| File name: | Ultimate_Drive_Increaser____1_.exe |
| Full analysis: | https://app.any.run/tasks/cc189735-bb51-429c-a436-8e80024375ae |
| Verdict: | No threats detected |
| Analysis date: | May 12, 2020, 09:04:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 6431796E550277FFDDFDA0B08A21184D |
| SHA1: | 56954A4EFB32C241D844EF6BFB8AB6048E9AE480 |
| SHA256: | 37F0E0CAC605030526D2D42E39D8FBA6C00F5569599763D7EC727C9C376CF93B |
| SSDEEP: | 3072:fLdSro1G2CmPzzJyE39mnb5o82NilMcju45fpR:ffTCmZtmbZhMcjJR |
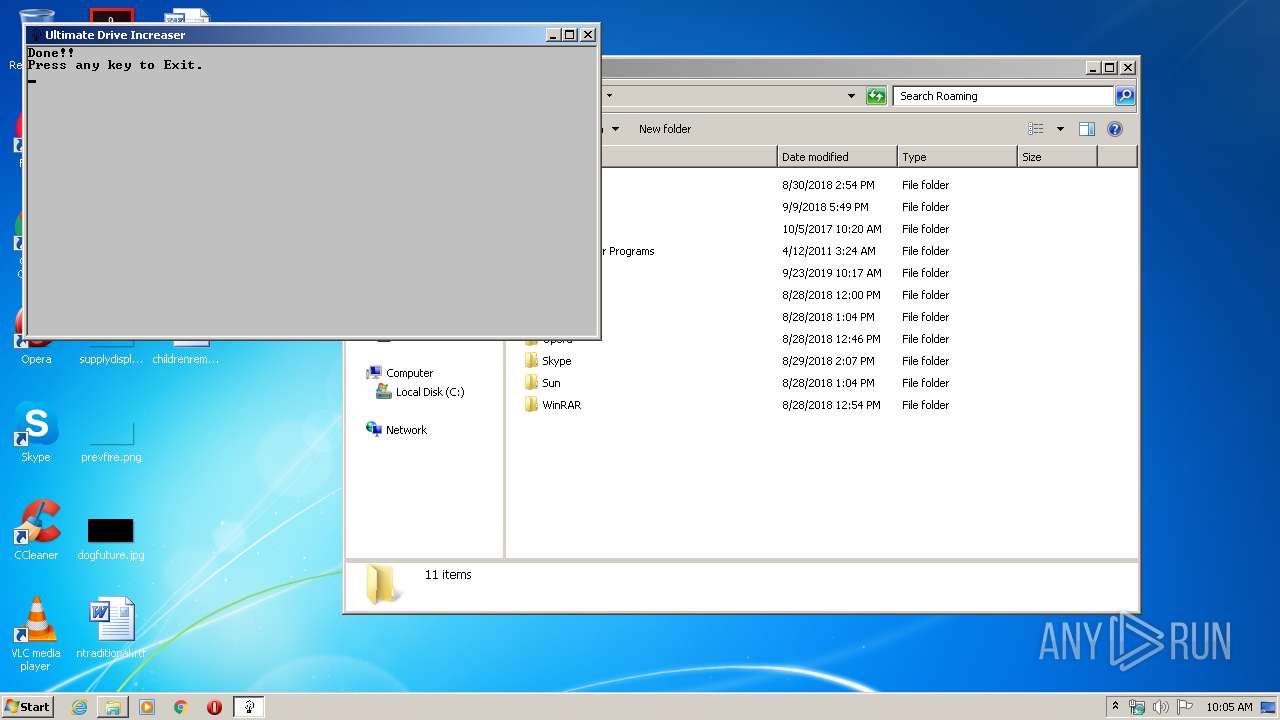
MALICIOUS
Application was dropped or rewritten from another process
- mkdosfs.exe (PID: 2612)
SUSPICIOUS
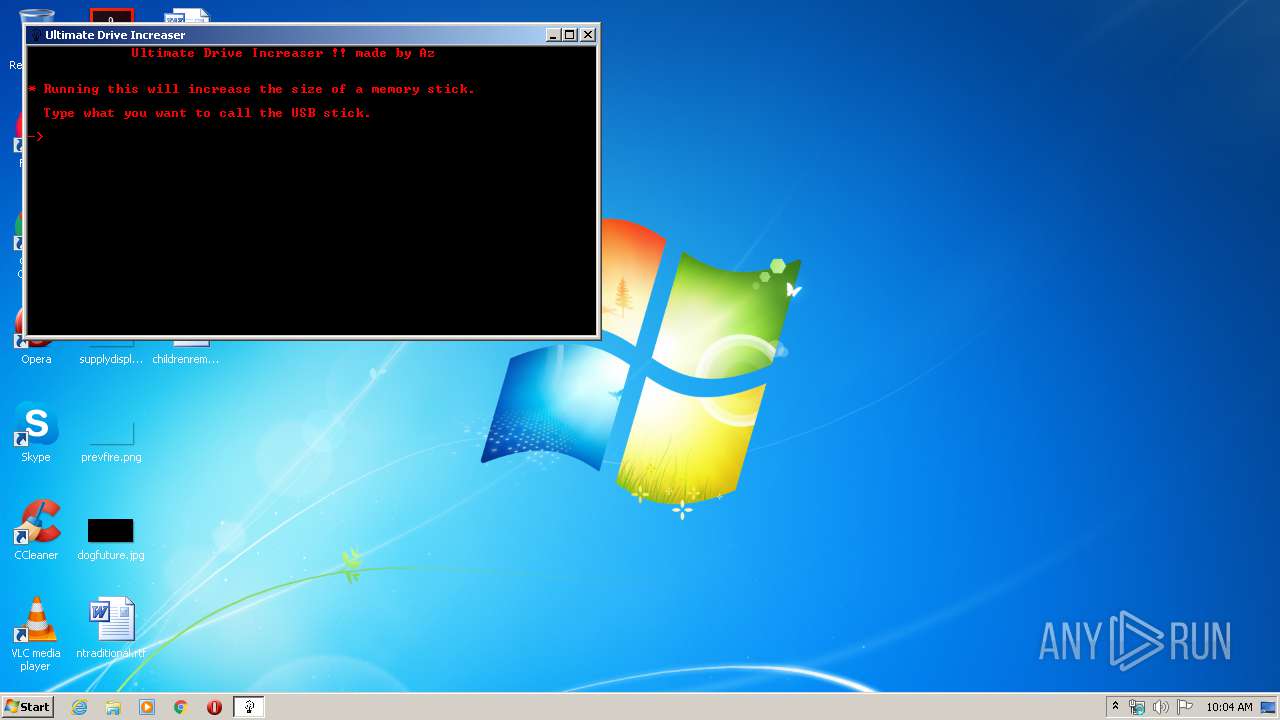
Starts CMD.EXE for commands execution
- Ultimate_Drive_Increaser____1_.exe (PID: 2436)
Executable content was dropped or overwritten
- Ultimate_Drive_Increaser____1_.exe (PID: 2436)
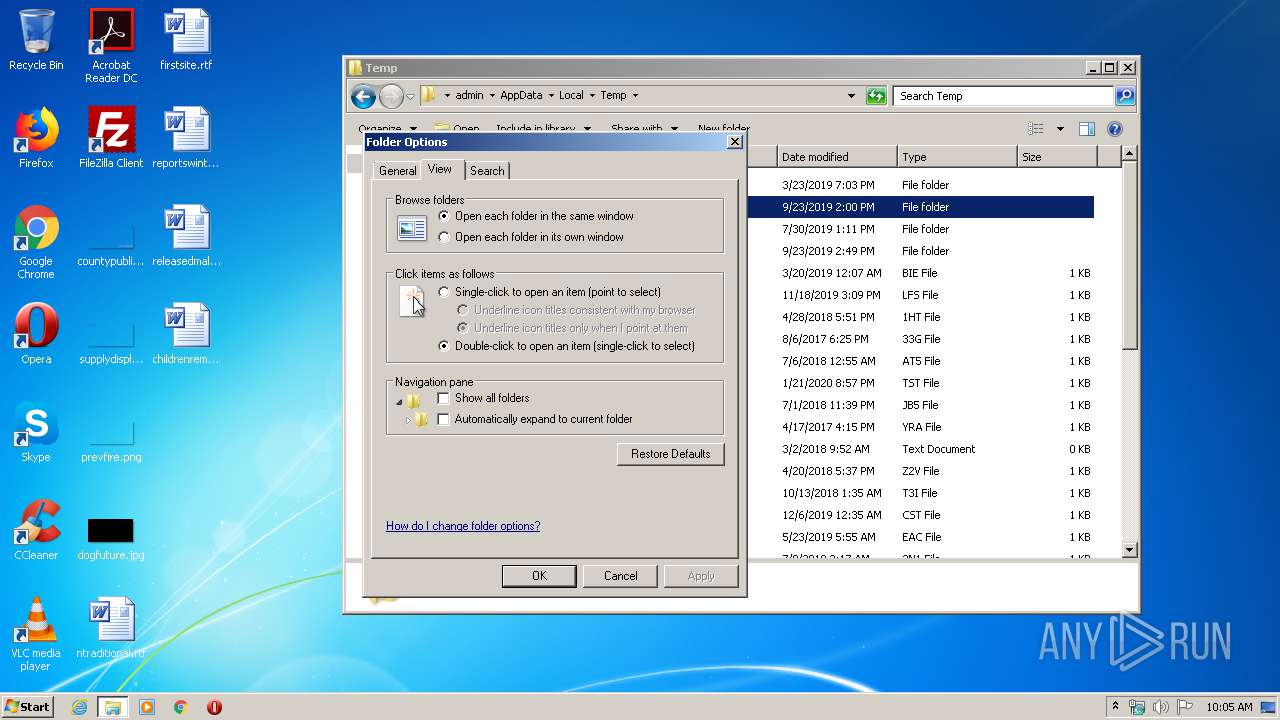
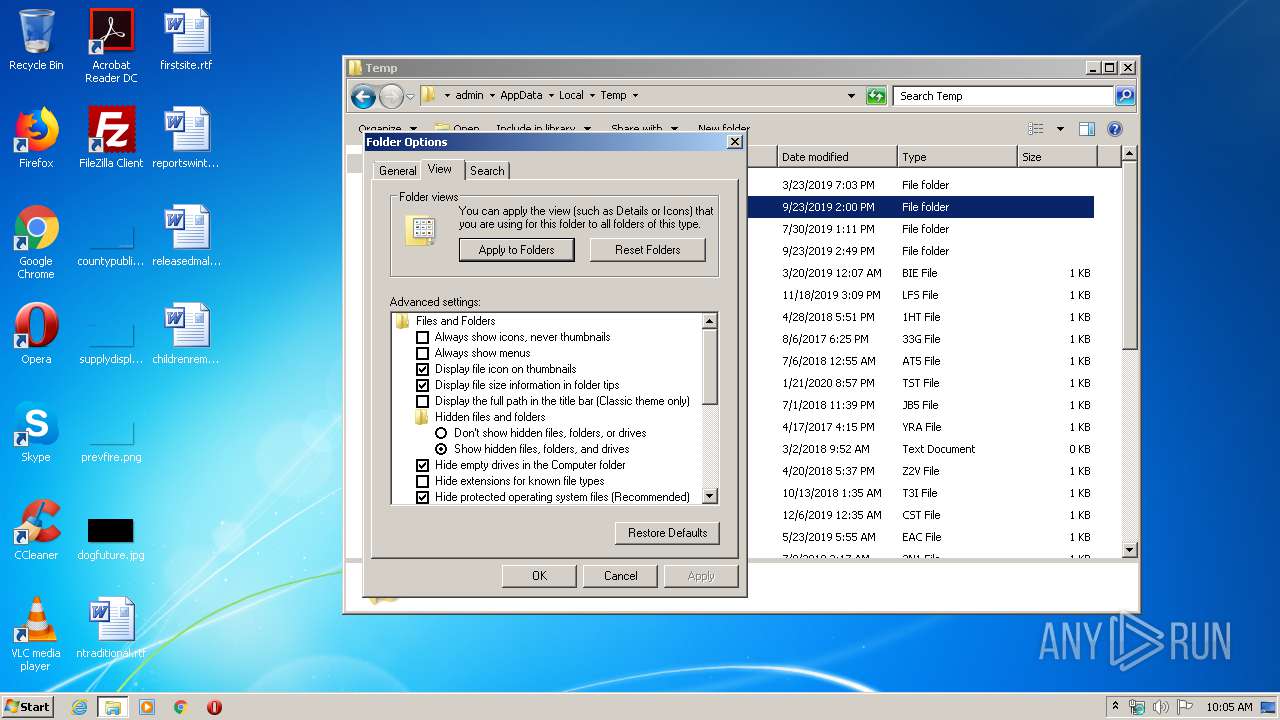
INFO
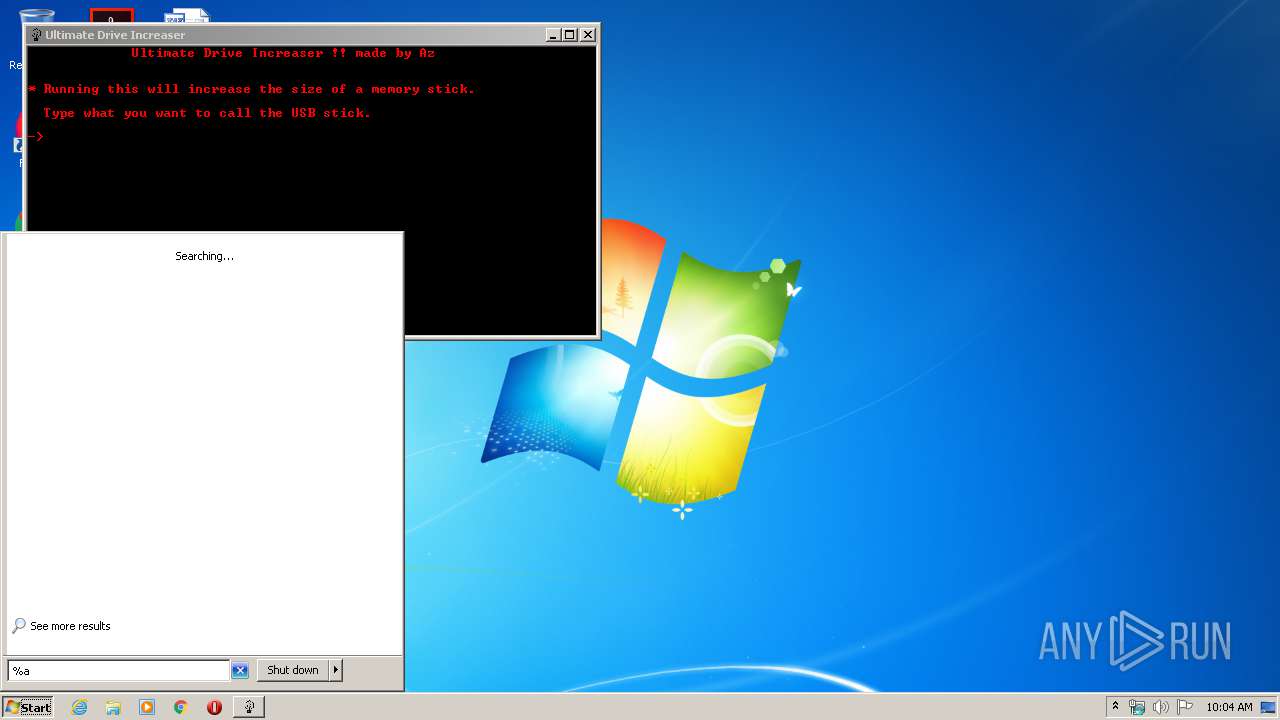
Manual execution by user
- verclsid.exe (PID: 3080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (30.9) |
| .scr | | | Windows screen saver (14.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.3) |
| .exe | | | Win32 Executable (generic) (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:07:30 18:15:11+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 29696 |
| InitializedDataSize: | 110592 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 30-Jul-2014 16:15:11 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jul-2014 16:15:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x0000187C | 0x00001A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.3379 |
.text | 0x00003000 | 0x000058B7 | 0x00005A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55244 |
.rdata | 0x00009000 | 0x0000050A | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.87307 |
.data | 0x0000A000 | 0x000013F8 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.78029 |
.rsrc | 0x0000C000 | 0x00019668 | 0x00019800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.70572 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92322 | 611 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
B | 4.87752 | 627 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
D | 3.46772 | 14 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
F | 6.51125 | 93184 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
I | 3.83659 | 18 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
N | 3.86933 | 28 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
O | 0.650022 | 6 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSVCRT.dll |
OLE32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
Total processes
45
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1140 | mode con: cols=71 lines=24 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2240 | cmd /c ""C:\Users\admin\AppData\Local\Temp\86E2.tmp\Ultimate Drive Increaser.bat"" | C:\Windows\system32\cmd.exe | — | Ultimate_Drive_Increaser____1_.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2436 | "C:\Users\admin\AppData\Local\Temp\Ultimate_Drive_Increaser____1_.exe" | C:\Users\admin\AppData\Local\Temp\Ultimate_Drive_Increaser____1_.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
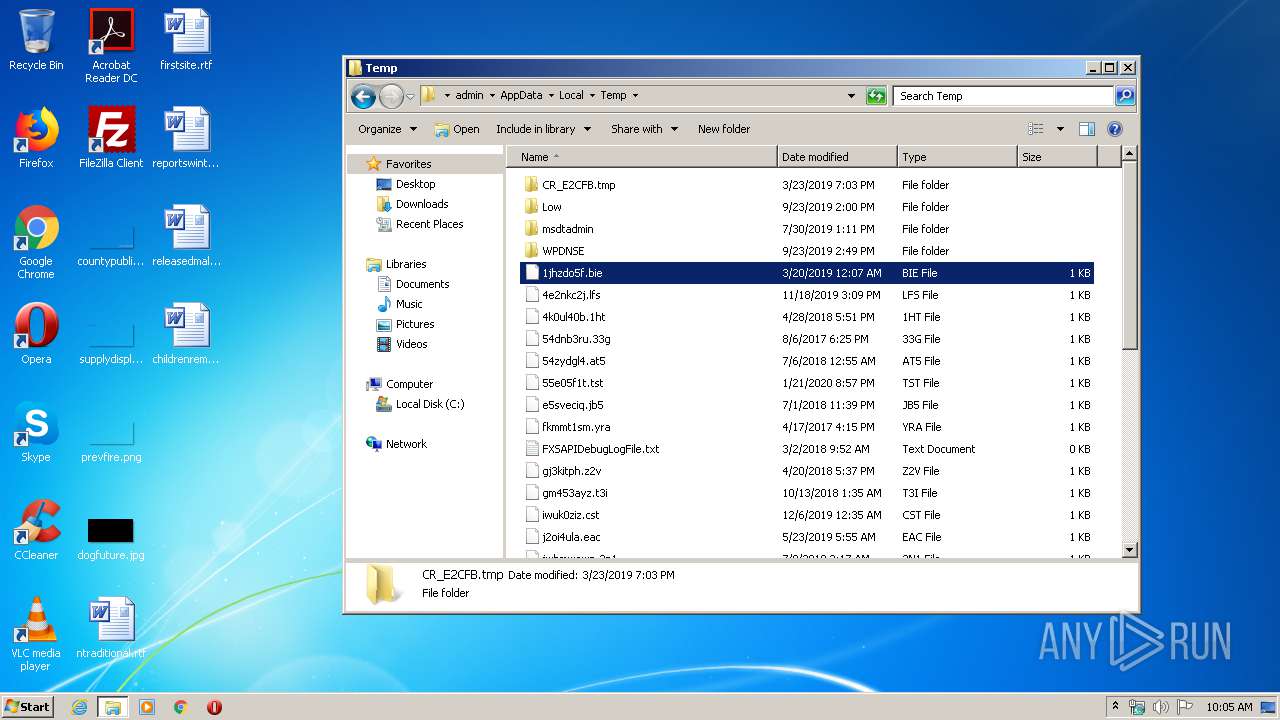
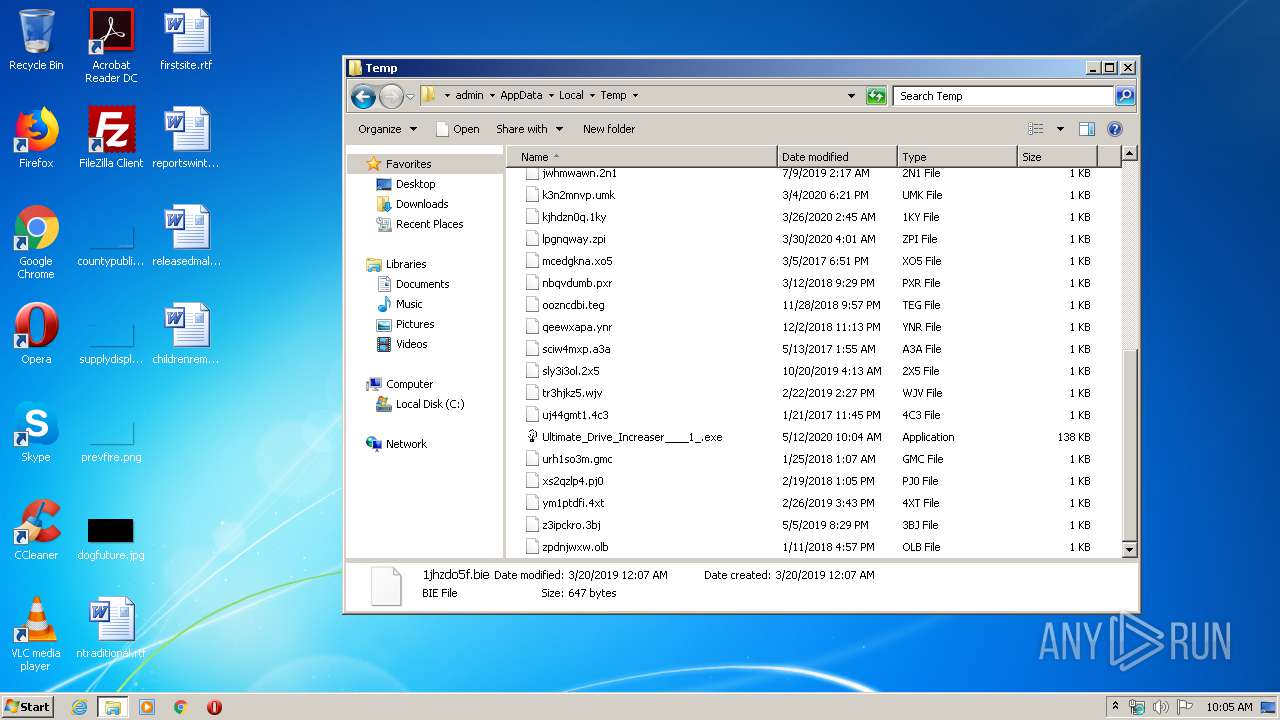
| 2612 | mkdosfs.exe -F 32 -n 1 -v 59: 123706775 | C:\Users\admin\AppData\Local\Temp\86E2.tmp\mkdosfs.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3080 | "C:\Windows\system32\verclsid.exe" /S /C {0B2C9183-C9FA-4C53-AE21-C900B0C39965} /I {0C733A8A-2A1C-11CE-ADE5-00AA0044773D} /X 0x401 | C:\Windows\system32\verclsid.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extension CLSID Verification Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6
Read events
6
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
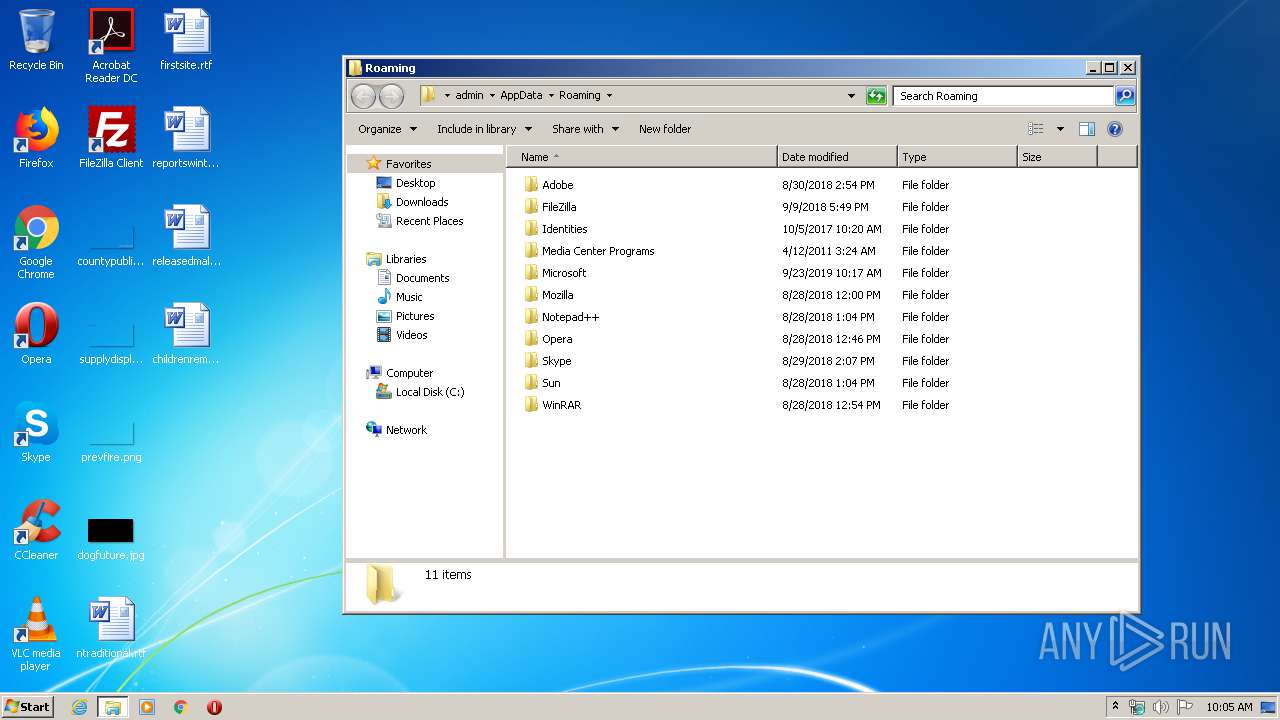
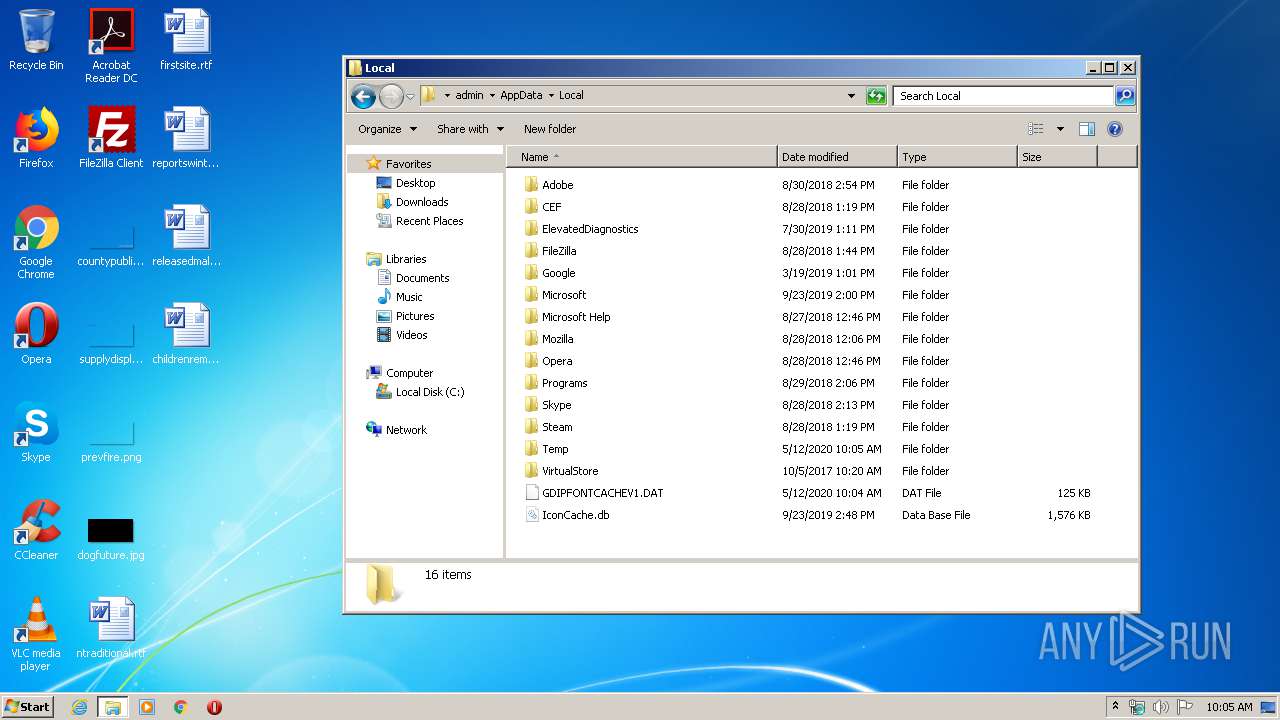
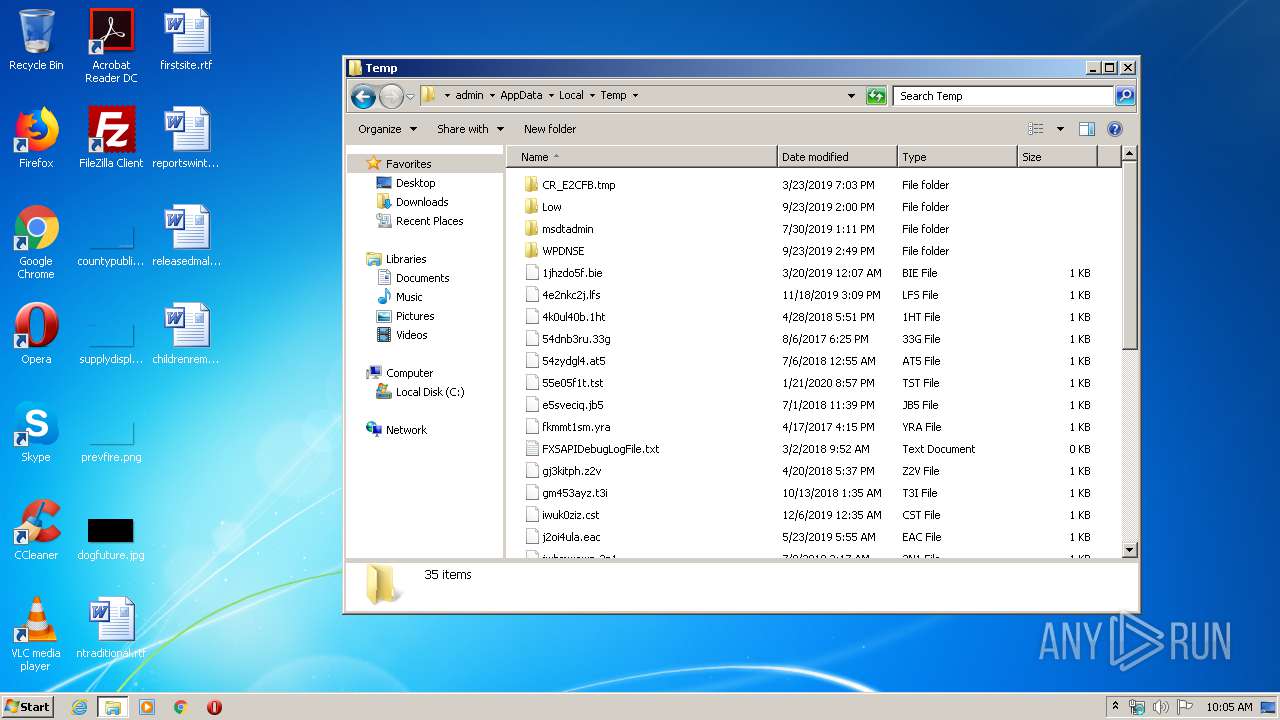
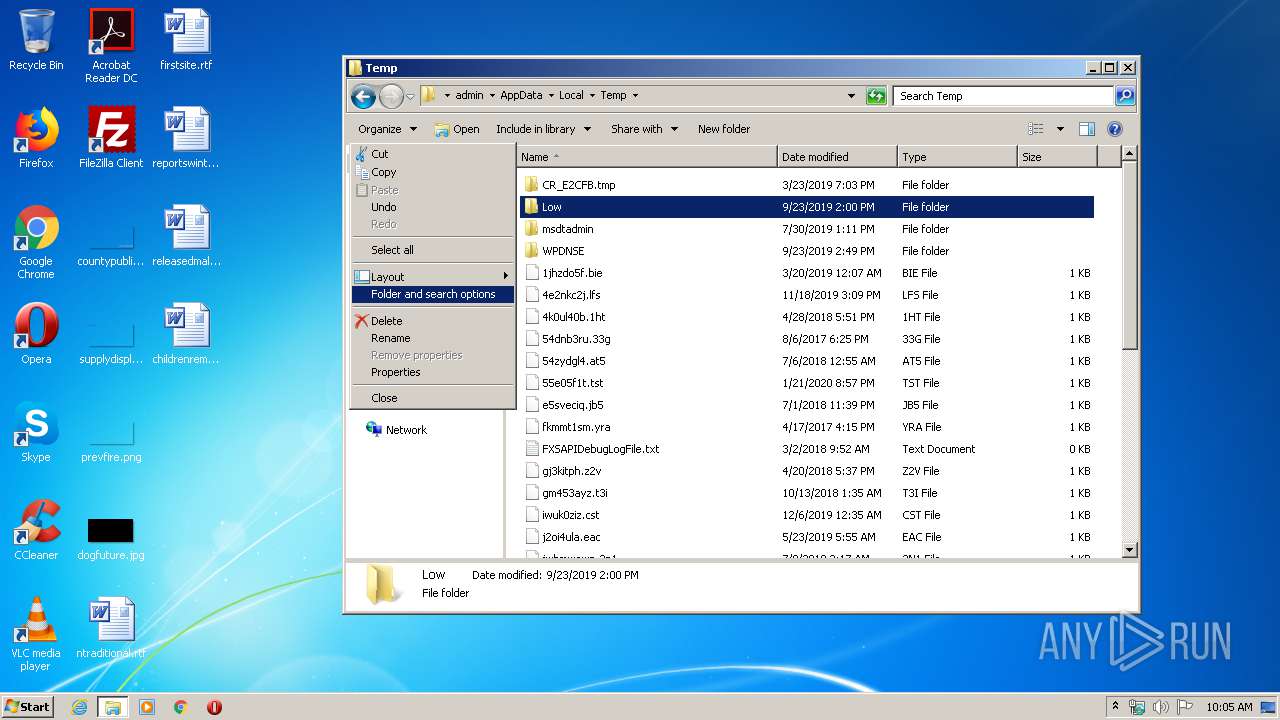
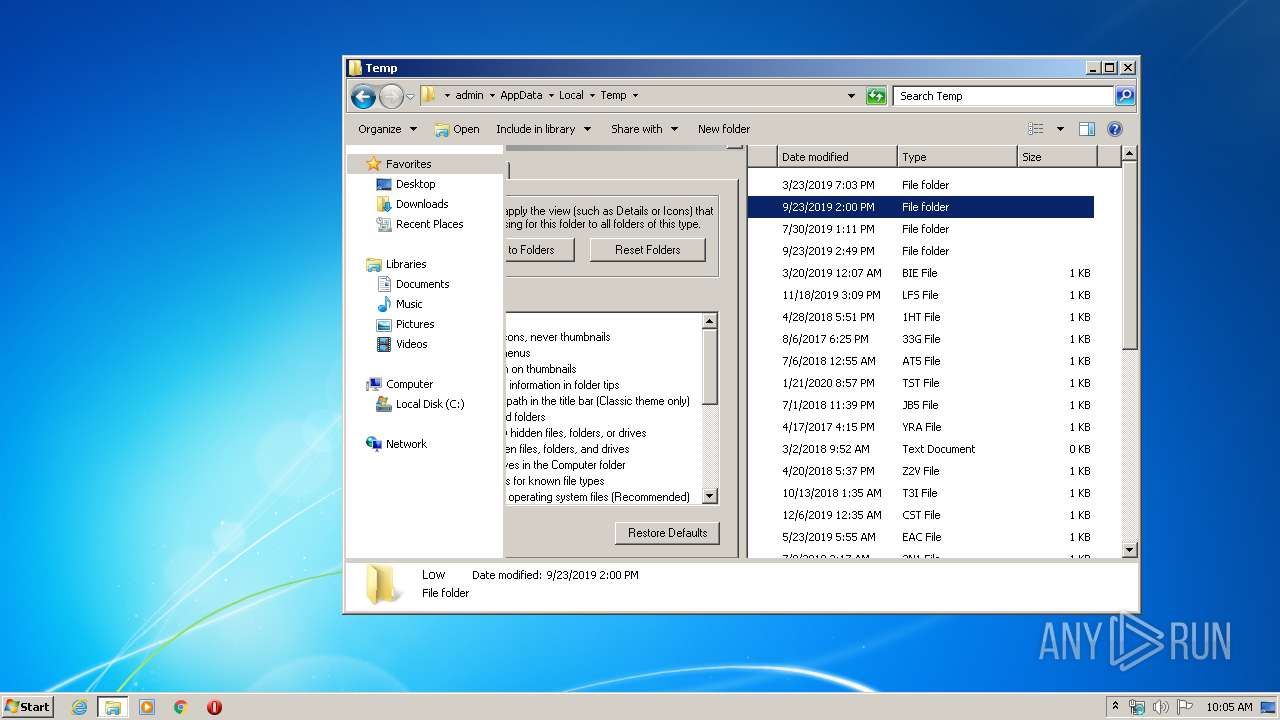
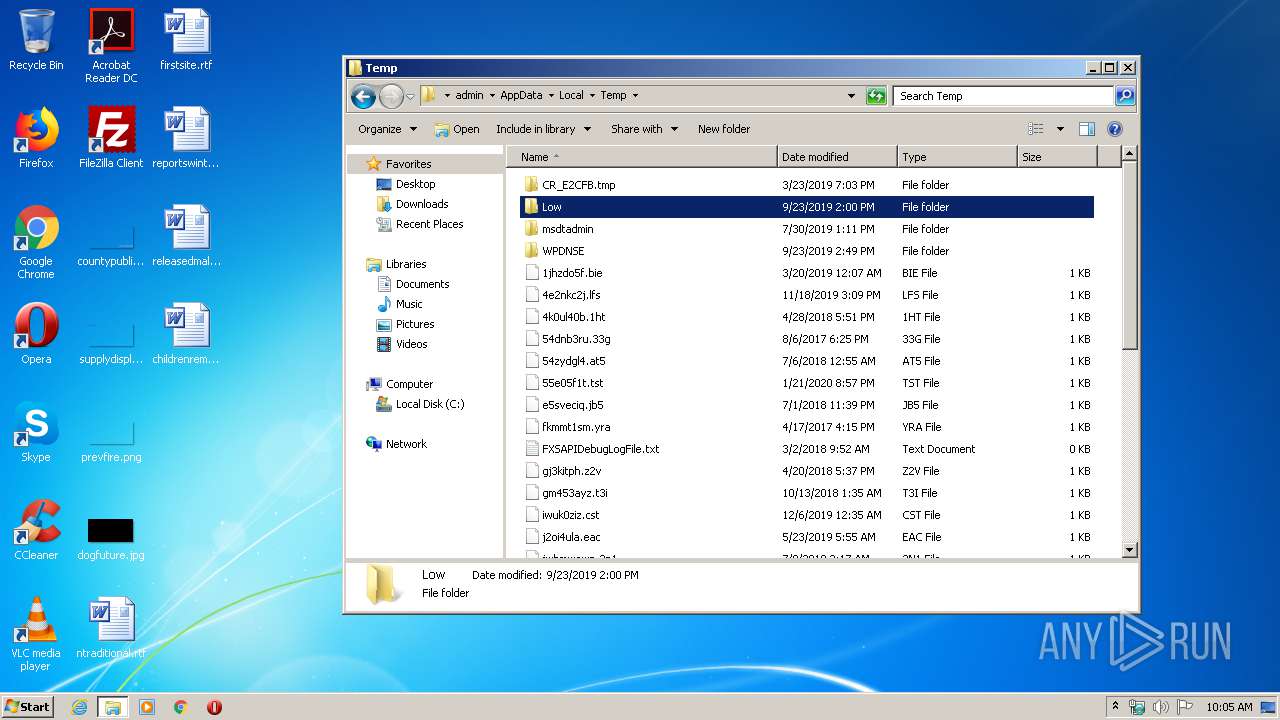
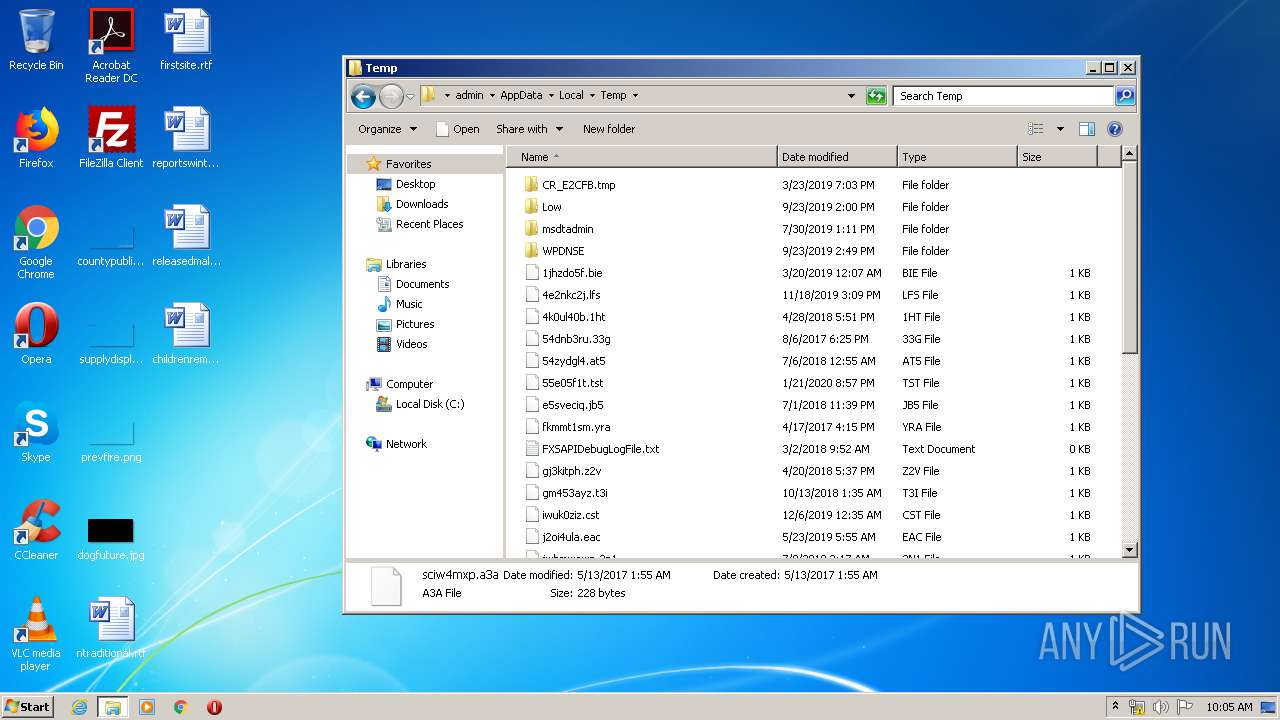
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
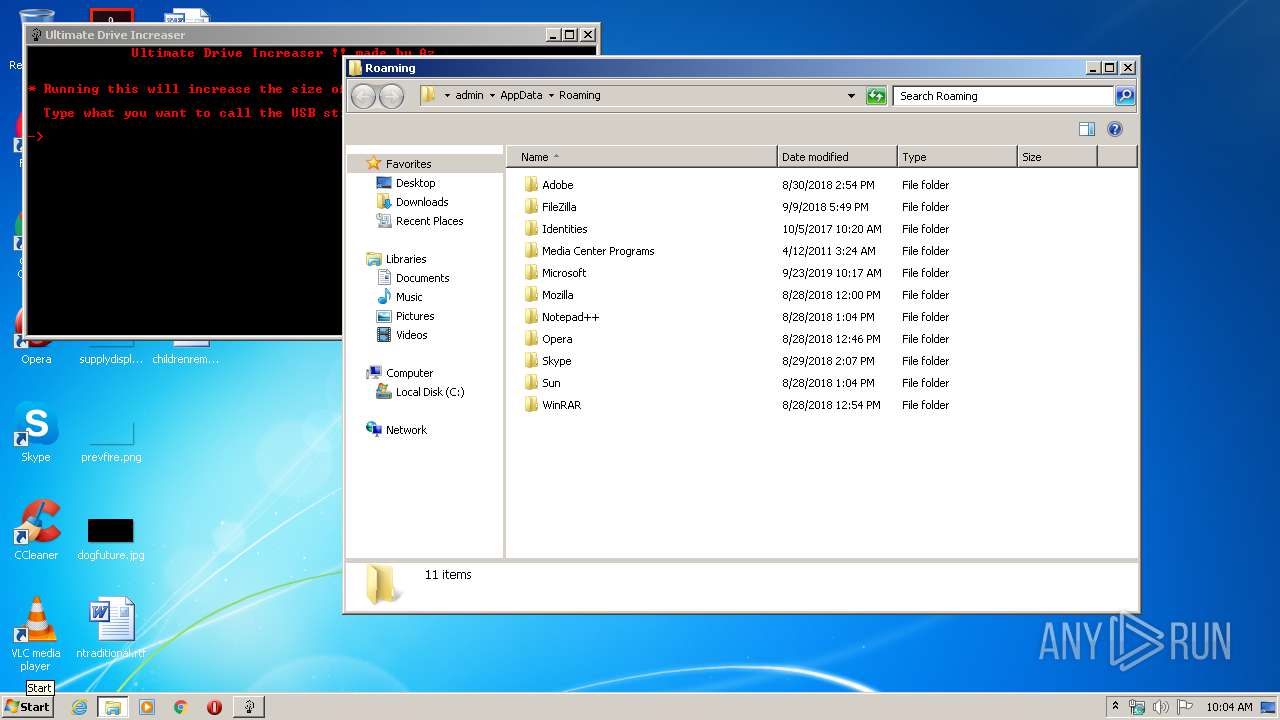
| 2436 | Ultimate_Drive_Increaser____1_.exe | C:\Users\admin\AppData\Local\Temp\86E2.tmp\Ultimate Drive Increaser.bat | text | |
MD5:— | SHA256:— | |||
| 2436 | Ultimate_Drive_Increaser____1_.exe | C:\Users\admin\AppData\Local\Temp\86E2.tmp\mkdosfs.exe | executable | |
MD5:534C1150803F9C2BB43CB94FCF9642E7 | SHA256:2580CEE164941D0A2F4C1D6C7BC4144D52BC8D161A6886523E3C4F75FBC679A9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report