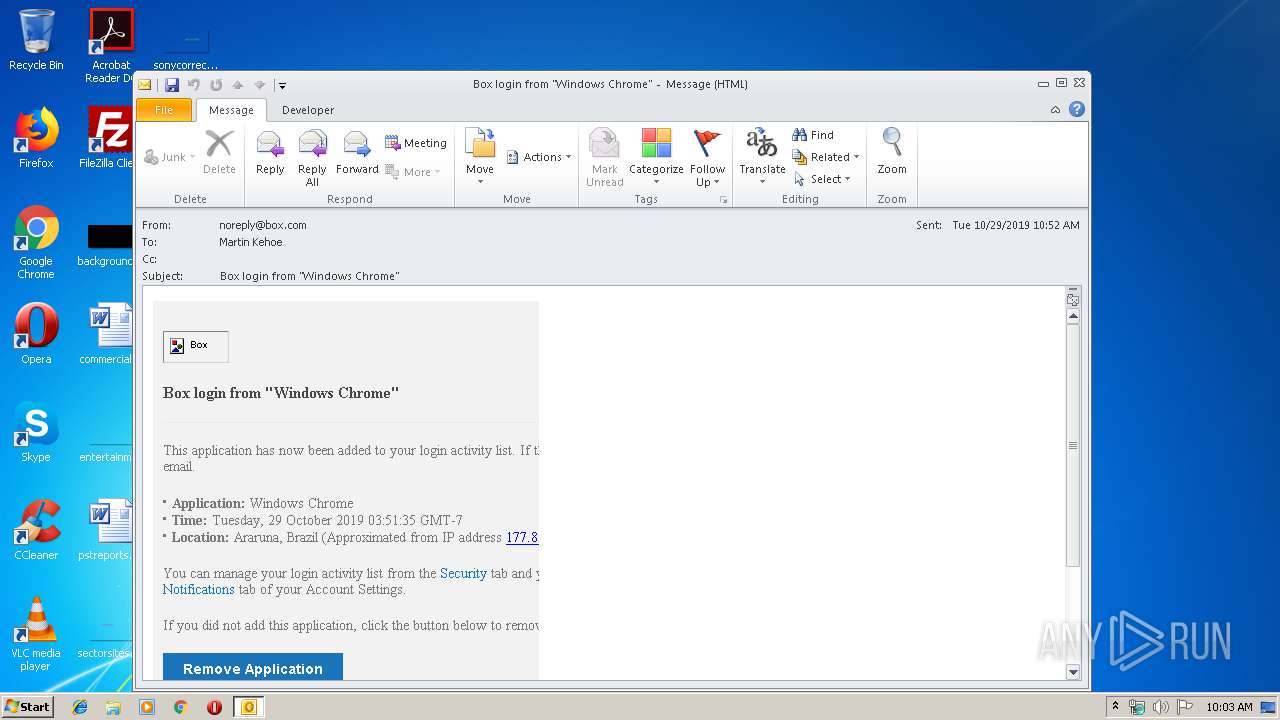
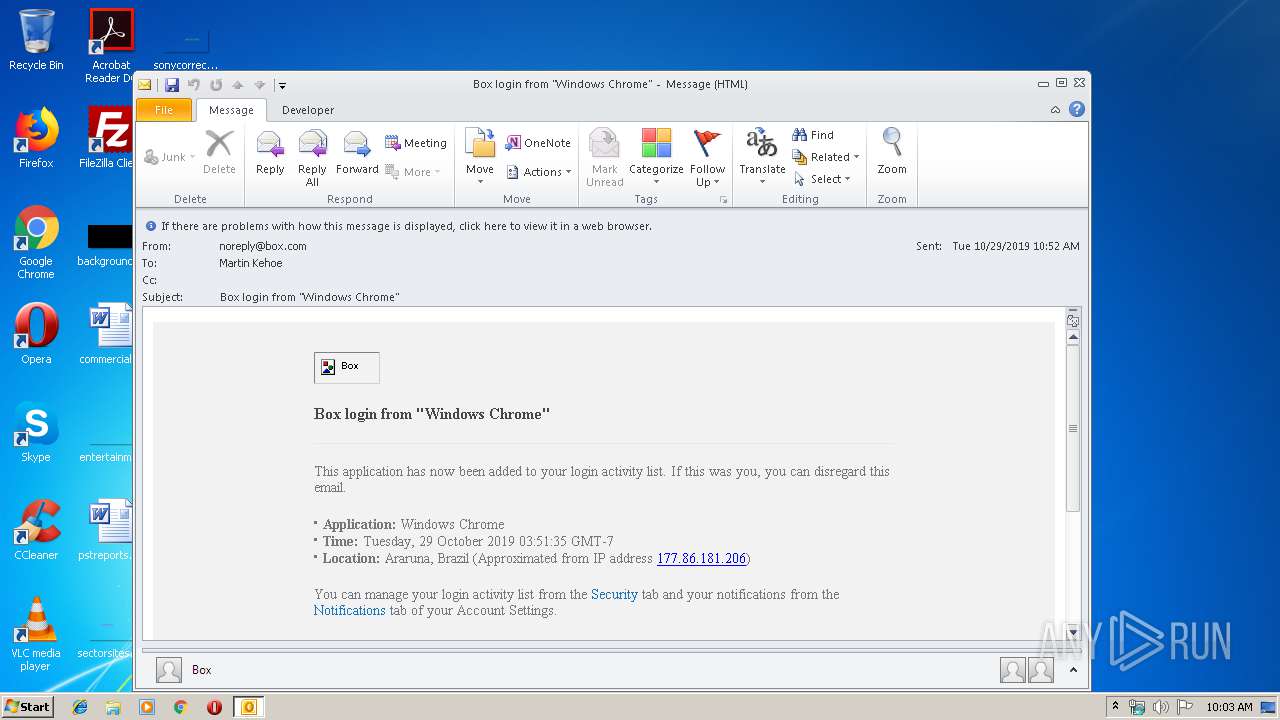
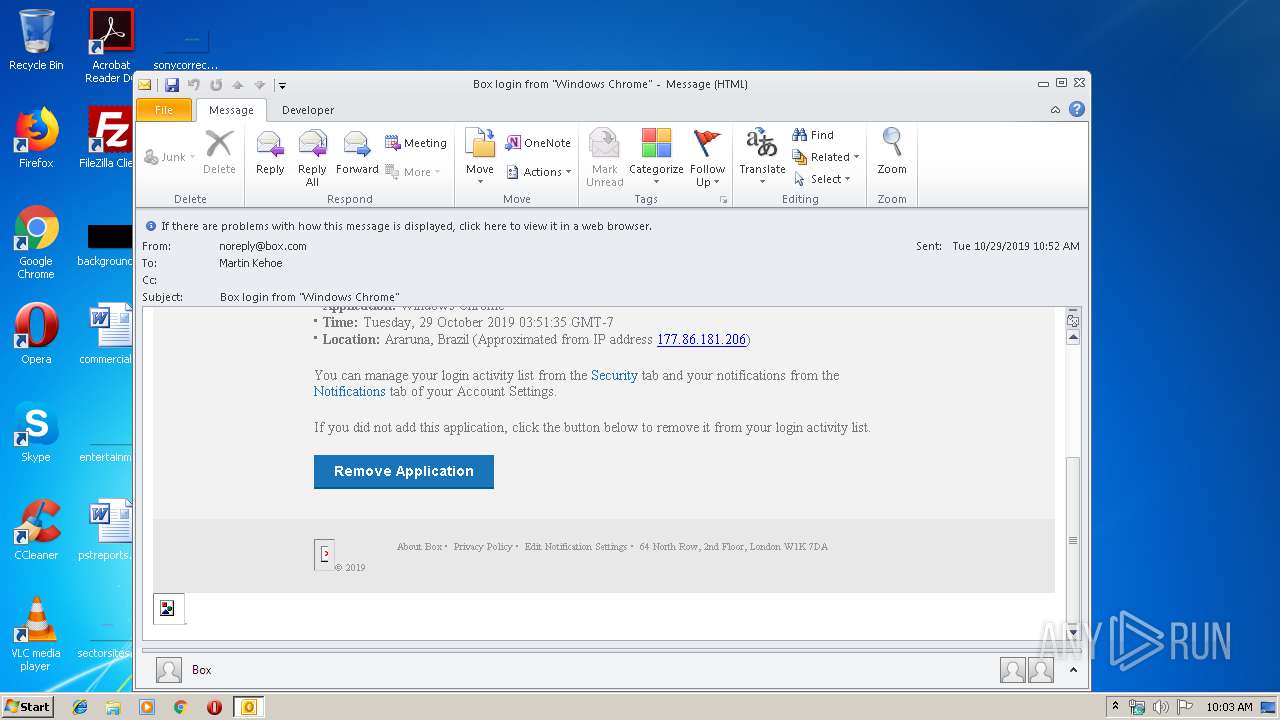
| File name: | Box login from Windows Chrome.msg |
| Full analysis: | https://app.any.run/tasks/9f1ce142-7eaf-47d8-ac5a-52d726261815 |
| Verdict: | Malicious activity |
| Analysis date: | November 05, 2019, 10:03:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 27BB0F0C49EE5C91003991BF69C5DB7B |
| SHA1: | E2E1F849777B4CCC288A238DAF08680C2362470B |
| SHA256: | 37EC279D0292C08DAFA41B415A437066075875779AAB391816419687350265DC |
| SSDEEP: | 768:29G00mwJmaeQeXrwLkrMgpL+wDNhd5Eal7Z6oQlZtmD4e:uP0mwJmMeXkUMgllZ5e |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2364)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2364)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2364)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2364)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2364)
Reads internet explorer settings
- iexplore.exe (PID: 2500)
Changes internet zones settings
- iexplore.exe (PID: 1096)
Reads Internet Cache Settings
- iexplore.exe (PID: 2500)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
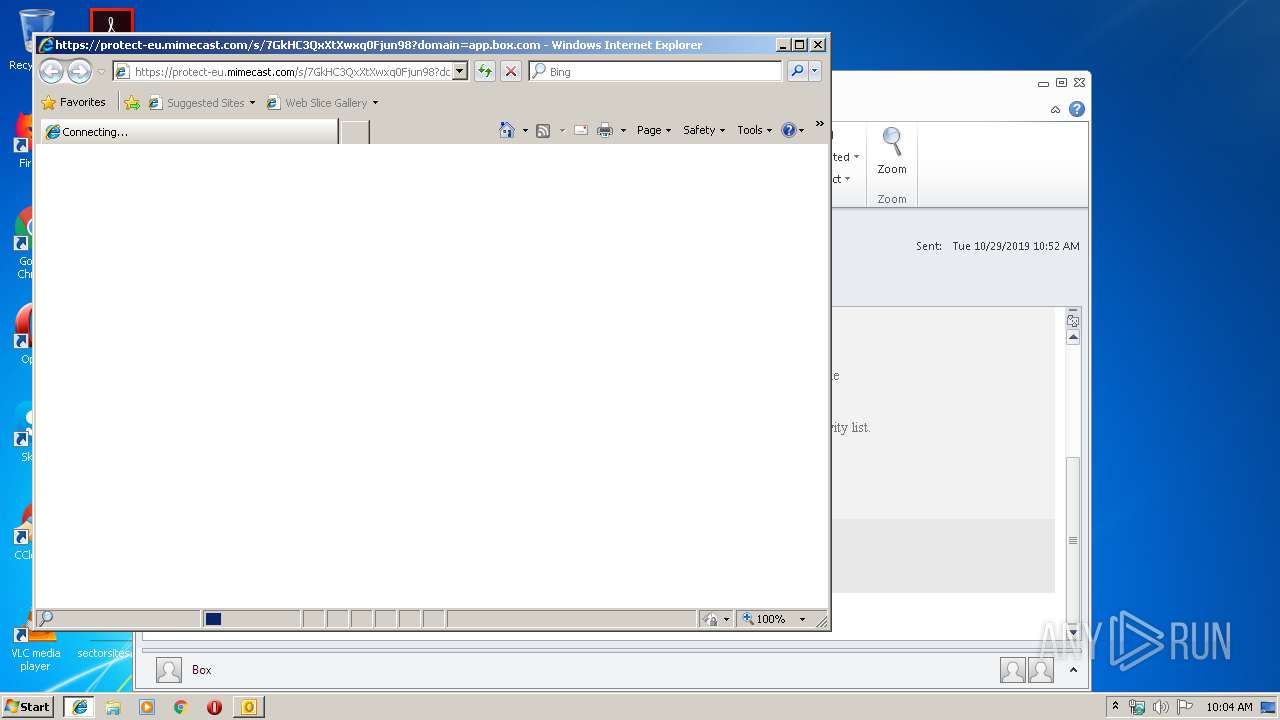
| 1096 | "C:\Program Files\Internet Explorer\iexplore.exe" https://protect-eu.mimecast.com/s/7GkHC3QxXtXwxq0Fjun98?domain=app.box.com | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2364 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Box login from Windows Chrome.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2500 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1096 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 899
Read events
1 289
Write events
591
Delete events
19
Modification events
| (PID) Process: | (2364) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2364) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2364) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2364) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2364) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2364) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2364) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2364) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2364) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1332019380 | |||
| (PID) Process: | (2364) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources |
| Operation: | write | Name: | UISnapshot |
Value: 1033;1046;1036;1031;1040;1041;1049;3082;1042;1055 | |||
Executable files
0
Suspicious files
2
Text files
40
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2364 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA87F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1096 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1096 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2500 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab2FC0.tmp | — | |
MD5:— | SHA256:— | |||
| 2500 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2FC1.tmp | — | |
MD5:— | SHA256:— | |||
| 2500 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab2FD2.tmp | — | |
MD5:— | SHA256:— | |||
| 2500 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2FD3.tmp | — | |
MD5:— | SHA256:— | |||
| 2500 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab309F.tmp | — | |
MD5:— | SHA256:— | |||
| 2500 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar30AF.tmp | — | |
MD5:— | SHA256:— | |||
| 2364 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
19
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2364 | OUTLOOK.EXE | GET | 503 | 162.88.175.18:80 | http://trk.email.dynect.net/trk.php?a=/o2/66/%2B4aqk1bRO2i%2FtmOuUntz6kKj44LEct2R5VK7YMhzWgnOgSDyhJtUaG%2FGgZ8zzMIOeM2J783aMXblwC%2FmG3DporTFBCW006kPrr7q0O8Os9vINlc6G%2BtyArxZntskkf3HJ9etMIgjvLs%3D/i.gif&i=20191029105135.000008330630%40mail6-99-ussnn1&x= | US | — | — | whitelisted |
2364 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2500 | iexplore.exe | GET | 200 | 8.253.95.120:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.0 Kb | whitelisted |
1096 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 162.88.175.18:80 | trk.email.dynect.net | Dynamic Network Services, Inc. | US | unknown |
2364 | OUTLOOK.EXE | 185.235.236.197:443 | www.box.com | — | — | suspicious |
2364 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2364 | OUTLOOK.EXE | 104.18.103.56:443 | cdn01.boxcdn.net | Cloudflare Inc | US | shared |
— | — | 104.18.103.56:443 | cdn01.boxcdn.net | Cloudflare Inc | US | shared |
2500 | iexplore.exe | 195.130.217.187:443 | protect-eu.mimecast.com | Mimecast Services Limited | GB | suspicious |
— | — | 185.235.236.198:443 | app.box.com | — | — | unknown |
2500 | iexplore.exe | 185.235.236.198:443 | app.box.com | — | — | unknown |
— | — | 8.253.95.120:80 | www.download.windowsupdate.com | Global Crossing | US | suspicious |
1096 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn01.boxcdn.net |
| whitelisted |
www.box.com |
| whitelisted |
trk.email.dynect.net |
| unknown |
config.messenger.msn.com |
| whitelisted |
protect-eu.mimecast.com |
| whitelisted |
www.bing.com |
| whitelisted |
dns.msftncsi.com |
| shared |
www.download.windowsupdate.com |
| whitelisted |
app.box.com |
| whitelisted |