| File name: | 37f5b68321a9645814569cfdbfa08c363f0e19b077c3b0174e578eff40a69f3b.bin |
| Full analysis: | https://app.any.run/tasks/5343be37-73b4-4c06-a170-c889b13203ef |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 10:42:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 1EFAA77A6F99D04EFFA4DC710C3909F0 |
| SHA1: | C4F79C464150C21CFDE7A31C415130AF9C6BAF02 |
| SHA256: | 37F5B68321A9645814569CFDBFA08C363F0E19B077C3B0174E578EFF40A69F3B |
| SSDEEP: | 98304:hFFIVzWVtifrnekQTYTBT5t+md9qdbGgxYkAYz+8yB:tCzKASUlT5t+md81GgxqYz+8yB |
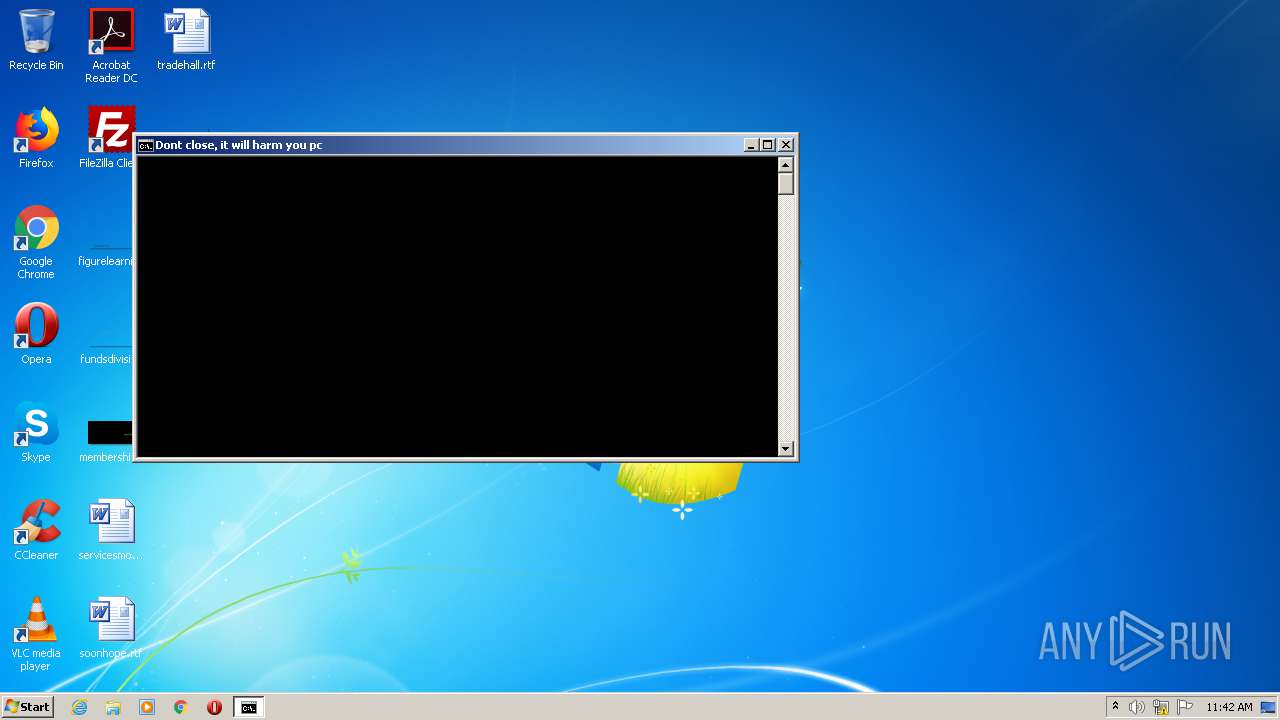
MALICIOUS
Deletes shadow copies
- cmd.exe (PID: 3116)
- cmd.exe (PID: 2620)
Loads dropped or rewritten executable
- thankyou.exe (PID: 2192)
Starts BCDEDIT.EXE to disable recovery
- cmd.exe (PID: 2620)
Application was dropped or rewritten from another process
- thankyou.exe (PID: 2192)
SUSPICIOUS
Starts CMD.EXE for commands execution
- thankyou.exe (PID: 2192)
- cmd.exe (PID: 2620)
Executable content was dropped or overwritten
- 37f5b68321a9645814569cfdbfa08c363f0e19b077c3b0174e578eff40a69f3b.bin.exe (PID: 2356)
Application launched itself
- cmd.exe (PID: 2620)
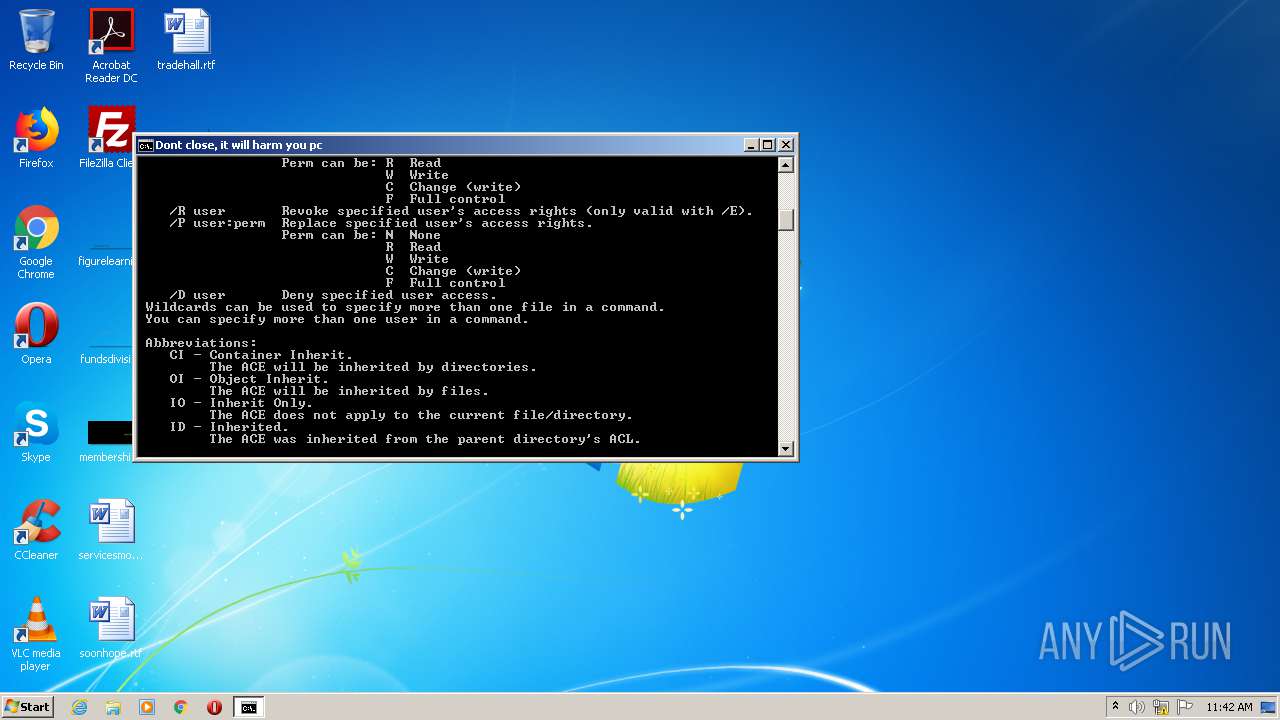
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2620)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:06:10 19:11:07+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 165376 |
| InitializedDataSize: | 314368 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d41b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jun-2014 17:11:07 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 10-Jun-2014 17:11:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00028553 | 0x00028600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.72377 |
.rdata | 0x0002A000 | 0x00004F53 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.35228 |
.data | 0x0002F000 | 0x000218FC | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.47003 |
.rsrc | 0x00051000 | 0x00046480 | 0x00046600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.67062 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22792 | 1600 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 5.65383 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 6.36797 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.11693 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 3.66634 | 508 | Latin 1 / Western European | UNKNOWN | RT_STRING |
8 | 3.71728 | 582 | Latin 1 / Western European | UNKNOWN | RT_STRING |
9 | 3.74776 | 476 | Latin 1 / Western European | UNKNOWN | RT_STRING |
10 | 3.55807 | 220 | Latin 1 / Western European | UNKNOWN | RT_STRING |
11 | 3.88515 | 1086 | Latin 1 / Western European | UNKNOWN | RT_STRING |
12 | 3.68258 | 356 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
48
Monitored processes
13
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 940 | wmic shadowcopy delete | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2192 | "C:\Users\admin\AppData\Local\Temp\build\thankyou.exe" /thankyou.exe | C:\Users\admin\AppData\Local\Temp\build\thankyou.exe | — | 37f5b68321a9645814569cfdbfa08c363f0e19b077c3b0174e578eff40a69f3b.bin.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2232 | cacls C:\Users\admin /T /C /P admin :F | C:\Windows\system32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 8023 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2356 | "C:\Users\admin\AppData\Local\Temp\37f5b68321a9645814569cfdbfa08c363f0e19b077c3b0174e578eff40a69f3b.bin.exe" | C:\Users\admin\AppData\Local\Temp\37f5b68321a9645814569cfdbfa08c363f0e19b077c3b0174e578eff40a69f3b.bin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1000 Modules
| |||||||||||||||
| 2504 | bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Boot Configuration Data Editor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2528 | bcdedit /set {default} recoveryenabled no | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Boot Configuration Data Editor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2536 | attrib -r -a -s -h -i /s C:\Users\admin | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2608 | wbadmin delete catalog -quiet | C:\Windows\system32\wbadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® BLB Backup Exit code: 4294967294 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2620 | cmd /c ""a.bat"" | C:\Windows\system32\cmd.exe | — | thankyou.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3116 | cmd.exe /c @vssadmin delete shadows /all /quiet | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
411
Read events
407
Write events
4
Delete events
0
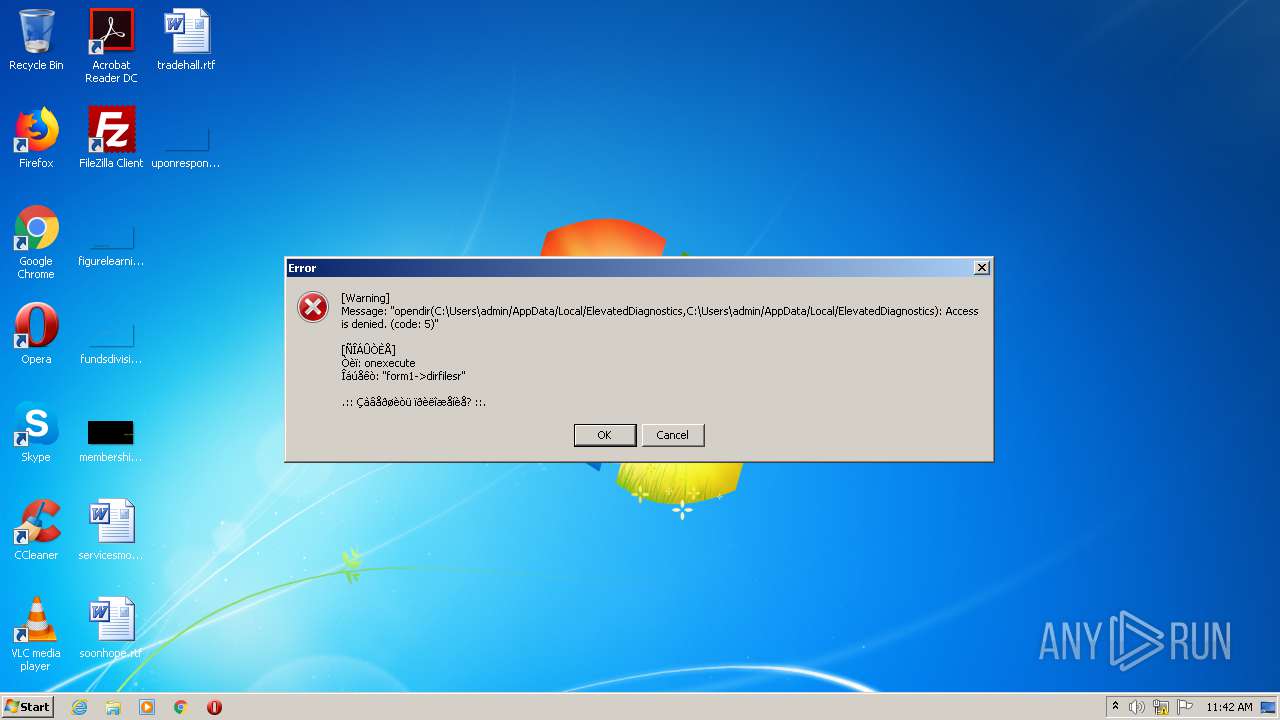
Modification events
| (PID) Process: | (2356) 37f5b68321a9645814569cfdbfa08c363f0e19b077c3b0174e578eff40a69f3b.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2356) 37f5b68321a9645814569cfdbfa08c363f0e19b077c3b0174e578eff40a69f3b.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
4
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2356 | 37f5b68321a9645814569cfdbfa08c363f0e19b077c3b0174e578eff40a69f3b.bin.exe | C:\Users\admin\AppData\Local\Temp\build\ext\php_osinfo.dll | executable | |
MD5:— | SHA256:— | |||
| 2356 | 37f5b68321a9645814569cfdbfa08c363f0e19b077c3b0174e578eff40a69f3b.bin.exe | C:\Users\admin\AppData\Local\Temp\build\ext\php_fileinfo.dll | executable | |
MD5:— | SHA256:— | |||
| 2192 | thankyou.exe | C:\Users\admin\AppData\Local\Temp\PSE20\0b64b427081edba525bf5ea908350aef\php.ini | text | |
MD5:— | SHA256:— | |||
| 2356 | 37f5b68321a9645814569cfdbfa08c363f0e19b077c3b0174e578eff40a69f3b.bin.exe | C:\Users\admin\AppData\Local\Temp\build\thankyou.exe | executable | |
MD5:— | SHA256:— | |||
| 2192 | thankyou.exe | C:\Users\admin\AppData\Local\Temp\build\a.bat | text | |
MD5:— | SHA256:— | |||
| 2192 | thankyou.exe | C:\Users\admin\AppData\Local\Temp\build\f.scrbr | text | |
MD5:D7AA32B0C582222819B91C8E0CCCA765 | SHA256:82179DA1705476F753FDBB9FB58FEF251195A42A5D468128266E12228AF7E75B | |||
| 2356 | 37f5b68321a9645814569cfdbfa08c363f0e19b077c3b0174e578eff40a69f3b.bin.exe | C:\Users\admin\AppData\Local\Temp\build\php5ts.dll | executable | |
MD5:C9AFF68F6673FAE7580527E8C76805B6 | SHA256:9B2C8B8C4CEC301C4303F58CA4E8B261D516F10FEB24573B092DFCCC263BAEA4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report