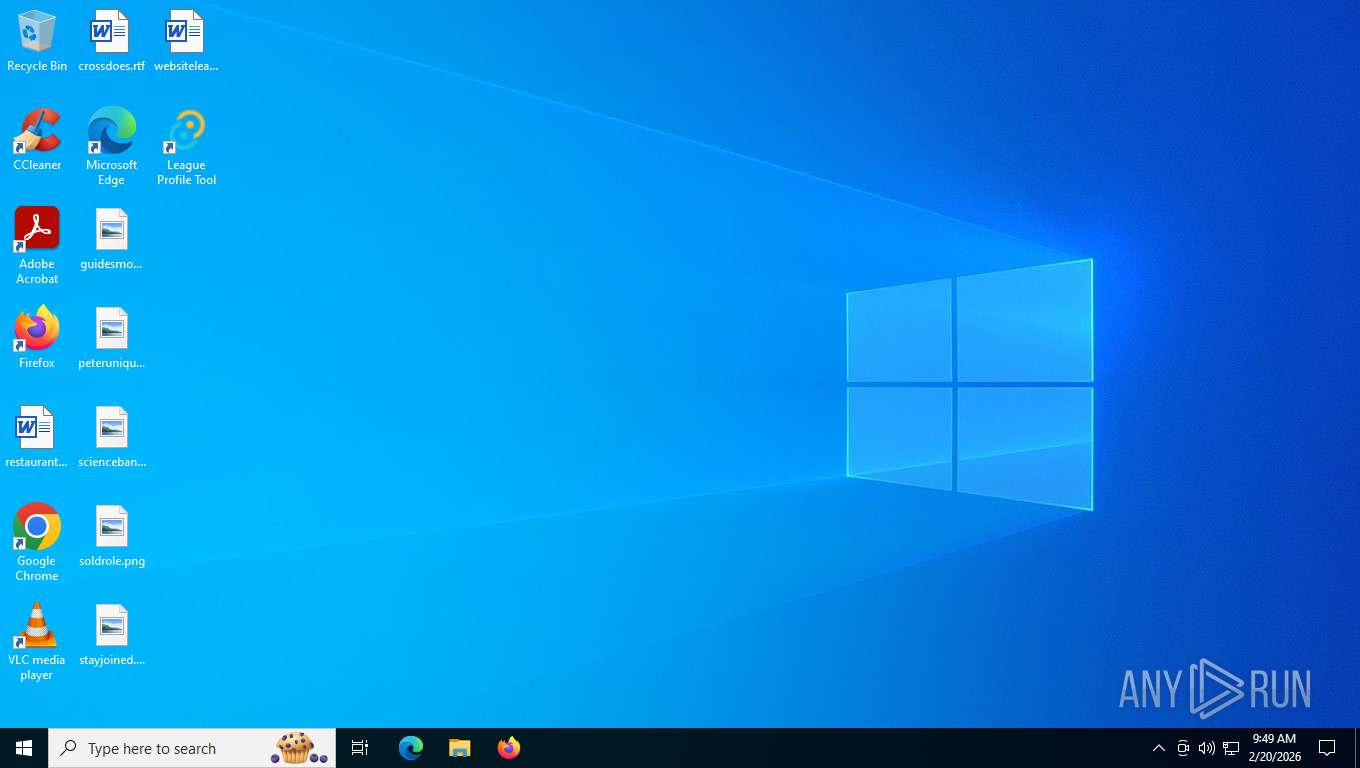
| File name: | League.Profile.Tool_1.3.7_x64_en-US.msi |
| Full analysis: | https://app.any.run/tasks/e5d3e24b-afa1-4e28-abf7-022e4ae2fc45 |
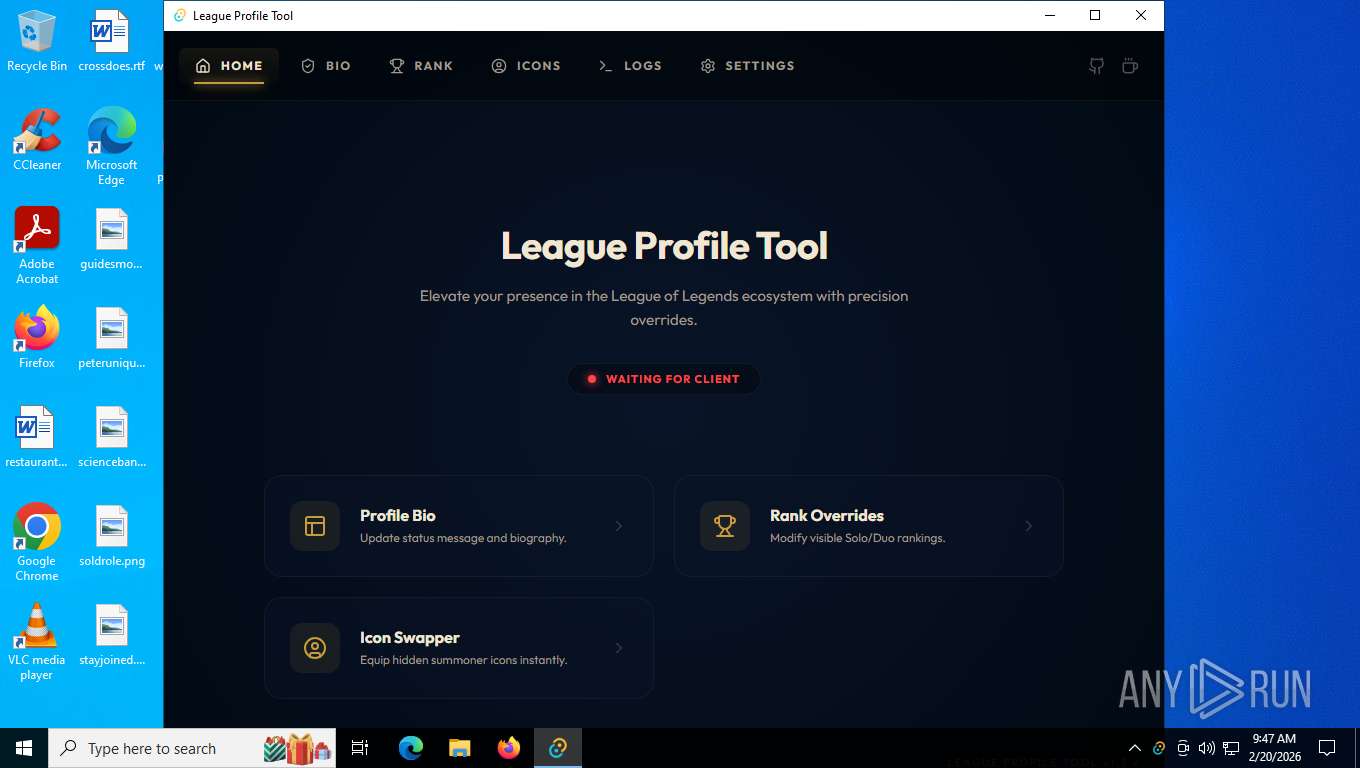
| Verdict: | Malicious activity |
| Analysis date: | February 20, 2026, 14:46:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: League Profile Tool, Author: leenny, Keywords: Installer, Comments: This installer database contains the logic and data required to install League Profile Tool., Template: x64;0, Revision Number: {B1006C4D-F4A5-4E26-AFC5-F43006EBBA35}, Create Time/Date: Thu Feb 19 19:57:20 2026, Last Saved Time/Date: Thu Feb 19 19:57:20 2026, Number of Pages: 450, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.14.1.8722), Security: 2 |
| MD5: | 835B7618F8FCB8AE4FC47D4F75725549 |
| SHA1: | CDB3E2D83E51E6E6290F35EDFA401205441DE246 |
| SHA256: | 38028F265C9E85AFF0015189C3E0853DE9BDEEA47EDCEDF297AA68FEAC36C7B7 |
| SSDEEP: | 98304:TWr9jyhc5JT3g6EkjWtU2J75FvGPB4hXNRjspUUBdoZlJxBf5i48CGJCdGfnrJlk:WtO66Om |
MALICIOUS
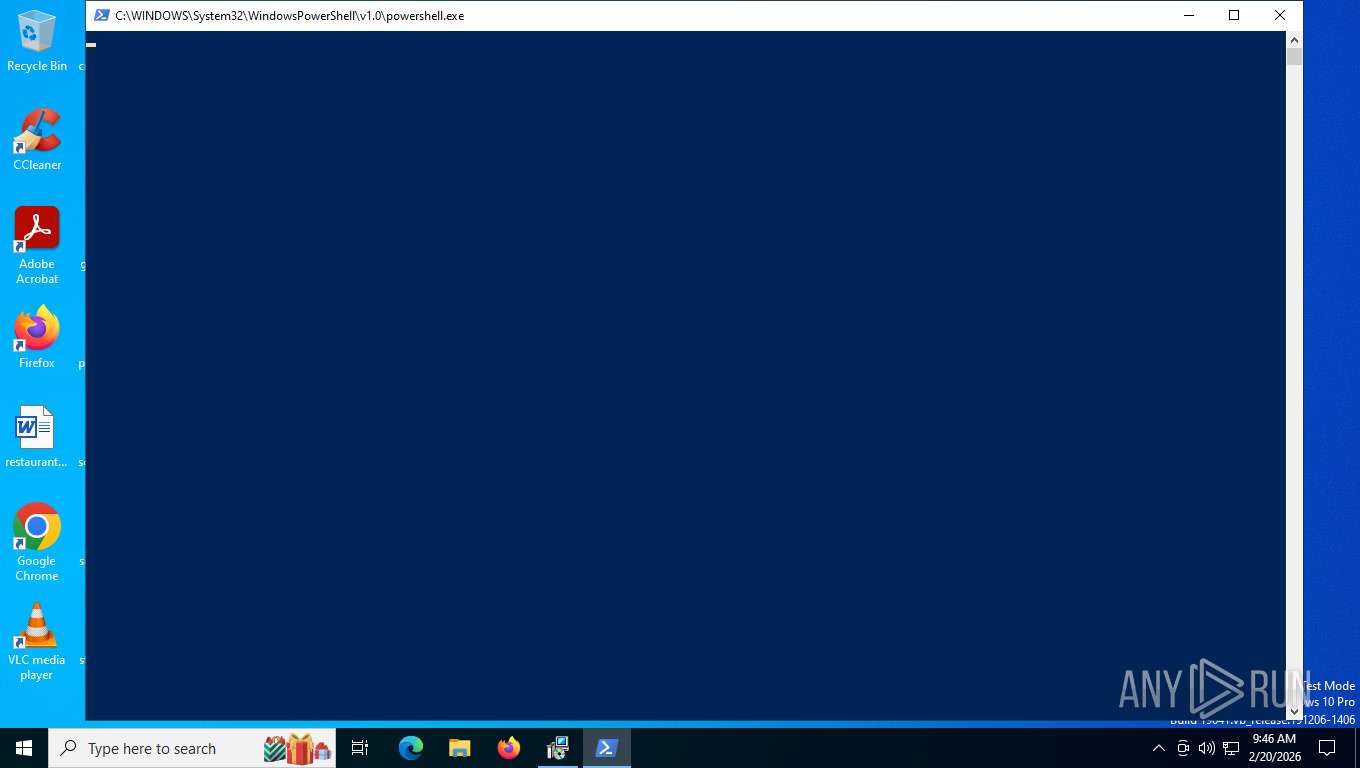
Run PowerShell with an invisible window
- powershell.exe (PID: 4952)
Changes the autorun value in the registry
- MicrosoftEdgeUpdate.exe (PID: 7620)
Potential DLL hijacking behavior detected
- msedgewebview2.exe (PID: 2900)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 7164)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 5204)
Starts process via Powershell
- powershell.exe (PID: 4952)
Manipulates environment variables
- powershell.exe (PID: 4952)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 5204)
Downloads file from URI via Powershell
- powershell.exe (PID: 4952)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 4952)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 7416)
- MicrosoftEdgeUpdate.exe (PID: 7620)
Executable content was dropped or overwritten
- MicrosoftEdgeWebview2Setup.exe (PID: 7416)
- MicrosoftEdgeUpdate.exe (PID: 7620)
- powershell.exe (PID: 4952)
- MicrosoftEdge_X64_145.0.3800.65.exe (PID: 9152)
- setup.exe (PID: 1948)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 7620)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8628)
- MicrosoftEdgeUpdate.exe (PID: 5580)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2232)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8160)
Application launched itself
- setup.exe (PID: 1948)
- MicrosoftEdgeUpdate.exe (PID: 7396)
- msedgewebview2.exe (PID: 4332)
Searches for installed software
- setup.exe (PID: 1948)
INFO
Reads the computer name
- msiexec.exe (PID: 5204)
- msiexec.exe (PID: 7376)
- MicrosoftEdgeUpdate.exe (PID: 7620)
- MicrosoftEdgeUpdate.exe (PID: 5580)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8628)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8160)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2232)
- MicrosoftEdgeUpdate.exe (PID: 5796)
- MicrosoftEdgeUpdate.exe (PID: 7396)
- MicrosoftEdgeUpdate.exe (PID: 7948)
- MicrosoftEdge_X64_145.0.3800.65.exe (PID: 9152)
- setup.exe (PID: 1948)
- league-profile-tool.exe (PID: 6500)
- msedgewebview2.exe (PID: 4332)
- msedgewebview2.exe (PID: 2364)
- msedgewebview2.exe (PID: 2900)
- MicrosoftEdgeUpdate.exe (PID: 5440)
An automatically generated document
- msiexec.exe (PID: 4712)
Checks supported languages
- msiexec.exe (PID: 7376)
- msiexec.exe (PID: 5204)
- MicrosoftEdgeUpdate.exe (PID: 5580)
- MicrosoftEdgeUpdate.exe (PID: 7620)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8628)
- MicrosoftEdgeWebview2Setup.exe (PID: 7416)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 8160)
- MicrosoftEdgeUpdate.exe (PID: 5796)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 2232)
- MicrosoftEdgeUpdate.exe (PID: 7948)
- MicrosoftEdgeUpdate.exe (PID: 7396)
- MicrosoftEdge_X64_145.0.3800.65.exe (PID: 9152)
- setup.exe (PID: 2096)
- MicrosoftEdgeUpdate.exe (PID: 5440)
- league-profile-tool.exe (PID: 6500)
- msedgewebview2.exe (PID: 4332)
- msedgewebview2.exe (PID: 7924)
- msedgewebview2.exe (PID: 2364)
- msedgewebview2.exe (PID: 2900)
- msedgewebview2.exe (PID: 488)
- setup.exe (PID: 1948)
- msedgewebview2.exe (PID: 2764)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4712)
- msiexec.exe (PID: 5204)
Manages system restore points
- SrTasks.exe (PID: 2480)
Disables trace logs
- powershell.exe (PID: 4952)
Drops script file
- powershell.exe (PID: 4952)
- setup.exe (PID: 1948)
Checks proxy server information
- powershell.exe (PID: 4952)
- MicrosoftEdgeUpdate.exe (PID: 5796)
- MicrosoftEdgeUpdate.exe (PID: 7396)
- MicrosoftEdgeUpdate.exe (PID: 5440)
- msedgewebview2.exe (PID: 4332)
- slui.exe (PID: 2684)
The sample compiled with english language support
- MicrosoftEdgeWebview2Setup.exe (PID: 7416)
- MicrosoftEdgeUpdate.exe (PID: 7620)
- MicrosoftEdge_X64_145.0.3800.65.exe (PID: 9152)
- powershell.exe (PID: 4952)
- setup.exe (PID: 1948)
Create files in a temporary directory
- MicrosoftEdgeWebview2Setup.exe (PID: 7416)
- msedgewebview2.exe (PID: 4332)
Creates files or folders in the user directory
- MicrosoftEdgeUpdate.exe (PID: 7620)
- MicrosoftEdgeUpdate.exe (PID: 7396)
- MicrosoftEdge_X64_145.0.3800.65.exe (PID: 9152)
- setup.exe (PID: 1948)
- league-profile-tool.exe (PID: 6500)
- msedgewebview2.exe (PID: 4332)
- msedgewebview2.exe (PID: 7924)
- setup.exe (PID: 2096)
- msedgewebview2.exe (PID: 2364)
- mmc.exe (PID: 4760)
Launching a file from a Registry key
- MicrosoftEdgeUpdate.exe (PID: 7620)
The executable file from the user directory is run by the Powershell process
- MicrosoftEdgeWebview2Setup.exe (PID: 7416)
Reads security settings of Internet Explorer
- MicrosoftEdgeUpdate.exe (PID: 7620)
- MicrosoftEdgeUpdate.exe (PID: 7396)
- msedgewebview2.exe (PID: 4332)
- Taskmgr.exe (PID: 6612)
- mmc.exe (PID: 4760)
Reads Environment values
- MicrosoftEdgeUpdate.exe (PID: 5796)
- MicrosoftEdgeUpdate.exe (PID: 5440)
- msedgewebview2.exe (PID: 4332)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 7620)
- setup.exe (PID: 1948)
- msedgewebview2.exe (PID: 4332)
- msedgewebview2.exe (PID: 2764)
Reads the machine GUID from the registry
- MicrosoftEdgeUpdate.exe (PID: 7396)
- msedgewebview2.exe (PID: 4332)
Creates a software uninstall entry
- setup.exe (PID: 1948)
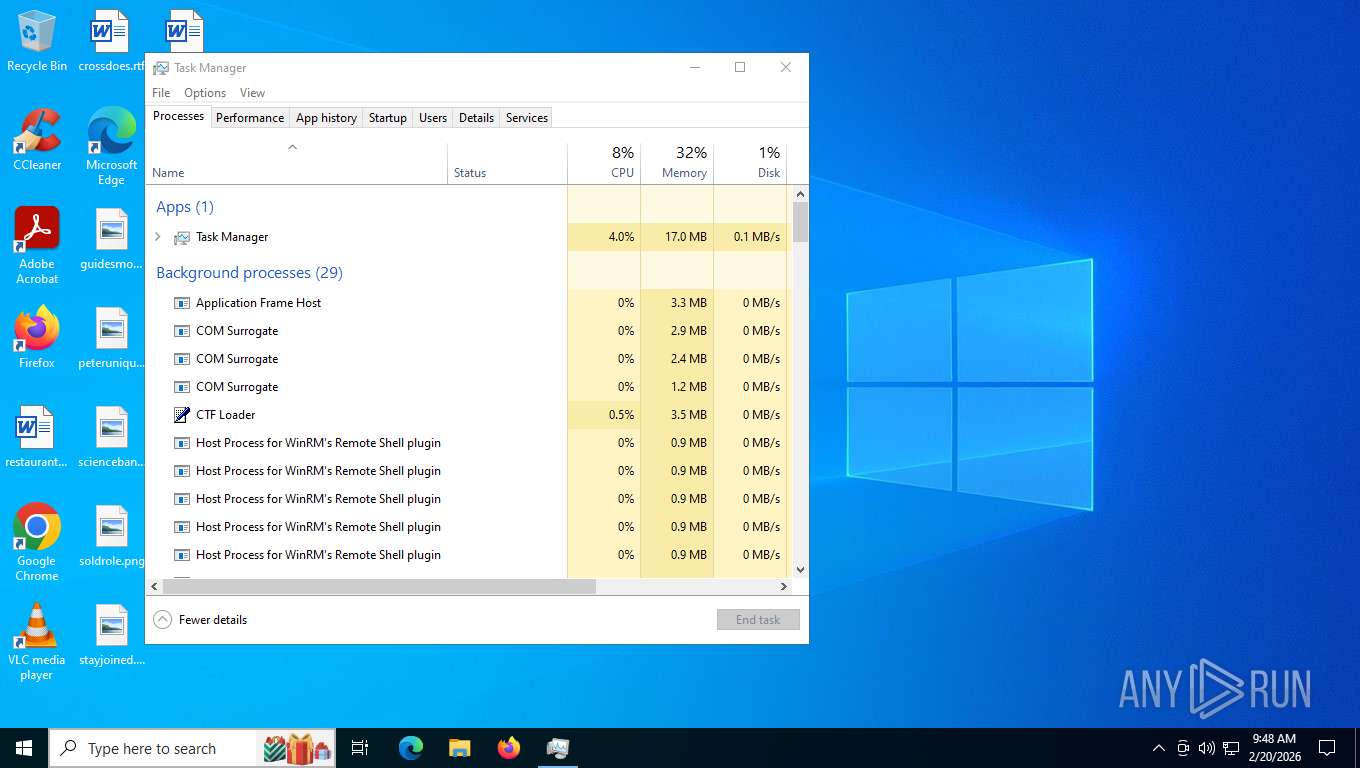
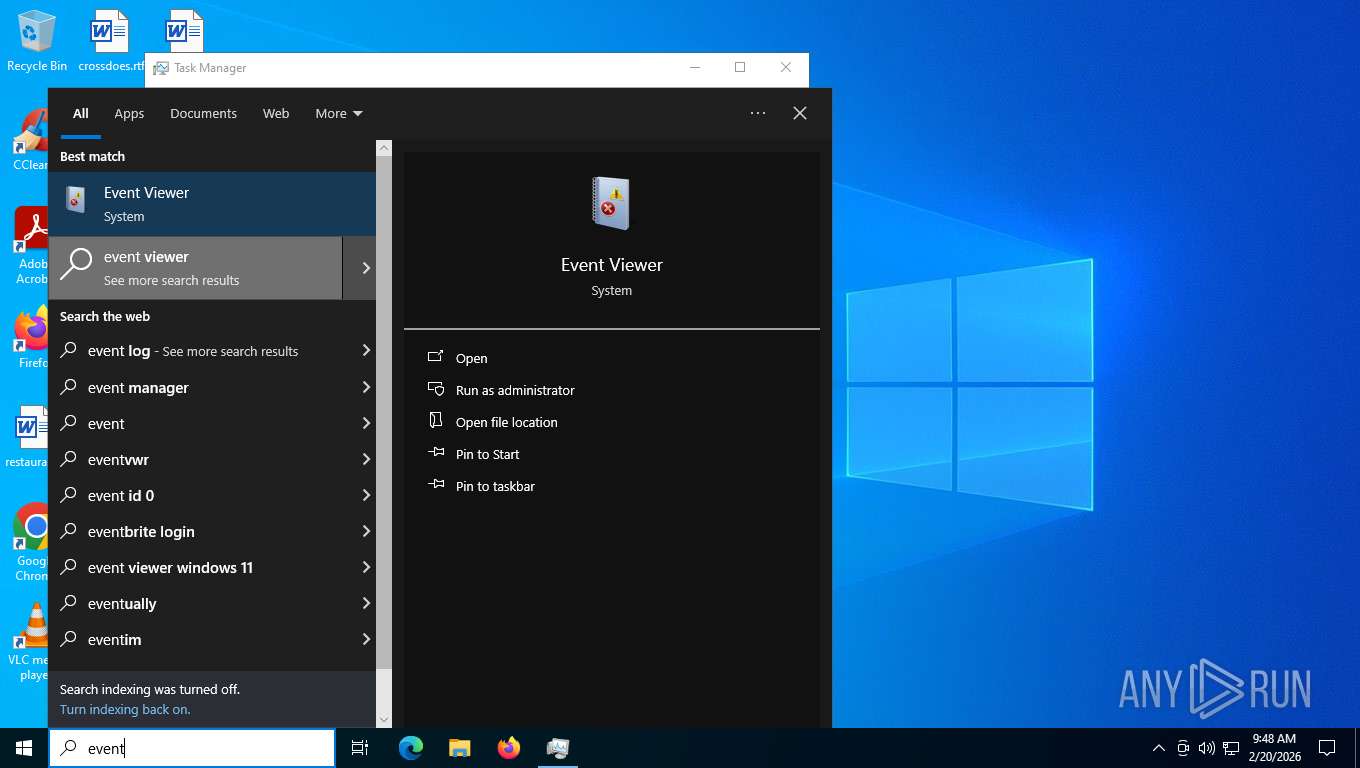
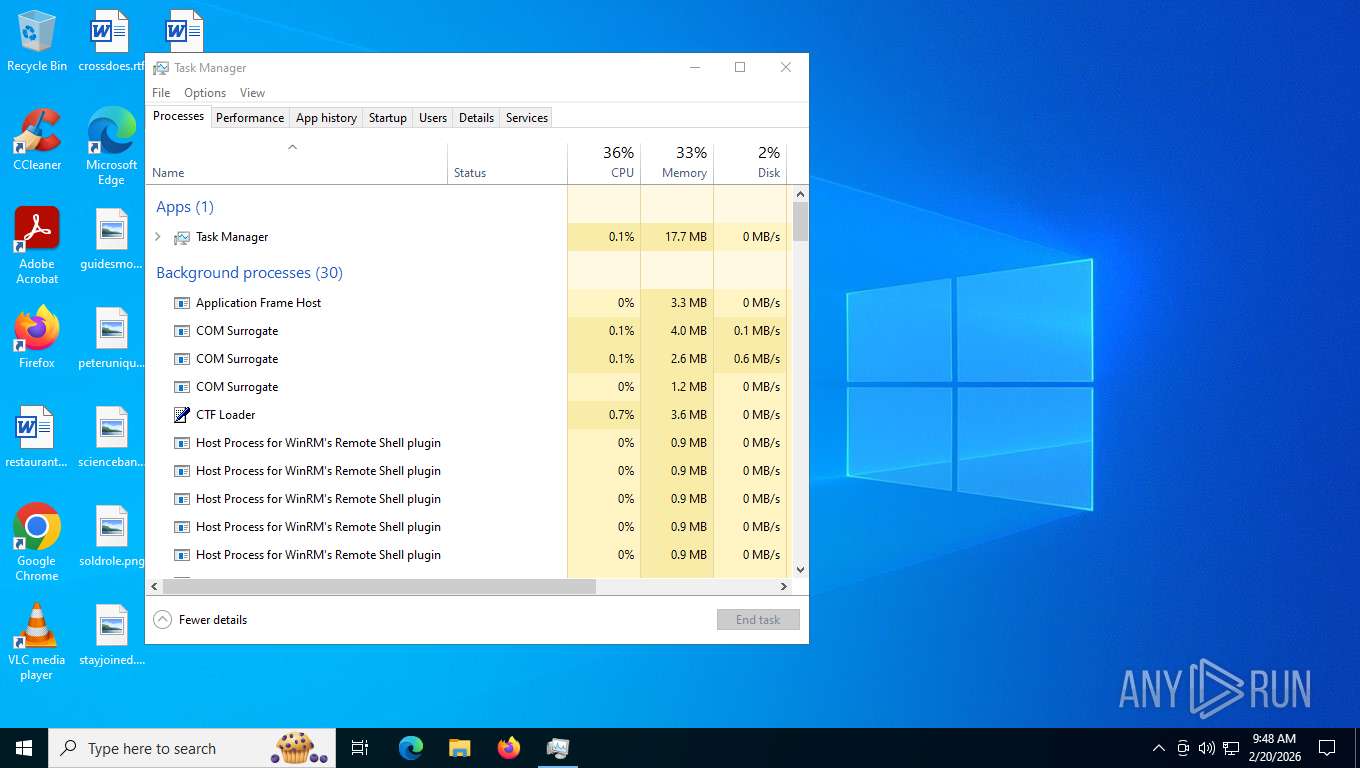
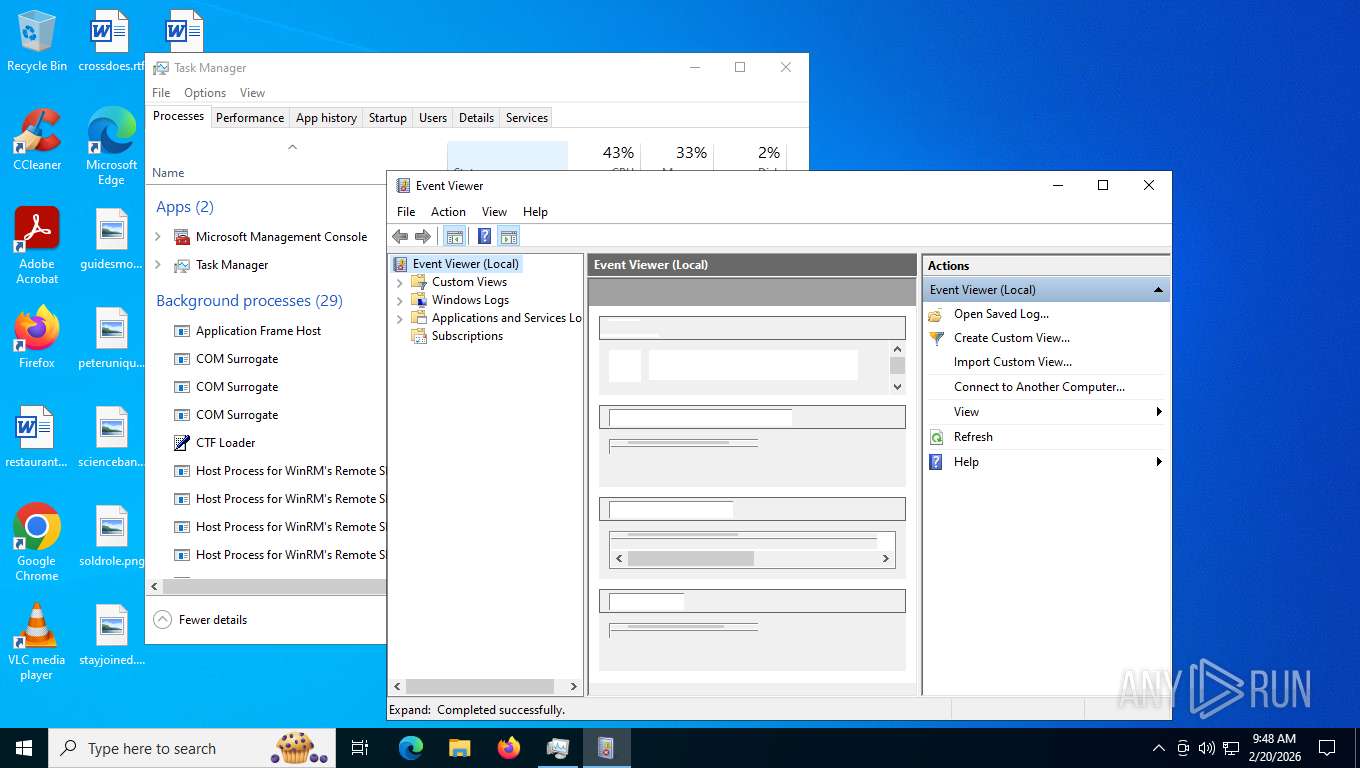
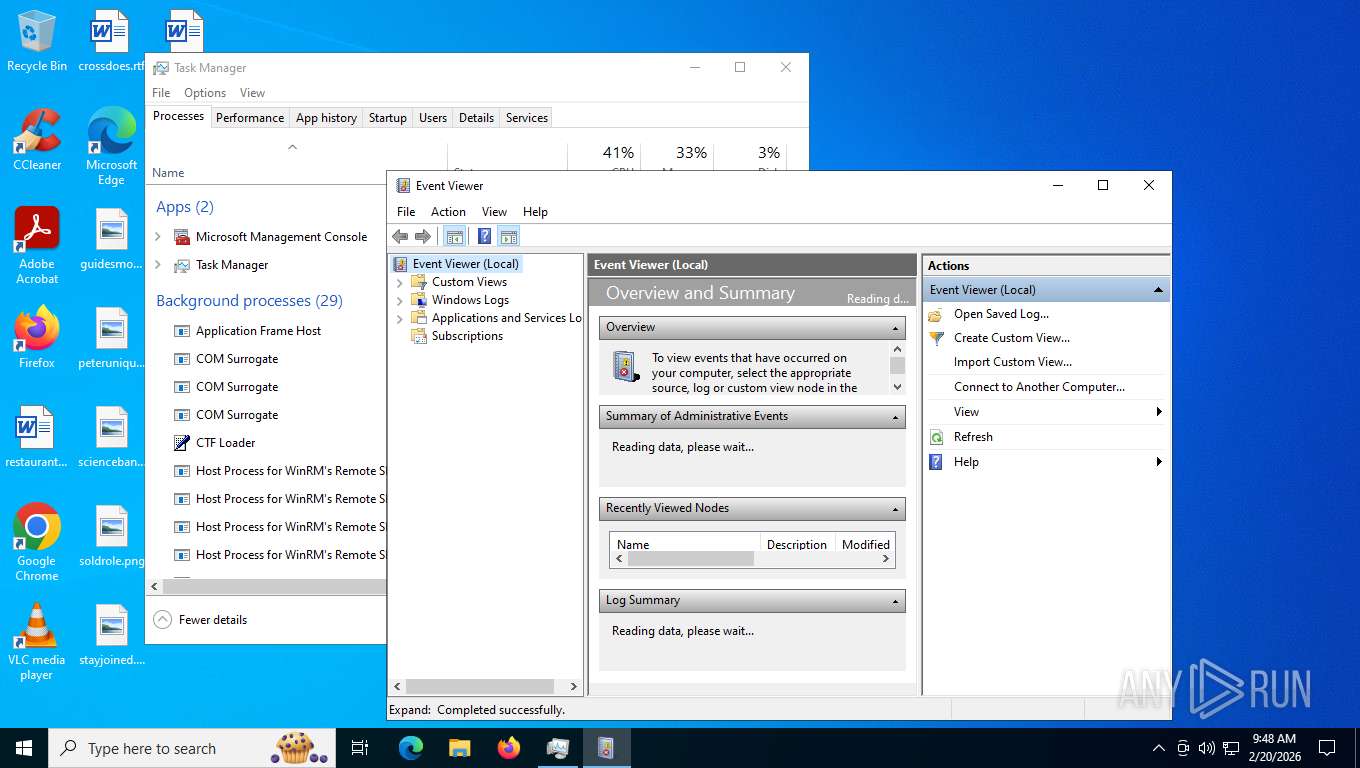
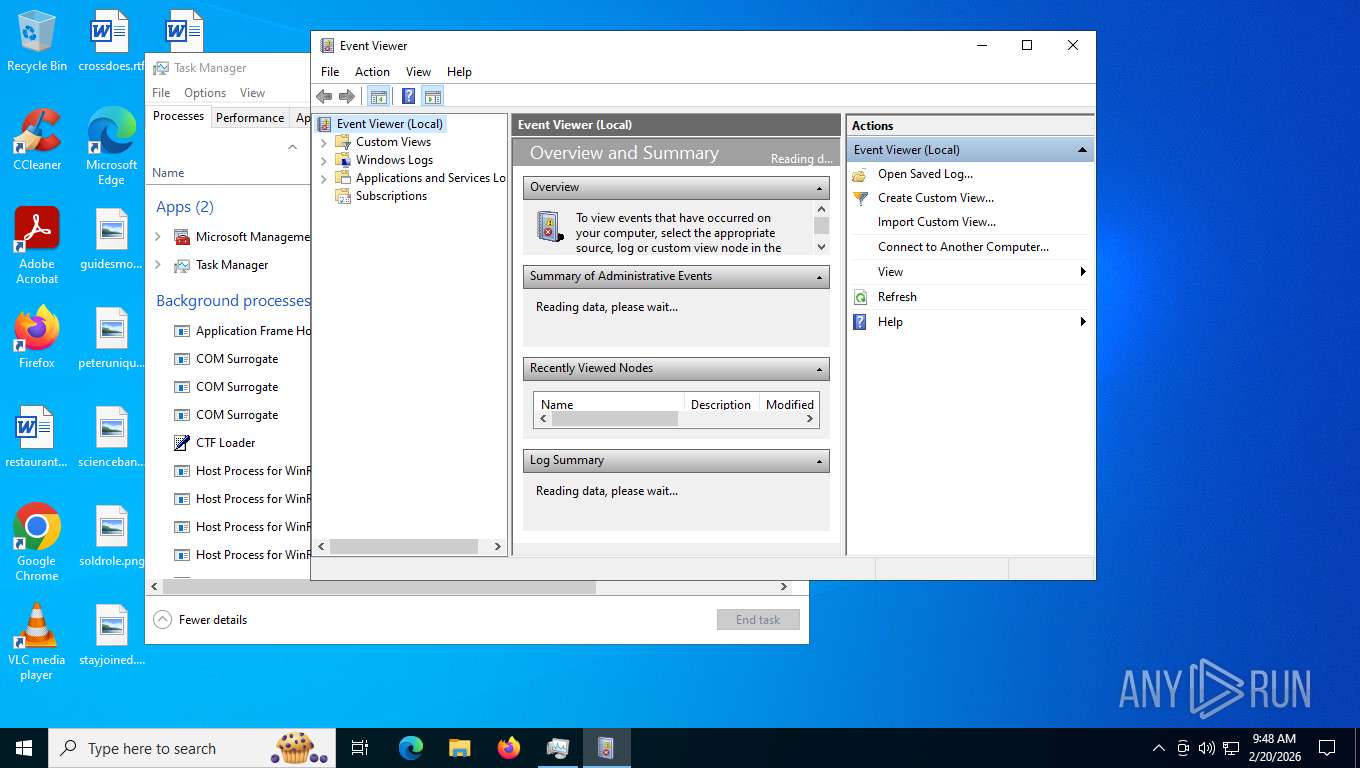
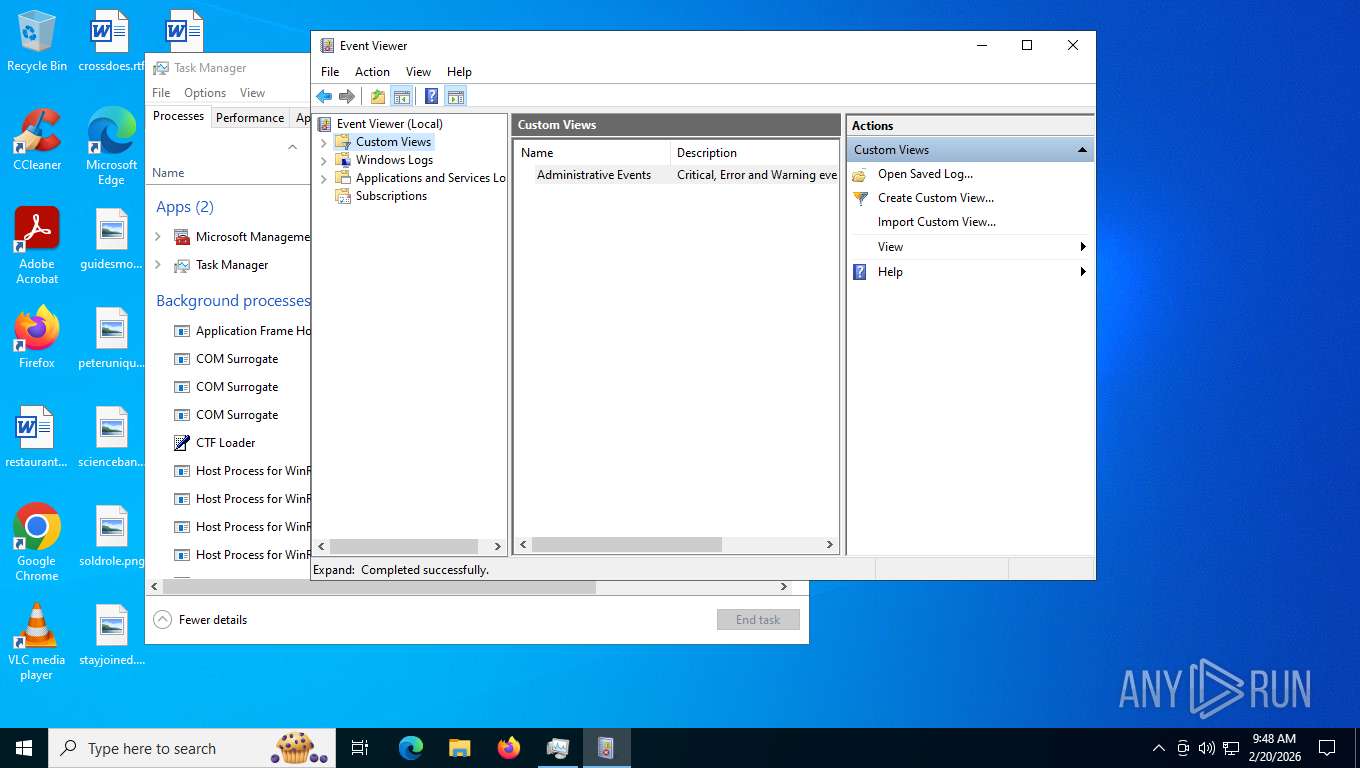
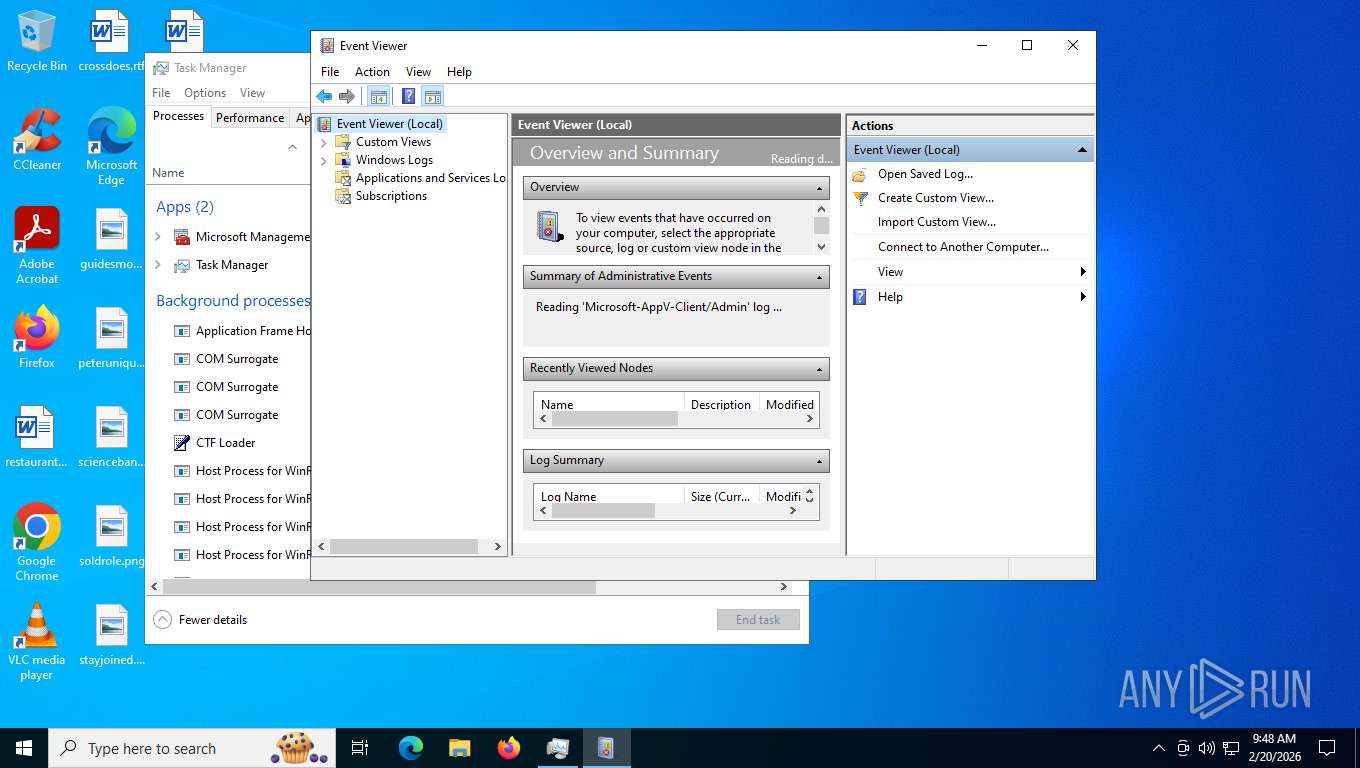
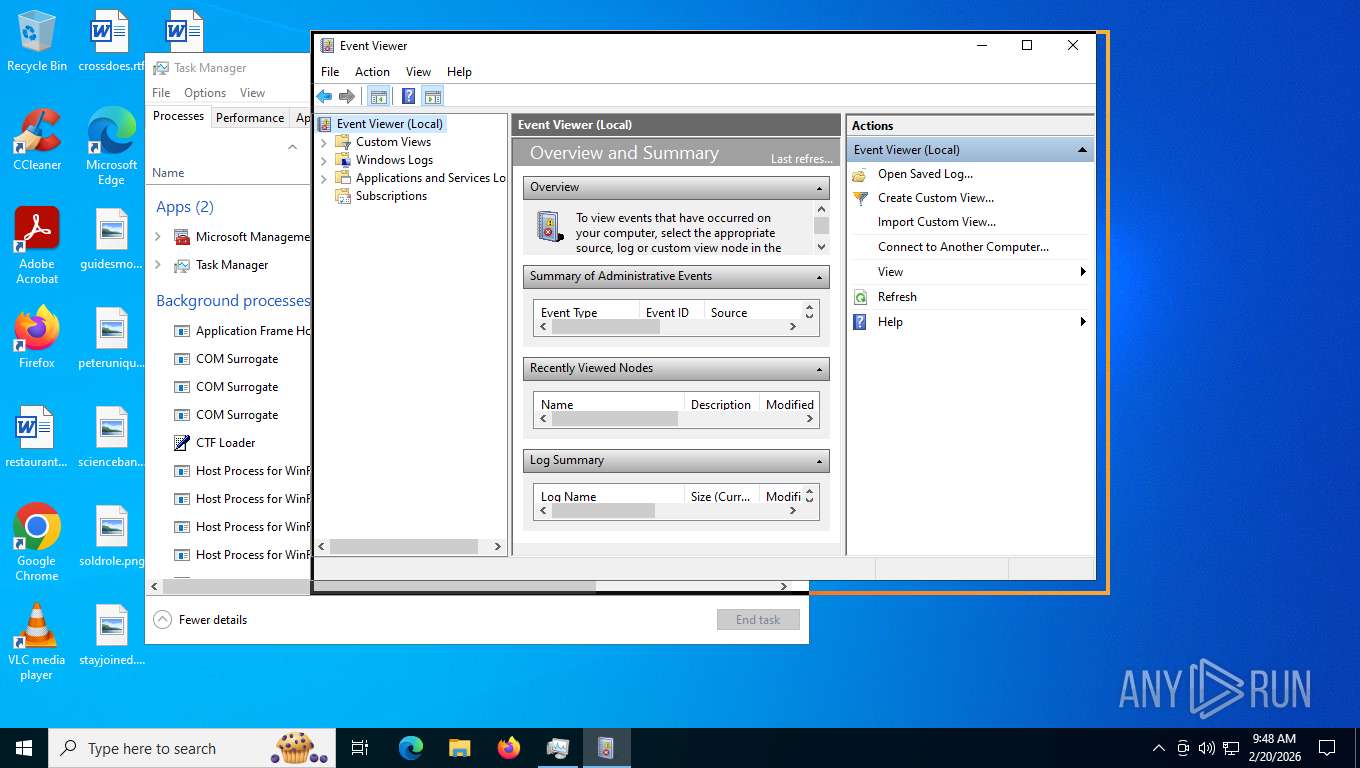
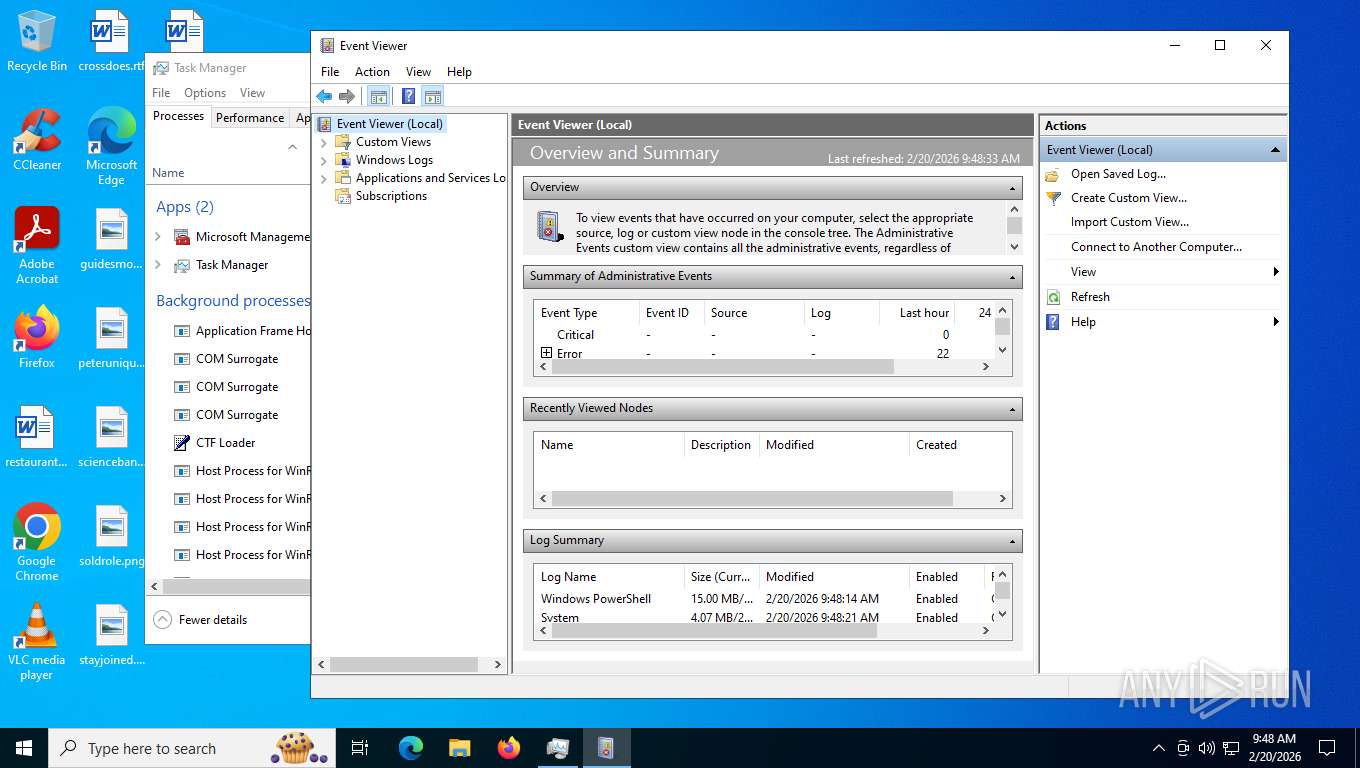
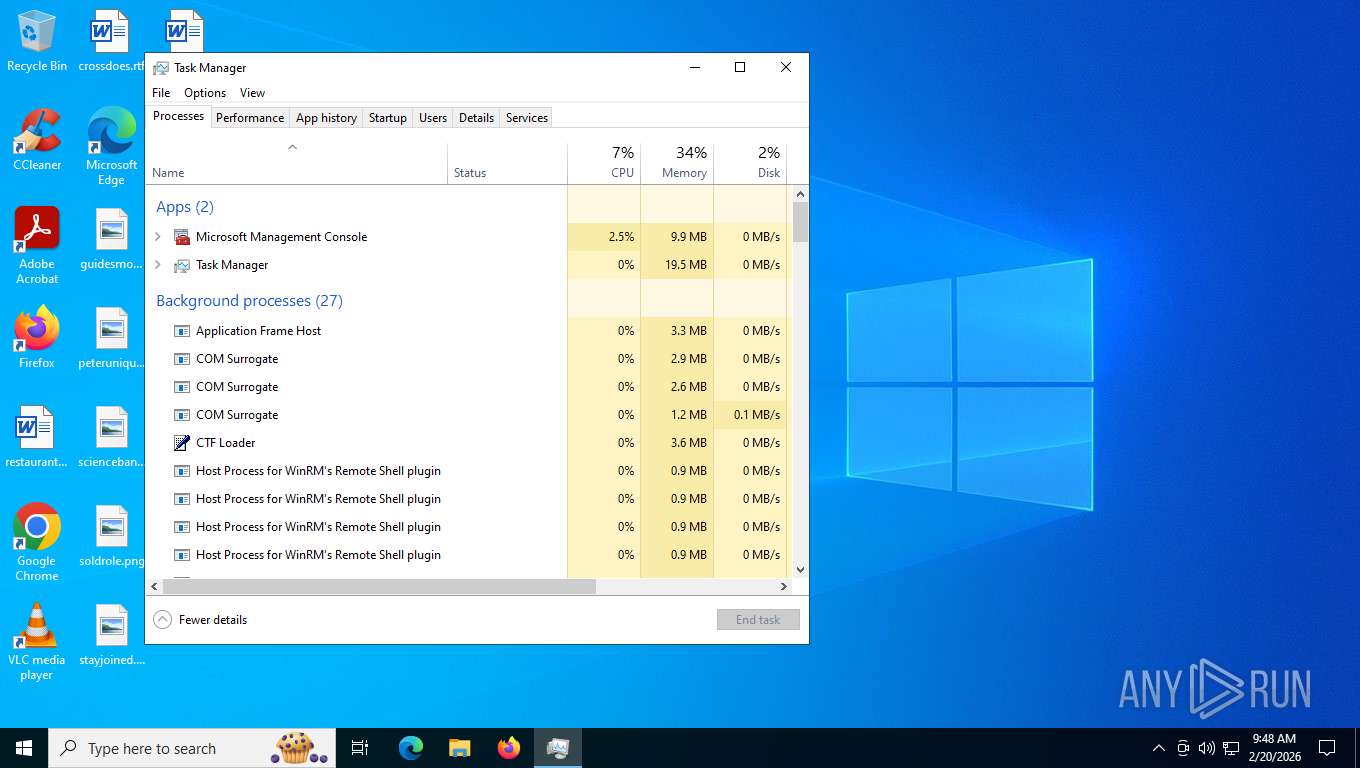
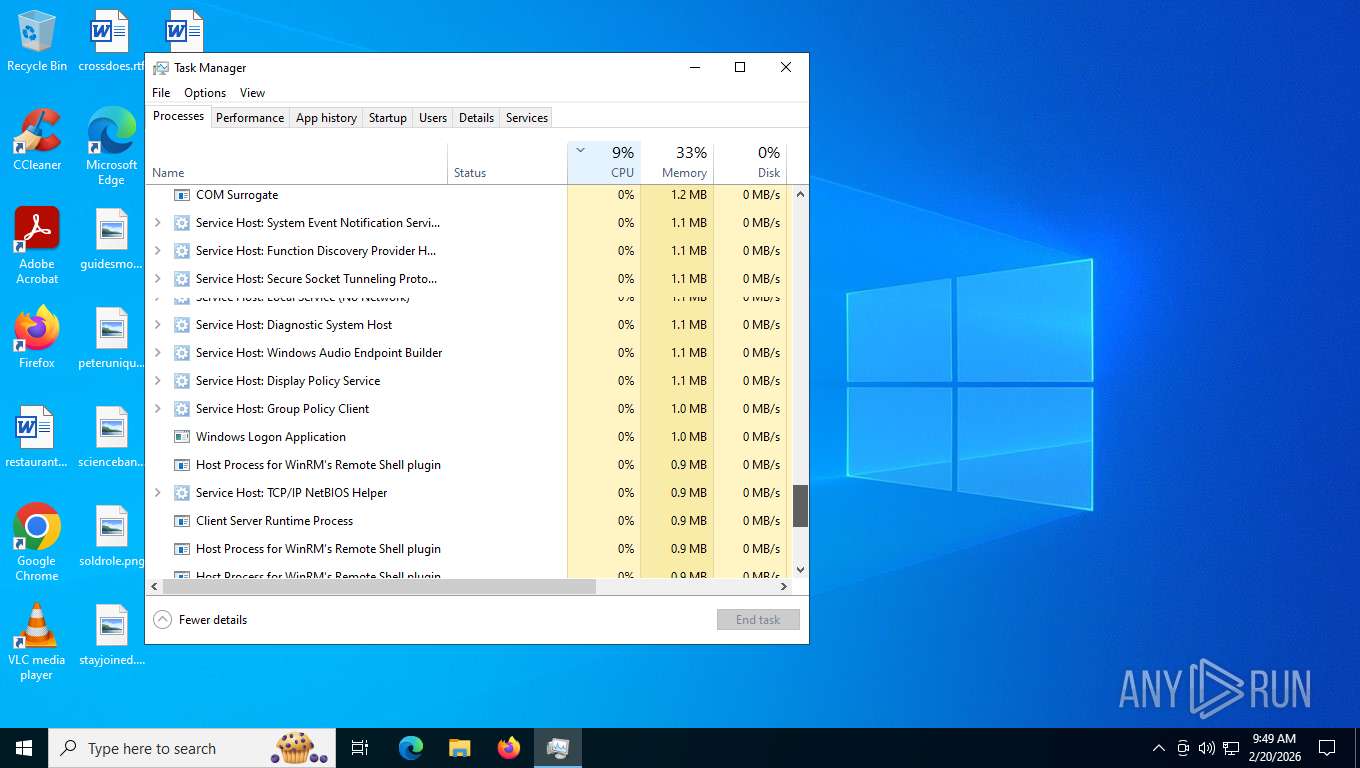
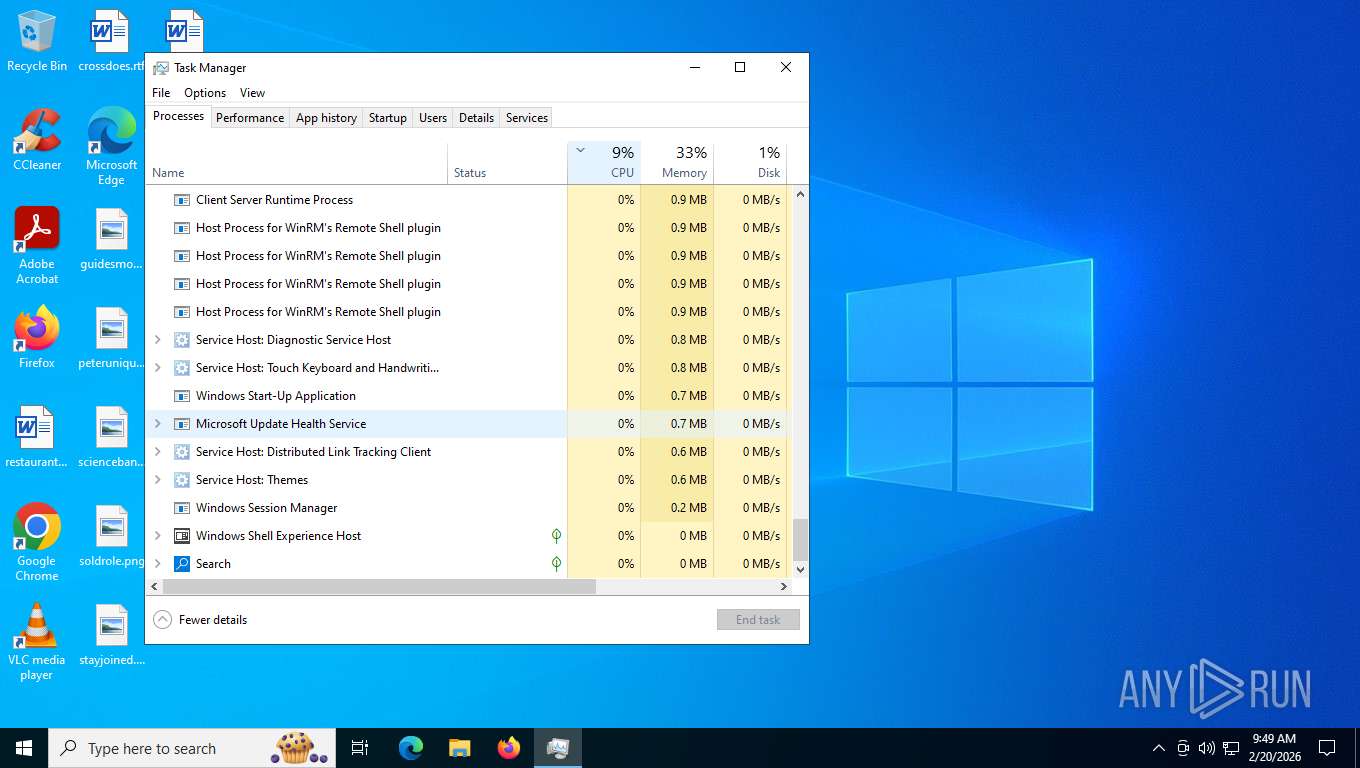
Manual execution by a user
- Taskmgr.exe (PID: 8624)
- mmc.exe (PID: 1612)
- mmc.exe (PID: 4760)
- Taskmgr.exe (PID: 6612)
Creates files in the program directory
- mmc.exe (PID: 4760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
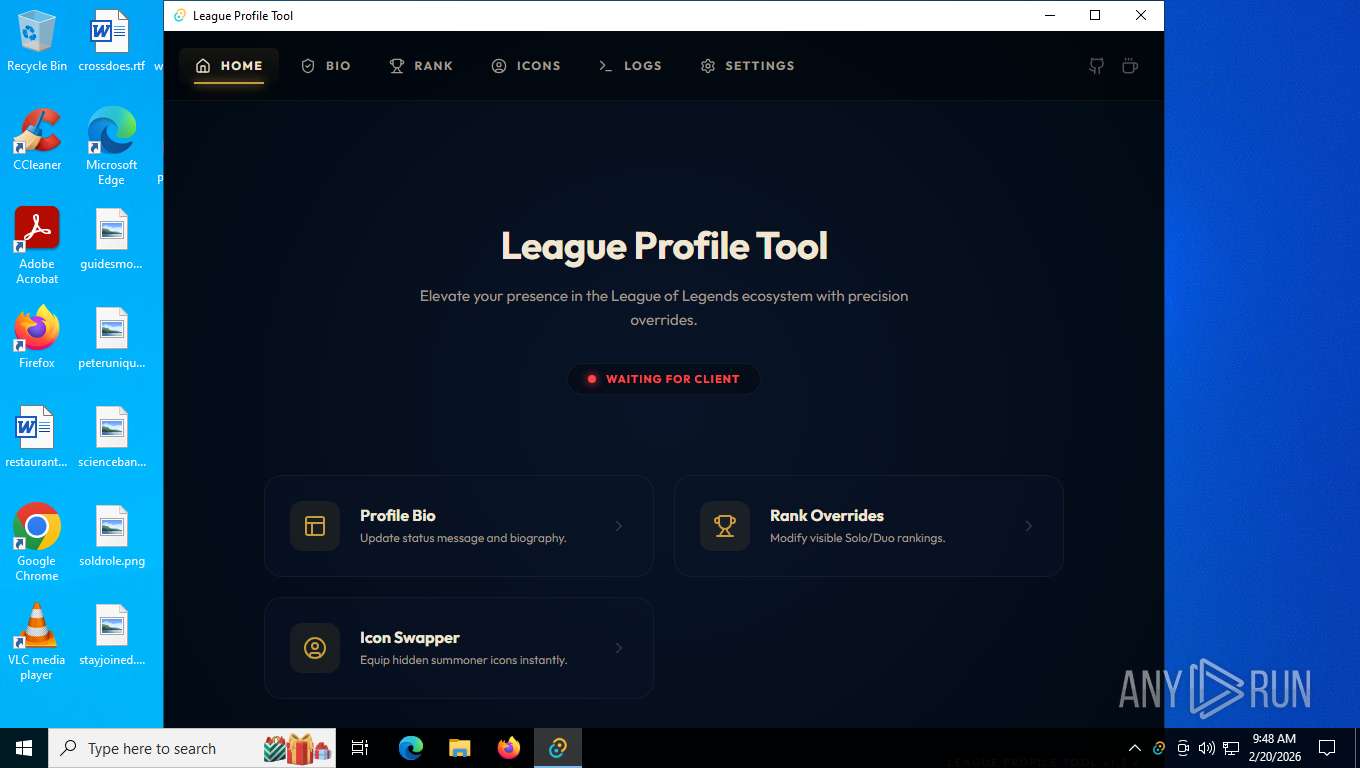
| Subject: | League Profile Tool |
| Author: | leenny |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install League Profile Tool. |
| Template: | x64;0 |
| RevisionNumber: | {B1006C4D-F4A5-4E26-AFC5-F43006EBBA35} |
| CreateDate: | 2026:02:19 19:57:20 |
| ModifyDate: | 2026:02:19 19:57:20 |
| Pages: | 450 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.14.1.8722) |
| Security: | Read-only recommended |
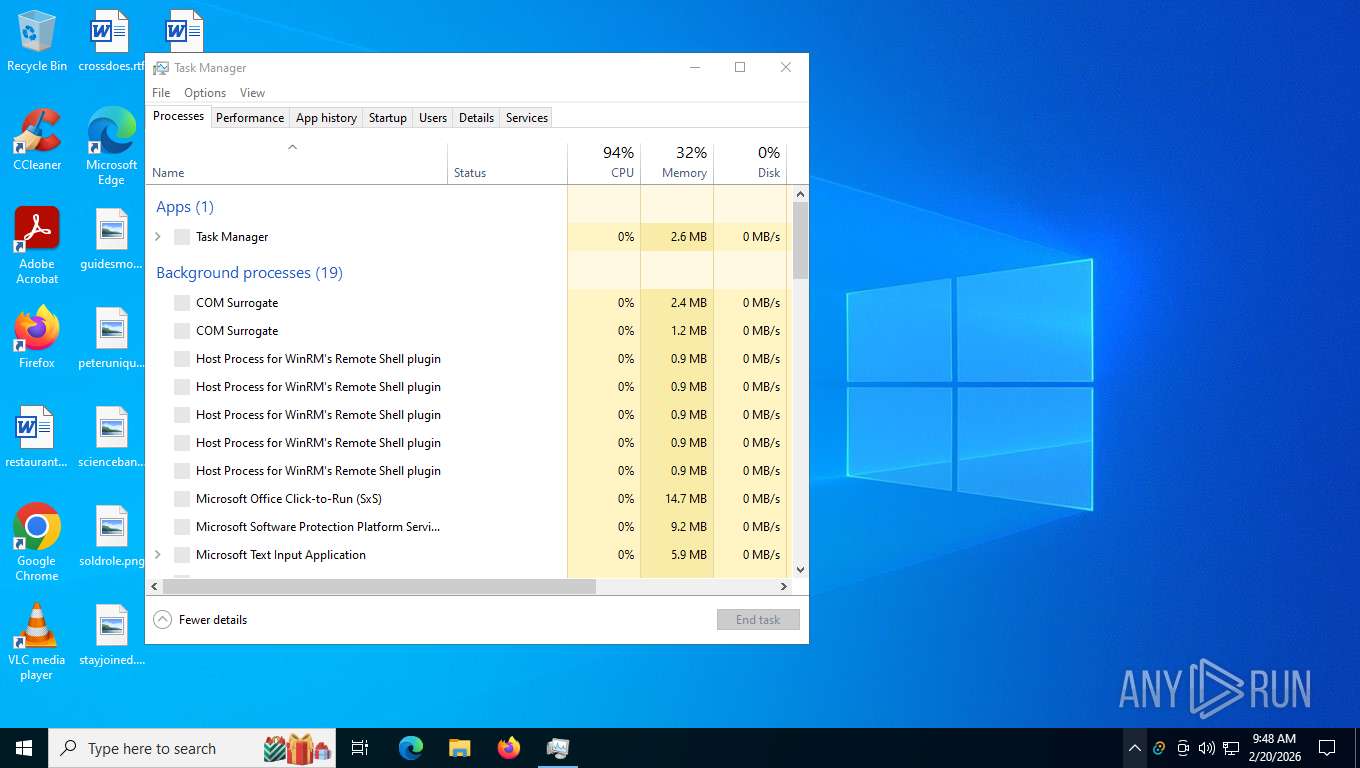
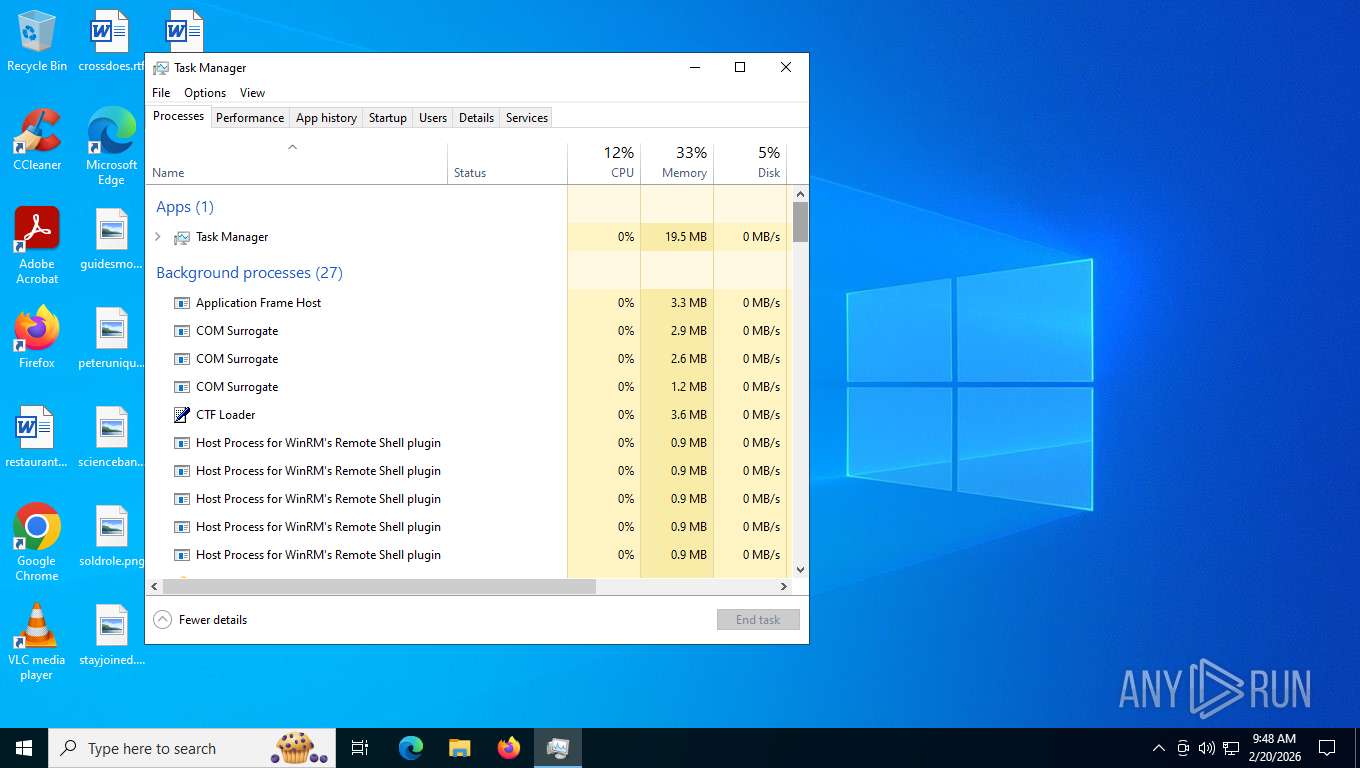
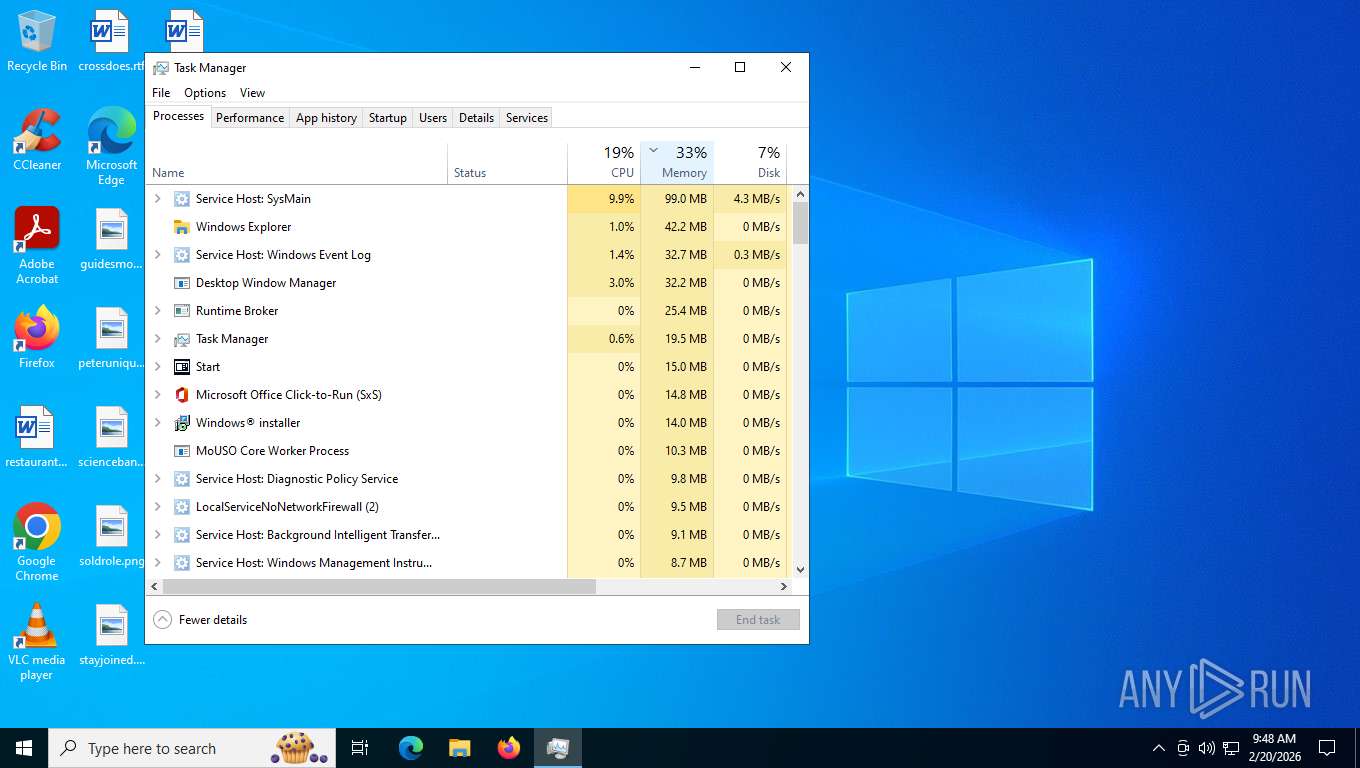
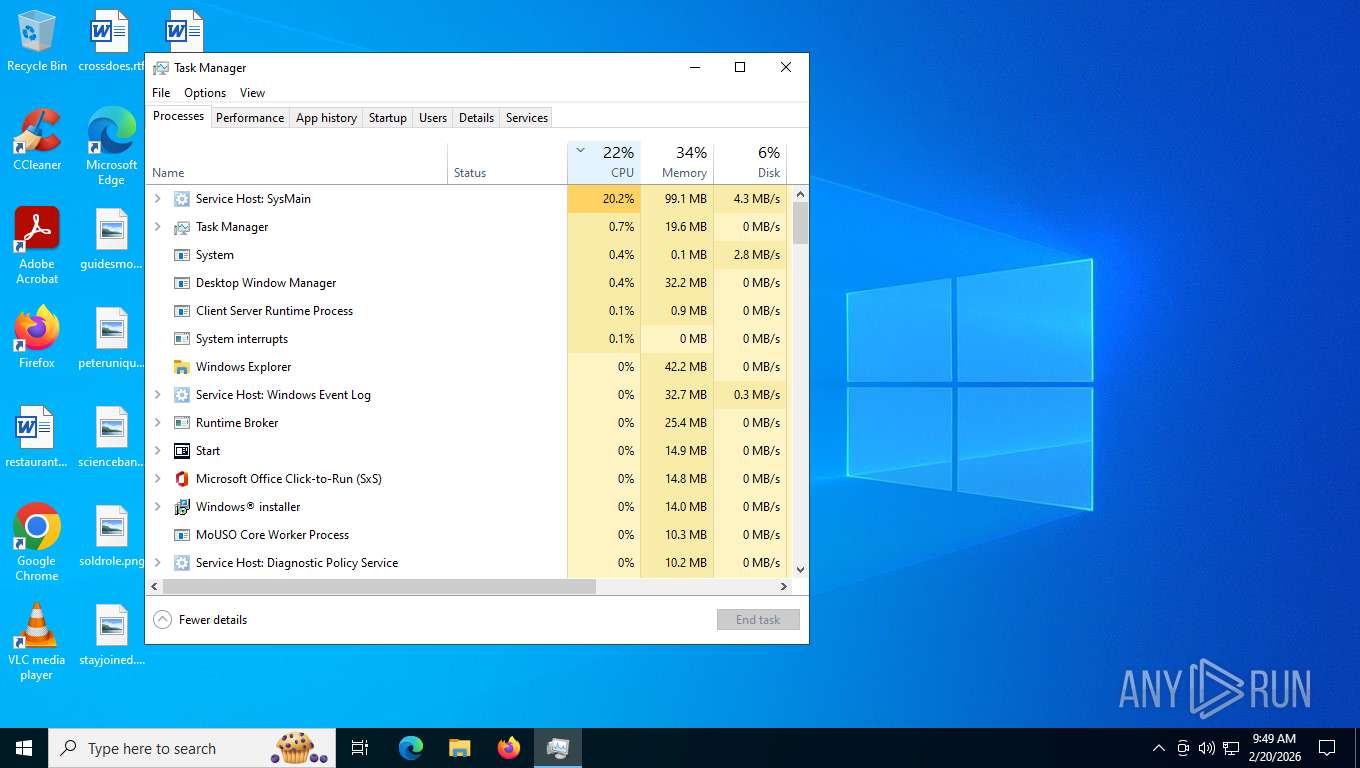
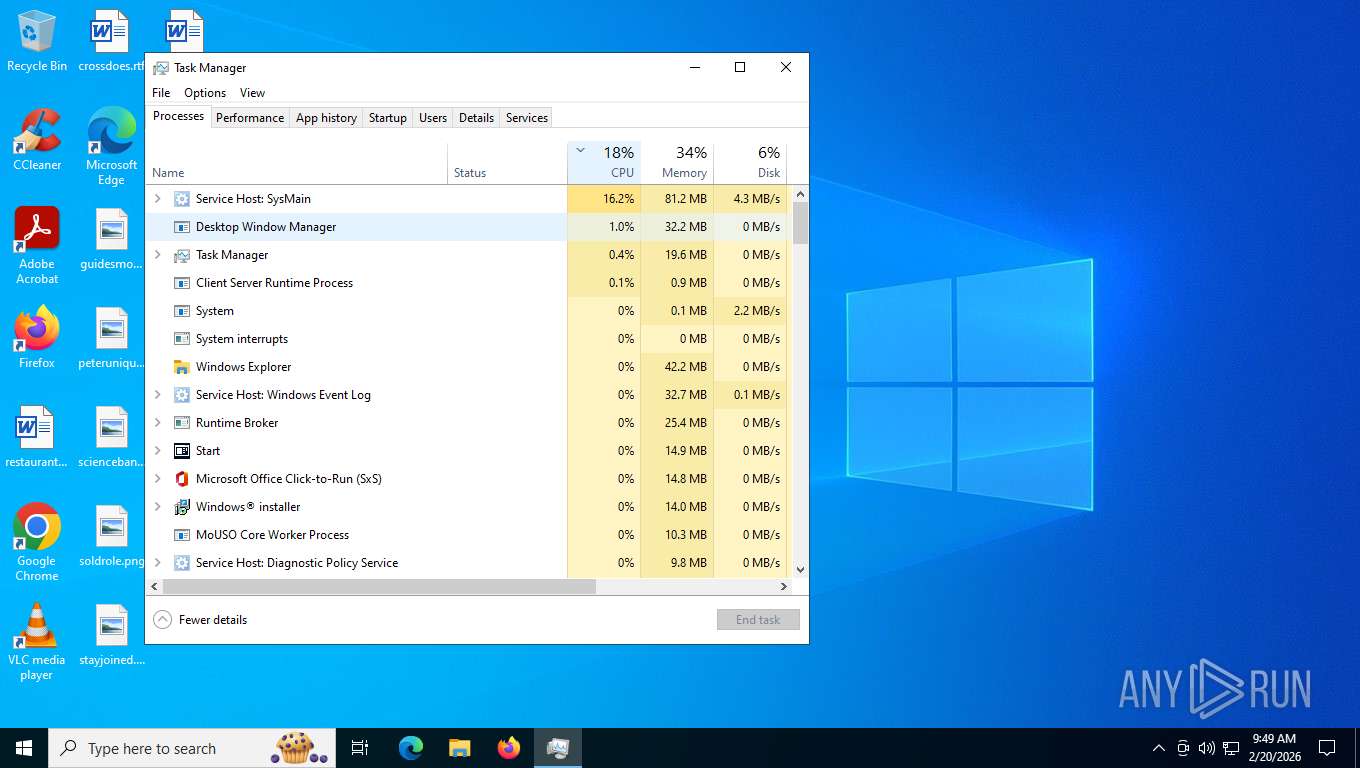
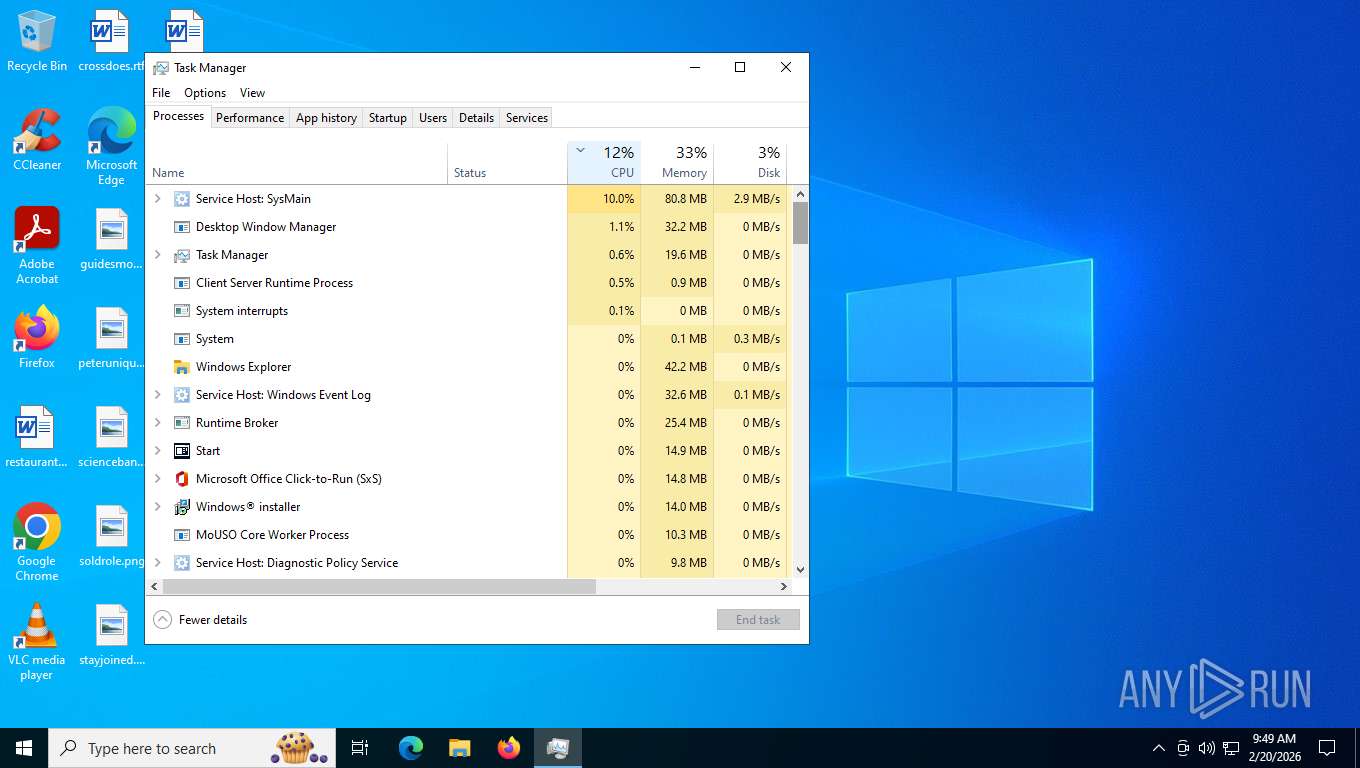
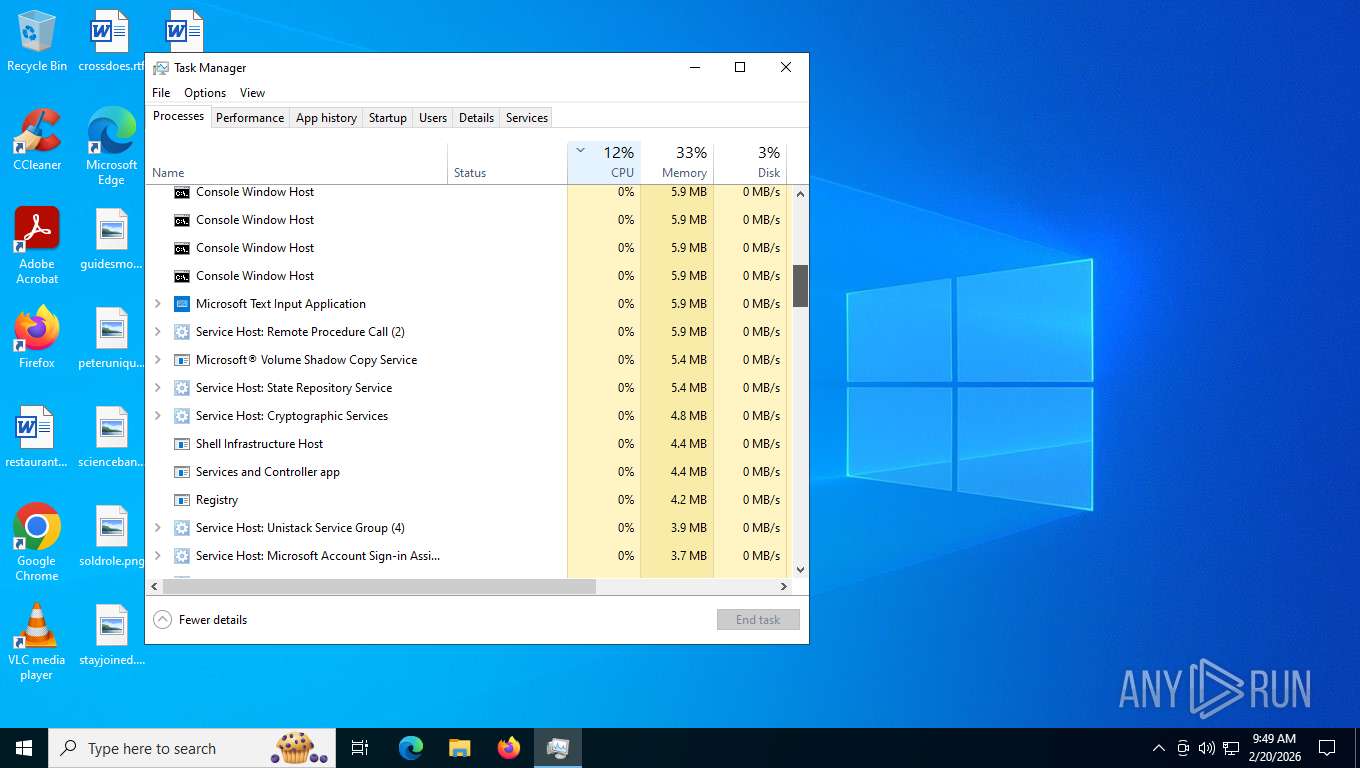
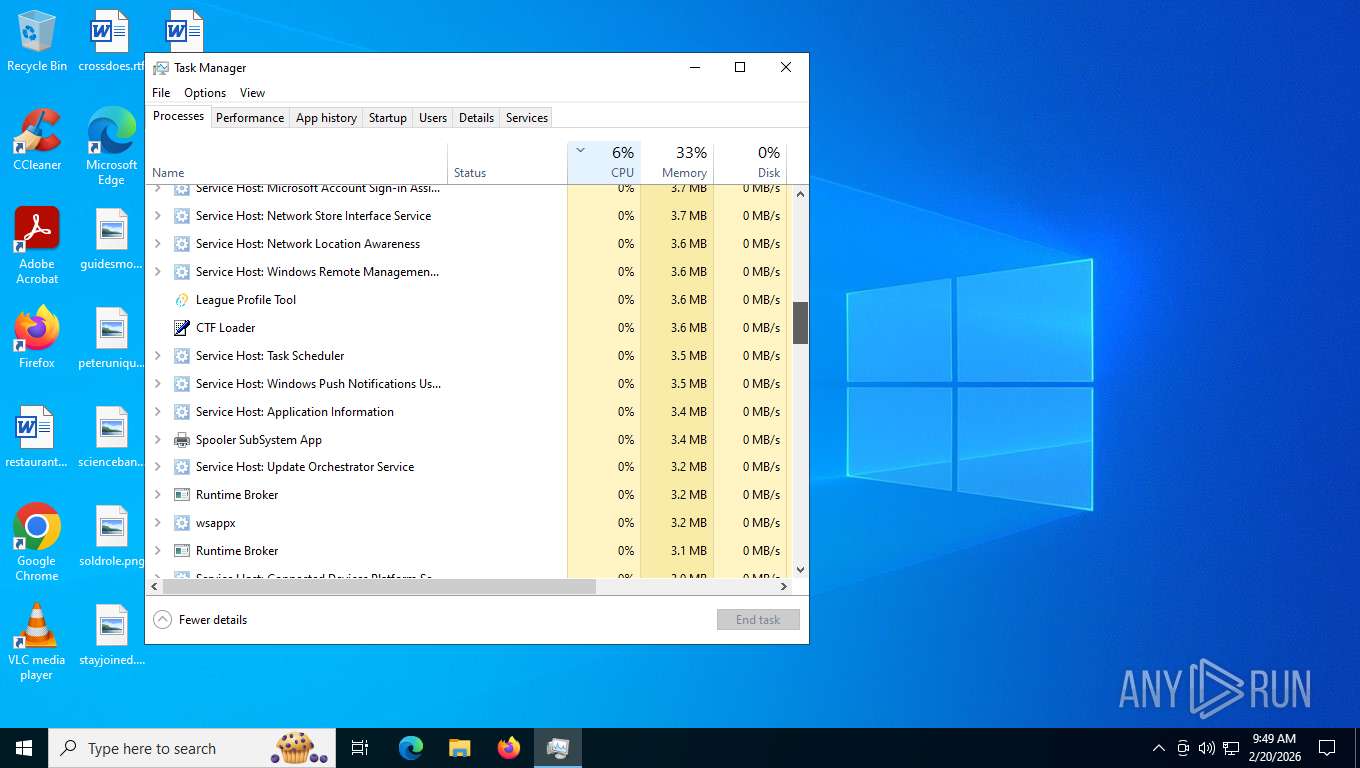
Total processes
192
Monitored processes
33
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 488 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\145.0.3800.65\msedgewebview2.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\com.leenny.league-profile-tool\EBWebView" --webview-exe-name=league-profile-tool.exe --webview-exe-version=1.3.7 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=2 --startup-read-main-dll --metrics-shmem-handle=1448,i,5332161415153132533,15356794010294937484,524288 --field-trial-handle=1836,i,3712181366016954332,13556811098659033923,262144 --disable-features=msPdfOOUI,msSmartScreenProtection,msWebOOUI --variations-seed-version --trace-process-track-uuid=3190708990060038890 --mojo-platform-channel-handle=2304 /prefetch:8 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\145.0.3800.65\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Exit code: 0 Version: 145.0.3800.65 Modules
| |||||||||||||||
| 1612 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\eventvwr.msc" /s | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1948 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{50742FF1-EF65-4927-B531-BBE1D87993F2}\EDGEMITMP_8F19C.tmp\setup.exe" --install-archive="C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{50742FF1-EF65-4927-B531-BBE1D87993F2}\MicrosoftEdge_X64_145.0.3800.65.exe" --msedgewebview --verbose-logging --do-not-launch-msedge --user-level | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{50742FF1-EF65-4927-B531-BBE1D87993F2}\EDGEMITMP_8F19C.tmp\setup.exe | MicrosoftEdge_X64_145.0.3800.65.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Installer Exit code: 0 Version: 145.0.3800.65 Modules
| |||||||||||||||
| 2096 | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{50742FF1-EF65-4927-B531-BBE1D87993F2}\EDGEMITMP_8F19C.tmp\setup.exe --type=crashpad-handler /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=145.0.7632.76 --annotation=exe=C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{50742FF1-EF65-4927-B531-BBE1D87993F2}\EDGEMITMP_8F19C.tmp\setup.exe --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=145.0.3800.65 --initial-client-data=0x230,0x234,0x238,0x20c,0x23c,0x7ff65437cc68,0x7ff65437cc74,0x7ff65437cc80 | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{50742FF1-EF65-4927-B531-BBE1D87993F2}\EDGEMITMP_8F19C.tmp\setup.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Installer Exit code: 0 Version: 145.0.3800.65 Modules
| |||||||||||||||
| 2232 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.221.3\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.221.3\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.221.3 Modules
| |||||||||||||||
| 2364 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\145.0.3800.65\msedgewebview2.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\com.leenny.league-profile-tool\EBWebView" --webview-exe-name=league-profile-tool.exe --webview-exe-version=1.3.7 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=2 --startup-read-main-dll --metrics-shmem-handle=2156,i,17338426300700562772,7508370149695164791,524288 --field-trial-handle=1836,i,3712181366016954332,13556811098659033923,262144 --disable-features=msPdfOOUI,msSmartScreenProtection,msWebOOUI --variations-seed-version --trace-process-track-uuid=3190708989122997041 --mojo-platform-channel-handle=2164 /prefetch:3 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\145.0.3800.65\msedgewebview2.exe | msedgewebview2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebView2 Exit code: 0 Version: 145.0.3800.65 Modules
| |||||||||||||||
| 2480 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:15 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2684 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2764 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\145.0.3800.65\msedgewebview2.exe" --type=renderer --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\com.leenny.league-profile-tool\EBWebView" --webview-exe-name=league-profile-tool.exe --webview-exe-version=1.3.7 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=2 --autoplay-policy=no-user-gesture-required --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--expose-gc --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --ram-no-pressure-read-main-dll --metrics-shmem-handle=3408,i,17523520027791420425,18332369564972314097,2097152 --field-trial-handle=1836,i,3712181366016954332,13556811098659033923,262144 --disable-features=msPdfOOUI,msSmartScreenProtection,msWebOOUI --variations-seed-version --trace-process-track-uuid=3190708990997080739 --mojo-platform-channel-handle=3412 /prefetch:1 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\145.0.3800.65\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Exit code: 0 Version: 145.0.3800.65 Modules
| |||||||||||||||
| 2900 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\145.0.3800.65\msedgewebview2.exe" --type=gpu-process --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\com.leenny.league-profile-tool\EBWebView" --webview-exe-name=league-profile-tool.exe --webview-exe-version=1.3.7 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=2 --gpu-preferences=SAAAAAAAAADgAAAEAAAAAAAAAAAAAGAAAQAAAAAAAAAAAAAAAAAAAAIAAAAAAAAAAAAAAAAAAAAQAAAAAAAAABAAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --startup-read-main-dll --metrics-shmem-handle=1736,i,6656486455268562718,14271253887843211776,262144 --field-trial-handle=1836,i,3712181366016954332,13556811098659033923,262144 --disable-features=msPdfOOUI,msSmartScreenProtection,msWebOOUI --variations-seed-version --trace-process-track-uuid=3190708988185955192 --mojo-platform-channel-handle=1860 /prefetch:2 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\145.0.3800.65\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Exit code: 0 Version: 145.0.3800.65 Modules
| |||||||||||||||
Total events
24 502
Read events
22 619
Write events
1 804
Delete events
79
Modification events
| (PID) Process: | (5204) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000C42A88B377A2DC015414000000230000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5204) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000C42A88B377A2DC015414000000230000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5204) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000528AC8B377A2DC015414000000230000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5204) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000528AC8B377A2DC015414000000230000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5204) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000528AC8B377A2DC015414000000230000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5204) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 480000000000000089ECCAB377A2DC015414000000230000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5204) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000FD61E0B377A2DC015414000000230000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5204) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000FD61E0B377A2DC015414000060230000E803000001000000000000000000000000DCC9E79ECD65438078A49F4851458300000000000000000000000000000000 | |||
| (PID) Process: | (5204) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 15 | |||
| (PID) Process: | (7164) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000006E4DECB377A2DC01FC1B0000B8130000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
209
Suspicious files
133
Text files
89
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5204 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5204 | msiexec.exe | C:\Windows\Installer\1e9558.msi | — | |
MD5:— | SHA256:— | |||
| 5204 | msiexec.exe | C:\Windows\Installer\1e955a.msi | — | |
MD5:— | SHA256:— | |||
| 5204 | msiexec.exe | C:\Windows\Installer\MSI97D9.tmp | binary | |
MD5:4F48F2FDBB4EA2B3DB6E7C95353AC36A | SHA256:EF0EFF39B6DC71D03178332DF4C58E0DF1C6D915D1A31BC535D4F538F1124D09 | |||
| 4712 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI605E.tmp | executable | |
MD5:CFBB8568BD3711A97E6124C56FCFA8D9 | SHA256:7F47D98AB25CFEA9B3A2E898C3376CC9BA1CD893B4948B0C27CAA530FD0E34CC | |||
| 5204 | msiexec.exe | C:\Windows\Installer\{2DAA9363-8B52-4E52-A9FD-E6EB16F93BE3}\ProductIcon | image | |
MD5:89F8F32178133FF3191ADEA3984E64D4 | SHA256:392206B573A809997F3FF16FE68F456A52E931C372107EADE9572B329BBE3321 | |||
| 5204 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:EFDC4452829183519BF2AB90B00CBD52 | SHA256:0C2FB1F60DEC24A9A25E66ECB784343A02428B9286D02D37FDDB526BA73887B1 | |||
| 5204 | msiexec.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\League Profile Tool\~eague Profile Tool.tmp | binary | |
MD5:6CAC308D9313C8844B959A4C77E597B5 | SHA256:35CEA0B2F0618668CF00A568F51497F819C58EEB201720F1067891CA0F8E8355 | |||
| 5204 | msiexec.exe | C:\Program Files\League Profile Tool\league-profile-tool.exe | executable | |
MD5:63A750CE0590AF2F9CBDC12AC216BE42 | SHA256:BD99EC75A5482F2459157E6E23A5C3A784EDAEE1F4E72E299340F48B147B392D | |||
| 5204 | msiexec.exe | C:\Users\Public\Desktop\League Profile Tool.lnk | binary | |
MD5:47F190B023B0F2AD91428B94C7D0600B | SHA256:FD74BA23A57B954D198159FD8FE4DC48E7338BE82B1C36452846833CC6D31504 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
100
TCP/UDP connections
56
DNS requests
44
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7428 | svchost.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
4952 | powershell.exe | GET | 301 | 88.221.169.205:443 | https://go.microsoft.com/fwlink/p/?LinkId=2124703 | US | — | — | whitelisted |
7428 | svchost.exe | GET | 200 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=1&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | binary | 5.70 Kb | whitelisted |
7428 | svchost.exe | GET | 200 | 184.24.77.38:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
7428 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
2352 | SIHClient.exe | GET | 304 | 74.178.76.128:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
3236 | svchost.exe | POST | 403 | 88.221.169.205:443 | https://go.microsoft.com/fwlink/?LinkID=2257403&clcid=0x409 | US | html | 386 b | whitelisted |
3236 | svchost.exe | POST | 403 | 88.221.169.205:443 | https://go.microsoft.com/fwlink/?LinkID=2257403&clcid=0x409 | US | html | 386 b | whitelisted |
3236 | svchost.exe | POST | 403 | 88.221.169.205:443 | https://go.microsoft.com/fwlink/?LinkID=2257403&clcid=0x409 | US | html | 386 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7428 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
492 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7428 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7428 | svchost.exe | 184.24.77.38:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
7428 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3236 | svchost.exe | 88.221.169.205:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
msedge.sf.dl.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7428 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
4952 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
4952 | powershell.exe | Misc activity | ET INFO Request for EXE via Powershell |
4952 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
4952 | powershell.exe | Misc activity | ET INFO Packed Executable Download |
4660 | svchost.exe | Misc activity | ET INFO Packed Executable Download |
2364 | msedgewebview2.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2364 | msedgewebview2.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
Process | Message |
|---|---|
msedgewebview2.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\com.leenny.league-profile-tool directory exists )
|
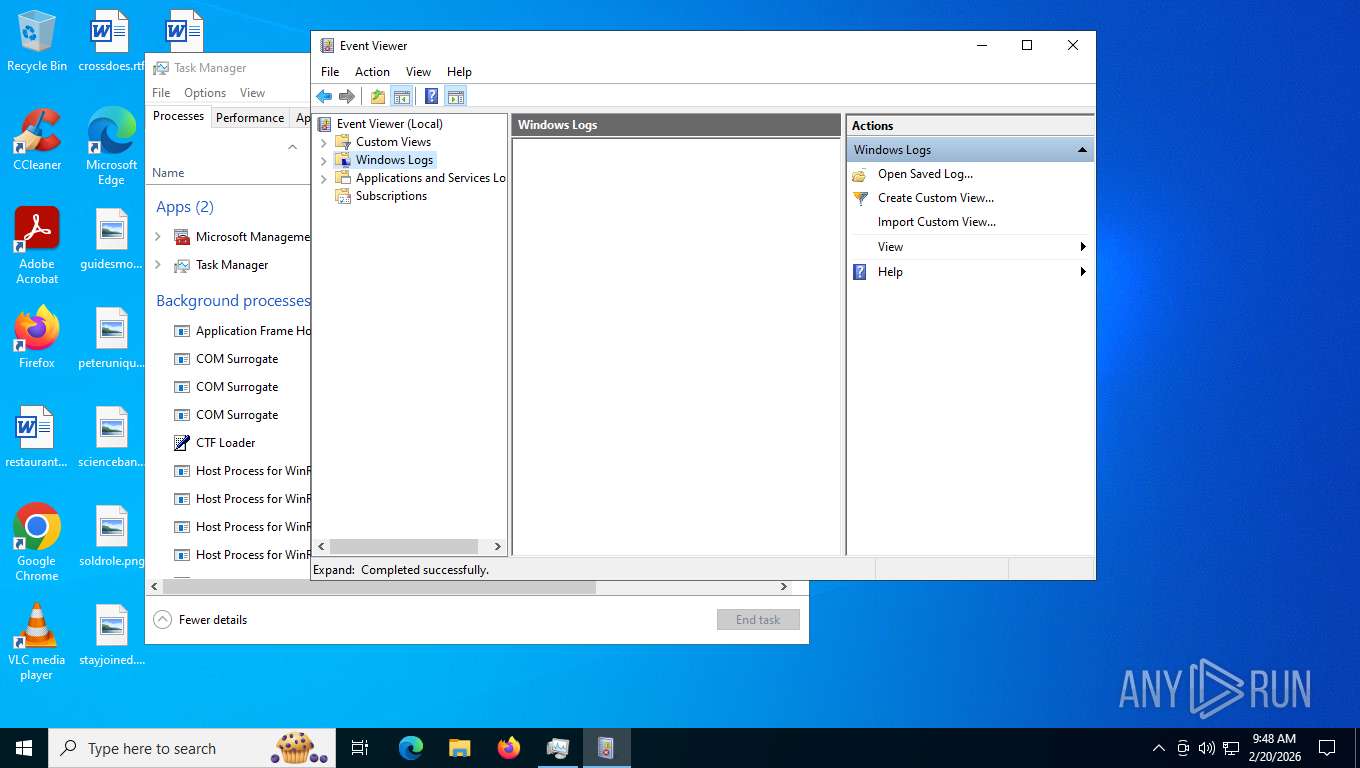
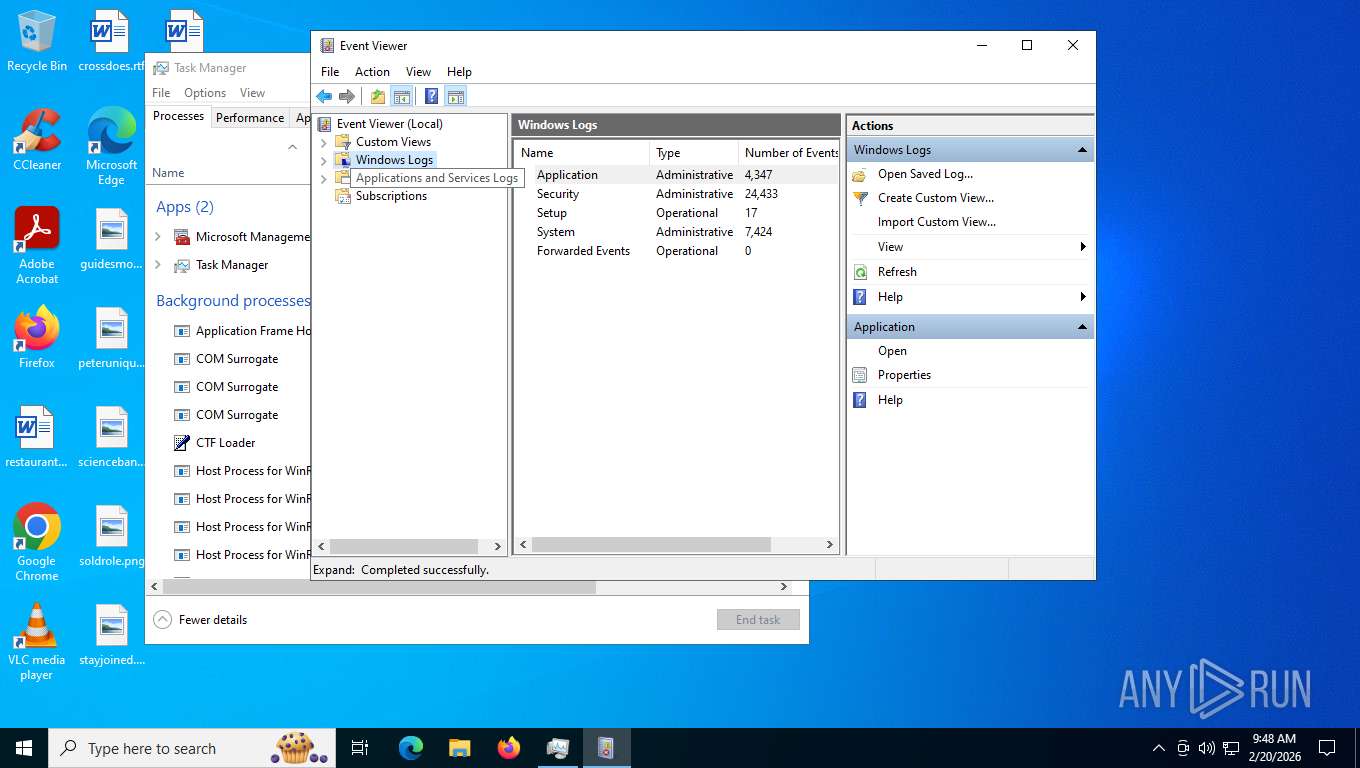
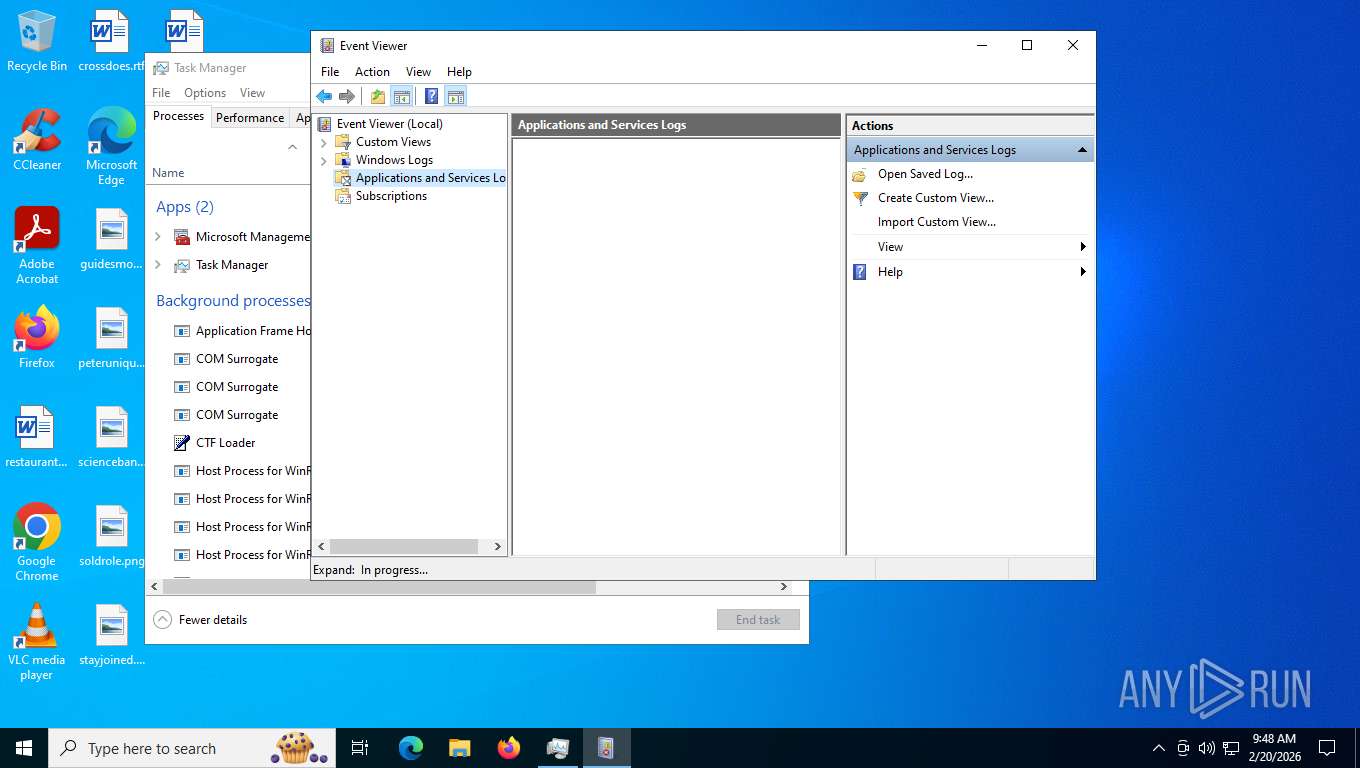
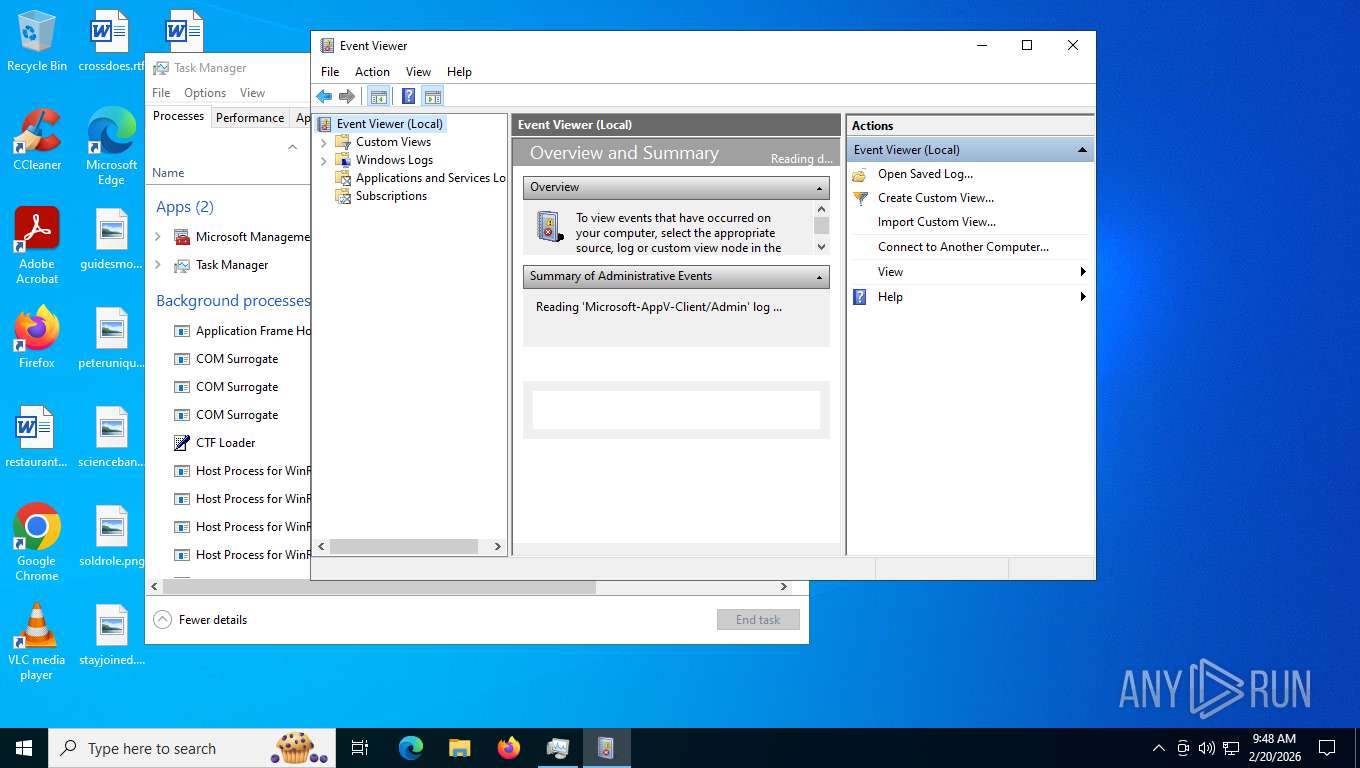
mmc.exe | ViewerConfigPath = 'C:\ProgramData\Microsoft\Event Viewer': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerAdminViewsPath = 'C:\ProgramData\Microsoft\Event Viewer\Views\ApplicationViewsRootNode': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerViewsFolderPath = 'C:\ProgramData\Microsoft\Event Viewer\Views': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerExternalLogsPath = 'C:\ProgramData\Microsoft\Event Viewer\ExternalLogs': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | Failed to get ChannelConfigOwningPublisher -122-The data area passed to a system call is too small
|
mmc.exe | Getting next publisher from enum failed-259-No more data is available
|
mmc.exe | Failed to get ChannelConfigOwningPublisher -122-The data area passed to a system call is too small
|
mmc.exe | ExpandNode:After EventsNode:InsertChildren CountOfChildren = 5
|
mmc.exe | PublisherMetadataKeywordName failed for not providing enough memory. Trying with the correct memory -122-The data area passed to a system call is too small
|